Secure Operating Systems Lesson E Windows Security Overview
- Slides: 15
Secure Operating Systems Lesson E: Windows Security - Overview
Where are we? o o We’ve discovered SELinux is moderately cool How does this compare to Windows? There’s a lot here, so we’ll just scratch the surface
Windows: History o o o So, Windows really does have a long history DOS survived for a long time, until we moved on to the NT core The current version of Windows 8 has finally started to move away from the backward compatibility that has dogged us
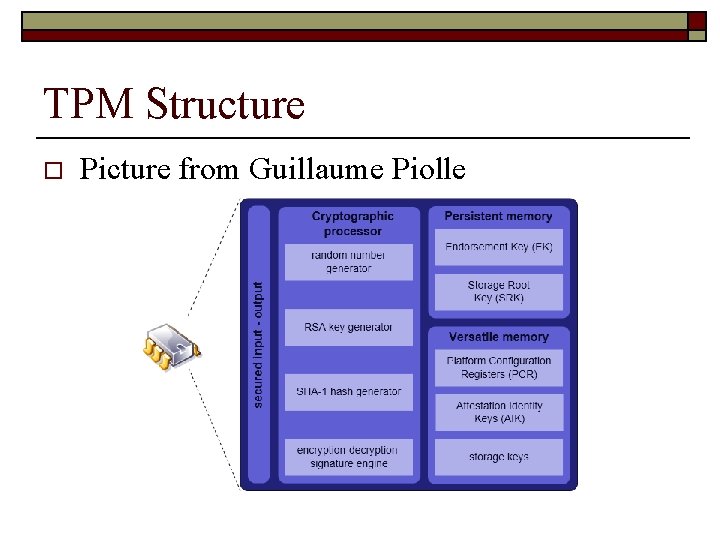
Bitlocker o o Full hard drive encryption is actually pretty cool: Bitlocker Can leverage the TPM, which is nice n n n Can provide remote attestation for hardware and software Not only for disk encryption; has been used for DRM too Can use in combination with a USB token
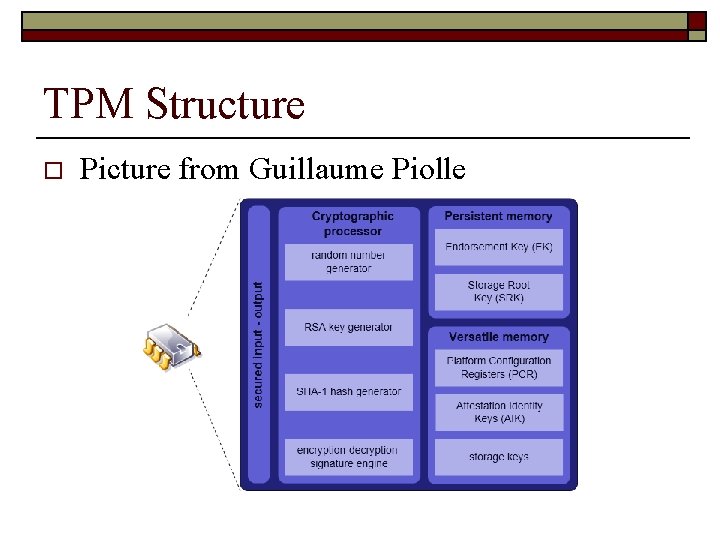
TPM Structure o Picture from Guillaume Piolle
Windows Integrity Control o o Although we don’t think about them, Windows uses MACLs (Mandatory Access Control Lists) Thus, the OS can make a security decision based on how trusted an object is n Let’s take a look with Process Explorer (from sysinternals)
SACLS and DACLS o SACLS beat DACLS n n o o o System Access Control List Discretionary Access Control List Thus, even if the DACL grants access, the SACL must also grant access for the operation to go through This is all documented well by MS… http: //msdn. microsoft. com/enus/library/windows/desktop/bb 648648(v=vs. 85). aspx Enables things like SYSTEM_MANDATORY_LABEL_NO_READ_UP
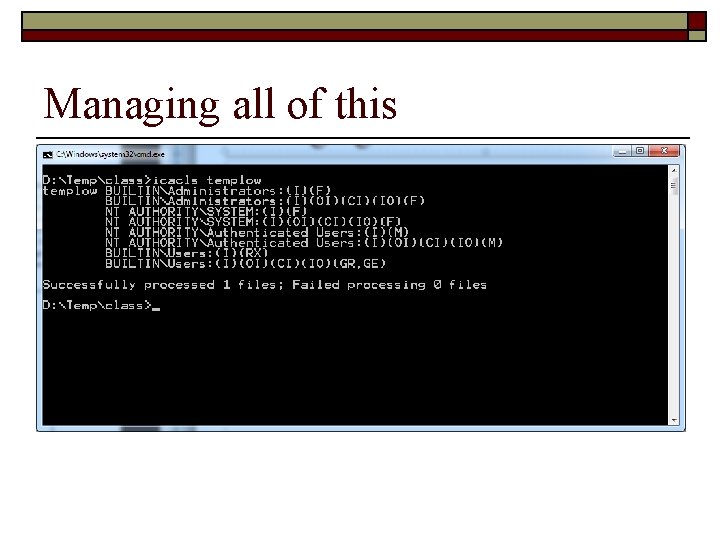
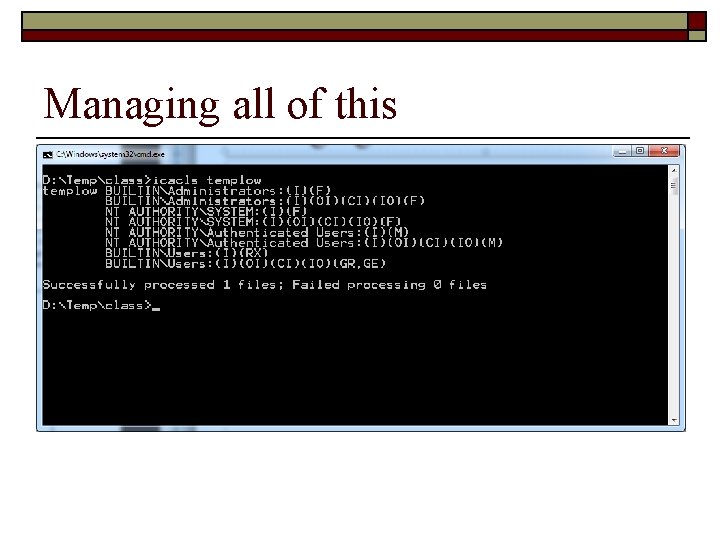
Managing all of this
Of course, we need o o o Run As… administrator icacls templow /setintegritylevel L for example But of course, we never use this, except for using the defaults, which seems like a pity, eh? n There’s a philosophical point here
UAC (Woohoo!) o o o Everyone seems to hate UAC, but it does help in terms of users making mistakes It’s certainly not bulletproof (cue Shaun) The idea is the principle of least privilege The problem is that we don’t read the popups very well The basic idea: run with lower privileges, and then upgrade as you need it
Service Resource Isolation o o o What happens when a service gets broken in to? Let’s look sc query type= service | more sc showsid Adobe. Active. File. Monitor 9. 0 psgetsid <sid> Can create a *restricted* SID n Two checks: one on the enabled token, one on the restricted SID
Service Refactoring o o Basically, run services with base least privilege New service hosts (low to high): n n n Local. Service. No. Network Local. Service. Restricted Local. Service. Network. Restricted Network. Service. Network. Restricted Local. System. Network. Restricted
Restricted Network Access o Network restriction policies can be applied to services too o o Direction: ingress and egress Protocol: what protocols should be allowed? Principal: Rules apply to specific users Interface: WLAN, Wireless, LAN etc.
Buffer Overflows o o Let’s remind ourselves how buffer overflows work The compiler now adds Cookies… let’s look at the code
Questions & Comments o What do you want to know?