San Francisco IIA Fall Seminar Data Protection Best

San Francisco IIA Fall Seminar Data Protection Best Practices December 1, 2017
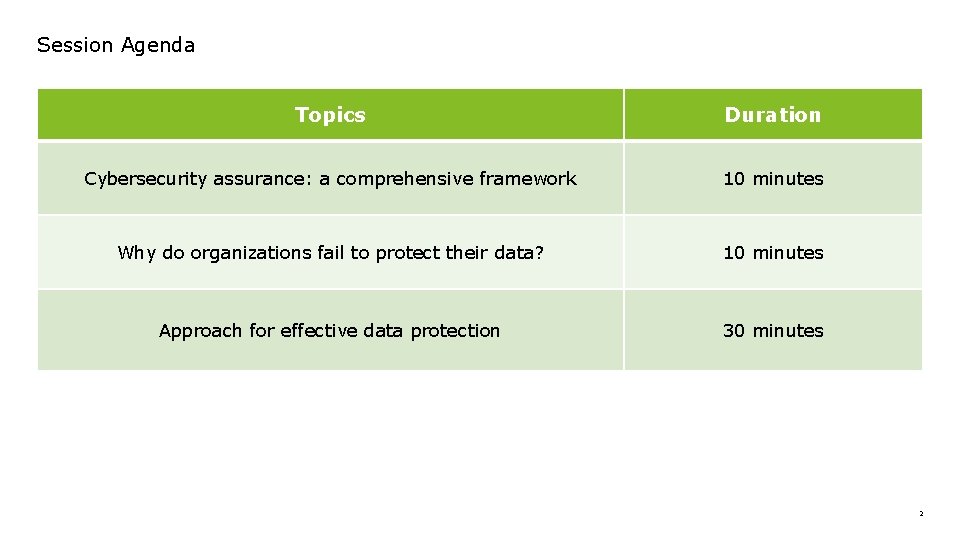
Session Agenda Topics Duration Cybersecurity assurance: a comprehensive framework 10 minutes Why do organizations fail to protect their data? 10 minutes Approach for effective data protection 30 minutes 2
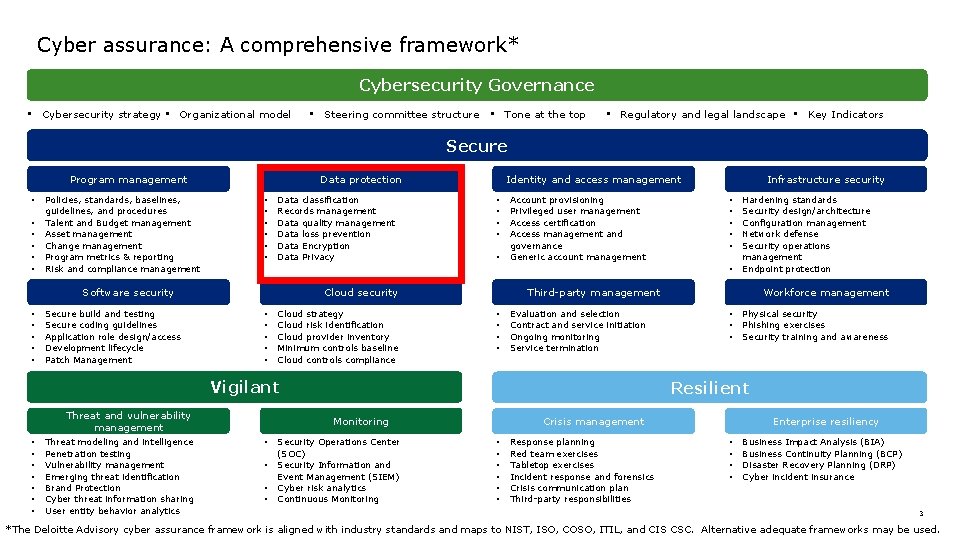
Cyber assurance: A comprehensive framework* Cybersecurity Governance • Cybersecurity strategy • Organizational model • Steering committee structure • Tone at the top • Regulatory and legal landscape • Key Indicators Secure Program management • • • Policies, standards, baselines, guidelines, and procedures Talent and Budget management Asset management Change management Program metrics & reporting Risk and compliance management Data protection • • • Data classification Records management Data quality management Data loss prevention Data Encryption Data Privacy Secure build and testing Secure coding guidelines Application role design/access Development lifecycle Patch Management • • • Account provisioning Privileged user management Access certification Access management and governance Generic account management Cloud security • • • Cloud strategy Cloud risk identification Cloud provider inventory Minimum controls baseline Cloud controls compliance Threat and vulnerability management Threat modeling and intelligence Penetration testing Vulnerability management Emerging threat identification Brand Protection Cyber threat information sharing User entity behavior analytics • • Evaluation and selection Contract and service initiation Ongoing monitoring Service termination • • • Workforce management • • • Physical security Phishing exercises Security training and awareness Resilient Monitoring • Hardening standards Security design/architecture Configuration management Network defense Security operations management Endpoint protection Third-party management Vigilant • • • • Software security • • • Infrastructure security Identity and access management Security Operations Center (SOC) Security Information and Event Management (SIEM) Cyber risk analytics Continuous Monitoring Enterprise resiliency Crisis management • • • Response planning Red team exercises Tabletop exercises Incident response and forensics Crisis communication plan Third-party responsibilities • • Business Impact Analysis (BIA) Business Continuity Planning (BCP) Disaster Recovery Planning (DRP) Cyber incident insurance 3 *The Deloitte Advisory cyber assurance framework is aligned with industry standards and maps to NIST, ISO, COSO, ITIL, and CIS CSC. Alternative adequate frameworks may be used.
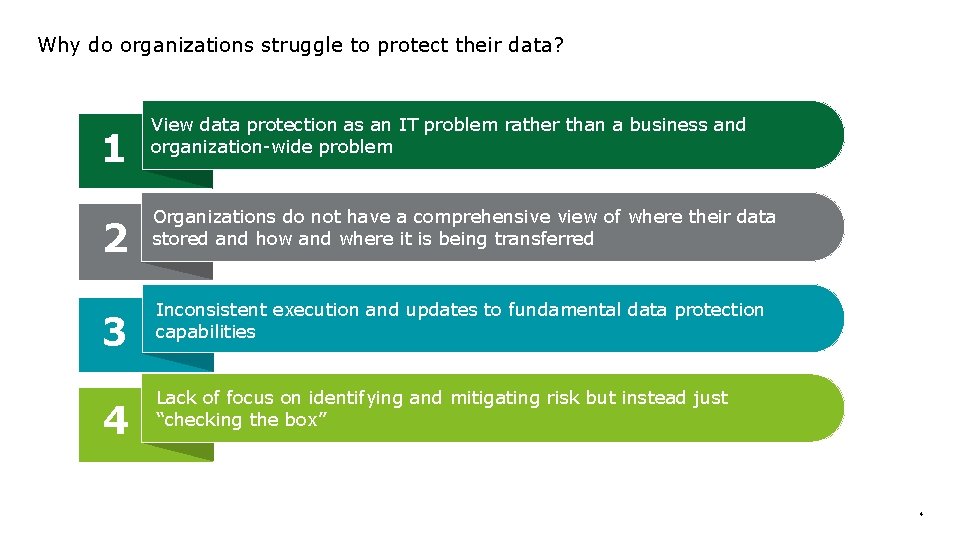
Why do organizations struggle to protect their data? 1 2 3 4 View data protection as an IT problem rather than a business and organization-wide problem Organizations do not have a comprehensive view of where their data stored and how and where it is being transferred Inconsistent execution and updates to fundamental data protection capabilities Lack of focus on identifying and mitigating risk but instead just “checking the box” 4
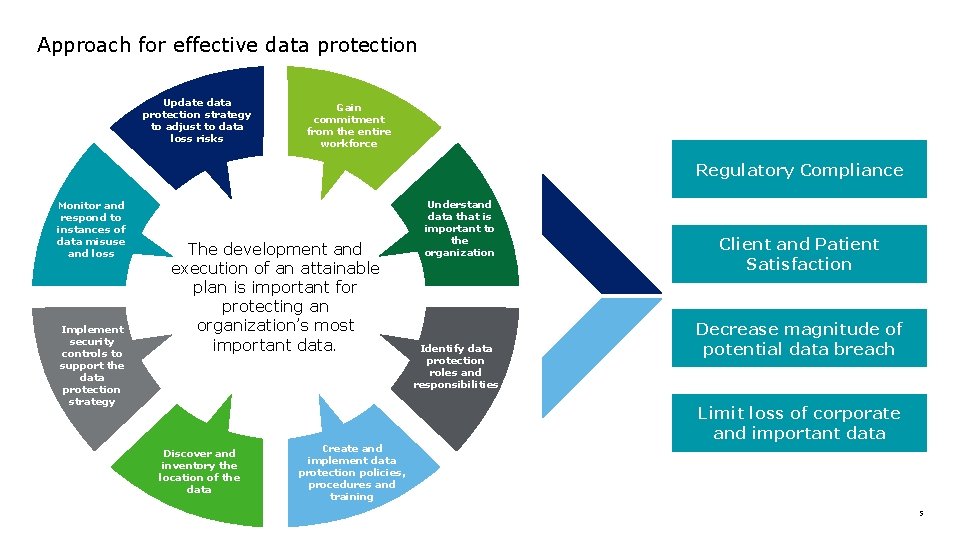
Approach for effective data protection Update data protection strategy to adjust to data loss risks Gain commitment from the entire workforce Regulatory Compliance Monitor and respond to instances of data misuse and loss Implement security controls to support the data protection strategy The development and execution of an attainable plan is important for protecting an organization’s most important data. Discover and inventory the location of the data Create and implement data protection policies, procedures and training Understand data that is important to the organization Identify data protection roles and responsibilities Client and Patient Satisfaction Decrease magnitude of potential data breach Limit loss of corporate and important data 5
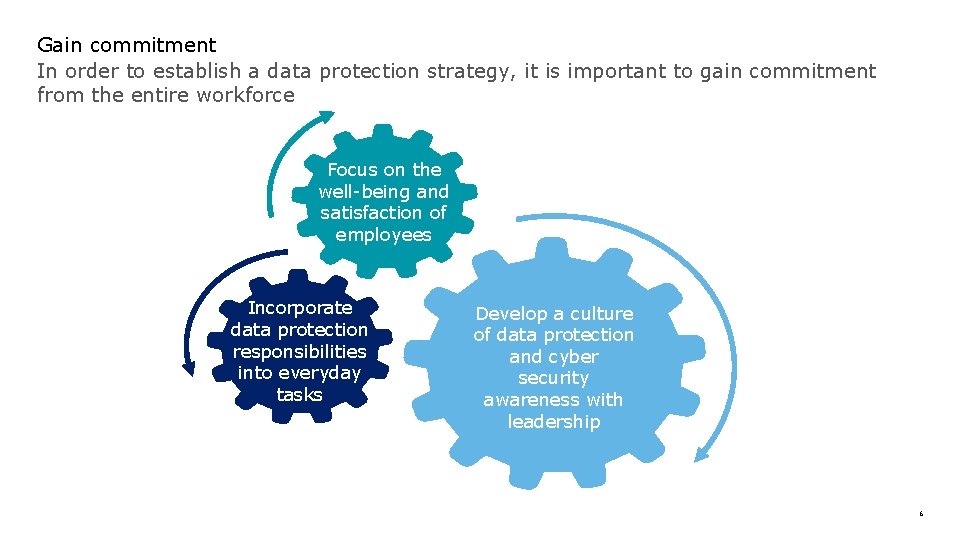
Gain commitment In order to establish a data protection strategy, it is important to gain commitment from the entire workforce Focus on the well-being and satisfaction of employees Incorporate data protection responsibilities into everyday tasks Develop a culture of data protection and cyber security awareness with leadership 6
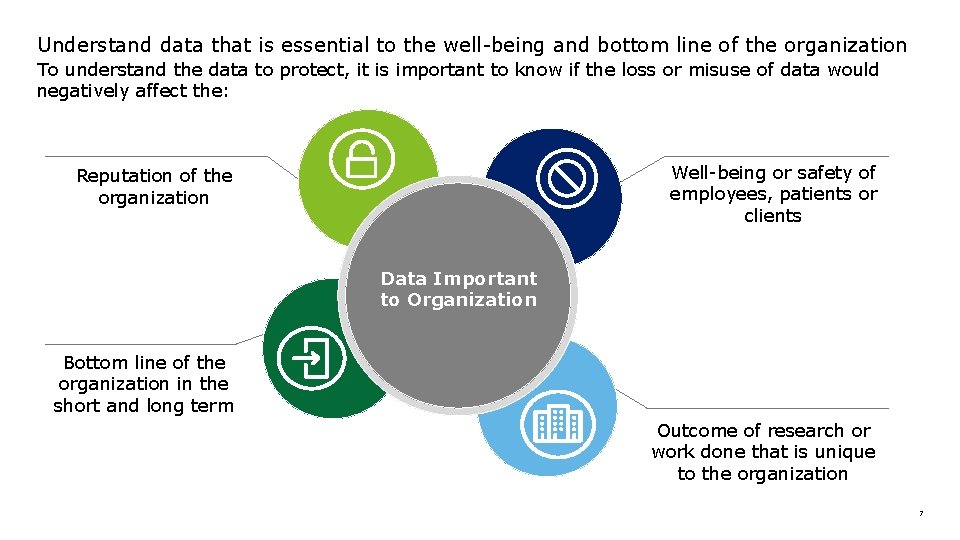
Understand data that is essential to the well-being and bottom line of the organization To understand the data to protect, it is important to know if the loss or misuse of data would negatively affect the: Well-being or safety of employees, patients or clients Reputation of the organization Data Important to Organization Bottom line of the organization in the short and long term Outcome of research or work done that is unique to the organization 7
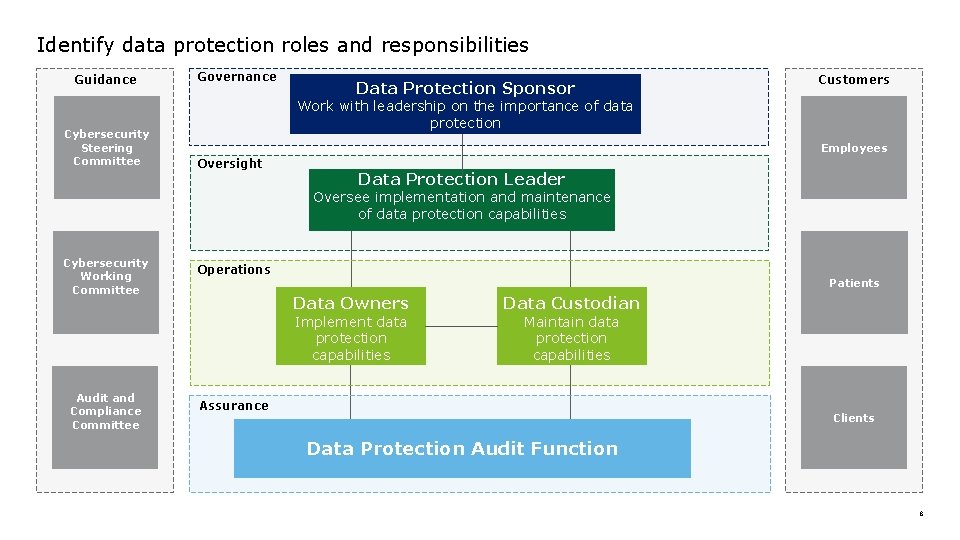
Identify data protection roles and responsibilities Guidance Cybersecurity Steering Committee Governance Data Protection Sponsor Strategic Technology Decisions Customers Work with leadership on the importance of data protection Employees Oversight Data Protection Leader Oversee implementation and maintenance of data protection capabilities Cybersecurity Working Committee Operations Patients Data Owners Implement data protection capabilities Audit and Compliance Committee Data Custodian Maintain data protection capabilities Assurance Clients Data Protection Audit Function 8
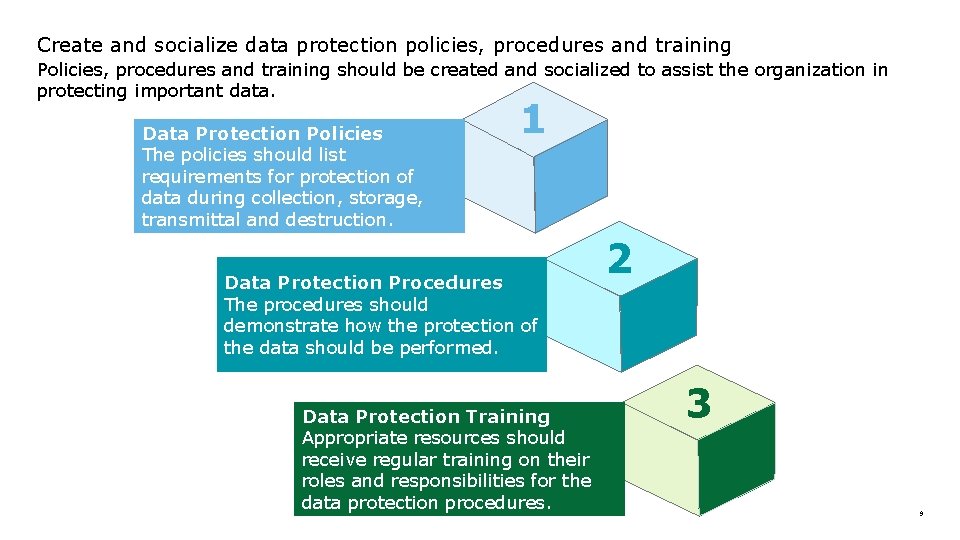
Create and socialize data protection policies, procedures and training Policies, procedures and training should be created and socialized to assist the organization in protecting important data. Data Protection Policies The policies should list requirements for protection of data during collection, storage, transmittal and destruction. 1 Data Protection Procedures The procedures should demonstrate how the protection of the data should be performed. Data Protection Training Appropriate resources should receive regular training on their roles and responsibilities for the data protection procedures. 2 3 9
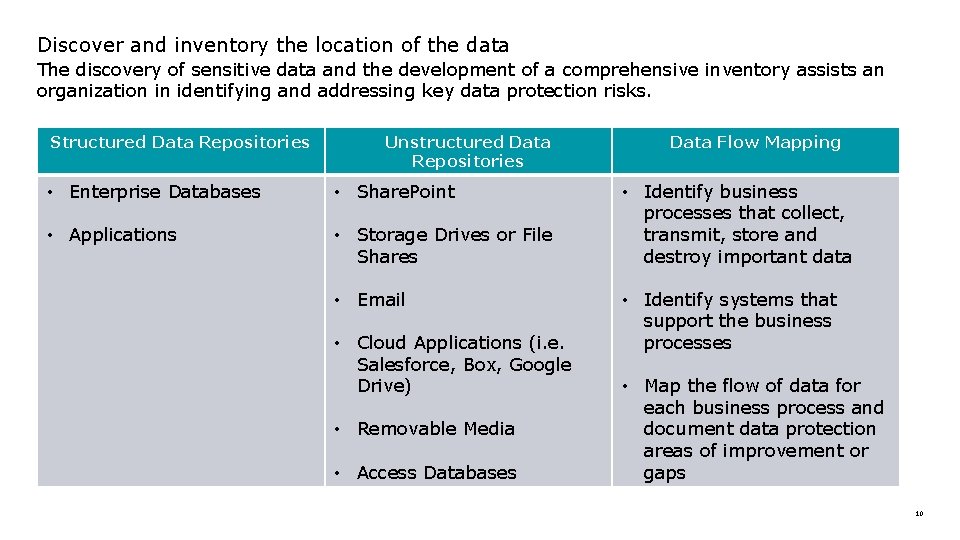
Discover and inventory the location of the data The discovery of sensitive data and the development of a comprehensive inventory assists an organization in identifying and addressing key data protection risks. Structured Data Repositories Unstructured Data Repositories • Enterprise Databases • Share. Point • Applications • Storage Drives or File Shares • Email • Cloud Applications (i. e. Salesforce, Box, Google Drive) • Removable Media • Access Databases Data Flow Mapping • Identify business processes that collect, transmit, store and destroy important data • Identify systems that support the business processes • Map the flow of data for each business process and document data protection areas of improvement or gaps 10
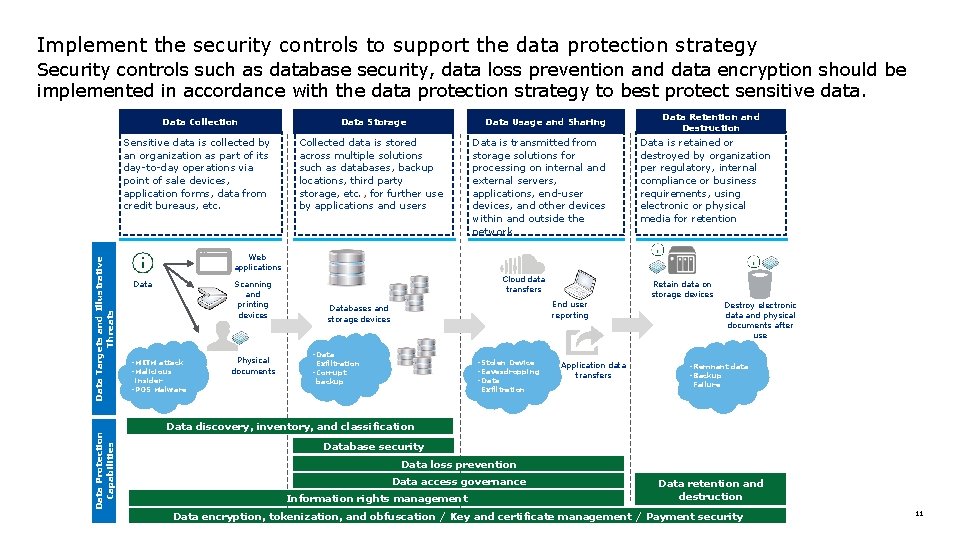
Implement the security controls to support the data protection strategy Data Protection Capabilities Data Targets and Illustrative Threats Security controls such as database security, data loss prevention and data encryption should be implemented in accordance with the data protection strategy to best protect sensitive data. Data Collection Data Storage Sensitive data is collected by an organization as part of its day-to-day operations via point of sale devices, application forms, data from credit bureaus, etc. Collected data is stored across multiple solutions such as databases, backup locations, third party storage, etc. , for further use by applications and users Data Usage and Sharing Data is transmitted from storage solutions for processing on internal and external servers, applications, end-user devices, and other devices within and outside the network Data Retention and Destruction Data is retained or destroyed by organization per regulatory, internal compliance or business requirements, using electronic or physical media for retention Web applications Data Scanning and printing devices - MITM attack - Malicious insider - POS Malware Physical documents Cloud data transfers Retain data on storage devices End user reporting Databases and storage devices - Data - Stolen Device - Eavesdropping - Data Exfiltration - Corrupt backup Exfiltration Application data transfers Destroy electronic data and physical documents after use - Remnant data - Backup Failure Data discovery, inventory, and classification Database security Data loss prevention Data access governance Information rights management Data retention and destruction Data encryption, tokenization, and obfuscation / Key and certificate management / Payment security 11
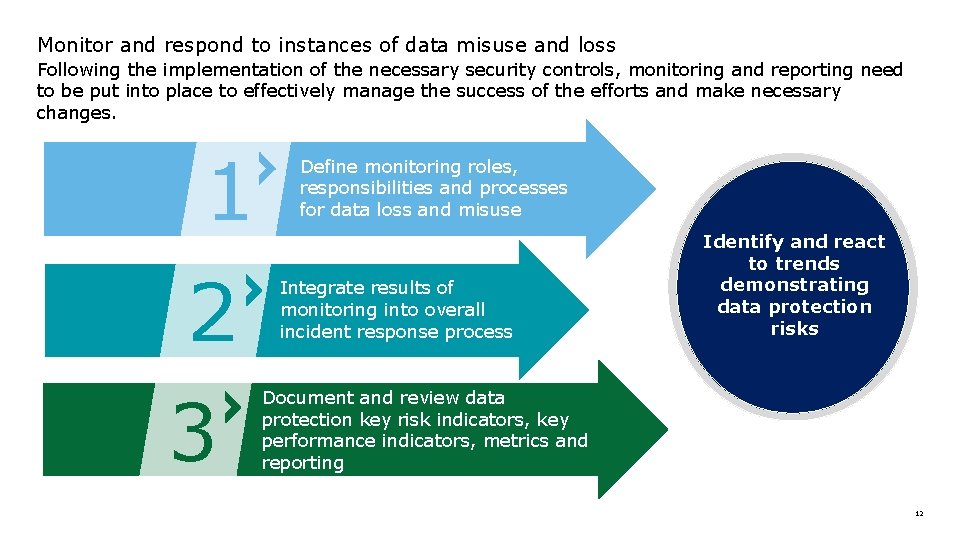
Monitor and respond to instances of data misuse and loss Following the implementation of the necessary security controls, monitoring and reporting need to be put into place to effectively manage the success of the efforts and make necessary changes. 1 2 3 Define monitoring roles, responsibilities and processes for data loss and misuse Integrate results of monitoring into overall incident response process Identify and react to trends demonstrating data protection risks Document and review data protection key risk indicators, key performance indicators, metrics and reporting 12
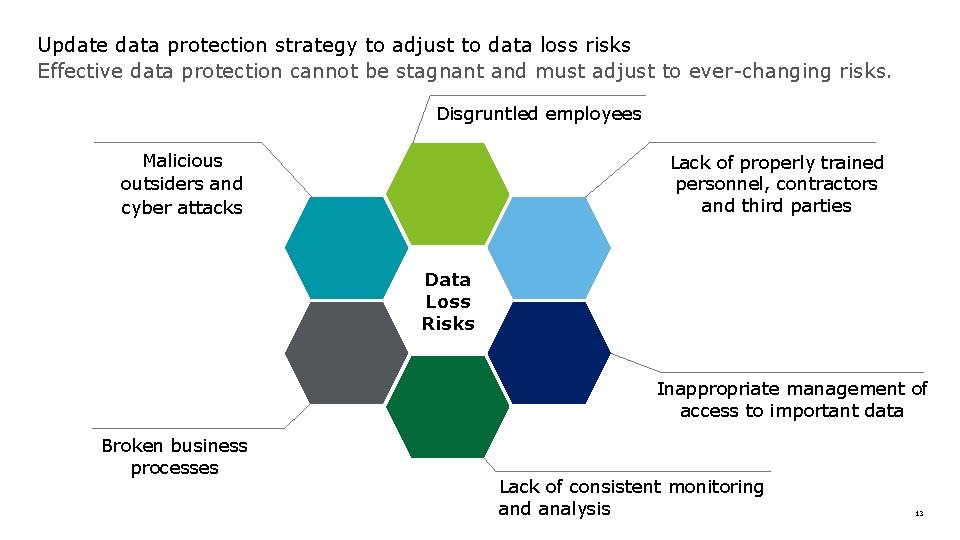
Update data protection strategy to adjust to data loss risks Effective data protection cannot be stagnant and must adjust to ever-changing risks. Disgruntled employees Malicious outsiders and cyber attacks Lack of properly trained personnel, contractors and third parties Data Loss Risks Inappropriate management of access to important data Broken business processes Lack of consistent monitoring and analysis 13

Questions? ? ? 14
- Slides: 14