Secure Sharding in Mongo DB KTH Applied Information
Secure Sharding in Mongo. DB KTH Applied Information Security Lab Presented By: Anam Zahid Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
Agenda n n n Scaling Mongo. DB’s Approach Architecture Mechanism Proposed Architecture KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
Scaling n Scaling UP (Vertical Scaling) – Addition of more CPUs and Storage Capacity 64 MB KTH Applied Information Security Lab 64 MB 64 MB Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
Scaling n Scaling OUT (Horizontal Scaling) – Distribution of data across multiple servers KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
Mongo. DB’s Approach n Sharding (horizontal scalability) – A method to store data across multiple machines/shards – Supports deployments with very large datasets – Maintains high throughput operations KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
Mongo. DB’s Approach n KTH Applied Information Security Lab Sharding Advantages – Reduces the number of operations each shard handles – Reduces the Amount of data that each server stores – Make the Cluster invisible for Clients – Ensures Cluster availability for reads and writes – Easy scaling out Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
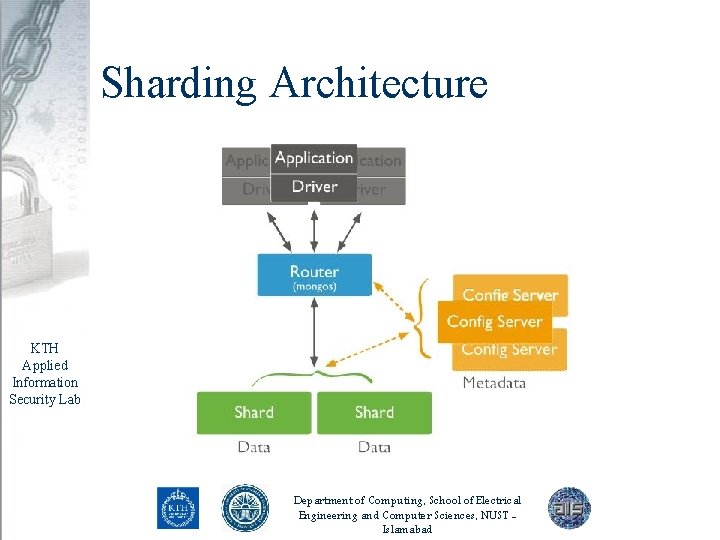
Sharding Architecture KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
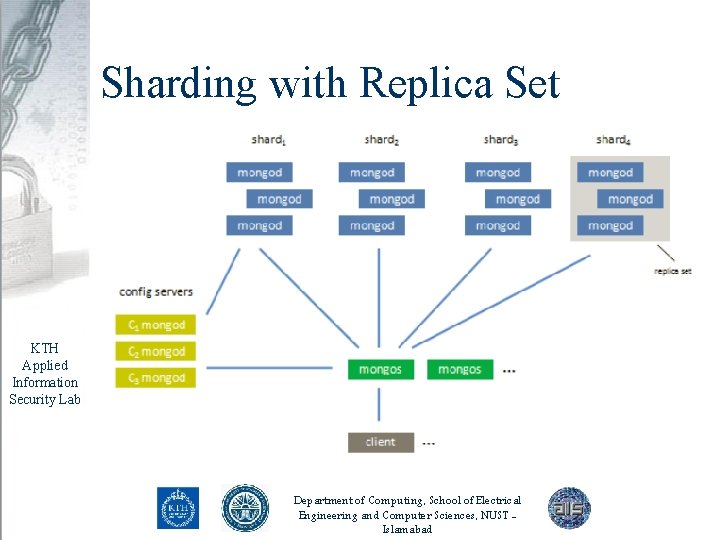
Sharding with Replica Set KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
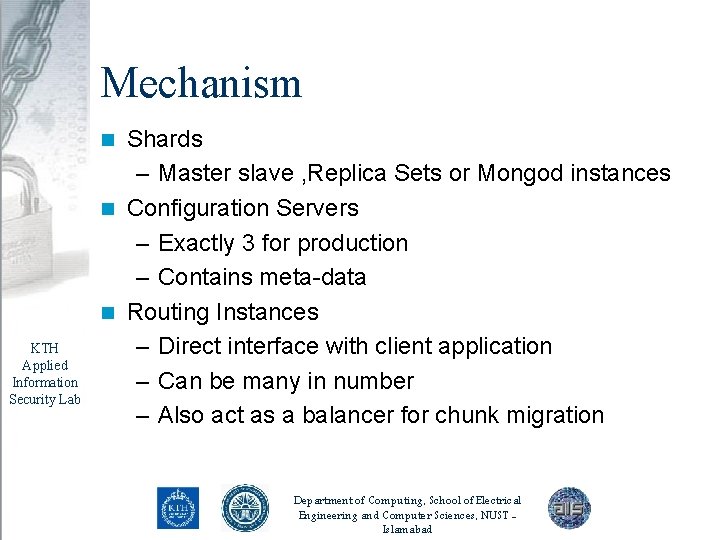
Mechanism Shards – Master slave , Replica Sets or Mongod instances n Configuration Servers – Exactly 3 for production – Contains meta-data n Routing Instances – Direct interface with client application – Can be many in number – Also act as a balancer for chunk migration n KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
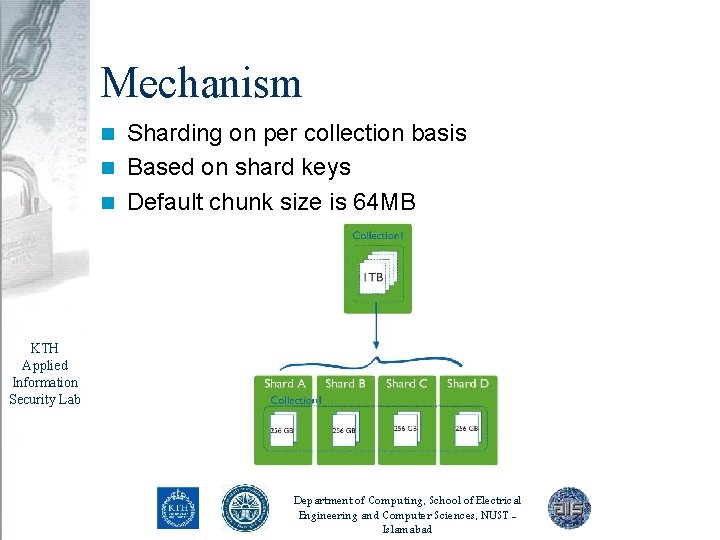
Mechanism Sharding on per collection basis n Based on shard keys n Default chunk size is 64 MB n KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
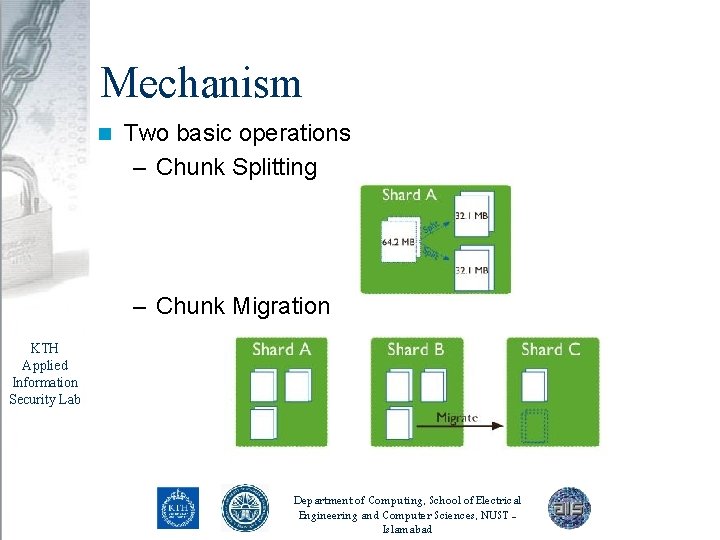
Mechanism n Two basic operations – Chunk Splitting – Chunk Migration KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
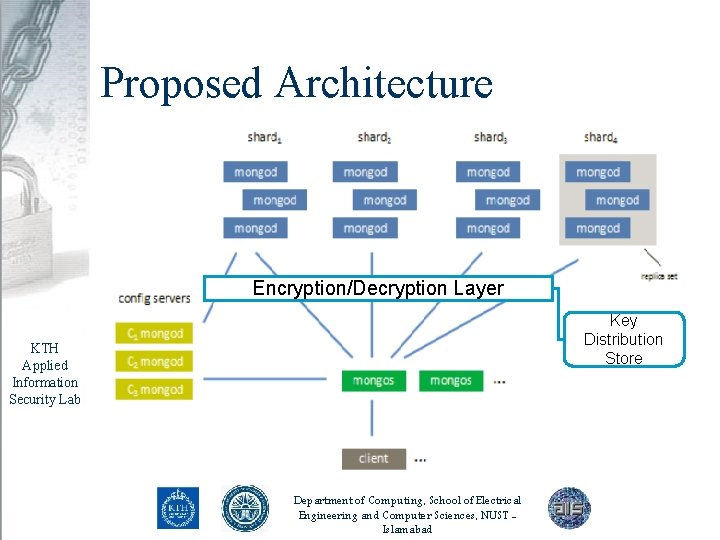
Proposed Architecture Encryption/Decryption Layer Key Distribution Store KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
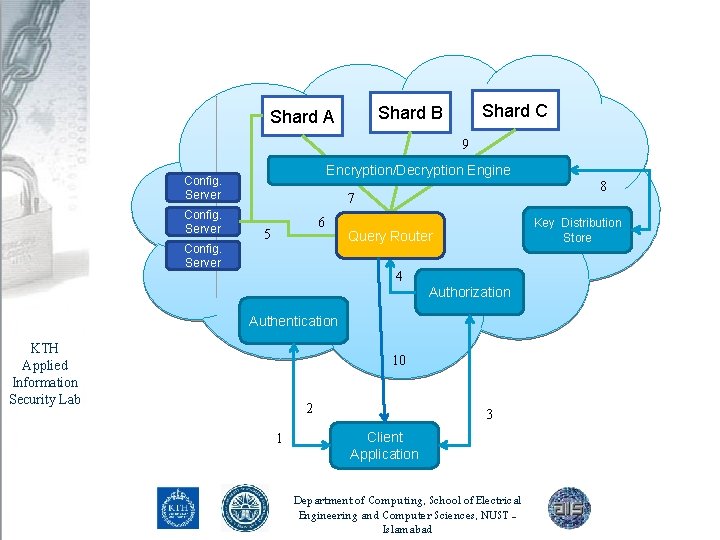
Shard C Shard B Shard A 9 Encryption/Decryption Engine Config. Server 8 7 6 5 Key Distribution Store Query Router 4 Authorization Authentication KTH Applied Information Security Lab 10 2 1 3 Client Application Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
Proposed Architecture 1. 2. 3. 4. Client Application sends Login Request to authentication Module Authentication Module authenticates it on the basis of certificate and sends reply back to client application Client application sends query to authorization server. The Authorization server generates policies and maps user policies with user profile. Then it verifies user query against user policy. In case of successful authorization, authorization server sends the query to Query Router KTH Applied Information Security Lab Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
Proposed Architecture 5. 6. 7. 8. 9. KTH Applied Information Security Lab 10. Query router get meta-data information about shards from the configuration server/s It then looks for appropriate shard/s on the basis of query parameters Query router sends query request to encryption/decryption Engine The encryption/Decryption Engine requests key distribution store for encryption key The Engine requests data from appropriate shards, decrypt it and sends the response back to query router. Query router forwards this data to Client Application Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
KTH Applied Information Security Lab Thank You Department of Computing, School of Electrical Engineering and Computer Sciences, NUST Islamabad
- Slides: 16