SECO Physical case Dimensions SECO is 7 by
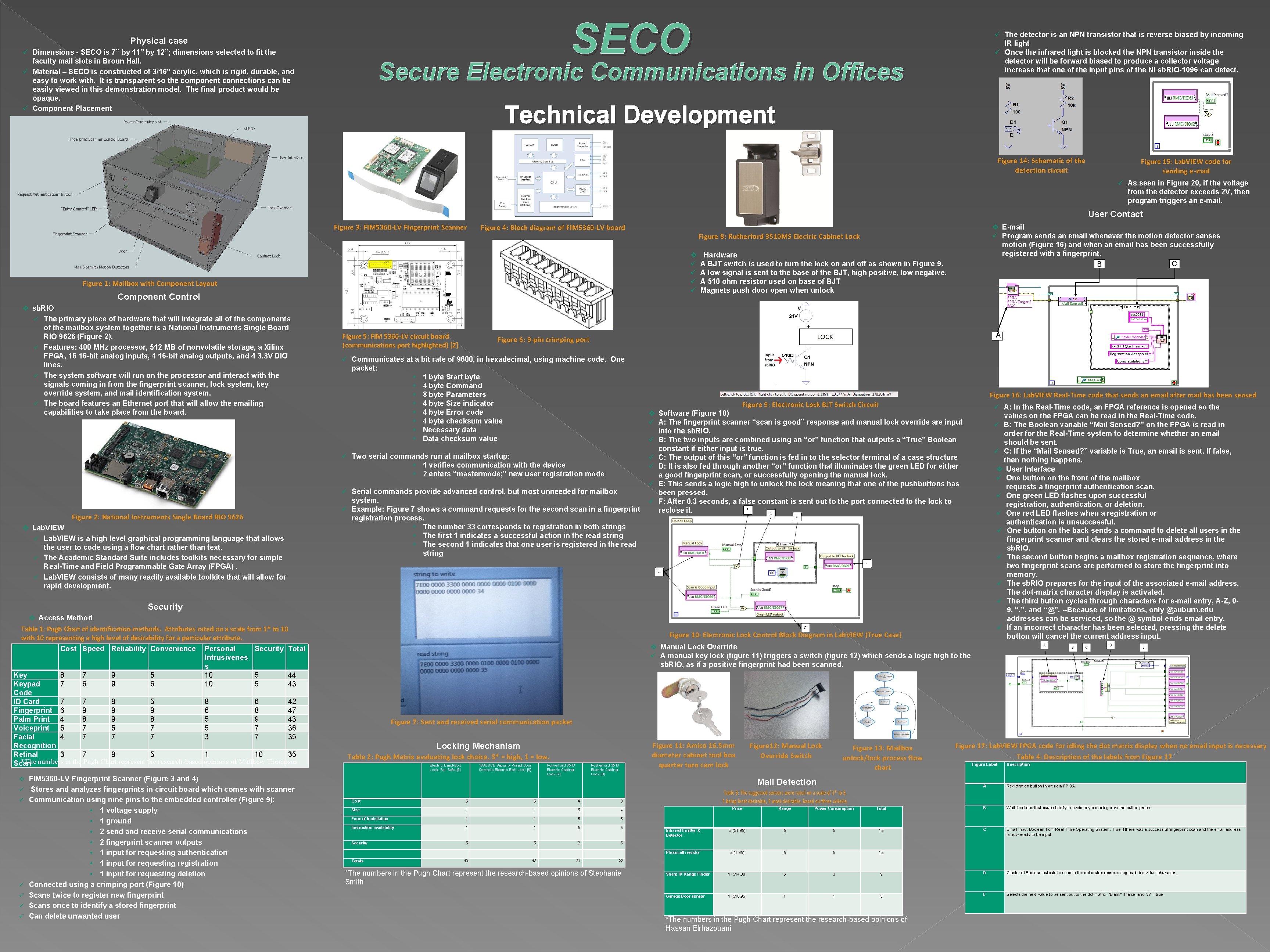
SECO Physical case ü Dimensions - SECO is 7” by 11” by 12”; dimensions selected to fit the faculty mail slots in Broun Hall. ü Material – SECO is constructed of 3/16” acrylic, which is rigid, durable, and easy to work with. It is transparent so the component connections can be easily viewed in this demonstration model. The final product would be opaque. ü Component Placement ü The detector is an NPN transistor that is reverse biased by incoming IR light ü Once the infrared light is blocked the NPN transistor inside the detector will be forward biased to produce a collector voltage increase that one of the input pins of the NI sb. RIO-1096 can detect. Secure Electronic Communications in Offices Technical Development Figure 14: Schematic of the detection circuit Figure 15: Lab. VIEW code for sending e-mail ü As seen in Figure 20, if the voltage from the detector exceeds 2 V, then program triggers an e-mail. User Contact Figure 3: FIM 5360 -LV Fingerprint Scanner Figure 4: Block diagram of FIM 5360 -LV board Figure 8: Rutherford 3510 MS Electric Cabinet Lock v ü ü Component Control v sb. RIO ü The primary piece of hardware that will integrate all of the components of the mailbox system together is a National Instruments Single Board RIO 9626 (Figure 2). ü Features: 400 MHz processor, 512 MB of nonvolatile storage, a Xilinx FPGA, 16 16 -bit analog inputs, 4 16 -bit analog outputs, and 4 3. 3 V DIO lines. ü The system software will run on the processor and interact with the signals coming in from the fingerprint scanner, lock system, key override system, and mail identification system. ü The board features an Ethernet port that will allow the emailing capabilities to take place from the board. Figure 5: FIM 5360 -LV circuit board (communications port highlighted) [2] v Lab. VIEW ü Lab. VIEW is a high level graphical programming language that allows the user to code using a flow chart rather than text. ü The Academic Standard Suite includes toolkits necessary for simple Real-Time and Field Programmable Gate Array (FPGA). ü Lab. VIEW consists of many readily available toolkits that will allow for rapid development. Hardware A BJT switch is used to turn the lock on and off as shown in Figure 9. A low signal is sent to the base of the BJT, high positive, low negative. A 510 ohm resistor used on base of BJT Magnets push door open when unlock A A Figure 6: 9 -pin crimping port ü Communicates at a bit rate of 9600, in hexadecimal, using machine code. One packet: • 1 byte Start byte • 4 byte Command • 8 byte Parameters • 4 byte Size indicator • 4 byte Error code • 4 byte checksum value • Necessary data • Data checksum value ü Two serial commands run at mailbox startup: • 1 verifies communication with the device • 2 enters “mastermode; ” new user registration mode Figure 2: National Instruments Single Board RIO 9626 v E-mail ü Program sends an email whenever the motion detector senses motion (Figure 16) and when an email has been successfully registered with a fingerprint. C C B ü Serial commands provide advanced control, but most unneeded for mailbox system. ü Example: Figure 7 shows a command requests for the second scan in a fingerprint registration process. • The number 33 corresponds to registration in both strings • The first 1 indicates a successful action in the read string • The second 1 indicates that one user is registered in the read string Figure 16: Lab. VIEW Real-Time code that sends an email after mail has been sensed Figure 9: Electronic Lock BJT Switch Circuit ü A: In the Real-Time code, an FPGA reference is opened so the values on the FPGA can be read in the Real-Time code. ü B: The Boolean variable “Mail Sensed? ” on the FPGA is read in order for the Real-Time system to determine whether an email should be sent. ü C: If the “Mail Sensed? ” variable is True, an email is sent. If false, then nothing happens. v User Interface ü One button on the front of the mailbox requests a fingerprint authentication scan. ü One green LED flashes upon successful registration, authentication, or deletion. ü One red LED flashes when a registration or authentication is unsuccessful. ü One button on the back sends a command to delete all users in the fingerprint scanner and clears the stored e-mail address in the sb. RIO. ü The second button begins a mailbox registration sequence, where two fingerprint scans are performed to store the fingerprint into memory. ü The sb. RIO prepares for the input of the associated e-mail address. The dot-matrix character display is activated. ü The third button cycles through characters for e-mail entry, A-Z, 09, “. ”, and “@”. --Because of limitations, only @auburn. edu addresses can be serviced, so the @ symbol ends email entry. ü If an incorrect character has been selected, pressing the delete button will cancel the current address input. v Software (Figure 10) ü A: The fingerprint scanner “scan is good” response and manual lock override are input into the sb. RIO. ü B: The two inputs are combined using an “or” function that outputs a “True” Boolean constant if either input is true. ü C: The output of this “or” function is fed in to the selector terminal of a case structure ü D: It is also fed through another “or” function that illuminates the green LED for either a good fingerprint scan, or successfully opening the manual lock. ü E: This sends a logic high to unlock the lock meaning that one of the pushbuttons has been pressed. ü F: After 0. 3 seconds, a false constant is sent out to the port connected to the lock to B reclose it. C E F A Security v Access Method Table 1: Pugh Chart of identification methods. Attributes rated on a scale from 1* to 10 with 10 representing a high level of desirability for a particular attribute. Cost Speed Reliability Convenience Personal Security Total Intrusivenes s Key 8 7 9 5 10 5 44 Keypad 7 6 9 6 10 5 43 Code ID Card 7 7 9 5 8 6 42 Fingerprint 6 9 9 9 6 8 47 Palm Print 4 8 9 8 5 9 43 Voiceprint 5 7 5 7 36 Facial 4 7 7 7 35 Recognition Retinal 3 7 9 5 1 10 35 *The numbers in the Pugh Chart represent the research-based opinions of Matthew Thompson Scan v ü ü ü FIM 5360 -LV Fingerprint Scanner (Figure 3 and 4) Stores and analyzes fingerprints in circuit board which comes with scanner Communication using nine pins to the embedded controller (Figure 9): • 1 voltage supply • 1 ground • 2 send and receive serial communications • 2 fingerprint scanner outputs • 1 input for requesting authentication • 1 input for requesting registration • 1 input for requesting deletion Connected using a crimping port (Figure 10) Scans twice to register new fingerprint Scans once to identify a stored fingerprint Can delete unwanted user D Figure 10: Electronic Lock Control Block Diagram in Lab. VIEW (True Case) v Manual Lock Override ü A manual key lock (figure 11) triggers a switch (figure 12) which sends a logic high to the sb. RIO, as if a positive fingerprint had been scanned. Figure 7: Sent and received serial communication packet Figure 11: Amico 16. 5 mm diameter cabinet tool box quarter turn cam lock Locking Mechanism Table 2: Pugh Matrix evaluating lock choice. 5* = high, 1 = low. Electric Dead-Bolt Lock, Fail Safe [5] 168 GSCD Security Wired Door Controls Electric Bolt Lock [6] Rutherford 3510 Electric Cabinet Lock [7] Rutherford 3513 Electric Cabinet Lock [8] Figure 12: Manual Lock Override Switch Figure 13: Mailbox unlock/lock process flow chart Mail Detection Cost 5 5 4 3 Size 1 1 5 4 Ease of Installation 1 1 5 5 Instruction availability 1 1 5 5 Security 5 5 2 5 Totals 13 13 21 Figure 17: Lab. VIEW FPGA code for idling the dot matrix display when no email input is necessary Table 4: Description of the labels from Figure 17 Figure Label Description A Registration button Input from FPGA. Price Range Power Consumption Total B Wait functions that pause briefly to avoid any bouncing from the button press. Infrared Emitter & Detector 5 ($1. 95) 5 5 15 C Email Input Boolean from Real-Time Operating System. True if there was a successful fingerprint scan and the email address is now ready to be input. Photocell resistor 5 (1. 95) 5 5 15 Sharp IR Range Finder 1 ($14. 00) 5 3 9 D Cluster of Boolean outputs to send to the dot matrix representing each individual character. Garage Door sensor 1 ($16. 95) 1 1 3 E Selects the next value to be sent out to the dot matrix. “Blank” if false, and “A” if true. 22 *The numbers in the Pugh Chart represent the research-based opinions of Stephanie Smith *The numbers in the Pugh Chart represent the research-based opinions of Hassan Elrhazouani
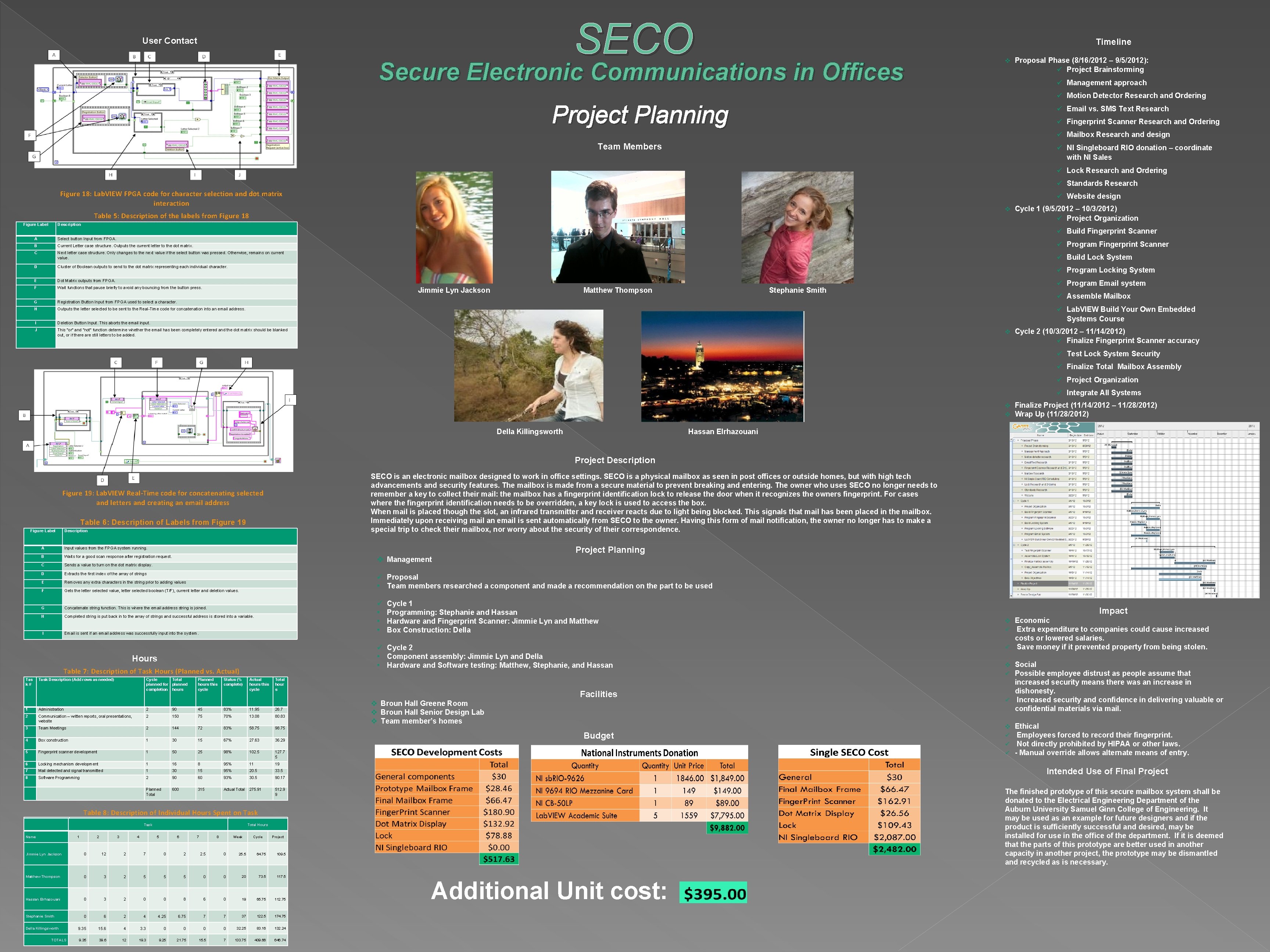
SECO User Contact Timeline Secure Electronic Communications in Offices v Proposal Phase (8/16/2012 – 9/5/2012): ü Project Brainstorming ü Management approach ü Motion Detector Research and Ordering Project Planning ü Email vs. SMS Text Research ü Fingerprint Scanner Research and Ordering ü Mailbox Research and design Team Members ü NI Singleboard RIO donation – coordinate with NI Sales ü Lock Research and Ordering ü Standards Research Figure 18: Lab. VIEW FPGA code for character selection and dot matrix interaction ü Website design v Table 5: Description of the labels from Figure 18 Figure Label Description Cycle 1 (9/5/2012 – 10/3/2012) ü Project Organization ü Build Fingerprint Scanner A Select button Input from FPGA. B Current Letter case structure. Outputs the current letter to the dot matrix. ü Program Fingerprint Scanner C Next letter case structure. Only changes to the next value if the select button was pressed. Otherwise, remains on current value. ü Build Lock System D Cluster of Boolean outputs to send to the dot matrix representing each individual character. ü Program Locking System E Dot Matrix outputs from FPGA. F Wait functions that pause briefly to avoid any bouncing from the button press. ü Program Email system G Registration Button Input from FPGA used to select a character. H Outputs the letter selected to be sent to the Real-Time code for concatenation into an email address. I Deletion Button Input. This aborts the email input. J This “or” and “not” function determine whether the email has been completely entered and the dot matrix should be blanked out, or if there are still letters to be added. Jimmie Lyn Jackson Matthew Thompson Stephanie Smith ü Assemble Mailbox ü Lab. VIEW Build Your Own Embedded Systems Course v Cycle 2 (10/3/2012 – 11/14/2012) ü Finalize Fingerprint Scanner accuracy ü Test Lock System Security ü Finalize Total Mailbox Assembly ü Project Organization ü Integrate All Systems v v Della Killingsworth Finalize Project (11/14/2012 – 11/28/2012) Wrap Up (11/28/2012) Hassan Elrhazouani Project Description SECO is an electronic mailbox designed to work in office settings. SECO is a physical mailbox as seen in post offices or outside homes, but with high tech advancements and security features. The mailbox is made from a secure material to prevent breaking and entering. The owner who uses SECO no longer needs to remember a key to collect their mail: the mailbox has a fingerprint identification lock to release the door when it recognizes the owners fingerprint. For cases where the fingerprint identification needs to be overridden, a key lock is used to access the box. When mail is placed though the slot, an infrared transmitter and receiver reacts due to light being blocked. This signals that mail has been placed in the mailbox. Immediately upon receiving mail an email is sent automatically from SECO to the owner. Having this form of mail notification, the owner no longer has to make a special trip to check their mailbox, nor worry about the security of their correspondence. Figure 19: Lab. VIEW Real-Time code for concatenating selected and letters and creating an email address Table 6: Description of Labels from Figure 19 Figure Label Description Project Planning A Input values from the FPGA system running. B Waits for a good scan response after registration request. C Sends a value to turn on the dot matrix display. D Extracts the first index of the array of strings E Removes any extra characters in the string prior to adding values F Gets the letter selected value, letter selected boolean (T/F), current letter and deletion values. G Concatenate string function. This is where the email address string is joined. H Completed string is put back in to the array of strings and successful address is stored into a variable. I Email is sent if an email address was successfully input into the system. v Management ü Proposal • Team members researched a component and made a recommendation on the part to be used ü • • • ü Cycle 2 • Component assembly: Jimmie Lyn and Della • Hardware and Software testing: Matthew, Stephanie, and Hassan Hours Table 7: Description of Task Hours (Planned vs. Actual) Tas k# Task Description (Add rows as needed) Cycle 1 Programming: Stephanie and Hassan Hardware and Fingerprint Scanner: Jimmie Lyn and Matthew Box Construction: Della Cycle Total planned for planned completion hours Planned hours this cycle Status (% complete) Actual hours this cycle Total hour s 1 Administration 2 90 45 83% 11. 95 26. 7 2 Communication – written reports, oral presentations, website 2 150 75 70% 13. 08 80. 83 3 Team Meetings 2 144 72 83% 58. 75 98. 75 4 Box construction 1 30 15 67% 27. 63 36. 29 5 Fingerprint scanner development 1 50 25 98% 102. 5 127. 7 5 6 Locking mechanism development 1 16 8 95% 11 19 7 Mail detected and signal transmitted 1 30 15 95% 20. 5 33. 5 8 Software Programming 2 90 60 93% 30. 5 90. 17 Planned Total 600 315 Actual Total 275. 91 512. 9 9 Facilities v Broun Hall Greene Room v Broun Hall Senior Design Lab v Team member’s homes Budget Name 1 Name 2 1 Jimmie Lyn. Jackson Jimmie Lyn 0 Matthew Thompson 0 Hassan Elrhazouani 0 Matthew Thompson 0 0 0 Della Killingsworth 1. 25 9. 35 0 TOTALS 1. 25 0 TOTALS 3 0 9. 35 2 2 0 6 15. 6 39. 6 Total Hours 2 2 1 0 2. 5 10. 5 2 7 5 4 12 2 8 2. 3 3. 3 4 0 5 3. 3 19. 3 0 0 0 21 4. 25 2 5 0 9. 25 2 0 0 1 6. 75 2. 5 0 0 21. 75 0 0 0 4 7 0 0 0 15. 5 7 25. 5 10 20 6 0 5. 5 7 0 7 Cycle 53. 5 73. 5 19 17. 5 Project 65. 75 97. 5 117. 5 93. 75 112. 75 85. 5 137. 75 6. 05 50. 91 99. 99 46. 55 275. 91 512. 99 37 32. 25 133. 75 122. 5 83. 16 409. 66 174. 75 132. 24 646. 74 Social Possible employee distrust as people assume that increased security means there was an increase in dishonesty. ü Increased security and confidence in delivering valuable or confidential materials via mail. v ü ü ü Ethical Employees forced to record their fingerprint. Not directly prohibited by HIPAA or other laws. - Manual override allows alternate means of entry. The finished prototype of this secure mailbox system shall be donated to the Electrical Engineering Department of the Auburn University Samuel Ginn College of Engineering. It may be used as an example for future designers and if the product is sufficiently successful and desired, may be installed for use in the office of the department. If it is deemed that the parts of this prototype are better used in another capacity in another project, the prototype may be dismantled and recycled as is necessary. 39. 25 64. 75 84 109. 5 46. 75 0 5. 5 Cycle Week 0 6 0 Week 8 2 8 0 8 7 1 0 10 7 6 1 0 0 6 5 0 2 2 5 4 2 3 Stephanie Smith 12 Total Hours 4 3 0 0 Hassan Elrhazouani 3 2 Task Economic Extra expenditure to companies could cause increased costs or lowered salaries. ü Save money if it prevented property from being stolen. v ü Intended Use of Final Project Table 8: Description of Individual Hours Spent on Task Impact Additional Unit cost:
- Slides: 2