Section 4 Network Security Topics Enterprise Network Architecture
- Slides: 15
Section 4: Network Security Topics Enterprise Network Architecture
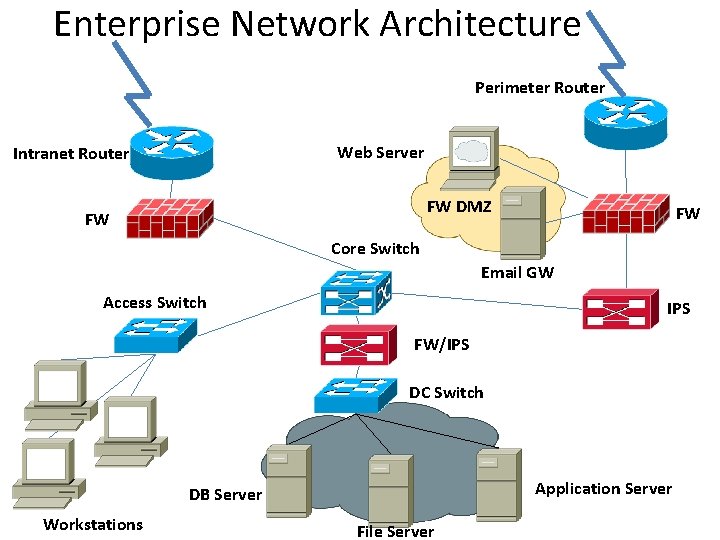
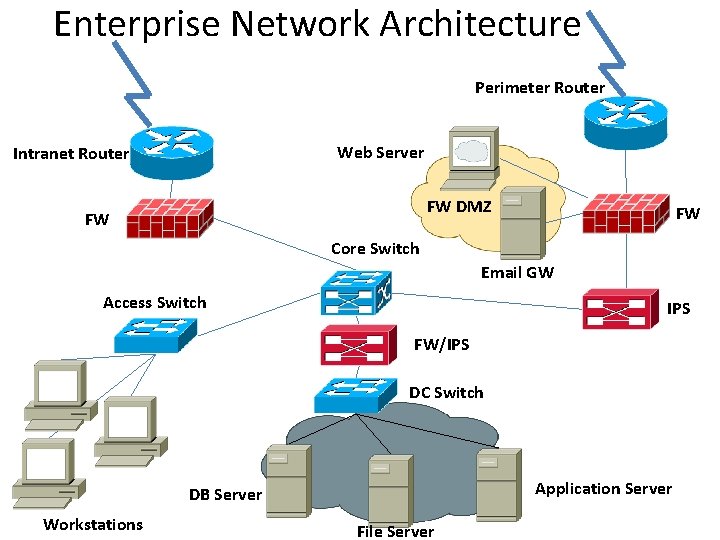
Enterprise Network Architecture Perimeter Router Web Server Intranet Router FW DMZ FW FW Core Switch Email GW Access Switch IPS FW/IPS DC Switch Application Server DB Server Workstations File Server
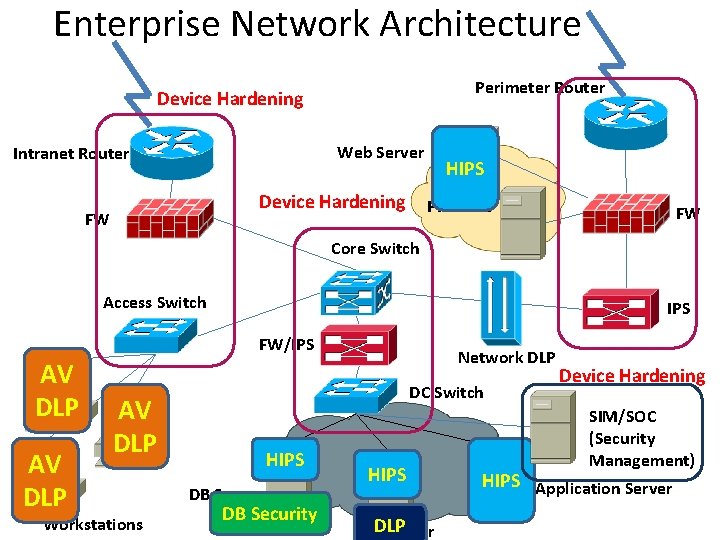
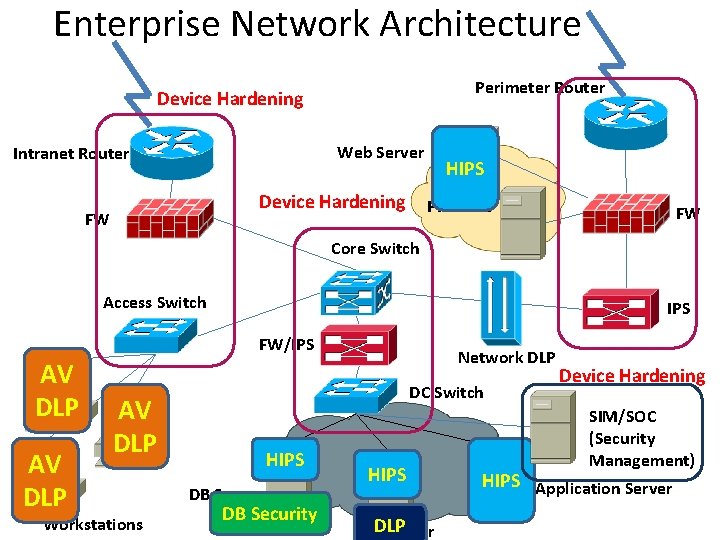
Enterprise Network Architecture Perimeter Router Device Hardening Web Server Intranet Router Device Hardening FW HIPS FW DMZ FW Core Switch Access Switch IPS FW/IPS AV DLP DC Switch AV DLP Workstations Network DLP HIPS DB Server DB Security HIPS File. DLP Server Device Hardening SIM/SOC (Security Management) HIPS Application Server
4. 2. 8 Vulnerability Assessment Scanner • A vulnerability scanner is a computer program designed to assess computers, computer systems, networks or applications for weaknesses. • While functionality varies between different types of vulnerability scanners, they share a common, core purpose of enumerating the vulnerabilities present in one or more targets. • Vulnerability scanners are a core technology component of vulnerability management.
Vulnerability Assessment Scanner • A vulnerability scanner can be used to conduct network reconnaissance, which is typically carried out by a remote attacker attempting to gain information or access to a network on which it is not authorized or allowed. • Network reconnaissance is increasingly used to exploit network standards and automated communication methods. • The aim is to determine what types of computers are present, along with additional information about those computers— such as the type and version of the operating system. • This information can be analyzed for known or recently discovered vulnerabilities that can be exploited to gain access to secure networks and computers.
4. 2. 9 Web & Application Security • Web application security is a branch of information security that deals specifically with security of websites and web applications • Application security encompasses measures taken throughout the application's life-cycle to prevent exceptions in the security policy of an application or the underlying system (vulnerabilities) through flaws in the design, development, deployment, upgrade, or maintenance of the application
Web & Application Security • The majority of web application attacks occur through cross-site scripting (XSS) and SQL injection attacks which typically result from flawed coding, and failure to sanitize input to and output from the web application
4. 2. 10 Database Security • Database security is the system, processes, and procedures that protect a database from unintended activity • Unintended activity can be categorized as authenticated misuse, malicious attacks or inadvertent mistakes made by authorized individuals or processes • Databases provide many layers and types of information security: – – – Access control Auditing Authentication Encryption Integrity controls
4. 2. 11 Security Operations Center (SOC) • A security operations center (SOC) is an Information Security function within the company or of separate organization that delivers IT security services • It attempts to detect unauthorized access in any form to prevent and manage security related incidents using processes and procedures • The mission is risk management through centralized analysis using the combined resources consisting of personnel, dedicated hardware and specialized software • Typically, these systems operate constantly. These resources offer continuous events monitoring and risk analysis to detect intrusion to guarantee protection against it
Security Operations Center (SOC) • The SOC consists of monitoring and analyzing all types of systems, devices, or applications events such as users activities, firewall activity, Intrusion Detection System (IDS/IPS) activity, antivirus activity, individual vulnerabilities, etc. • SOC Services – – – – Proactive analysis & system management Security device management Reporting Security alert DDo. S mitigation Security assessment Technical assistance
4. 2. 12 Secure Remote Access & VPNs • Employees may want to access the corporate network from a remote location – Email – Fileserver – Other corporate network resources • VPN connections terminate into a firewall or secure remote access server solution • Virtual Private Networks (VPNs) may be established to connect to remote sites (site-tosite VPNs) within the intranet
4. 2. 13 Penetration Testing • A penetration test, occasionally pentest, is a method of evaluating the security of a computer system or network by simulating an attack from a malicious source, known as a Black Hat Hacker, or Cracker. • The process involves an active analysis of the system for any potential vulnerabilities that could result from poor or improper system configuration, both known and unknown hardware or software flaws, or operational weaknesses in process or technical countermeasures.
Penetration Testing • This analysis is carried out from the position of a potential attacker and can involve active exploitation of security vulnerabilities. • Any security issues that are found will be presented to the system owner, together with an assessment of their impact, and often with a proposal for mitigation or a technical solution. • The intent of a penetration test is to determine the feasibility of an attack and the amount of business impact of a successful exploit, if discovered. • It is a component of a full security audit
4. 2. 14 Network Forensics • Network forensics is a sub-branch of digital forensics relating to the monitoring and analysis of computer network traffic for the purposes of information gathering, legal evidence or intrusion detection • Unlike other areas of digital forensics, network investigations deal with volatile and dynamic information. Network traffic is transmitted and then lost, so network forensics is often a proactive investigation.
Network Forensics Network forensics generally has two uses. • The first, relating to security, involves monitoring a network for anomalous traffic and identifying intrusions – An attacker might be able to erase all log files on a compromised host; network-based evidence might therefore be the only evidence available forensic analysis • The second form of Network forensics relates to law enforcement – In this case analysis of captured network traffic can include tasks such as reassembling transferred files, searching for keywords and parsing human communication such as emails or chat sessions