Securing Email The Border Ware Mail Gateway TM
Securing E-mail The Border. Ware Mail Gateway TM
Confusion over E-mail Security “I don’t know why we got hit, …. we have a Firewall” Quote from a well-known Far East Financial Institution in the wake of the I Love You Virus TM
Hacker launched Anna bug 'as a warning' A young Dutchman confessed yesterday to having engineered the Anna Kournikova computer virus that brought chaos to millions of machines around the world this week, saying he believed that the Russian tennis star deserved the extra attention. TM
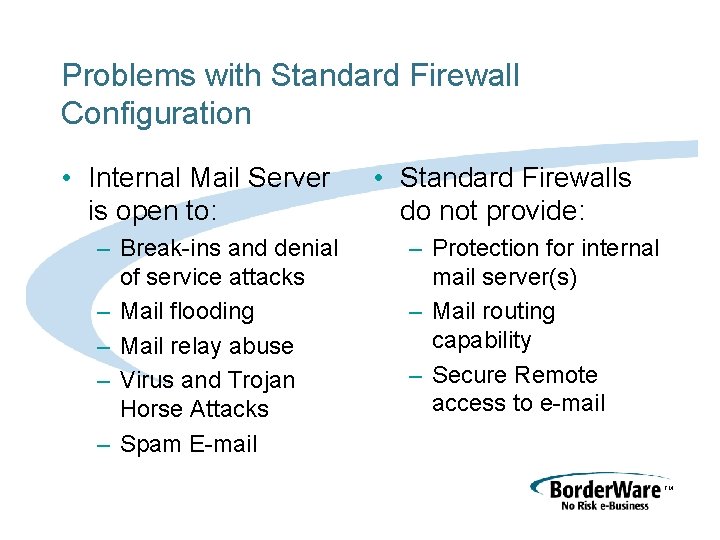
Problems with Standard Firewall Configuration • Internal Mail Server is open to: – Break-ins and denial of service attacks – Mail flooding – Mail relay abuse – Virus and Trojan Horse Attacks – Spam E-mail • Standard Firewalls do not provide: – Protection for internal mail server(s) – Mail routing capability – Secure Remote access to e-mail TM
S. A. F. E. R. Security Bulletin 10123. EXP. 1. 10 TITLE : Buffer overflow in Lotus Domino SMTP Server DATE : January 23, 2001 NATURE : Remote execution of code, Denial-of-Service AFFECTED : Lotus Notes/Domino 5 (up to and including 5. 05) TM
Simple Mail Transport Protocol, the root of the problem • SMTP, defined in 1983 as the Internet Mail Transport Protocol • RFC 821 • Based on an “open” and “co-operative” model TM
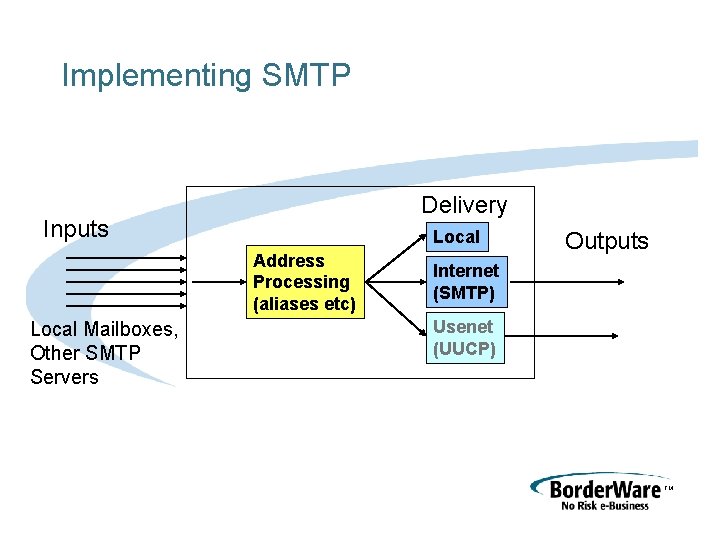
Implementing SMTP Delivery Inputs Local Address Processing (aliases etc) Local Mailboxes, Other SMTP Servers Outputs Internet (SMTP) Usenet (UUCP) TM
Implementing SMTP • SMTP’s Architecture and design philosophy has lead to implementations that lack: – Privacy and security for Mail Transport – Authentication of sender/recipient – Message authenticity checks – Relay controls TM
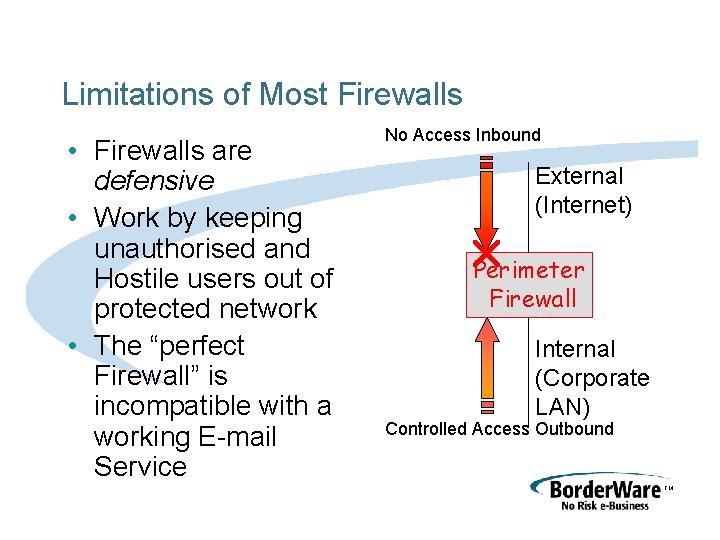
Limitations of Most Firewalls • Firewalls are defensive • Work by keeping unauthorised and Hostile users out of protected network • The “perfect Firewall” is incompatible with a working E-mail Service No Access Inbound External (Internet) Perimeter Firewall Internal (Corporate LAN) Controlled Access Outbound TM
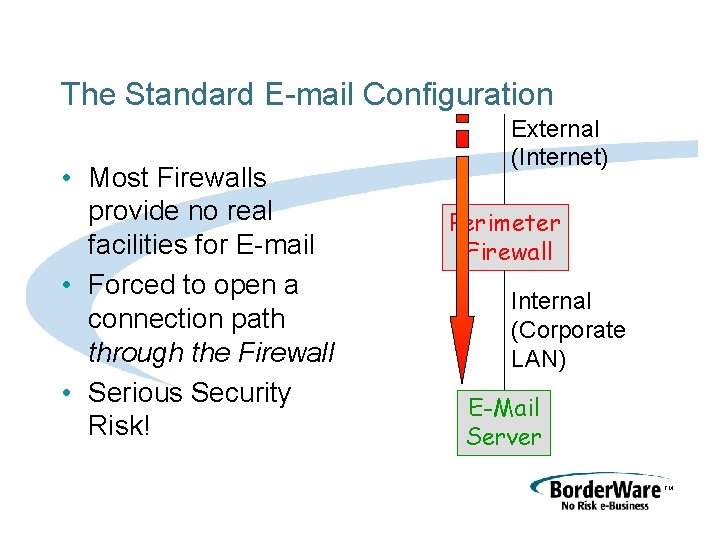
The Standard E-mail Configuration • Most Firewalls provide no real facilities for E-mail • Forced to open a connection path through the Firewall • Serious Security Risk! External (Internet) Perimeter Firewall Internal (Corporate LAN) E-Mail Server TM
The Border. Ware Mail Gateway • Protects E-mail servers • Provides added value facilities to maximise return on investment in E-mail Services • Provides Unified Mailbox with future plans for integration with Wireless Services • Includes S-Core secure operating system for maximum security and fast deployment TM
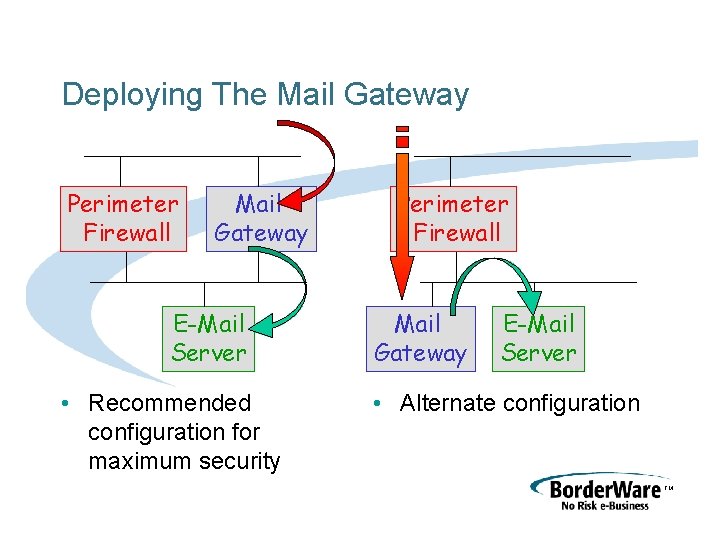
Deploying The Mail Gateway Perimeter Firewall Mail Gateway E-Mail Server • Recommended configuration for maximum security Perimeter Firewall Mail Gateway E-Mail Server • Alternate configuration TM
Store and Forward Relay • Mail Gateway’s security derives from a store and forward relay • No direct connections through the Gateway • Inbound and outbound delivery is a two stage process TM
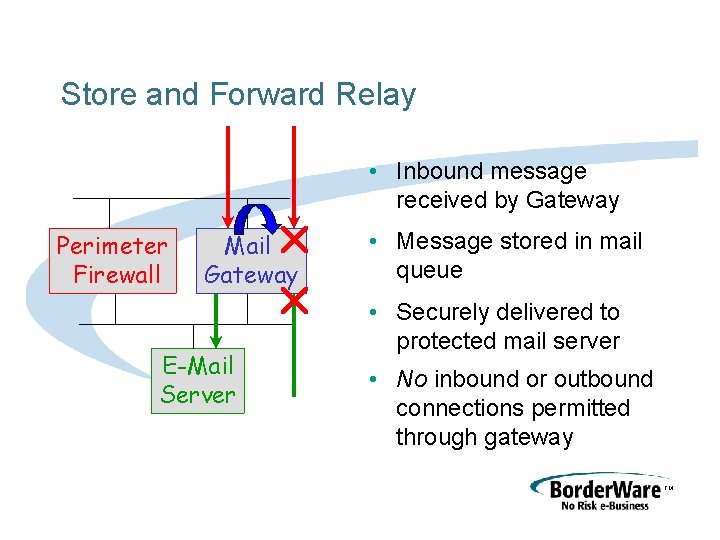
Store and Forward Relay • Inbound message received by Gateway Perimeter Firewall Mail Gateway E-Mail Server • Message stored in mail queue • Securely delivered to protected mail server • No inbound or outbound connections permitted through gateway TM
Mail Gateway Processing and Protecting E-mail • Mail routing for multiple servers • Controlling E-mail relay • Controlling unsolicited E-mail • Controlling Mail Attachments • Anti-virus controls • Secure Remote access to e-mail TM
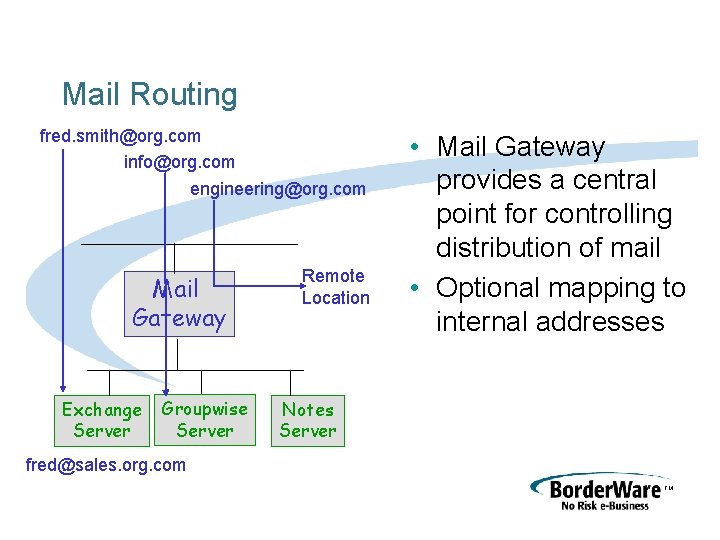
Mail Routing fred. smith@org. com info@org. com engineering@org. com Mail Gateway Exchange Server Groupwise Server Remote Location • Mail Gateway provides a central point for controlling distribution of mail • Optional mapping to internal addresses Notes Server fred@sales. org. com TM
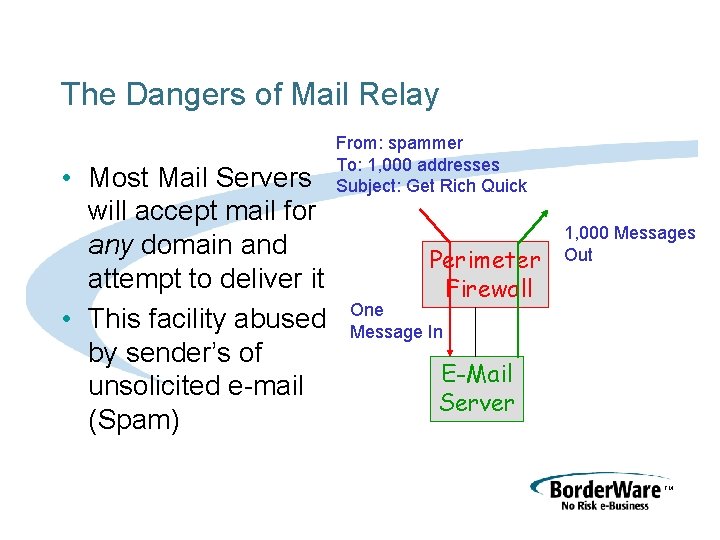
The Dangers of Mail Relay • Most Mail Servers will accept mail for any domain and attempt to deliver it • This facility abused by sender’s of unsolicited e-mail (Spam) From: spammer To: 1, 000 addresses Subject: Get Rich Quick Perimeter Firewall 1, 000 Messages Out One Message In E-Mail Server TM
Dangers of Mail Relay • ORBS (Open Relay Behaviour Modification system) black list of “open relays” • If your site is listed many servers will reject all mail • Affects legitimate mail and Spam TM
Defending against Mail Relay • Border. Ware Mail Gateway accepts only mail for local domains • Passes all the ORBS tests (http: //www. orbs. org) TM
Problems with unsolicited E-mail • Your organisation can become a target for Spam • Unwanted e-mail: – Wastes employee time – Wastes network bandwidth – Can fill mailboxes, preventing delivery of legitimate messages – Is irritating! TM

Defending Against Spam • Border. Ware Mail Gateway stops Spam by – Using the Real-Time Black Lists (http: //maps. vix. com) to reject Spam – Customised Filters From: Online. Casino@kxxk-8. fsnet. co. uk To: Online. Casino@kxxk-8. fsnet. co. uk Subject: [x] Play Free With Our Casino Sign-up Bonus TM
Problems with Mail Attachments • Viruses and Trojan Horses – the I Love You Virus was propagated as an attachment • Breach of confidentiality – Accidental or deliberate mailing of confidential information TM
Controlling Mail Attachments • Border. Ware Mail Gateway Filters on name • “*. vbs” blocks all Visual Basic Scripts (would block Love Virus) • Choice of actions on matched messages – Strip attachment, log, discard message, send e-mail alert TM
Anti-Virus Controls • Mail Gateway supports Trend’s Interscan Virus Wall technology as an additional cost option • Scans all mail and attachments for – Viruses, Macro Viruses, Trojan Horses – Messages cleaned, logged, or rejected TM
Remote Access to E-mail • Growing need as E-mail becomes primary method of communication • Access required from: – Branch Offices – Home Workers – Travelling employees TM
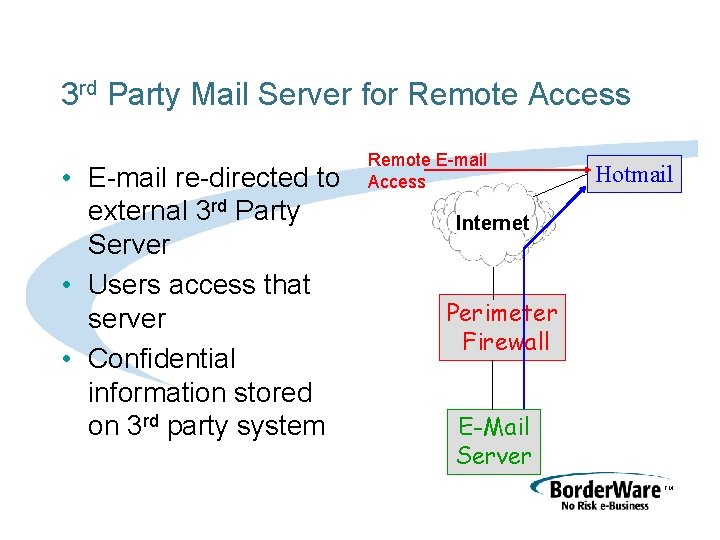
3 rd Party Mail Server for Remote Access • E-mail re-directed to external 3 rd Party Server • Users access that server • Confidential information stored on 3 rd party system Remote E-mail Access Hotmail Internet Perimeter Firewall E-Mail Server TM
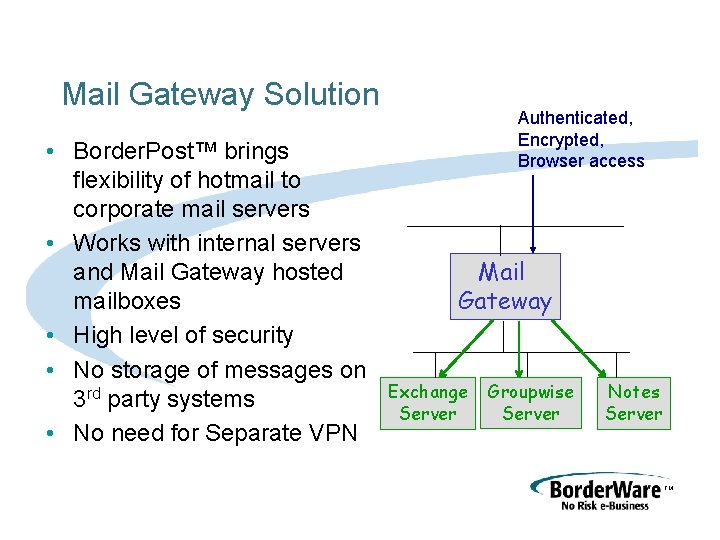
Mail Gateway Solution • Border. Post™ brings flexibility of hotmail to corporate mail servers • Works with internal servers and Mail Gateway hosted mailboxes • High level of security • No storage of messages on 3 rd party systems • No need for Separate VPN Authenticated, Encrypted, Browser access Mail Gateway Exchange Server Groupwise Server Notes Server TM
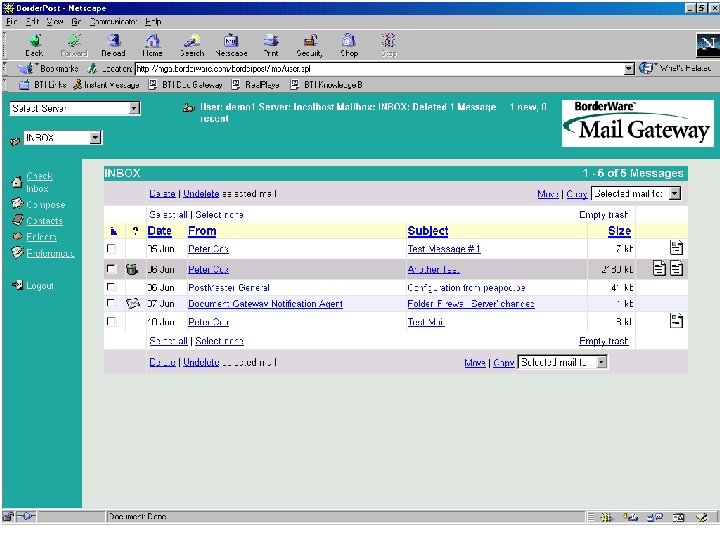
TM
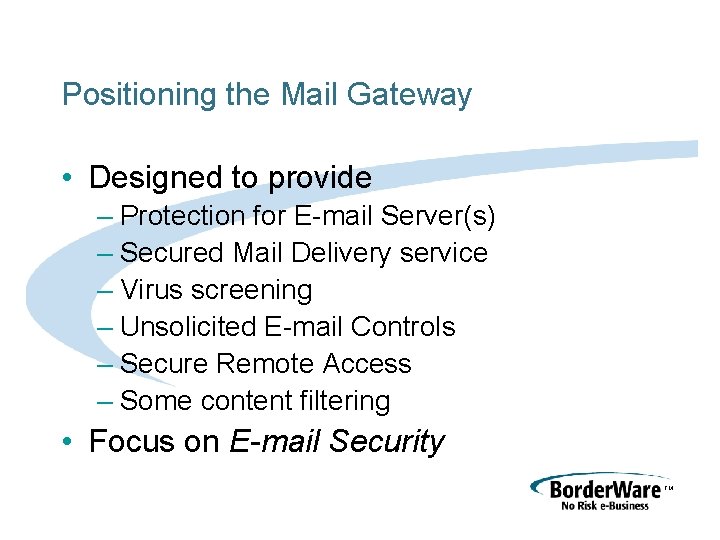
Positioning the Mail Gateway • Designed to provide – Protection for E-mail Server(s) – Secured Mail Delivery service – Virus screening – Unsolicited E-mail Controls – Secure Remote Access – Some content filtering • Focus on E-mail Security TM
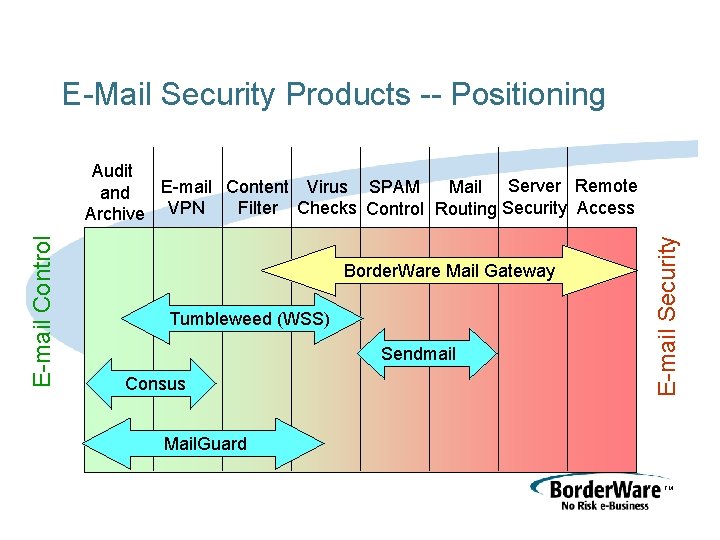
E-Mail Security Products -- Positioning Border. Ware Mail Gateway Tumbleweed (WSS) Sendmail Consus E-mail Security E-mail Control Audit E-mail Content Virus SPAM Mail Server Remote and Filter Checks Control Routing Security Access Archive VPN Mail. Guard TM
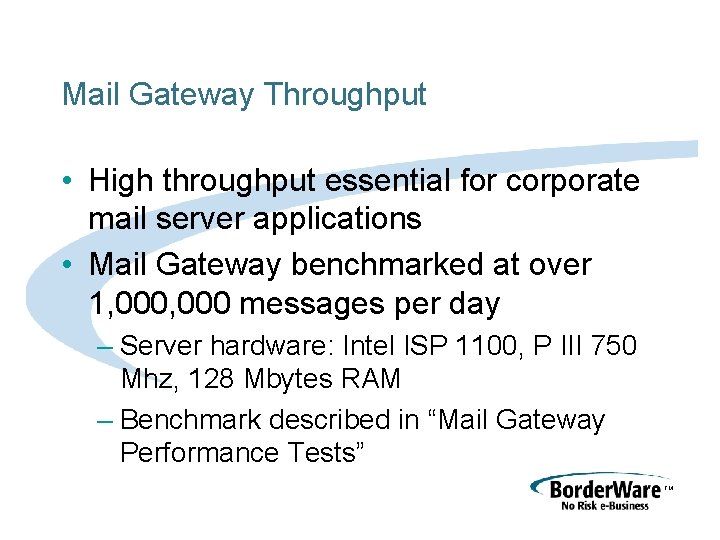
Mail Gateway Throughput • High throughput essential for corporate mail server applications • Mail Gateway benchmarked at over 1, 000 messages per day – Server hardware: Intel ISP 1100, P III 750 Mhz, 128 Mbytes RAM – Benchmark described in “Mail Gateway Performance Tests” TM
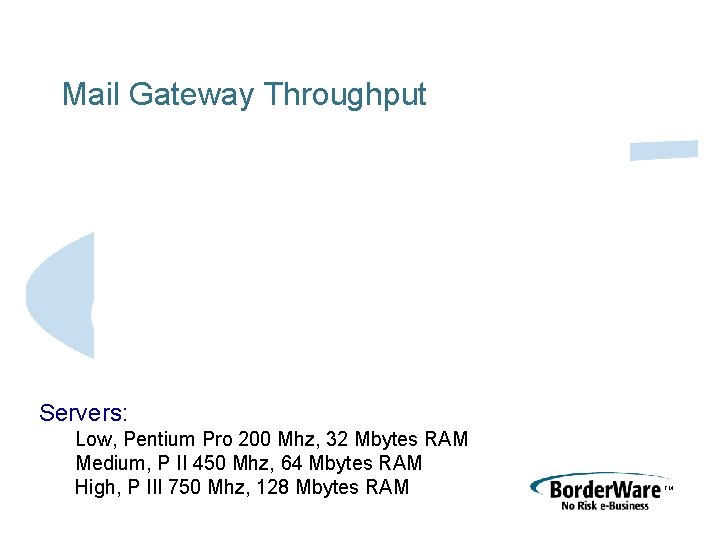
Mail Gateway Throughput Servers: Low, Pentium Pro 200 Mhz, 32 Mbytes RAM Medium, P II 450 Mhz, 64 Mbytes RAM High, P III 750 Mhz, 128 Mbytes RAM TM
Border. Ware Mail Gateway Summary • Complete Easy to manage e-mail security solution • Runs on S-Core Secure Operating System • Unified Mailbox for remote access with future extension to wireless access TM
- Slides: 33