Securing your Personal Wireless Networks By Bryan Oxendale
Securing your Personal Wireless Networks By: Bryan Oxendale
Topics Overview of wireless networks n Types of wireless encryption n Top 5 things to do to secure your wireless network. n Advanced ways of controlling users in accessing network resources n My case study n
Overview of Wireless networks
Wireless Networks Advantages of a Wireless Network. n Easy to install n Easy to configure n Very convenient n Cost efficient Disadvantages of Wireless networks n Security n Speed n Interference People that don’t know how to protect themselves especially in a college town leave their networks open for anyone to get on, take up bandwidth, use network resources, and even lock you out of the network
Types of Wireless Encryption
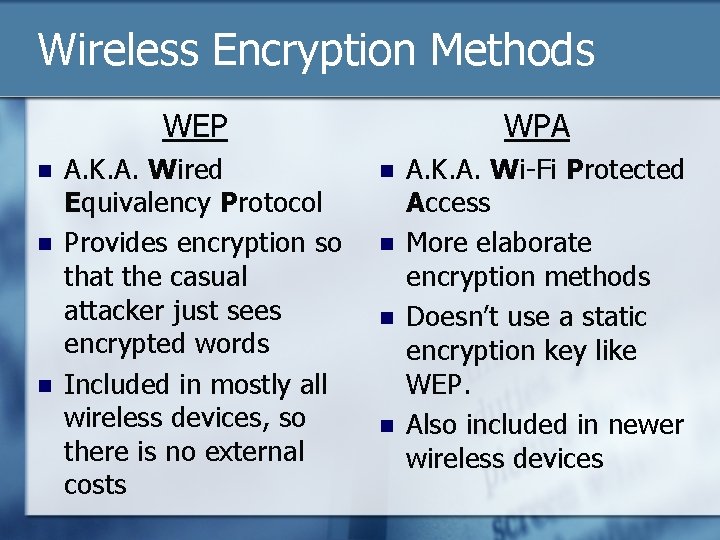
Wireless Encryption Methods WEP n n n A. K. A. Wired Equivalency Protocol Provides encryption so that the casual attacker just sees encrypted words Included in mostly all wireless devices, so there is no external costs WPA n n A. K. A. Wi-Fi Protected Access More elaborate encryption methods Doesn’t use a static encryption key like WEP. Also included in newer wireless devices
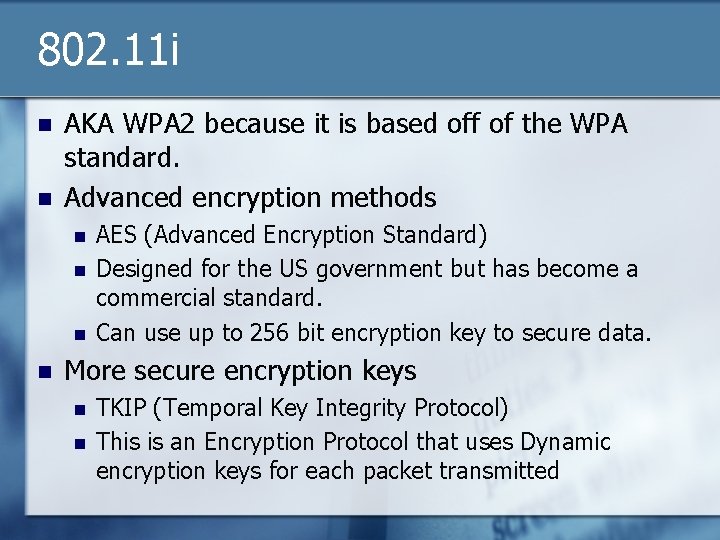
802. 11 i n n AKA WPA 2 because it is based off of the WPA standard. Advanced encryption methods n n AES (Advanced Encryption Standard) Designed for the US government but has become a commercial standard. Can use up to 256 bit encryption key to secure data. More secure encryption keys n n TKIP (Temporal Key Integrity Protocol) This is an Encryption Protocol that uses Dynamic encryption keys for each packet transmitted
Top 5 things to do when you first get a wireless router.
Top 5 things to do when you first get a wireless network 1. 2. 3. 4. 5. Change the default router password Disable SSID broadcast Change SSID Enable WPA 2 encryption Enable MAC address filtering
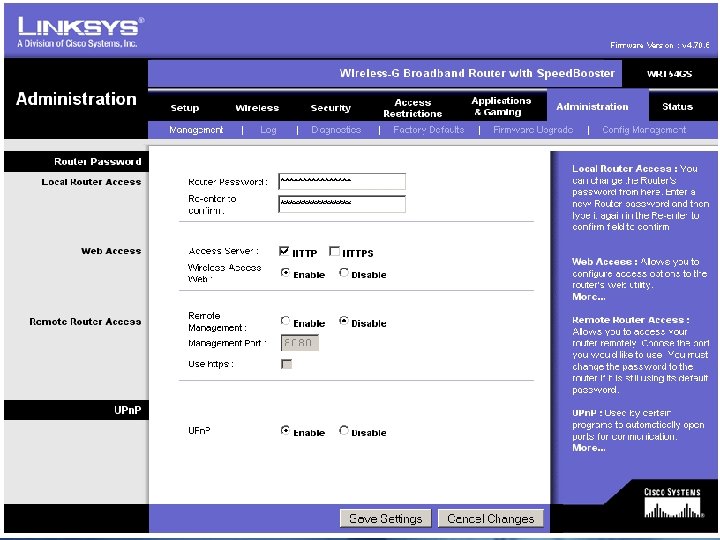
Changing Default Password First thing that you should do n Change the password so that it is secure but so that you can remember it n Reasons to change the password: n So wardrivers cannot get onto you router n So people on your network can’t get on an disable settings. n
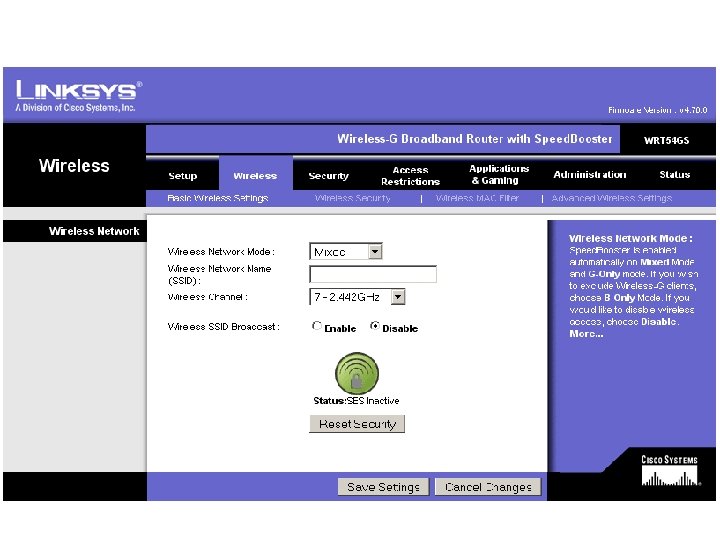
Disabling SSID broadcast. SSID stands for Service Set Identifier n SSID broadcast is the broadcast of your wireless network name. n This SSID name is unique to your network n Reasoning to disable this broadcast n n Prevents any novice attacker from walking down the street and doing a network scan and discovering your wireless network’s SSID.
Changing your SSID Change your SSID to something unique to you or your network. n Anyone that has a little bit of knowledge knows that most of the default SSIDs are manufacturer’s names such as linksys, netgear, dlink, etc… n You want to make sure that you change the SSID often. n
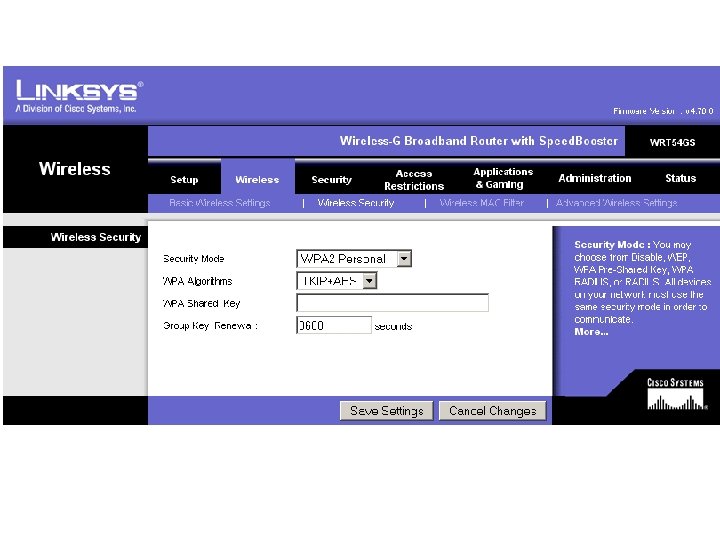
Enabling WPA 2 Chose to enable 802. 11 i a. k. a. WPA 2 because it is the best and most secure method of encryption available to consumers today. n If one of your user’s computer does not support WPA 2 you can still use WPA 2 because it is backwards compatible with WPA n
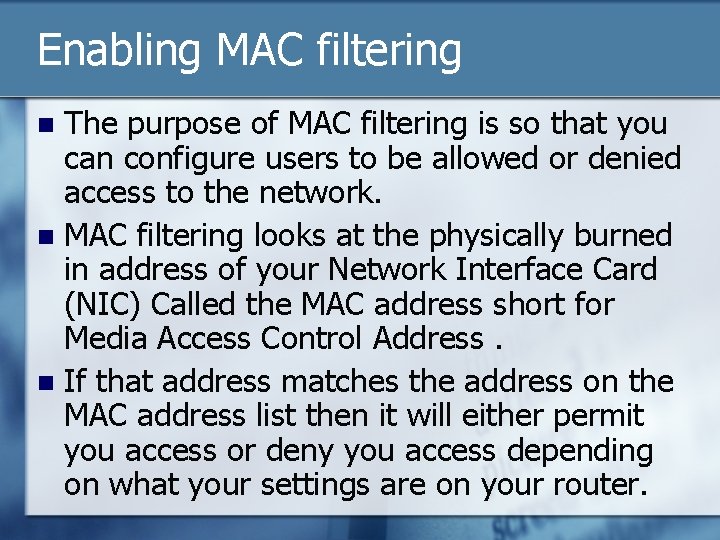
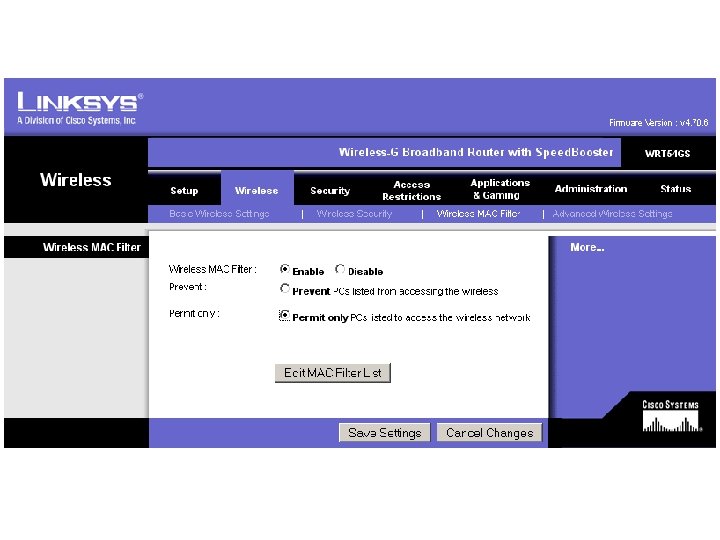
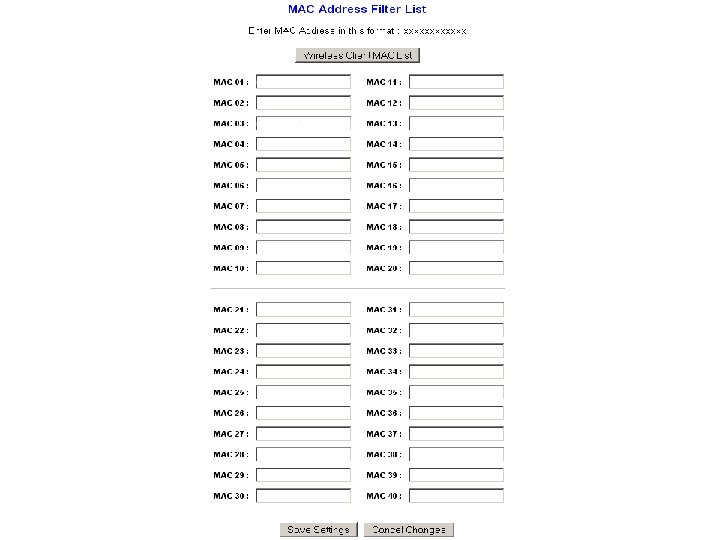
Enabling MAC filtering The purpose of MAC filtering is so that you can configure users to be allowed or denied access to the network. n MAC filtering looks at the physically burned in address of your Network Interface Card (NIC) Called the MAC address short for Media Access Control Address. n If that address matches the address on the MAC address list then it will either permit you access or deny you access depending on what your settings are on your router. n
Advanced ways of controlling internet access
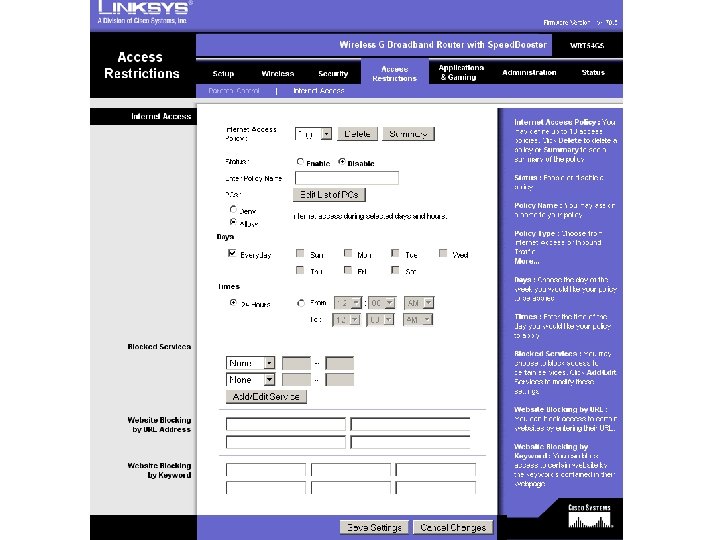
Advanced ways of Controlling Network clients: Internet Access n Internet Limitations n This option is located in the Access restriction tab under internet access. Lets you designate what times a day and week you are going to let users access the internet. n Comes in useful when you have young children or annoying roommates n
Advanced ways of Controlling Network clients: Parental Control n Parental Controls n n n This option is located in the Access restriction tab under Parental Control. This option lets you customize levels of control for each member of your family. You can pick from 16 categories of access Can give you detailed reports of what site you members are trying to access Can also set up Email filters and Instant message filters to chose who your children are talking to.
My Case Study of wireless networks in the Indiana Area
Case Study What I did as a case study is I drove a 2. 7 mile loop around Indiana. I picked 9 locations and did a wireless network search. I counted the total number of wireless networks and then I counted the total number of unprotected networks. The purpose of this was to see how many people out there protect their wireless network.
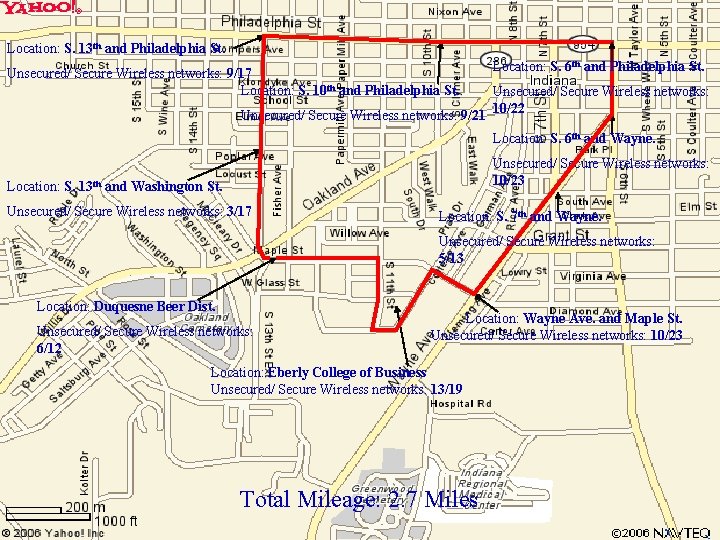
Location: S. 13 th and Philadelphia St. Unsecured/ Secure Wireless networks: 9/17 Location: S. 10 th and Philadelphia St. Unsecured/ Secure Wireless networks: 9/21 Location: S. 6 th and Philadelphia St. Unsecured/ Secure Wireless networks: 10/22 Location: S. 6 th and Wayne. Unsecured/ Secure Wireless networks: 10/23 Location: S. 13 th and Washington St. Unsecured/ Secure Wireless networks: 3/17 Location: S. 7 th and Wayne. Unsecured/ Secure Wireless networks: 5/13 Location: Duquesne Beer Dist. Unsecured/ Secure Wireless networks: 6/12 Location: Wayne Ave. and Maple St. Unsecured/ Secure Wireless networks: 10/23 Location: Eberly College of Business Unsecured/ Secure Wireless networks: 13/19 Total Mileage: 2. 7 Miles
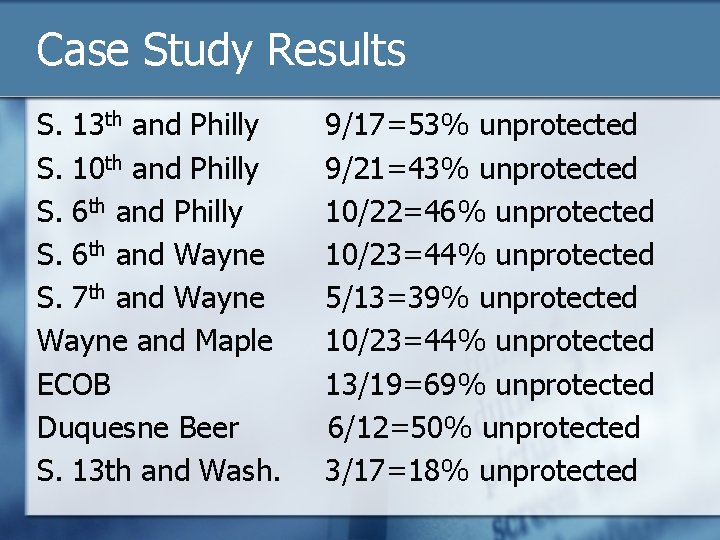
Case Study Results S. 13 th and Philly S. 10 th and Philly S. 6 th and Wayne S. 7 th and Wayne and Maple ECOB Duquesne Beer S. 13 th and Wash. 9/17=53% unprotected 9/21=43% unprotected 10/22=46% unprotected 10/23=44% unprotected 5/13=39% unprotected 10/23=44% unprotected 13/19=69% unprotected 6/12=50% unprotected 3/17=18% unprotected
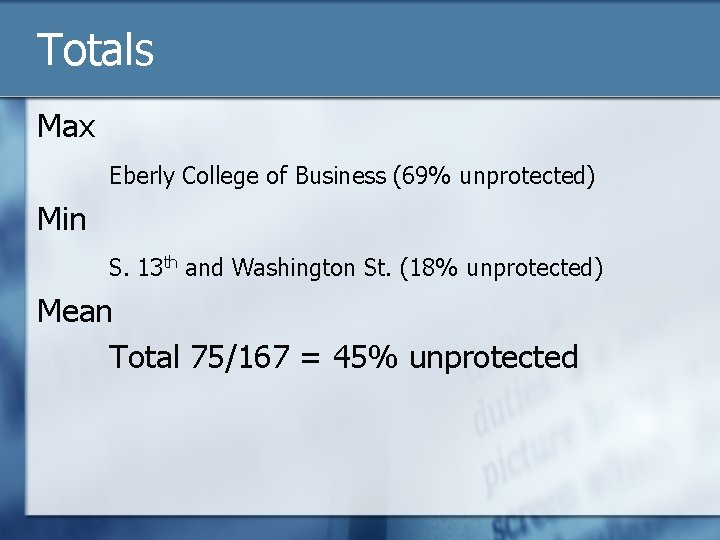
Totals Max Eberly College of Business (69% unprotected) Min S. 13 th and Washington St. (18% unprotected) Mean Total 75/167 = 45% unprotected
Conclusion to Case Study An average of 45% of the networks around this area are unprotected. At least this is below 50% but still this number should be 0% So the more we can talk to people and inform them of how to protect their network the better off everyone will be.
Reference Page n Linksys Wireless G Router with Speedbooster. 4 Oct. 2006 <http: //www. linksys. com>. Path: support; downloads; WRT 54 GS V 2. 0; downloads for the product; User Manual. n Tomsho, Greg, Ed Tittel, and David Johnson. Guide to Networking Essentials. Ed. Will Pitkin, III, et al. 5 th ed. N. p. : Thomson Course Technology, n. d.
The End
- Slides: 31