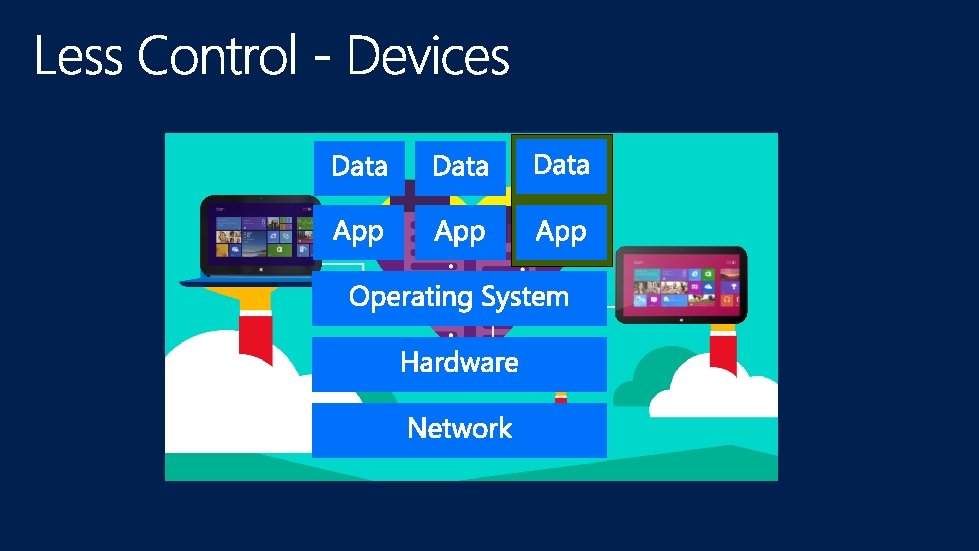
Saa S Paa S Iaa S B Bring




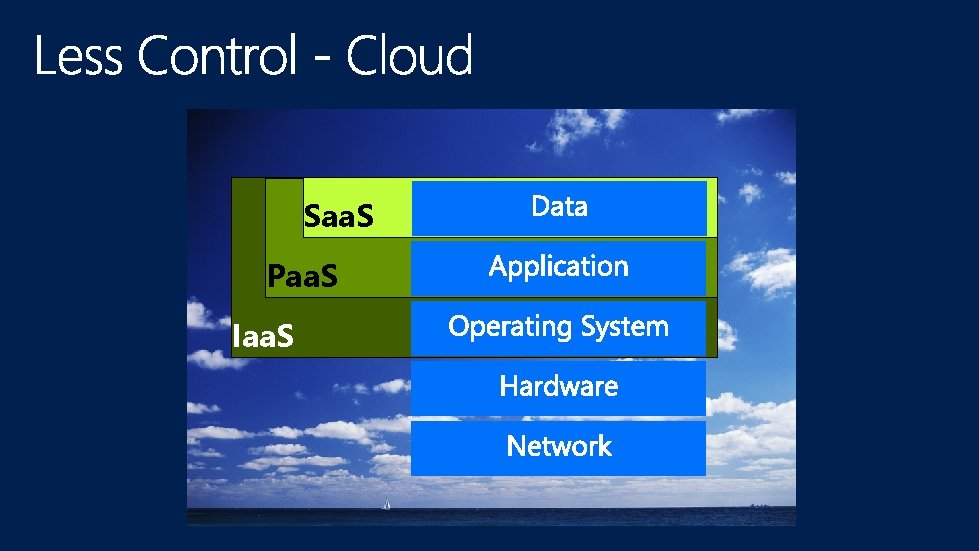
Saa. S Paa. S Iaa. S
B Bring Y Your O Own D Disaster


This is, in fact, the only risk to which we can lose the entire company. Chief Risk Manager

Competitors want your Intellectual Property Intel Agencies want your personal data Organized crime wants your money Terrorists want your life

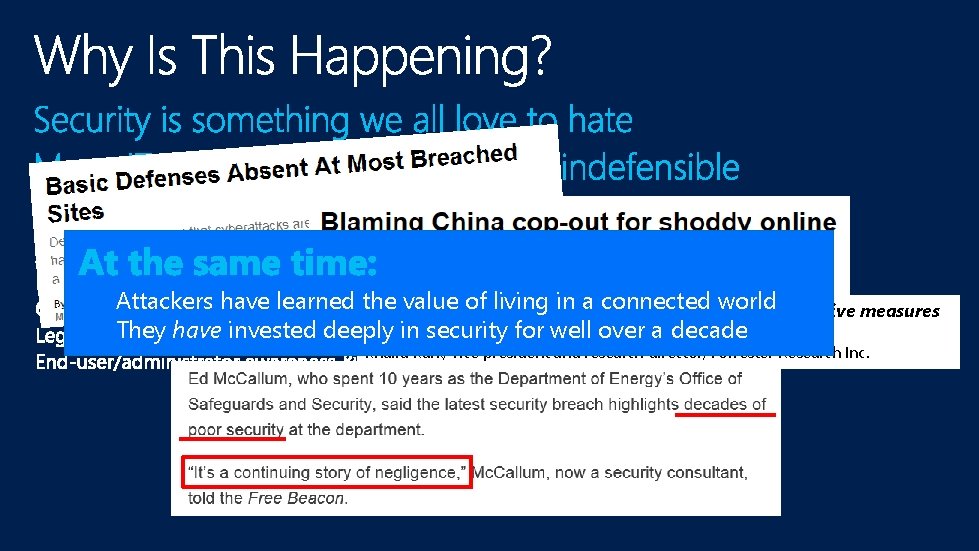
Attackers have learned the value of gap living in a connected world There’s a huge between the threats and our protective measures They have invested deeply in security well over a decade to defend against for those attacks. Khalid Kark, vice president and research director, Forrester Research Inc.


“If you protect your paper clips and diamonds with equal vigor, you’ll soon have more paper clips and fewer diamonds” -Attributed to Dean Rusk, US Secretary of State, 1961 -1969
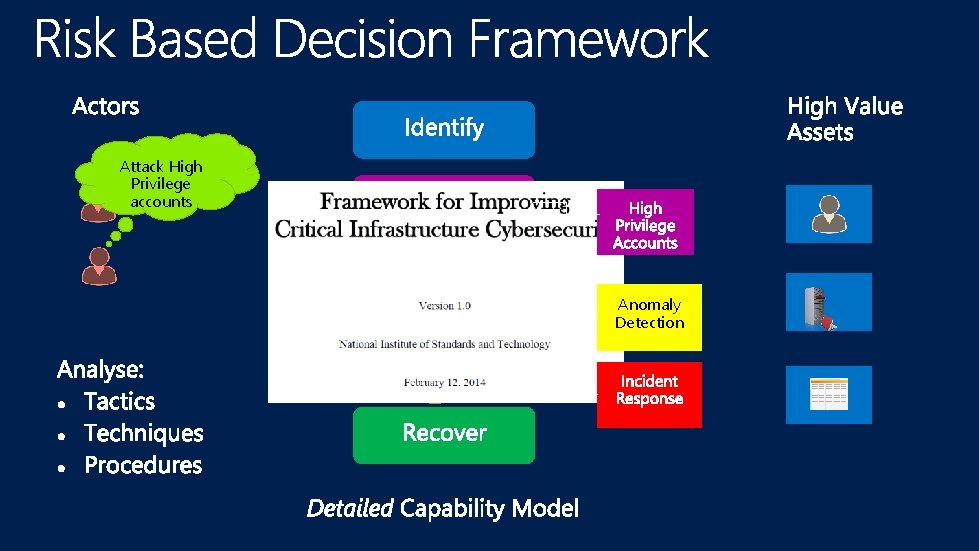
Attack High Privilege accounts Desired Current state Cyber Detect Capabilities Anomaly Detection

One More Thing… No such thing as a silver bullet…

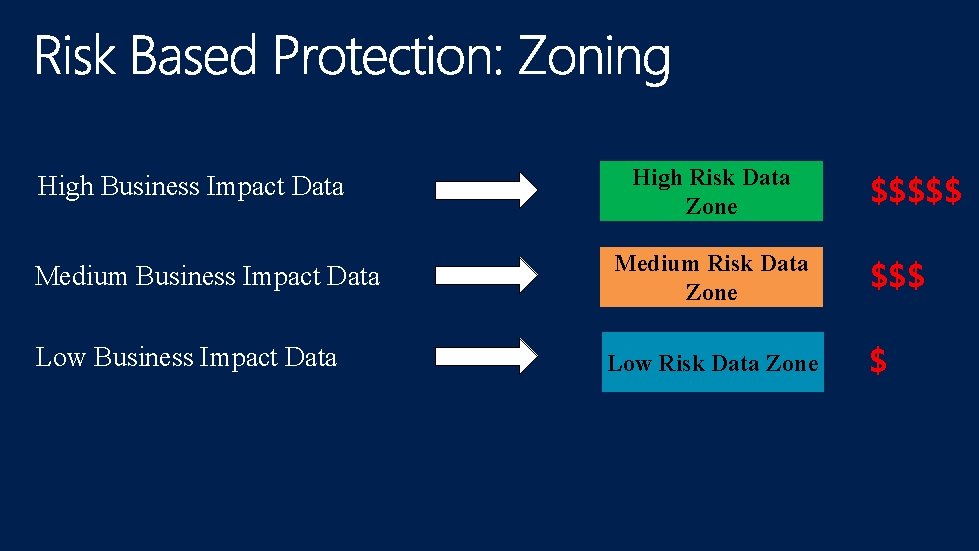
High Business Impact Data Medium Business Impact Data Low Business Impact Data High Risk Data Zone Medium Risk Data Zone Low Risk Data Zone $$$$$ $
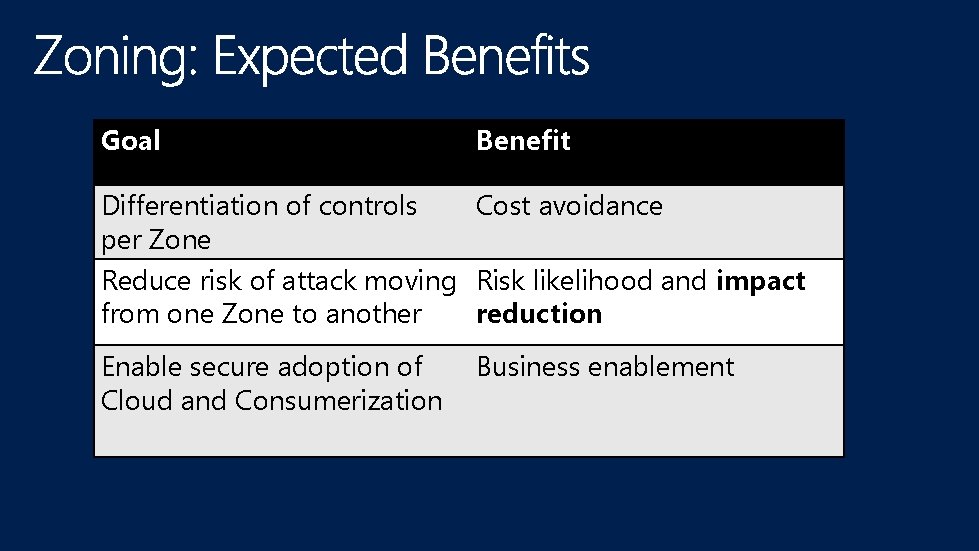
Goal Benefit Differentiation of controls Cost avoidance per Zone Reduce risk of attack moving Risk likelihood and impact from one Zone to another reduction Enable secure adoption of Cloud and Consumerization Business enablement
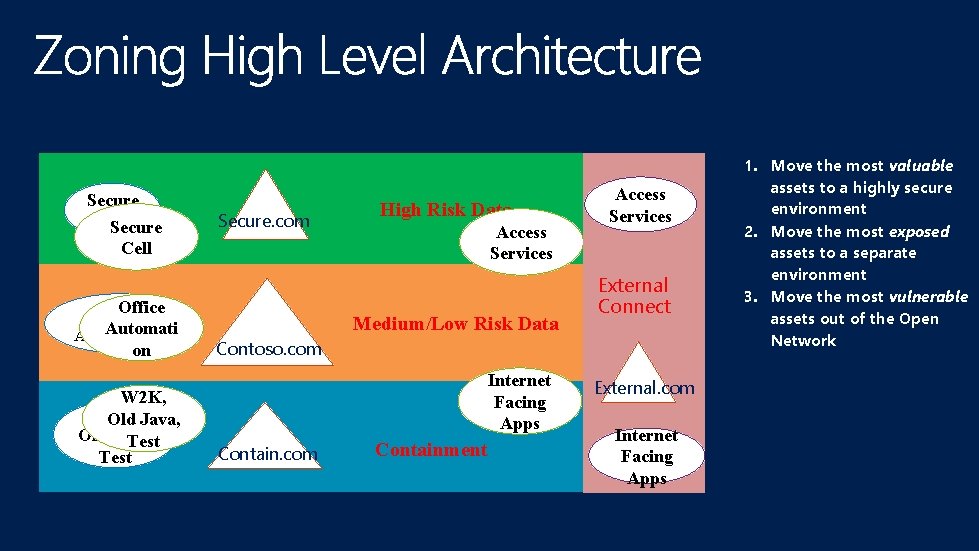
Secure Cell Secure. com High Risk Data Access Services Office One Open Network Office Medium/Low Risk Data Automation Contoso. com on W 2 K, Old Java, Test Contoso. com Containment Internet Facing Apps Access Services External Connect External. com Internet Facing Apps 1. Move the most valuable assets to a highly secure environment 2. Move the most exposed assets to a separate environment 3. Move the most vulnerable assets out of the Open Network

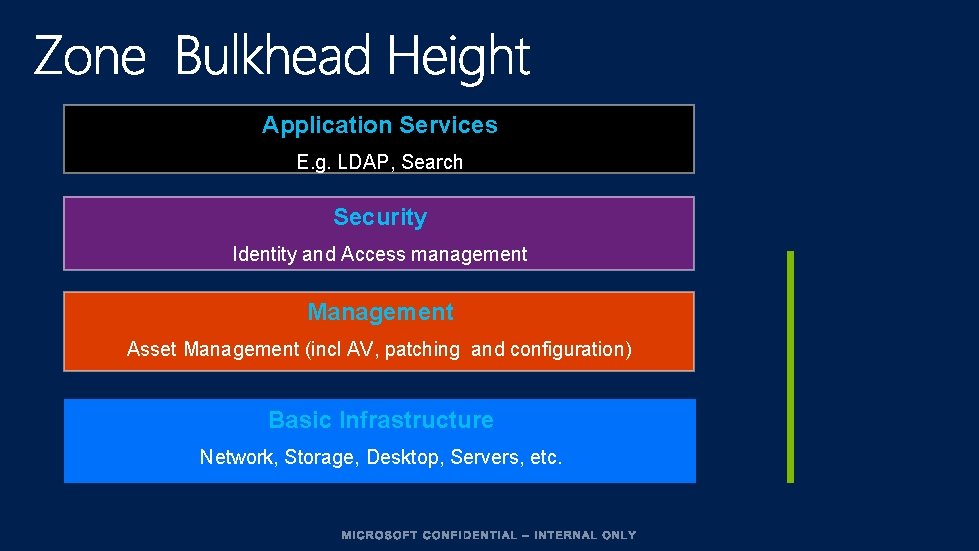
Application Services E. g. LDAP, Search Security Identity and Access management Management Asset Management (incl AV, patching and configuration) Basic Infrastructure Network, Storage, Desktop, Servers, etc.
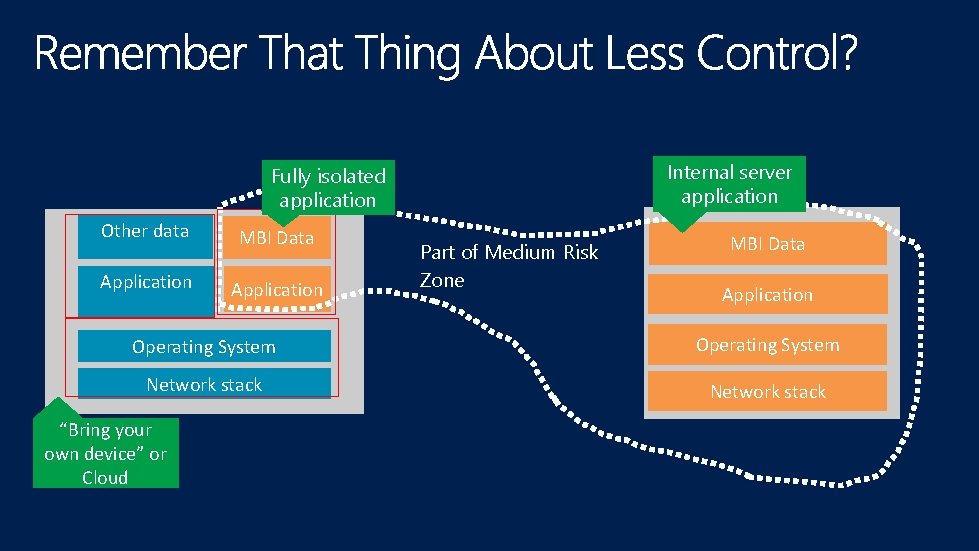
Internal server application Fully isolated application Other data MBI Data Application Part of Medium Risk Zone MBI Data Application Operating System Network stack “Bring your own device” or Cloud

Example Controls Start Data Protection Adequate? Yes Done Encryption (e. g. RMS) Done Sandboxing, Presentation virtualization (e. g. RDS) No Application Protection Adequate? Yes No Operating System Network stack Adequate? Yes No Fully managed corporate device Done Health check/contractual, Mobile Device Management




Power: Domain Controllers Data: Servers and Applications Access: Users and Workstations DCIM-B 213 TWC: Pass-the-Hash and Credential Theft Mitigation Architectures DCIM-B 359 TWC: Pass-the-Hash: How Attackers Spread and How to Stop Them


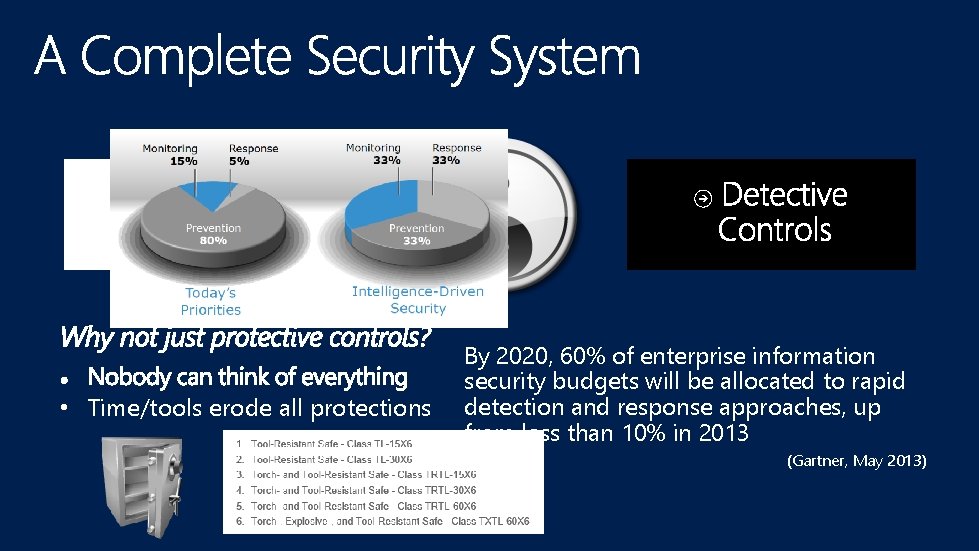
Protective Controls • Time/tools erode all protections By 2020, 60% of enterprise information security budgets will be allocated to rapid detection and response approaches, up from less than 10% in 2013 (Gartner, May 2013)
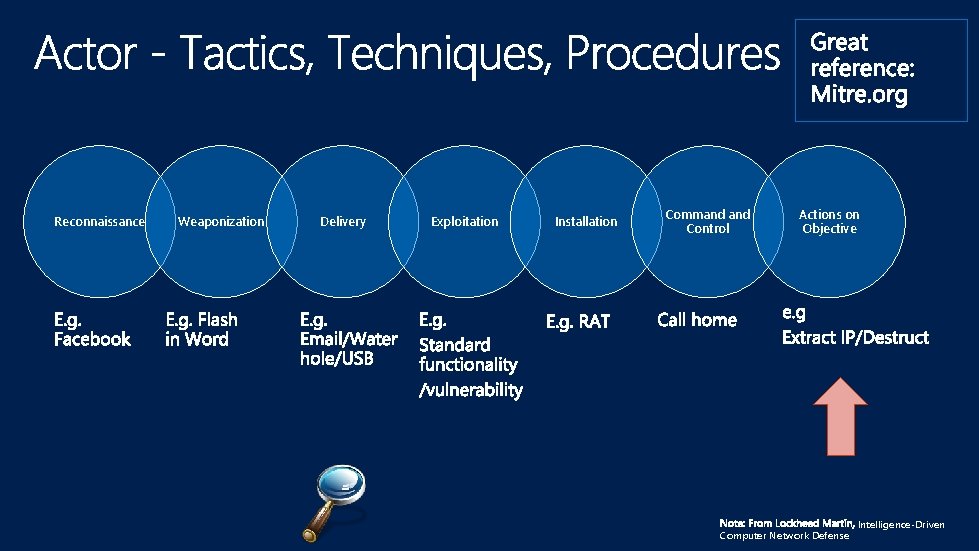
Reconnaissance Weaponization Delivery Exploitation Installation Command Control Actions on Objective Computer Network Defense Intelligence-Driven


PANIC…




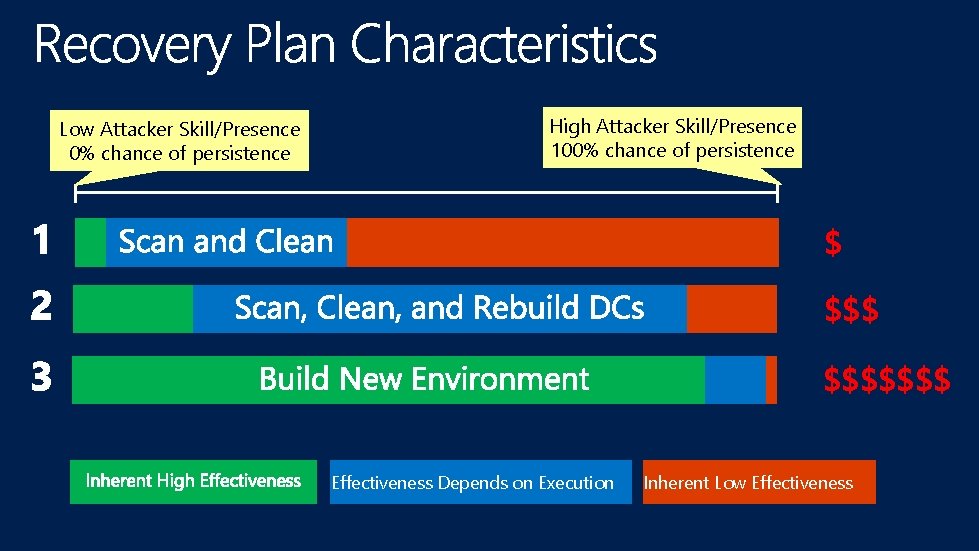
Low Attacker Skill/Presence 0% chance of persistence High Attacker Skill/Presence 100% chance of persistence $ $$$$$$$ Effectiveness Depends on Execution Inherent Low Effectiveness




http: //channel 9. msdn. com/Events/Tech. Ed www. microsoft. com/learning http: //microsoft. com/technet http: //microsoft. com/msdn



- Slides: 48