Secure Nested Codes for Type II Wiretap Channels
- Slides: 1
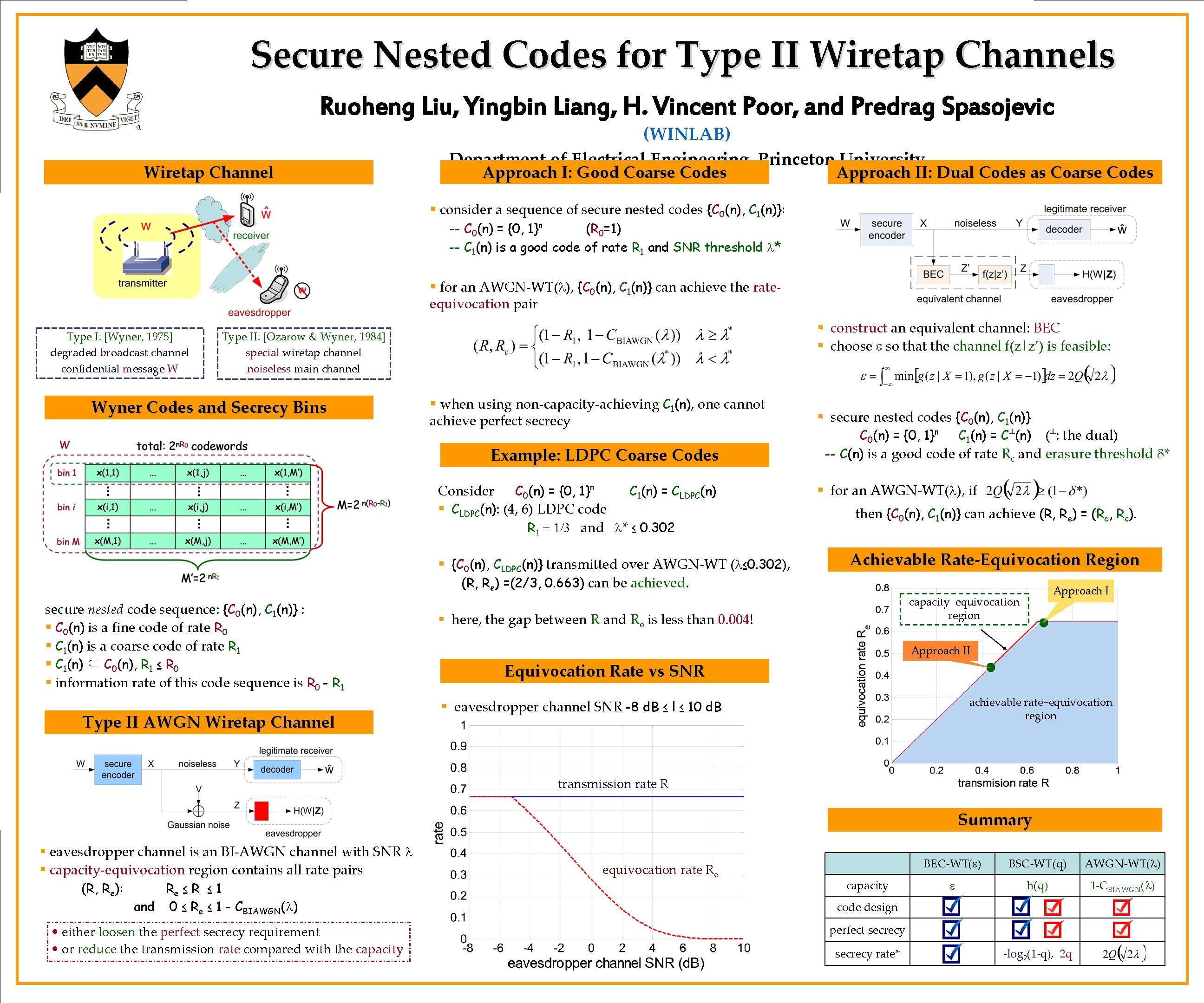
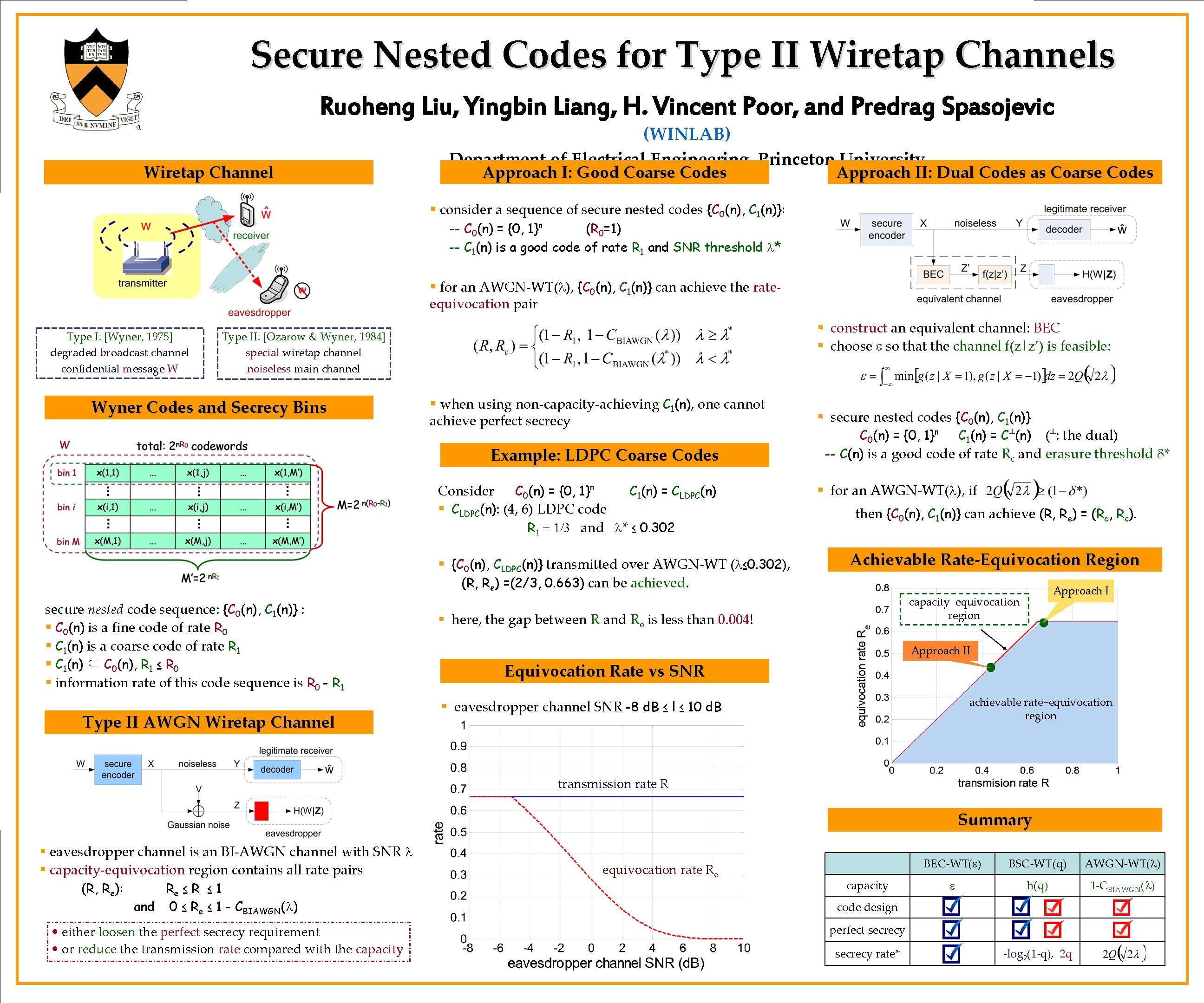
Secure Nested Codes for Type II Wiretap Channels Ruoheng Liu, Yingbin Liang, H. Vincent Poor, and Predrag Spasojevic Wiretap Channel (WINLAB) Department of Electrical Engineering, Princeton University Approach I: Good Coarse Codes Approach II: Dual Codes as Coarse Codes § consider a sequence of secure nested codes {C 0(n), C 1(n)}: -- C 0(n) = {0, 1}n (R 0=1) -- C 1(n) is a good code of rate R 1 and SNR threshold l* § for an AWGN-WT(l), {C 0(n), C 1(n)} can achieve the rateequivocation pair Type I: [Wyner, 1975] degraded broadcast channel confidential message W § construct an equivalent channel: BEC § choose e so that the channel f(z|z’) is feasible: Type II: [Ozarow & Wyner, 1984] special wiretap channel noiseless main channel Wyner Codes and Secrecy Bins § when using non-capacity-achieving C 1(n), one cannot achieve perfect secrecy Example: LDPC Coarse Codes Consider C 0(n) = {0, 1}n C 1(n) = CLDPC(n) § CLDPC(n): (4, 6) LDPC code R 1 = 1/3 and l* ≤ 0. 302 § {C 0(n), CLDPC(n)} transmitted over AWGN-WT (l≤ 0. 302), (R, Re) =(2/3, 0. 663) can be achieved. secure nested code sequence: {C 0(n), C 1(n)} : § C 0(n) is a fine code of rate R 0 § C 1(n) is a coarse code of rate R 1 § C 1(n) ⊆ C 0(n), R 1 ≤ R 0 § information rate of this code sequence is R 0 - R 1 Type II AWGN Wiretap Channel § secure nested codes {C 0(n), C 1(n)} C 0(n) = {0, 1}n C 1(n) = C┴(n) (┴: the dual) -- C(n) is a good code of rate Rc and erasure threshold d* § for an AWGN-WT(l), if then {C 0(n), C 1(n)} can achieve (R, Re) = (Rc, Rc). Achievable Rate-Equivocation Region Approach I capacity−equivocation region § here, the gap between R and Re is less than 0. 004! Approach II Equivocation Rate vs SNR achievable rate−equivocation region § eavesdropper channel SNR -8 d. B ≤ l ≤ 10 d. B transmission rate R Summary § eavesdropper channel is an BI-AWGN channel with SNR l § capacity-equivocation region contains all rate pairs (R, Re): Re ≤ R ≤ 1 and 0 ≤ Re ≤ 1 - CBIAWGN(l) • either loosen the perfect secrecy requirement • or reduce the transmission rate compared with the capacity equivocation rate Re capacity BEC-WT(e) BSC-WT(q) AWGN-WT(l) e h(q) 1 -CBIAWGN(l) code design perfect secrecy rate* -log 2(1 -q), 2 q