Securing Your Network Application Availability Radwares Security Solutions
Securing Your Network & Application Availability Radware’s Security Solutions

About Radware

Market Leading Attack Mitigation Solution 7 of Top 14 World’s Stock Exchanges Leading Online Businesses 6 of Top 10 World’s Telcos 12 of Top 22 World’s Commercial Banks 6 of Top 20 World’s Retailers 2 of Top 5 Cloud Service Providers Top organizations using Radware’s Security Services 3
Current Trends
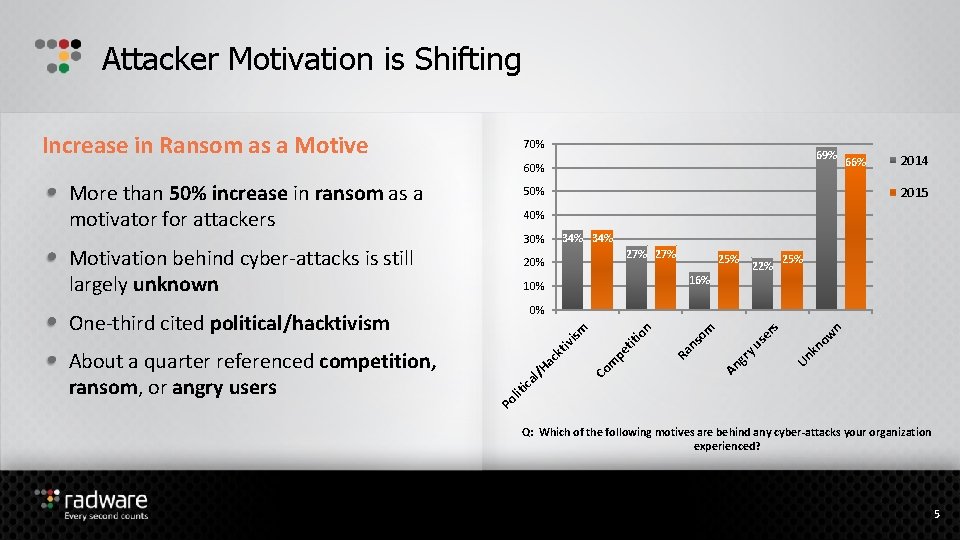
Attacker Motivation is Shifting Increase in Ransom as a Motive 70% 69% 60% More than 50% increase in ransom as a motivator for attackers 50% 2014 2015 40% 30% Motivation behind cyber-attacks is still largely unknown 34% 27% 20% 25% 22% 16% 10% 25% n ow kn Un An gr yu se rs om ns Ra tit pe Co m Po lit ica l/H ac kt iv i io sm n 0% One-third cited political/hacktivism About a quarter referenced competition, ransom, or angry users 66% Q: Which of the following motives are behind any cyber-attacks your organization experienced? 5
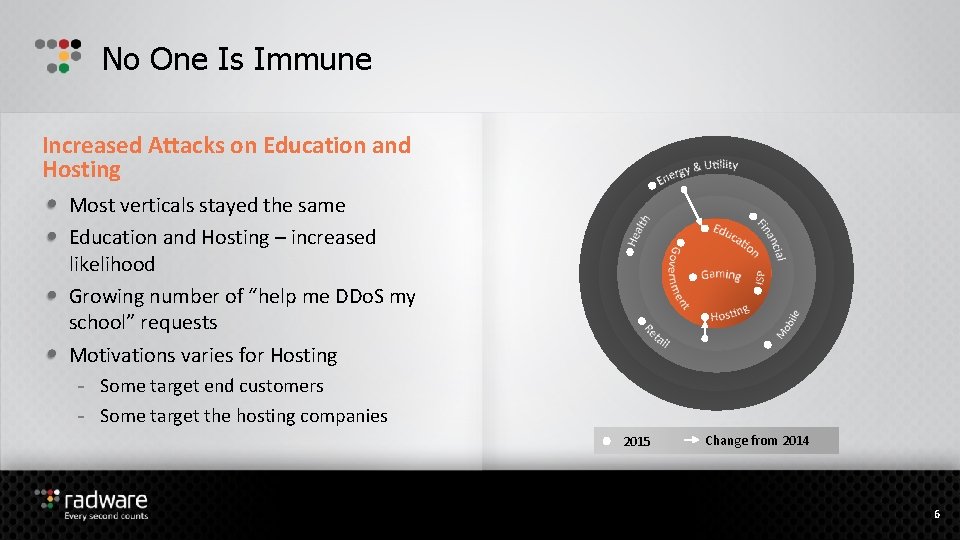
No One Is Immune Increased Attacks on Education and Hosting Most verticals stayed the same Education and Hosting – increased likelihood Growing number of “help me DDo. S my school” requests Motivations varies for Hosting - Some target end customers - Some target the hosting companies 2015 Change from 2014 6
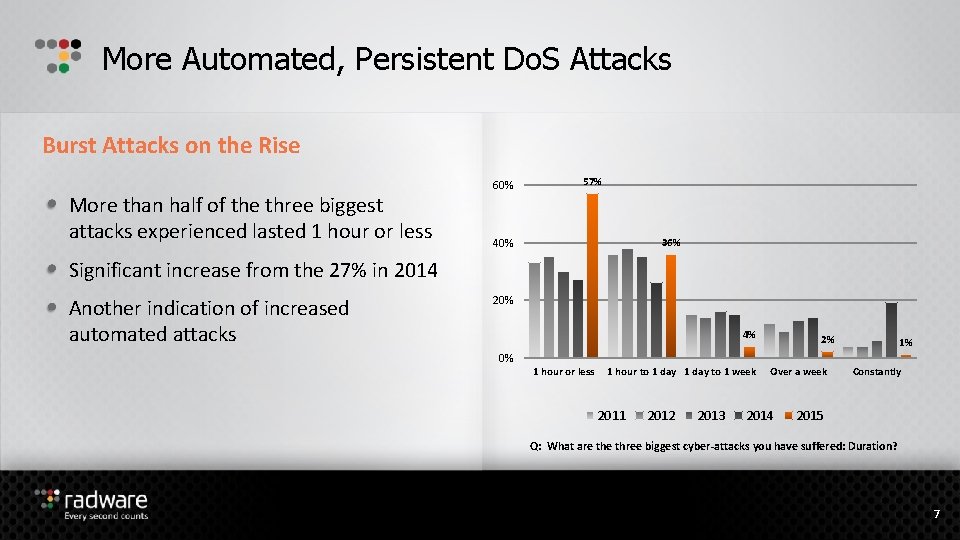
More Automated, Persistent Do. S Attacks Burst Attacks on the Rise More than half of the three biggest attacks experienced lasted 1 hour or less 60% 57% 40% 36% Significant increase from the 27% in 2014 Another indication of increased automated attacks 20% 4% 0% 1 hour or less 1 hour to 1 day to 1 week 2011 2012 2013 2% Over a week 2014 1% Constantly 2015 Q: What are three biggest cyber-attacks you have suffered: Duration? 7
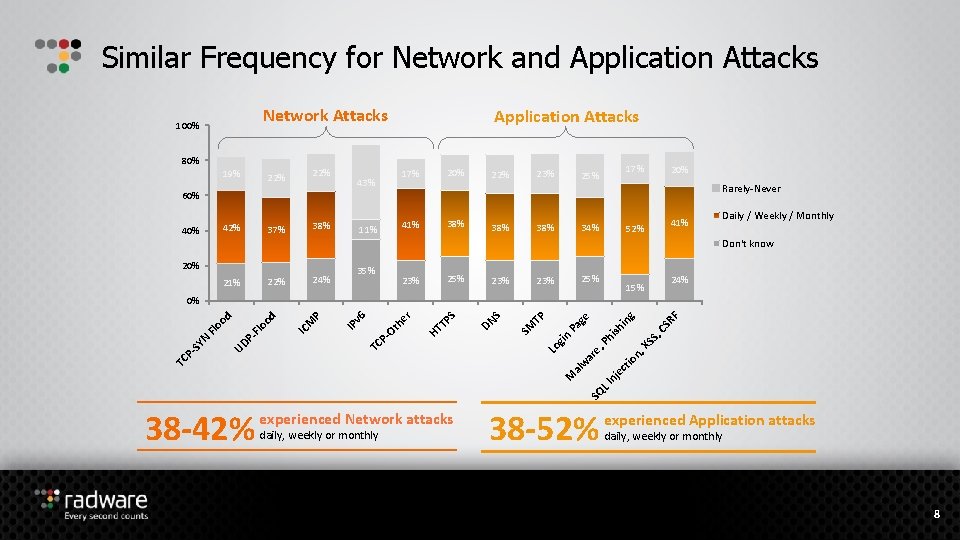
Similar Frequency for Network and Application Attacks Network Attacks 100% 80% 19% 22% Application Attacks 20% 17% 43% 22% 17% 25% 20% Rarely-Never 60% 42% 40% 38% 37% 38% 41% 11% 38% 34% 41% 52% Daily / Weekly / Monthly Don't know 20% 24% 22% 21% 35% 23% 25% 23% 24% 15% in SQ LI M nj ec tio n, e, ar al w XS Ph S, ish Pa n gi Lo CS RF g ge TP SM DN S S TP Ot PTC HT r he v 6 IP P M IC Flo od P- UD TC P- SY N Flo od 0% 38 -42% experienced Network attacks daily, weekly or monthly 38 -52% experienced Application attacks daily, weekly or monthly 8
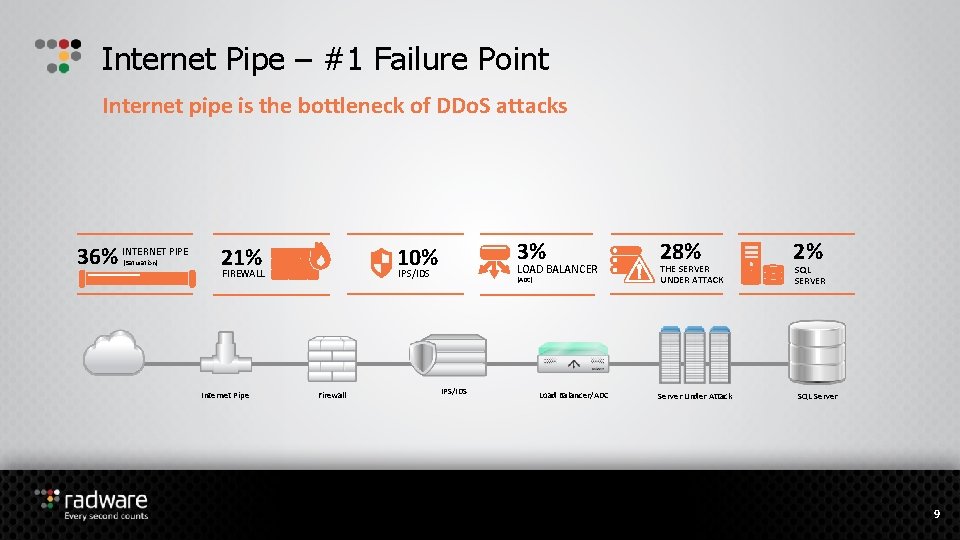
Internet Pipe – #1 Failure Point Internet pipe is the bottleneck of DDo. S attacks 36% INTERNET PIPE (Saturation) 21% FIREWALL Internet Pipe 3% 10% IPS/IDS Firewall LOAD BALANCER (ADC) IPS/IDS Load Balancer/ADC 28% THE SERVER UNDER ATTACK Server Under Attack 2% SQL SERVER SQL Server 9
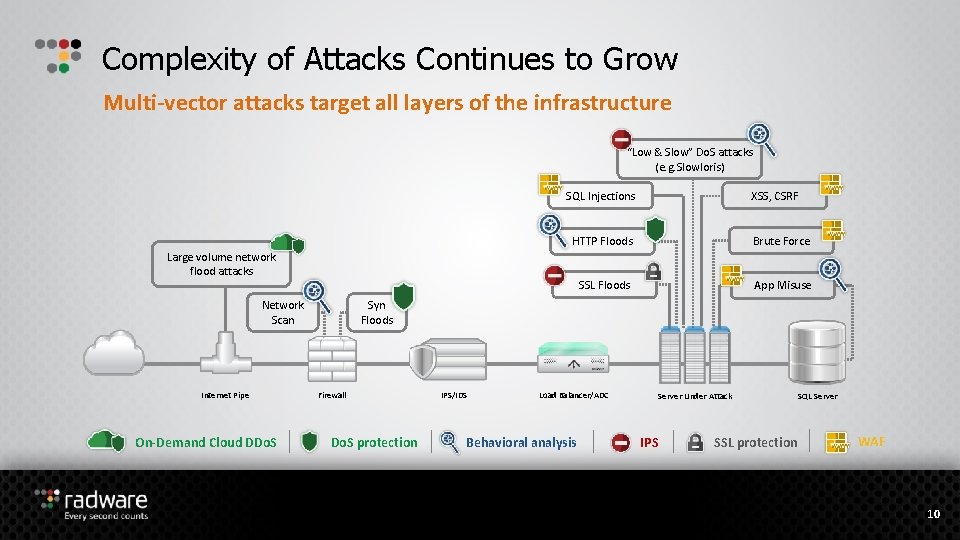
Complexity of Attacks Continues to Grow Multi-vector attacks target all layers of the infrastructure “Low & Slow” Do. S attacks (e. g. Slowloris) SQL Injections HTTP Floods Brute Force SSL Floods App Misuse Large volume network flood attacks Network Scan Internet Pipe On-Demand Cloud DDo. S XSS, CSRF Syn Floods Firewall Do. S protection IPS/IDS Load Balancer/ADC Behavioral analysis Server Under Attack IPS SSL protection SQL Server WAF 10
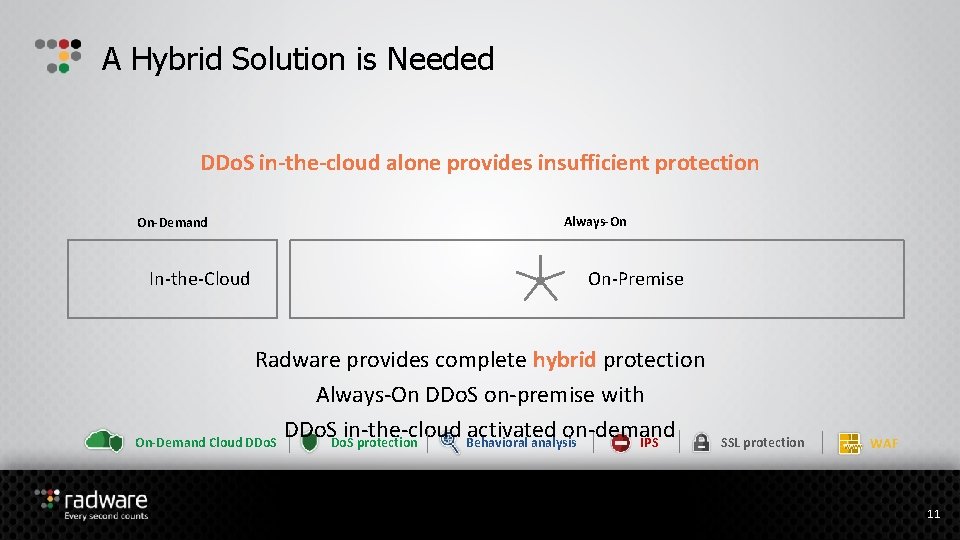
A Hybrid Solution is Needed DDo. S in-the-cloud alone provides insufficient protection On-Demand In-the-Cloud Always-On On-Premise Radware provides complete hybrid protection Always-On DDo. S on-premise with DDo. Sin-the-cloud activated on-demand On-Demand Cloud DDo. S protection Behavioral analysis IPS SSL protection WAF 11
Radware’s Attack Mitigation Solution
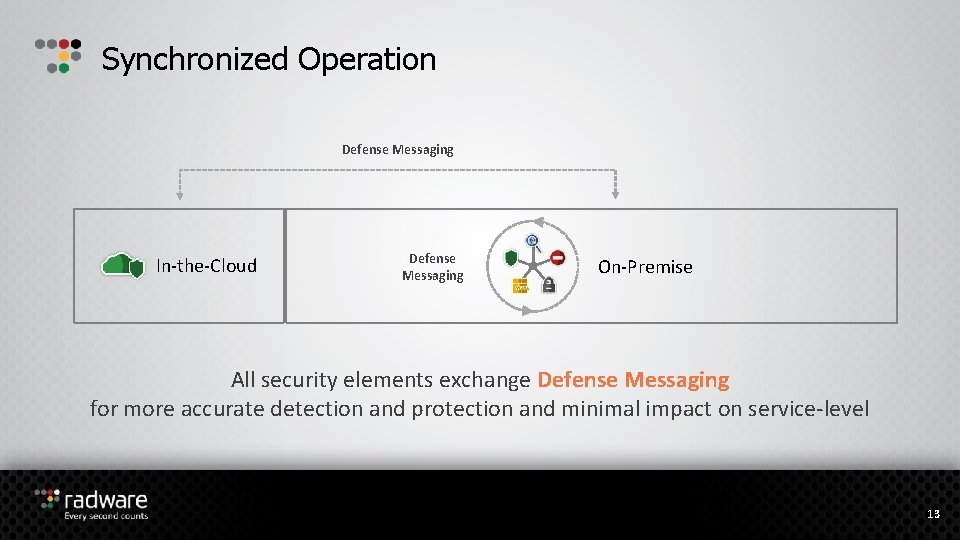
Synchronized Operation Defense Messaging In-the-Cloud Defense Messaging On-Premise All security elements exchange Defense Messaging for more accurate detection and protection and minimal impact on service-level 13
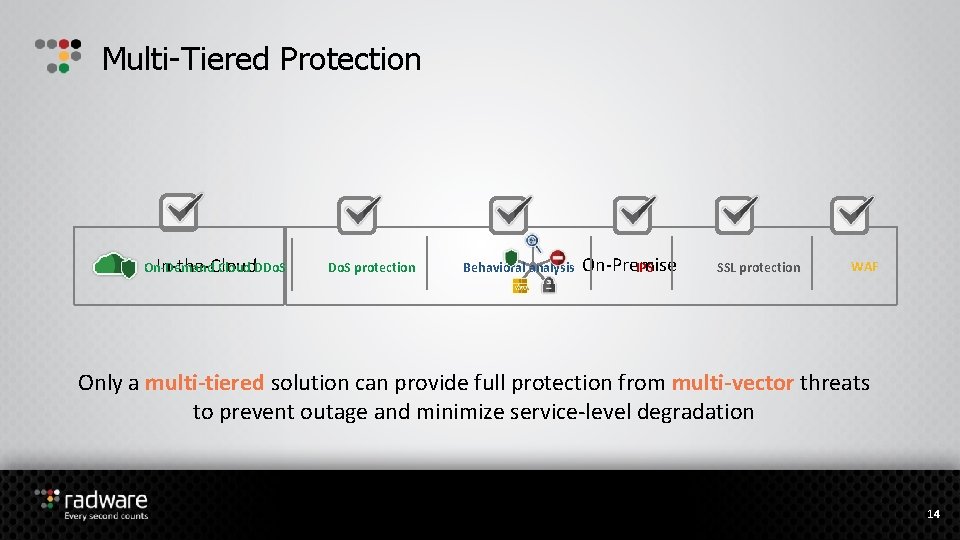
Multi-Tiered Protection On-Demand Cloud DDo. S In-the-Cloud Do. S protection Behavioral analysis On-Premise IPS SSL protection WAF Only a multi-tiered solution can provide full protection from multi-vector threats to prevent outage and minimize service-level degradation 14
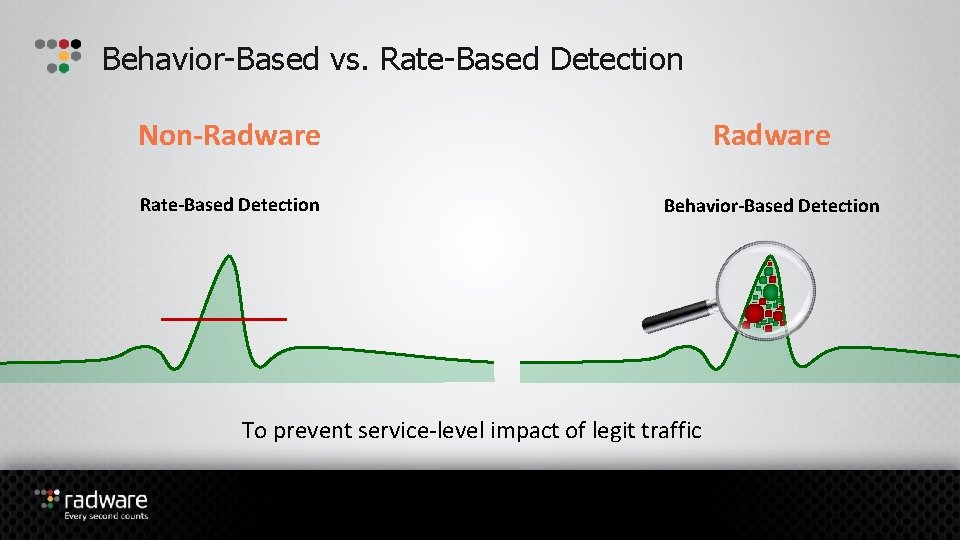
Behavior-Based vs. Rate-Based Detection Non-Radware Rate-Based Detection Behavior-Based Detection To prevent service-level impact of legit traffic
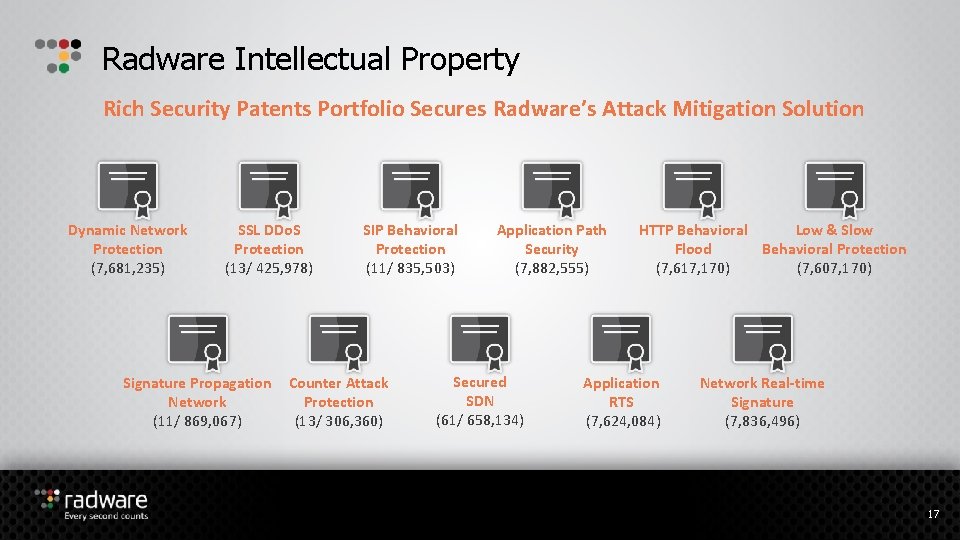
Radware Intellectual Property Rich Security Patents Portfolio Secures Radware’s Attack Mitigation Solution Dynamic Network Protection (7, 681, 235) SSL DDo. S Protection (13/ 425, 978) Signature Propagation Network (11/ 869, 067) SIP Behavioral Protection (11/ 835, 503) Counter Attack Protection (13/ 306, 360) Application Path Security (7, 882, 555) Secured SDN (61/ 658, 134) HTTP Behavioral Low & Slow Flood Behavioral Protection (7, 617, 170) (7, 607, 170) Application RTS (7, 624, 084) Network Real-time Signature (7, 836, 496) 17
Emergency Response Team (ERT) Protecting against top attack campaigns Emergency Response Team (ERT) - 24 x 7 dedicated team of security experts for fast mitigation under attack “We've been fortunate to be able to work with the ERT to help us deploy custom signatures that are very specific, reactive approaches to a customized attack, which has been a fantastic thing. ” Ron Winward, Director of Network Engineering, Server. Central 18
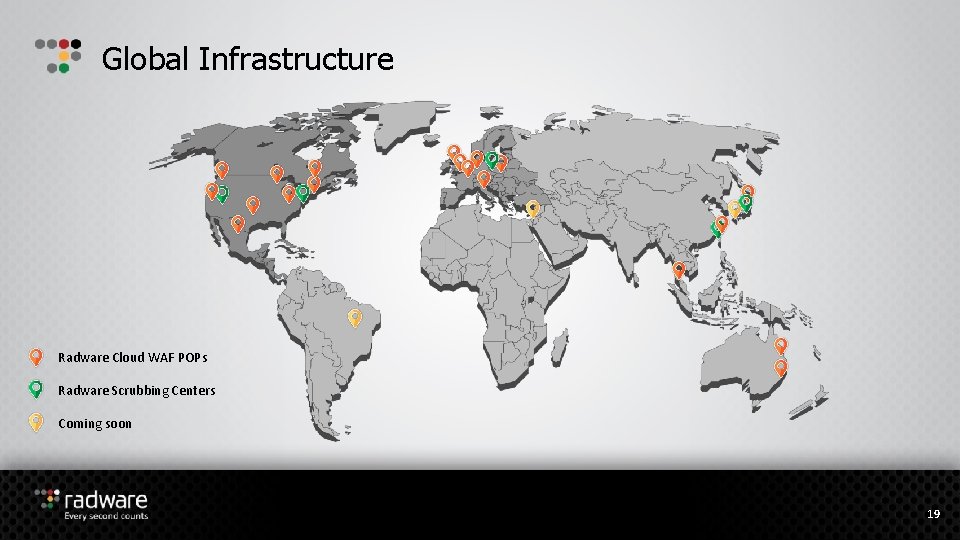
Global Infrastructure Radware Cloud WAF POPs Radware Scrubbing Centers Coming soon 19
Radware’s Attack Mitigation Device (Defense. Pro)
Real-Time Attack Mitigation with Defense. Pro is a real-time attack prevention device that protects your application infrastructure against network and application downtime, application vulnerability exploitation and network anomalies 21
Real-Time Attack Mitigation with Defense. Pro Integrated Anti-Do. S, IPS, SSL protection and Behavioral Analysis protection Patent-protected behavioral analysis to limit false positives Automatic real-time signature creation for zero-day attack prevention Advanced challenge-response mechanism for accurate detection with minimal impact on legitimate traffic Unique messaging between solution elements to maximize protection 22
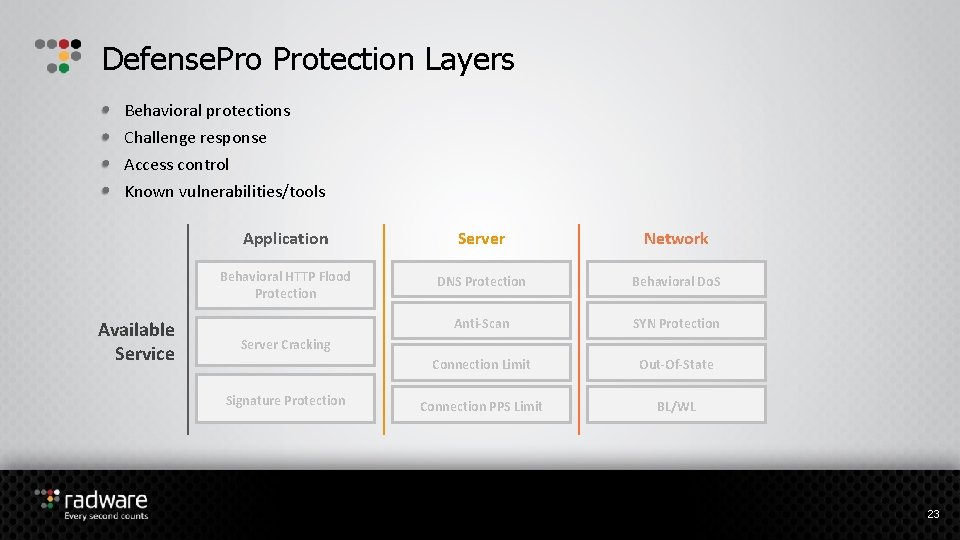
Defense. Protection Layers Behavioral protections Challenge response Access control Known vulnerabilities/tools Available Service Application Server Network Behavioral HTTP Flood Protection DNS Protection Behavioral Do. S Anti-Scan SYN Protection Connection Limit Out-Of-State Connection PPS Limit BL/WL Server Cracking Signature Protection 23
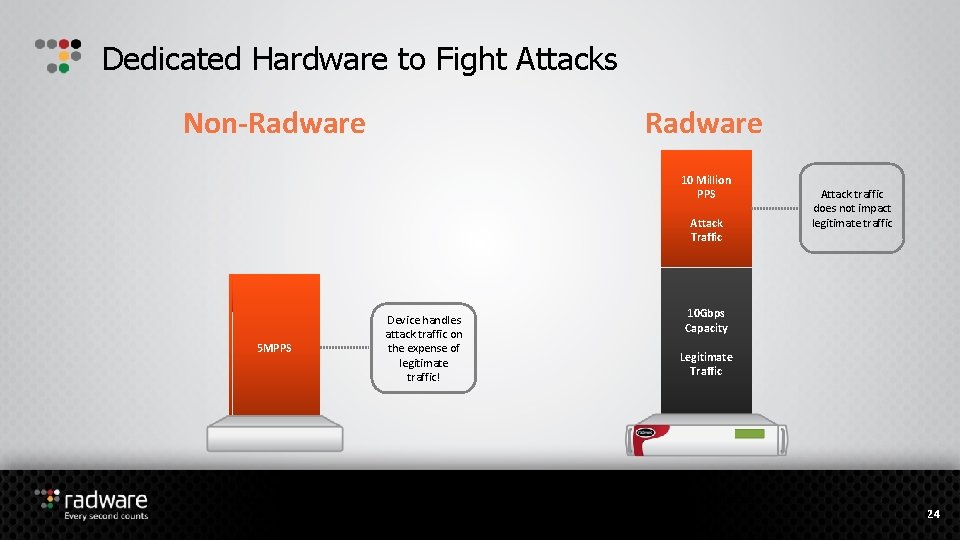
Dedicated Hardware to Fight Attacks Non-Radware 10 Million PPS Attack Traffic Attack traffic does not impact legitimate traffic 1 MPPS 2 MPPS 10 Gbps Capacity 5 MPPS Legitimate Traffic + Attack Defense. Pro Device handles attack traffic on the expense of legitimate traffic! 10 Gbps Capacity Legitimate Traffic Other IPS Solutions 24
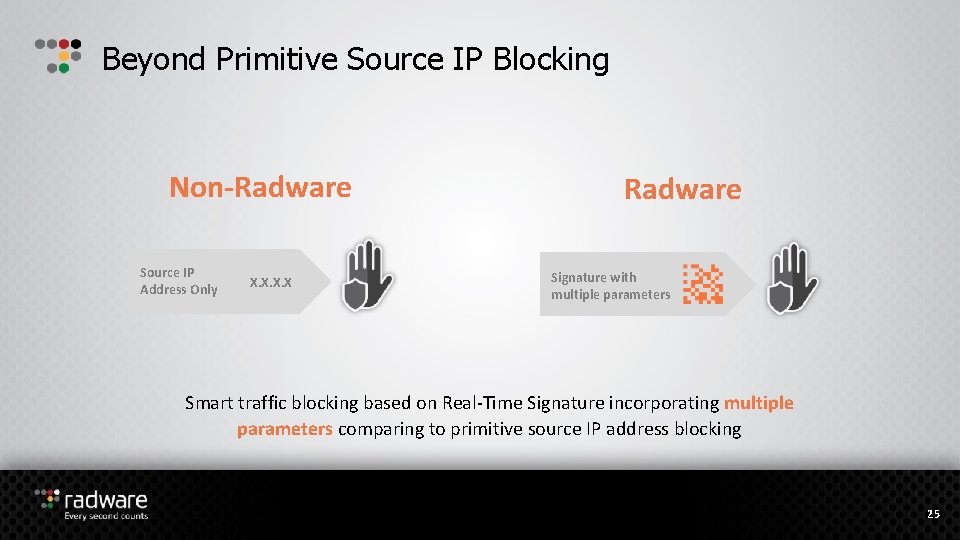
Beyond Primitive Source IP Blocking Non-Radware Source IP Address Only X. X Radware Signature with multiple parameters Smart traffic blocking based on Real-Time Signature incorporating multiple parameters comparing to primitive source IP address blocking 25
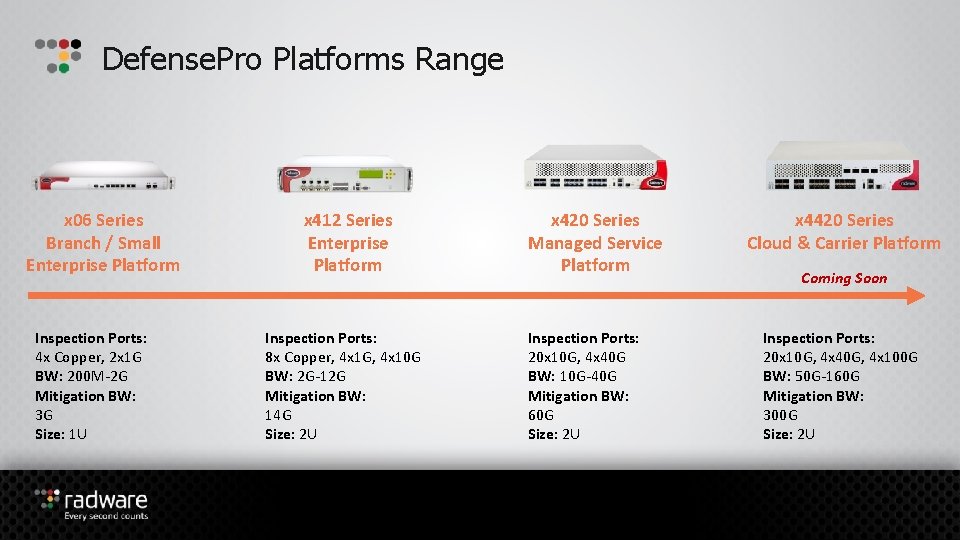
Defense. Pro Platforms Range x 06 Series Branch / Small Enterprise Platform Inspection Ports: 4 x Copper, 2 x 1 G BW: 200 M-2 G Mitigation BW: 3 G Size: 1 U x 412 Series Enterprise Platform Inspection Ports: 8 x Copper, 4 x 1 G, 4 x 10 G BW: 2 G-12 G Mitigation BW: 14 G Size: 2 U x 420 Series Managed Service Platform Inspection Ports: 20 x 10 G, 4 x 40 G BW: 10 G-40 G Mitigation BW: 60 G Size: 2 U x 4420 Series Cloud & Carrier Platform Coming Soon Inspection Ports: 20 x 10 G, 4 x 40 G, 4 x 100 G BW: 50 G-160 G Mitigation BW: 300 G Size: 2 U
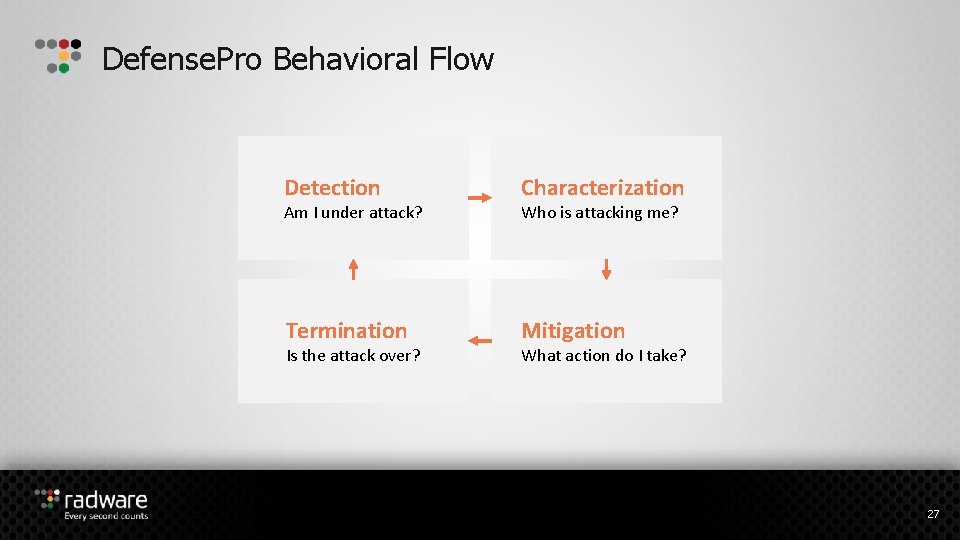
Defense. Pro Behavioral Flow Detection Characterization Termination Mitigation Am I under attack? Is the attack over? Who is attacking me? What action do I take? 27
Defense. Pro Behavioral Flow Detection: Am I under attack? 28
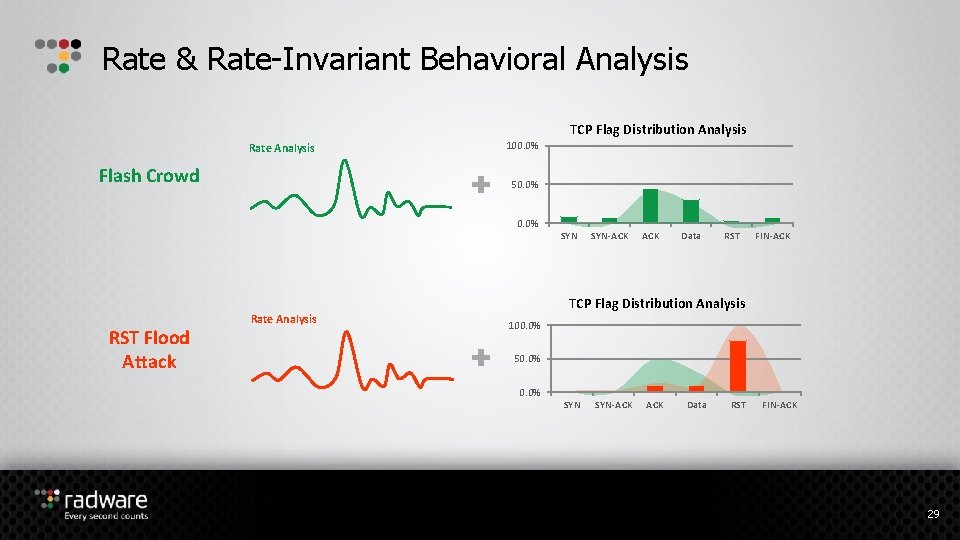
Rate & Rate-Invariant Behavioral Analysis TCP Flag Distribution Analysis Rate Analysis Flash Crowd 100. 0% 50. 0% SYN SYN-ACK Data RST FIN-ACK TCP Flag Distribution Analysis RST Flood Attack Rate Analysis 100. 0% 50. 0% SYN SYN-ACK Data RST FIN-ACK 29
Defense. Pro Behavioral Flow Characterization: Who is attacking me? 30
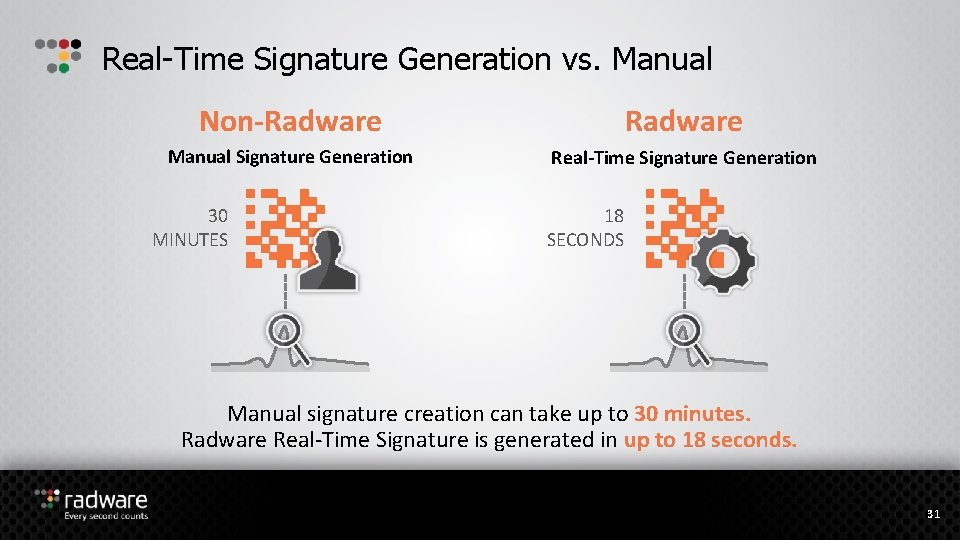
Real-Time Signature Generation vs. Manual Non-Radware Manual Signature Generation Real-Time Signature Generation 30 MINUTES 18 SECONDS Manual signature creation can take up to 30 minutes. Radware Real-Time Signature is generated in up to 18 seconds. 31
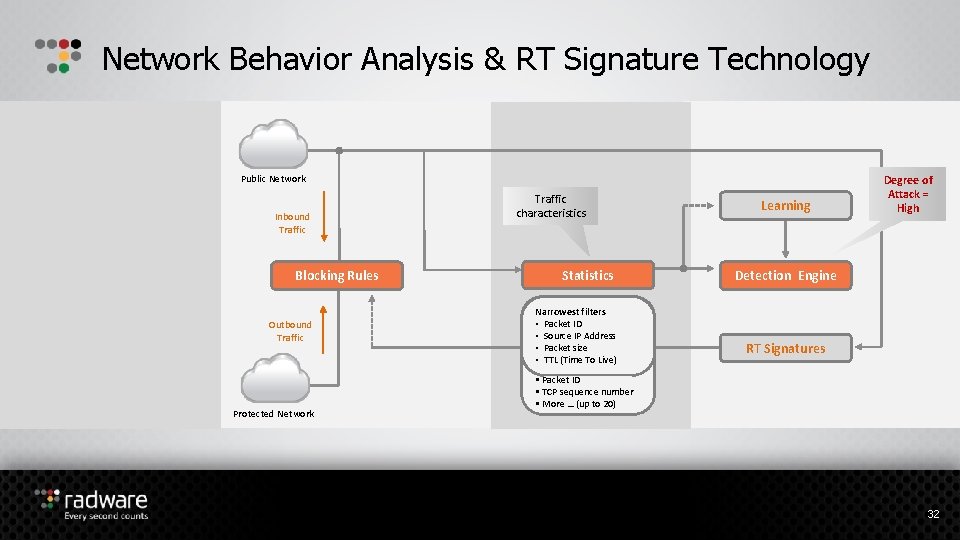
Network Behavior Analysis & RT Signature Technology Public Network Inbound Traffic Blocking Rules Outbound Traffic Protected Network Traffic characteristics Statistics Signature Narrowestparameters filters • • Source/Destination IP Packet ID • • Source/Destination Source IP Address Port • • Packet size • • TTL (Time To To Live) • DNS Query • Packet ID • TCP sequence number • More … (up to 20) Learning Degree of Attack = High Detection Engine RT Signatures 32
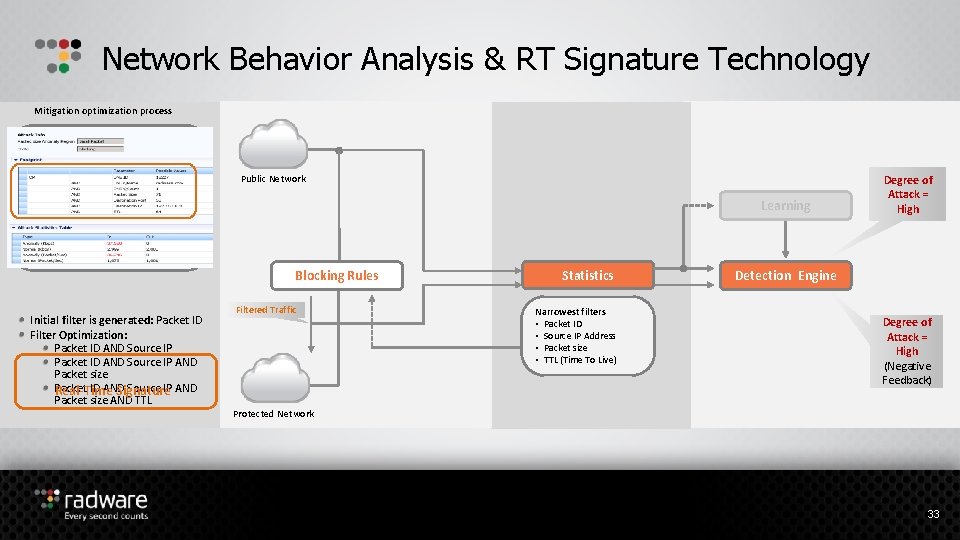
Network Behavior Analysis & RT Signature Technology Mitigation optimization process Closed feedback Public Network Initial Filter Learning Start mitigation 0 Degree of Attack = Low High Final Filter Up to 10 sec 10+X sec Blocking Rules Initial filter is generated: Packet ID Filter Optimization: Packet ID AND Source IP AND Packet size Packet ID AND Source IP AND Real-Time Signature Packet size AND TTL Filtered Traffic Statistics Narrowest filters • Packet ID • Source IP Address • Packet size • TTL (Time To Live) Detection Engine Degree of Attack = High Low (Negative (Positive Feedback) Protected Network 33
Defense. Pro Behavioral Flow Mitigation: What Action do I take? 34
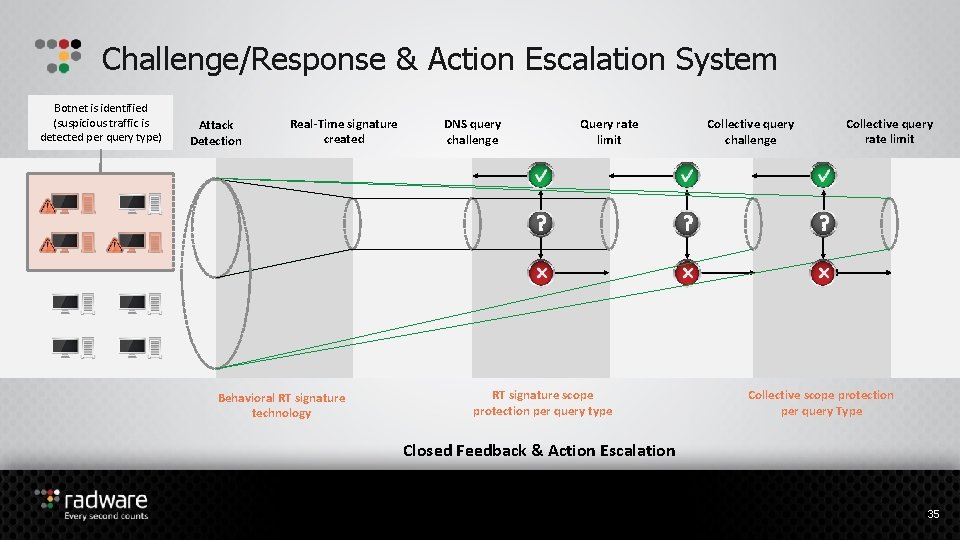
Challenge/Response & Action Escalation System Botnet is identified (suspicious traffic is detected per query type) Attack Detection Real-Time signature created Behavioral RT signature technology DNS query challenge Query rate limit RT signature scope protection per query type Collective query challenge Collective query rate limit Collective scope protection per query Type Closed Feedback & Action Escalation 35
Radware’s Cloud Scrubbing Service (Defense. Pipe)
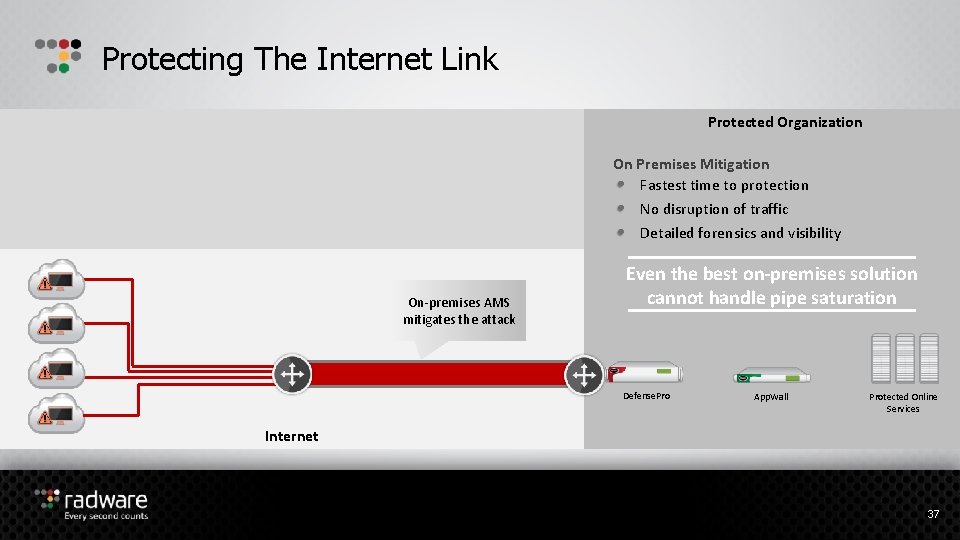
Protecting The Internet Link Protected Organization On Premises Mitigation Fastest time to protection No disruption of traffic Detailed forensics and visibility On-premises AMS mitigates the attack Even the best on-premises solution cannot handle pipe saturation Defense. Pro App. Wall Protected Online Services Internet 37
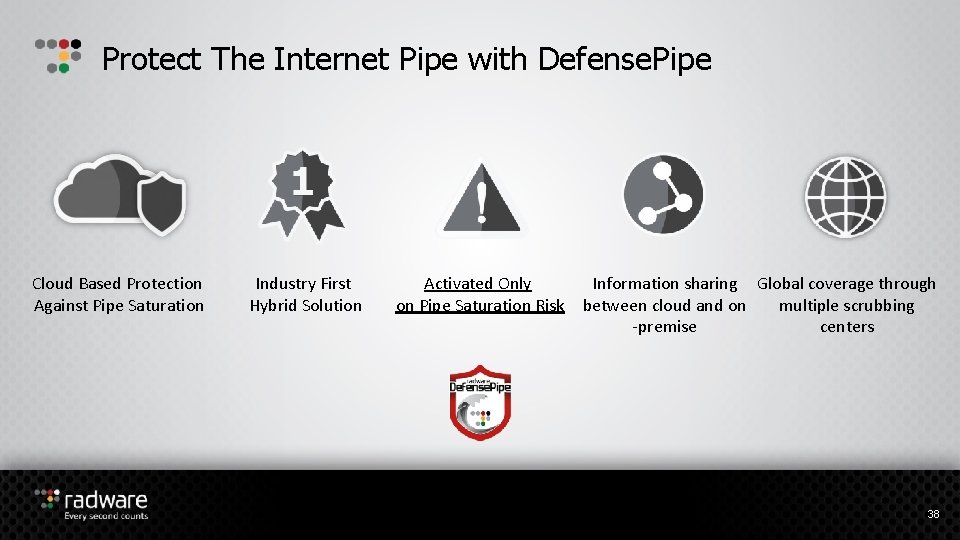
Protect The Internet Pipe with Defense. Pipe Cloud Based Protection Against Pipe Saturation Industry First Hybrid Solution Activated Only on Pipe Saturation Risk Information sharing Global coverage through between cloud and on multiple scrubbing -premise centers 38
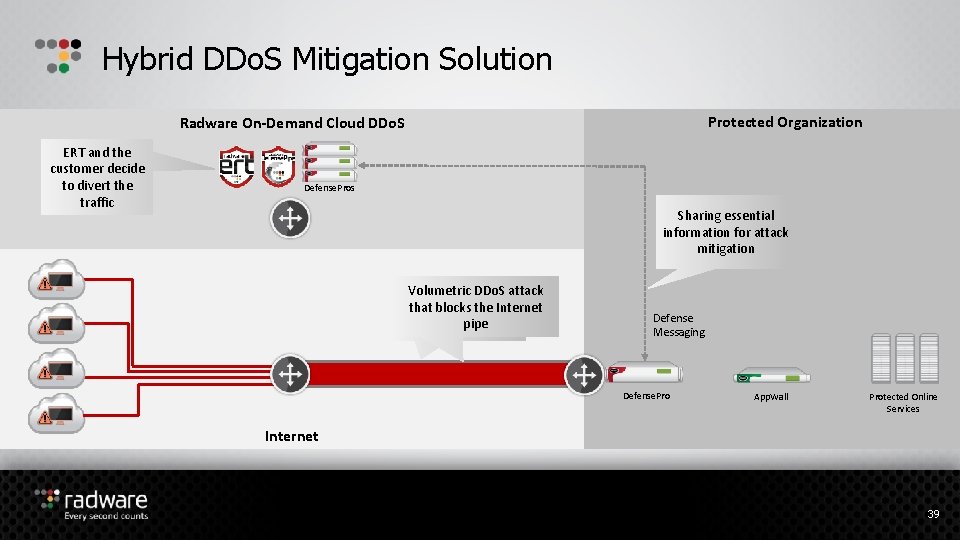
Hybrid DDo. S Mitigation Solution Protected Organization Radware On-Demand Cloud DDo. S ERT and the customer decide to divert the traffic Defense. Pros Sharing essential information for attack mitigation Volumetric DDo. S attack On-premises AMS that blocks the Internet mitigates the attack pipe Defense Messaging Defense. Pro App. Wall Protected Online Services Internet 39
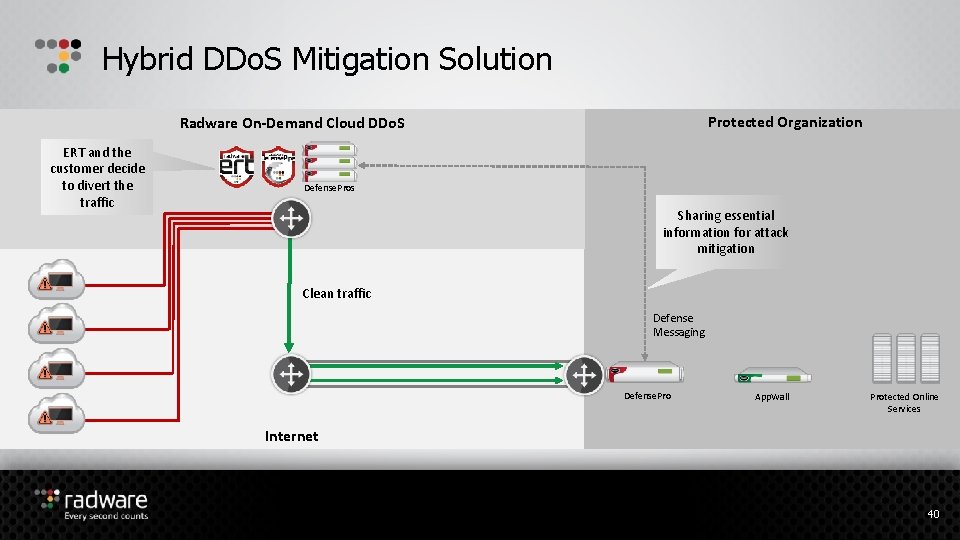
Hybrid DDo. S Mitigation Solution Protected Organization Radware On-Demand Cloud DDo. S ERT and the customer decide to divert the traffic Defense. Pros Sharing essential information for attack mitigation Clean traffic Defense Messaging Defense. Pro App. Wall Protected Online Services Internet 40
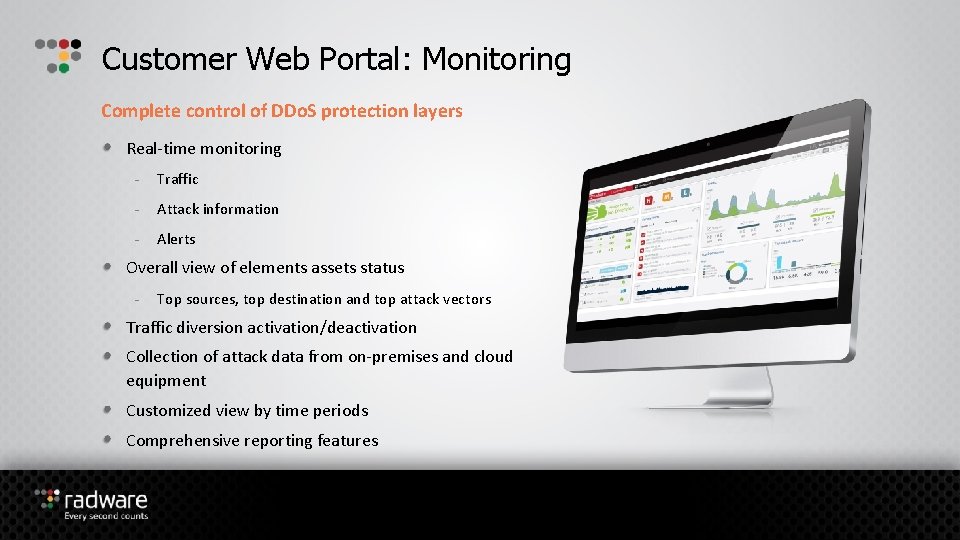
Customer Web Portal: Monitoring Complete control of DDo. S protection layers Real-time monitoring - Traffic - Attack information - Alerts Overall view of elements assets status - Top sources, top destination and top attack vectors Traffic diversion activation/deactivation Collection of attack data from on-premises and cloud equipment Customized view by time periods Comprehensive reporting features
Radware’s Security Command Control (Defense. Flow)
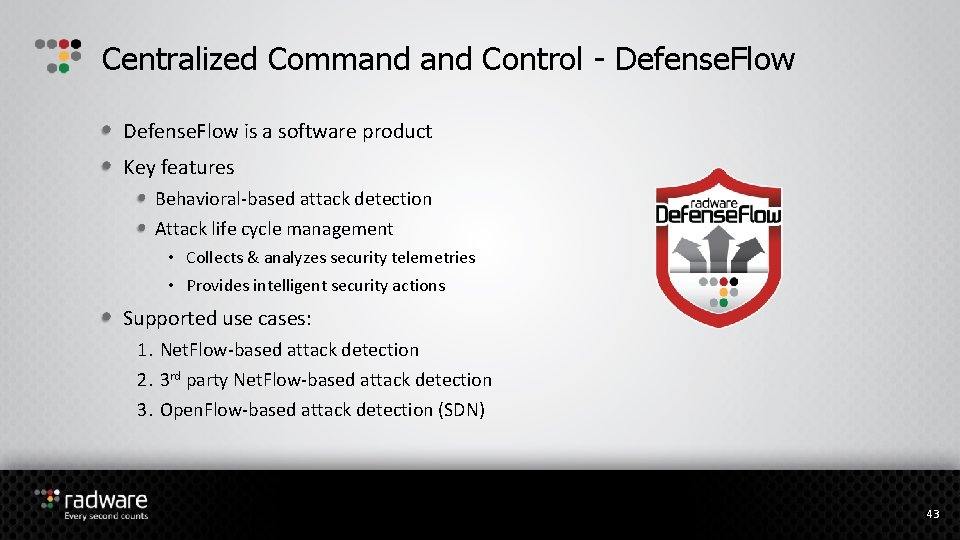
Centralized Command Control - Defense. Flow is a software product Key features Behavioral-based attack detection Attack life cycle management • Collects & analyzes security telemetries • Provides intelligent security actions Supported use cases: 1. Net. Flow-based attack detection 2. 3 rd party Net. Flow-based attack detection 3. Open. Flow-based attack detection (SDN) 43
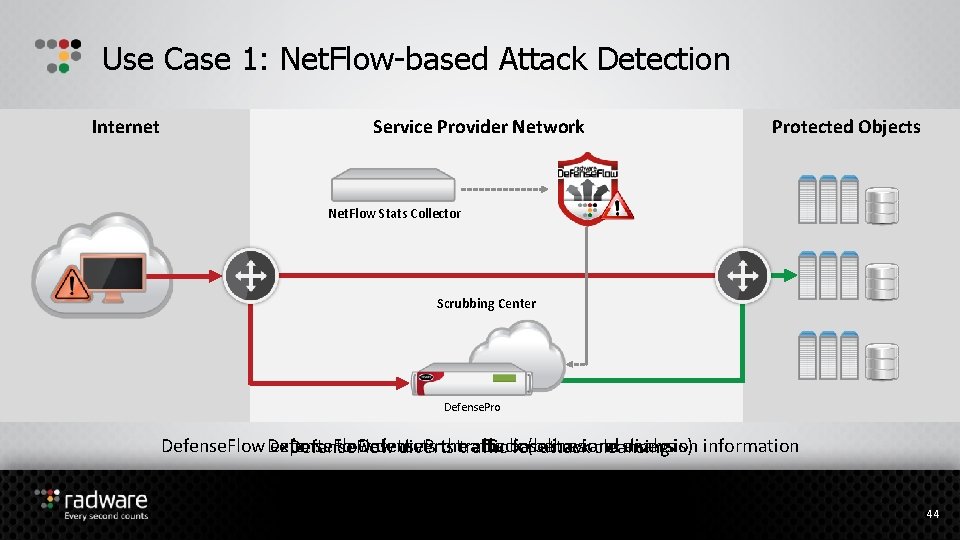
Use Case 1: Net. Flow-based Attack Detection Internet Service Provider Network Protected Objects Net. Flow Stats Collector Scrubbing Center Defense. Pro detects the attack analysis) Defense. Flow exports to Defense. Pro traffic baselines diversion information Defense. Flow diverts traffic for(behavioral attackand cleansing 44
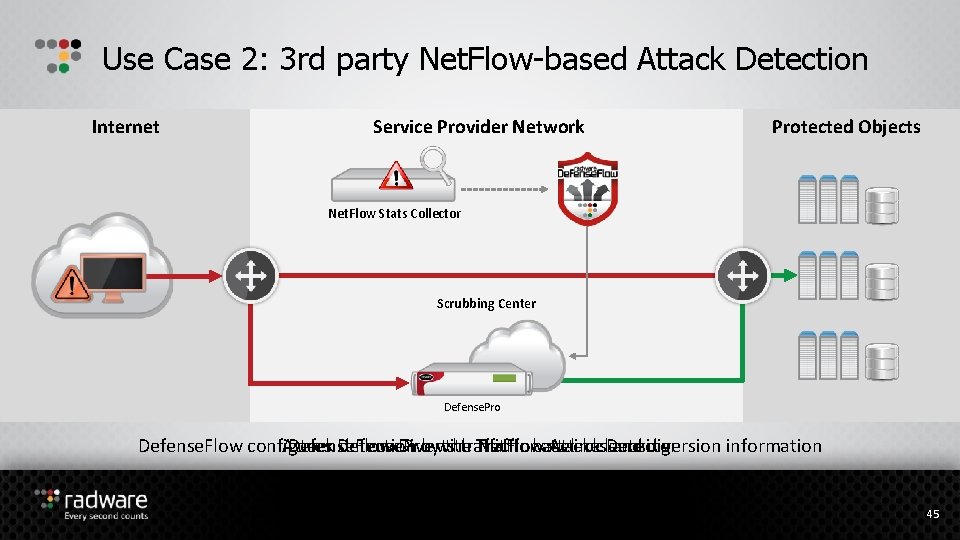
Use Case 2: 3 rd party Net. Flow-based Attack Detection Internet Service Provider Network Protected Objects Net. Flow Stats Collector Scrubbing Center Defense. Pro Defense. Flow configures Attack Defense. Pro detection bywith the Traffic Net. Flow Attackcleansing Detector and diversion information Defense. Flow Diverts traffic forbaselines attack 45
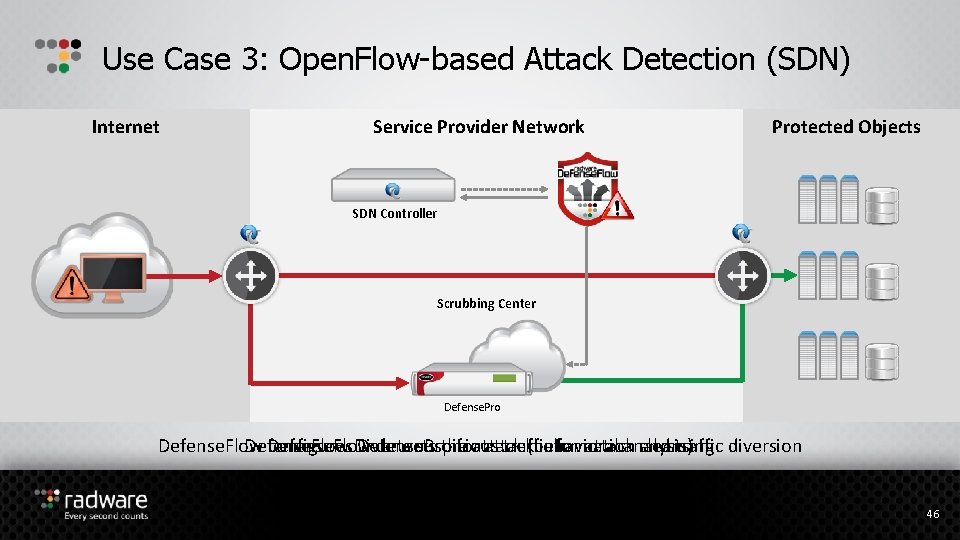
Use Case 3: Open. Flow-based Attack Detection (SDN) Internet Service Provider Network Protected Objects SDN Controller Scrubbing Center Defense. Pro Defense. Flow suspicious traffic for attack cleansing Defense. Flow configures Diverts Defense. Pro detects the forattack (behavioral information analysis) and traffic diversion 46
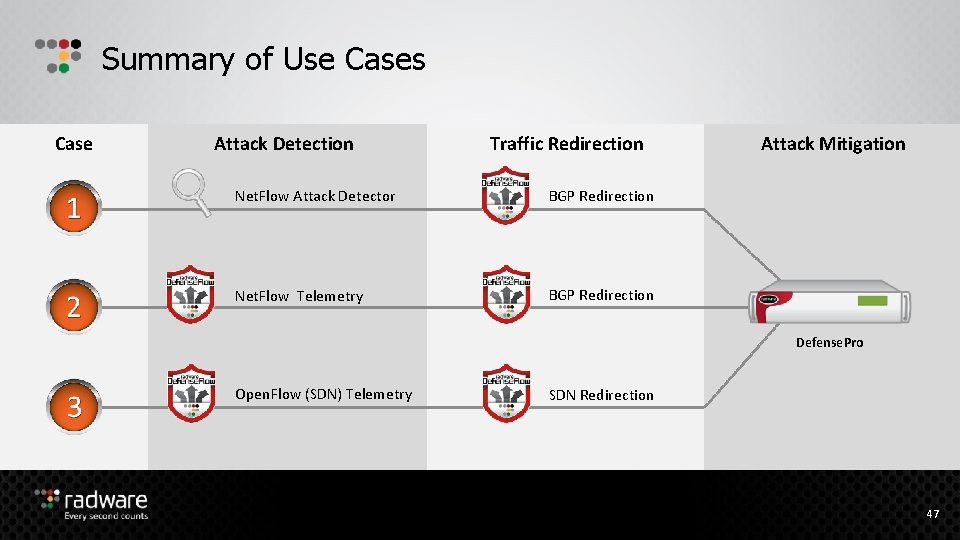
Summary of Use Cases Case Attack Detection Traffic Redirection Net. Flow Attack Detector BGP Redirection Net. Flow Telemetry BGP Redirection Attack Mitigation Defense. Pro Open. Flow (SDN) Telemetry SDN Redirection 47

Service Provider Solution
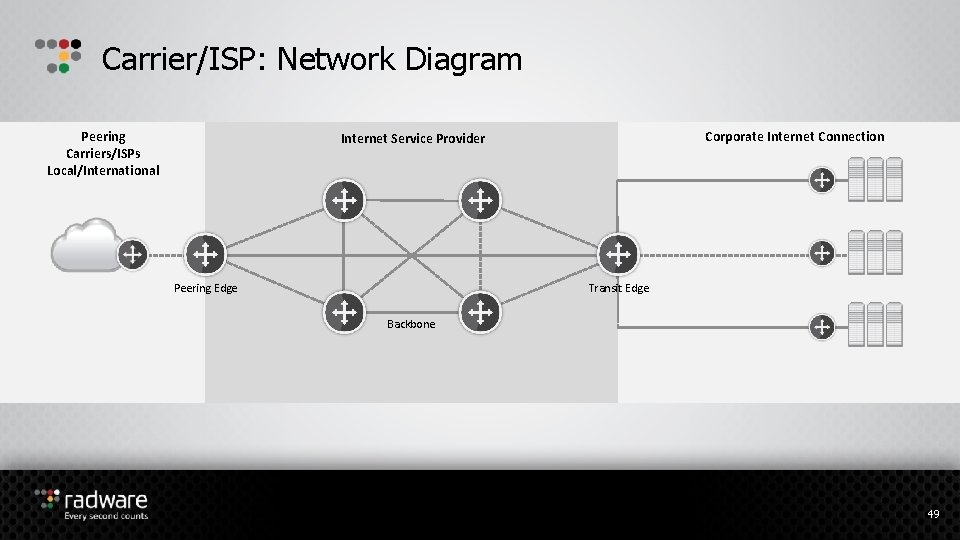
Carrier/ISP: Network Diagram Peering Carriers/ISPs Local/International Corporate Internet Connection Internet Service Provider Peering Edge Transit Edge Backbone 49
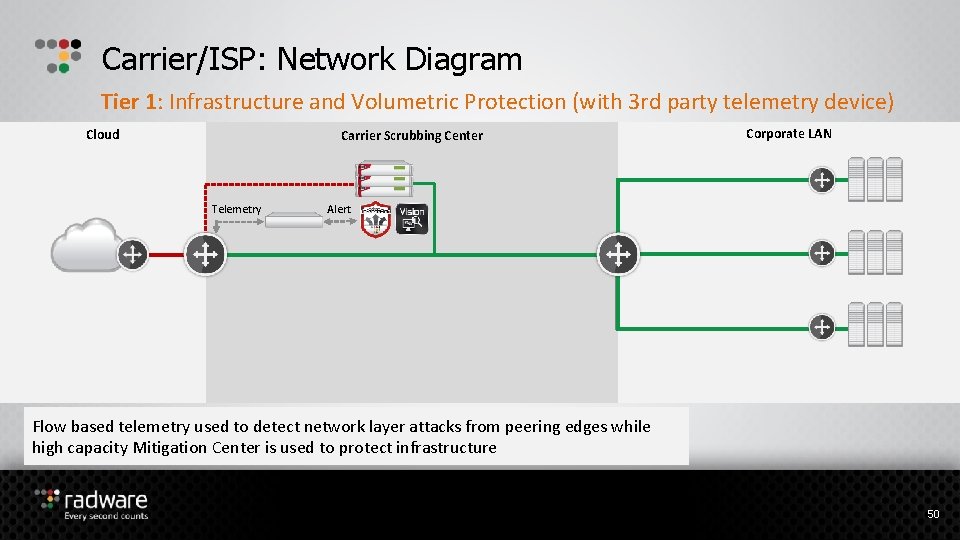
Carrier/ISP: Network Diagram Tier 1: Infrastructure and Volumetric Protection (with 3 rd party telemetry device) Cloud Carrier Scrubbing Center Telemetry Corporate LAN Alert Flow based telemetry used to detect network layer attacks from peering edges while high capacity Mitigation Center is used to protect infrastructure 50
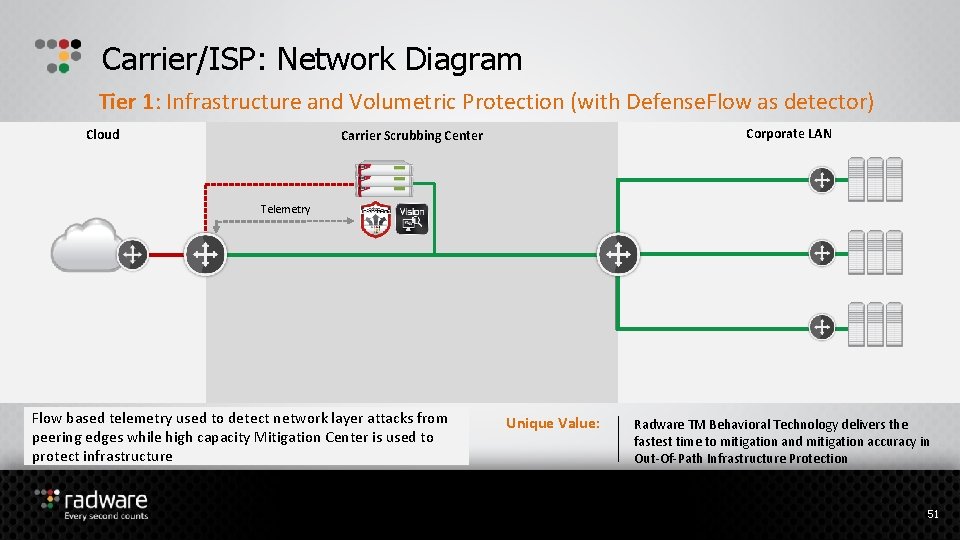
Carrier/ISP: Network Diagram Tier 1: Infrastructure and Volumetric Protection (with Defense. Flow as detector) Cloud Corporate LAN Carrier Scrubbing Center Telemetry Flow based telemetry used to detect network layer attacks from peering edges while high capacity Mitigation Center is used to protect infrastructure Unique Value: Radware TM Behavioral Technology delivers the fastest time to mitigation and mitigation accuracy in Out-Of-Path Infrastructure Protection 51
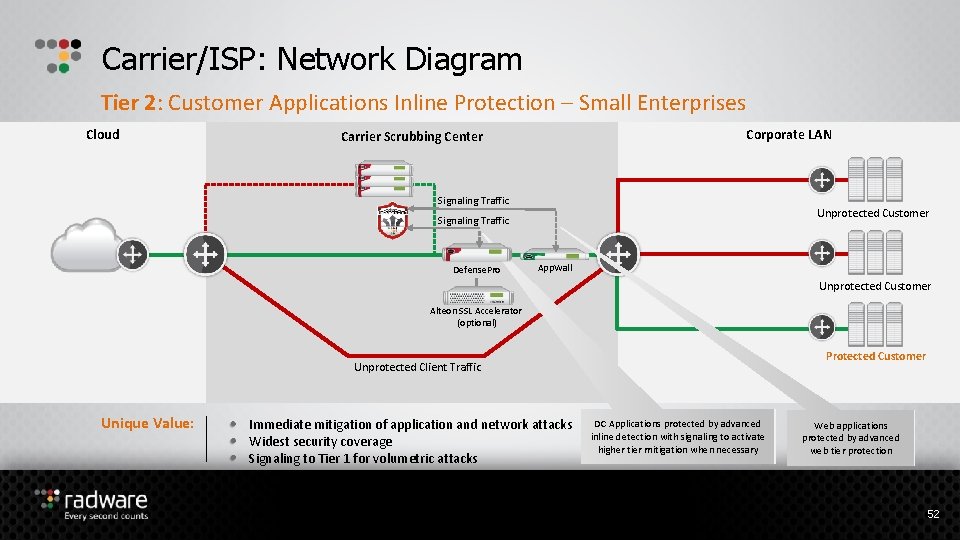
Carrier/ISP: Network Diagram Tier 2: Customer Applications Inline Protection – Small Enterprises Cloud Corporate LAN Carrier Scrubbing Center Signaling Traffic Unprotected Customer Signaling Traffic Defense. Pro App. Wall Unprotected Customer Alteon SSL Accelerator (optional) Protected Customer Unprotected Client Traffic Unique Value: Immediate mitigation of application and network attacks Widest security coverage Signaling to Tier 1 for volumetric attacks DC Applications protected by advanced inline detection with signaling to activate higher tier mitigation when necessary Web applications protected by advanced web tier protection 52
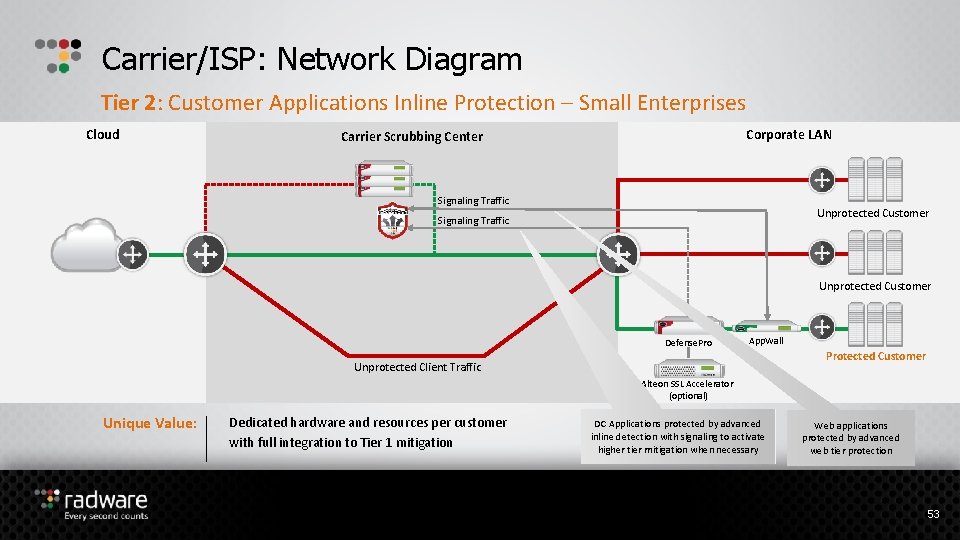
Carrier/ISP: Network Diagram Tier 2: Customer Applications Inline Protection – Small Enterprises Cloud Corporate LAN Carrier Scrubbing Center Signaling Traffic Unprotected Customer Defense. Pro App. Wall Protected Customer Unprotected Client Traffic Alteon SSL Accelerator (optional) Unique Value: Dedicated hardware and resources per customer with full integration to Tier 1 mitigation DC Applications protected by advanced inline detection with signaling to activate higher tier mitigation when necessary Web applications protected by advanced web tier protection 53
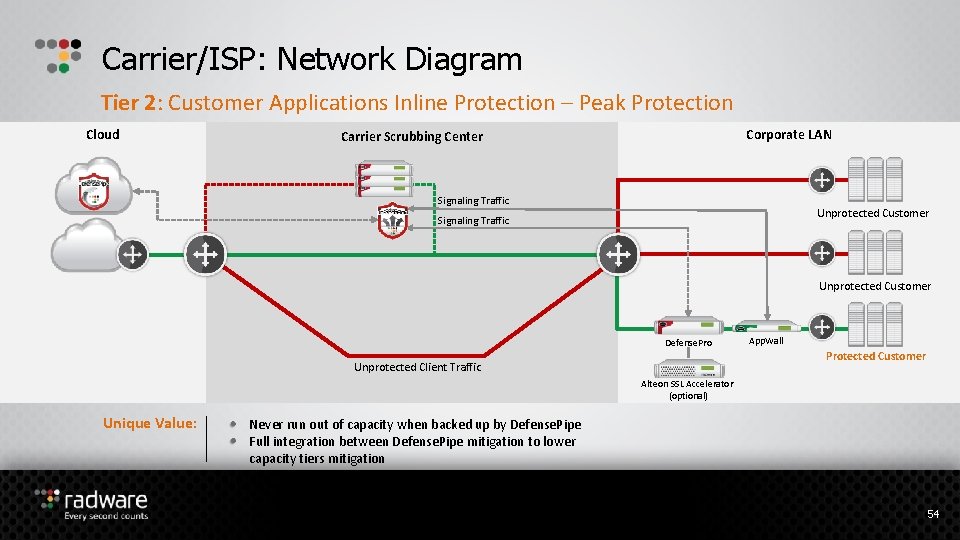
Carrier/ISP: Network Diagram Tier 2: Customer Applications Inline Protection – Peak Protection Cloud Corporate LAN Carrier Scrubbing Center Signaling Traffic Unprotected Customer Defense. Pro App. Wall Protected Customer Unprotected Client Traffic Alteon SSL Accelerator (optional) Unique Value: Never run out of capacity when backed up by Defense. Pipe Full integration between Defense. Pipe mitigation to lower capacity tiers mitigation 54

Emergency Response Team
Emergency Response Team (ERT) Protecting against top attack campaigns Emergency Response Team (ERT) - 24 x 7 dedicated team of security experts for fast mitigation under attack “We've been fortunate to be able to work with the ERT to help us deploy custom signatures that are very specific, reactive approaches to a customized attack, which has been a fantastic thing. ” Ron Winward, Director of Network Engineering, Server. Central 56
ERT Premium Service 24/7 DDo. S Protection On-Premise Device Management Online Portal & Reporting Periodic Security Consulting Fully outsource the monitoring and management to Radware’s security experts 57
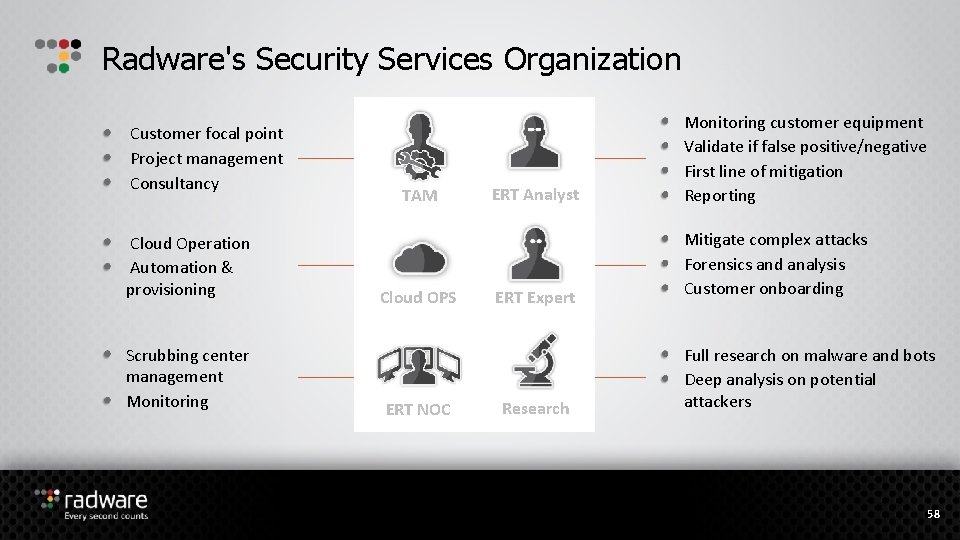
Radware's Security Services Organization Customer focal point Project management Consultancy Cloud Operation Automation & provisioning Scrubbing center management Monitoring TAM Cloud OPS ERT NOC ERT Analyst Monitoring customer equipment Validate if false positive/negative First line of mitigation Reporting ERT Expert Mitigate complex attacks Forensics and analysis Customer onboarding Research Full research on malware and bots Deep analysis on potential attackers 58
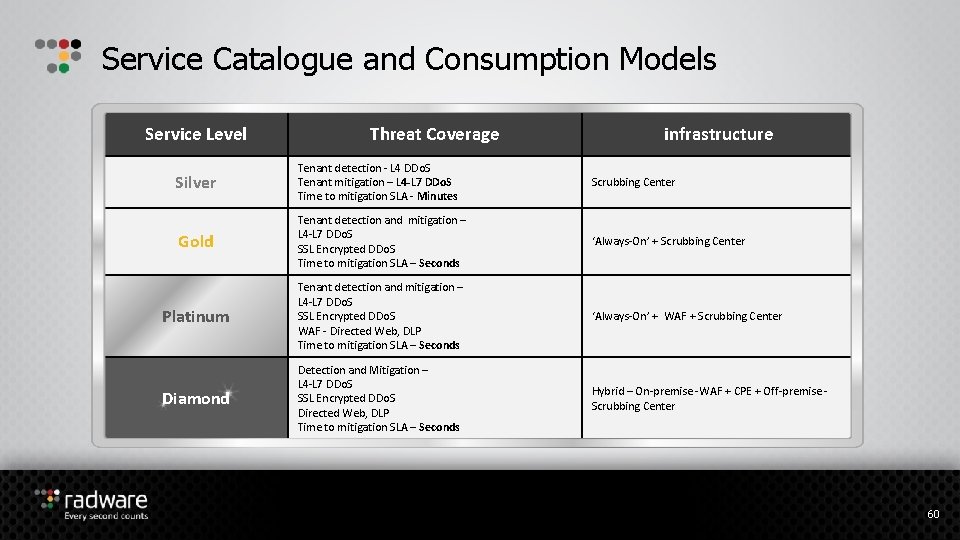
Service Catalogue and Consumption Models Service Level Threat Coverage infrastructure Silver Tenant detection - L 4 DDo. S Tenant mitigation – L 4 -L 7 DDo. S Time to mitigation SLA - Minutes Scrubbing Center Gold Tenant detection and mitigation – L 4 -L 7 DDo. S SSL Encrypted DDo. S Time to mitigation SLA – Seconds ‘Always-On’ + Scrubbing Center Platinum Tenant detection and mitigation – L 4 -L 7 DDo. S SSL Encrypted DDo. S WAF - Directed Web, DLP Time to mitigation SLA – Seconds ‘Always-On’ + WAF + Scrubbing Center Diamond Detection and Mitigation – L 4 -L 7 DDo. S SSL Encrypted DDo. S Directed Web, DLP Time to mitigation SLA – Seconds Hybrid – On-premise -WAF + CPE + Off-premise Scrubbing Center 60

Radware’s SSL Mitigation Solution
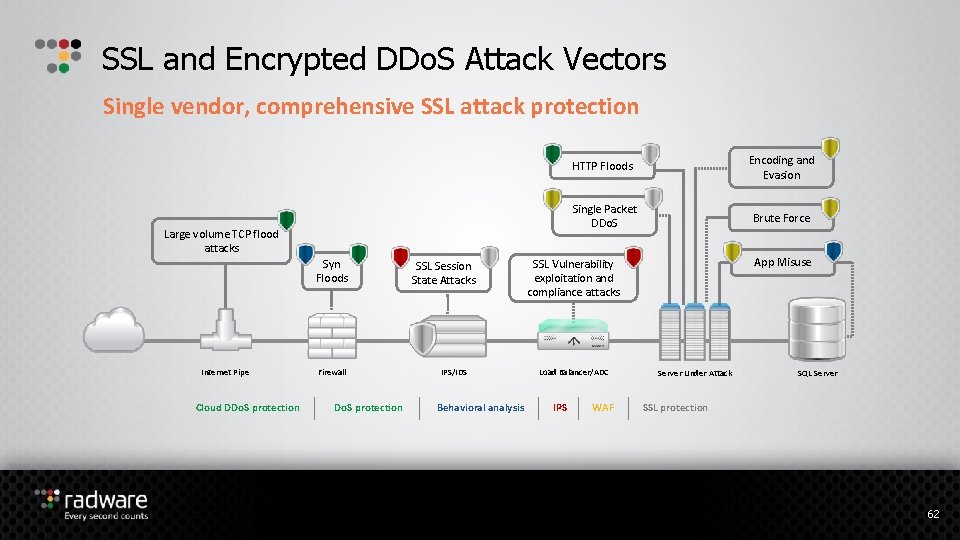
SSL and Encrypted DDo. S Attack Vectors Single vendor, comprehensive SSL attack protection Large volume TCP flood attacks Syn Floods Internet Pipe Cloud DDo. S protection Firewall Do. S protection SSL Session State Attacks IPS/IDS Behavioral analysis HTTP Floods Encoding and Evasion Single Packet DDo. S Brute Force App Misuse SSL Vulnerability exploitation and compliance attacks Load Balancer/ADC IPS WAF Server Under Attack SQL Server SSL protection 62
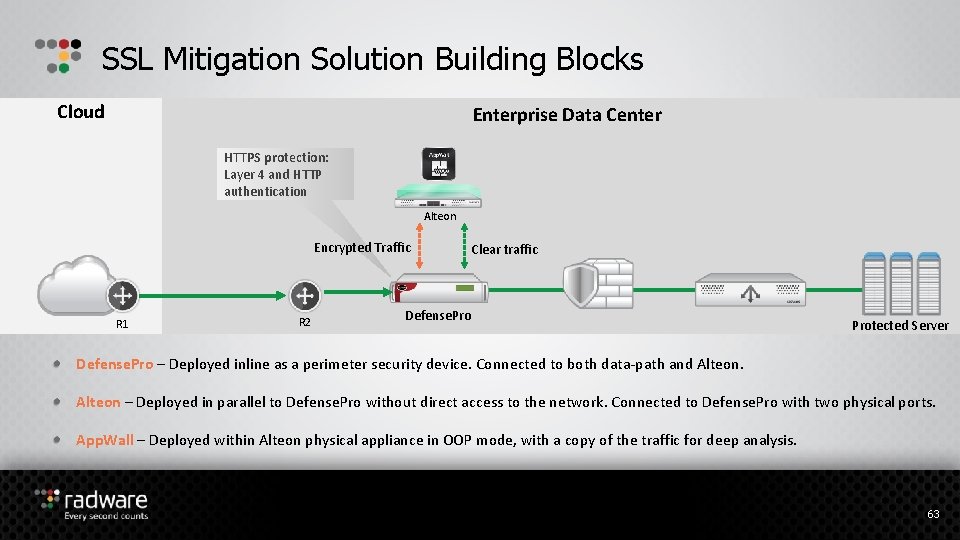
SSL Mitigation Solution Building Blocks Cloud Enterprise Data Center HTTPS protection: Layer 4 and HTTP authentication Alteon Encrypted Traffic R 1 R 2 Clear traffic Defense. Protected Server Defense. Pro – Deployed inline as a perimeter security device. Connected to both data-path and Alteon – Deployed in parallel to Defense. Pro without direct access to the network. Connected to Defense. Pro with two physical ports. App. Wall – Deployed within Alteon physical appliance in OOP mode, with a copy of the traffic for deep analysis. 63
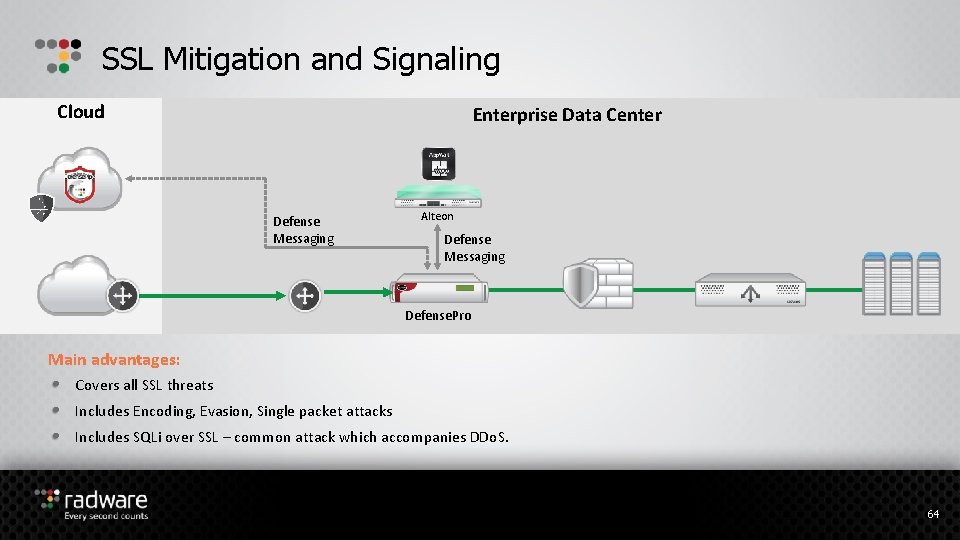
SSL Mitigation and Signaling Cloud Enterprise Data Center Defense Messaging Alteon Defense Messaging Defense. Pro Main advantages: Covers all SSL threats Includes Encoding, Evasion, Single packet attacks Includes SQLi over SSL – common attack which accompanies DDo. S. 64
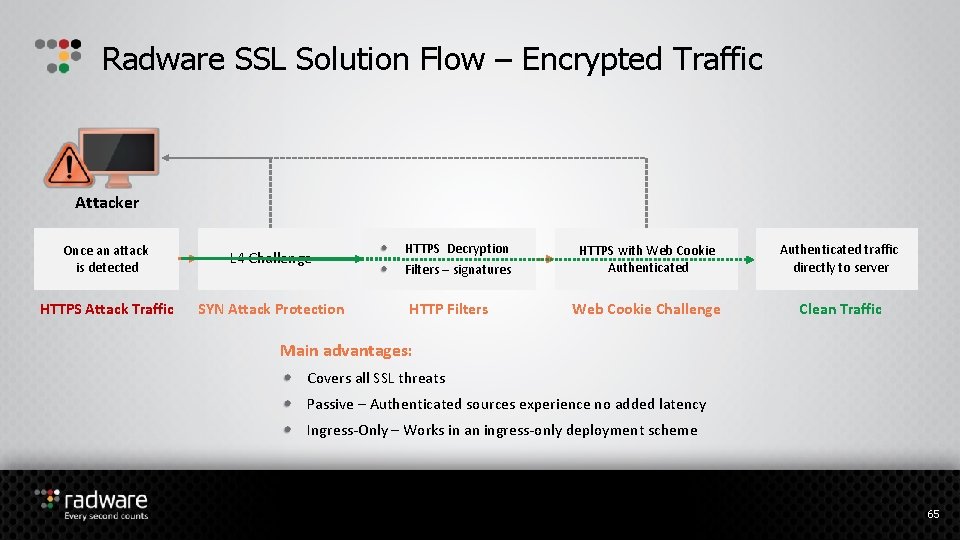
Radware SSL Solution Flow – Encrypted Traffic Attacker Once an attack is detected L 4 Challenge HTTPS Attack Traffic SYN Attack Protection HTTPS Decryption Filters – signatures HTTP Filters HTTPS with Web Cookie Authenticated traffic directly to server Web Cookie Challenge Clean Traffic Main advantages: Covers all SSL threats Passive – Authenticated sources experience no added latency Ingress-Only – Works in an ingress-only deployment scheme 65
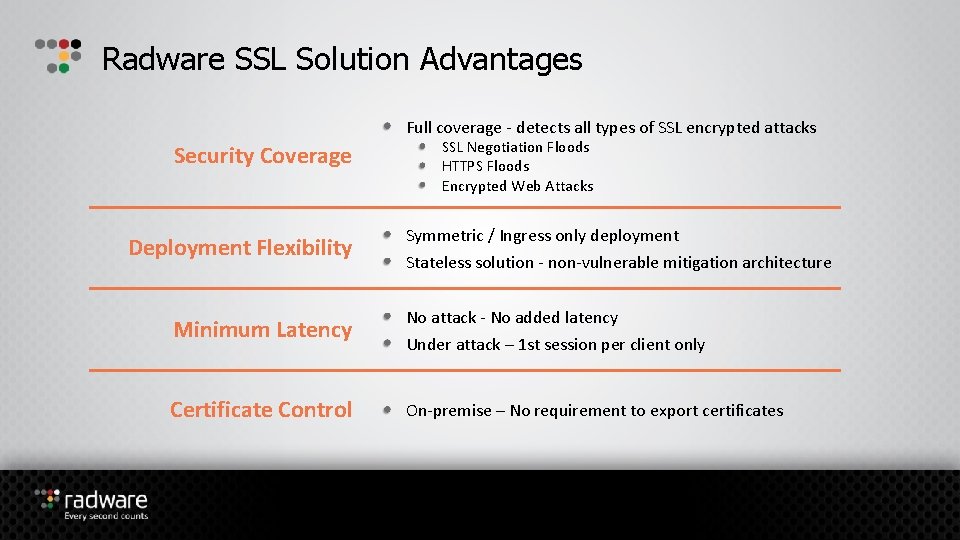
Radware SSL Solution Advantages Full coverage - detects all types of SSL encrypted attacks Security Coverage Deployment Flexibility SSL Negotiation Floods HTTPS Floods Encrypted Web Attacks Symmetric / Ingress only deployment Stateless solution - non-vulnerable mitigation architecture Minimum Latency No attack - No added latency Under attack – 1 st session per client only Certificate Control On-premise – No requirement to export certificates
Radware’s Application and Security Management System (APSolute Vision)
Centralized Management & Reporting with Vision Key modules and capabilities: Multi-device configuration and monitoring Security monitoring – real time and historical Device level monitoring Service level monitoring Advanced productivity capabilities for streamlining day-to-day operations Re. ST API for automation and integration with 3 rd party tools Available in multiple form factors – physical or virtual appliance 68
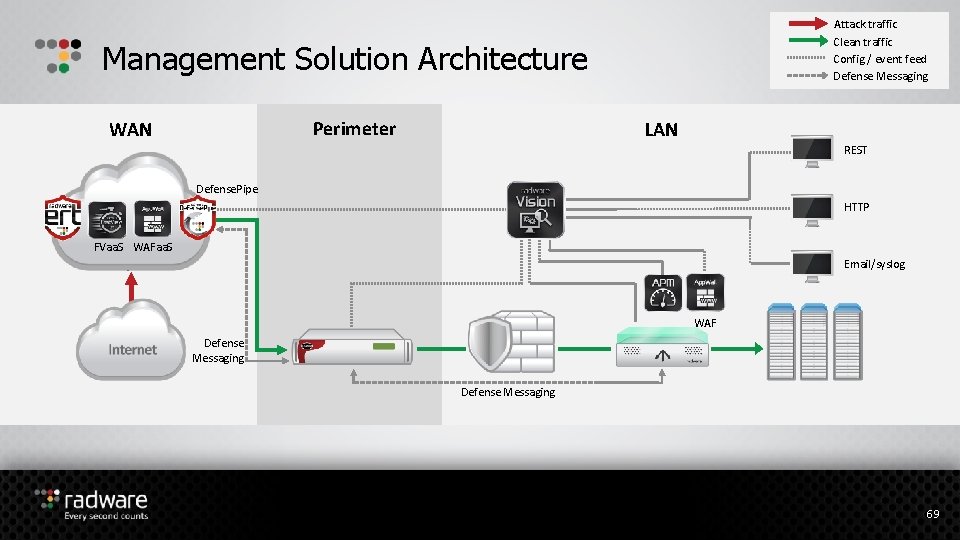
Attack traffic Clean traffic Config / event feed Defense Messaging Management Solution Architecture Perimeter WAN LAN REST Defense. Pipe HTTP FVaa. S WAFaa. S ז Email/syslog WAF Defense Messaging 69
Built in Security Information and Events Management (SIEM) Real Time Monitoring Historical Reporting Engine Customizable Dashboards Event Correlation Engine Advanced Forensics Reports Compliance Reports Ticket Work Flow Management 3 rd Party Event Notifications Role/User Based Access Control Works with all Radware’s Security Modules 70
Multi Tenancy Support Separate processing capabilities per tenant Role based access control for management permissions per policy Each tenant can view and monitor only the resources that are relevant for them Personalized, per tenant, historical reporting, dashboards and event management 71
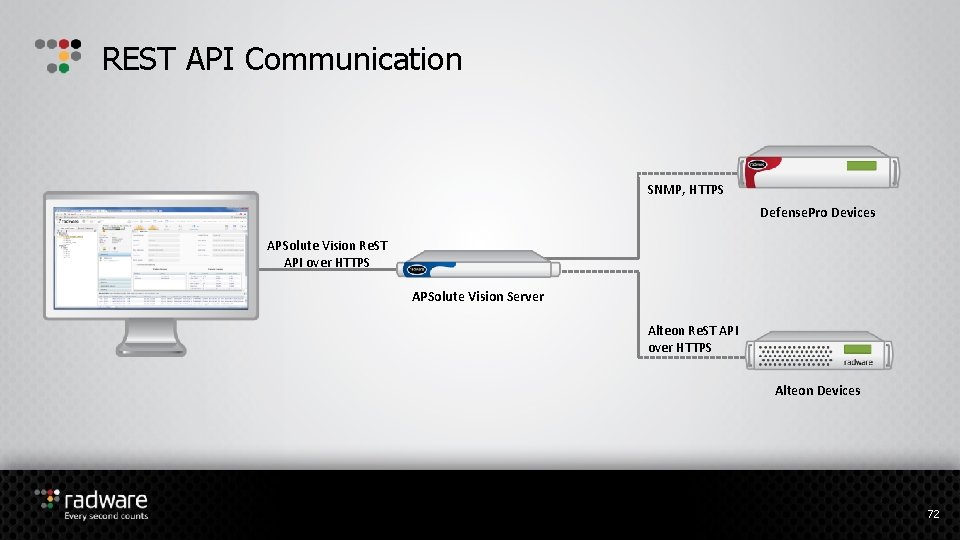
REST API Communication SNMP, HTTPS Defense. Pro Devices APSolute Vision Re. ST API over HTTPS APSolute Vision Server Alteon Re. ST API over HTTPS Alteon Devices 72
Predefined Defense. Pro Configuration Templates A list of predefined Defense. Pro Configuration Templates is bundled with Vision Installation 73
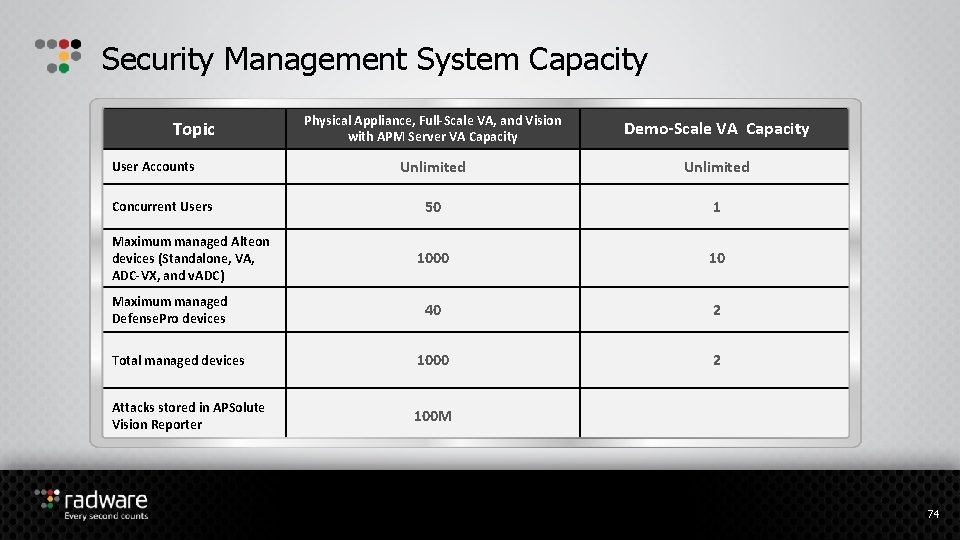
Security Management System Capacity Physical Appliance, Full-Scale VA, and Vision with APM Server VA Capacity Demo-Scale VA Capacity Unlimited 50 1 1000 10 40 2 Total managed devices 1000 2 Attacks stored in APSolute Vision Reporter 100 M Topic User Accounts Concurrent Users Maximum managed Alteon devices (Standalone, VA, ADC-VX, and v. ADC) Maximum managed Defense. Pro devices 74
- Slides: 73