security and trusted vs Vulnerability vs Structure Space
安全与可信 security and trusted 脆弱性安全 vs. 结构性安全 Vulnerability vs. Structure 攻防两端如何在结构性安全环境中寻求空间 Space in the structural environment 潘柱廷(大潘) Jordan Pan http: //blog. jordanpan. cn mailto: jordan@venustech. com. cn 1
摘要Summary • 脆弱性安全Vulnerability-oriented security • 结构性安全Structural security • 结构性安全中的脆弱性 Vulnerabilities in structures • 结构性威胁Structural threats 2
脆弱性安全 Vulnerability-oriented security 3
脆弱性Vulnerabilities • • • 弱口令 simple password 病毒 virus 操作系统漏洞 OS flaw 协议漏洞 protocol flaw 造成拒绝服务攻击的性能限制 performance limitation • 防火墙配置不当 bad configuration of firewalls • …… 4
面向脆弱性的安全 Vulnerability-oriented security • • 防病毒系统 anti-virus system 漏洞扫描系统 vulnerability scanner 补丁管理系统 patch management system 入侵检测系统 IDS 防拒绝服务攻击系统 anti-Do. S 防火墙 Firewall 多功能安全网关 UTM …… 5
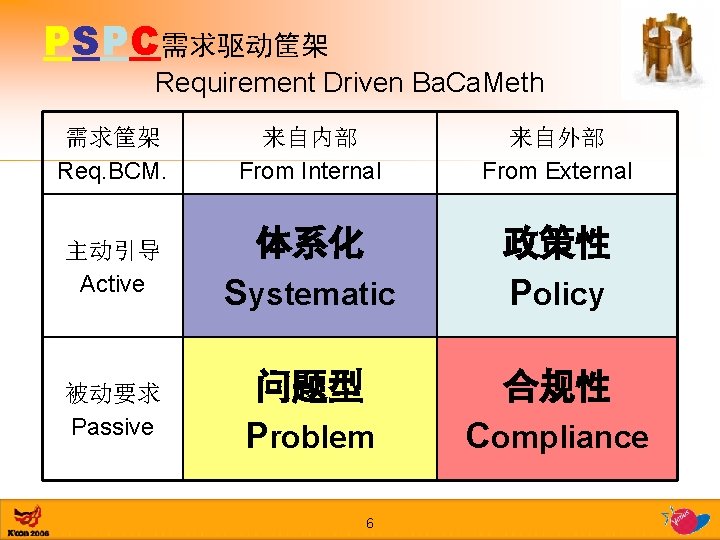
PSPC需求驱动筐架 Requirement Driven Ba. Ca. Meth 需求筐架 Req. BCM. 主动引导 Active 被动要求 Passive 来自内部 From Internal 来自外部 From External 体系化 政策性 Policy Systematic 问题型 Problem 6 合规性 Compliance
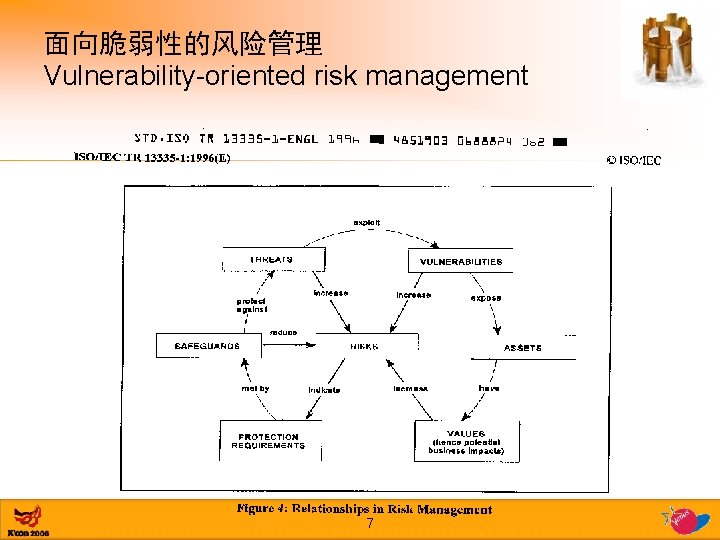
面向脆弱性的风险管理 Vulnerability-oriented risk management 7
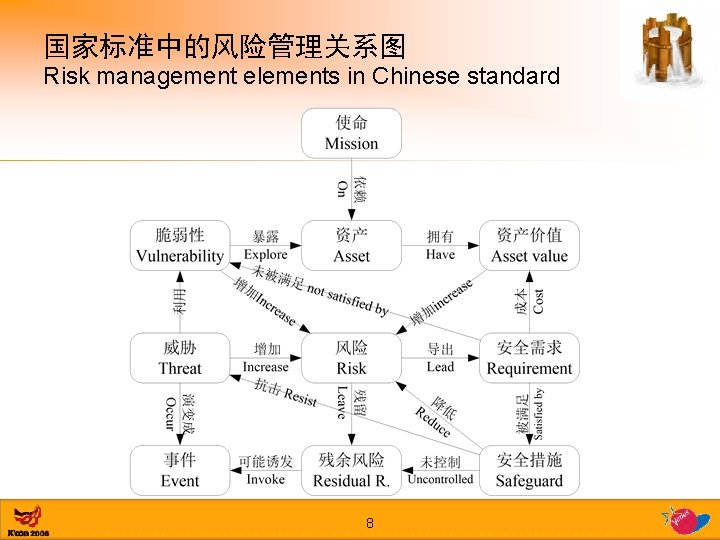
国家标准中的风险管理关系图 Risk management elements in Chinese standard 8
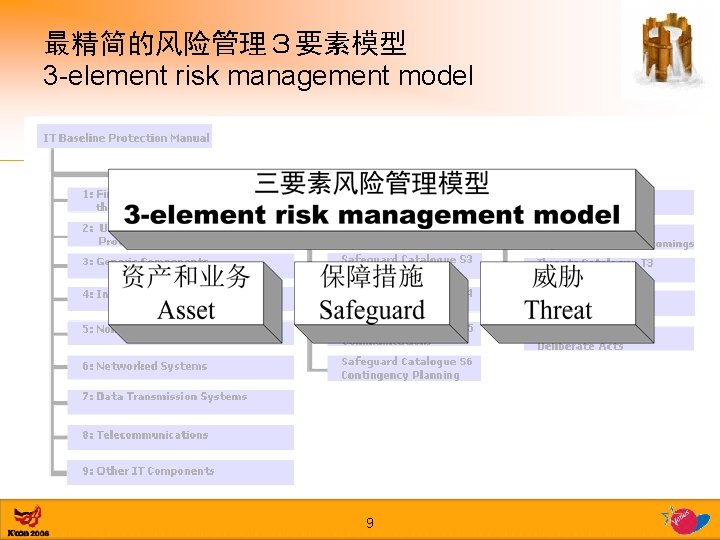
最精简的风险管理3要素模型 3 -element risk management model 9
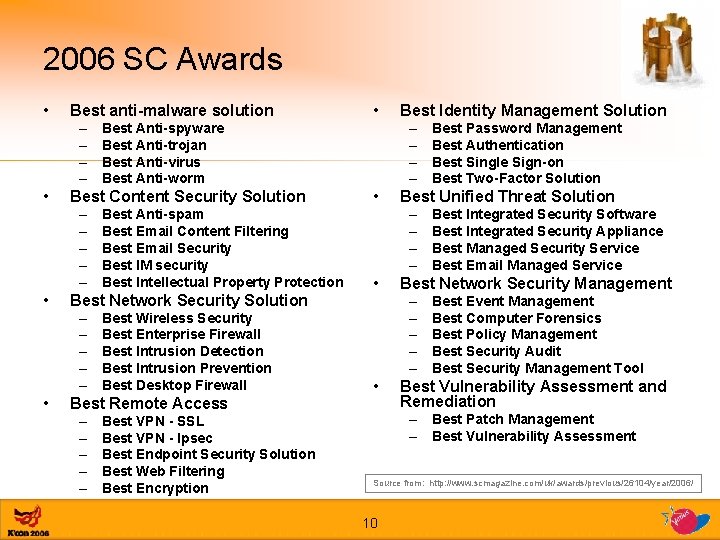
2006 SC Awards • Best anti-malware solution – – • • Best Network Security Solution – – – • Best Anti-spam Best Email Content Filtering Best Email Security Best IM security Best Intellectual Property Protection Best Wireless Security Best Enterprise Firewall Best Intrusion Detection Best Intrusion Prevention Best Desktop Firewall Best Remote Access – – – Best VPN - SSL Best VPN - Ipsec Best Endpoint Security Solution Best Web Filtering Best Encryption Best Identity Management Solution – – Best Anti-spyware Best Anti-trojan Best Anti-virus Best Anti-worm Best Content Security Solution – – – • • Best Unified Threat Solution – – • Best Integrated Security Software Best Integrated Security Appliance Best Managed Security Service Best Email Managed Service Best Network Security Management – – – • Best Password Management Best Authentication Best Single Sign-on Best Two-Factor Solution Best Event Management Best Computer Forensics Best Policy Management Best Security Audit Best Security Management Tool Best Vulnerability Assessment and Remediation – Best Patch Management – Best Vulnerability Assessment Source from: http: //www. scmagazine. com/uk/awards/previous/26104/year/2006/ 10
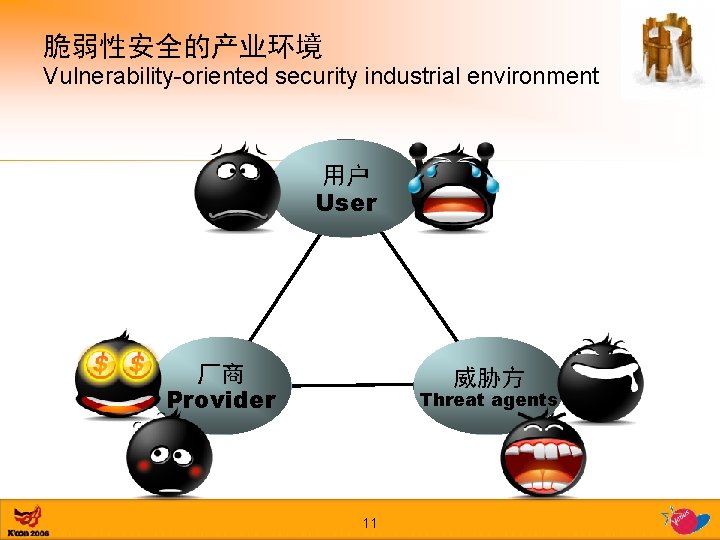
脆弱性安全的产业环境 Vulnerability-oriented security industrial environment 用户 User 厂商 Provider 威胁方 Threat agents 11
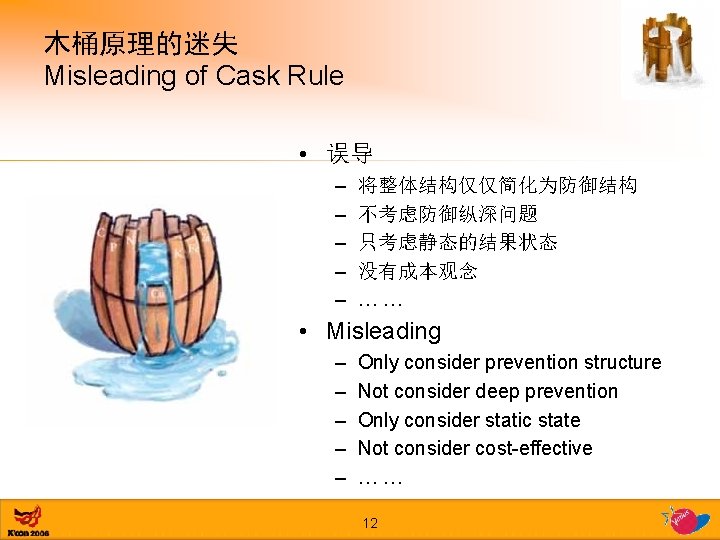
木桶原理的迷失 Misleading of Cask Rule • 误导 – – – 将整体结构仅仅简化为防御结构 不考虑防御纵深问题 只考虑静态的结果状态 没有成本观念 …… • Misleading – – – Only consider prevention structure Not consider deep prevention Only consider static state Not consider cost-effective …… 12
结构性安全 Structural security 基本结构basic structure 紧密结构 tight structure 松散结构loose structure 13
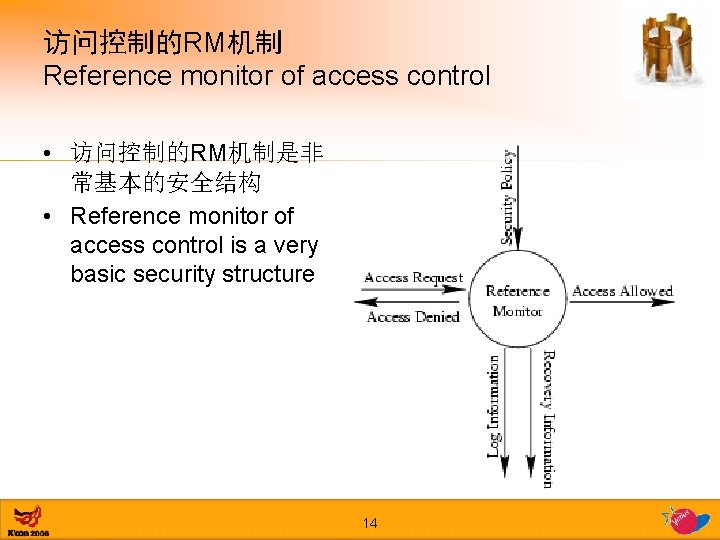
访问控制的RM机制 Reference monitor of access control • 访问控制的RM机制是非 常基本的安全结构 • Reference monitor of access control is a very basic security structure 14
RM机制有效的结构性条件 Structural conditions of valid RM mechanism • 三个条件 • 3 conditions of VRM – Can not be bypass – Can not be tampered – Be small enough, can be proved – 不能被绕过 – 不可篡改 – 足够小,可以被证明 15
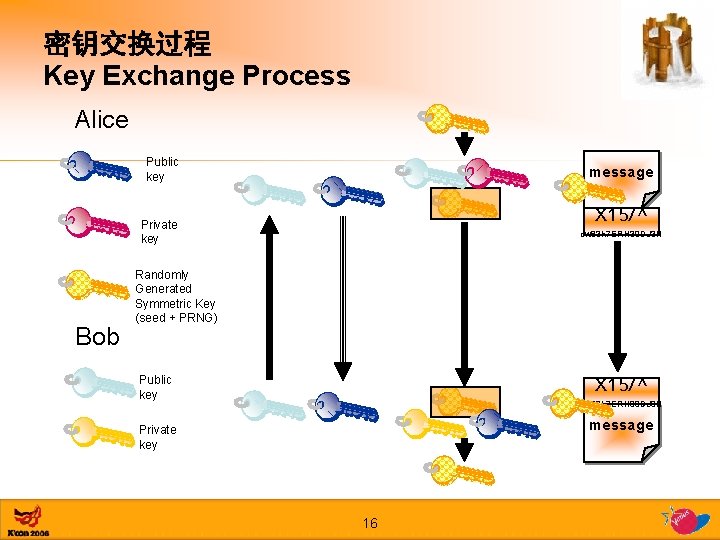
密钥交换过程 Key Exchange Process Alice Public key message X 15/^ Private key Bob ow 83 h 7 ERH 39 DJ 3 H Randomly Generated Symmetric Key (seed + PRNG) Public key X 15/^ ow 83 h 7 ERH 39 DJ 3 H message Private key 16
紧密安全结构的代表——可信计算 Tight security structure — Trusted Computing http: //www. trustedcomputinggroup. org • 可信的定义 Definition of trust – 可信就是,一个设备的行为是按照其预期目标和指定方式执行的 Trust is the expectation that a device will behave in a particular manner for a specific purpose. – 一个可信平台应当至少提供三个基本特性:保护能力、完整性测量 和完整性报告 A trusted platform should provide at least three basic features: protected capabilities, integrity measurement and integrity reporting. (From section 4. 1, TCG Architecture Overview 1. 0) 17
TCG的基石性原理 Fundamental rule of TCG • 信任根就像“公理”一样,是信任的基础。在PC 系统中,常常用硬件芯片实现。 • Roots of trust – In TCG systems roots of trust are components that must be trusted because misbehavior might not be detected. • 信任链则是信任传递的机制。常常采用密码 技术。 • Chains of trust – Transitive trust also known as “Inductive Trust”, is a process where the Root of Trust gives a trustworthy description of a second group of functions. 18
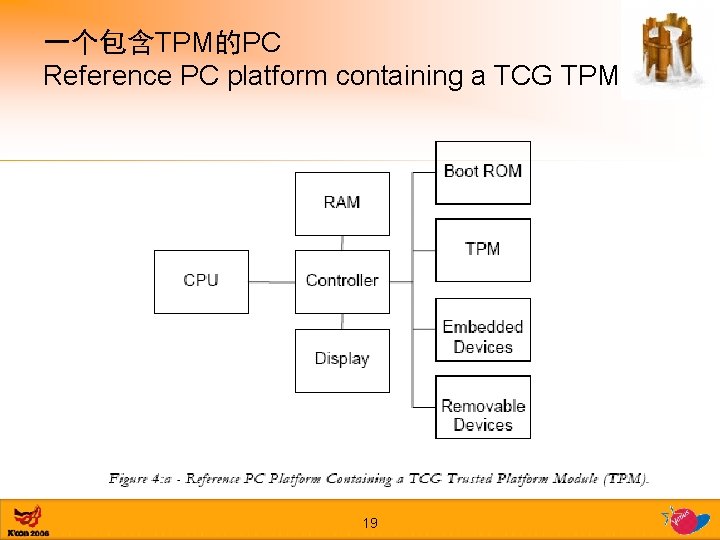
一个包含TPM的PC Reference PC platform containing a TCG TPM 19
TCG – 可信平台模块 TCG – Trusted Platform Module (TPM) • 一个可信平台常常拥有三个可信根 There are commonly three Roots of Trust in a trusted platform – 测量可信根 root of trust for measurement (RTM) – 存储可信根 root of trust for storage (RTS) – 报告可信根 root of trust for reporting (RTR) 20
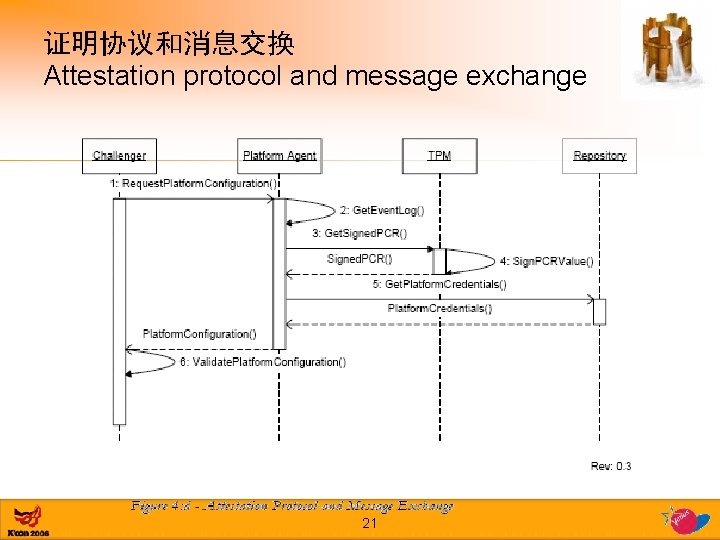
证明协议和消息交换 Attestation protocol and message exchange 21
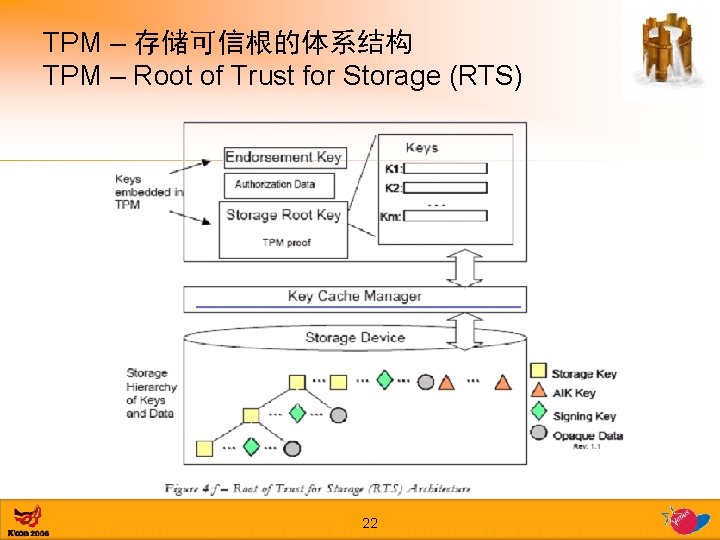
TPM – 存储可信根的体系结构 TPM – Root of Trust for Storage (RTS) 22
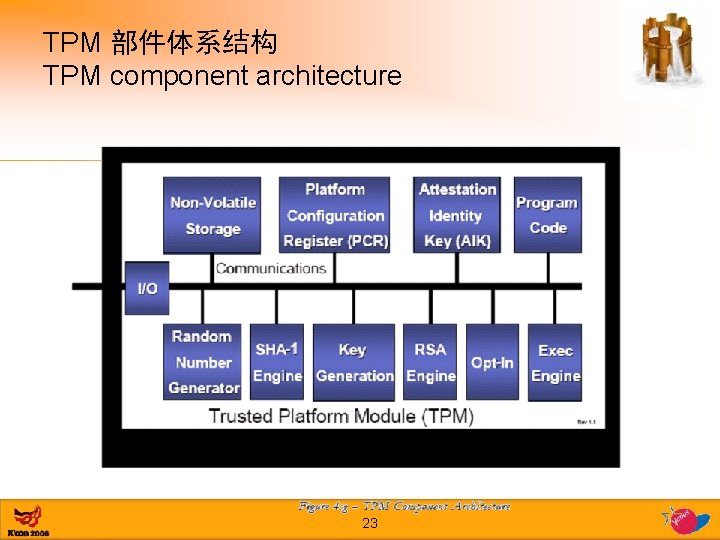
TPM 部件体系结构 TPM component architecture 23
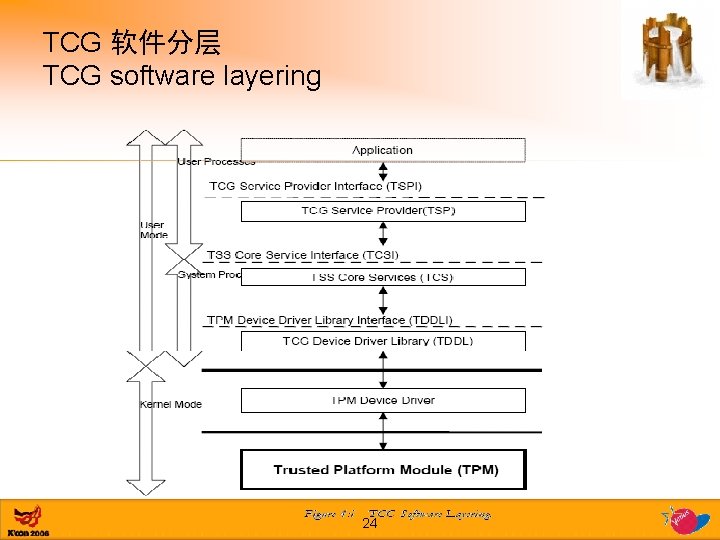
TCG 软件分层 TCG software layering 24
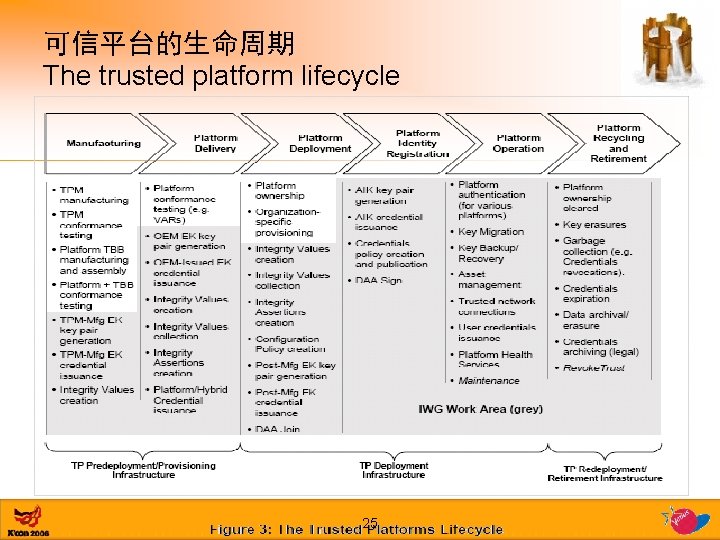
可信平台的生命周期 The trusted platform lifecycle 25
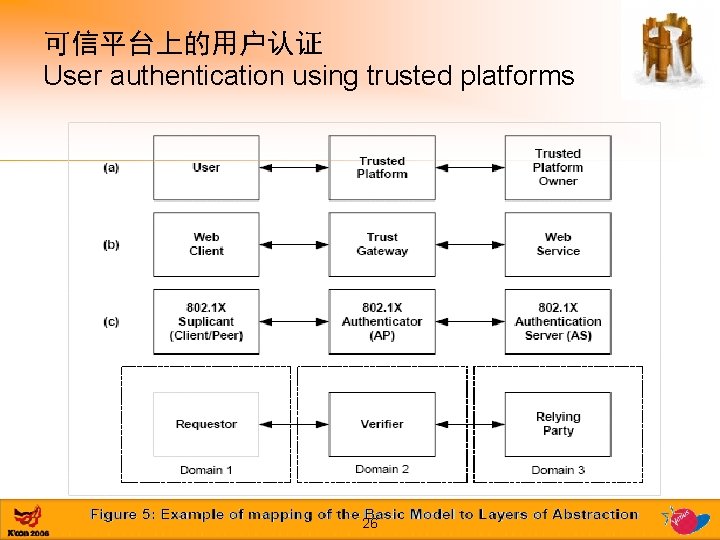
可信平台上的用户认证 User authentication using trusted platforms 26
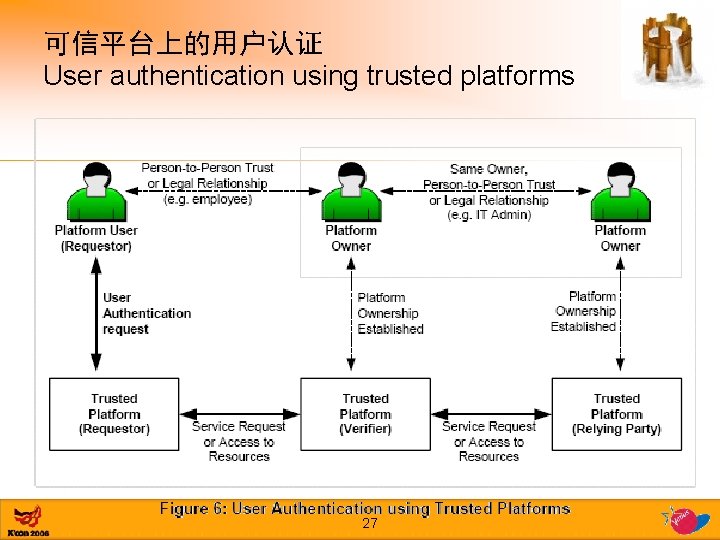
可信平台上的用户认证 User authentication using trusted platforms 27
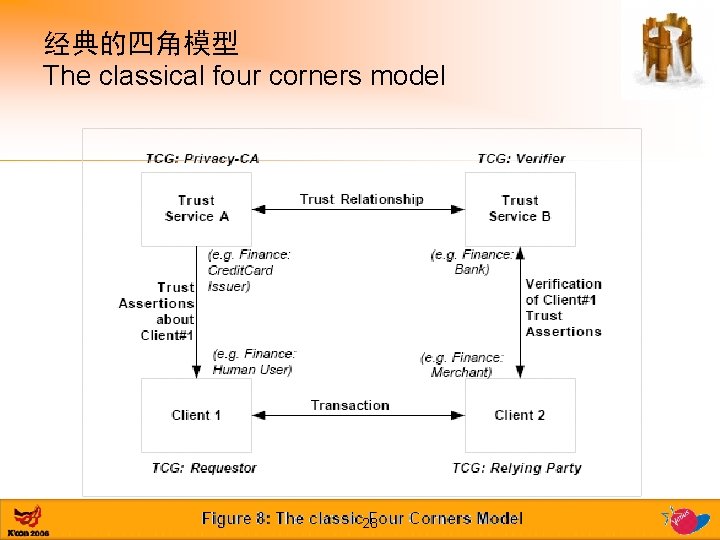
经典的四角模型 The classical four corners model 28
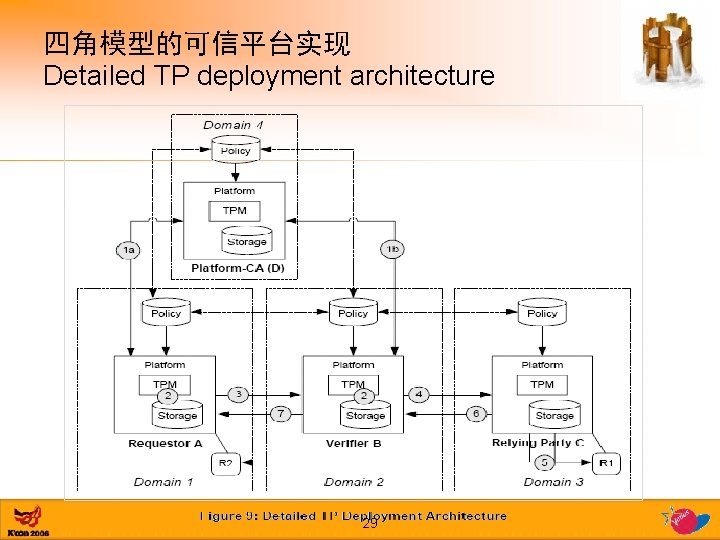
四角模型的可信平台实现 Detailed TP deployment architecture 29
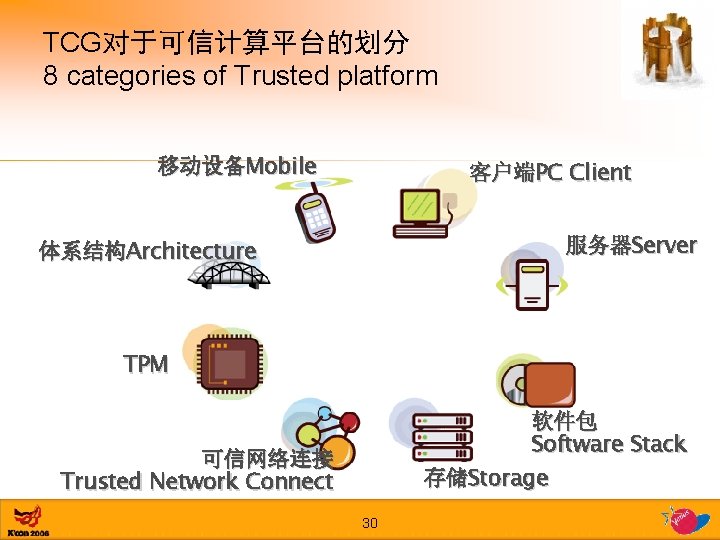
TCG对于可信计算平台的划分 8 categories of Trusted platform 移动设备Mobile 客户端PC Client 服务器Server 体系结构Architecture TPM 软件包 Software Stack 存储Storage 可信网络连接 Trusted Network Connect 30
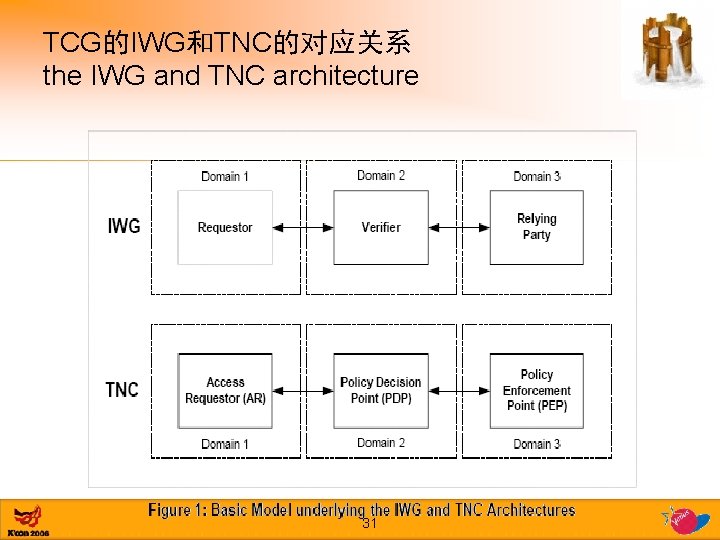
TCG的IWG和TNC的对应关系 the IWG and TNC architecture 31
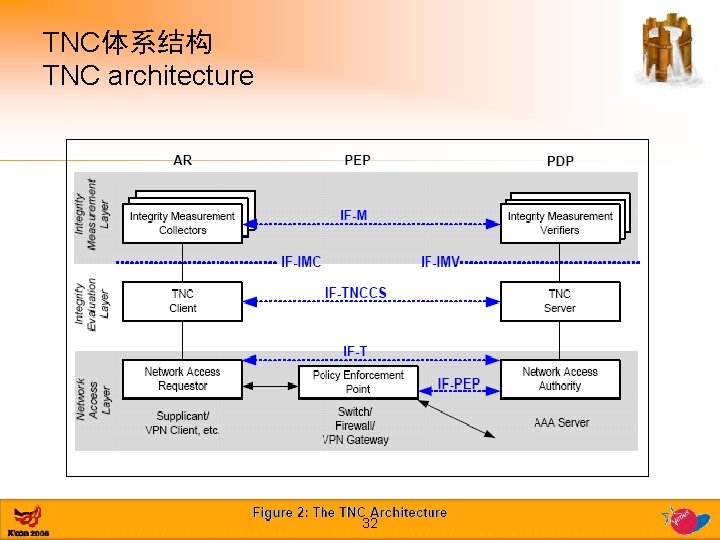
TNC体系结构 TNC architecture 32
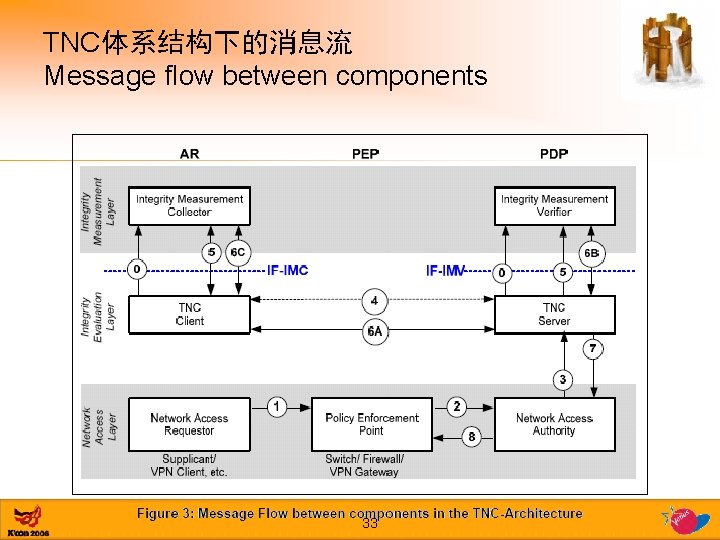
TNC体系结构下的消息流 Message flow between components 33
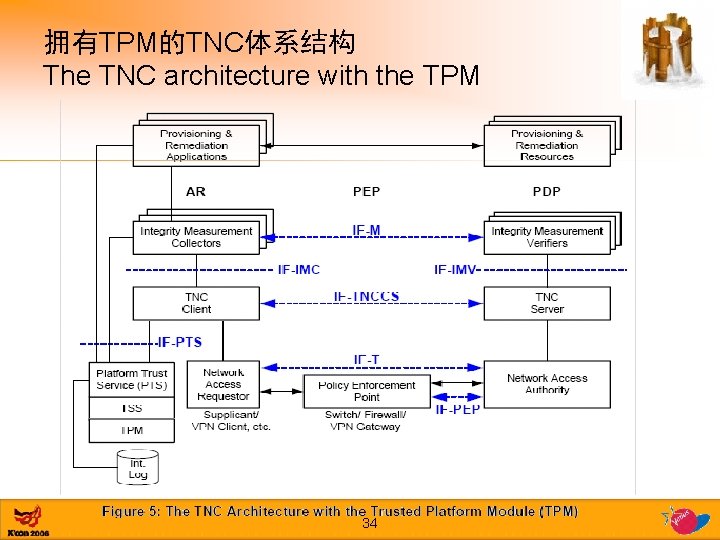
拥有TPM的TNC体系结构 The TNC architecture with the TPM 34
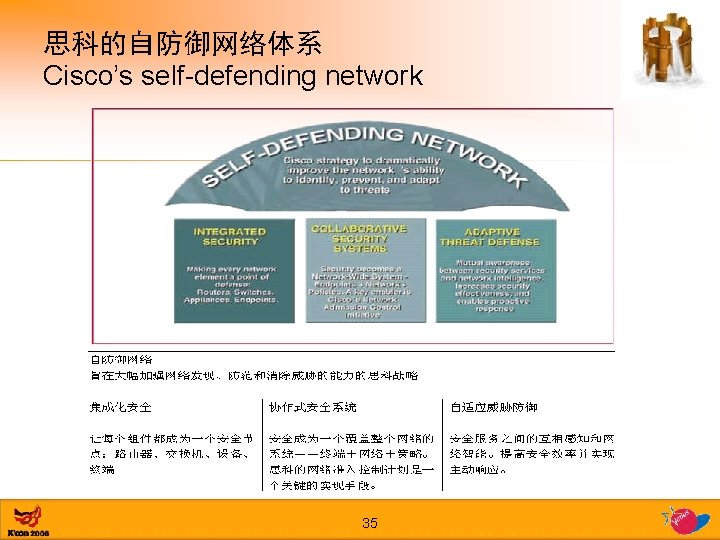
思科的自防御网络体系 Cisco’s self-defending network 35
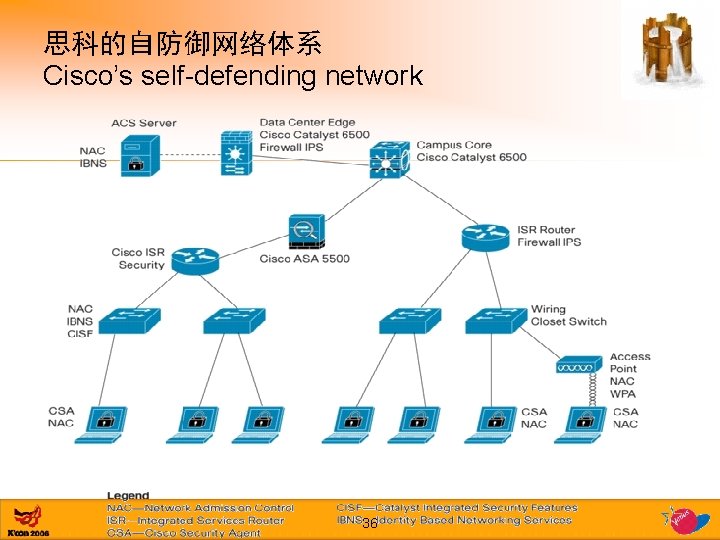
思科的自防御网络体系 Cisco’s self-defending network 36
松散安全结构的代表——框架和方案 Loose security structure — Framework • 松散结构中的各个部件关联关系,常常靠人的集 成来实现 The connection among the components of loose structure is always integrated by human. • 松散结构常常表现为框架Framework – 技术框架Technology framework – 管理体系Management system • ISO 27001, ISO 20000, etc. 37
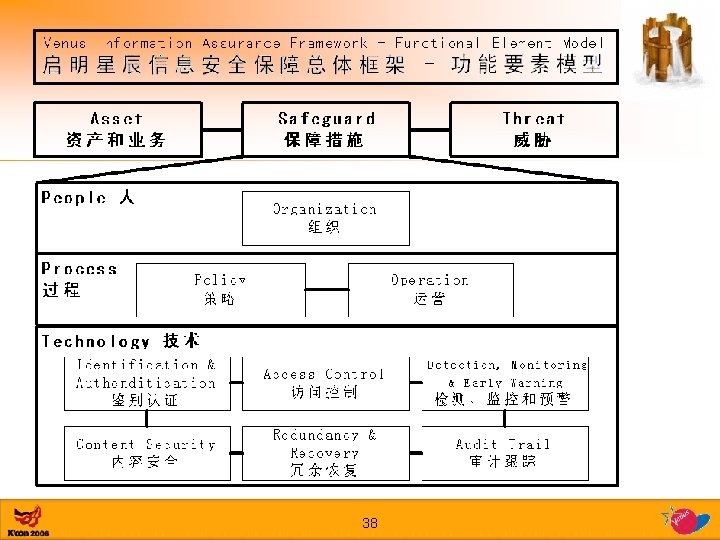
38

技术功能是PDR的衍生 PDR can express technology framework 39
检测能力是松散技术结构的关联要素 Detection make the loose structure tight • 攻击者不得不面对越来越多的 Attackers have to face more – – – – 入侵检测 IDS 漏洞扫描 scanner 应用审计系统 Application auditing system 日志系统 log system 蜜罐 honey pot 取证系统 forensic system 监控平台 monitoring platform 等等 etc. 40
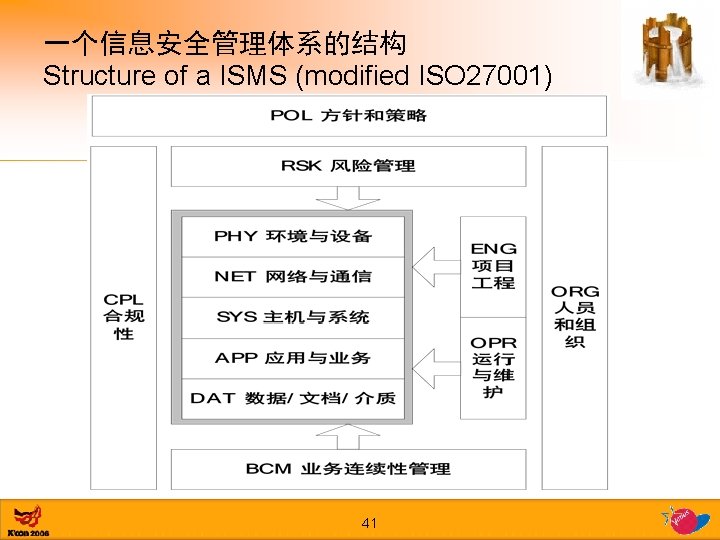
一个信息安全管理体系的结构 Structure of a ISMS (modified ISO 27001) 41
结构性安全中的脆弱性 Vulnerabilities in structures 42
你对刚才阐述的结构性安全有什么感觉? What’s your feeling about structural security? • • • 复杂 complex 怀疑其完备性 concern about the completion 成本 cost 蠢人永远有 stupid guys are there …… 43
不要被“结构性安全”给忽悠了! Do not be misled by structural security • 不要被“结构性安全”给忽悠了!脆弱性安全和结构 性安全并不是对立的,也不是两个发展阶段;脆 弱性安全也有结构,结构性安全也有脆弱性。 • Do not be misled by structural security – Vulnerability-oriented security also has structure – Structural security also has vulnerabilities 44
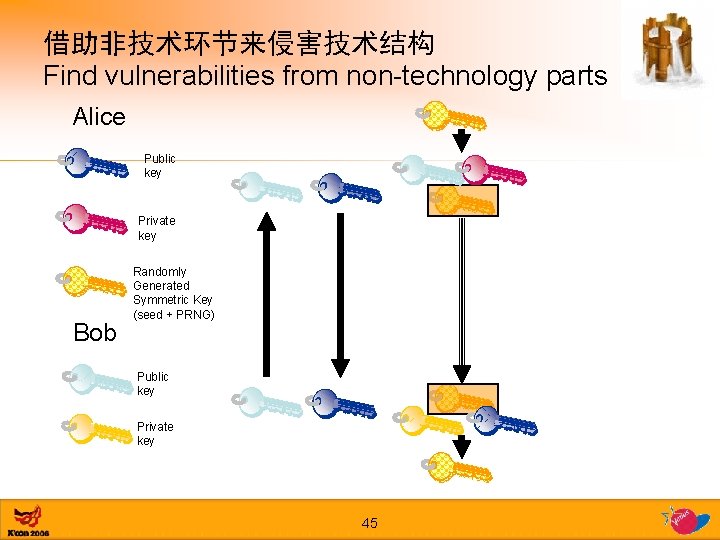
借助非技术环节来侵害技术结构 Find vulnerabilities from non-technology parts Alice Public key Private key Bob Randomly Generated Symmetric Key (seed + PRNG) Public key Private key 45
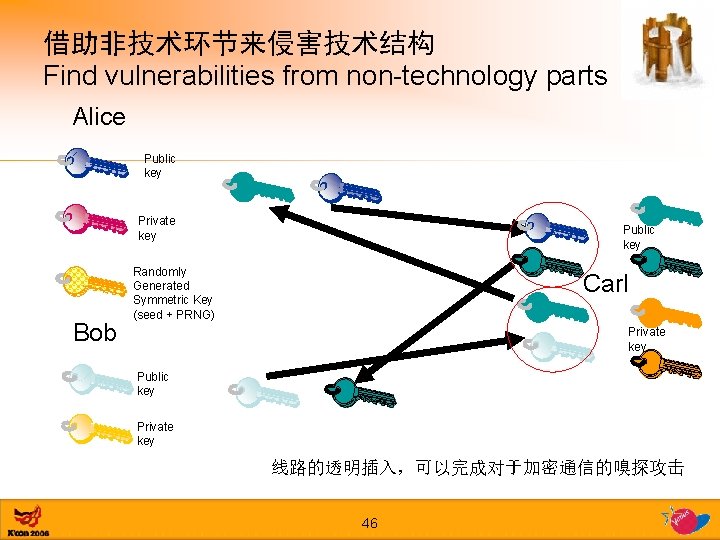
借助非技术环节来侵害技术结构 Find vulnerabilities from non-technology parts Alice Public key Private key Bob Public key Randomly Generated Symmetric Key (seed + PRNG) Carl Private key Public key Private key 线路的透明插入,可以完成对于加密通信的嗅探攻击 46
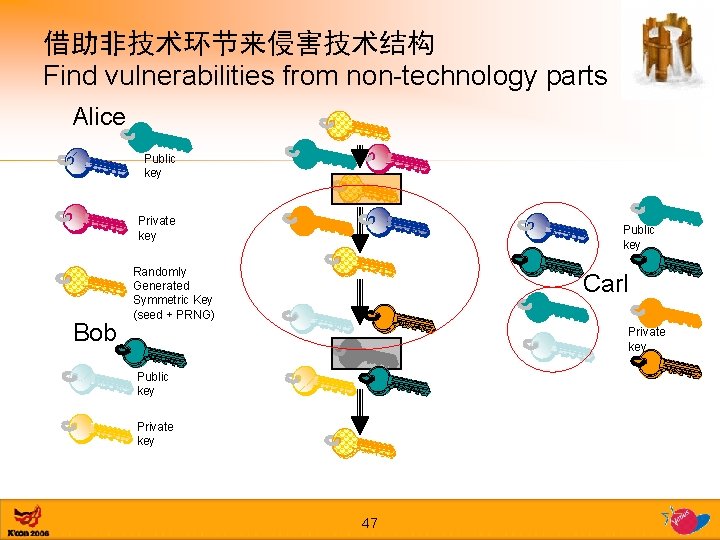
借助非技术环节来侵害技术结构 Find vulnerabilities from non-technology parts Alice Public key Private key Bob Public key Randomly Generated Symmetric Key (seed + PRNG) Carl Private key Public key Private key 47
结构性安全的局限性 Limitation of structural security • 结构是在环境中的、有边界的 environment and boundary 48
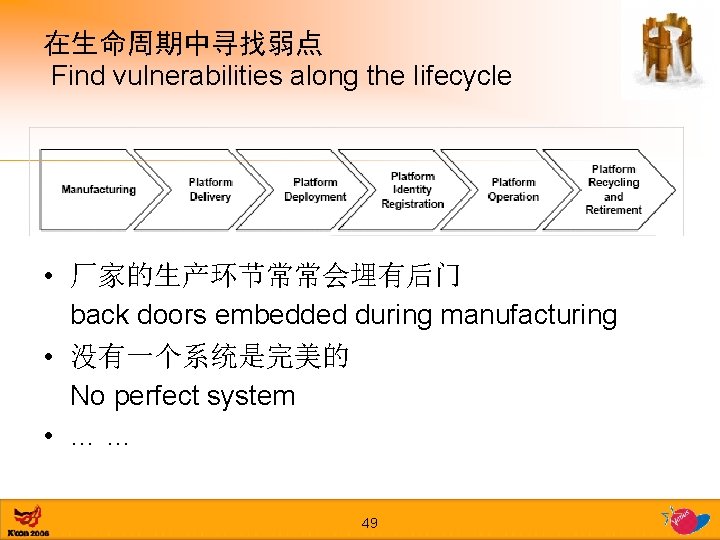
在生命周期中寻找弱点 Find vulnerabilities along the lifecycle • 厂家的生产环节常常会埋有后门 back doors embedded during manufacturing • 没有一个系统是完美的 No perfect system • …… 49
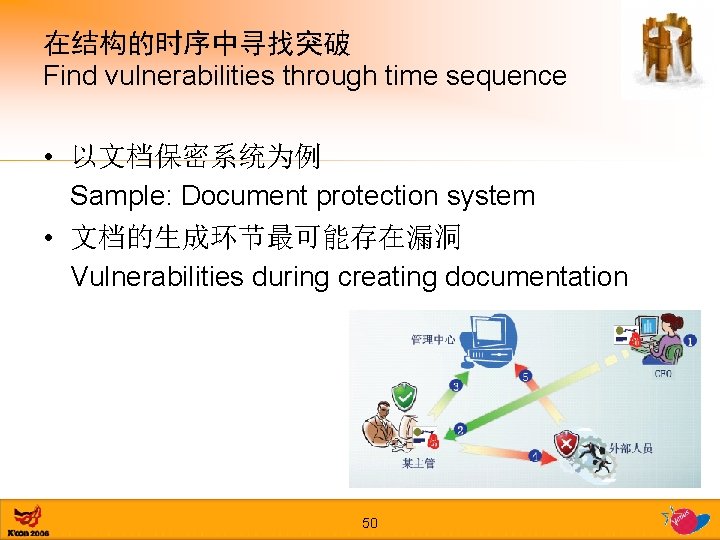
在结构的时序中寻找突破 Find vulnerabilities through time sequence • 以文档保密系统为例 Sample: Document protection system • 文档的生成环节最可能存在漏洞 Vulnerabilities during creating documentation 50
结构性安全的局限性 Limitation of structural security • 结构是在环境中的、有边界的 environment and boundary • 在不同阶段、不同人手中保持安全很困难 different phases and organizations 51
在人性中寻找弱点 Find vulnerabilities from human behavior • • • 社交 程攻击Social Engineering 隐私保护Privacy protection 自由倾向Anti-DRM 懒惰Lazy …… 52
结构性安全的局限性 Limitation of structural security • 结构是在环境中的、有边界的 environment and boundary • 在不同阶段、不同人手中保持安全很困难 different phases and organizations • 人把科学变成了艺术 Human transform science to art 53
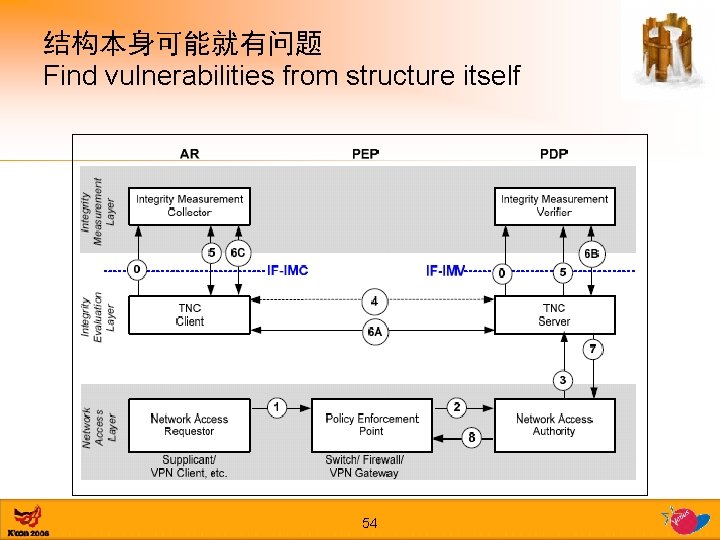
结构本身可能就有问题 Find vulnerabilities from structure itself 54
结构本身可能就有问题 Find vulnerabilities from structure itself • 对于AR/PEP/PDP的伪装,可能打破整个结构 every role may be spoofed • 所有看似漂亮的结构,其性能和可用性问题可能 会非常严重,会轻易被拒绝服务攻击击垮 Most beautiful structures have performance and availability problems and may be easy to be kick down by Do. S. • 那么多传统攻击方式,可能有的还有效 Some traditional attacks are still effective 55
结构性安全还要继续博弈 We are still in the game • 怎么博弈? How to Play the game? – 你了解对方的结构吗? Do you know the structure of all players? – 你了解对方了解多少自己的结构吗? Do you know “how much have the other player known about your structure” ? 56
结构性威胁 Structural threats 知识、资源和原则 Knowledge, Resources and Principles 57
资源 Resources • 从分布式拒绝服务攻击到僵尸网络,掌握具有结 构和组织的攻击体 Botnet is a sample of structural software organization for attacking • 在时序上组成结构,非常有利于攻击 Time sequence spreading is a good thinking of structural attack • …… 59
结构的一些关键字 Key words of structure • • • 业务 分布式 层次 时序 生命周期 管理 • • • – 组织 – 制度 – 过程控制 • 价值 Business Distribution Hierarchy Time sequence Life-cycle Management – Organization – Regular – Process Control • Value 60
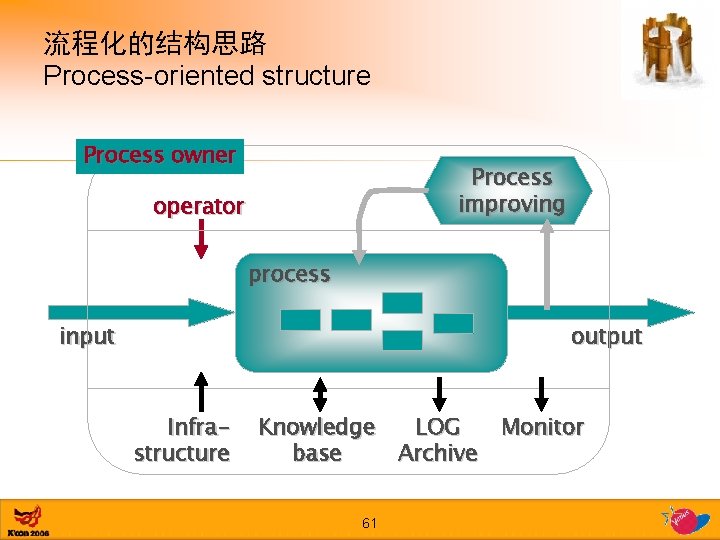
流程化的结构思路 Process-oriented structure Process owner Process improving operator process output input Infrastructure Knowledge LOG base Archive 61 Monitor
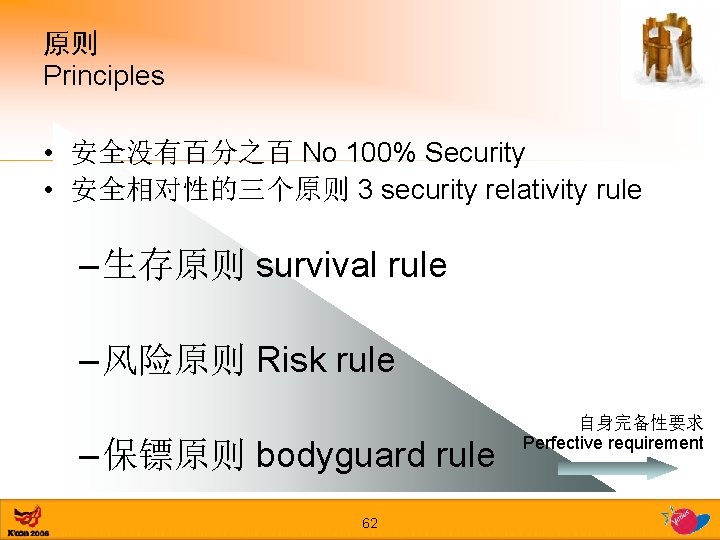
原则 Principles • 安全没有百分之百 No 100% Security • 安全相对性的三个原则 3 security relativity rule – 生存原则 survival rule – 风险原则 Risk rule – 保镖原则 bodyguard rule 62 自身完备性要求 Perfective requirement
总结 Conclusion • 脆弱性安全Vulnerability-oriented security • 结构性安全Structural security • 结构性安全中的脆弱性 Vulnerabilities in structures • 结构性威胁Structural threats 63
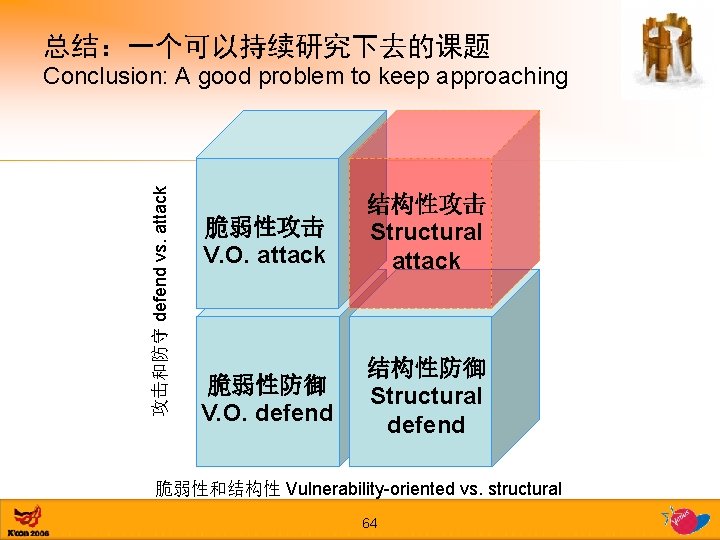
总结:一个可以持续研究下去的课题 攻击和防守 defend vs. attack Conclusion: A good problem to keep approaching 脆弱性攻击 V. O. attack 结构性攻击 Structural attack 脆弱性防御 V. O. defend 结构性防御 Structural defend 脆弱性和结构性 Vulnerability-oriented vs. structural 64
谢谢… Thanks… 大潘 Jordan Pan 65
- Slides: 65