SEC 316 Bit Locker Drive Encryption Russell Humphries
SEC 316: Bit. Locker™ Drive Encryption Russell Humphries Senior Product Manager – Window Vista Security
Disclaimer • This presentation contains preliminary information that may be changed substantially prior to final commercial release of the software described herein. • The information contained in this presentation represents the current view of Microsoft Corporation on the issues discussed as of the date of the presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information presented after the date of the presentation. • This presentation is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION. • Microsoft may have patents, patent applications, trademarks, copyrights, or other intellectual property rights covering subject matter in this presentation. Except as expressly provided in any written license agreement from Microsoft, the furnishing of this information does not give you any license to these patents, trademarks, copyrights, or other intellectual property. • © 2006 Microsoft Corporation. All rights reserved.
“Bit. Locker Drive Encryption provides stronger protection for data stored on your Windows Vista ™ systems – even when the system is in unauthorized hands or is running a different or attacking OS. Bit. Locker does this by utilizing full volume encryption; this prevents a thief who boots another OS or runs a software disk inspection tool from breaking Vista file and system protections or even the offline viewing of data files. ”
Bit. Locker Drive Encryption fully encrypts the entire Windows Vista volume. Designed specifically to prevent the unauthorized disclosure of data when it is at rest. Provides data protection on your Windows client systems, even when the system is in unauthorized hands. Designed to utilize a v 1. 2 Trusted Platform Module (TPM) for secure key storage and boot environment authentication Bit. Locker
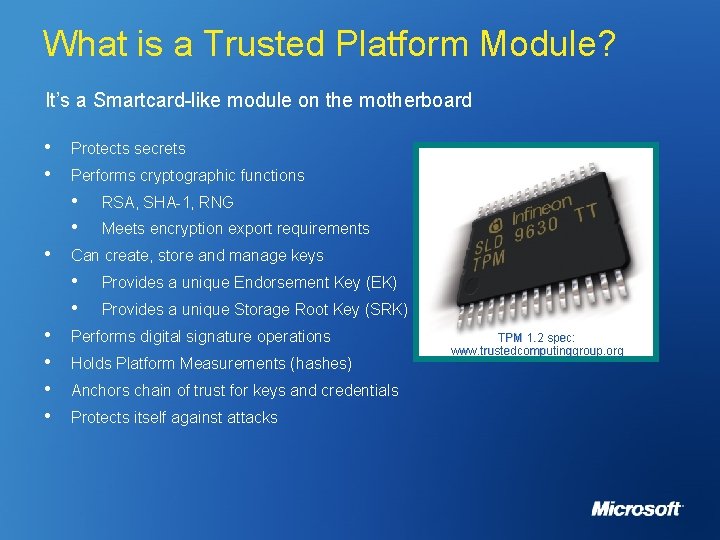
What is a Trusted Platform Module? It’s a Smartcard-like module on the motherboard • • Protects secrets Performs cryptographic functions • • • Meets encryption export requirements Can create, store and manage keys • • • RSA, SHA-1, RNG Provides a unique Endorsement Key (EK) Provides a unique Storage Root Key (SRK) Performs digital signature operations Holds Platform Measurements (hashes) Anchors chain of trust for keys and credentials Protects itself against attacks TPM 1. 2 spec: www. trustedcomputinggroup. org
Why use a TPM 1. 2 chip? • The TPM solves the ‘where do we put the encryption key? ’ problem • Hardware can be made to be robust against attacks • • • Certified to be tamper resistant Provides anti-hammering capabilities A TPM is an implementation of a Root-of-Trust • • Enables implementation of the Static Root of Trust Measurement Hardware based solution more secure than software one • Difficult to root trust in software that has to validate itself
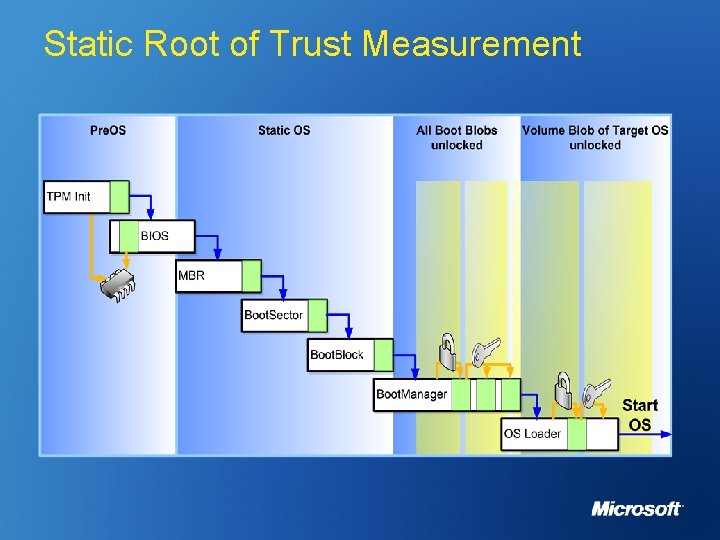
Static Root of Trust Measurement
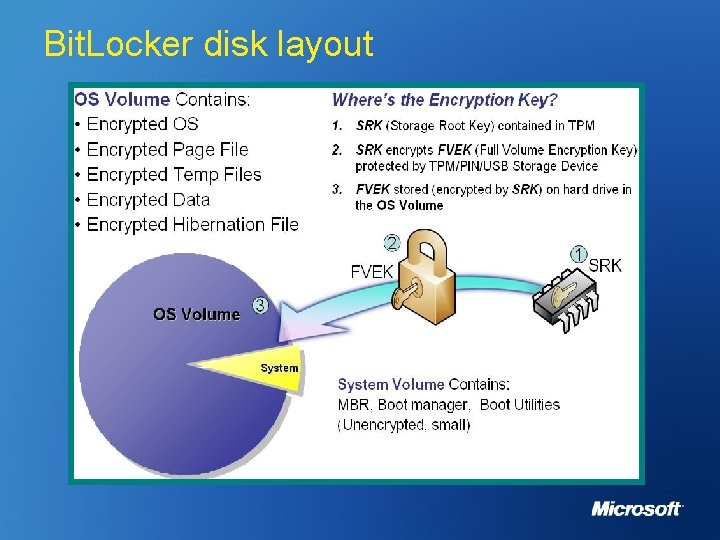
Bit. Locker disk layout
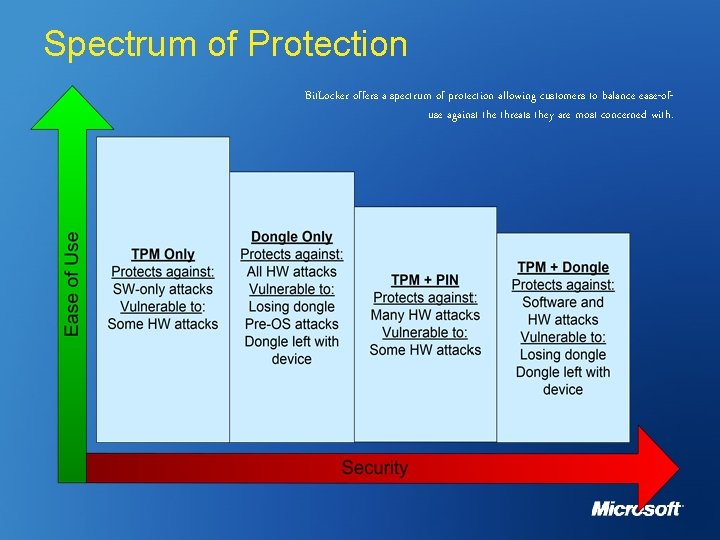
Spectrum of Protection Bit. Locker offers a spectrum of protection allowing customers to balance ease-ofuse against the threats they are most concerned with.
An integrated solution • Bit. Locker is integrated in WMI and Group Policy • • Bit. Locker automatically escrow keys and passwords into AD • • Enables customizable, automated deployment Centralized storage/management keys Recovery console built into the new Vista boot architecture • • Recovery can occur “in the field” Windows operation can continue as normal after a recovery
Further information? • Web Resources: • Specs & Whitepapers: • • TCG: • • www. microsoft. com/technet/windowsvista/security/bitlockr. mspx www. trustedcomputinggroup. org Bit. Locker™ Questions or Ideas: BDEInfo@microsoft. com

Ask The Experts Get Your Questions Answered You can find me at the Microsoft Ask the Experts area, located in the Exhibition Hall: Wednesday 15 November. Lunch Thursday 16 November 14. 45 – 15. 45



© 2006 Microsoft Corporation. All rights reserved. This presentation is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, IN THIS SUMMARY.
- Slides: 17