Safe Zone Classic Encryption Issued by Mixof Tix
Safe. Zone --Classic Encryption-- Issued by_ Mixof. Tix Developers Network Director Network & Security Overview Information: URL: http: //www. Mixof. Tix. net E-Mail: info {AT} mixoftix {DOT} net Document # 7856 -SECU-EHR-01 © Mixof. Tix Developers Network July, 2006
n n n n Networking Solutions Security Between Particles Total Security Architecture Anti-Virus Compare Databases Compare Develoment Paltforms Analysis of Qo. S © Mixof. Tix Developers Network July, 2006

Networking Solutions © Mixof. Tix Developers Network July, 2006
Network Parts A core zone link to the distributed servers n Connection between particles is internet n Connections in core is Ethernet n © Mixof. Tix Developers Network July, 2006
Solutions for internet connection Leased line n Point 2 Point n Satellite n © Mixof. Tix Developers Network July, 2006
Network Protocol n TCP/IP © Mixof. Tix Developers Network July, 2006
Security Between Particles © Mixof. Tix Developers Network July, 2006
What is a firewall? n Different firewall technologies n Firewall functionalities n Firewall as a part of total security solution n © Mixof. Tix Developers Network July, 2006
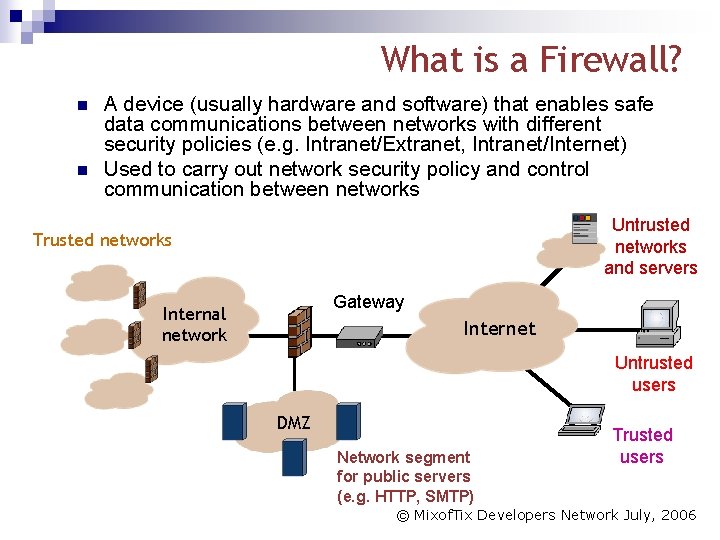
What is a Firewall? n n A device (usually hardware and software) that enables safe data communications between networks with different security policies (e. g. Intranet/Extranet, Intranet/Internet) Used to carry out network security policy and control communication between networks Untrusted networks and servers Trusted networks Gateway Internal network Internet Untrusted users DMZ Network segment for public servers (e. g. HTTP, SMTP) Trusted users © Mixof. Tix Developers Network July, 2006
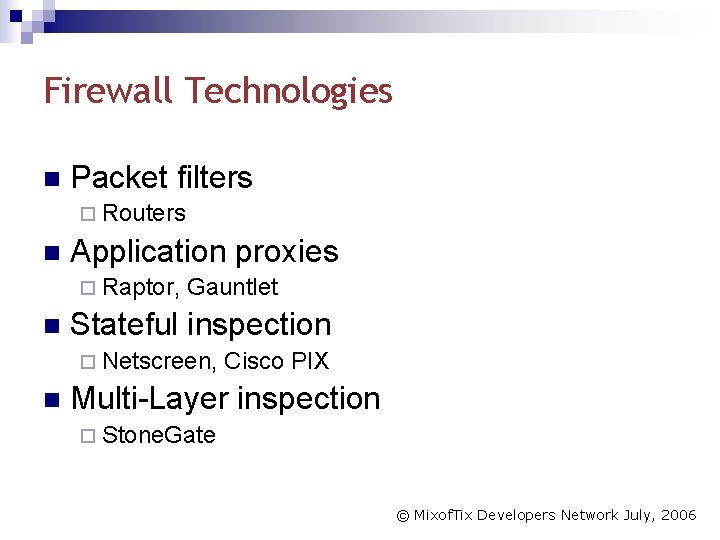
Firewall Technologies n Packet filters ¨ Routers n Application proxies ¨ Raptor, n Gauntlet Stateful inspection ¨ Netscreen, n Cisco PIX Multi-Layer inspection ¨ Stone. Gate © Mixof. Tix Developers Network July, 2006
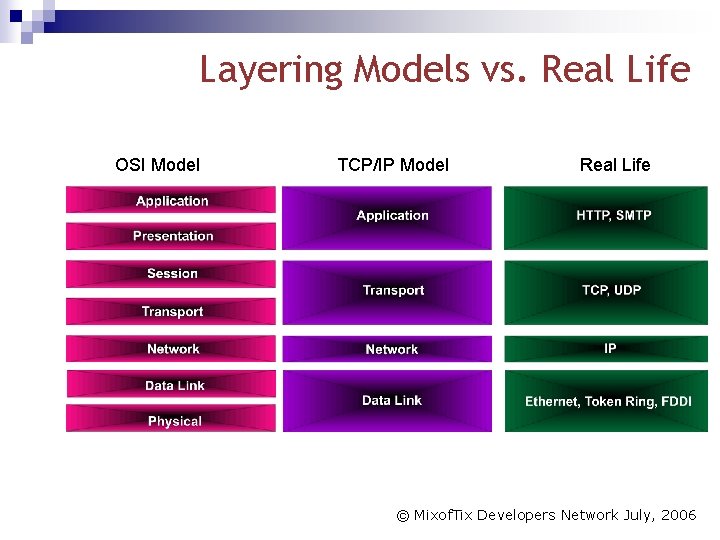
Layering Models vs. Real Life OSI Model TCP/IP Model Real Life © Mixof. Tix Developers Network July, 2006
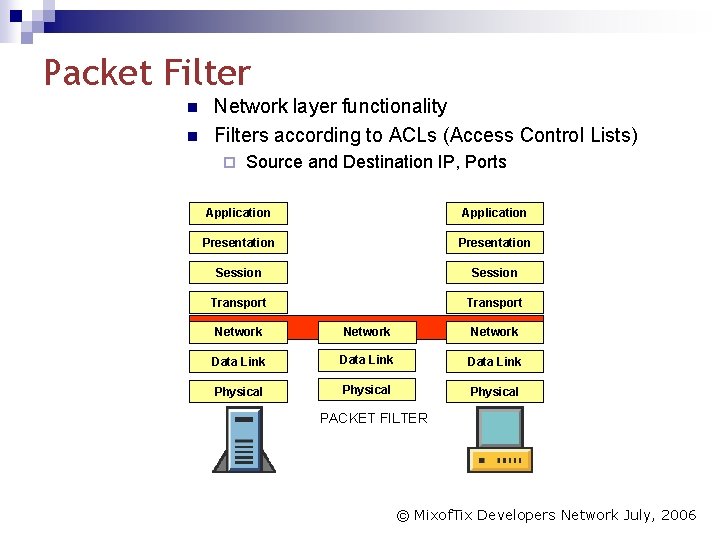
Packet Filter n n Network layer functionality Filters according to ACLs (Access Control Lists) ¨ Source and Destination IP, Ports Application Presentation Session Transport Network Data Link Physical PACKET FILTER © Mixof. Tix Developers Network July, 2006
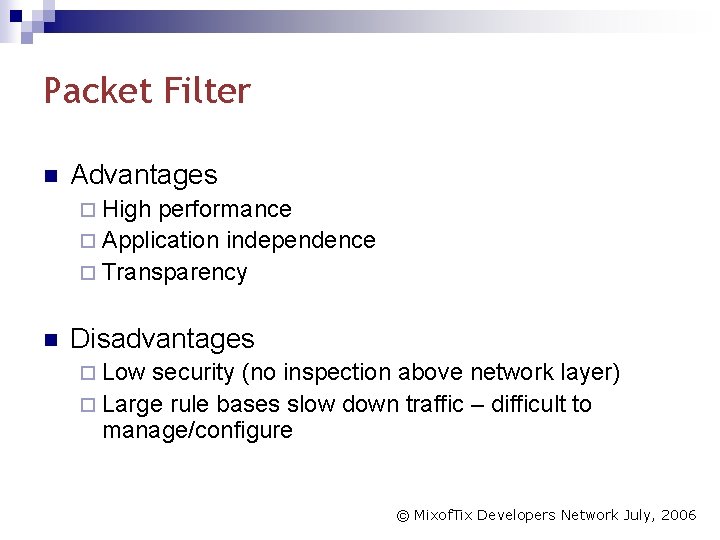
Packet Filter n Advantages ¨ High performance ¨ Application independence ¨ Transparency n Disadvantages ¨ Low security (no inspection above network layer) ¨ Large rule bases slow down traffic – difficult to manage/configure © Mixof. Tix Developers Network July, 2006
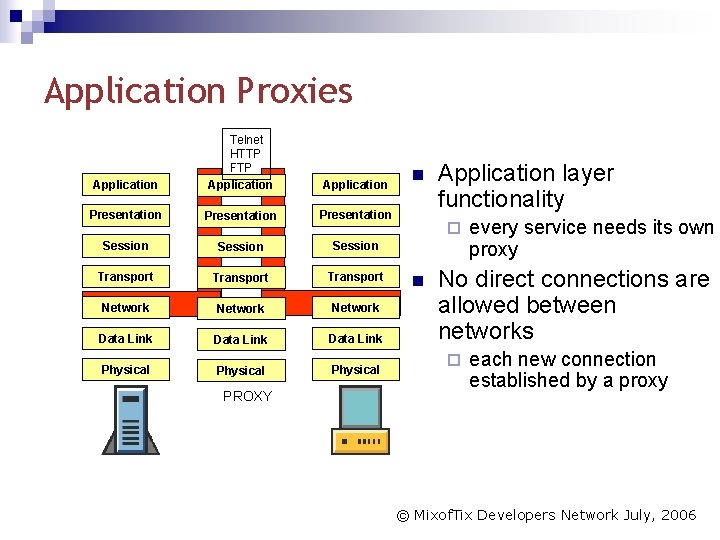
Application Proxies Application Telnet HTTP FTP Application Presentation Session Transport Network Data Link Physical PROXY n Application layer functionality ¨ n every service needs its own proxy No direct connections are allowed between networks ¨ each new connection established by a proxy © Mixof. Tix Developers Network July, 2006
Application Proxies n Advantages ¨ Very high security ¨ Application layer screening n Disadvantages ¨ Poor Performance ¨ Limited application support ¨ No connection failover © Mixof. Tix Developers Network July, 2006
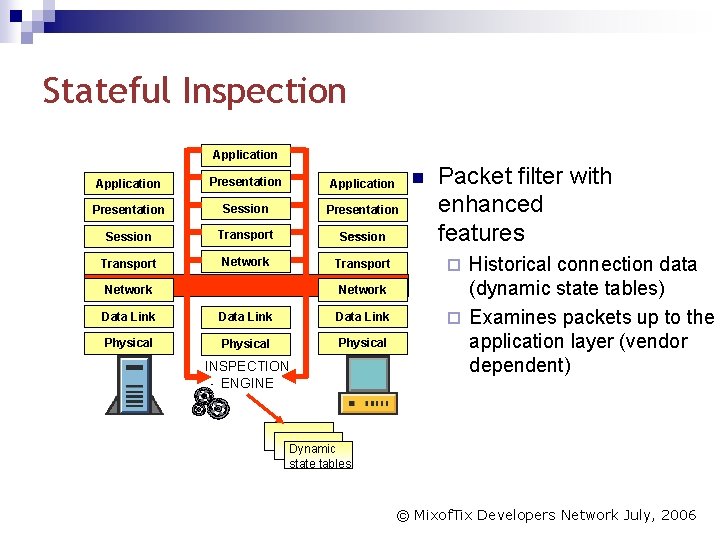
Stateful Inspection Application Presentation Session Transport Network Data Link Physical INSPECTION ENGINE Packet filter with enhanced features Historical connection data (dynamic state tables) ¨ Examines packets up to the application layer (vendor dependent) ¨ Dynamic state tables © Mixof. Tix Developers Network July, 2006
Stateful Inspection n Advantages ¨ Transparency ¨ Security ¨ Performance ¨ Scalability n (add-on products) Disadvantages ¨ Limited application layer screening © Mixof. Tix Developers Network July, 2006
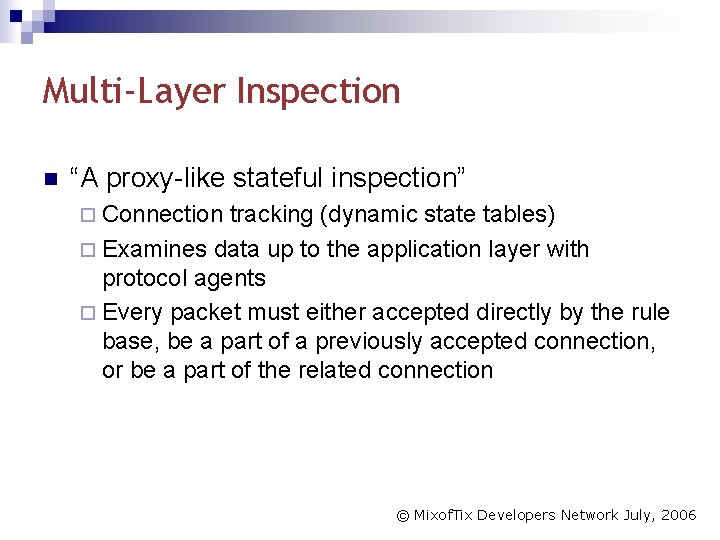
Multi-Layer Inspection n “A proxy-like stateful inspection” ¨ Connection tracking (dynamic state tables) ¨ Examines data up to the application layer with protocol agents ¨ Every packet must either accepted directly by the rule base, be a part of a previously accepted connection, or be a part of the related connection © Mixof. Tix Developers Network July, 2006
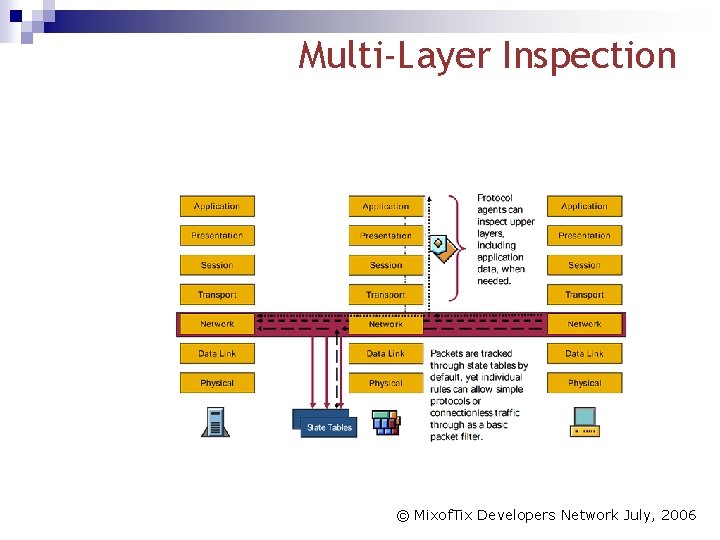
Multi-Layer Inspection © Mixof. Tix Developers Network July, 2006
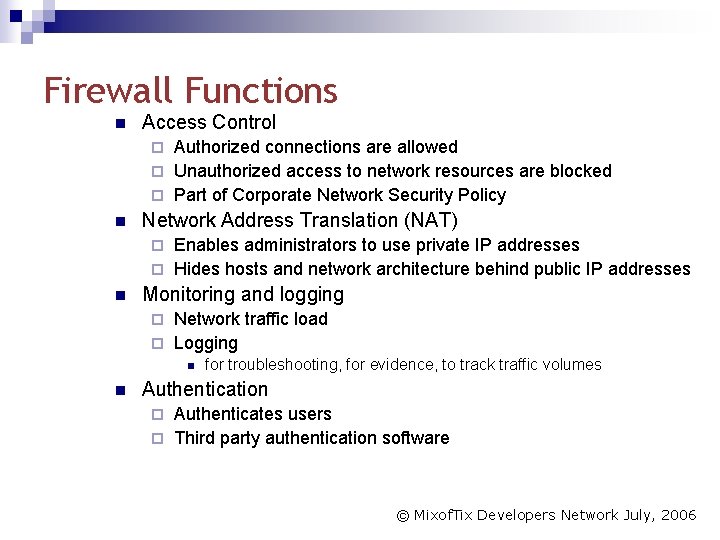
Firewall Functions n Access Control Authorized connections are allowed ¨ Unauthorized access to network resources are blocked ¨ Part of Corporate Network Security Policy ¨ n Network Address Translation (NAT) Enables administrators to use private IP addresses ¨ Hides hosts and network architecture behind public IP addresses ¨ n Monitoring and logging Network traffic load ¨ Logging ¨ n n for troubleshooting, for evidence, to track traffic volumes Authentication Authenticates users ¨ Third party authentication software ¨ © Mixof. Tix Developers Network July, 2006
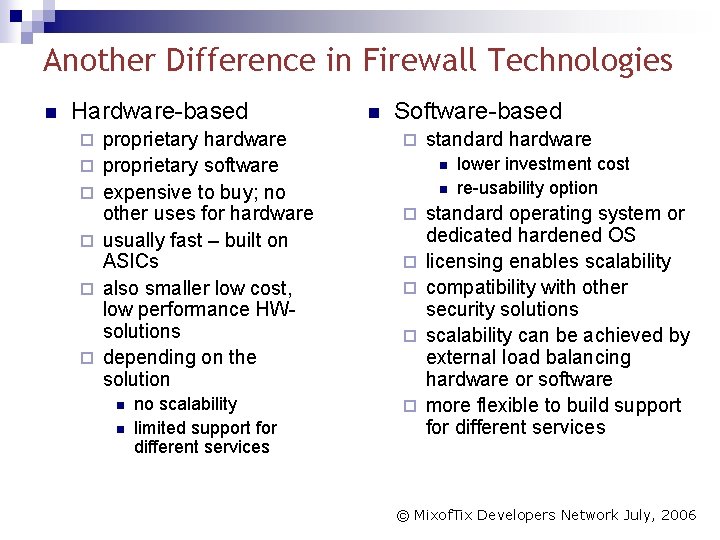
Another Difference in Firewall Technologies n Hardware-based ¨ ¨ ¨ n Software-based proprietary hardware proprietary software expensive to buy; no other uses for hardware usually fast – built on ASICs also smaller low cost, low performance HWsolutions depending on the solution ¨ no scalability limited support for different services ¨ n n standard hardware n n ¨ ¨ lower investment cost re-usability option standard operating system or dedicated hardened OS licensing enables scalability compatibility with other security solutions scalability can be achieved by external load balancing hardware or software more flexible to build support for different services © Mixof. Tix Developers Network July, 2006
Total Security Architecture © Mixof. Tix Developers Network July, 2006
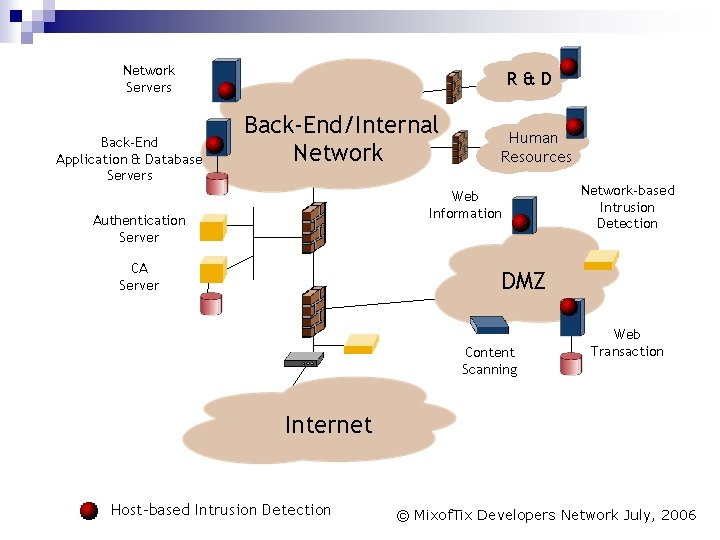
Network Servers Back-End Application & Database Servers R&D Back-End/Internal Network Human Resources Web Information Authentication Server CA Server Network-based Intrusion Detection DMZ Content Scanning Web Transaction Internet Host-based Intrusion Detection © Mixof. Tix Developers Network July, 2006
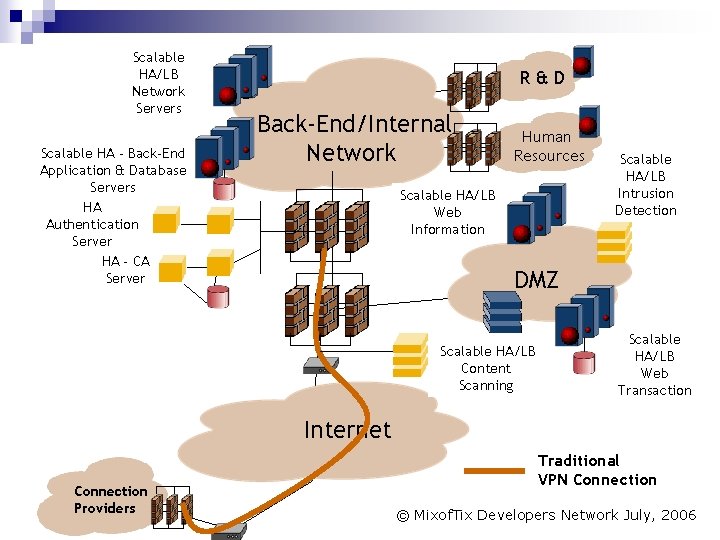
Scalable Network HA/LB Servers Network Servers Scalable. Back-End HA - Back-End Application&&Database Servers HAAuthentication Server HA - CA CA Server R&D Back-End/Internal Network Human Resources Scalable. Web HA/LB Web Information Scalable Intrusion HA/LB Detection Intrusion Detection DMZ Scalable HA/LB Content Scanning Web Scalable Transaction HA/LB Web Transaction Internet Connection Providers Traditional VPN Connection © Mixof. Tix Developers Network July, 2006
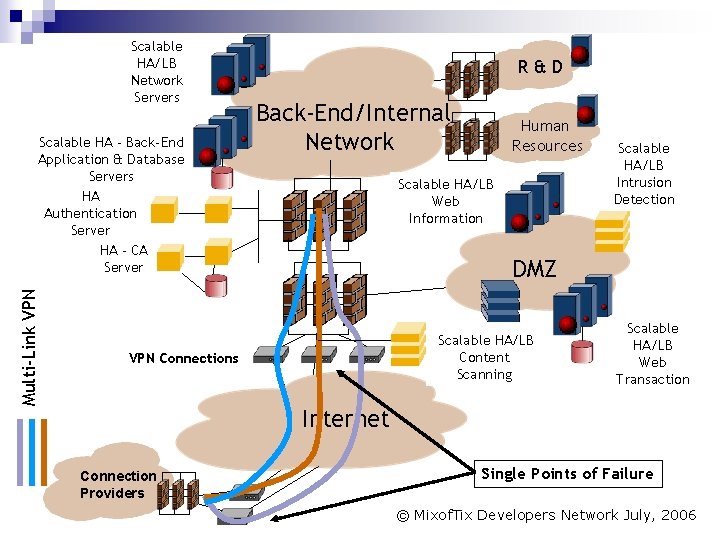
Scalable Network HA/LB Servers Network Servers Multi-Link VPN Scalable. Back-End HA - Back-End Application&&Database Servers HAAuthentication Server HA - CA CA Server R&D Back-End/Internal Network Human Resources Scalable. Web HA/LB Web Information Scalable Intrusion HA/LB Detection Intrusion Detection DMZ Scalable HA/LB Content Scanning VPN Connections Web Scalable Transaction HA/LB Web Transaction Internet Connection Providers Single Points of Failure © Mixof. Tix Developers Network July, 2006
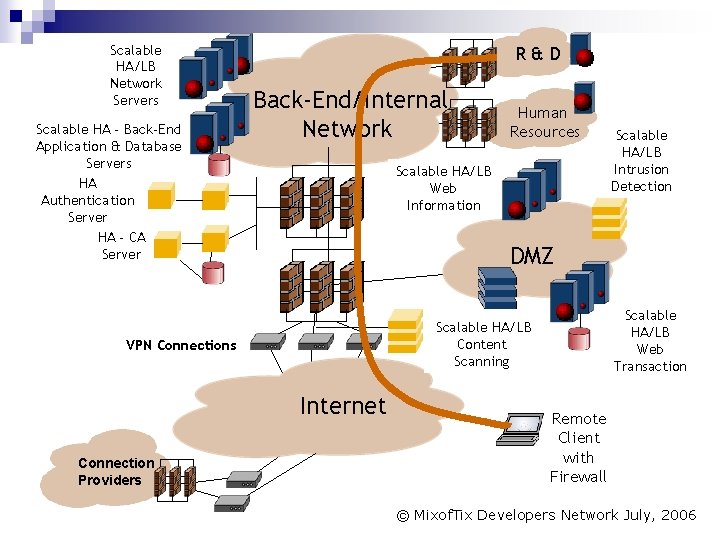
Network Scalable Servers HA/LB Network Servers Scalable. Back-End HA - Back-End Application&&Database Servers HAAuthentication Server HA - CA CA Server R&D Back-End/Internal Network Scalable. Web HA/LB Web Information Scalable Intrusion HA/LB Detection Intrusion Detection DMZ Web Scalable Transaction HA/LB Web Transaction Scalable HA/LB Content Scanning VPN Connections Internet Connection Providers Human Resources Remote Client with Firewall © Mixof. Tix Developers Network July, 2006
Functions of a VPNs facilitate the connection of LANs and clients (e. g. notebooks) via the Internet which is very low-priced and available worldwide. n By means of VPNs the corporate access via the Internet can be effected confidentially, independent of the selected media. n © Mixof. Tix Developers Network July, 2006
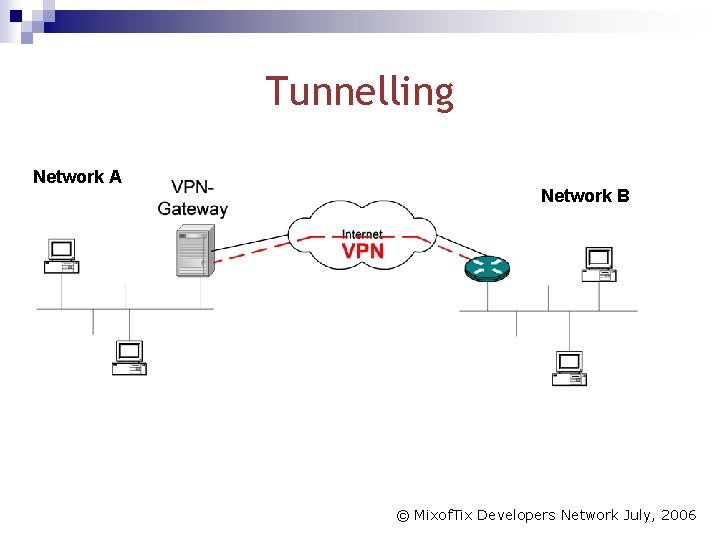
Tunnelling Network A Network B © Mixof. Tix Developers Network July, 2006
Layer 2 VPNs n n n Work on the OSI-layer 2 ¨ Security layer (data-link layer) Entire IP packets are „packed “ in the tunnel protocol Tunnel the point-to-point protocol (PPP) Use the functions of the PPP infrastructure ¨ DHCP ¨ User-oriented authentication ¨ Compression A layer-2 tunnel is a “virtual cable” ¨ Can be set up across any IP structure ¨ Supports multiple protocols © Mixof. Tix Developers Network July, 2006
Stone. Gate VPN n n n n VPN gateway with Stone. Gate technology DES, 3 DES, AES (256), Blowfish, CAST Managed through centralized management system Includes firewall IPSec compatible Comes with SG VPN client (includes personal firewall) Supported user authentication methods: ¨ RADIUS, TACACS+ or LDAP(S) back-end protocols ¨ Client certificates ¨ Smart Cards (PKCS#11, PKCS#15, Microsoft CAPI) ¨ USB tokens © Mixof. Tix Developers Network July, 2006
What is a CA A Certification authority is responsible for providing and assigning the keys for encryption, decryption and authentication. n A CA can issue certificates to a computer, a user account or a service. n © Mixof. Tix Developers Network July, 2006
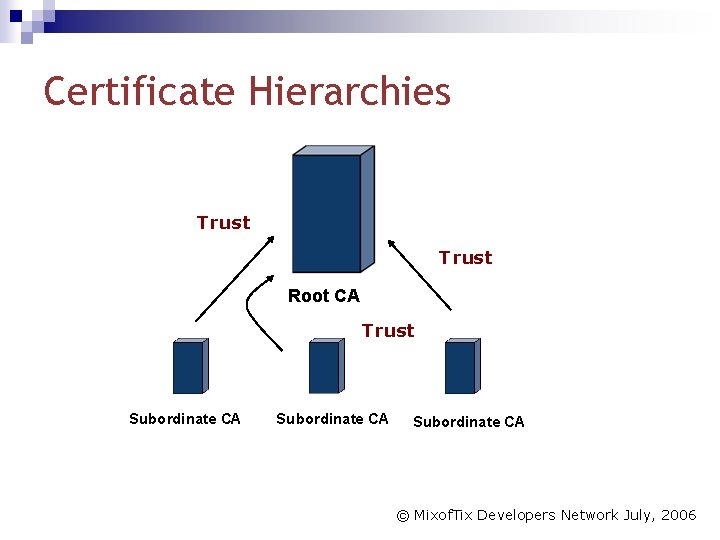
Certificate Hierarchies Trust Root CA Trust Subordinate CA © Mixof. Tix Developers Network July, 2006
Using Public Keys and Private Keys A private key which is kept confidential n A public key which is freely given out to all potential correspondents n © Mixof. Tix Developers Network July, 2006
Anti-Virus © Mixof. Tix Developers Network July, 2006
Anti Virus Features Centralized Management n Automatic Daily Updates n Minimum Reaction time n © Mixof. Tix Developers Network July, 2006
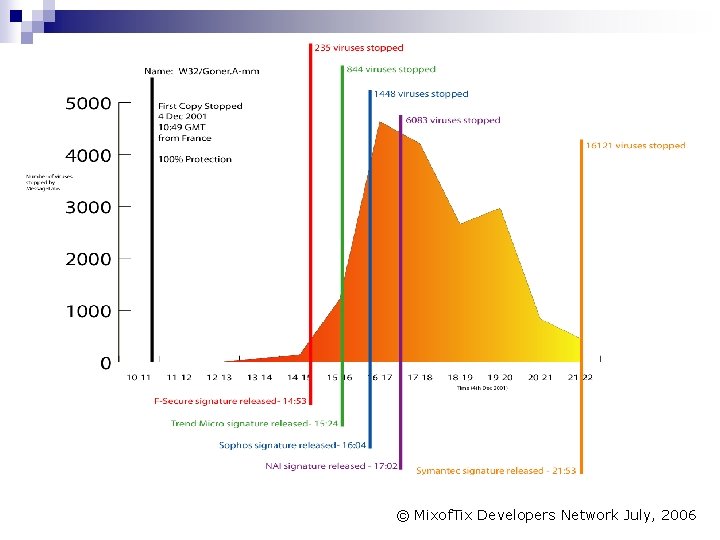
© Mixof. Tix Developers Network July, 2006
F-Secure n n Easy-to-use solution for keeping customers rapidly and automatically protected against fastspreading Internet-borne viruses and other malicious code F-Secure Anti-Virus protects both site-based and mobile workers, ensuring system availability and data integrity every minute of every day, everywhere in the world. © Mixof. Tix Developers Network July, 2006
Comapre Databases © Mixof. Tix Developers Network July, 2006
Technical Comparison of: Oracle vs. SQL Server vs. My. SQL © Mixof. Tix Developers Network July, 2006
PLATFORM AVAILABILITY Oracle 9 i Database is available on a large selection of hardware and operating systems, scaling from low-end uni-processor servers to large symmetrical multiprocessor machines to multi-node clusters. Oracle 9 i Database supports all major Unix platforms, including Linux, Microsoft operating systems, and a variety of other systems, including OS/390 mainframes. With Oracle 9 i, users are able to upgrade hardware and operating systems without changing or rewriting their applications. © Mixof. Tix Developers Network July, 2006
PLATFORM AVAILABILITY SQL Server 2000 only runs on Microsoft’s operating systems. Customers wishing to upgrade hardware limited to platforms running these systems and must face the cost of converting their systems completely if they ever outgrow the capacity of their platform. © Mixof. Tix Developers Network July, 2006
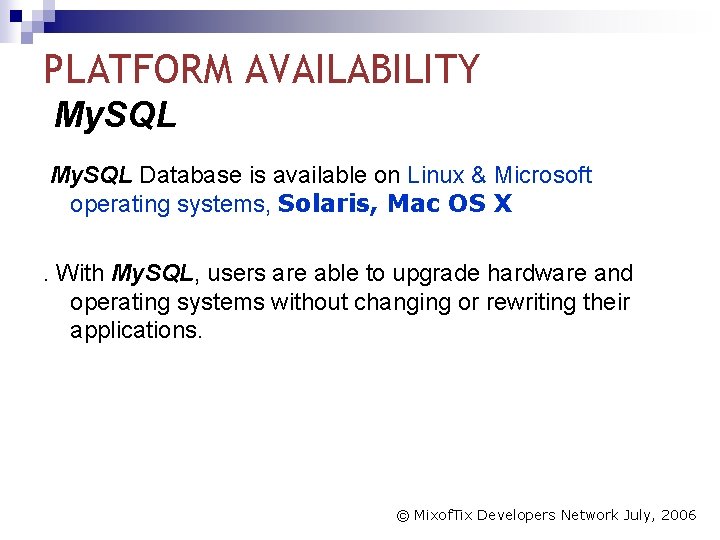
PLATFORM AVAILABILITY My. SQL Database is available on Linux & Microsoft operating systems, Solaris, Mac OS X. With My. SQL, users are able to upgrade hardware and operating systems without changing or rewriting their applications. © Mixof. Tix Developers Network July, 2006
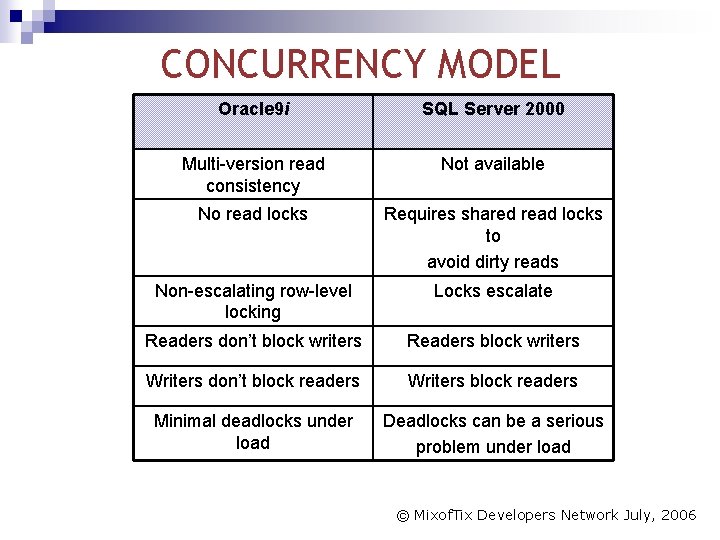
CONCURRENCY MODEL Oracle 9 i SQL Server 2000 Multi-version read consistency Not available No read locks Requires shared read locks to avoid dirty reads Non-escalating row-level locking Locks escalate Readers don’t block writers Readers block writers Writers don’t block readers Writers block readers Minimal deadlocks under load Deadlocks can be a serious problem under load © Mixof. Tix Developers Network July, 2006
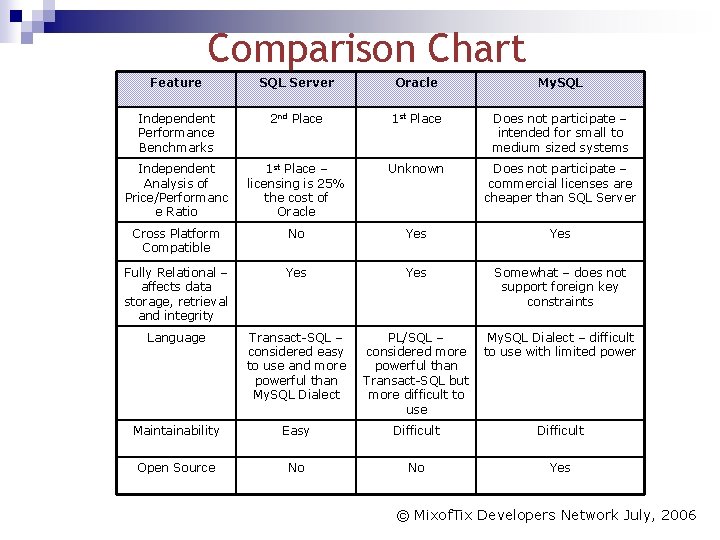
Comparison Chart Feature SQL Server Oracle My. SQL Independent Performance Benchmarks 2 nd Place 1 st Place Does not participate – intended for small to medium sized systems Independent Analysis of Price/Performanc e Ratio 1 st Place – licensing is 25% the cost of Oracle Unknown Does not participate – commercial licenses are cheaper than SQL Server Cross Platform Compatible No Yes Fully Relational – affects data storage, retrieval and integrity Yes Somewhat – does not support foreign key constraints Language Transact-SQL – considered easy to use and more powerful than My. SQL Dialect Maintainability Easy Difficult Open Source No No Yes PL/SQL – My. SQL Dialect – difficult considered more to use with limited powerful than Transact-SQL but more difficult to use © Mixof. Tix Developers Network July, 2006
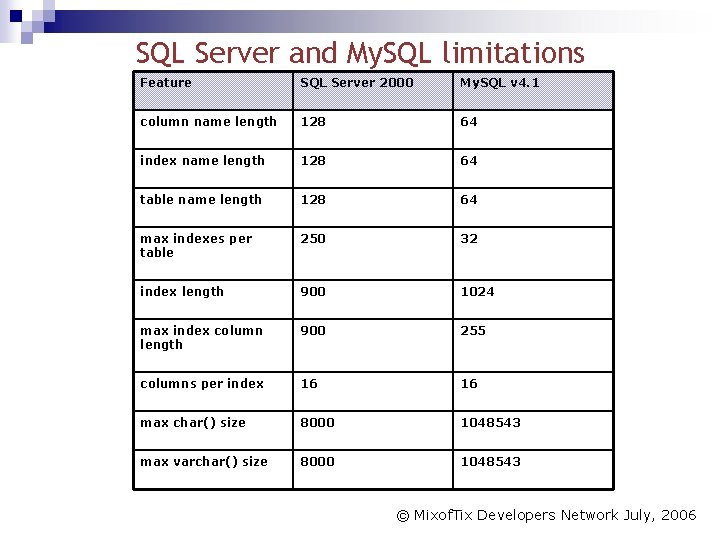
SQL Server and My. SQL limitations Feature SQL Server 2000 My. SQL v 4. 1 column name length 128 64 index name length 128 64 table name length 128 64 max indexes per table 250 32 index length 900 1024 max index column length 900 255 columns per index 16 max char() size 8000 1048543 max varchar() size 8000 1048543 © Mixof. Tix Developers Network July, 2006
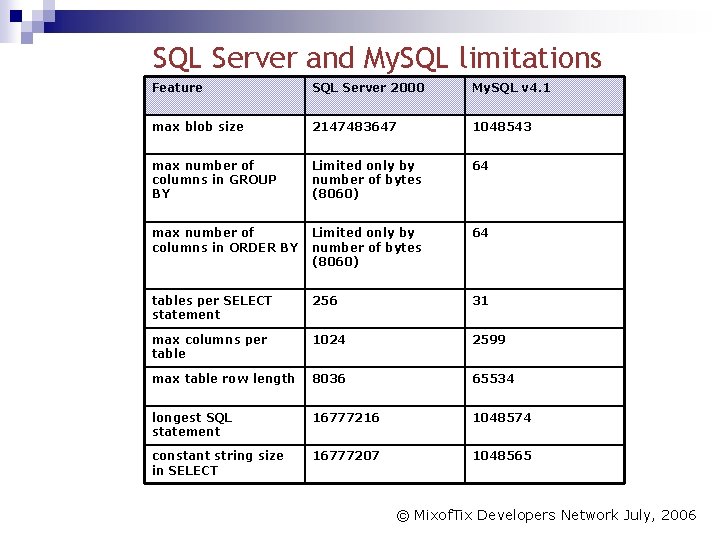
SQL Server and My. SQL limitations Feature SQL Server 2000 My. SQL v 4. 1 max blob size 2147483647 1048543 max number of columns in GROUP BY Limited only by number of bytes (8060) 64 max number of columns in ORDER BY Limited only by number of bytes (8060) 64 tables per SELECT statement 256 31 max columns per table 1024 2599 max table row length 8036 65534 longest SQL statement 16777216 1048574 constant string size in SELECT 16777207 1048565 © Mixof. Tix Developers Network July, 2006
Compare Development Platforms © Mixof. Tix Developers Network July, 2006
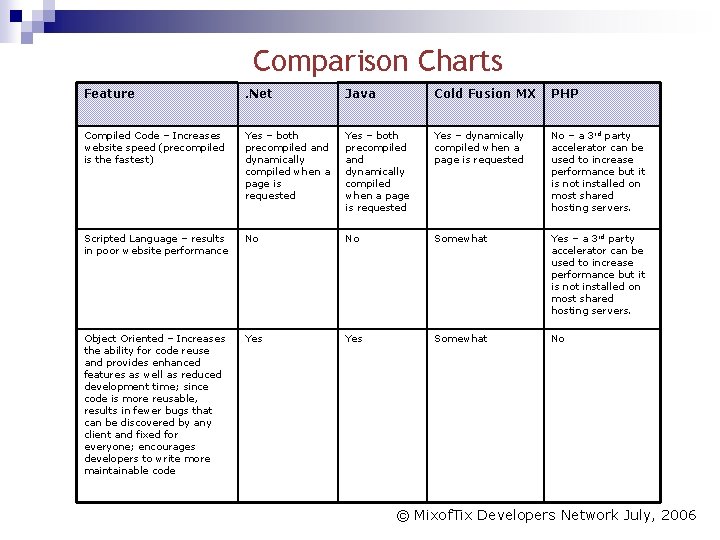
Comparison Charts Feature . Net Java Cold Fusion MX PHP Compiled Code – Increases website speed (precompiled is the fastest) Yes – both precompiled and dynamically compiled when a page is requested Yes – dynamically compiled when a page is requested No – a 3 rd party accelerator can be used to increase performance but it is not installed on most shared hosting servers. Scripted Language – results in poor website performance No No Somewhat Yes – a 3 rd party accelerator can be used to increase performance but it is not installed on most shared hosting servers. Object Oriented – Increases the ability for code reuse and provides enhanced features as well as reduced development time; since code is more reusable, results in fewer bugs that can be discovered by any client and fixed for everyone; encourages developers to write more maintainable code Yes Somewhat No © Mixof. Tix Developers Network July, 2006
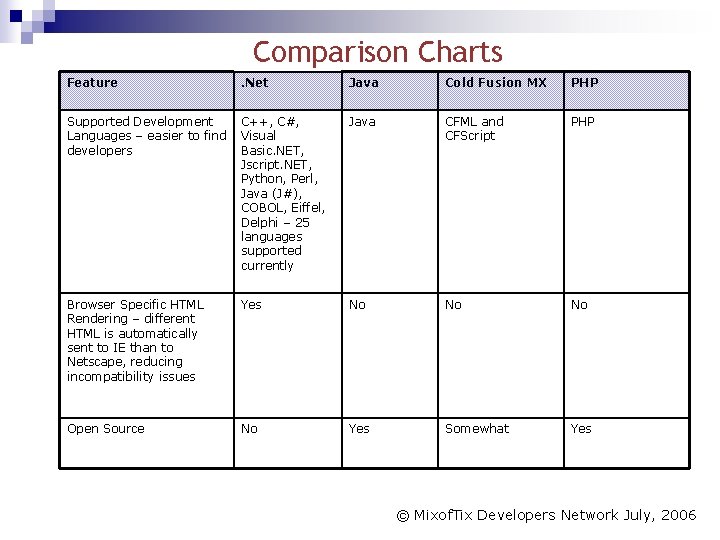
Comparison Charts Feature . Net Java Cold Fusion MX PHP Supported Development C++, C#, Languages – easier to find Visual developers Basic. NET, Jscript. NET, Python, Perl, Java (J#), COBOL, Eiffel, Delphi – 25 languages supported currently Java CFML and CFScript PHP Browser Specific HTML Rendering – different HTML is automatically sent to IE than to Netscape, reducing incompatibility issues Yes No No No Open Source No Yes Somewhat Yes © Mixof. Tix Developers Network July, 2006
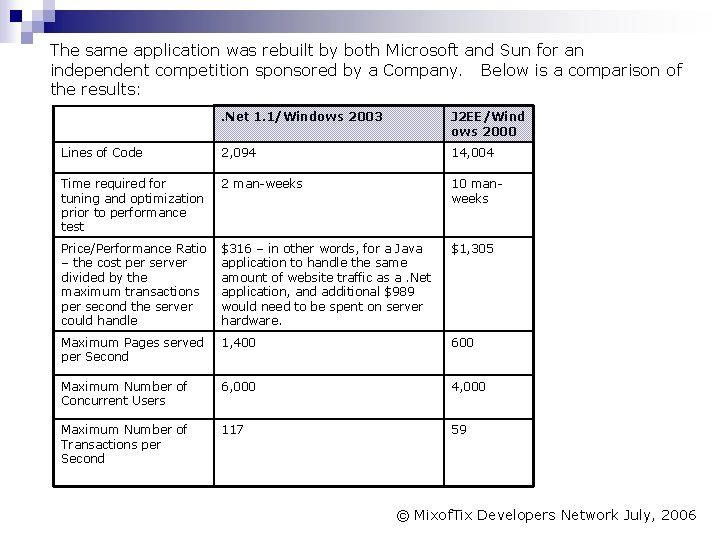
The same application was rebuilt by both Microsoft and Sun for an independent competition sponsored by a Company. Below is a comparison of the results: . Net 1. 1/Windows 2003 J 2 EE/Wind ows 2000 Lines of Code 2, 094 14, 004 Time required for tuning and optimization prior to performance test 2 man-weeks 10 manweeks Price/Performance Ratio – the cost per server divided by the maximum transactions per second the server could handle $316 – in other words, for a Java application to handle the same amount of website traffic as a. Net application, and additional $989 would need to be spent on server hardware. $1, 305 Maximum Pages served per Second 1, 400 600 Maximum Number of Concurrent Users 6, 000 4, 000 Maximum Number of Transactions per Second 117 59 © Mixof. Tix Developers Network July, 2006
Analysis of Qo. S © Mixof. Tix Developers Network July, 2006
Applications Requirements n n n Advance Resource Reservation Policy Agreement Protocol Security Simplicity Scalability © Mixof. Tix Developers Network July, 2006
Advance Resource Reservation The system should support mechanisms for advance, immediate, or ‘on-demand’ resource reservation. Advance reservation is particularly important when dealing with scarce resources, as is often the case with high-end resources made available. © Mixof. Tix Developers Network July, 2006
Reservation Policy The system should support a mechanism that allows resource owners to enforce their policies governing when, how, and who can use their resource. This should be undertaken while decoupling reservation and policy entities, in order to improve reservation flexibility © Mixof. Tix Developers Network July, 2006
Agreement Protocol The system should assure the clients of their advance reservation status, and the resource quality they expect during the service session. Such assurance can be contained in an agreement protocol, such as Service Level Agreements (SLAs). © Mixof. Tix Developers Network July, 2006
Security The system should prevent malicious users penetrating, or altering, data repositories that hold information about reservations, policies and agreement protocols. In addition to a secure channel between an application and the resources it uses, a security infrastructure that provides support for authentication, authorization and access control should be provided. © Mixof. Tix Developers Network July, 2006
Simplicity The Qo. S enhancement should have a reasonably simple design that requires minimal changes to be made to existing computation, storage or network infrastructure. © Mixof. Tix Developers Network July, 2006
Scalability The approach should be scalable to a large number of entities, since the System is a global-scale infrastructure. This is especially true as the System are expected to be open and dynamic, with resources and users joining and leaving the System in a nondeterministic manner. © Mixof. Tix Developers Network July, 2006
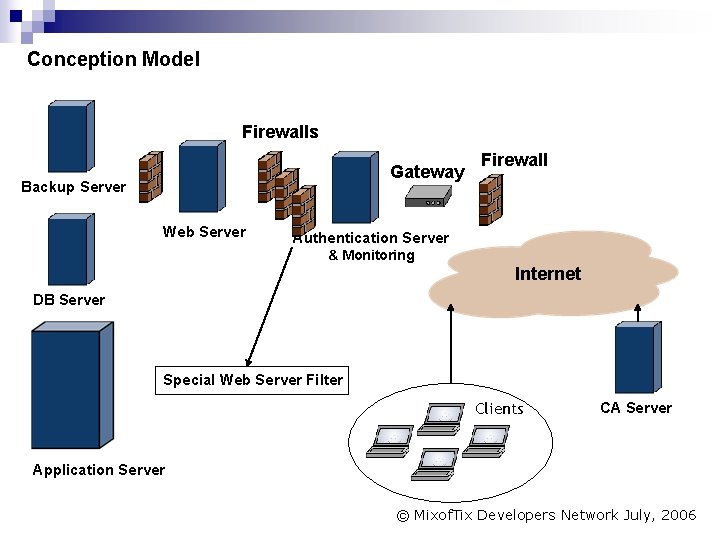
Conception Model Firewalls Gateway Backup Server Web Server Firewall Authentication Server & Monitoring Internet DB Server Special Web Server Filter Clients CA Server Application Server © Mixof. Tix Developers Network July, 2006

Discussion - Q&A © Mixof. Tix Developers Network July, 2006
- Slides: 60