Secure Credit Card Processing Presented by Jason Timian
Secure Credit Card Processing Presented by: Jason Timian, CBORD 1 | CBORD 2018 User Group Conference | Presentation
PCI DSS 12 requirements 1. Install and maintain a firewall configuration to protect cardholder data 2. Do not use vendor-supplied defaults for system passwords and other security parameters 3. Protect stored cardholder data 4. Encrypt transmission of cardholder data across open, public networks 5. Protect all systems against malware and regularly update anti-virus software 2 | CBORD 2018 User Group Conference | Presentation
PCI DSS, continued 12 requirements 6. Develop and maintain secure systems and applications 7. Restrict access to cardholder data by business need to know 8. Identify and authentic access to system components 9. Restrict Physical access to cardholder data 10. Track and monitor all access to network resources and cardholder data 11. Regularly test security systems and processes 12. Maintain a policy that addresses information security for all personnel 3 | CBORD 2018 User Group Conference | Presentation
Compliance Validation Merchant Levels • Level 1 - Processing over 6 million Visa transactions annually • Level 2 – processing 1 – 6 million Visa transactions annually • Level 3 – 20, 000 – 1 million e-commerce Visa transactions annually • Level 4 – Less than 1 million transactions or less than 20, 000 ecommerce Visa transactions 4 | CBORD 2018 User Group Conference | Presentation
Payment Application Data Security Standard PA DSS • Standards for software vendors that develop payment applications • PCI SSC lists validated version on its website • Acceptable for new deployments • Acceptable for existing deployments 5 | CBORD 2018 User Group Conference | Presentation
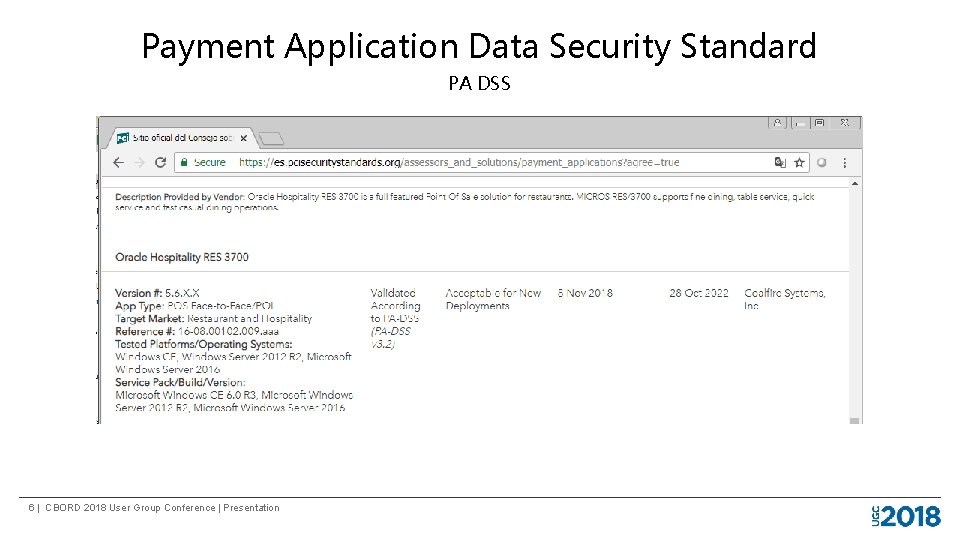
Payment Application Data Security Standard PA DSS 6 | CBORD 2018 User Group Conference | Presentation
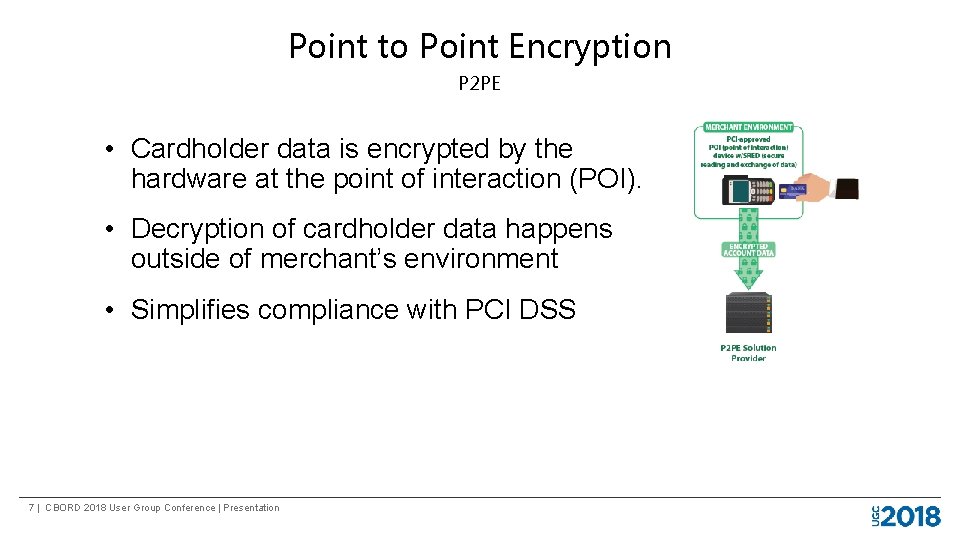
Point to Point Encryption P 2 PE • Cardholder data is encrypted by the hardware at the point of interaction (POI). • Decryption of cardholder data happens outside of merchant’s environment • Simplifies compliance with PCI DSS 7 | CBORD 2018 User Group Conference | Presentation
Point to Point Encryption P 2 PE • 26 Self-Assessment Questionnaire • Merchant must follow P 2 PE Instruction Manual (PIM) • Securing devices • Inventory tracking • Validated P 2 PE solutions listed on PCI SSC website 8 | CBORD 2018 User Group Conference | Presentation
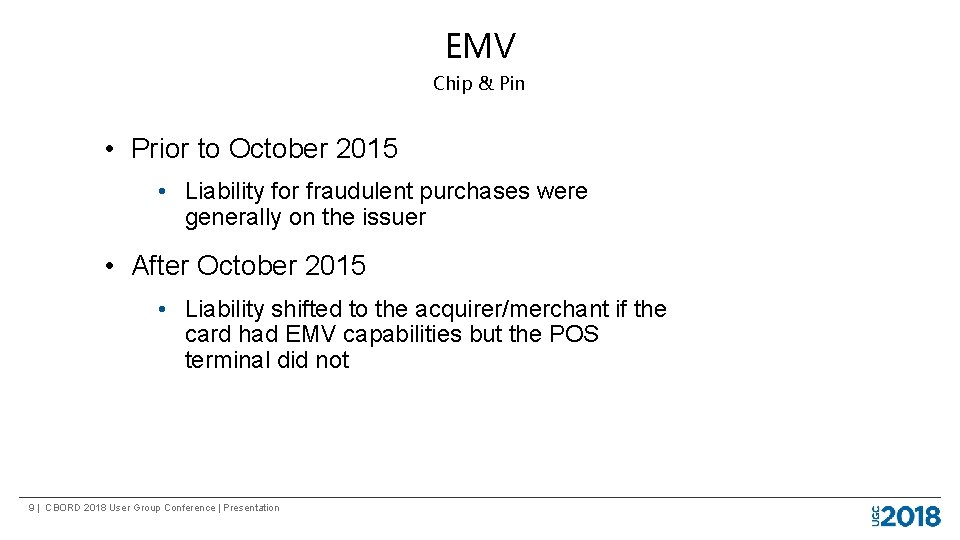
EMV Chip & Pin • Prior to October 2015 • Liability for fraudulent purchases were generally on the issuer • After October 2015 • Liability shifted to the acquirer/merchant if the card had EMV capabilities but the POS terminal did not 9 | CBORD 2018 User Group Conference | Presentation
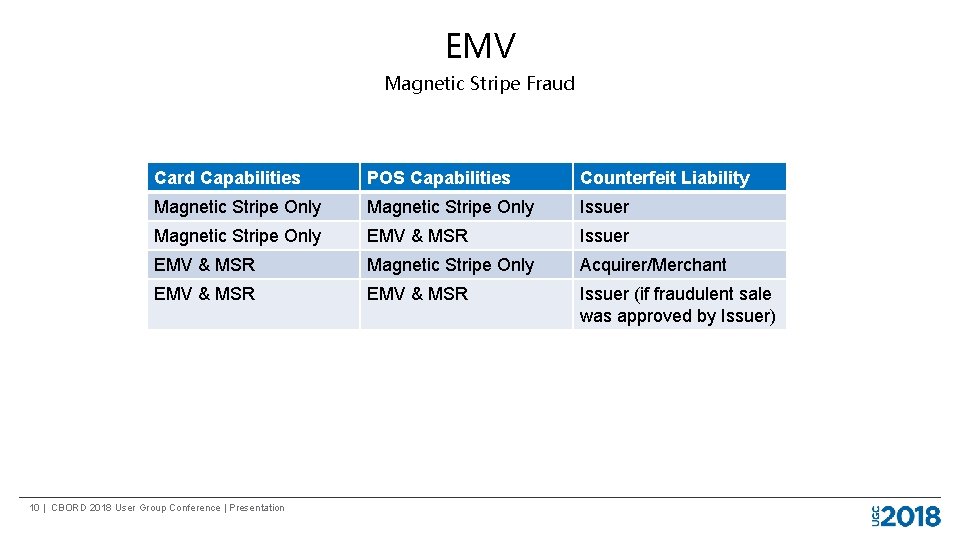
EMV Magnetic Stripe Fraud Card Capabilities POS Capabilities Counterfeit Liability Magnetic Stripe Only Issuer Magnetic Stripe Only EMV & MSR Issuer EMV & MSR Magnetic Stripe Only Acquirer/Merchant EMV & MSR Issuer (if fraudulent sale was approved by Issuer) 10 | CBORD 2018 User Group Conference | Presentation
EMV - Cardholder Verification Method CVM • Used to evaluate if the person presenting the card is the legitimate cardholder • In EMV context, there are 3 applicable categories: • PIN (online/offline) • Signature • No CVM Requirement 11 | CBORD 2018 User Group Conference | Presentation
EMV - Cardholder Verification Method CVM • Online PIN Verification • Card is inserted into POI PED • Cardholder is prompted to enter PIN • Transaction authorization request includes encrypted PIN when sent to the Issuer. • Issuer validates PIN “online” along with authorization amount • Sale is approved at POS terminal 12 | CBORD 2018 User Group Conference | Presentation
EMV - Cardholder Verification Method CVM • Offline PIN Verification • Card is inserted into POI PED • Cardholder is prompted to enter PIN • PIN is verified with Chip on the card before authorization request is sent • Authorization request is sent to be approved by Issuer • Issuer approves/denies transaction 13 | CBORD 2018 User Group Conference | Presentation
EMV - Cardholder Verification Method CVM • Signature Verification • Card is inserted into POI device • Authorization request is sent to be approved by Issuer • Issuer approves transaction • Cardholder signs signature pad or paper voucher • Merchant verifies signature 14 | CBORD 2018 User Group Conference | Presentation
EMV - Cardholder Verification Method CVM • No CVM • No signature or PIN entry is required • Typically for low value amounts • No CVM limits are set by card brands 15 | CBORD 2018 User Group Conference | Presentation
EMV - Cardholder Verification Method CVM • EMV enabled credit cards have CVM preference programmed into it by the Issuer • POI PED knows which CVM options it can support • CVM preferred by the card that the PED supports will be used 16 | CBORD 2018 User Group Conference | Presentation
EMV - Cardholder Verification Method CVM • US debit cards typically have two CVM preferences programmed • One for when processed as a credit card • One for when processed as a debit card 17 | CBORD 2018 User Group Conference | Presentation
EMV - Cardholder Verification Method CVM • US debit cards typically have two CVM preferences programmed • One for when processed as a credit card • One for when processed as a debit card • Online PIN verification requires PED to be injected with key serial number (KSN) that is specific to the processor/acquiring bank 18 | CBORD 2018 User Group Conference | Presentation
Qualified Integrators & Resellers QIR • Program applies to installers who carry out Qualified Installations of payment applications on behalf of merchants or service providers. • Requires technicians to attend training and pass certification test • Must requalify every year 19 | CBORD 2018 User Group Conference | Presentation
Qualified Integrators & Resellers QIR • Visa required all acquirers to ensure that level 4 merchants use a QIR professional as of January 31, 2017 • Visa does not enforce compliance against merchants 20 | CBORD 2018 User Group Conference | Presentation
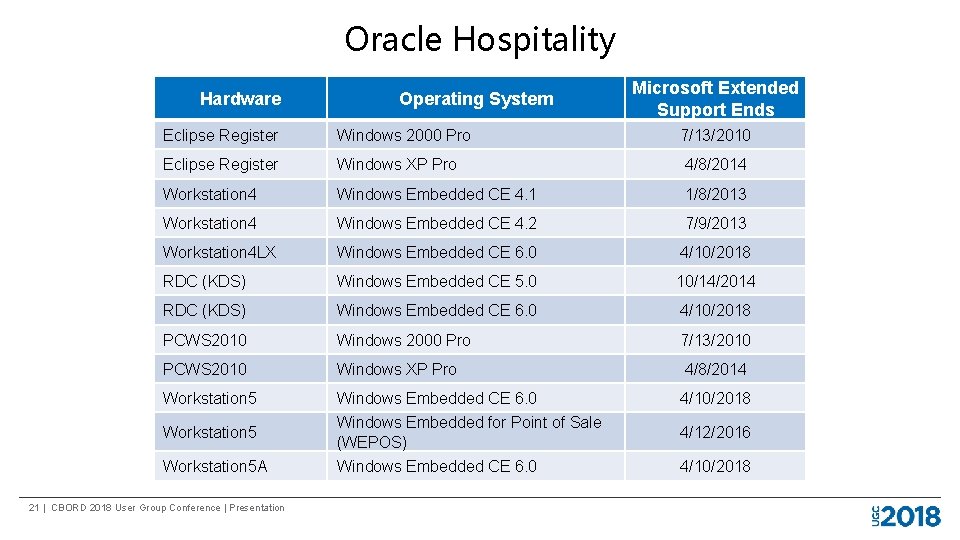
Oracle Hospitality Hardware Operating System Microsoft Extended Support Ends Eclipse Register Windows 2000 Pro 7/13/2010 Eclipse Register Windows XP Pro 4/8/2014 Workstation 4 Windows Embedded CE 4. 1 1/8/2013 Workstation 4 Windows Embedded CE 4. 2 7/9/2013 Workstation 4 LX Windows Embedded CE 6. 0 4/10/2018 RDC (KDS) Windows Embedded CE 5. 0 10/14/2014 RDC (KDS) Windows Embedded CE 6. 0 4/10/2018 PCWS 2010 Windows 2000 Pro 7/13/2010 PCWS 2010 Windows XP Pro 4/8/2014 Workstation 5 Windows Embedded CE 6. 0 4/10/2018 Workstation 5 Windows Embedded for Point of Sale (WEPOS) 4/12/2016 Workstation 5 A Windows Embedded CE 6. 0 4/10/2018 21 | CBORD 2018 User Group Conference | Presentation
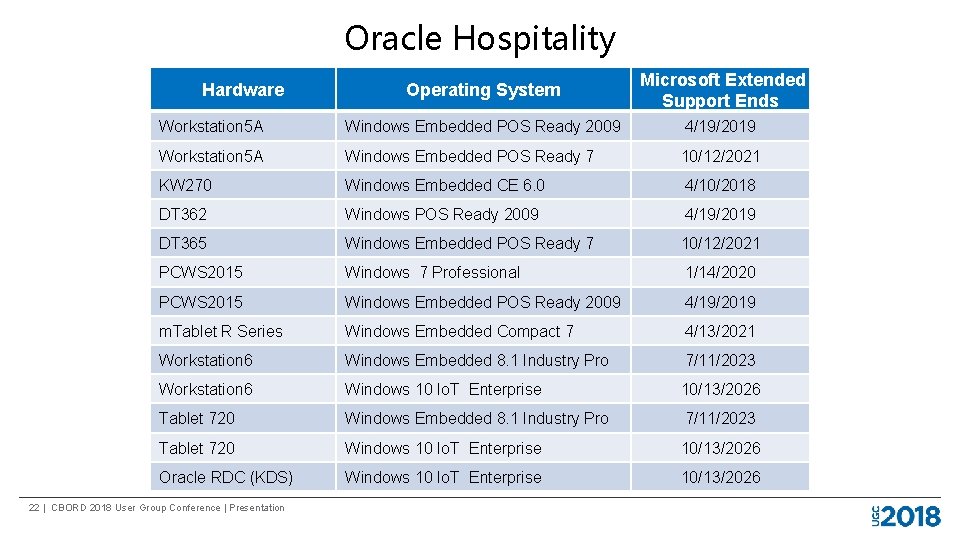
Oracle Hospitality Operating System Microsoft Extended Support Ends Workstation 5 A Windows Embedded POS Ready 2009 4/19/2019 Workstation 5 A Windows Embedded POS Ready 7 10/12/2021 KW 270 Windows Embedded CE 6. 0 4/10/2018 DT 362 Windows POS Ready 2009 4/19/2019 DT 365 Windows Embedded POS Ready 7 10/12/2021 PCWS 2015 Windows 7 Professional 1/14/2020 PCWS 2015 Windows Embedded POS Ready 2009 4/19/2019 m. Tablet R Series Windows Embedded Compact 7 4/13/2021 Workstation 6 Windows Embedded 8. 1 Industry Pro 7/11/2023 Workstation 6 Windows 10 Io. T Enterprise 10/13/2026 Tablet 720 Windows Embedded 8. 1 Industry Pro 7/11/2023 Tablet 720 Windows 10 Io. T Enterprise 10/13/2026 Oracle RDC (KDS) Windows 10 Io. T Enterprise 10/13/2026 Hardware 22 | CBORD 2018 User Group Conference | Presentation
Oracle Hospitality PA DSS • PA DSS Implementation Guides available from Oracle’s website: https: //docs. oracle. com/en/industries/hospitality/ • PA DSS Application ≠ PCI DSS compliance • Application must be installed in a PCI DSS environment and according to implementation guide 23 | CBORD 2018 User Group Conference | Presentation
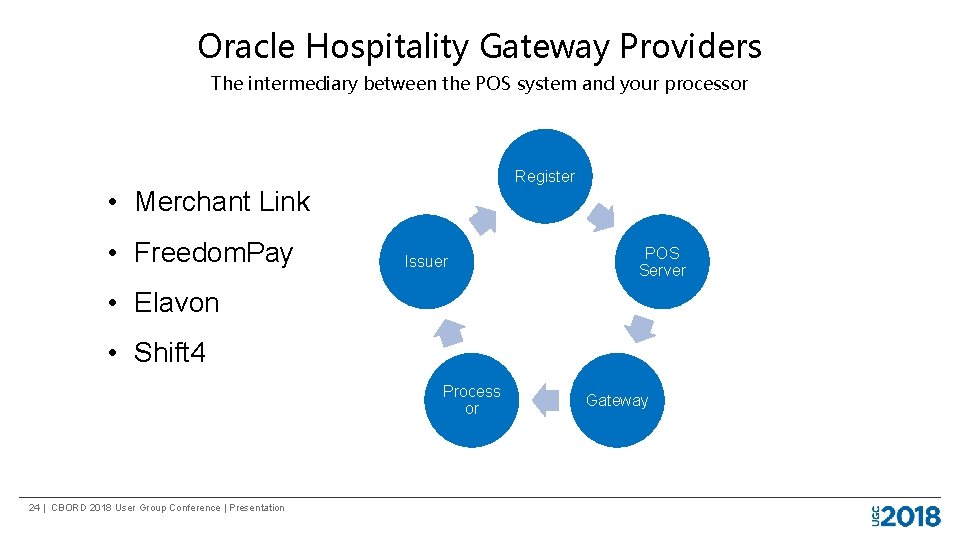
Oracle Hospitality Gateway Providers The intermediary between the POS system and your processor Register • Merchant Link • Freedom. Pay Issuer POS Server • Elavon • Shift 4 Process or 24 | CBORD 2018 User Group Conference | Presentation Gateway
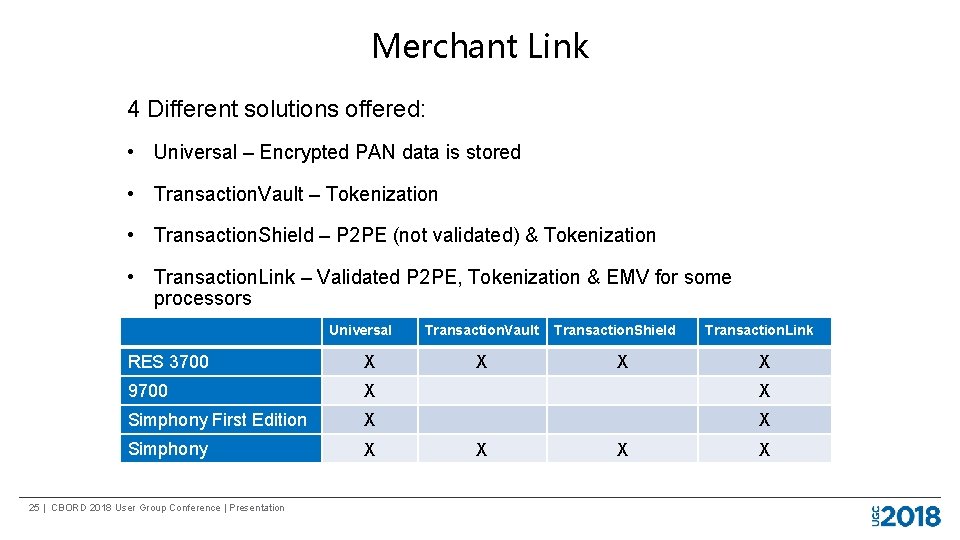
Merchant Link 4 Different solutions offered: • Universal – Encrypted PAN data is stored • Transaction. Vault – Tokenization • Transaction. Shield – P 2 PE (not validated) & Tokenization • Transaction. Link – Validated P 2 PE, Tokenization & EMV for some processors Universal Transaction. Vault Transaction. Shield Transaction. Link RES 3700 X 9700 X X Simphony First Edition X X Simphony X 25 | CBORD 2018 User Group Conference | Presentation X X X
Merchant Link - Transaction. Link • Latest solution offered by Merchant Link • Partnered with Bluefin Payment Systems for P 2 PE encryption • Uses Ingenico pin pad readers • Devices isolated from POS system and have separate network connection • EMV support • TSYS, Vantiv, First Data, Chase Paymentech, & Elavon • Near Field Communication (NFC) support - Apple Pay, Android Pay, etc. • Requires the use of OPI 26 | CBORD 2018 User Group Conference | Presentation
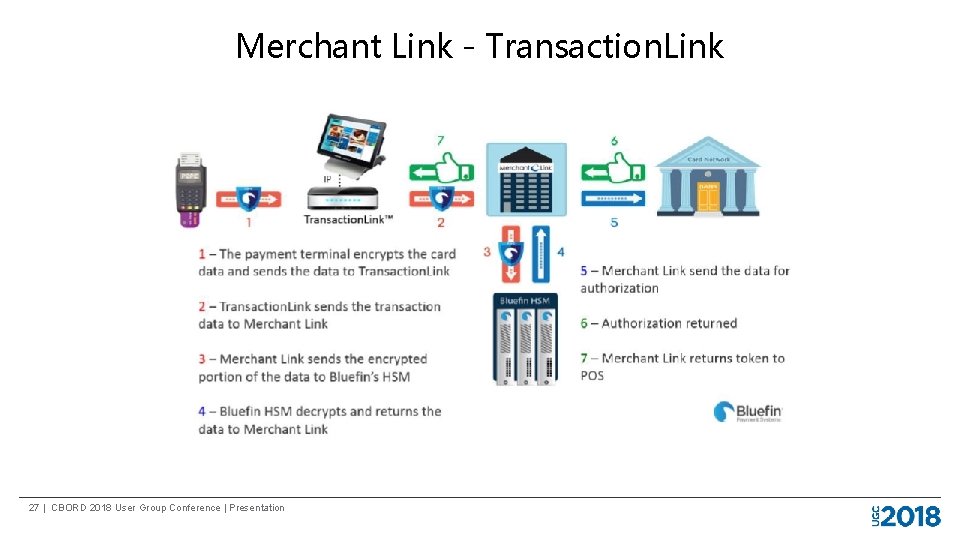
Merchant Link - Transaction. Link 27 | CBORD 2018 User Group Conference | Presentation
Freedom. Pay • First to the market with P 2 PE validated solution • EMV certified for most processors • Ingenico pin pad readers • Does not require OPI 28 | CBORD 2018 User Group Conference | Presentation
Freedom. Pay • Readers connect to register via USB Terminal • Near Field Communication (NFC) support - Apple Pay, Android Pay, etc. • Supported on 3700, 9700, Simphony First Edition and Simphony 29 | CBORD 2018 User Group Conference | Presentation
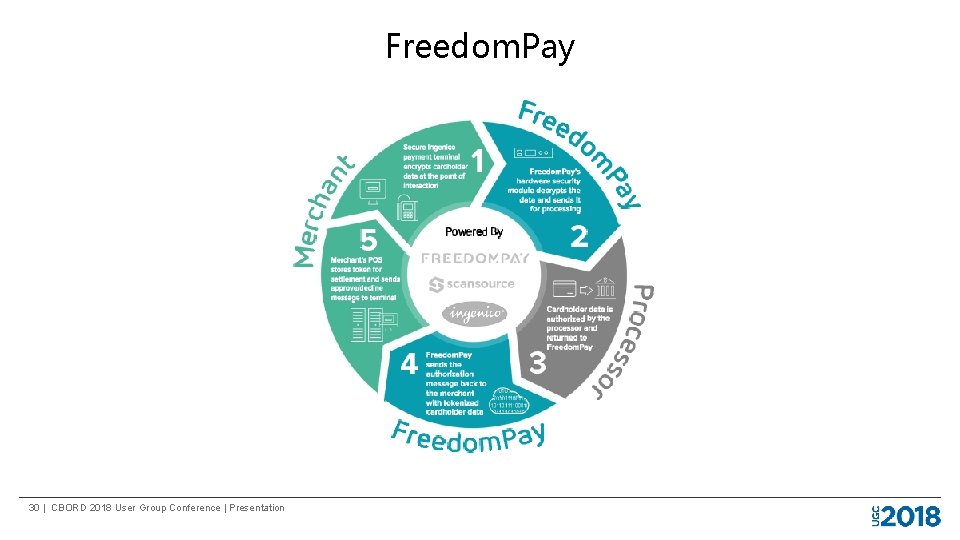
Freedom. Pay 30 | CBORD 2018 User Group Conference | Presentation
Elavon Simplify • P 2 PE, Tokenization & EMV • Requires separate network drop • Near Field Communication (NFC) support - Apple Pay, Android Pay, etc. • Supported on 3700, Simphony & 9700 • Requires OPI 31 | CBORD 2018 User Group Conference | Presentation
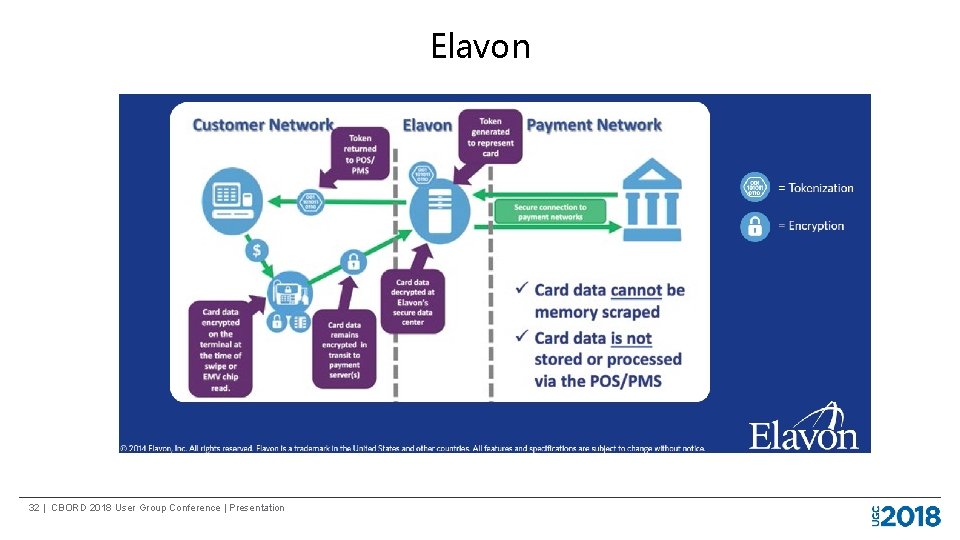
Elavon 32 | CBORD 2018 User Group Conference | Presentation
Appetize • Freedom. Pay is the gateway provider • P 2 PE support • EMV depends on processor • Ingenico USB i. PP 350 readers 33 | CBORD 2018 User Group Conference | Presentation
Thank You Questions and Answers 34 | CBORD 2018 User Group Conference | Presentation
We want your feedback! Please evaluate this session in the ERMobile app. Your feedback helps us improve future sessions. Find this session in the app, and touch COMPLETE SESSION SURVEY. Thank you! 35 | CBORD 2018 User Group Conference | Presentation

- Slides: 36