SCADAspecific Intrusion DetectionPrevention Systems a Survey Taxonomy Bonnie
SCADA-specific Intrusion Detection/Prevention Systems - a Survey & Taxonomy Bonnie Zhu Shankar Sastry EECS, UC Berkeley 1 st SCS Workshop KTH April 12 th, 2010
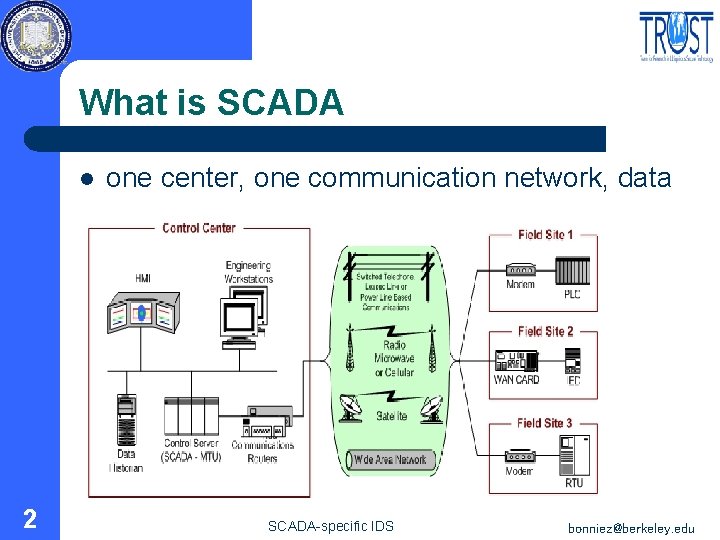
What is SCADA l 2 one center, one communication network, data SCADA-specific IDS bonniez@berkeley. edu
What is IDS l l 3 An intrusion alarm coupled with a security response. “Prevention is best combined with detection and response. ” SCADA-specific IDS bonniez@berkeley. edu
Why SCADA-specific IDS l l l 4 Hard real-time, 24 X 7, timeliness Legacy systems without fully retrofitting Field knowledge SCADA-specific IDS bonniez@berkeley. edu
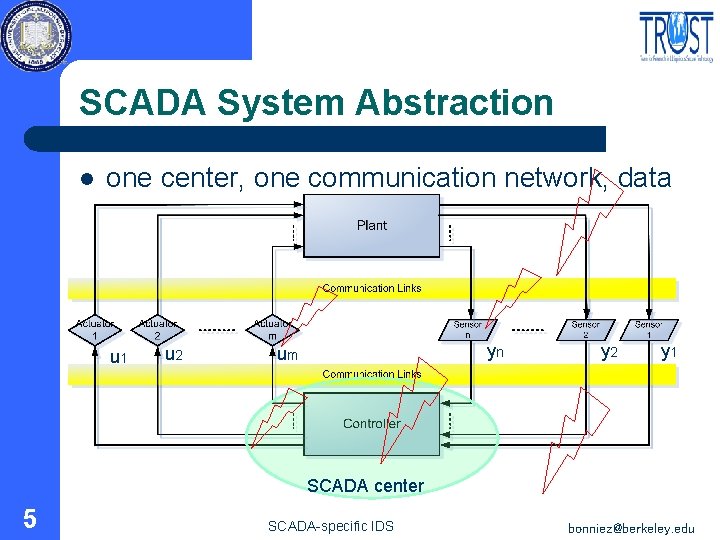
SCADA System Abstraction l one center, one communication network, data u 1 u 2 yn um y 2 y 1 SCADA center 5 SCADA-specific IDS bonniez@berkeley. edu
Definitions l l l 6 Fault Anomaly Misuse Noise False alarm Missed detection SCADA-specific IDS bonniez@berkeley. edu
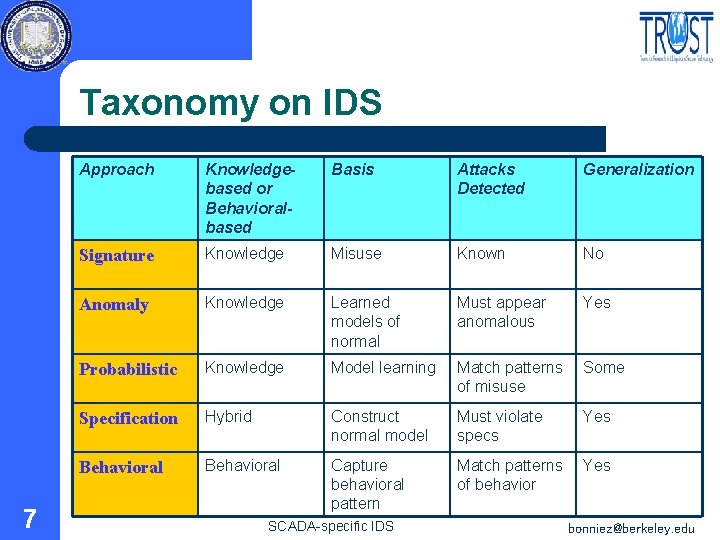
Taxonomy on IDS 7 Approach Knowledgebased or Behavioralbased Basis Attacks Detected Generalization Signature Knowledge Misuse Known No Anomaly Knowledge Learned models of normal Must appear anomalous Yes Probabilistic Knowledge Model learning Match patterns of misuse Some Specification Hybrid Construct normal model Must violate specs Yes Behavioral Capture behavioral pattern Match patterns of behavior Yes SCADA-specific IDS bonniez@berkeley. edu
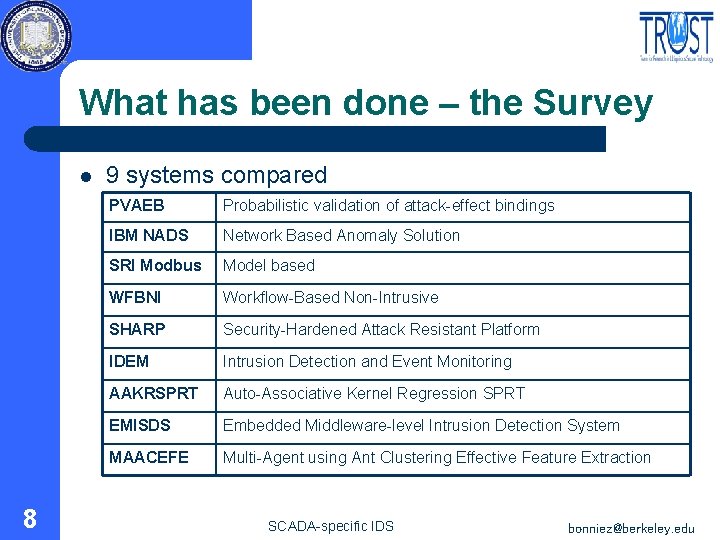
What has been done – the Survey l 8 9 systems compared PVAEB Probabilistic validation of attack-effect bindings IBM NADS Network Based Anomaly Solution SRI Modbus Model based WFBNI Workflow-Based Non-Intrusive SHARP Security-Hardened Attack Resistant Platform IDEM Intrusion Detection and Event Monitoring AAKRSPRT Auto-Associative Kernel Regression SPRT EMISDS Embedded Middleware-level Intrusion Detection System MAACEFE Multi-Agent using Ant Clustering Effective Feature Extraction SCADA-specific IDS bonniez@berkeley. edu
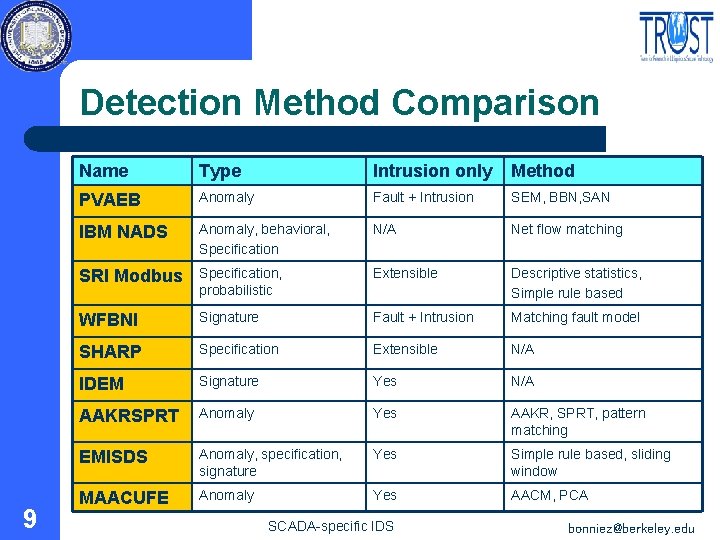
Detection Method Comparison 9 Name Type Intrusion only Method PVAEB Anomaly Fault + Intrusion SEM, BBN, SAN IBM NADS Anomaly, behavioral, Specification N/A Net flow matching SRI Modbus Specification, probabilistic Extensible Descriptive statistics, Simple rule based WFBNI Signature Fault + Intrusion Matching fault model SHARP Specification Extensible N/A IDEM Signature Yes N/A AAKRSPRT Anomaly Yes AAKR, SPRT, pattern matching EMISDS Anomaly, specification, signature Yes Simple rule based, sliding window MAACUFE Anomaly Yes AACM, PCA SCADA-specific IDS bonniez@berkeley. edu
Metrics for SCADA-suitability l Proposed a set of 16 variables – – – 10 Self-security Fallacy analysis Data set Unit of analysis … SCADA-specific IDS bonniez@berkeley. edu
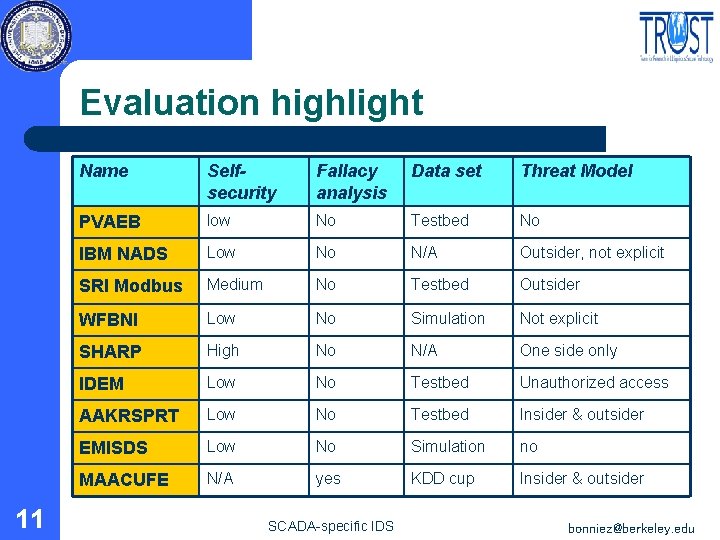
Evaluation highlight 11 Name Selfsecurity Fallacy analysis Data set Threat Model PVAEB low No Testbed No IBM NADS Low No N/A Outsider, not explicit SRI Modbus Medium No Testbed Outsider WFBNI Low No Simulation Not explicit SHARP High No N/A One side only IDEM Low No Testbed Unauthorized access AAKRSPRT Low No Testbed Insider & outsider EMISDS Low No Simulation no MAACUFE N/A yes KDD cup Insider & outsider SCADA-specific IDS bonniez@berkeley. edu
Discussion l Voids & deficits – – l Future directions – – l Reachability analysis, safety sets Protocol analysis, cyber-physical interaction Our work-in-progress – 12 well-considered threat model false alarm/negative rates Judicious Intelligent Executive SCADA-specific IDS bonniez@berkeley. edu
Thanks l 13 Prof. Vern Paxson ……. SCADA-specific IDS bonniez@berkeley. edu
Q&A l 14 bonniez@berkeley. edu SCADA-specific IDS bonniez@berkeley. edu
Key Characteristics l l l 15 Real-time : deadline Distributed: synchronization Embedded: interaction Software <=>Hardware SCADA-specific IDS bonniez@berkeley. edu
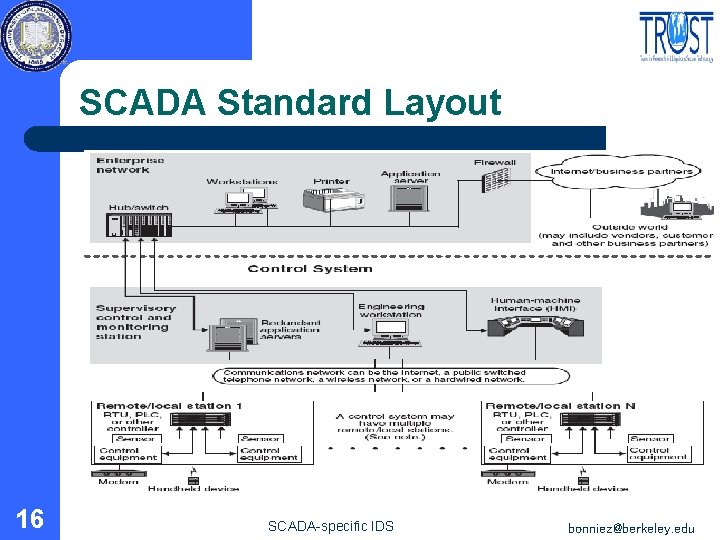
SCADA Standard Layout 16 SCADA-specific IDS bonniez@berkeley. edu
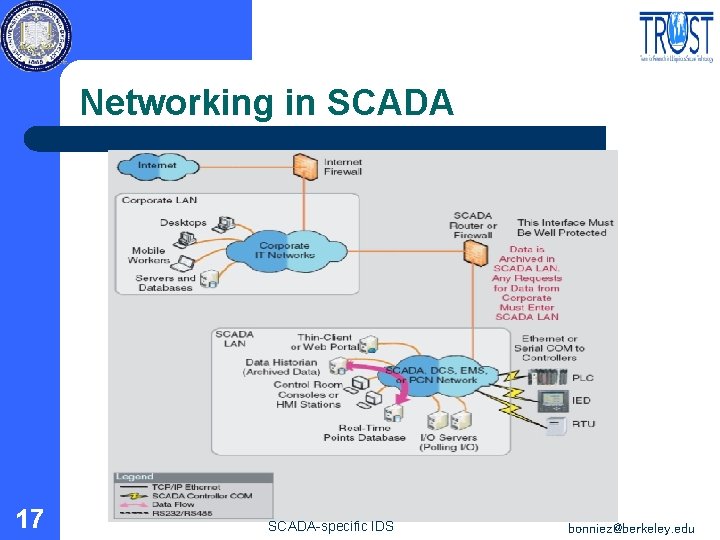
Networking in SCADA 17 SCADA-specific IDS bonniez@berkeley. edu
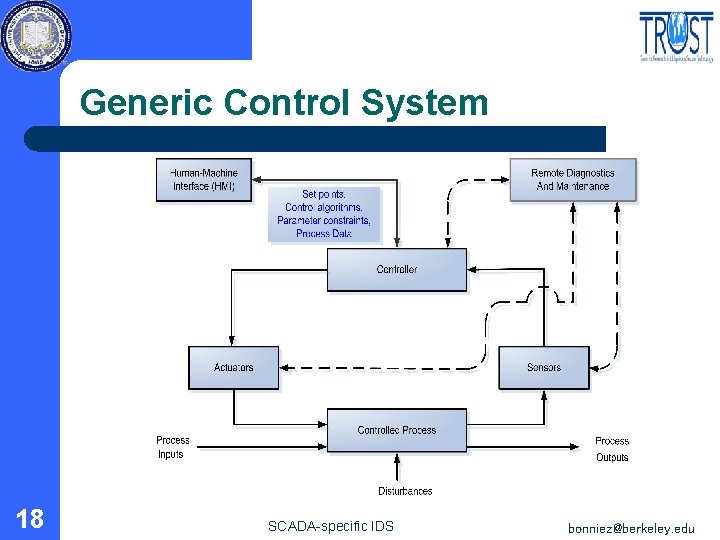
Generic Control System 18 SCADA-specific IDS bonniez@berkeley. edu
- Slides: 18