SCP A System Call Protector against Buffer Overflow

SCP: A System Call Protector against Buffer Overflow Attacks 先進防禦實驗室 國立中央大學 資訊 程系
Outline u u u u Introduction Attacking Method Related Work SCP System Design Experimental Result Conclusion Future Work 2
Introduction u u Buffer Overflow Attack • Easily launched • Huge amount of targets • Strongly damage • One of the most dangerous threats in the Internet Developing an efficient and effective approach becomes a critical and emergent issue. 3
Difficulty in Protection u Many countermeasures were proposed, but were defeated by new mutants. 4
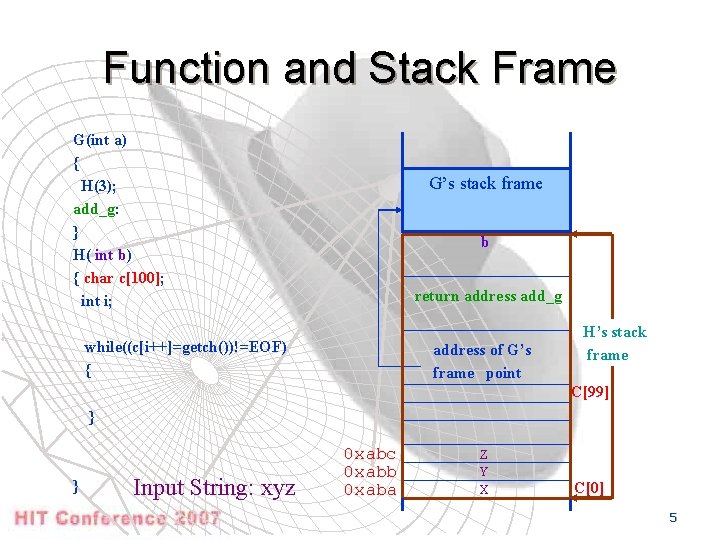
Function and Stack Frame G(int a) { H(3); add_g: } H( int b) { char c[100]; int i; G’s stack frame b return address add_g while((c[i++]=getch())!=EOF) { address of G’s frame point H’s stack frame C[99] } } Input String: xyz 0 xabc 0 xabb 0 xaba Z Y X C[0] 5
Stack Smashing Attack – Principle u Stack Smashing Attack • Overflow a return address to transfer program execution flow into injected code (shell code) 6
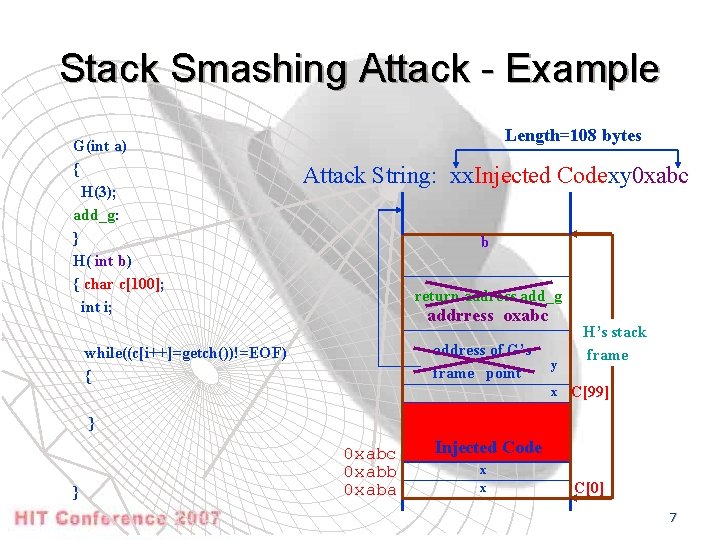
Stack Smashing Attack - Example G(int a) { H(3); add_g: } H( int b) { char c[100]; int i; Length=108 bytes Attack String: xx. Injected Codexy 0 xabc b return address add_g addrress oxabc address of G’s frame point while((c[i++]=getch())!=EOF) { y x H’s stack frame C[99] } } 0 xabc 0 xabb 0 xaba Injected Code x x C[0] 7
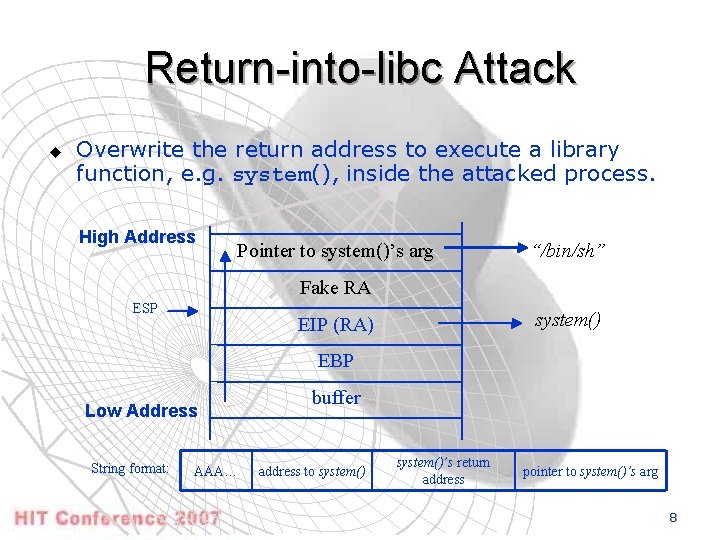
Return-into-libc Attack u Overwrite the return address to execute a library function, e. g. system(), inside the attacked process. High Address Pointer to system()’s arg “/bin/sh” Fake RA ESP system() EIP (RA) EBP Low Address String format: AAA… buffer address to system()’s return address pointer to system()’s arg 8
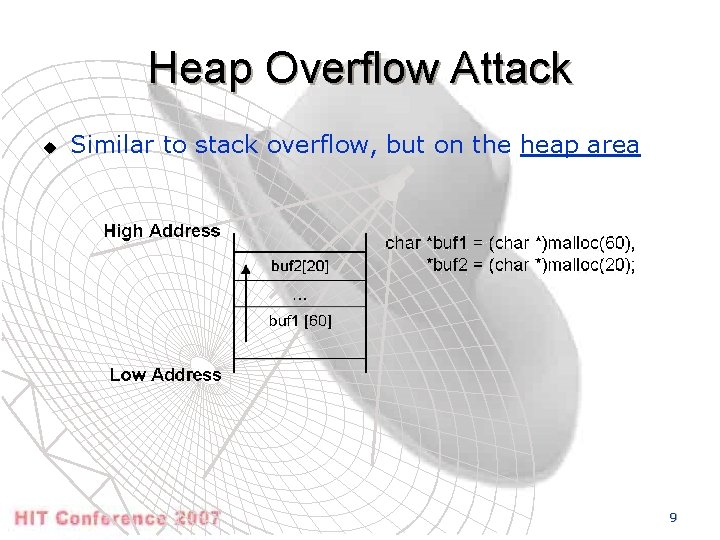
Heap Overflow Attack u Similar to stack overflow, but on the heap area 9
Other Mutants function pointer attack u Jump table attack u setjmp/longjmp attack u 10
Related Work u Some Countermeasures • Stack. Guard / Stack. Shield • Address Obfuscation (ASLR/Pa. X) • Exec Shield • Binary Obfuscation • Point. Guard™ • Instruction Set Randomization • RAD 11
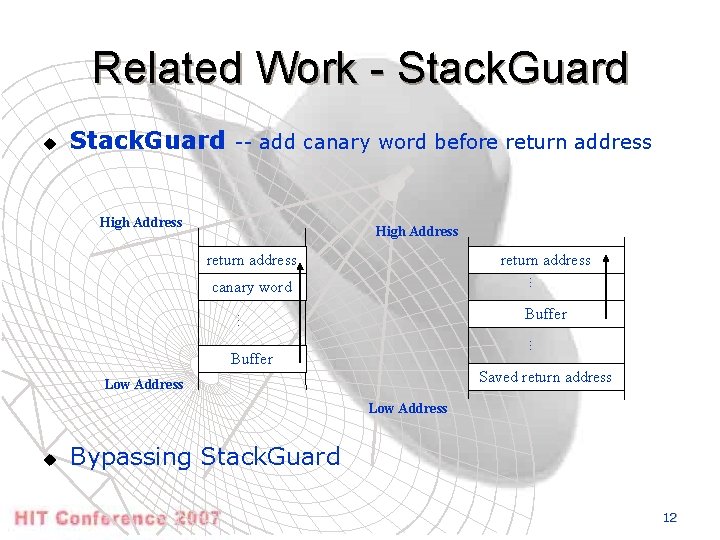
Related Work - Stack. Guard u Stack. Guard -- add canary word before return address High Address return address … canary word … Buffer Saved return address Low Address u Bypassing Stack. Guard 12
Related Work – ASLR/Pa. X u Address Obfuscation • Pa. X/ASLR project - Randomize the base address of memory regions -- Randomize the base address of stack/heap -- Randomize the starting address of dynamiclinked libraries -- Randomize the locations of routines and static data • • • Internal fragmentation problem Crash problem Derandomization Attack Local attack Non-relocatable code 13
Related Work – Bound Check u Bound Check • Bound Check for C Program • Require source code / recompile • Runtime overhead are huge - 4 x / 5 x when best case - 10 x general case - 100 x worst case 14
Related Work – Exec Shield u Exec Shield • Data/Stack section non-executable • Code section non-writable • Compatibility problem - ELF file format -- Add PT_GNU_STACK and PT_GNU_HEAP - Nested function - Recompile / porting - sigreturn() system call • Return into libc attack can be launched 15
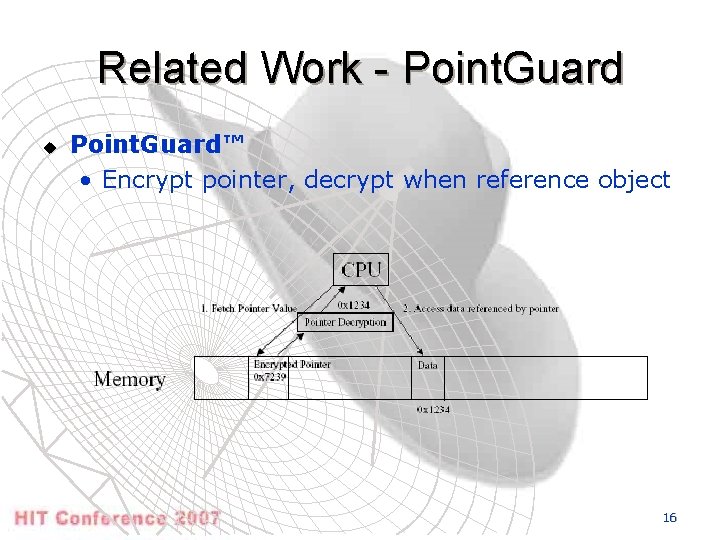
Related Work - Point. Guard u Point. Guard™ • Encrypt pointer, decrypt when reference object 16
Related Work - ISR u Instruction Set Randomization • Hardware solution, encrypt / decrypt CPU instructions Ø porting binaries 17
Related Work - RAD u RAD • Return Address Defender • Compiler solution • Push return address to RAR when prologue • Pop return address from RAR when eprologue Ø Need recompile 18
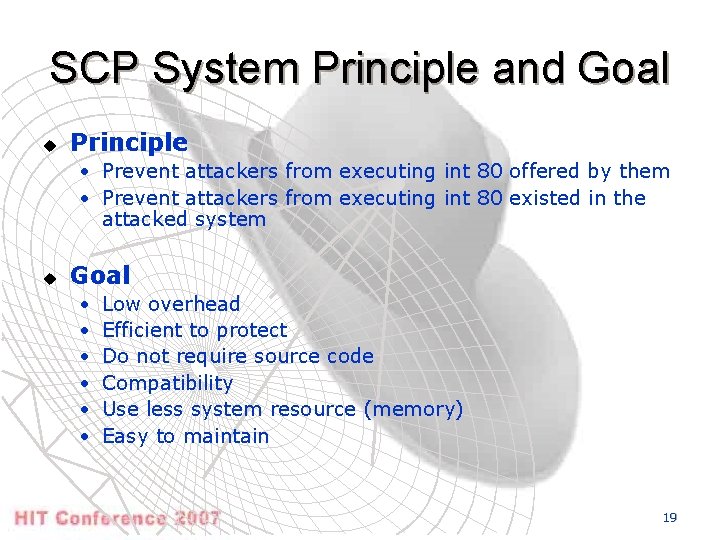
SCP System Principle and Goal u Principle • Prevent attackers from executing int 80 offered by them • Prevent attackers from executing int 80 existed in the attacked system u Goal • • • Low overhead Efficient to protect Do not require source code Compatibility Use less system resource (memory) Easy to maintain 19
Assumption u Assumption • Malicious code have to use system calls to damage an attacked system • Vulnerable programs use dynamic linked libraries 20
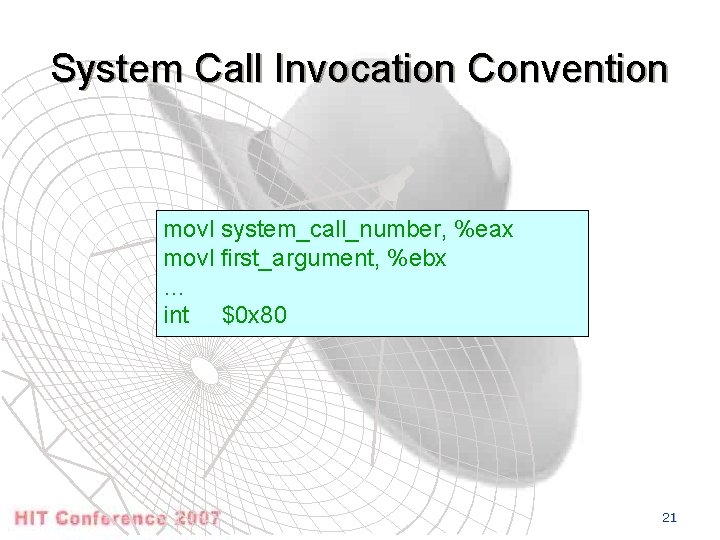
System Call Invocation Convention movl system_call_number, %eax movl first_argument, %ebx … int $0 x 80 21
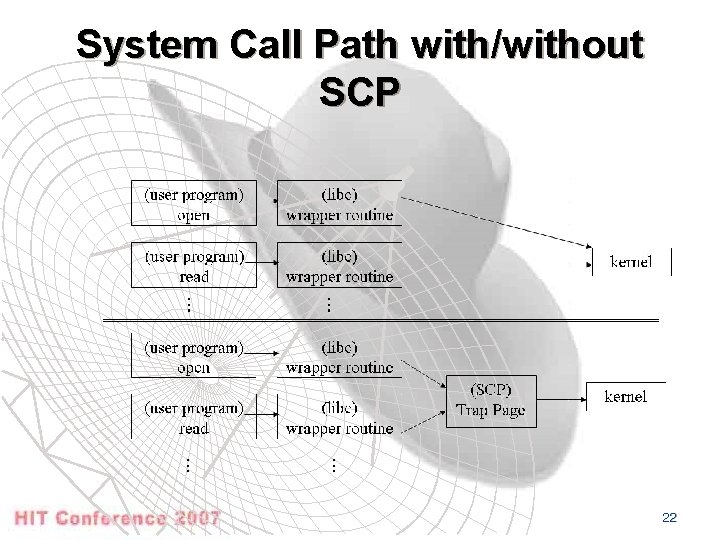
System Call Path with/without SCP 22
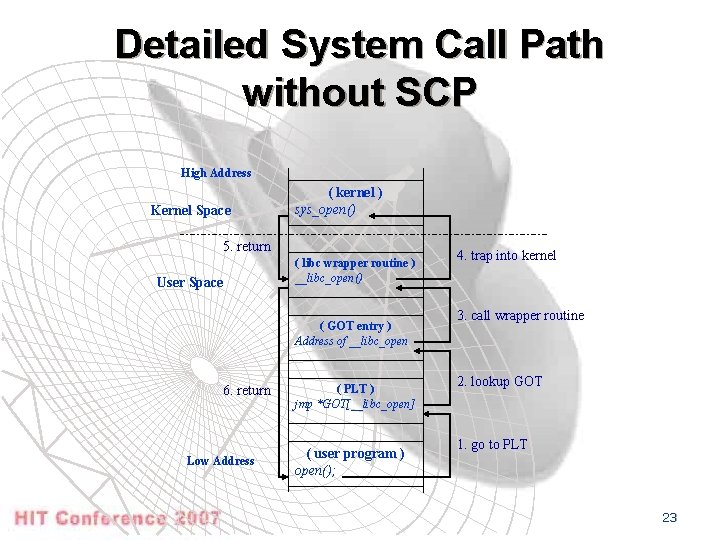
Detailed System Call Path without SCP High Address Kernel Space ( kernel ) sys_open() 5. return User Space ( libc wrapper routine ) __libc_open() ( GOT entry ) Address of __libc_open 6. return Low Address ( PLT ) jmp *GOT[__libc_open] ( user program ) open(); 4. trap into kernel 3. call wrapper routine 2. lookup GOT 1. go to PLT 23
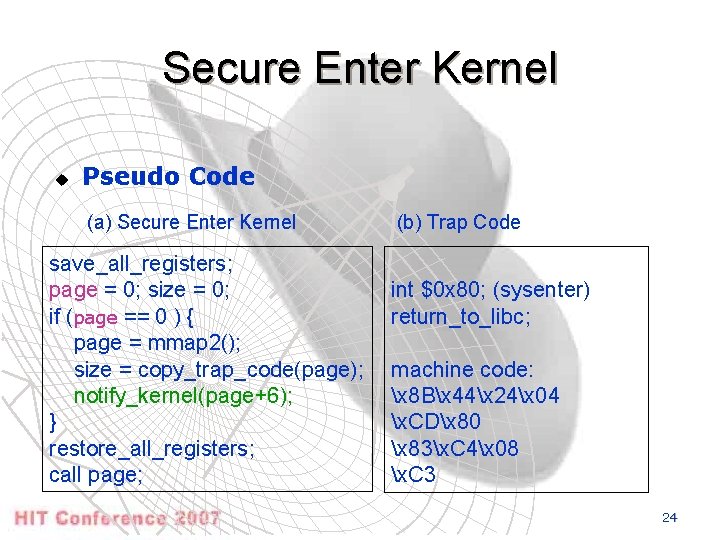
Secure Enter Kernel u Pseudo Code (a) Secure Enter Kernel save_all_registers; page = 0; size = 0; if (page == 0 ) { page = mmap 2(); size = copy_trap_code(page); notify_kernel(page+6); } restore_all_registers; call page; (b) Trap Code int $0 x 80; (sysenter) return_to_libc; machine code: x 8 Bx 44x 24x 04 x. CDx 80 x 83x. C 4x 08 x. C 3 24
Replacement • Use secure enter kernel to replace ALL sysenter (int $0 x 80) 25
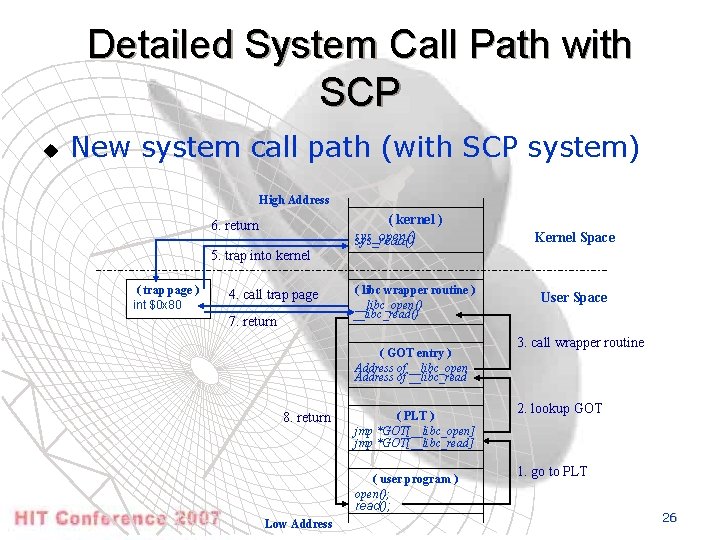
Detailed System Call Path with SCP u New system call path (with SCP system) High Address 6. return 5. trap into kernel ( trap page ) int $0 x 80 4. call trap page 7. return ( kernel ) sys_open() sys_read() ( libc wrapper routine ) __libc_open() __libc_read() ( GOT entry ) Address of __libc_open Address of __libc_read 8. return ( PLT ) jmp *GOT[__libc_open] jmp *GOT[__libc_read] ( user program ) open(); read(); Low Address Kernel Space User Space 3. call wrapper routine 2. lookup GOT 1. go to PLT 26
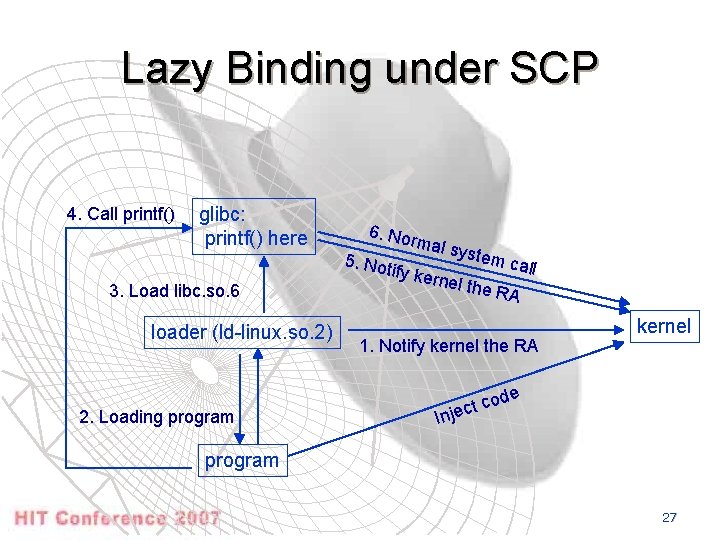
Lazy Binding under SCP 4. Call printf() glibc: printf() here 3. Load libc. so. 6 loader (ld-linux. so. 2) 2. Loading program 6. No rm al sys 5. Not ify ker tem c a nel th ll e RA 1. Notify kernel the RA t co c e j In kernel de program 27
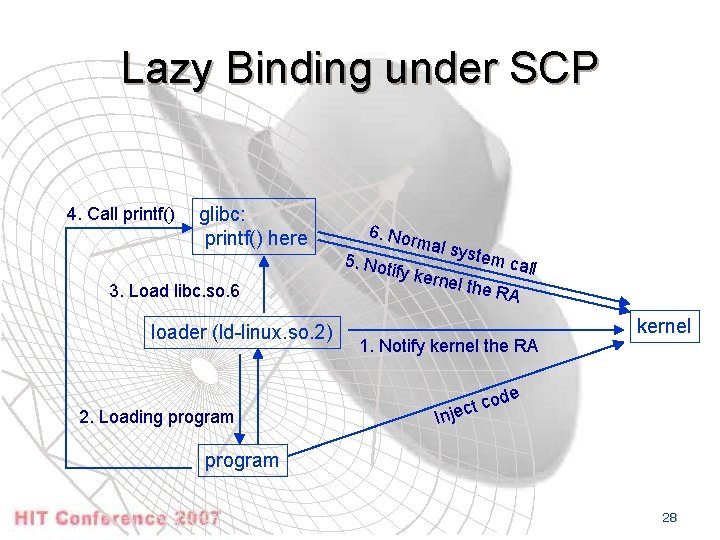
Lazy Binding under SCP 4. Call printf() glibc: printf() here 3. Load libc. so. 6 loader (ld-linux. so. 2) 2. Loading program 6. No rm al sys 5. Not ify ker tem c a nel th ll e RA 1. Notify kernel the RA t co c e j In kernel de program 28
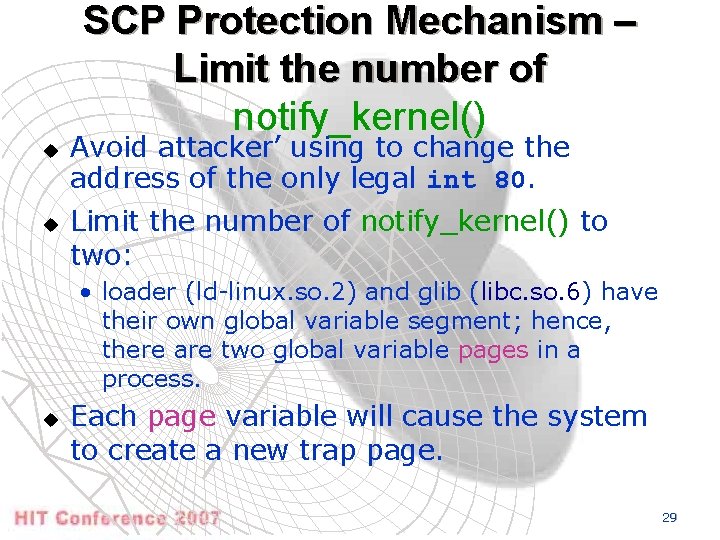
SCP Protection Mechanism – Limit the number of notify_kernel() u u Avoid attacker’ using to change the address of the only legal int 80. Limit the number of notify_kernel() to two: • loader (ld-linux. so. 2) and glib (libc. so. 6) have their own global variable segment; hence, there are two global variable pages in a process. u Each page variable will cause the system to create a new trap page. 29
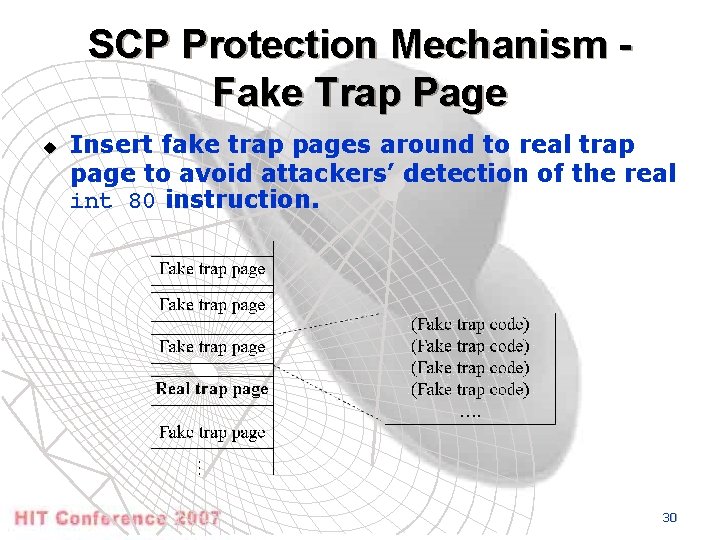
SCP Protection Mechanism Fake Trap Page u Insert fake trap pages around to real trap page to avoid attackers’ detection of the real int 80 instruction. 30
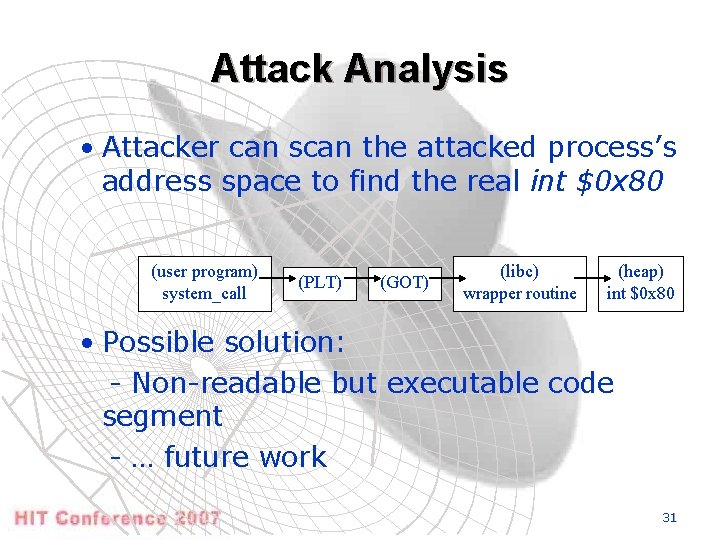
Attack Analysis • Attacker can scan the attacked process’s address space to find the real int $0 x 80 (user program) system_call (PLT) (GOT) (libc) wrapper routine (heap) int $0 x 80 • Possible solution: - Non-readable but executable code segment - … future work 31
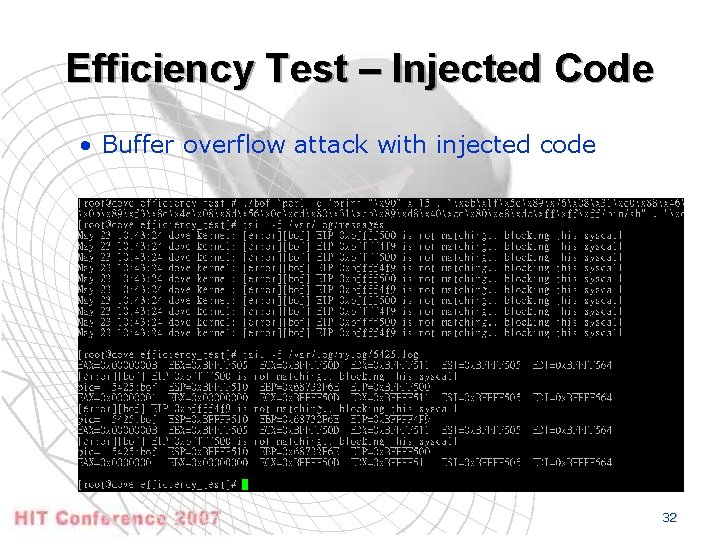
Efficiency Test – Injected Code • Buffer overflow attack with injected code 32
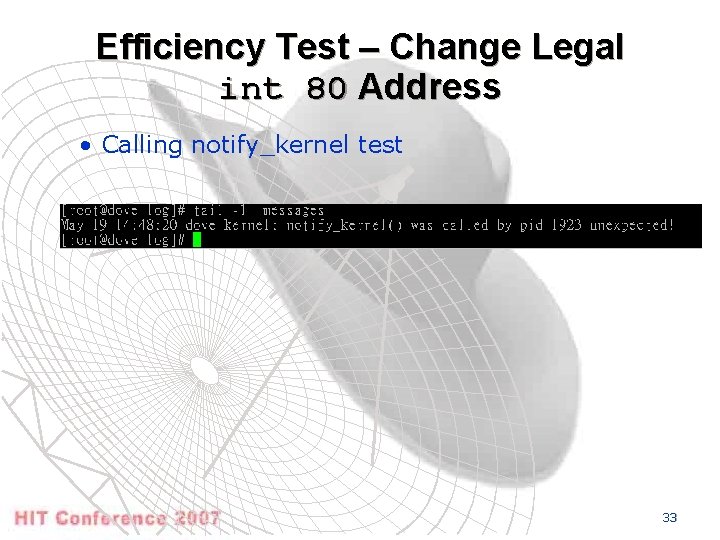
Efficiency Test – Change Legal int 80 Address • Calling notify_kernel test 33
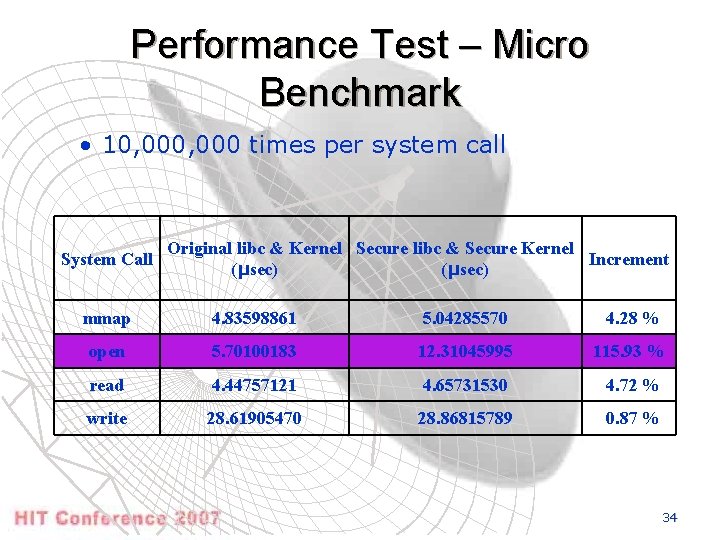
Performance Test – Micro Benchmark • 10, 000 times per system call System Call Original libc & Kernel Secure libc & Secure Kernel Increment (μsec) mmap 4. 83598861 5. 04285570 4. 28 % open 5. 70100183 12. 31045995 115. 93 % read 4. 44757121 4. 65731530 4. 72 % write 28. 61905470 28. 86815789 0. 87 % 34
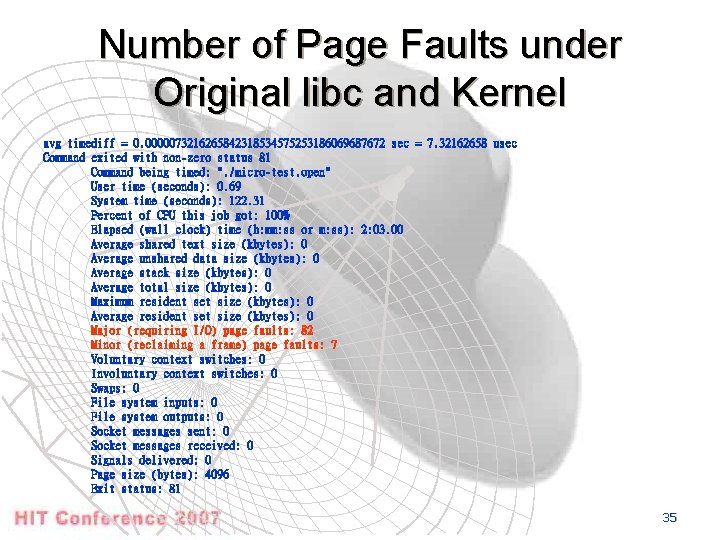
Number of Page Faults under Original libc and Kernel avg timediff = 0. 0000073216265842318534575253186069687672 sec = 7. 32162658 usec Command exited with non-zero status 81 Command being timed: ". /micro-test. open" User time (seconds): 0. 69 System time (seconds): 122. 31 Percent of CPU this job got: 100% Elapsed (wall clock) time (h: mm: ss or m: ss): 2: 03. 00 Average shared text size (kbytes): 0 Average unshared data size (kbytes): 0 Average stack size (kbytes): 0 Average total size (kbytes): 0 Maximum resident set size (kbytes): 0 Average resident set size (kbytes): 0 Major (requiring I/O) page faults: 82 Minor (reclaiming a frame) page faults: 7 Voluntary context switches: 0 Involuntary context switches: 0 Swaps: 0 File system inputs: 0 File system outputs: 0 Socket messages sent: 0 Socket messages received: 0 Signals delivered: 0 Page size (bytes): 4096 Exit status: 81 35
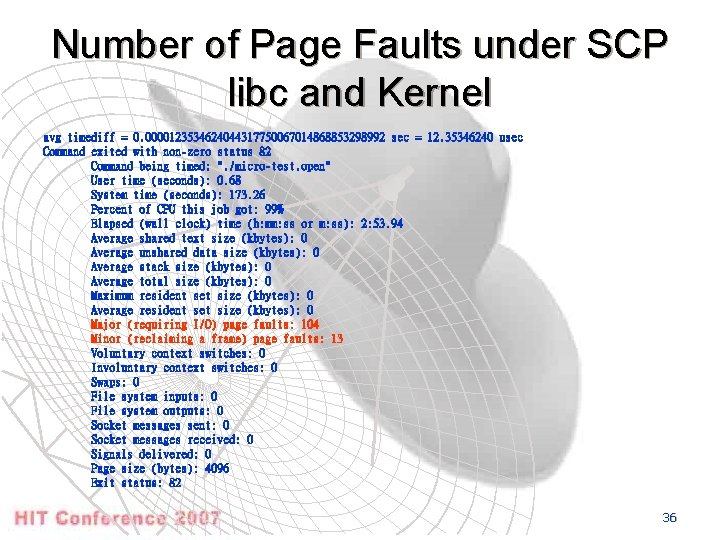
Number of Page Faults under SCP libc and Kernel avg timediff = 0. 0000123534624044317750067014868853298992 sec = 12. 35346240 usec Command exited with non-zero status 82 Command being timed: ". /micro-test. open" User time (seconds): 0. 68 System time (seconds): 173. 26 Percent of CPU this job got: 99% Elapsed (wall clock) time (h: mm: ss or m: ss): 2: 53. 94 Average shared text size (kbytes): 0 Average unshared data size (kbytes): 0 Average stack size (kbytes): 0 Average total size (kbytes): 0 Maximum resident set size (kbytes): 0 Average resident set size (kbytes): 0 Major (requiring I/O) page faults: 104 Minor (reclaiming a frame) page faults: 13 Voluntary context switches: 0 Involuntary context switches: 0 Swaps: 0 File system inputs: 0 File system outputs: 0 Socket messages sent: 0 Socket messages received: 0 Signals delivered: 0 Page size (bytes): 4096 Exit status: 82 36
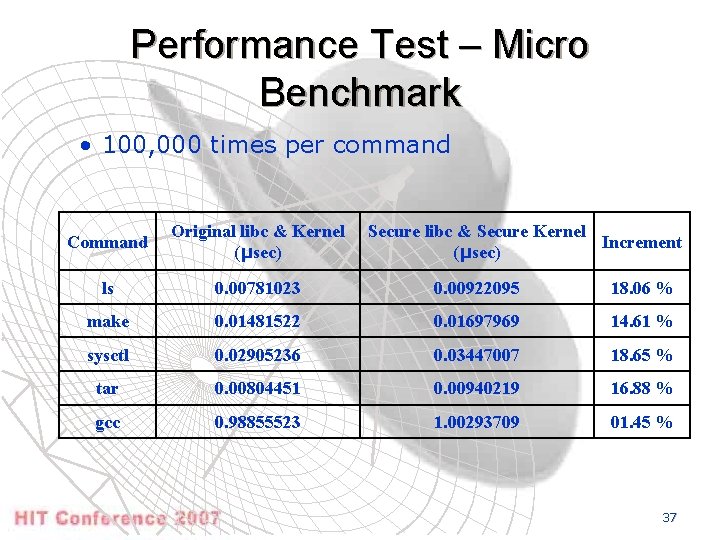
Performance Test – Micro Benchmark • 100, 000 times per command Command Original libc & Kernel (μsec) Secure libc & Secure Kernel Increment (μsec) ls 0. 00781023 0. 00922095 18. 06 % make 0. 01481522 0. 01697969 14. 61 % sysctl 0. 02905236 0. 03447007 18. 65 % tar 0. 00804451 0. 00940219 16. 88 % gcc 0. 98855523 1. 00293709 01. 45 % 37
Conclusion u We propose a new method to protect system calls by registering valid int 80 on premise • Low performance overhead • Protect programs against all known code injection style BOAs • No modification to source code or executable files is required • Compatible with existing systems and applications • Not increase the workload of program maintenance • Terminate attacked processes normally • Effective in defending local BO attacks 38
Future Work u More secure • Implement “executable but non-readable” region in segment section on i 386 • The NX Bit chip • AMD 64 CPU 39
u u Thanks Q&A 40
- Slides: 40