Sandboxing and Content Security Policies Tyler Moore The
Sandboxing and Content Security Policies Tyler Moore The University of Tulsa
Principle of Least Privilege “Every program and every privileged user of the system should operate using the least amount of privilege necessary to complete the job. ” - Jerome Saltzer, Comm. ACM (1974)
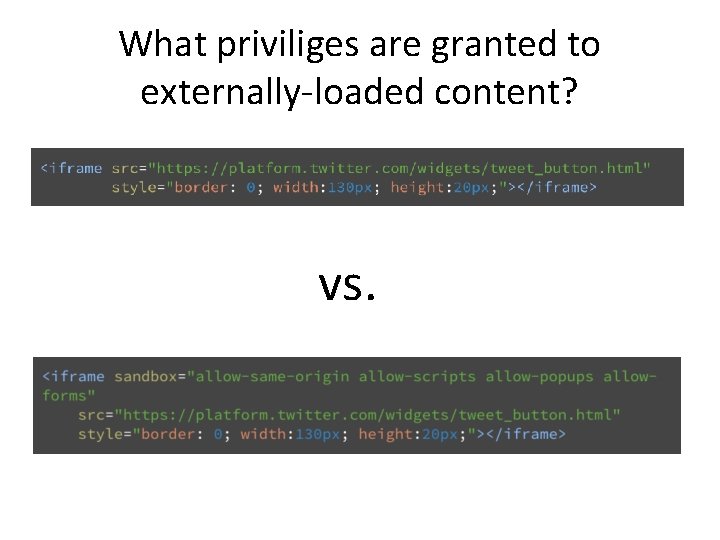
What priviliges are granted to externally-loaded content? vs.
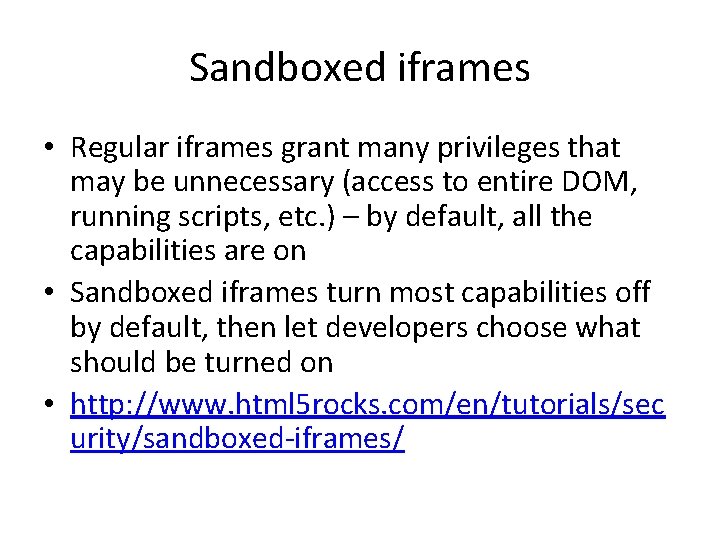
Sandboxed iframes • Regular iframes grant many privileges that may be unnecessary (access to entire DOM, running scripts, etc. ) – by default, all the capabilities are on • Sandboxed iframes turn most capabilities off by default, then let developers choose what should be turned on • http: //www. html 5 rocks. com/en/tutorials/sec urity/sandboxed-iframes/
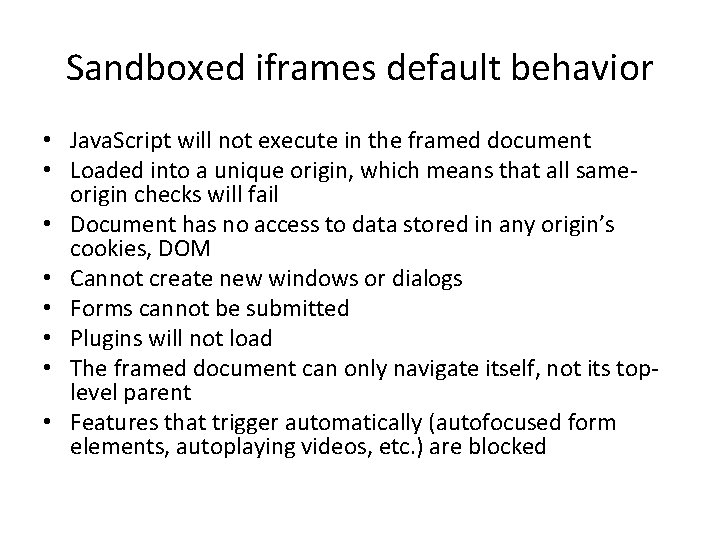
Sandboxed iframes default behavior • Java. Script will not execute in the framed document • Loaded into a unique origin, which means that all sameorigin checks will fail • Document has no access to data stored in any origin’s cookies, DOM • Cannot create new windows or dialogs • Forms cannot be submitted • Plugins will not load • The framed document can only navigate itself, not its toplevel parent • Features that trigger automatically (autofocused form elements, autoplaying videos, etc. ) are blocked
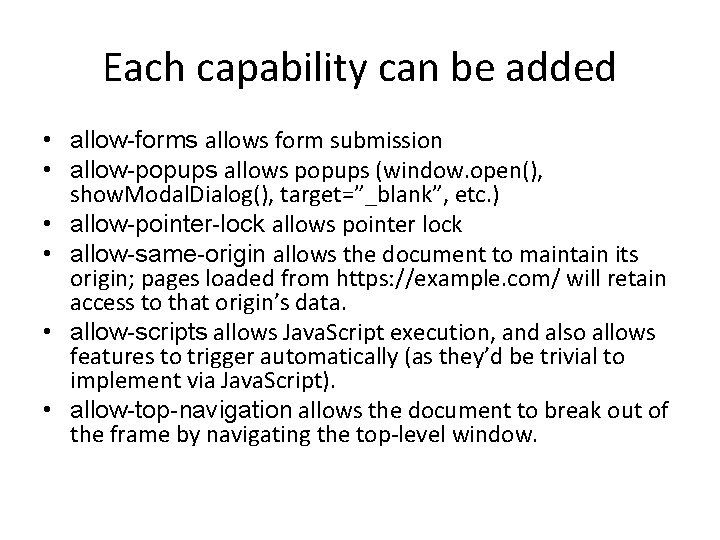
Each capability can be added • allow-forms allows form submission • allow-popups allows popups (window. open(), show. Modal. Dialog(), target=”_blank”, etc. ) • allow-pointer-lock allows pointer lock • allow-same-origin allows the document to maintain its origin; pages loaded from https: //example. com/ will retain access to that origin’s data. • allow-scripts allows Java. Script execution, and also allows features to trigger automatically (as they’d be trivial to implement via Java. Script). • allow-top-navigation allows the document to break out of the frame by navigating the top-level window.
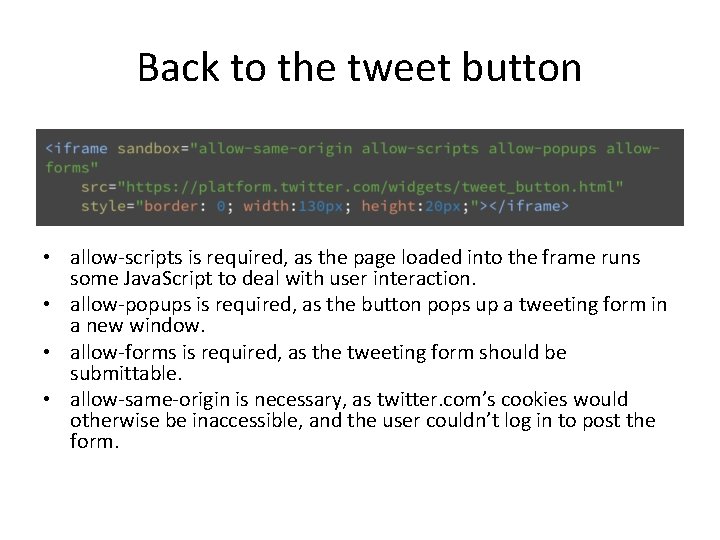
Back to the tweet button • allow-scripts is required, as the page loaded into the frame runs some Java. Script to deal with user interaction. • allow-popups is required, as the button pops up a tweeting form in a new window. • allow-forms is required, as the tweeting form should be submittable. • allow-same-origin is necessary, as twitter. com’s cookies would otherwise be inaccessible, and the user couldn’t log in to post the form.
Sandboxing everywhere • Sandboxing isn’t only for third-party content • Principle of least privilege applies to your own code as well!
Content Security Policy • XSS attacks exploit the browser’s inability to distinguish between scripts intentionally loaded by a website and scripts maliciously injected by a third-party • Begs the question: can we limit the origins that the page can talk to? • With CSP, we can! • http: //www. html 5 rocks. com/en/tutorials/sec urity/content-security-policy/
Motivating example • Google +1 script located at https: //apis. google. com/js/plusone. js • Without CSP, no way a site can differentiate between apis. google. com and evil. com • Set HTTP Header Content-Security-Policy: script-src 'self' https: //apis. google. com • script-src directive specifies which sources can execute scripts on a page
CSPs aren’t just for scripts • base-uri restricts URLs allowd in a page’s <base> element • child-src lists the URLs for workers and embedded frame contents. (e. g. , child-src https: //youtube. com allows embedded videos only from You. Tube) • font-src specifies the origins that can serve web fonts. Google’s Web Fonts could be enabled via font-src https: //themes. googleusercontent. com • form-action lists valid endpoints for submission from <form> tags.
CSPs aren’t just for scripts • img-src defines the origins from which images can be loaded • media-src restricts the origins allowed to deliver video and audio • object-src allows control over Flash and other plugins • plugin-types limits the kinds of plugins a page may invoke
Summary • Principle of least privilege now available to web developers • Many of the vulnerabilities we have discussed were enabled by over-permissive design • Content Security Policy can whitelist permitted origins for 3 rd party content • Sandboxed iframes can restrict the capabilities granted to 3 rd party content • Responsibility for secure implementation now rests with developers
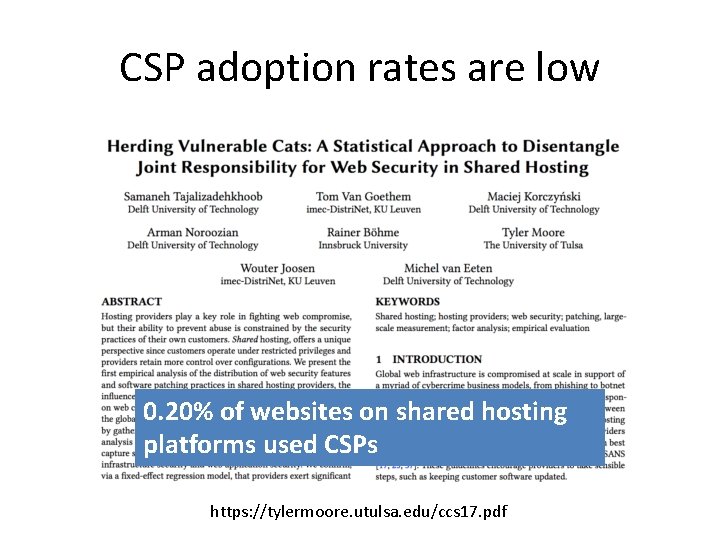
CSP adoption rates are low 0. 20% of websites on shared hosting platforms used CSPs https: //tylermoore. utulsa. edu/ccs 17. pdf
- Slides: 14