Safeguarding Personally Identifiable Information PII Samuel P Jenkins
Safeguarding Personally Identifiable Information (PII) Samuel P. Jenkins Director for Privacy Defense Privacy and Civil Liberties Office Identity Protection and Management Expo Orlando, Florida April 2011 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Purpose The purpose of this presentation is to provide a summary of the administrative, physical, and technical safeguards that are applicable to systems that collect, use, maintain, or disseminate personally identifiable information (PII). 2 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE

Objectives u Upon completion of this presentation, you should be able to: Understand the role of safeguards that should be applied to systems of records (SORs). Explore the physical, technical, and administrative safeguards for protecting PII. Define the role of Privacy Impact Assessments and SORNs in safeguarding PII. 3 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Privacy Act and Safeguards u The Privacy Act of 1974 requires agencies to: Establish Rules of Conduct. Establish Safeguards. Maintain accurate, relevant, timely, and complete information. 4 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE

Privacy Act and Safeguards u Safeguards are used to protect agencies from “reasonably anticipated threats. ” Threats may cause harm, embarrassment, inconvenience, or unfairness. u Threats to personal information Unauthorized access. Unauthorized alteration. Unauthorized disclosure. 5 include: DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Privacy Act and Safeguards u Safeguards should be tailored to the: Size and sensitivity of each system. System-specific vulnerabilities. u Types of Safeguards: Administrative. Physical. Technical. 6 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Physical Safeguards 7 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Physical Safeguards u Paper records should be stored in locked cabinets. u Records being faxed or mailed should have a coversheet. u Facilities handling PII should be access controlled and hardware should be locked up. u Never leave files, storage media, or computers unattended or in vehicles. 8 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE

Physical Safeguards u Records Disposal – Retirement or deletion of a record does not obviate need for safeguards. Must render discarded info unrecognizable and beyond reconstruction. Destruction should be tailored to the time of media involved. ○ Paper – burn, shred. ○ Electronic – overwrite, degauss incinerate. 9 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE

Technical Safeguards 10 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Technical Safeguards u Security Requirements include: Encryption. Control Remote Access. Time-Out Function. Log and Verify. Ensure Understanding of Responsibilities. 11 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE

Technical Safeguards u Ensure all emails with PII are encrypted and that all recipients have a ‘need to know. ’ u Ensure records are access controlled. PII on shared drives should only be accessible to people with a ‘need to know’ u Ensure Social Security numbers (including the last 4) are not posted on public facing websites. 12 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Administrative Safeguards 13 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE

Admin Safeguards - Policies u Agencies must have policies in place for PII handling, specifically defining: Affected Individuals. Affected Actions. Consequences. 14 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguards - Training u Agencies are responsible to ensure staff handling PII are adequately trained: Training must be commensurate with an individual’s responsibilities. Training will be a prerequisite before permitted access to Do. D systems. Such training is mandatory for affected Do. D personnel and contractors. 15 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguards - Training u Components shall ensure receipt of Privacy Act training, such as: Orientation Training. Specialized Training. Management Training. Privacy Act Systems of Records Training. 16 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguards - Training u Annual Refresher Training. Provided to ensure continued understand of their responsibilities. All personnel with authorized access to PII shall annually acknowledging their understanding. 17 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguards - Training u Do. D Components shall expand their training materials and program to include specific privacy and security awareness segments to their training program(s). 18 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguards – Breach Handling u Existing Requirements: FISMA Requirements. Incident Handling and Response Mechanism. u OMB M-07 -16 modified breach reporting rules. u Modified Agency Reporting Requirements: US-CERT Modification. Develop and Publish a Routine Use. ○ 19 ○ Effective Response. DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE Disclosure of Information.
Admin Safeguards – Breach Handling u Breach Notification: Criteria to Consider: Whether Breach Notification is Required. Timeliness of the Notification. Source of the Notification. Contents of the Notification. Means of Providing Notification. Who Receives Notification: Public Outreach in Response to a Breach. 20 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguards – Review & Report u Under the Federal Information Security Management Act (FISMA) agencies must: Review PII holdings & report to Congress Annually. Review and reduce the volume of PII. Specifically, Agencies Must Reduce the Use of Social Security Numbers. ○ ○ 21 Eliminate Unnecessary Use. Explore Alternatives. DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguards – Review & Report u As part of FISMA privacy reporting, Do. D Components are required to: Confirm that they have established, or are in the process of establishing, PII review plans; or Provide a schedule for periodically updating their review of their holdings. u It is Do. D policy that: All automated systems containing PII are registered in the Defense Information Technology Portfolio Repository (DITPR). 22 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguard – Review & Report u It is Do. D policy that (continued): Updates to OMB be designed so that: ○ IT systems with PII reviewed on same cycle as Defense Information Assurance Certification and Accreditation Process (DIACAP). ○ PIA/SORNs reviewed at least once every two years. Components shall report results to DPCLO on FISMA schedule. 23 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Privacy Impact Assessments (PIA) & System of Records Notices (SORN) 24 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE

Admin Safeguards – PIAs & SORNs u A Privacy Impact Assessment (PIA) is an analysis of how information is handled to: Ensure handling conforms to applicable legal, regulatory, and policy requirements. Determine the risks and effects of collecting, using, maintaining, and disseminating PII in an electronic information system, and Mitigate potential privacy risks. OMB 03 -22 (9/26/2003), EGOV 208(b) 25 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguards – PIAs & SORNs u When is a PIA Required when PII is collected from: Existing information systems and electronic collections where a PIA has not previously been completed and that collects PII about Federal personnel and contractors. New information systems or electronic collections: ○ Prior to developing or purchasing; and ○ When converting paper records to electronic systems. 26 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguard – PIAs & SORNs u. A PIA is not required when the information system or electronic collection: Does not collect, maintain or disseminate personal identifying information. Is a National Security System (including systems that process classified information). 27 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Admin Safeguards – PIAs & SORNs u What is a SORN? A SORN is a public notice of an agency’s intent to collect & retrieve PII in a SORNs include: ○ The safeguards that will be applied to the system. ○ The who, what, why, and where of the system. ○ Processes for access and correction of records. A SORN must be published in the Federal 28 Register before a system can begin to collect PII. DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
PIA/SORN Essential Elements Crosswalk 29 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE

PIA/SORN Crosswalk Privacy Impact Assessment (PIA)/ System of Record Notice (SORN) Essential Elements Crosswalk PIA SORN What privacy information is collected Categories of Records in the System Why the information is collected Authority/Purpose(s) What the intended uses are for the information Purposes(s) With whom the information is shared Routine Uses What opportunities individuals have to decline to provide PII Privacy Act Statement/Notification procedure How information is secured Safeguards What privacy risks need to be addressed Narrative Statement/Probable or potential effects on the privacy of individuals. Whether a System of Records Notice (SORN) exists (Not applicable) 30 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
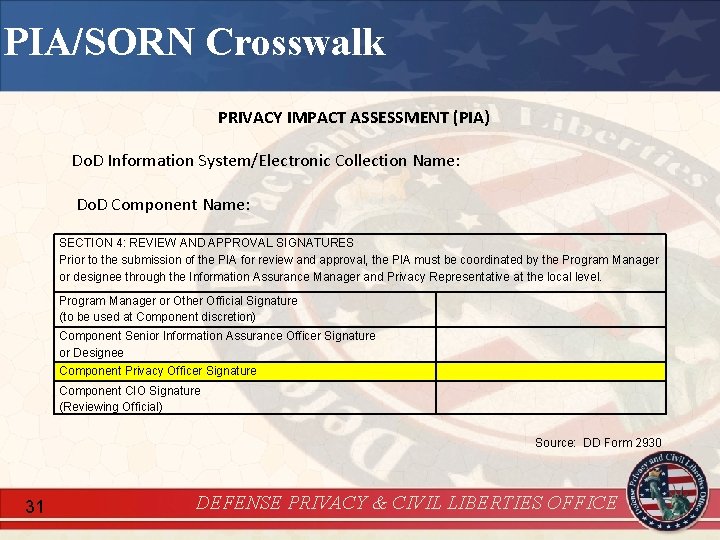
PIA/SORN Crosswalk PRIVACY IMPACT ASSESSMENT (PIA) Do. D Information System/Electronic Collection Name: Do. D Component Name: SECTION 4: REVIEW AND APPROVAL SIGNATURES Prior to the submission of the PIA for review and approval, the PIA must be coordinated by the Program Manager or designee through the Information Assurance Manager and Privacy Representative at the local level. Program Manager or Other Official Signature (to be used at Component discretion) Component Senior Information Assurance Officer Signature or Designee Component Privacy Officer Signature Component CIO Signature (Reviewing Official) Source: DD Form 2930 31 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
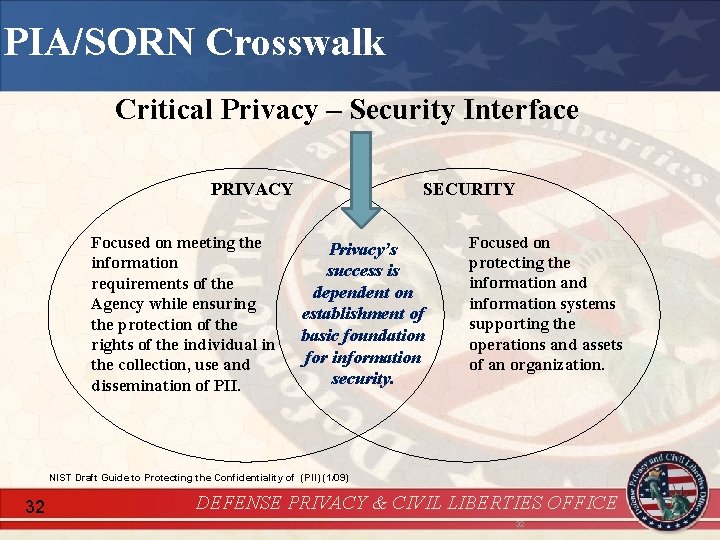
PIA/SORN Crosswalk Critical Privacy – Security Interface PRIVACY Focused on meeting the information requirements of the Agency while ensuring the protection of the rights of the individual in the collection, use and dissemination of PII. SECURITY Privacy’s success is dependent on establishment of basic foundation for information security. Focused on protecting the information and information systems supporting the operations and assets of an organization. NIST Draft Guide to Protecting the Confidentiality of (PII) (1/09) 32 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE 32
Summary u You should now be able to: Understand the role of safeguards that should be applied to systems of records (SORs). Explore the physical, technical, and administrative safeguards for protecting PII. Define the role of Privacy Impact Assessments and SORNs in safeguarding PII. 33 DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
Resources u u u Do. D 5400. 11 -R, Department of Defense Privacy Program, May 14, 2007. OMB M-07 -16, Safeguarding Against and Responding to the Breach of Personally Identifiable Information, May 22, 2007. Do. D Implementation: Safeguarding Against and Responding to the Breach of Personally Identifiable Information (PII), June 5, 2009. DD Form 2930, “Privacy Impact Assessment (PIA), ” 2008. OSD Memorandum 13798 -10, “Social Security Numbers Exposed on Public Facing & Open Government Websites. ” DEFENSE PRIVACY & CIVIL LIBERTIES OFFICE
- Slides: 34