RTCWEB STUN Extensions for Authenticated Firewall Traversal draftreddyrtcwebstunauthfwtraversal00
RTCWEB STUN Extensions for Authenticated Firewall Traversal draft-reddy-rtcweb-stun-auth-fw-traversal-00 Aug 2 nd 2012 IETF 84 meeting Authors: T. Reddy, Muthu A M Perumal, Ram Mohan R, Dan Wing draft-reddy-rtcweb-stun-auth-fw-traversal-00
Agenda Ø Problem Statement Ø Existing Model and Challenges Ø Proposed Model Ø Next Steps draft-reddy-rtcweb-stun-auth-fw-traversal-00
Problem Statement Ø Corporate firewall blocks UDP traffic Ø Thus, RTP/SRTP traffic has to use: – TCP – TURN – Session Border Controller draft-reddy-rtcweb-stun-auth-fw-traversal-00
Existing Model: ALG (Application Layer Gateway ) Ø Requires unencrypted signaling Ø RTCWEB has encrypted signaling (TLS) Ø Other reasons ALG is bad draft-reddy-rtcweb-stun-auth-fw-traversal-00
Proposed Solution • UDP flows are authorized to traverse firewall • Mechanism: new attribute in ICE connectivity checks draft-reddy-rtcweb-stun-auth-fw-traversal-00
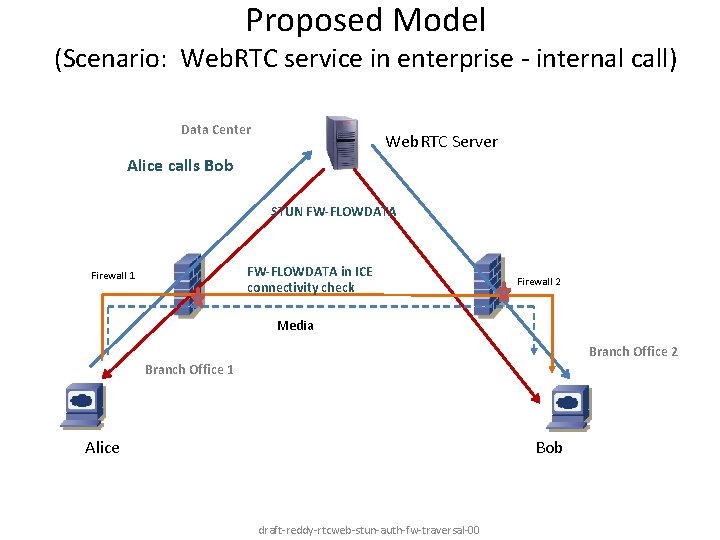
Proposed Model (Scenario: Web. RTC service in enterprise - internal call) Data Center Web. RTC Server Alice calls Bob STUN FW-FLOWDATA in ICE connectivity check Firewall 1 Firewall 2 Media Branch Office 2 Branch Office 1 Alice Bob draft-reddy-rtcweb-stun-auth-fw-traversal-00
Next steps Ø Firewalls blocking UDP a problem for RTCWEB? Ø Is there interest in solving this problem? Ø Interesting when crossing administrative domains? draft-reddy-rtcweb-stun-auth-fw-traversal-00
- Slides: 7