Security and Privacy in PervasiveUbiquitous Computing Systems Chair
Security and Privacy in Pervasive/Ubiquitous Computing Systems Chair Professor Chin-Chen Chang Feng Chia University National Chung Cheng University National Tsing Hua University http: //msn. iecs. fcu. edu. tw/~ccc MSN lab
Outline n n n Mobile services Radio Frequency Identification (RFID) Roaming between cellular network and WLAN MSN lab 2
Mobile services (1/4) MSN lab 3
Mobile services (2/4) MSN lab 4
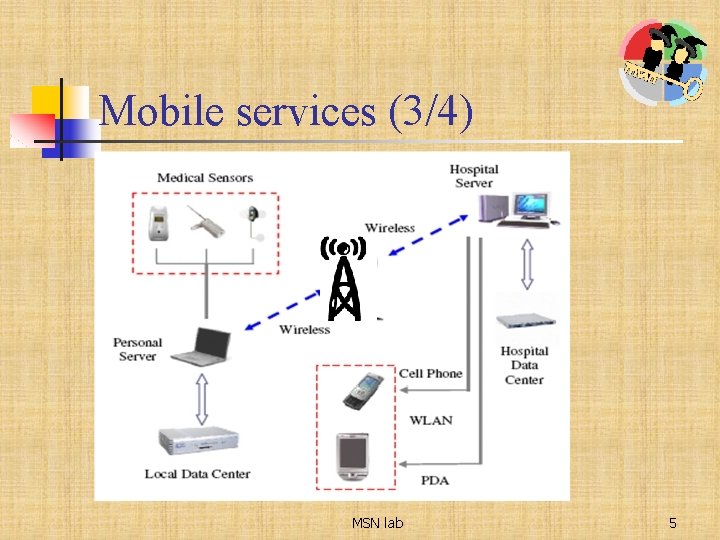
Mobile services (3/4) MSN lab 5
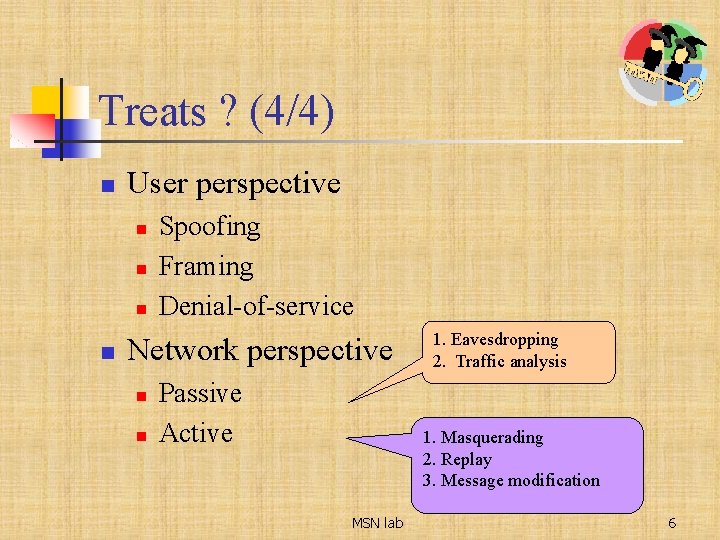
Treats ? (4/4) n User perspective n n Spoofing Framing Denial-of-service Network perspective n n Passive Active 1. Eavesdropping 2. Traffic analysis 1. Masquerading 2. Replay 3. Message modification MSN lab 6
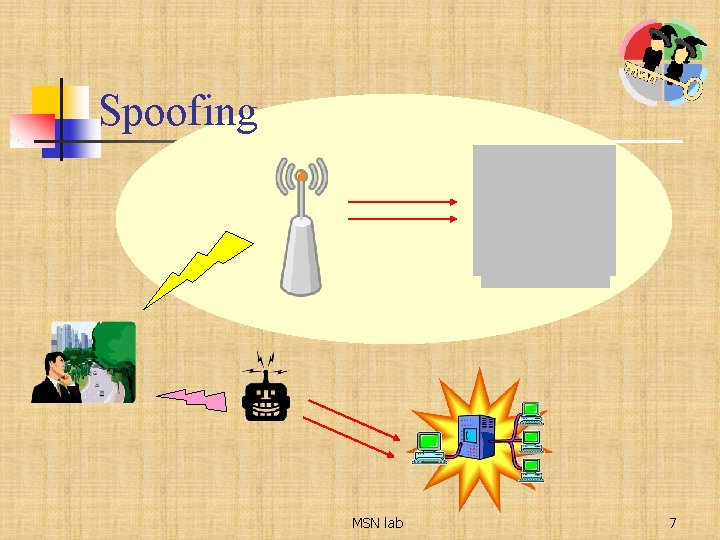
Spoofing MSN lab 7
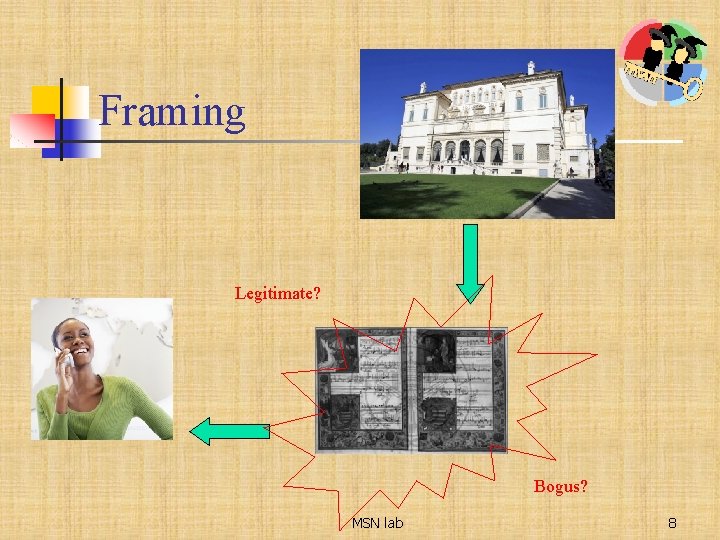
Framing Legitimate? Bogus? MSN lab 8

Denial-of-service MSN lab 9
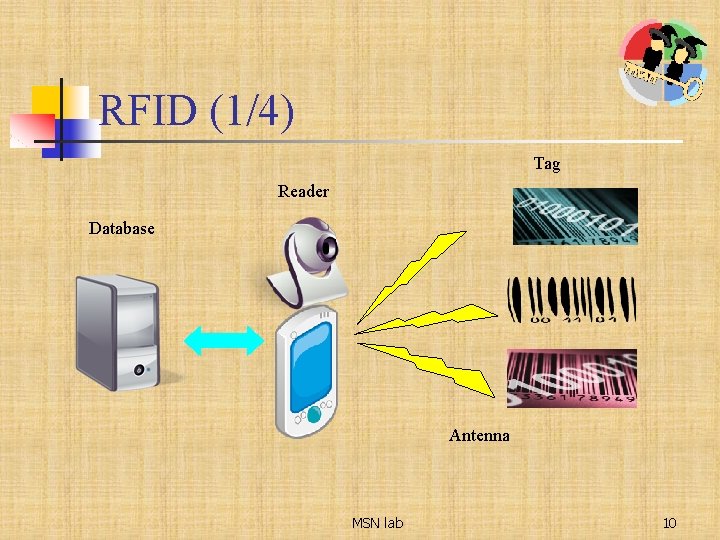
RFID (1/4) Tag Reader Database Antenna MSN lab 10
RFID (2/4) n n n Shopping Library Transportation Household appliance … MSN lab 11
Risk? (3/4) n n n Eavesdropping Traffic analysis Replay attack Position detection Physical attack MSN lab 12
Issue? (4/4) n n Anonymity -> Privacy Synchronization Authentication Efficiency MSN lab 13
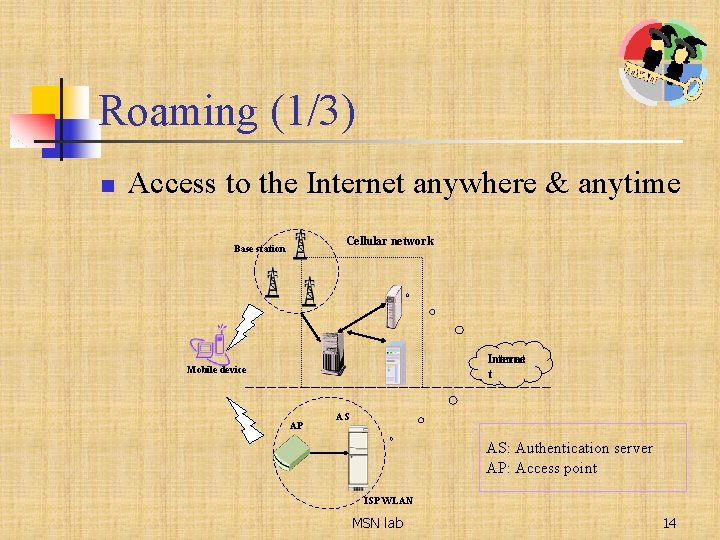
Roaming (1/3) n Access to the Internet anywhere & anytime Cellular network Base station Internet t Mobile device AP AS AS: Authentication server AP: Access point ISP WLAN MSN lab 14
Roaming (2/3) n n n Cellular networks : wide service areas and continuous pervasive access WLAN : high-speed pervasive communications How to integrate? MSN lab 15
Issues? (3/3) n n n Mutual authentication Anonymous service Charging MSN lab 16
Conclusions n n The biggest risk: eavesdropping The limitation: power & computing capability MSN lab 17
Security and Privacy in Pervasive/Ubiquitous Computing Systems MSN lab 18
- Slides: 18