Secure and Robust Fragile Watermarking Scheme for Medical
Secure and Robust Fragile Watermarking Scheme for Medical Images u Source : IEEE Access Vol. 6, pp. 10269 - 10278, Feb 2018 u Authors : Abdulaziz Shehab, Mohamed Elhoseny, Khan Muhammad, Arun Kumar Sangaiah, Po Yang, Haojun Huang, Guolin Hou u Speaker : Si-Liang He u Date : 2018/9/6 1
Outline Introduction Related work Proposed scheme Experimental results Conclusions 2
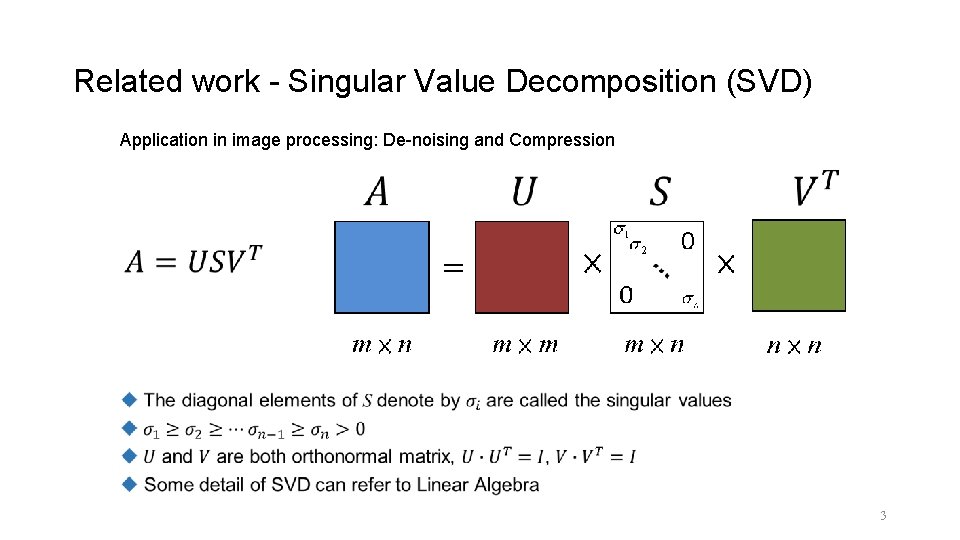
Related work - Singular Value Decomposition (SVD) Application in image processing: De-noising and Compression 3
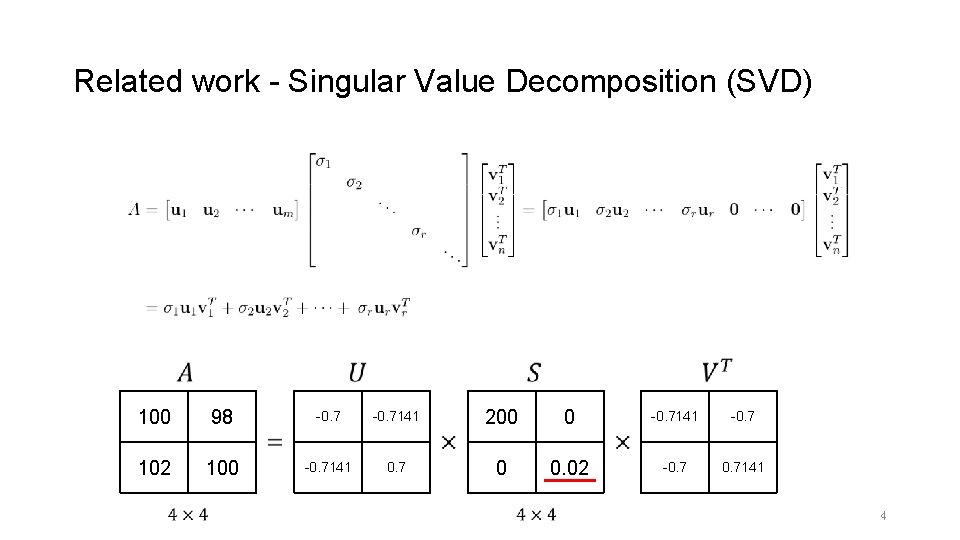
Related work - Singular Value Decomposition (SVD) 100 98 -0. 7141 200 0 -0. 7141 -0. 7 102 100 -0. 7141 0. 7 0 0. 02 -0. 7141 4
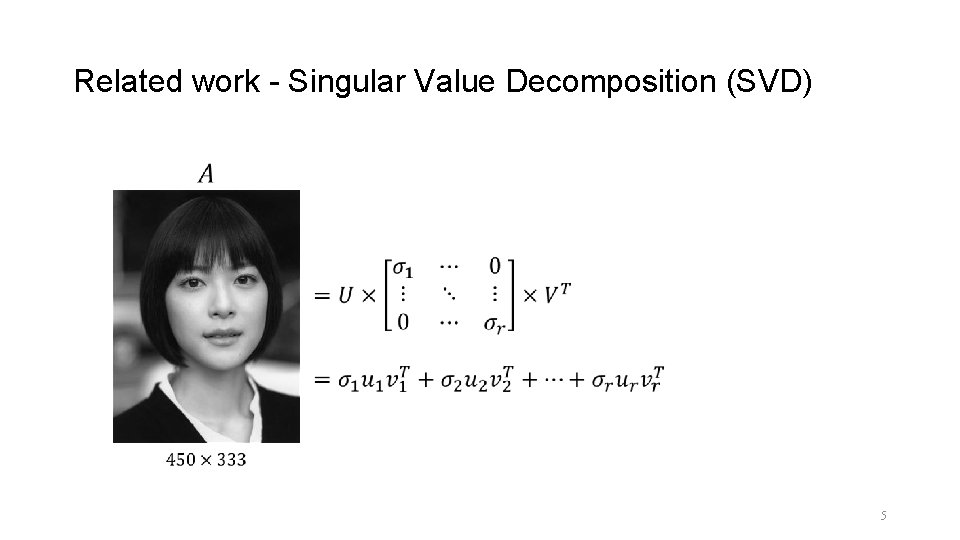
Related work - Singular Value Decomposition (SVD) 5
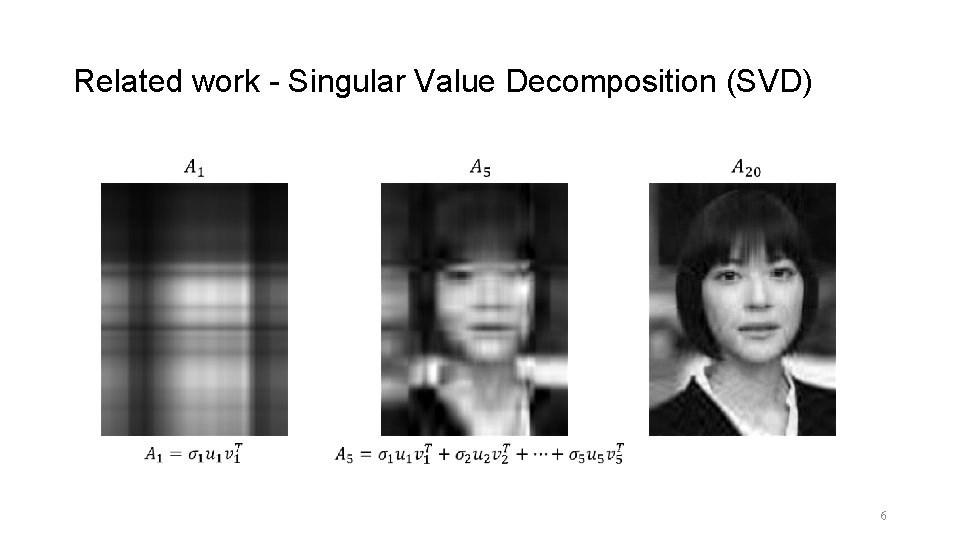
Related work - Singular Value Decomposition (SVD) 6
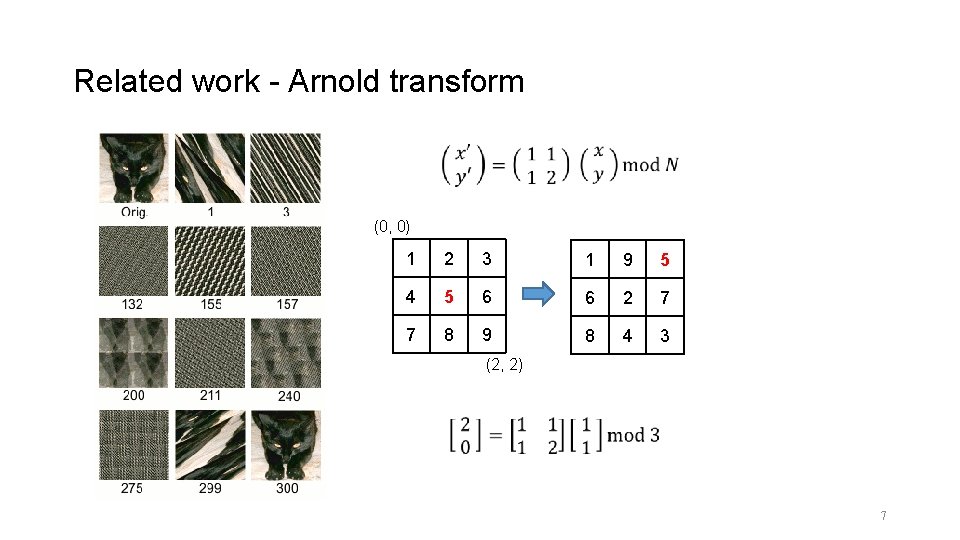
Related work - Arnold transform (0, 0) 1 2 3 1 9 5 4 5 6 6 2 7 7 8 9 8 4 3 (2, 2) 7
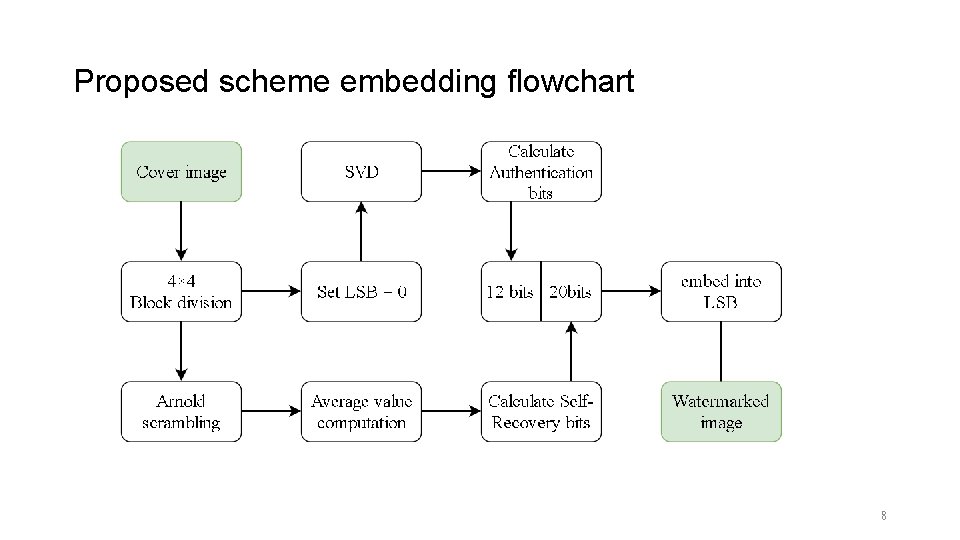
Proposed scheme embedding flowchart 8
![Proposed scheme - Authentication bits SVD map trace into [0, 4095] Authentication bits 12 Proposed scheme - Authentication bits SVD map trace into [0, 4095] Authentication bits 12](http://slidetodoc.com/presentation_image/2ccbaa5f6e930261890374eef006d3ab/image-9.jpg)
Proposed scheme - Authentication bits SVD map trace into [0, 4095] Authentication bits 12 bits 9
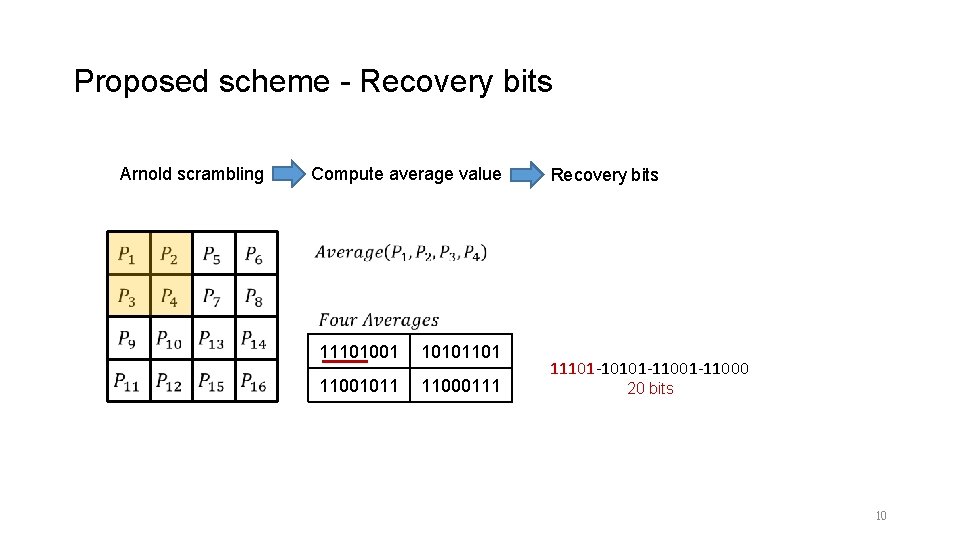
Proposed scheme - Recovery bits Arnold scrambling Compute average value 11101001 10101101 11001011 11000111 Recovery bits 11101 -10101 -11000 20 bits 10
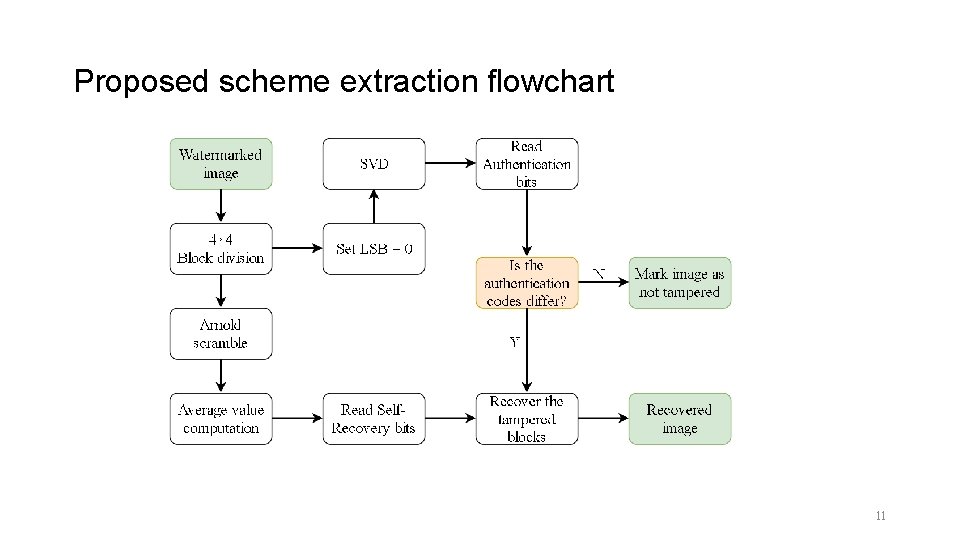
Proposed scheme extraction flowchart 11
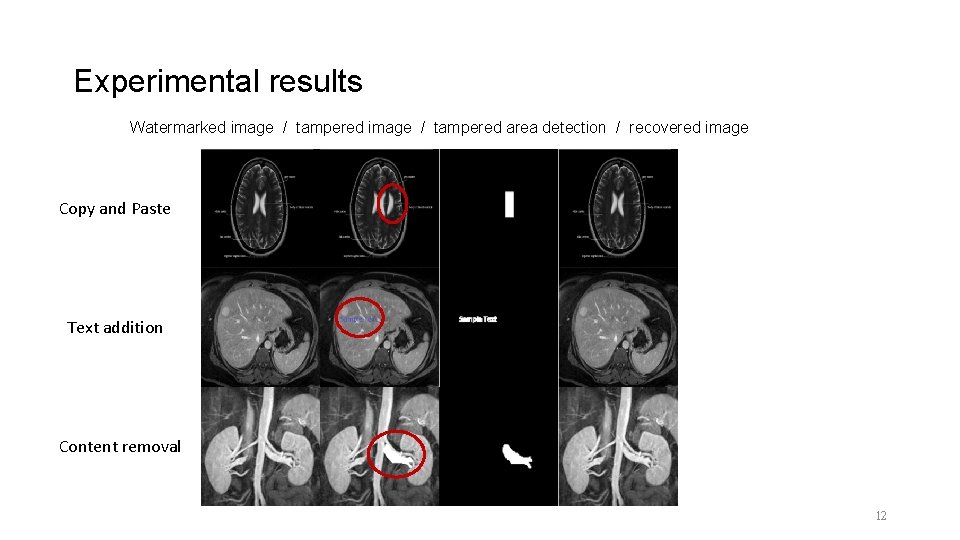
Experimental results Watermarked image / tampered area detection / recovered image Copy and Paste Text addition Content removal 12
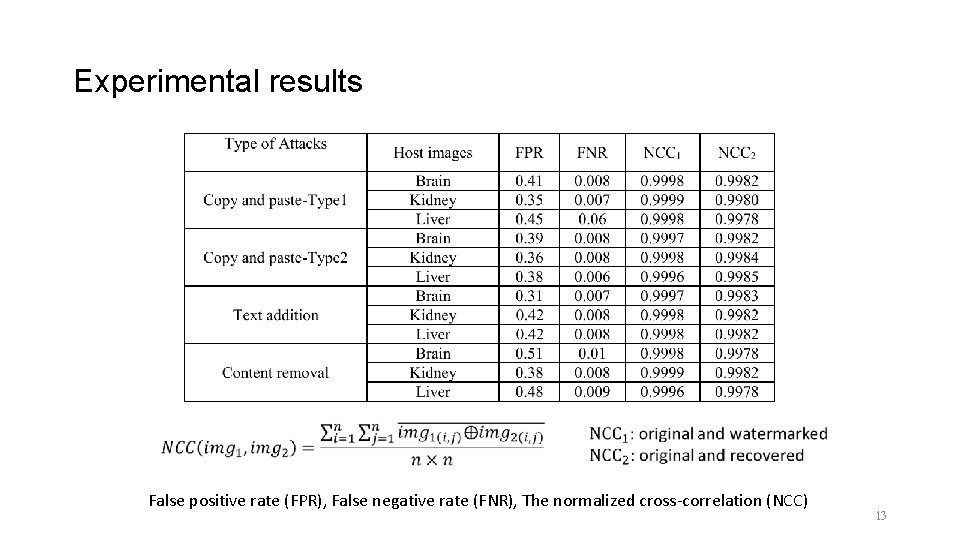
Experimental results False positive rate (FPR), False negative rate (FNR), The normalized cross-correlation (NCC) 13
![Experimental results [19] V. S. Dhole and N. N. Patil, ‘‘Self embedding fragile watermarking Experimental results [19] V. S. Dhole and N. N. Patil, ‘‘Self embedding fragile watermarking](http://slidetodoc.com/presentation_image/2ccbaa5f6e930261890374eef006d3ab/image-14.jpg)
Experimental results [19] V. S. Dhole and N. N. Patil, ‘‘Self embedding fragile watermarking for image tampering detection and image recovery using self recovery blocks, ’’ in Proc. Int. Conf. Comput. Commun. Control Autom. (ICCUBEA), Feb. 2015, pp. 752– 757. [20] Patra and J. C. Patra, ‘‘Crt-based fragile self-recovery watermarking scheme for image authentication and recovery, ’’ in Proc. IEEE Int. Symp. Intell. Signal Process. Commun. Syst. (ISPACS), Nov. 2012, pp. 430– 435. [27] R. O. Preda, ‘‘Self-recovery of unauthentic images using a new digital watermarking approach in the wavelet domain, ’’ in Proc. 10 th Int. Conf. IEEE Commun. (COMM), May 2014, pp. 1– 4. [28] M. El’Arbi and C. Ben Amar, ‘‘Image authentication algorithm with recovery capabilities based on neural networks in the DCT domain, ’’ IET Image Process. , vol. 8, no. 11, pp. 619– 626, 2014. 14
Conclusions The proposed scheme effectively prevents copy and paste attack, content removal attack and text addition attack. Compared with other papers, tamper localization and recovered PSNR has better performance. 15
- Slides: 15