Ruhr University Bochum Faculty of Mathematics InformationSecurity and
Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology On the Security of HFE, HFEv- and Quartz Nicolas T. Courtois Magnus Daum 08. 01. 2003 Patrick Felke Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
Ruhr University Bochum Overview Faculty of Mathematics Information-Security and Cryptology • HFE – Hidden Field Equations – Basic HFE • Solving HFE systems with – Gröbner Signing/Verifying HFE Bases with Algorithms – Perturbations • Simulations – Parameters • Conclusion 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
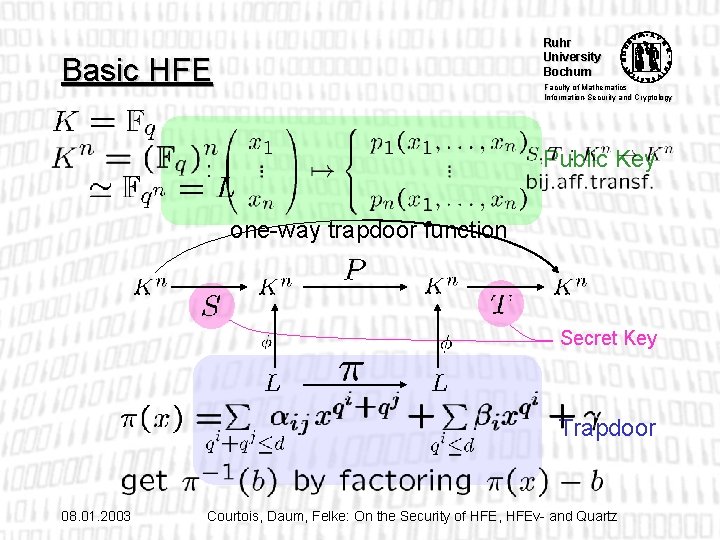
Ruhr University Bochum Basic HFE Faculty of Mathematics Information-Security and Cryptology Public Key one-way trapdoor function Secret Key Trapdoor 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
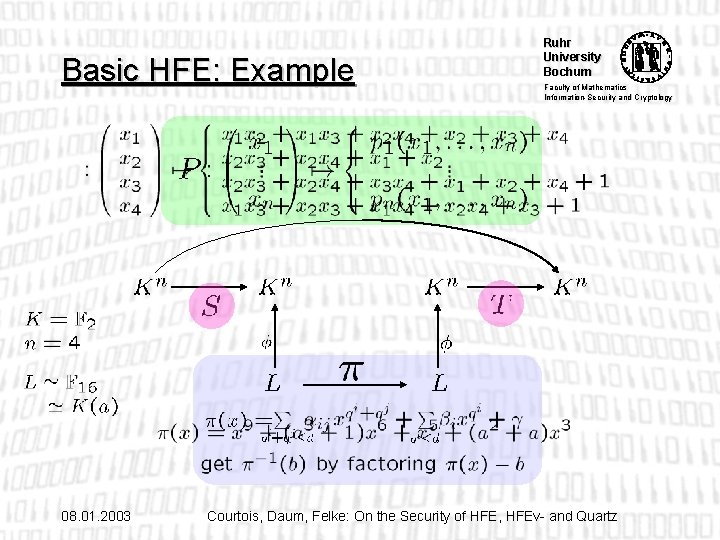
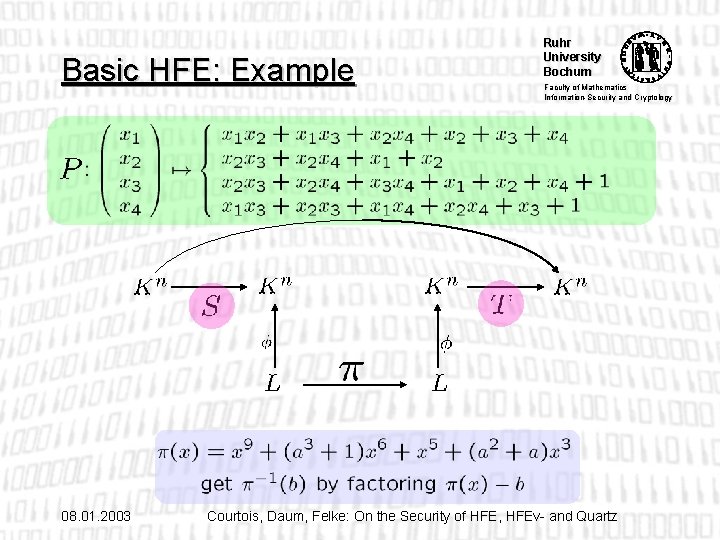
Basic HFE: Example 08. 01. 2003 Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
Basic HFE: Example 08. 01. 2003 Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
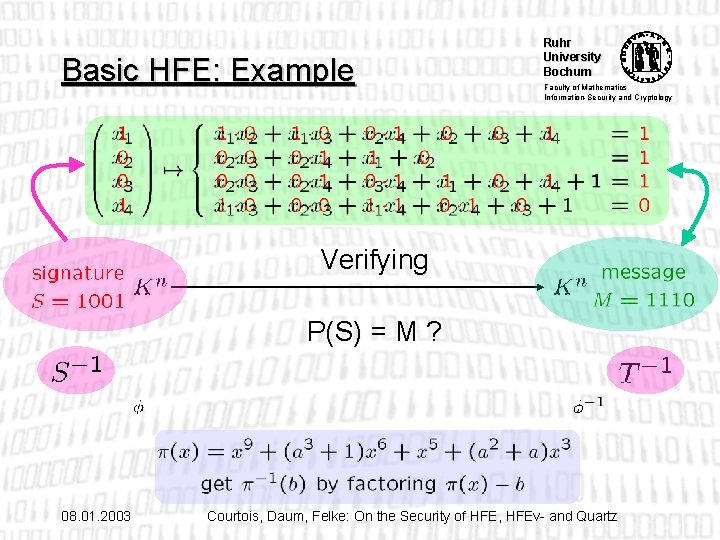
Basic HFE: Example Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology Verifying P(S) = M ? 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
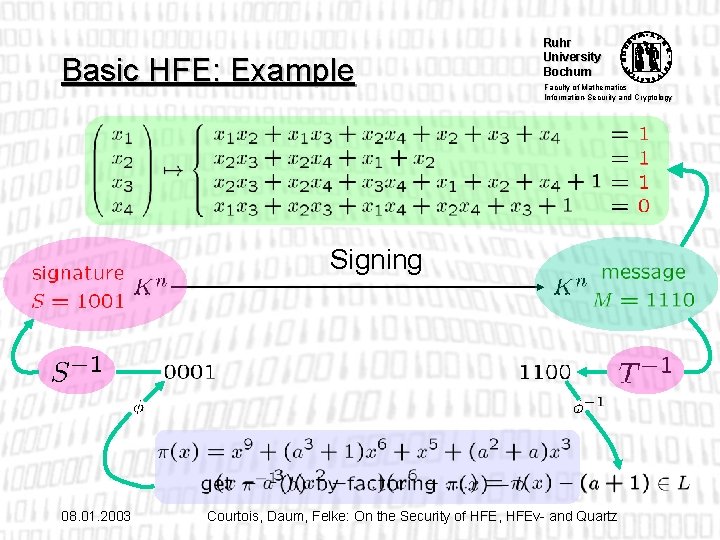
Basic HFE: Example Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology Signing 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
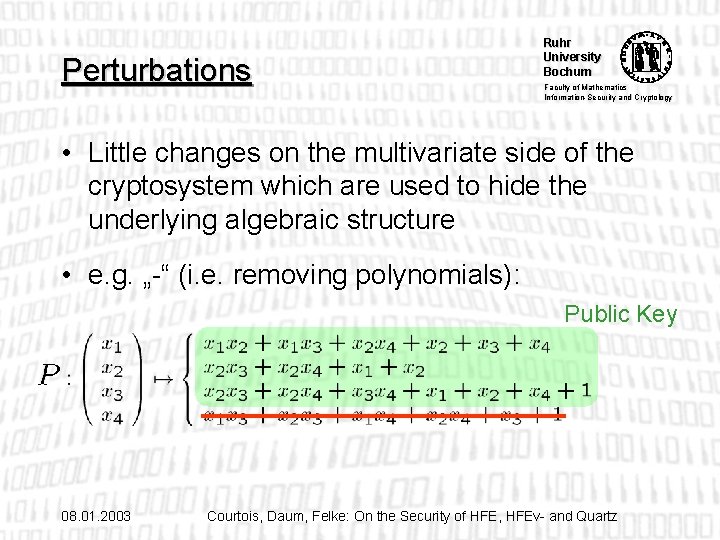
Perturbations Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • Little changes on the multivariate side of the cryptosystem which are used to hide the underlying algebraic structure • e. g. „-“ (i. e. removing polynomials): Public Key 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
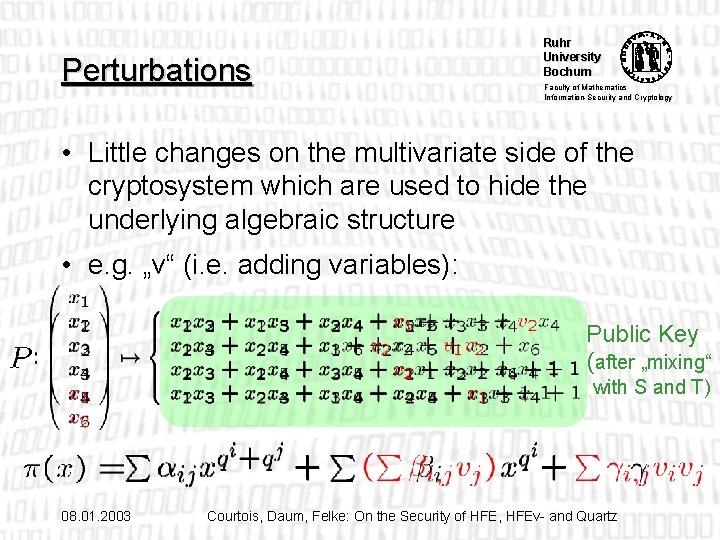
Perturbations Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • Little changes on the multivariate side of the cryptosystem which are used to hide the underlying algebraic structure • e. g. „v“ (i. e. adding variables): Public Key (after „mixing“ with S and T) 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
Perturbations Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • Other perturbations: – Adding random polynomials („+“) – Fixing some variables („f “) • Perturbations can be combined (e. g. to HFEv- systems) • Perturbated systems are claimed to be more secure • Quartz, Flash, SFlash are all perturbated HFE systems 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
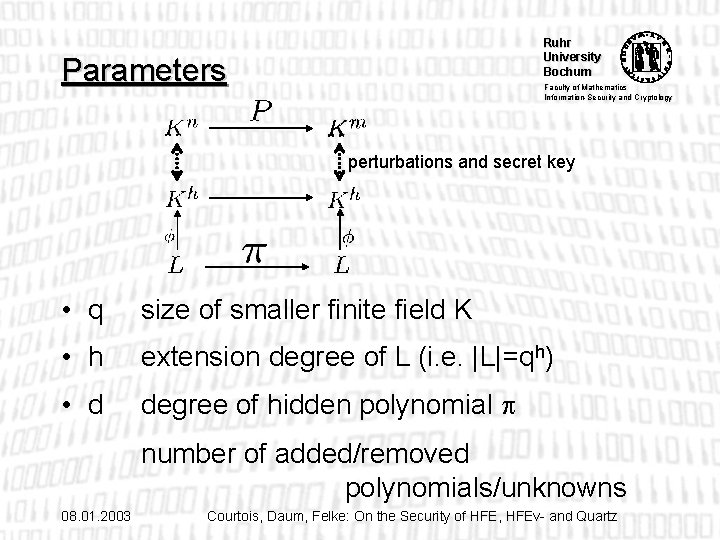
Ruhr University Bochum Parameters Faculty of Mathematics Information-Security and Cryptology perturbations and secret key • q size of smaller finite field K • h extension degree of L (i. e. |L|=qh) • d degree of hidden polynomial number of added/removed polynomials/unknowns 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
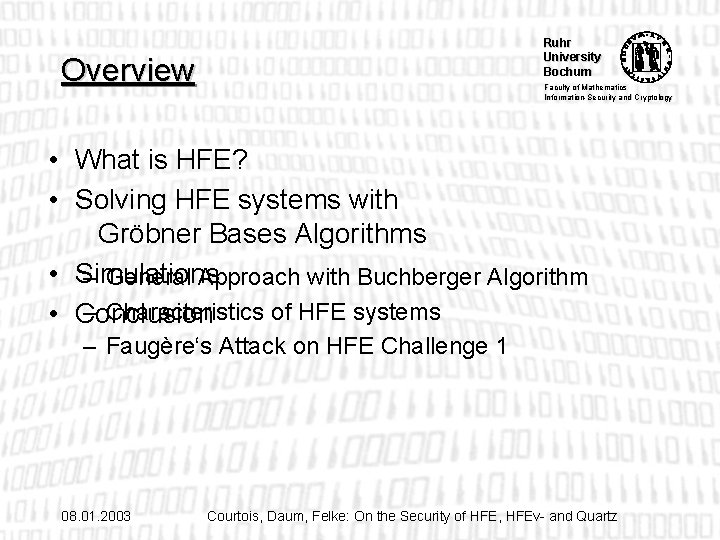
Ruhr University Bochum Overview Faculty of Mathematics Information-Security and Cryptology • What is HFE? • Solving HFE systems with Gröbner Bases Algorithms • Simulations – General Approach with Buchberger Algorithm – Characteristics of HFE systems • Conclusion – Faugère‘s Attack on HFE Challenge 1 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
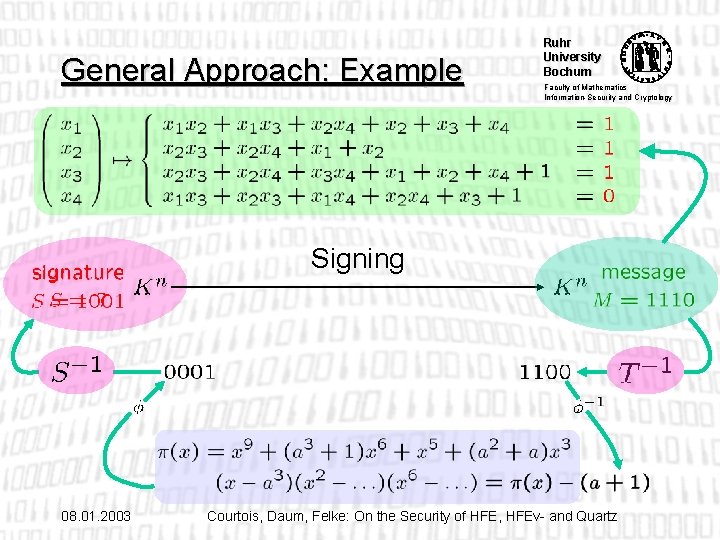
General Approach: Example Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology Signing 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
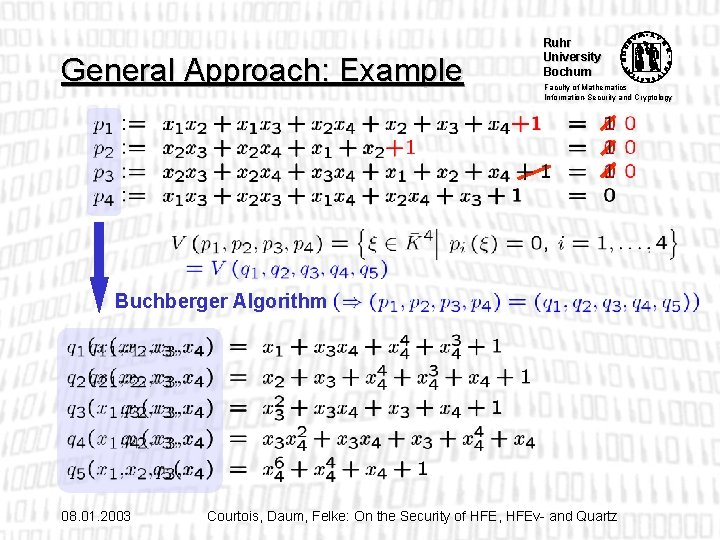
General Approach: Example Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology Buchberger Algorithm 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
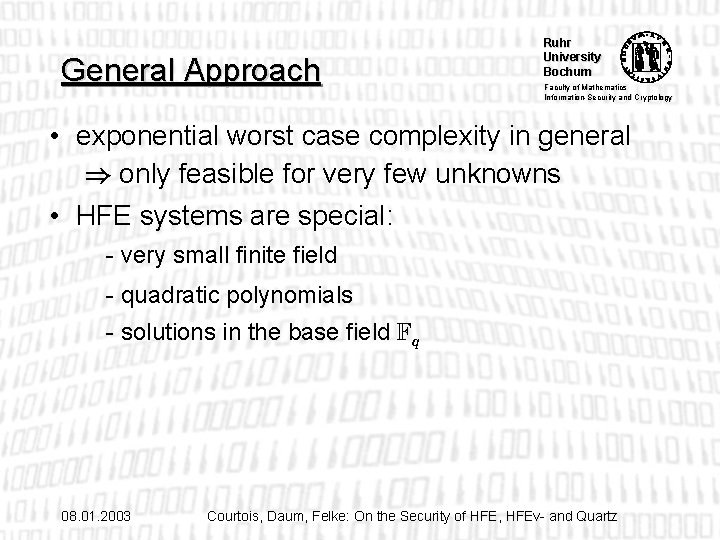
General Approach Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • exponential worst case complexity in general ) only feasible for very few unknowns • HFE systems are special: - very small finite field - quadratic polynomials - solutions in the base field Fq 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
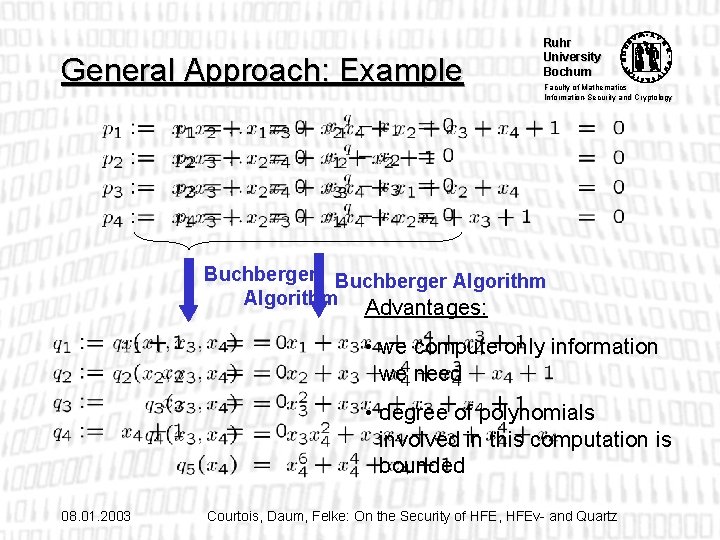
General Approach: Example Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology Buchberger Algorithm Advantages: • we compute only information we need • degree of polynomials involved in this computation is bounded 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
General Approach Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • exponential worst case complexity in general ) only feasible for very few unknowns • But HFE systems are special: - very small finite field - quadratic polynomials - solutions in the base field Fq - hidden polynomial ! Optimized variants of Buchberger algorithm might be able to solve Basic HFE systems 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
General Approach Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • Best known Attack on Basic HFE: Faugère’s Algorithm F 5/2 (April 2002) succesfully attacked HFE challenge 1 (h=80, d=96) in 96 h on 833 MHz Alpha workstation • On perturbated HFE systems: – No feasible attacks known yet – Algorithms like F 5/2 can be applied to such systems – Complexity is not known 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
Ruhr University Bochum Overview Faculty of Mathematics Information-Security and Cryptology • What is HFE? • Solving HFE systems with Gröbner Bases Algorithms • Simulations • Conclusion – What to measure? – Special Case of Signing – Results 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
Simulations Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • in SINGULAR using the stdfglm function • Parameters: • finite field K= F 2 • h 2 { 15, 19, 21 } • HFE systems with d 2 { 5, 9, 17 } and randomly generated quadratic systems • Signing • Perturbations „v“ and „-“ ( removed 0 to 3 polynomials and added 0 to 5 unknowns) 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
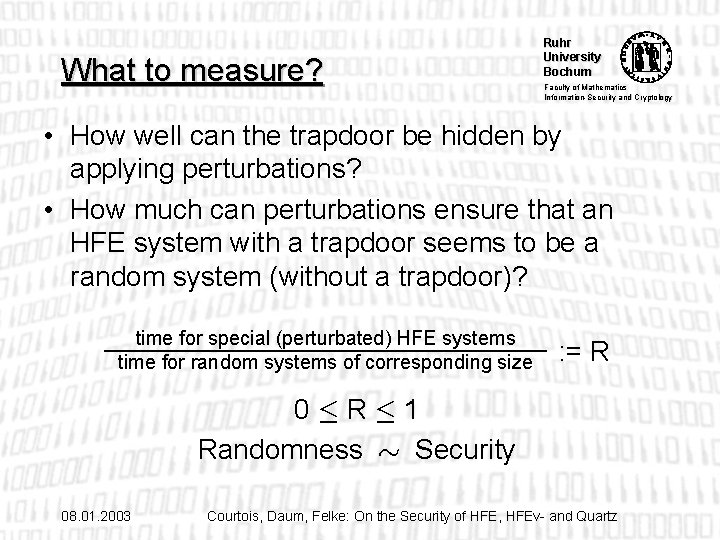
What to measure? Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • How well can the trapdoor be hidden by applying perturbations? • How much can perturbations ensure that an HFE system with a trapdoor seems to be a random system (without a trapdoor)? time for special (perturbated) HFE systems time for random systems of corresponding size : = R 0·R· 1 Randomness » Security 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
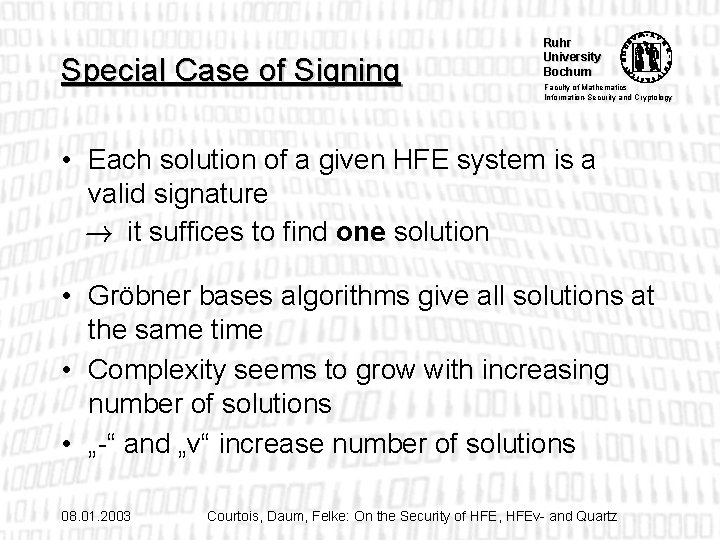
Special Case of Signing Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • Each solution of a given HFE system is a valid signature ! it suffices to find one solution • Gröbner bases algorithms give all solutions at the same time • Complexity seems to grow with increasing number of solutions • „-“ and „v“ increase number of solutions 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
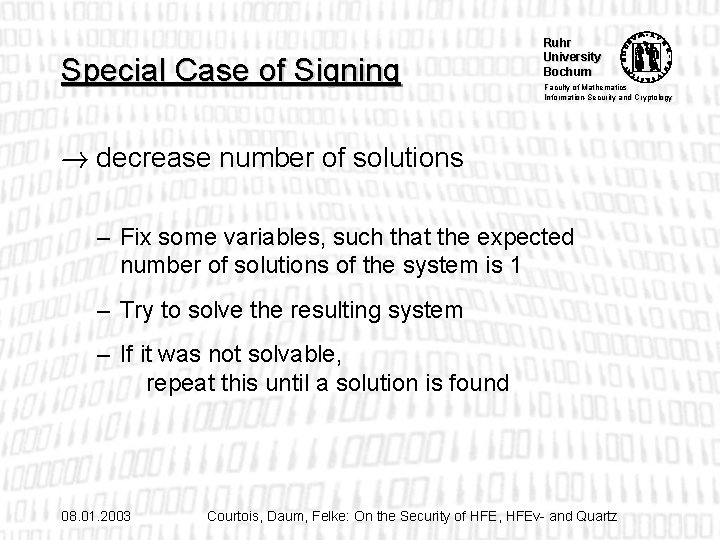
Special Case of Signing Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology ! decrease number of solutions – Fix some variables, such that the expected number of solutions of the system is 1 – Try to solve the resulting system – If it was not solvable, repeat this until a solution is found 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
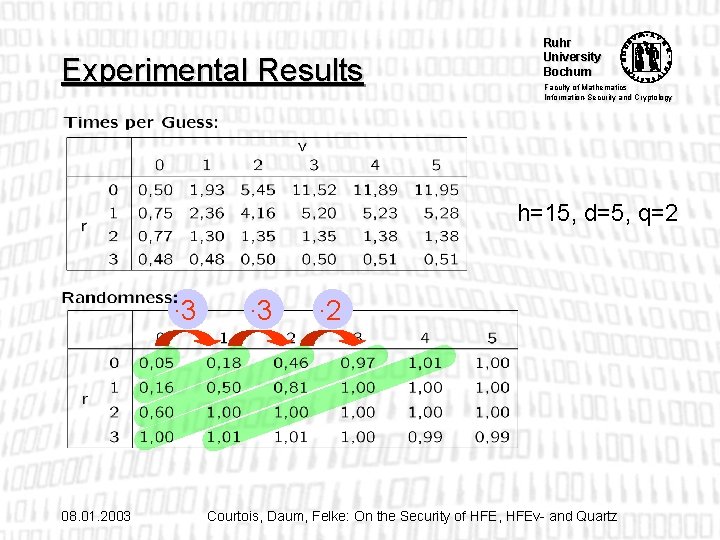
Experimental Results Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology h=15, d=5, q=2 ∙ 3 08. 01. 2003 ∙ 2 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
Experimental Results Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • R depends mainly on the total number v+r of applied perturbations • „-“ may even decrease the total time ! use more „v“ • d very small, i. e. R<<1: v+r perturbations make the complexity increase by a factor of about qv+r • The smaller R is, the stronger is the effect of the perturbations 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
Conclusion Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology • HFE can be attacked with Gröbner bases algorithms • Complexity is very high and can be increased by applying perturbations • In Quartz better take d=257 (instead of 129) but that slows down Quartz 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
Ruhr University Bochum Faculty of Mathematics Information-Security and Cryptology Thank you! Questions ? 08. 01. 2003 Courtois, Daum, Felke: On the Security of HFE, HFEv- and Quartz
- Slides: 27