Schwerpunktseminar Systemtechnik Firewalls erstellt von Jrg Raiber Content
Schwerpunktseminar Systemtechnik Firewalls erstellt von Jörg Raiber
Content § § § § 9/10/2020 Introduction Dangers Attacks The Firewall (general) Firewall Techniques Firewall Concepts Computer Crime (statistics) 2
introduction § IT Security within the last 40 years – at the beginning security was controlled spatially (access to data processing center) and administrative (administrator, operator, user). – in the middle of the 70 th the connection of data terminals determines the spatially insularity. – the development of the Home-PC shook the protective wall. – the fast development of networking till today‘s WWW was cause for security system „Firewall“. 9/10/2020 3
The Internet – trigger of the danger § wherever we are, we are confronted with the internet. § more and more people are connected to the internet. § these days, companys and organisations have to connect to the internet and are attacked frequently. § we are not alone on the data highway and there is always the risk of incursion out of the net. 9/10/2020 4
dangers: incursions § incursions – most frequent attack – allows the invader to use a computer system as if he is the legal user. – possibilities of access: • Social Engineering • guessing of username and password • special methodes without knowledge of username und password. 9/10/2020 5
dangers: denial-of-service-attacks § denial-of-service attacks – aim: persons or groups should be embrassed to use their computers or special services. – means: overload of a running service • e. g. : flooding a werserver with requests – first significant attack was the „Morris Worm“. – 1999 e-mail-worm Melissa over MS-Outlook – feb. 2000 attack against Yahoo!, CNN, Amazon, e. Bay; recently W 32. Blaster and Sobig. F § distributed denial-of-service-attack – distributed attack over serveral computers 9/10/2020 6
dangers: information theft § attacker wants to get data. § attacker is able to steal data without breaking into the machine (redirection of target address). § active theft: – simulation of a valid computer or user. § passive theft: – tapping a network and waiting for interesting data. 9/10/2020 7
attacks: scanning § scanning of ip-addresses – query the active ip-addresses of a network by means of the „ping“ instruction. – allows to determine the internal network structure. § scanning of users – finding out users by using „finger“ command. § scanning of services – attacker scans serveral ports to find out which services are running. 9/10/2020 8
password-snooping and ip-masquerade § password-snooping – listening of username and password – e. g. there is a risk to use ftp or telnet, because username and password are transmitted in plain text. § ip-masquerade – adopting a foreign ip-adress, which is valid inside the network to protect. – the characteristic of tcp/ip that erveryone is able to adopt every ip-address increases this risk. 9/10/2020 9
hopping § hopping means the scipping from one remote host to another host inside the network to protect. § aim: using the possibilities of the remote host which are refused by direct connection. example 9/10/2020 10
![hopping: example Quelle: [Pohl 01] 9/10/2020 11 hopping: example Quelle: [Pohl 01] 9/10/2020 11](http://slidetodoc.com/presentation_image/179b4ac984f4c9702c66685da5334ec7/image-11.jpg)
hopping: example Quelle: [Pohl 01] 9/10/2020 11
ip-spoofing § the attacker sends packets with wrong source address. § the faked address is valid into the network to protect. § acknowledgement is not sent to attacker. why this? – attacker is able to absorb the acknowledgement packets – attacker is not interested in acknowledgement (denial-ofservice-attack) – attacker wants to injure others. 9/10/2020 12
ICMP-attacks § ICMP is a component of TCP/IP § is a service for interchanging error and information messages inside the network. § messages: – – – echo request (ping) echo response (response to ping) fragmentation needed (smaller packets, please) destination unreachable redirect … § faked commands may manipulate. 9/10/2020 13
The Firewall (general) § the firewall connects the unsafe network with the network to protect. § serveral components are scanning the communication data for: – communication type (FTP, telnet, HTTP, …) – communication participant – communication content (Java. Script, Active. X, etc. ) § limitates the communication according to the security policy. 9/10/2020 14
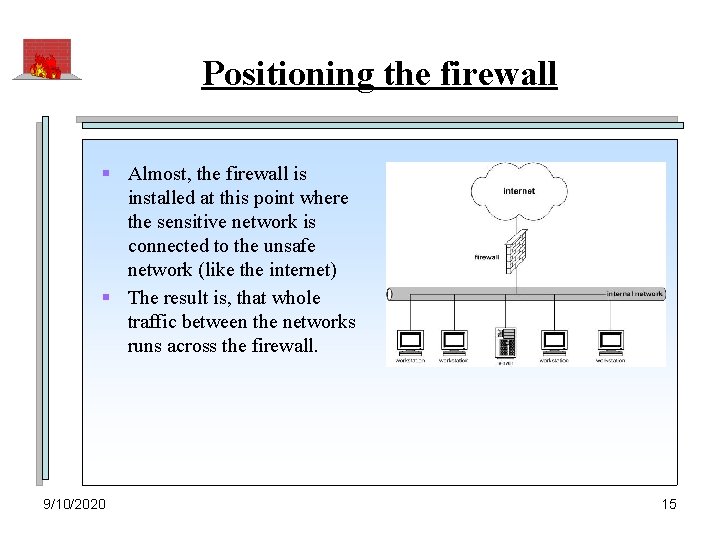
Positioning the firewall § Almost, the firewall is installed at this point where the sensitive network is connected to the unsafe network (like the internet) § The result is, that whole traffic between the networks runs across the firewall. 9/10/2020 15
General purposes of firewalls § Access control (network) – Which systems are allowed to communicate? § Access control (user) – Who is allowed to communicate? § Access control (data) – Which data can be sent? § Admission control – Which protocols and which services at which time? § § 9/10/2020 Isolationg of services Perpetuation of evidence and analysis Alerting Hiding of the internal network structure 16
Firewall-Techniques: Packet filter (1) § A packet filter routes IP-packets between the internal and the external network. § In addition to the normal routing-function, the packetfilter has to decide if he should transfer the packets, or not. § With this in mind there are specified packet filter roules which should help to decide. § Based on parsed packet headers the packet filter decides to transfer or block incoming packets. 9/10/2020 17
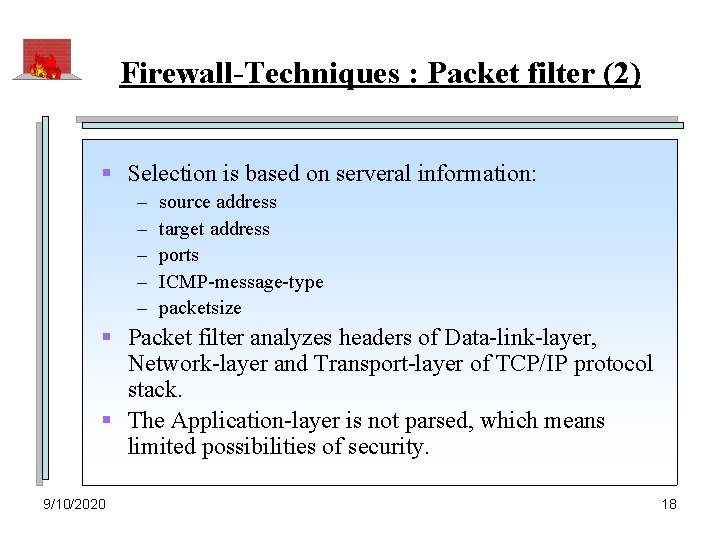
Firewall-Techniques : Packet filter (2) § Selection is based on serveral information: – – – source address target address ports ICMP-message-type packetsize § Packet filter analyzes headers of Data-link-layer, Network-layer and Transport-layer of TCP/IP protocol stack. § The Application-layer is not parsed, which means limited possibilities of security. 9/10/2020 18
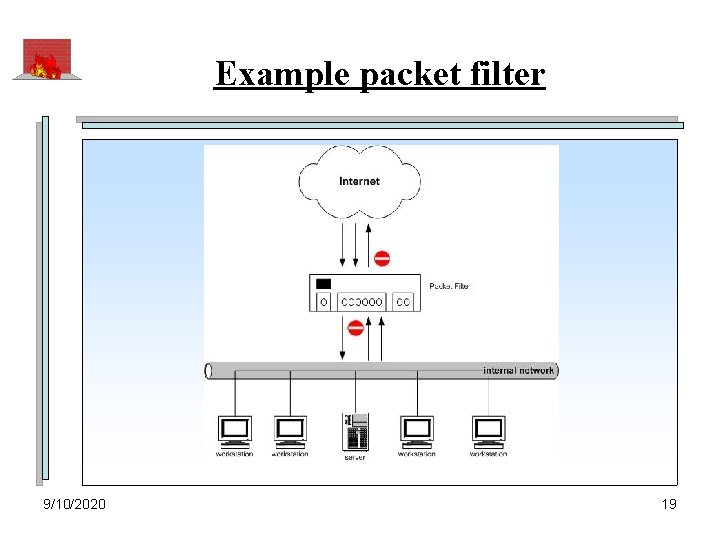
Example packet filter 9/10/2020 19
Filter roules § We are discerning between positive and negative roules: – positive: • It must explicitly be determined what should be allowd. All what is not determined is automatical forbidden. – negative: • Firstly, everything is allowed. With special entries we have to determine what should be forbidden. § Positive roules should be preferred, because forgotten prohibitions causes no risks. 9/10/2020 20
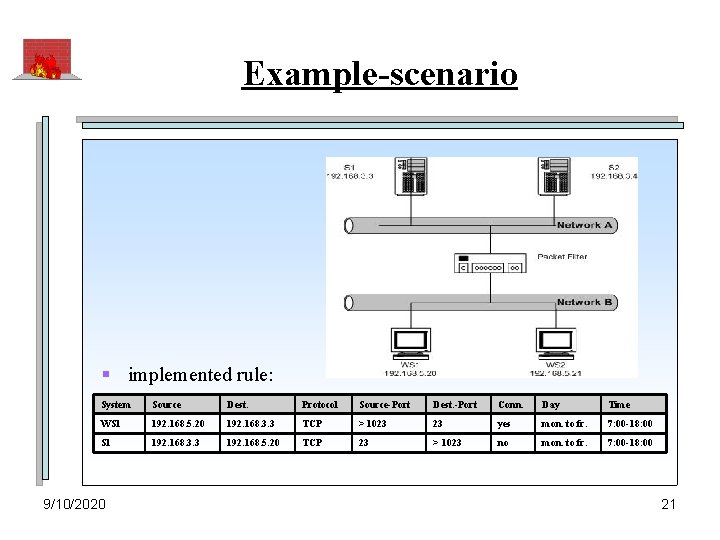
Example-scenario § implemented rule: System Source Dest. Protocol Source-Port Dest. -Port Conn. Day Time WS 1 192. 168. 5. 20 192. 168. 3. 3 TCP > 1023 23 yes mon. to fr. 7: 00 -18: 00 S 1 192. 168. 3. 3 192. 168. 5. 20 TCP 23 > 1023 no mon. to fr. 7: 00 -18: 00 9/10/2020 21
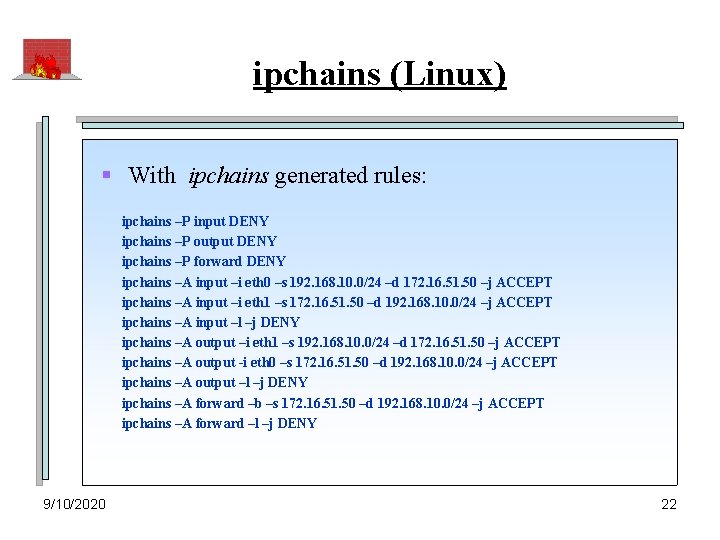
ipchains (Linux) § With ipchains generated rules: ipchains –P input DENY ipchains –P output DENY ipchains –P forward DENY ipchains –A input –i eth 0 –s 192. 168. 10. 0/24 –d 172. 16. 51. 50 –j ACCEPT ipchains –A input –i eth 1 –s 172. 16. 51. 50 –d 192. 168. 10. 0/24 –j ACCEPT ipchains –A input –l –j DENY ipchains –A output –i eth 1 –s 192. 168. 10. 0/24 –d 172. 16. 51. 50 –j ACCEPT ipchains –A output -i eth 0 –s 172. 16. 51. 50 –d 192. 168. 10. 0/24 –j ACCEPT ipchains –A output –l –j DENY ipchains –A forward –b –s 172. 16. 51. 50 –d 192. 168. 10. 0/24 –j ACCEPT ipchains –A forward –l –j DENY 9/10/2020 22

Application gateway with proxies (1) § Single-homed Application Gateway – one network interface only. – packets come and go across the same interface. – it consists the possibility to bypass the gateway. unsafe network sensitive network 9/10/2020 23
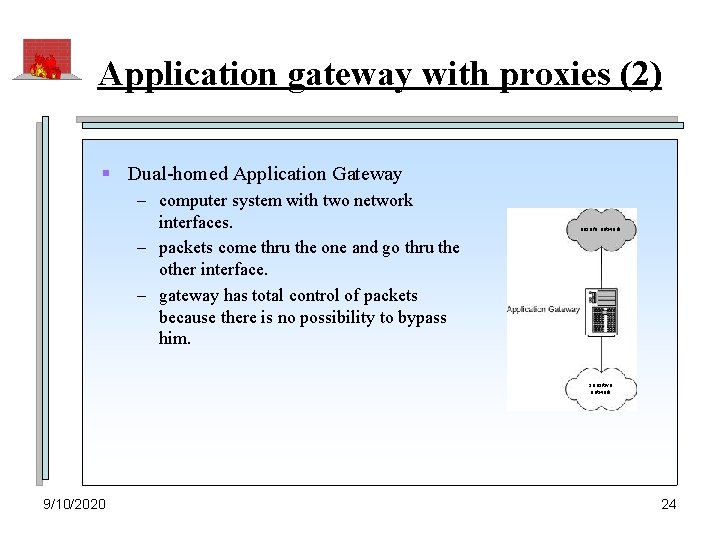
Application gateway with proxies (2) § Dual-homed Application Gateway – computer system with two network interfaces. – packets come thru the one and go thru the other interface. – gateway has total control of packets because there is no possibility to bypass him. unsafe network sensitive network 9/10/2020 24

Application gateway with proxies (3) § gateway decouples network logically and physikally. § gateway is ables to analyze the application layer. § configured as „dual-homed“, the gateway is the only computer system which is reachable from outside. Therefore he is extra worth to be protected. § this gateway is also named „Bastion“. § normally there are running one or servaral proxy services which manage communication substitutionally and transparently. § the proxies are able to estimate client requests for deciding, which requests they will leave out of consideration and which requests they will transfer. 9/10/2020 25
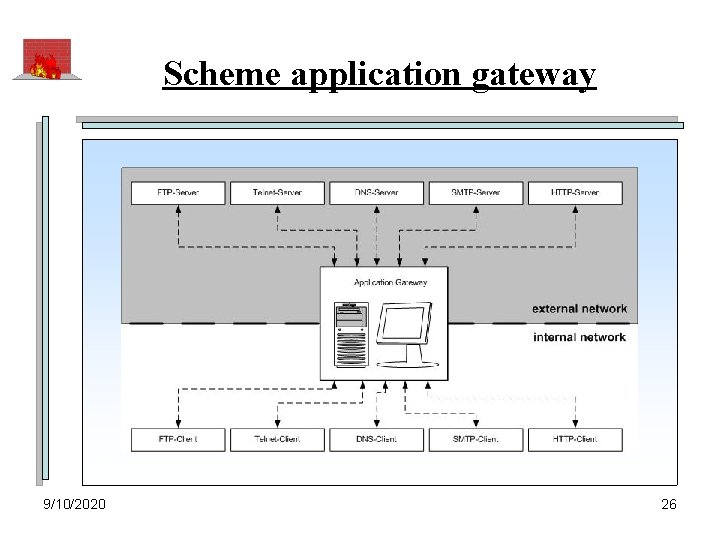
Scheme application gateway 9/10/2020 26
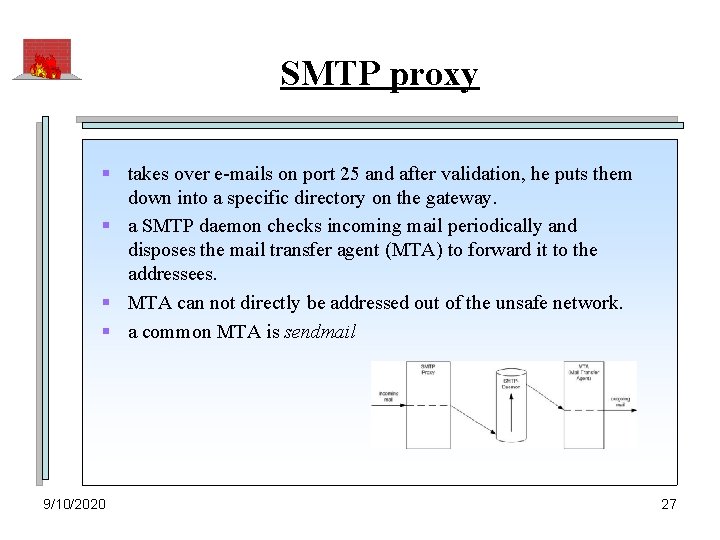
SMTP proxy § takes over e-mails on port 25 and after validation, he puts them down into a specific directory on the gateway. § a SMTP daemon checks incoming mail periodically and disposes the mail transfer agent (MTA) to forward it to the addressees. § MTA can not directly be addressed out of the unsafe network. § a common MTA is sendmail 9/10/2020 27
Telnet proxy § is responsible for telnet communication § connection establishment happens over port 23 of the gateway. § user must identify and authenticate with specification of destination. § depending on user data special rights can be assigned or detracted. § after identification and authentication, the proxy establishes the connection with destination. 9/10/2020 28
FTP proxy § is responsible for FTP connection § connection establishment happens over port 21 of the gateway. § user must identify and authenticate. § the FTP proxy disponses of some filter rules like: – command-filter ( cd: yes, del: no ) – data-filter ( *. jpg: yes, *. exe: no ) 9/10/2020 29

HTTP proxy § § is responsible for HTTP connection establishment happens over port 80. user-authentication is possible disponses of some filters like: – command-filter ( FTP? , SMTP? ) – data-filter ( e. g. defined URLs only ) – „content security“ ( applet-filter, malware-filter) 9/10/2020 30
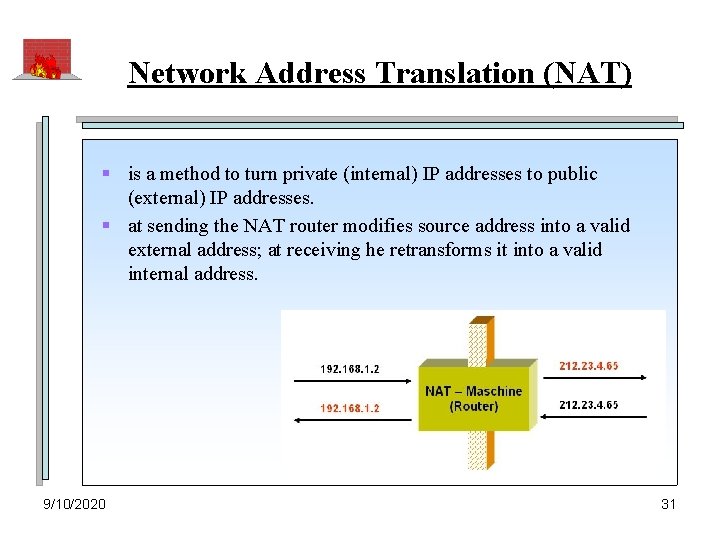
Network Address Translation (NAT) § is a method to turn private (internal) IP addresses to public (external) IP addresses. § at sending the NAT router modifies source address into a valid external address; at receiving he retransforms it into a valid internal address. 9/10/2020 31
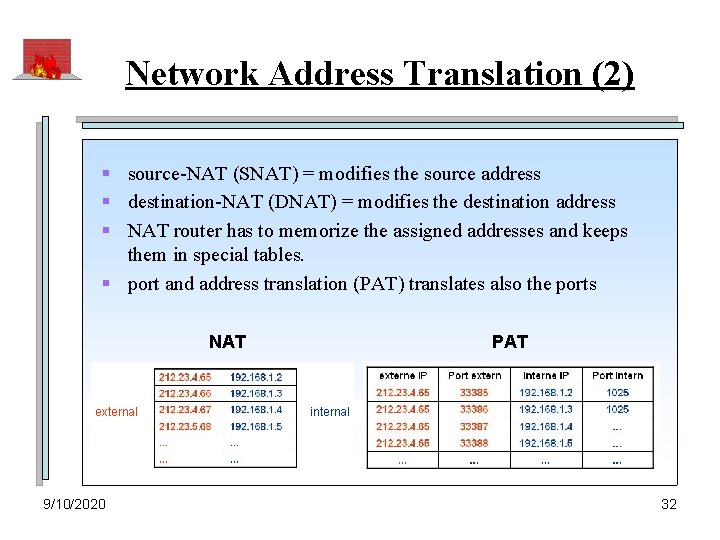
Network Address Translation (2) § source-NAT (SNAT) = modifies the source address § destination-NAT (DNAT) = modifies the destination address § NAT router has to memorize the assigned addresses and keeps them in special tables. § port and address translation (PAT) translates also the ports NAT external 9/10/2020 PAT internal 32
Network Address Translation (3) § field of application: – internetconnection of multiple computers with only one public IP address. – scimping on IP addresses (shortness) – protective function (only „NAT machine“ is visible) § security features: – control of outgoing traffic • all traffic goes thru NAT router. – control of incoming traffic • only incoming connections allowed which are initiated by the router. – internal network structure is hidden. 9/10/2020 33
firewall concepts (1) § exclusive use of packet filter: – allows and denys connection by checking source and destination address (MAC and IP). – limitatation of protocols (TCP, UDP, …) – limitation of ports and services – definition of timeslots – inadvisable for coupling sensitive network and internet. – exertion inside the intranet advisable. 9/10/2020 34
firewall concepts (2) § exclusive use of application gateways: – allows and denys connection by checking source IP address and destination IP address. – admission control on user level – limitation of protocols – limitation of services – definition of timeslots – limitation of commands, user data and files (application layer) – perpetuation of evidence and recording possible (logfile) – alerting of security management possible – … § inadvisable for coupling sensitive network and internet. § exertion inside the intranet advisable. 9/10/2020 35
firewall concepts (3) § combination of packet filter and und single-homed AG – two variations: • packet filter before AG (A) • packet filter behind AG (B) – A: • can be configured so that communication out of the unsave networks across the gateway only. • from the unsave network, only the gateway is visible. • the gateway adduces the most important security services. • caution: if an invader gets access to the gateway he may be capable to get access to all systems in the network. 9/10/2020 36
firewall concepts (4) – B: • can be configured so that communication out of the sensitive networks across the gateway only. • from the sensitive network, only the gateway is visible. • the gateway adduces the most important security services. • the application gateway must be extra resistant against attacks. § inadvisable for coupling sensitive network and internet. § might be used for separation of sensitive organisation departments inside the intranet. 9/10/2020 37
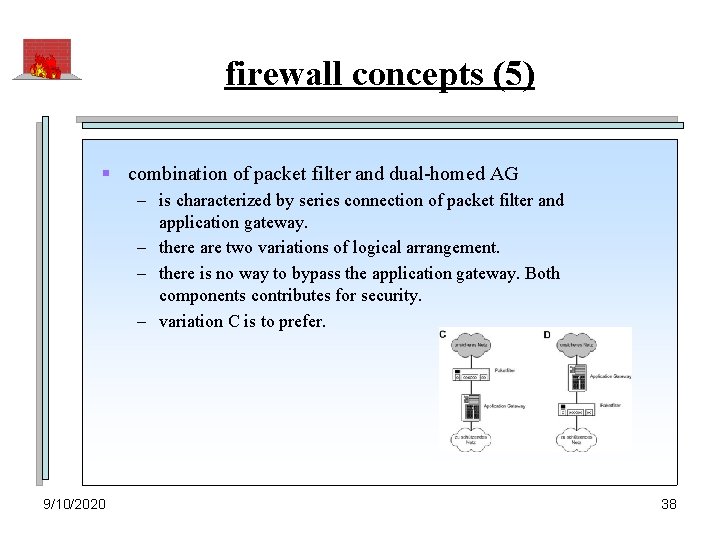
firewall concepts (5) § combination of packet filter and dual-homed AG – is characterized by series connection of packet filter and application gateway. – there are two variations of logical arrangement. – there is no way to bypass the application gateway. Both components contributes for security. – variation C is to prefer. 9/10/2020 38
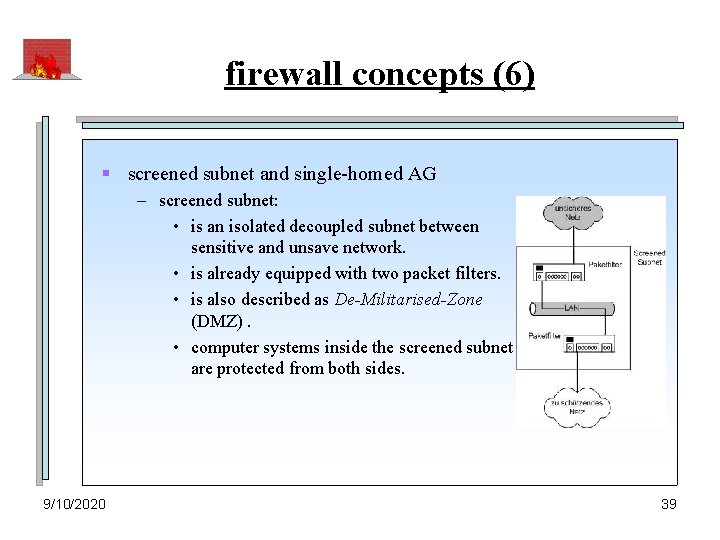
firewall concepts (6) § screened subnet and single-homed AG – screened subnet: • is an isolated decoupled subnet between sensitive and unsave network. • is already equipped with two packet filters. • is also described as De-Militarised-Zone (DMZ). • computer systems inside the screened subnet are protected from both sides. 9/10/2020 39
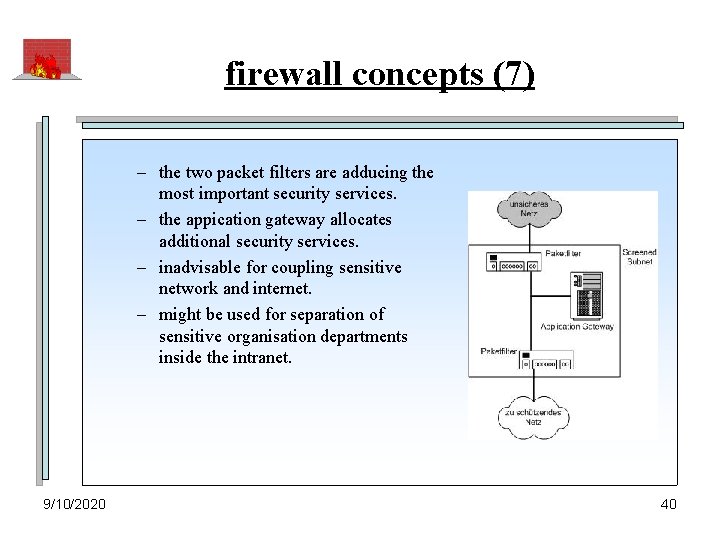
firewall concepts (7) – the two packet filters are adducing the most important security services. – the appication gateway allocates additional security services. – inadvisable for coupling sensitive network and internet. – might be used for separation of sensitive organisation departments inside the intranet. 9/10/2020 40
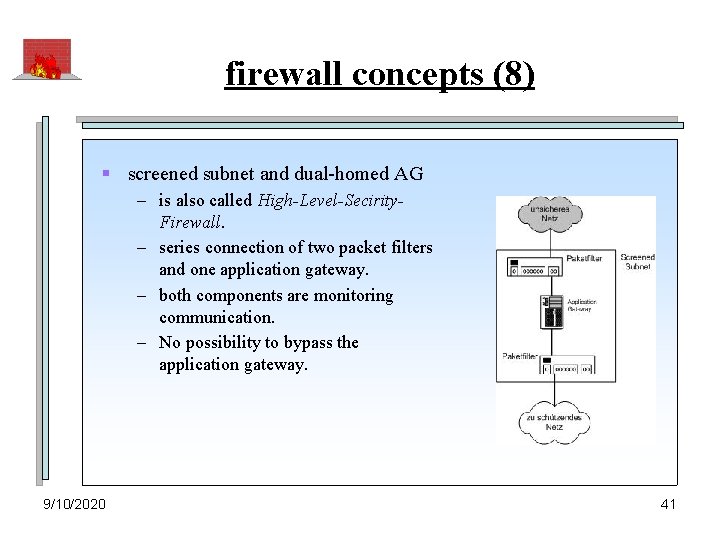
firewall concepts (8) § screened subnet and dual-homed AG – is also called High-Level-Secirity. Firewall. – series connection of two packet filters and one application gateway. – both components are monitoring communication. – No possibility to bypass the application gateway. 9/10/2020 41
firewall concepts (9) § quality characteristic of High-Level-Security-Firewall: – simple rules – mutual protection • packet filter protects application gateway – nested security • serveral hindrances: packet filter AG packet filter – various operating systems • particular components can be managed from serveral operation systems. – multiple option of analysis • all layers of TCP/IP can be inspected. § is suitable for coupling sensitive network and internet. 9/10/2020 42

final decision of firewall concept § an important measure before making a decision is to specify requirement of protection. § Matrix (basis: BSI) requirement of protection Risks field firewall concept low to middle - slight violation of laws - limited negative effects - financial demage < 15. 000 € inside organization packet filter outside organization dual-homed application gateway high - considerable violation of laws - wide negative effects - financial demage < 2, 5 Mio. € inside organization packet filter and single-homed AG outside organization packet filter and dual-homed AG - radical violation of laws - negative effect threatening our existence - financial demage > 2, 5 Mio. € inside organization screened subnet with packet filter and single-homed AG outside organization screened subnet with packet filter and dual-homed AG very high 9/10/2020 43
computer crime – facts and numbers § contains all criminal acts which contains features of electronic data processing (EDP). § in addition to it, computer crime contains criminal acts where is used IT for planning, preparation and execution. § to this form of crime the BKA creates an update yearly. 9/10/2020 44
quantum of computer crime § number of cases: – 6. 507. 394 criminal acts, 57. 490 (0, 88%) computer crime. regression of 27, 5 percents. § committers: – 78, 1% male – not german: 16, 2 % – 31% under 21 years old § financial demage: – ca. 85 Mio. € 9/10/2020 45
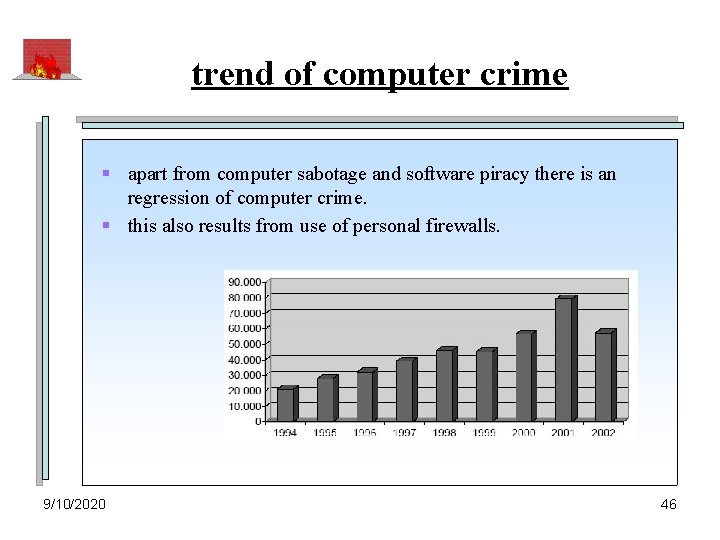
trend of computer crime § apart from computer sabotage and software piracy there is an regression of computer crime. § this also results from use of personal firewalls. 9/10/2020 46
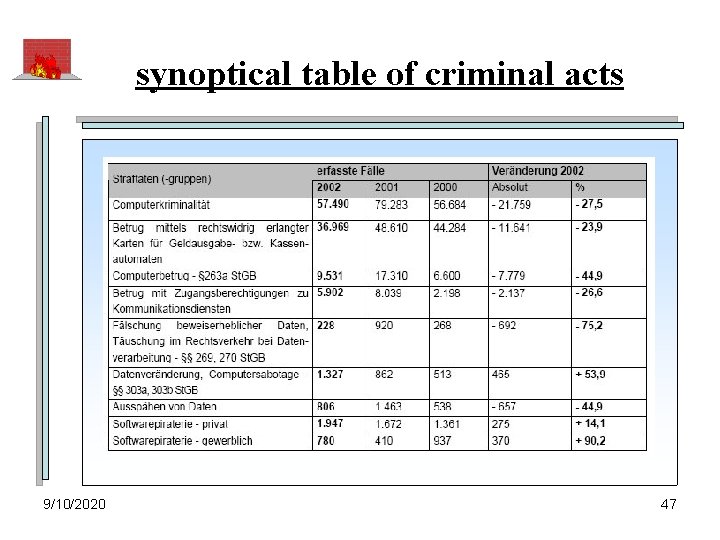
synoptical table of criminal acts 9/10/2020 47
Thank you for attention! 9/10/2020 48
- Slides: 48