SAuth Protecting User Accounts from Password Database Leaks
SAuth: Protecting User Accounts from Password Database Leaks Georgios Kontaxis‡, Elias Athanasopoulos‡ Georgios Portokalidis*, Angelos Keromytis‡ ‡Columbia University *Stevens Institute of Technology
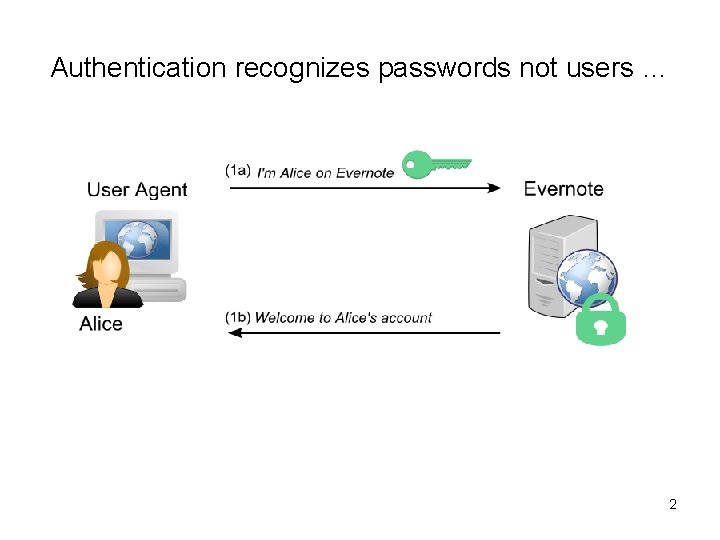
Authentication recognizes passwords not users … 2
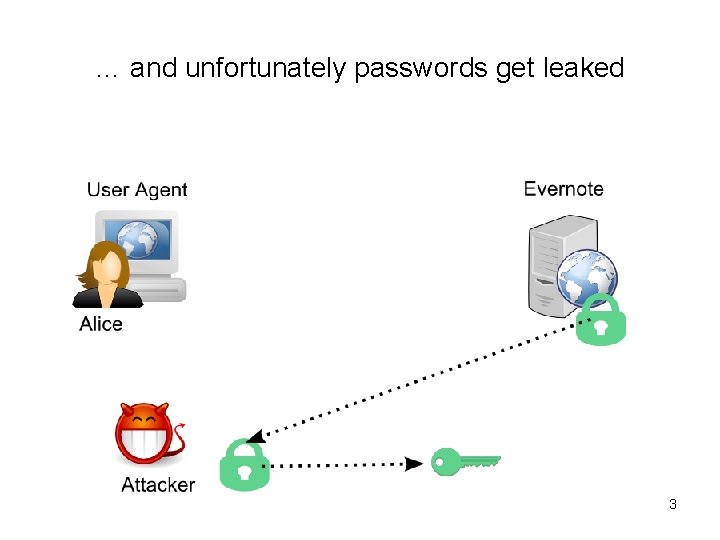
… and unfortunately passwords get leaked 3
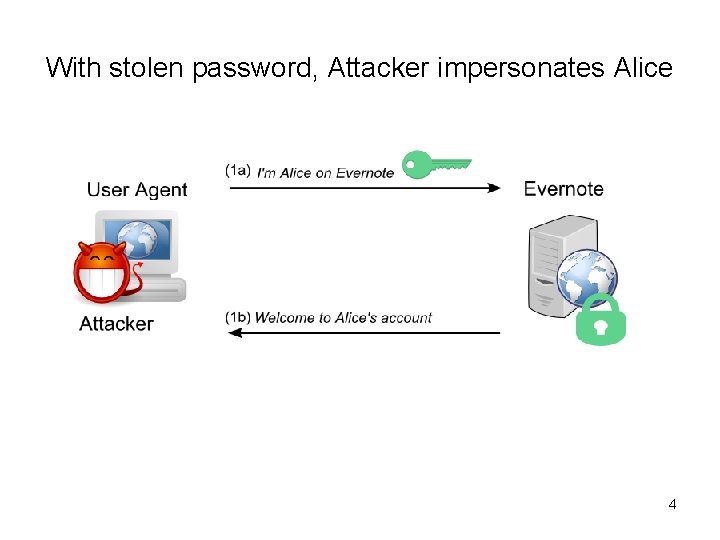
With stolen password, Attacker impersonates Alice 4
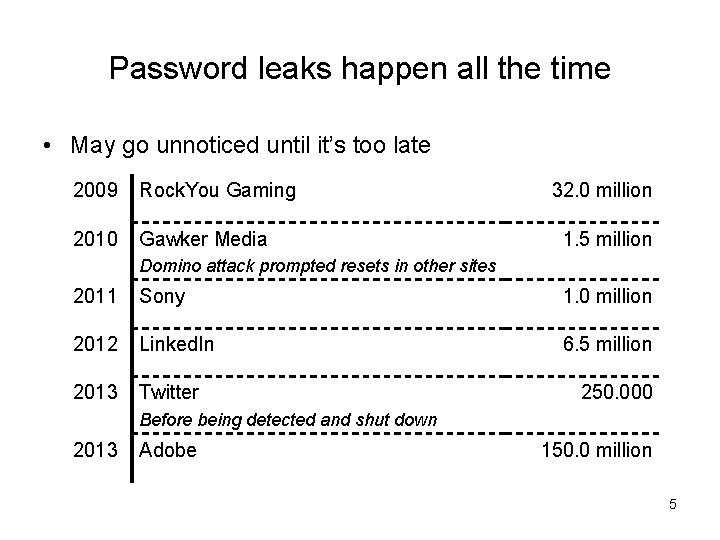
Password leaks happen all the time • May go unnoticed until it’s too late 2009 Rock. You Gaming 2010 Gawker Media 32. 0 million 1. 5 million Domino attack prompted resets in other sites 2011 Sony 1. 0 million 2012 Linked. In 6. 5 million 2013 Twitter 250. 000 Before being detected and shut down 2013 Adobe 150. 0 million 5

Passwords get cracked all the time Why? • Weak passwords – short, dictionary words, names, patterns, etc. • Fast hardware – Commodity parallel architectures (GPUs) – Cloud-powered cracking platforms • 6 days after the 6. 5 million Linked. In password leak, 90% of them were cracked 6
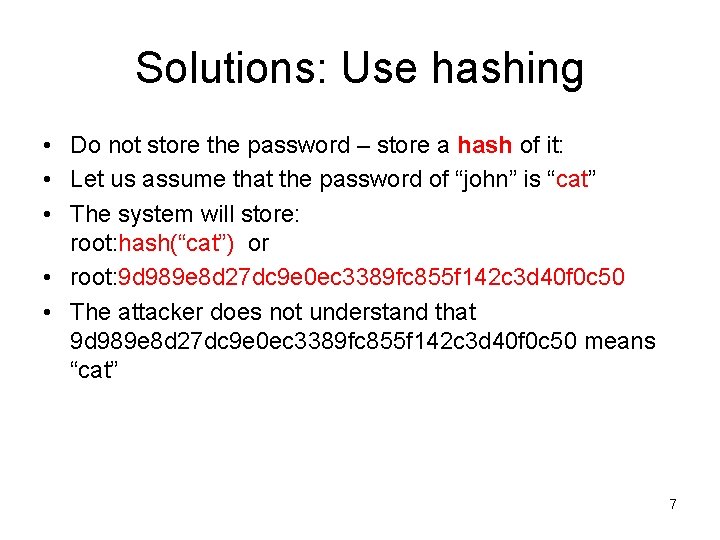
Solutions: Use hashing • Do not store the password – store a hash of it: • Let us assume that the password of “john” is “cat” • The system will store: root: hash(“cat”) or • root: 9 d 989 e 8 d 27 dc 9 e 0 ec 3389 fc 855 f 142 c 3 d 40 f 0 c 50 • The attacker does not understand that 9 d 989 e 8 d 27 dc 9 e 0 ec 3389 fc 855 f 142 c 3 d 40 f 0 c 50 means “cat” 7
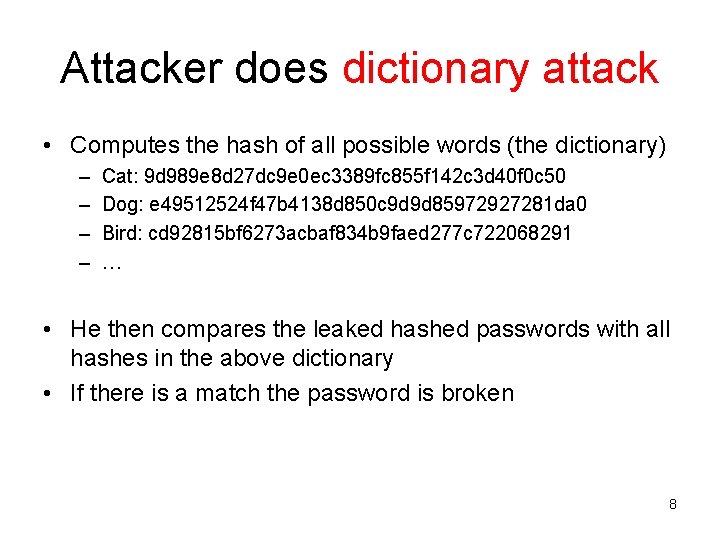
Attacker does dictionary attack • Computes the hash of all possible words (the dictionary) – – Cat: 9 d 989 e 8 d 27 dc 9 e 0 ec 3389 fc 855 f 142 c 3 d 40 f 0 c 50 Dog: e 49512524 f 47 b 4138 d 850 c 9 d 9 d 85972927281 da 0 Bird: cd 92815 bf 6273 acbaf 834 b 9 faed 277 c 722068291 … • He then compares the leaked hashed passwords with all hashes in the above dictionary • If there is a match the password is broken 8
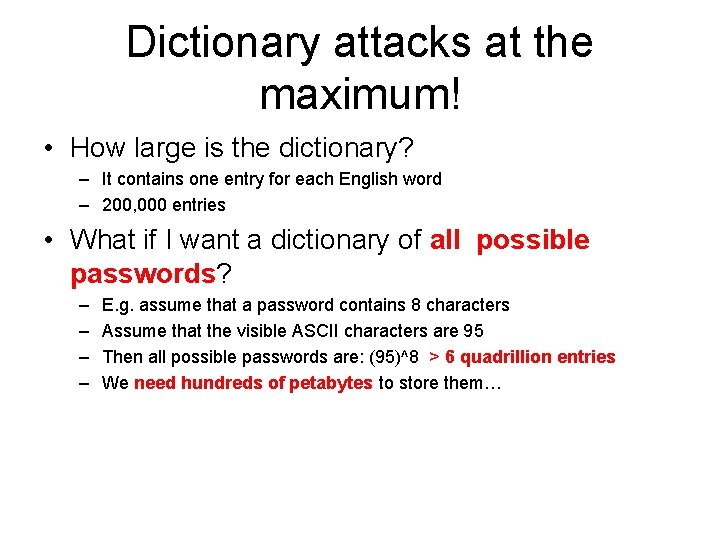
Dictionary attacks at the maximum! • How large is the dictionary? – It contains one entry for each English word – 200, 000 entries • What if I want a dictionary of all possible passwords? – – E. g. assume that a password contains 8 characters Assume that the visible ASCII characters are 95 Then all possible passwords are: (95)^8 > 6 quadrillion entries We need hundreds of petabytes to store them…
Rainbow Tables • We do not have storage to store all 6 quadrillions of hashes What should we do? • Option #2: • Do not store any hashes AT ALL! • Recompute them all dynamically • Recompute all 6 quadrillion of them BUT • Recomputing 6 quadrillion of hashes will take months or years ….
Rainbow tables • Problem: – If we store the hashes we need petabytes of space – If we re-compute all the hashes we need to do quadrillions of computations Μπρος γκρεμός και πίσω ρέμα… • Solution: • Store some of them and re-compute some others… • HOW? ? ?
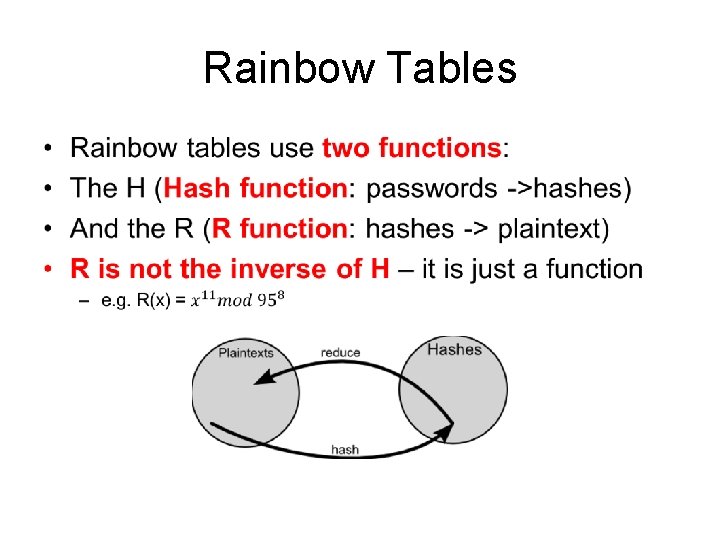
Rainbow Tables •
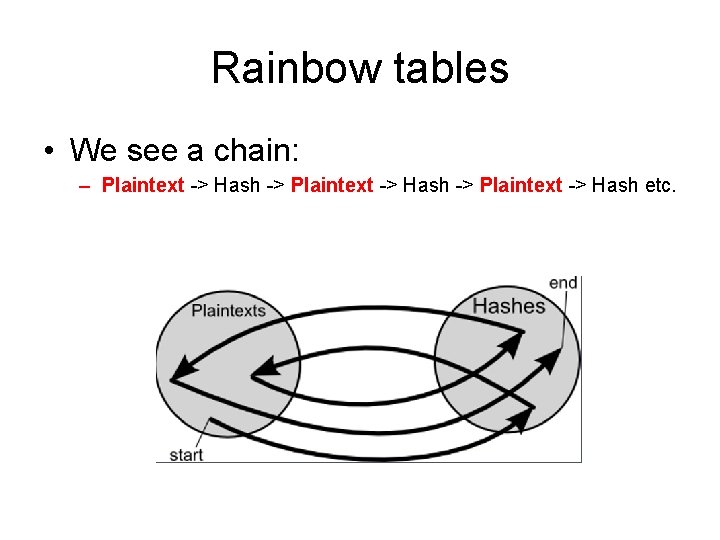
Rainbow tables • We see a chain: – Plaintext -> Hash -> Plaintext -> Hash etc.
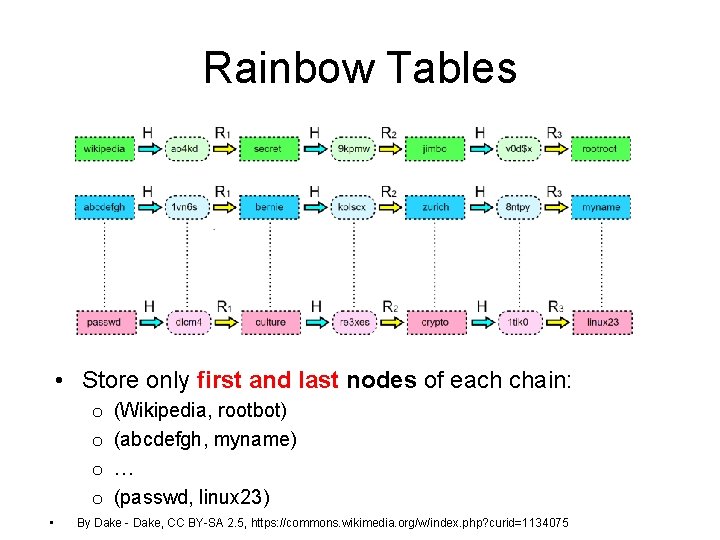
Rainbow Tables • Store only first and last nodes of each chain: o o • (Wikipedia, rootbot) (abcdefgh, myname) … (passwd, linux 23) By Dake - Dake, CC BY-SA 2. 5, https: //commons. wikimedia. org/w/index. php? curid=1134075
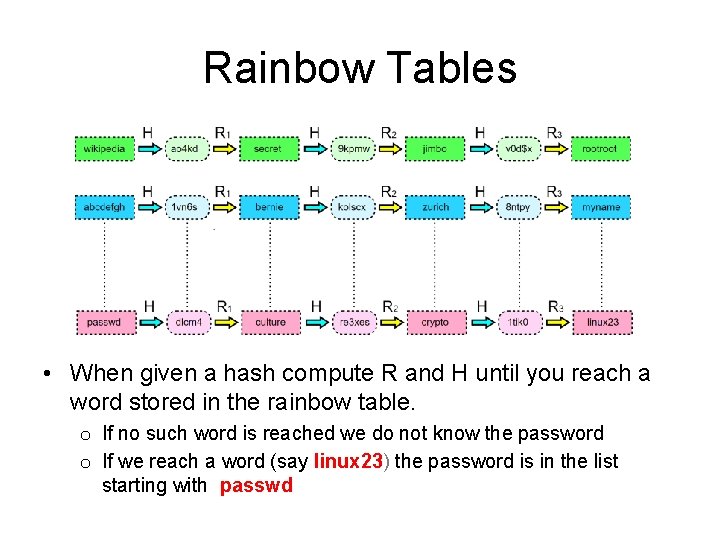
Rainbow Tables • When given a hash compute R and H until you reach a word stored in the rainbow table. o If no such word is reached we do not know the password o If we reach a word (say linux 23) the password is in the list starting with passwd
Solution: Use salt • The system will store: root: 1234: hash(“cat 1234”) • root: 1234: 5 a 04 fa 271 fcd 6843 e 143801494 f 459 aee 67 bb 91 d • The attacker does not understand that 5 a 04 fa 271 fcd 6843 e 143801494 f 459 aee 67 bb 91 d means “cat 1234” • Each user has a different salt • The attacker needs to create – One dictionary for each salt – One rainbow table for each salt 16
Other Solutions • Two-Factor Authentication – How many tokens/app can a user handle? • Single sign-on services – Single point of failure – Relying party gets to find out user identity* – Privacy issues from coarse-grained data sharing 17
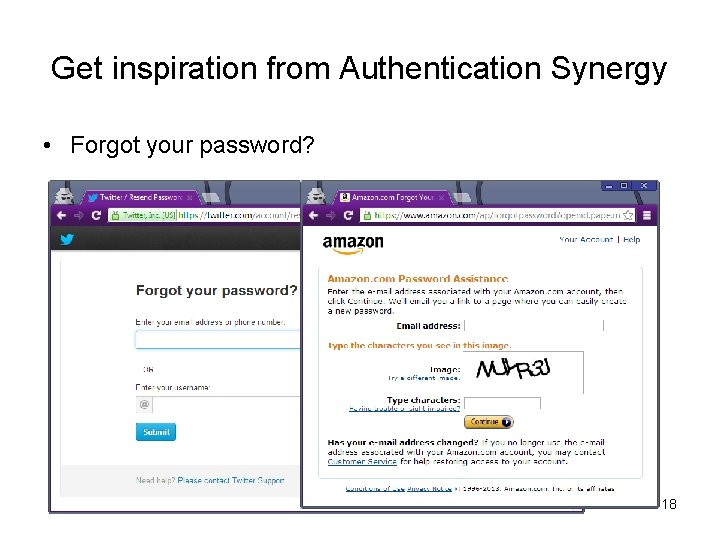
Get inspiration from Authentication Synergy • Forgot your password? 18
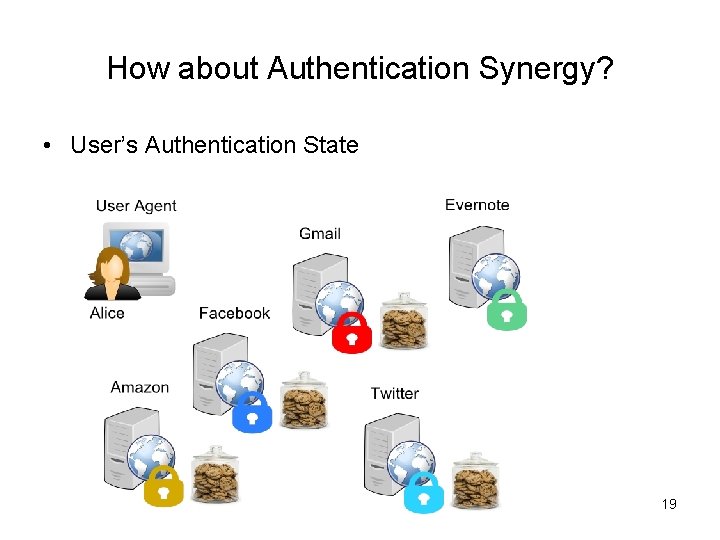
How about Authentication Synergy? • User’s Authentication State 19
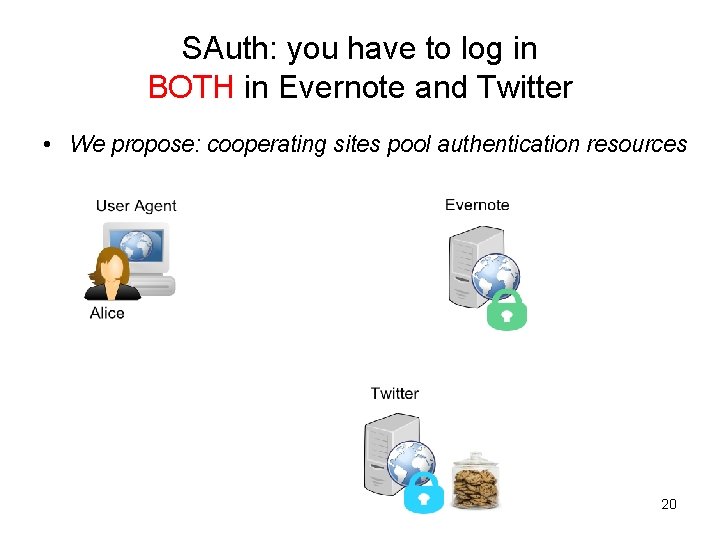
SAuth: you have to log in BOTH in Evernote and Twitter • We propose: cooperating sites pool authentication resources 20
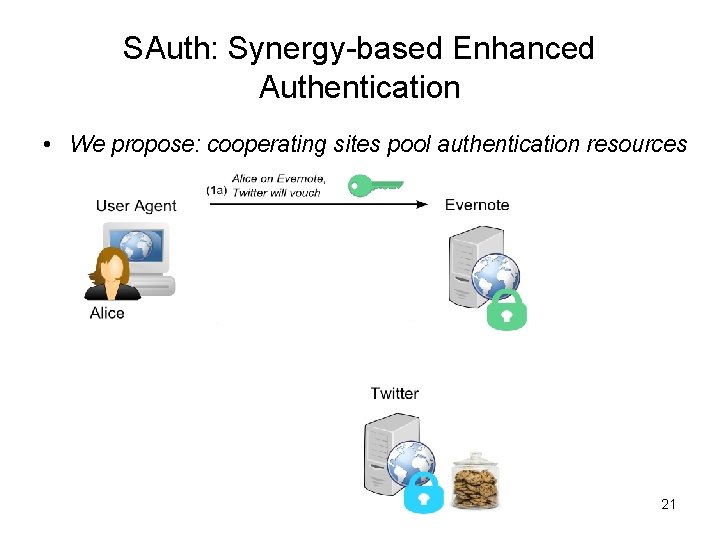
SAuth: Synergy-based Enhanced Authentication • We propose: cooperating sites pool authentication resources 21
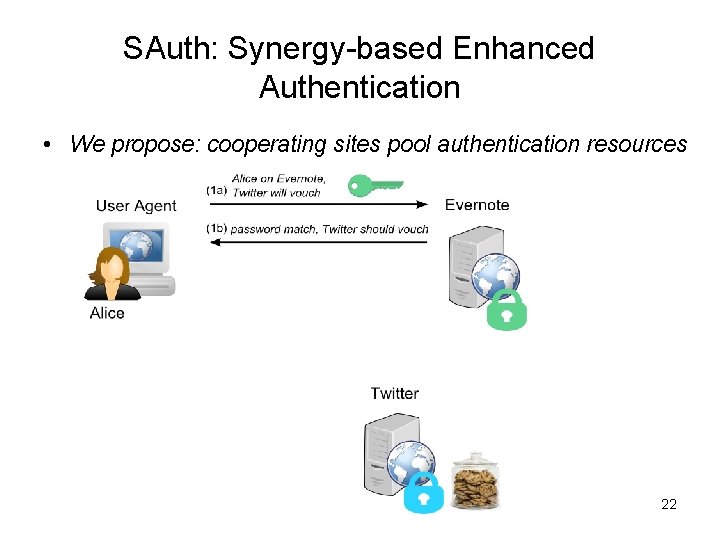
SAuth: Synergy-based Enhanced Authentication • We propose: cooperating sites pool authentication resources 22
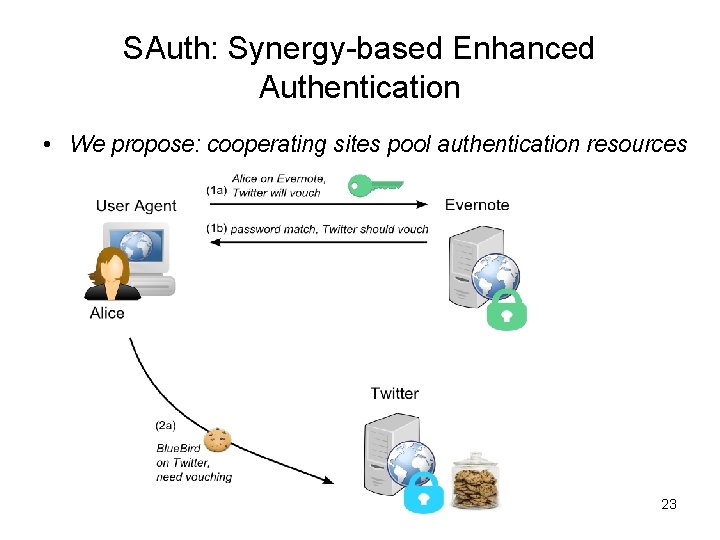
SAuth: Synergy-based Enhanced Authentication • We propose: cooperating sites pool authentication resources 23
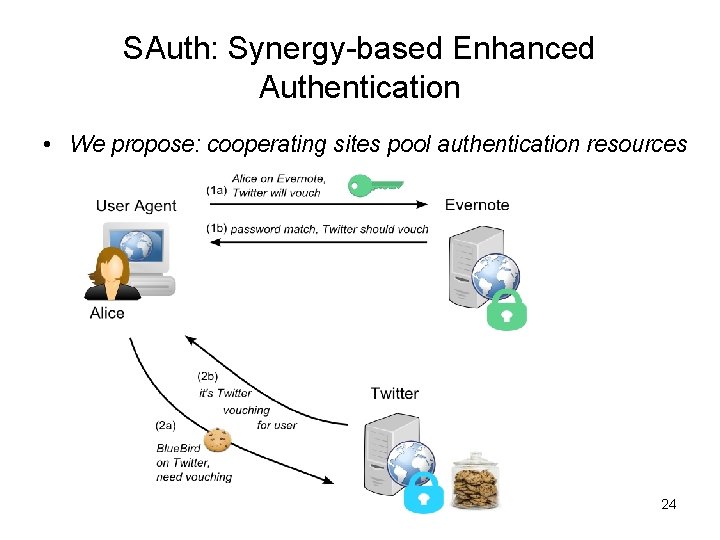
SAuth: Synergy-based Enhanced Authentication • We propose: cooperating sites pool authentication resources 24
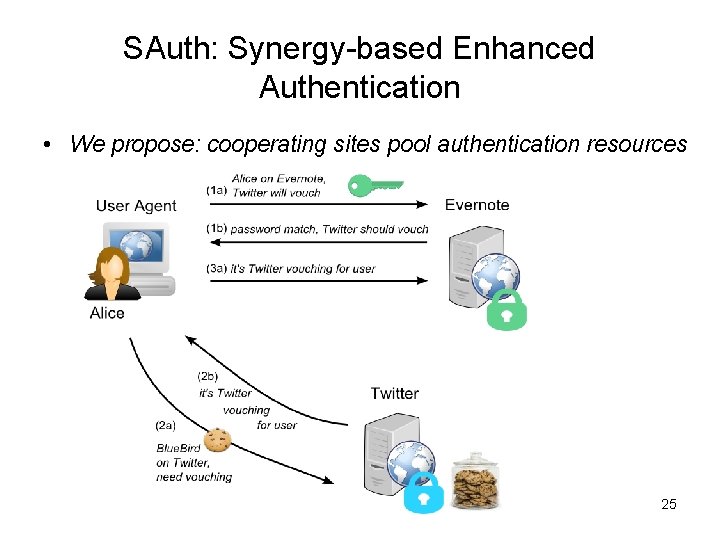
SAuth: Synergy-based Enhanced Authentication • We propose: cooperating sites pool authentication resources 25
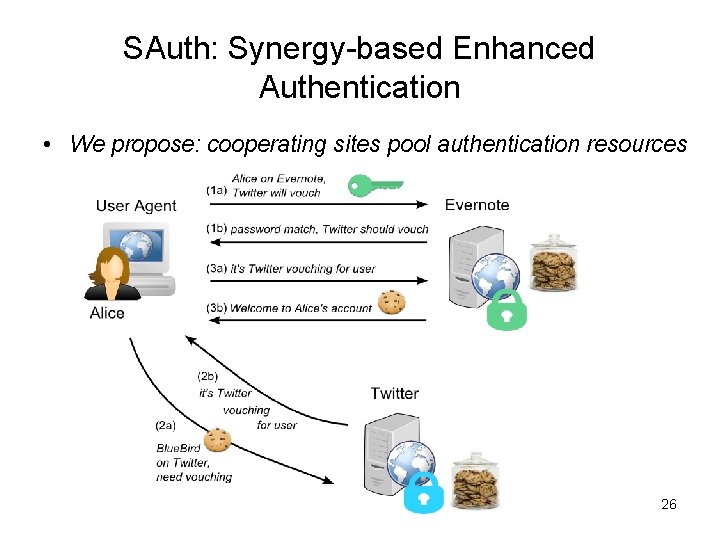
SAuth: Synergy-based Enhanced Authentication • We propose: cooperating sites pool authentication resources 26
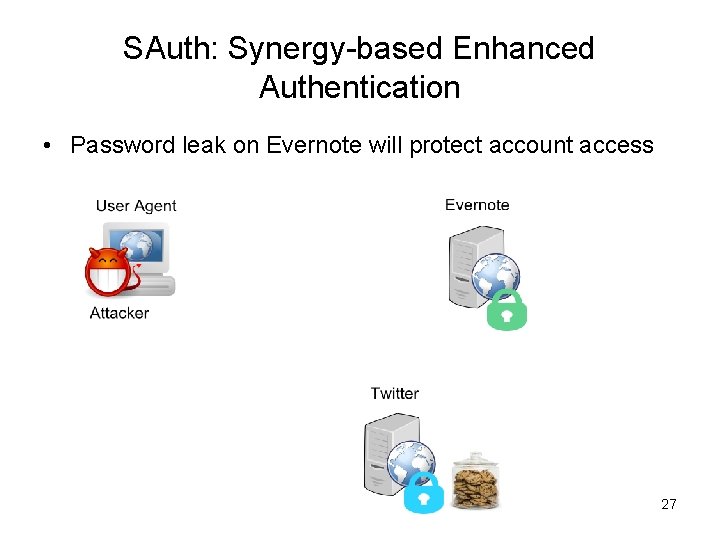
SAuth: Synergy-based Enhanced Authentication • Password leak on Evernote will protect account access 27
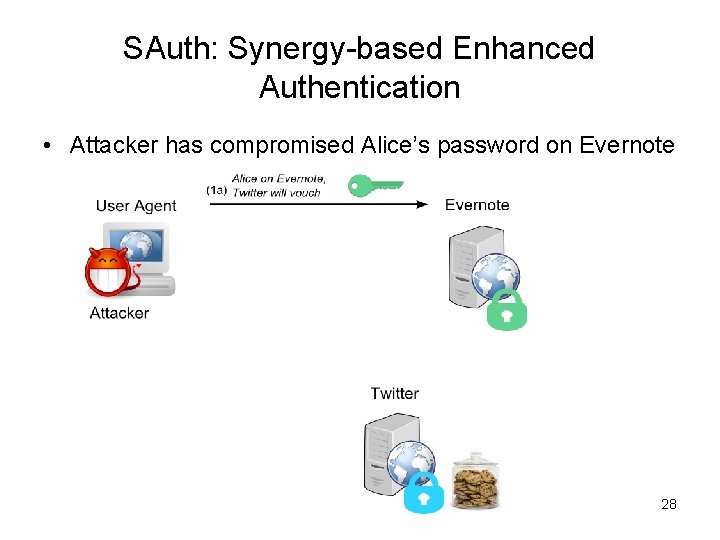
SAuth: Synergy-based Enhanced Authentication • Attacker has compromised Alice’s password on Evernote 28
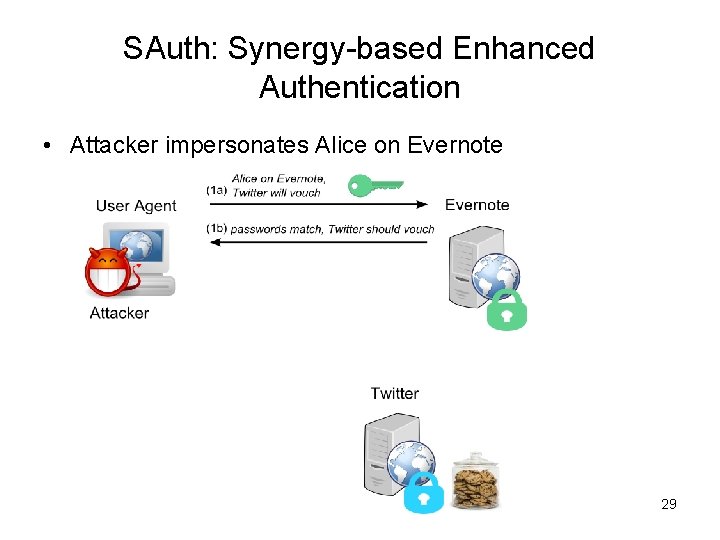
SAuth: Synergy-based Enhanced Authentication • Attacker impersonates Alice on Evernote 29
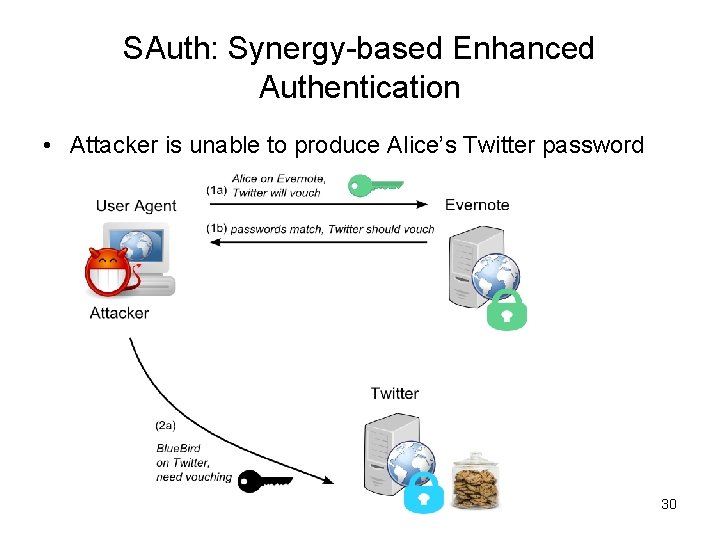
SAuth: Synergy-based Enhanced Authentication • Attacker is unable to produce Alice’s Twitter password 30
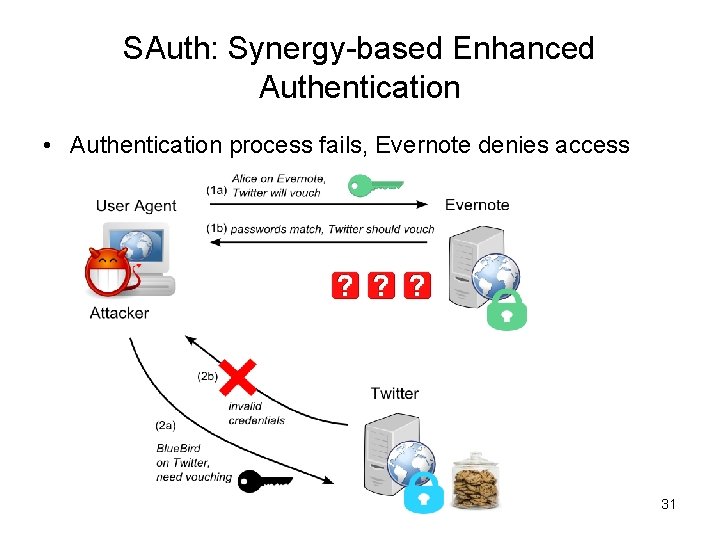
SAuth: Synergy-based Enhanced Authentication • Authentication process fails, Evernote denies access 31
Password Reuse Woes • • User has 7 passwords, re-uses 5 of them Password shared across 6 sites [Florencio WWW ’ 07] Problem: Attacker steals evernote password and uses it in Twitter 32
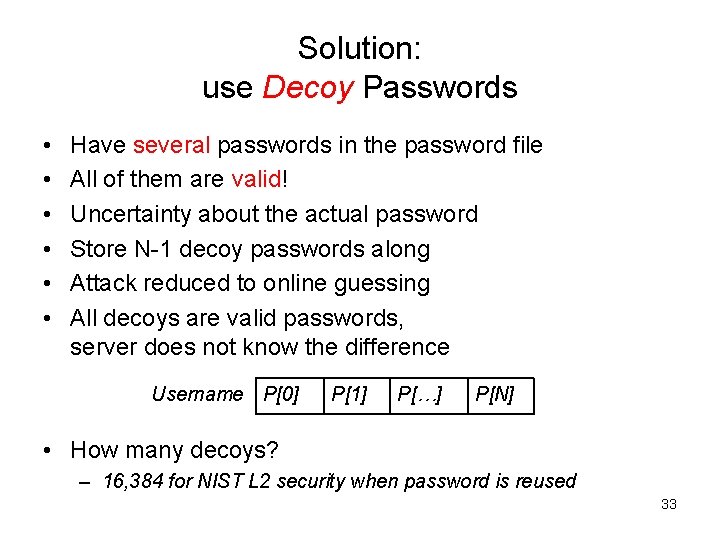
Solution: use Decoy Passwords • • • Have several passwords in the password file All of them are valid! Uncertainty about the actual password Store N-1 decoy passwords along Attack reduced to online guessing All decoys are valid passwords, server does not know the difference Username P[0] P[1] P[…] P[N] • How many decoys? – 16, 384 for NIST L 2 security when password is reused 33
Realistic Decoy Passwords • User password must blend-in with the decoys – Crackers are already factoring in human behavior – Complex vs Popular Passwords string-digit 37% digit-string 05% ! 10% $ 03% - Rock. You Leak ‘ 09 – Ideal: have the user type N passwords, remember 1 – Practical: generation within the password ecosystem • Any blind automated method will generate outliers • Probabilistic production seeded by user’s password, biased towards structures of similar popularity and semantics 34
Summary • Authentication Synergy results in leak-resistant password authentication – Complements existing security – Respect for user privacy, verifiable site cooperation – Minimal changes server-side, no changes client-side • Decoys mitigate password reuse habits – Generated off the user password, consider its context and general human password habits 35
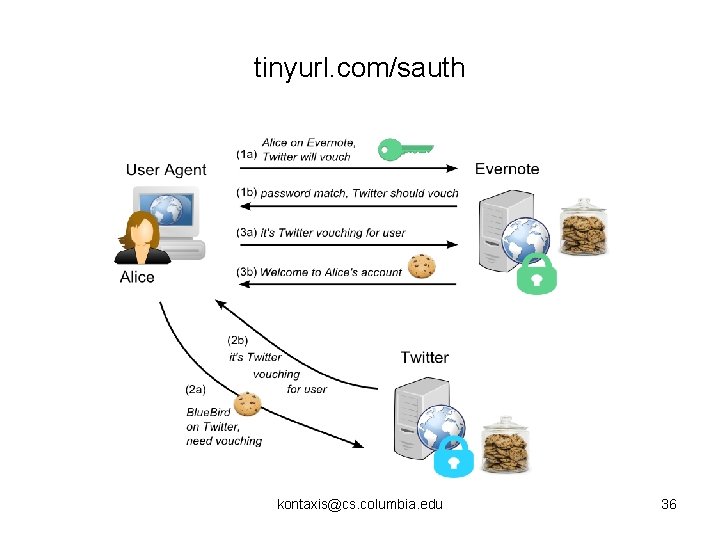
tinyurl. com/sauth kontaxis@cs. columbia. edu 36
Honeywords, Kamouflage and SAuth Decoy Passwords • Honeywords – – Does not yet consider human password habits Honeywords are not valid passwords Use of any honeyword will raise an alarm Auxiliary honeychecking server • Kamouflage password manager – Considers human password habits – Master password decoys are all valid – Online guessing attack should raise alarm • SAuth Decoy Passwords – Considers human password habits – Decoy passwords are all valid – Online guessing attack should raise alarm 37
- Slides: 37