Risk management essentials the imperative for proactive cyberrisk
Risk management essentials: the imperative for proactive cyber-risk management Angeline Chen, Jim Halpert and Dawn Stern April 2, 2020 *This presentation is offered for informational purposes only, and the content should not be construed as legal advice on any matter.
Agenda • Overview of risk management principles and fundamentals Presenters Angeline Chen Of Counsel T: 202. 799. 4107 angeline. chen@us. dlapiper. com • Relevant laws and regulations • Industry implementation example: US defense sector Jim Halpert • Incident response and litigation preparedness Partner T: 202. 799. 4441 jim. halpert@us. dlapiper. com • Key takeaways Dawn Stern Partner T: 202. 799. 4405 dawn. stern@us. dlapiper. com www. dlapiper. com 2

Overview of risk management principles and fundamentals www. dlapiper. com 3
Today’s landscape • Increasingly complex • Constantly evolving alongside emergent technology, changing social and communication norms and exponential increase in cyber-facilitated or -dependent resources (e. g. , Internet of Things, cloud usage, social media) • Interdependencies of systems, personnel, assets and organizations • Multifaceted threats, attack vectors and actors and expanded vulnerability surface area • Multiple overlapping legal, regulatory and data governance regimes relating to sensitive, proprietary and otherwise protected information (e. g. , GDPR, CCPA, NYDFS, NISPOM) with impactful consequences for violations and breaches The cyber aspect of today’s business environment is uniquely challenging and impacts industries and organizations of all sizes all over the world. The risk is heightened given the hyper-connected global business environment and deepening reliance upon digitized environments and communication norms. Today’s reality highlights the necessity of approaching cyber risks in a purposeful manner with an enterprise risk management mindset. www. dlapiper. com 4
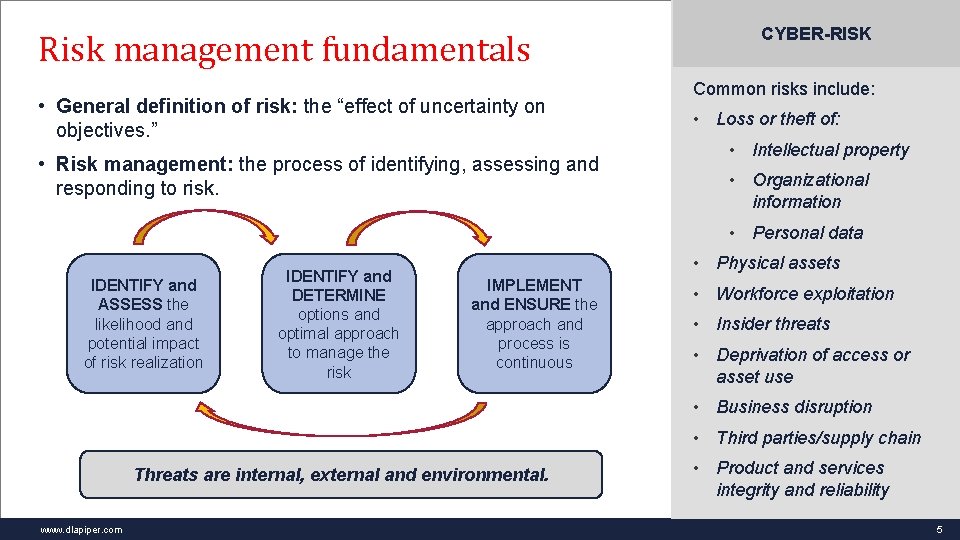
Risk management fundamentals • General definition of risk: the “effect of uncertainty on objectives. ” • Risk management: the process of identifying, assessing and responding to risk. CYBER-RISK Common risks include: • Loss or theft of: • Intellectual property • Organizational information • Personal data IDENTIFY and ASSESS the likelihood and potential impact of risk realization IDENTIFY and DETERMINE options and optimal approach to manage the risk • Physical assets IMPLEMENT and ENSURE the approach and process is continuous • Workforce exploitation • Insider threats • Deprivation of access or asset use • Business disruption • Third parties/supply chain Threats are internal, external and environmental. www. dlapiper. com • Product and services integrity and reliability 5
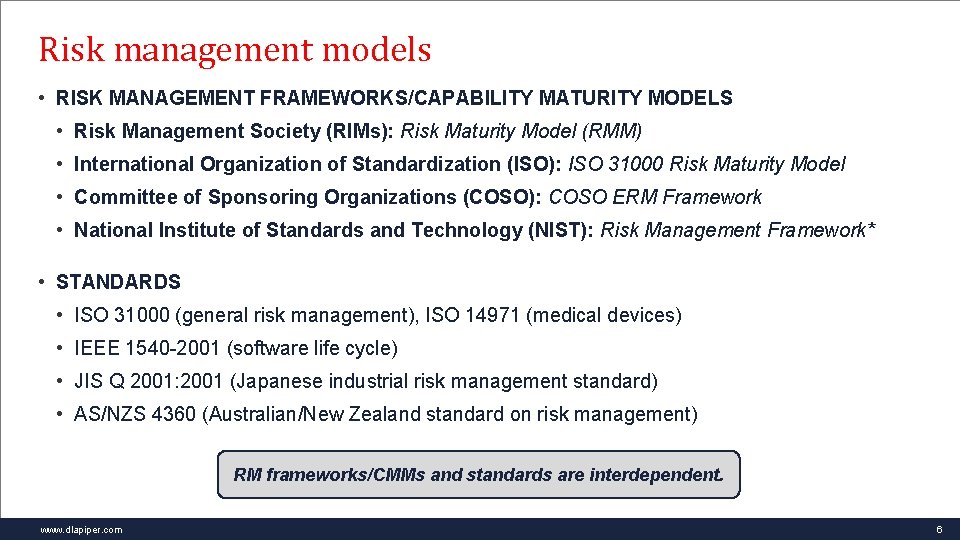
Risk management models • RISK MANAGEMENT FRAMEWORKS/CAPABILITY MATURITY MODELS • Risk Management Society (RIMs): Risk Maturity Model (RMM) • International Organization of Standardization (ISO): ISO 31000 Risk Maturity Model • Committee of Sponsoring Organizations (COSO): COSO ERM Framework • National Institute of Standards and Technology (NIST): Risk Management Framework* • STANDARDS • ISO 31000 (general risk management), ISO 14971 (medical devices) • IEEE 1540 -2001 (software life cycle) • JIS Q 2001: 2001 (Japanese industrial risk management standard) • AS/NZS 4360 (Australian/New Zealand standard on risk management) RM frameworks/CMMs and standards are interdependent. www. dlapiper. com 6
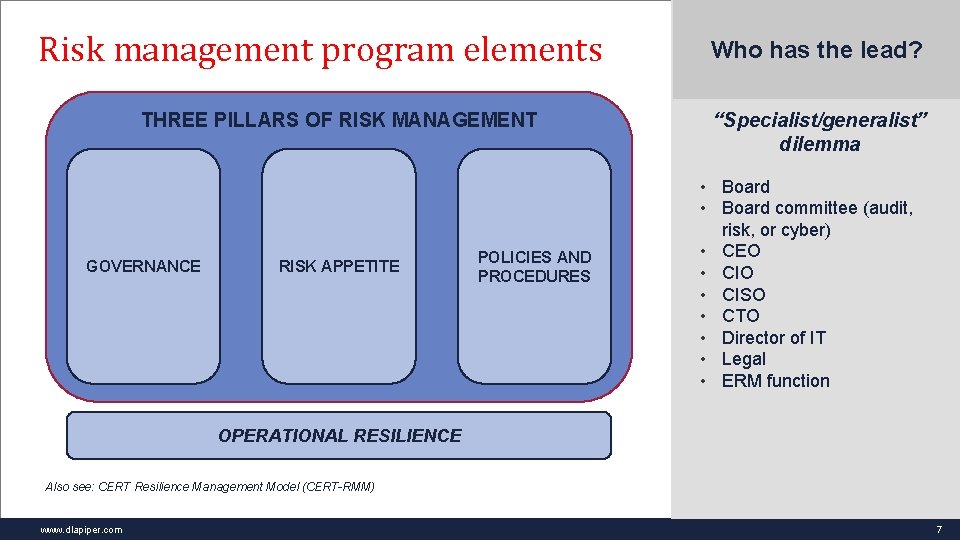
Risk management program elements THREE PILLARS OF RISK MANAGEMENT GOVERNANCE RISK APPETITE POLICIES AND PROCEDURES Who has the lead? “Specialist/generalist” dilemma • Board committee (audit, risk, or cyber) • CEO • CISO • CTO • Director of IT • Legal • ERM function OPERATIONAL RESILIENCE Also see: CERT Resilience Management Model (CERT-RMM) www. dlapiper. com 7
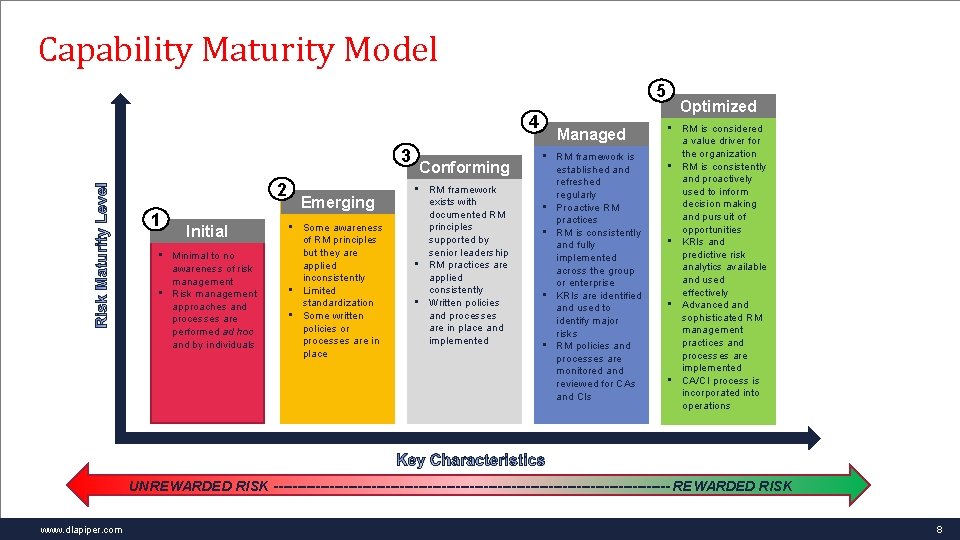
Capability Maturity Model 5 4 3 2 1 Initial • Minimal to no awareness of risk management • Risk management approaches and processes are performed ad hoc and by individuals Emerging • Some awareness of RM principles but they are applied inconsistently • Limited standardization • Some written policies or processes are in place Conforming • RM framework exists with documented RM principles supported by senior leadership • RM practices are applied consistently • Written policies and processes are in place and implemented Managed • RM framework is established and refreshed regularly • Proactive RM practices • RM is consistently and fully implemented across the group or enterprise • KRIs are identified and used to identify major risks • RM policies and processes are monitored and reviewed for CAs and CIs Optimized • RM is considered a value driver for the organization • RM is consistently and proactively used to inform decision making and pursuit of opportunities • KRIs and predictive risk analytics available and used effectively • Advanced and sophisticated RM management practices and processes are implemented • CA/CI process is incorporated into operations UNREWARDED RISK ------------------------------------------- REWARDED RISK www. dlapiper. com 8

Cyber-threat risk surface area Source: https: //insights. sei. cmu. edu/insider-threat/assets_c/2017/03/it-def 2 -2188. html www. dlapiper. com 9
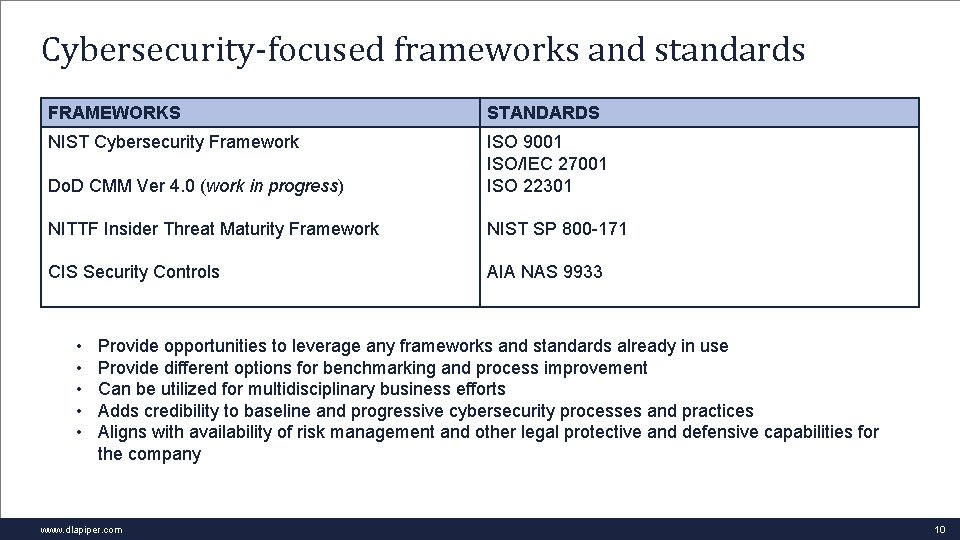
Cybersecurity-focused frameworks and standards FRAMEWORKS STANDARDS NIST Cybersecurity Framework Do. D CMM Ver 4. 0 (work in progress) ISO 9001 ISO/IEC 27001 ISO 22301 NITTF Insider Threat Maturity Framework NIST SP 800 -171 CIS Security Controls AIA NAS 9933 • • • Provide opportunities to leverage any frameworks and standards already in use Provide different options for benchmarking and process improvement Can be utilized for multidisciplinary business efforts Adds credibility to baseline and progressive cybersecurity processes and practices Aligns with availability of risk management and other legal protective and defensive capabilities for the company www. dlapiper. com 10
Relevant laws and regulations www. dlapiper. com 11
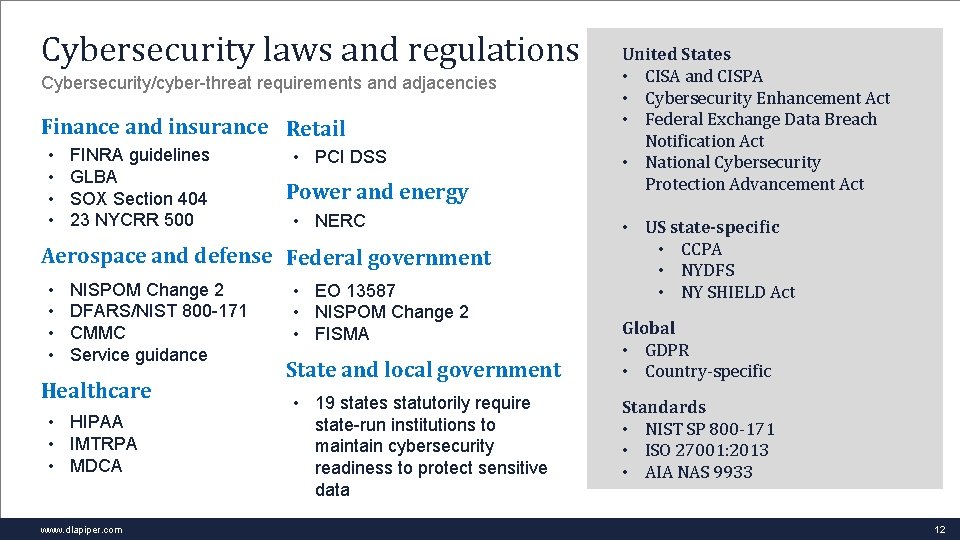
Cybersecurity laws and regulations Cybersecurity/cyber-threat requirements and adjacencies Finance and insurance Retail • • FINRA guidelines GLBA SOX Section 404 23 NYCRR 500 • PCI DSS Power and energy • NERC Aerospace and defense Federal government • • NISPOM Change 2 DFARS/NIST 800 -171 CMMC Service guidance Healthcare • HIPAA • IMTRPA • MDCA www. dlapiper. com • EO 13587 • NISPOM Change 2 • FISMA State and local government • 19 states statutorily require state-run institutions to maintain cybersecurity readiness to protect sensitive data United States • CISA and CISPA • Cybersecurity Enhancement Act • Federal Exchange Data Breach Notification Act • National Cybersecurity Protection Advancement Act • US state-specific • CCPA • NYDFS • NY SHIELD Act Global • GDPR • Country-specific Standards • NIST SP 800 -171 • ISO 27001: 2013 • AIA NAS 9933 12
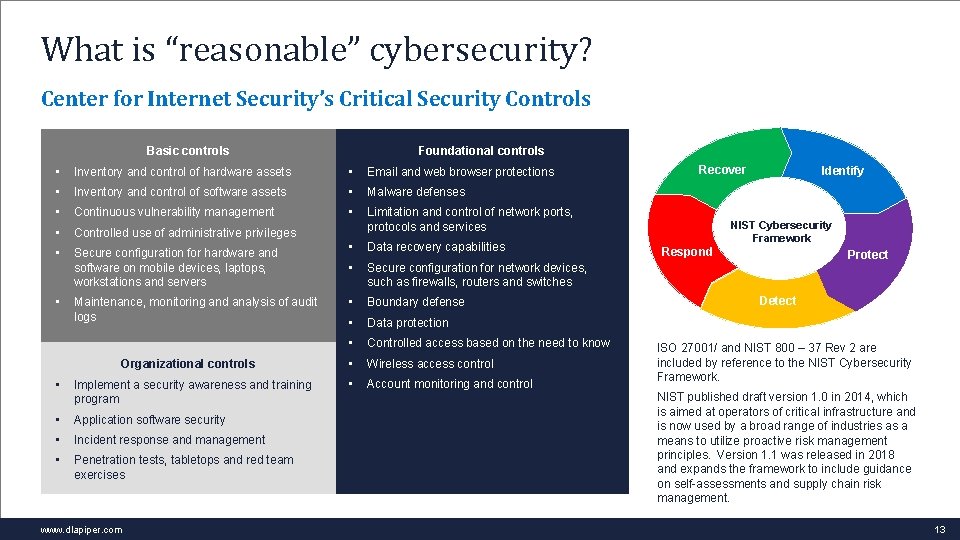
What is “reasonable” cybersecurity? Center for Internet Security’s Critical Security Controls Foundational controls Basic controls • Inventory and control of hardware assets • Email and web browser protections • Inventory and control of software assets • Malware defenses • Continuous vulnerability management • • Controlled use of administrative privileges Limitation and control of network ports, protocols and services • Secure configuration for hardware and software on mobile devices, laptops, workstations and servers • Data recovery capabilities • Secure configuration for network devices, such as firewalls, routers and switches • Boundary defense • Data protection • Controlled access based on the need to know • Wireless access control • Account monitoring and control • Maintenance, monitoring and analysis of audit logs Organizational controls • Implement a security awareness and training program • Application software security • Incident response and management • Penetration tests, tabletops and red team exercises www. dlapiper. com Recover Identify NIST Cybersecurity Framework Respond Protect Detect ISO 27001/ and NIST 800 – 37 Rev 2 are included by reference to the NIST Cybersecurity Framework. NIST published draft version 1. 0 in 2014, which is aimed at operators of critical infrastructure and is now used by a broad range of industries as a means to utilize proactive risk management principles. Version 1. 1 was released in 2018 and expands the framework to include guidance on self-assessments and supply chain risk management. 13

Industry implementation example: US defense sector www. dlapiper. com 14
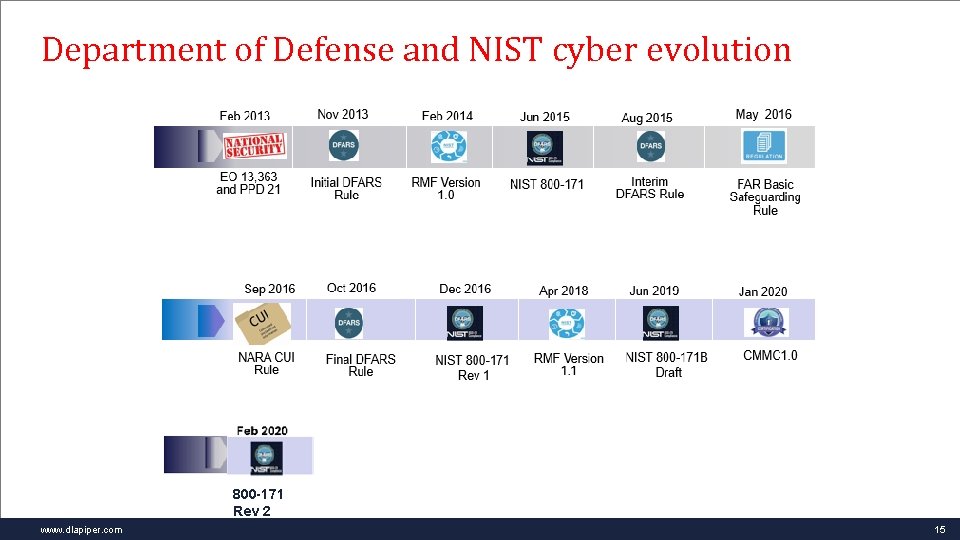
Department of Defense and NIST cyber evolution 800 -171 Rev 2 www. dlapiper. com 15
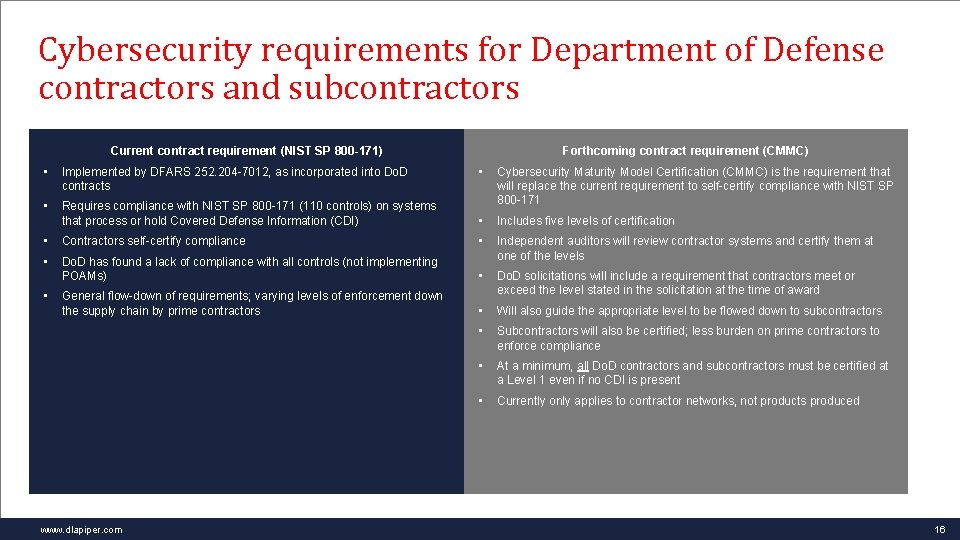
Cybersecurity requirements for Department of Defense contractors and subcontractors Current contract requirement (NIST SP 800 -171) • Implemented by DFARS 252. 204 -7012, as incorporated into Do. D contracts • Forthcoming contract requirement (CMMC) • Requires compliance with NIST SP 800 -171 (110 controls) on systems that process or hold Covered Defense Information (CDI) Cybersecurity Maturity Model Certification (CMMC) is the requirement that will replace the current requirement to self-certify compliance with NIST SP 800 -171 • Includes five levels of certification • Contractors self-certify compliance • • Do. D has found a lack of compliance with all controls (not implementing POAMs) Independent auditors will review contractor systems and certify them at one of the levels • General flow-down of requirements; varying levels of enforcement down the supply chain by prime contractors Do. D solicitations will include a requirement that contractors meet or exceed the level stated in the solicitation at the time of award • Will also guide the appropriate level to be flowed down to subcontractors • Subcontractors will also be certified; less burden on prime contractors to enforce compliance • At a minimum, all Do. D contractors and subcontractors must be certified at a Level 1 even if no CDI is present • Currently only applies to contractor networks, not products produced • www. dlapiper. com 16
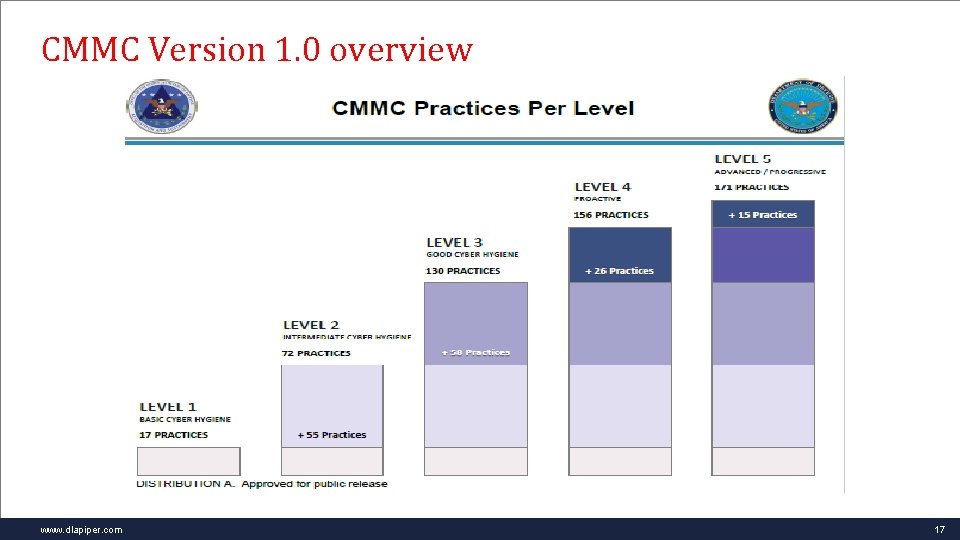
CMMC Version 1. 0 overview www. dlapiper. com 17
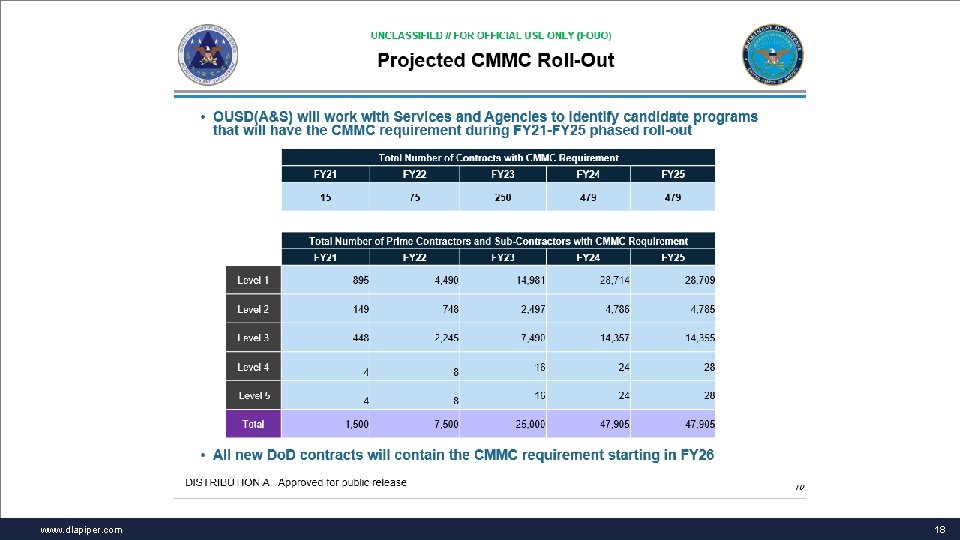
www. dlapiper. com 18

Incident response and litigation preparedness www. dlapiper. com 19
What type of incident are you experiencing? • Espionage and surveillance • Theft of data (e. g. , hacking, malicious insider) • System/device disruption and destruction • Extortion, stalking and threats • Cyber-facilitated fraud/corruption/violence • Disinformation campaign • Non-malicious incident www. dlapiper. com 20

Navigating disparate roles • Victim • Target of governmental investigations/enforcement • Civil/criminal litigant • Subject of media scrutiny • Repeat customer with a track record www. dlapiper. com 21
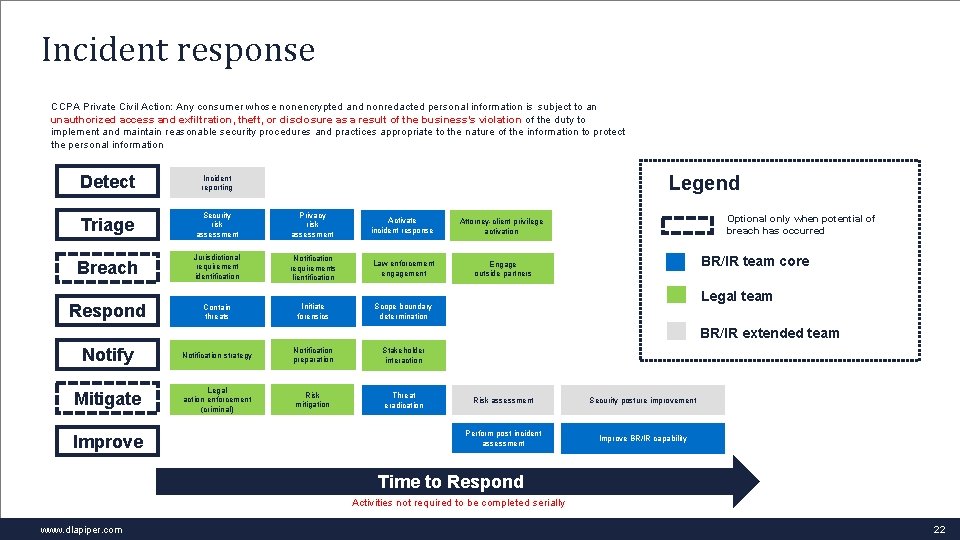
Incident response CCPA Private Civil Action: Any consumer whose nonencrypted and nonredacted personal information is subject to an unauthorized access and exfiltration, theft, or disclosure as a result of the business’s violation of the duty to implement and maintain reasonable security procedures and practices appropriate to the nature of the information to protect the personal information Detect Incident reporting Triage Security risk assessment Privacy risk assessment Activate incident response Attorney-client privilege activation Breach Jurisdictional requirement identification Notification requirements Iientification Law enforcement engagement Engage outside partners Respond Contain threats Initiate forensics Scope boundary determination Legend Optional only when potential of breach has occurred BR/IR team core Legal team BR/IR extended team Notify Notification strategy Notification preparation Stakeholder interaction Mitigate Legal action enforcement (criminal) Risk mitigation Threat eradication Improve Risk assessment Security posture improvement Perform post incident assessment Improve BR/IR capability Time to Respond Activities not required to be completed serially www. dlapiper. com 22
Response to a cyberattack – executing your playbook • Make an initial assessment of the scope and nature of the incident, particularly whether it is a malicious act or a technological glitch. • Scale the incident response team as appropriate to the particular incident and institute legal privilege. • Determine and implement appropriate detection, containment and remediation strategy. • Establish internal and external communications strategy. • Communicate with insurance carrier as appropriate. • Minimize continuing damage consistent with IR plan. • Collect and preserve data related to the incident (a digital crime scene). • Evaluate with legal counsel whether and how to notify stakeholders for legal compliance purposes. • Complete investigation and determine, through counsel, the particulars regarding the creation of any incident report. • Incorporate lessons learned into IR plan with eye on potential litigation. www. dlapiper. com 23
Understanding the cyber-incident • • • Type of attack Means of access Attack tools Data subject to exposure/compromise Movements within networks Possible business disruption/destruction Attribution Information sharing and leakage Time period of incident Current status of networks and devices ID of impacted users Mitigation and remediation www. dlapiper. com 24
Law enforcement interaction • Learning of the cyber threat • Engagement in proactive undercover investigations – consumer notification delays • Regulatory compliance during criminal investigations • Evidence gathering and victim cooperation • Ongoing threat mitigation • Preparing for public disclosure • Role in criminal and civil litigation www. dlapiper. com 25
www. dlapiper. com 26
Recurring incident response issues • Lack of planning and practice • Inadequate definition of IR team members, roles and responsibilities • No immediate team scalability • Asynchronous IR activities • Service provider and third-party breaches • System-wide disruptions/data destruction • Investigations are moving too slowly for the law • Notification timeframes • Evidence and opportunity are getting lost in containment • Privilege is not being adequately protected • Potential liability is increasing due to the incident response process • Law enforcement is not as engaged as it could be www. dlapiper. com 27
The CCPA data breach cause of action Cal. Civ. Code § 1798. 150 • (a)(1) Any consumer whose nonencrypted or nonredacted personal information, as defined in subparagraph (A) of paragraph (1) of subdivision (d) of Section 1798. 81. 5, is subject to an unauthorized access and exfiltration, theft, or disclosure as a result of the business’s violation of the duty to implement and maintain reasonable security procedures and practices appropriate to the nature of the information to protect the personal information may institute a civil action for any of the following: • To recover damages in an amount not less than one hundred dollars ($100) and not greater than seven hundred and fifty ($750) per consumer per incident or actual damages, whichever is greater. • Injunctive or declaratory relief. • Any other relief the court deems proper. www. dlapiper. com 28
CCPA data breach cause of action Elements • Any of the combination of data elements previously discussed that were not encrypted or redacted • Subject to “unauthorized access” and “exfiltration, theft, or disclosure” • Access is required maybe not a laptop theft or accidentally emailing the info to the wrong address? • Resulting from “the business’s violation of the duty to implement and maintain reasonable security procedures and practices appropriate to the nature of the information” • Invites broad discovery into the business’s: • Cybersecurity program – from the board on down • Cyber-incident history and past remedial measures • Current cyber-incident history and response process www. dlapiper. com 29
CCPA private right of action Unprecedented civil litigation and class action exposure Statutory damages • Statutory damages of up to $750 per consumer, per data breach for a breach of unencrypted/unredacted personal information resulting from a business’s failure to implement reasonable security measures. • Court may also award actual damages (if greater than statutory damages), injunctive or other relief. • Damage assessment considers, among other factors: nature, seriousness, persistence and duration of misconduct; number of violations; willfulness of the business’s misconduct; business’s assets, liabilities and net worth. • Discovery focused on reasonableness of cybersecurity program. www. dlapiper. com 30
Attorney-client privilege and work product protection • ATTORNEY-CLIENT PRIVILEGE – a state and federal common law privilege that protects confidential communications between the attorney and client for the purpose of seeking and providing legal advice. It may encompass non-lawyer agents working at the direction of counsel for the purpose of assisting counsel in providing legal advice. • WORK PRODUCT DOCTRINE – a qualified immunity protecting from discovery documents and tangible things prepared by a party or its representative in anticipation of litigation or for trial. Creates a presumption against discoverability that may be overcome on a showing of compelling need (for the attorney’s mental impressions and opinions) or substantial need (for non-opinion work product). Also may encompass non-lawyer agents working at the direction of counsel for the purpose of assisting counsel in providing legal advice in anticipation of litigation. www. dlapiper. com 31
Waiver of the privilege and work product protection Privilege/protection can be waived explicitly or implicitly. • A client may expressly and voluntarily waive the assertion of privilege. • Voluntarily disclosing privileged information to a third party • A client may implicitly waive the assertion of privilege. • Placing facts and issues in controversy. • Privilege as to corporate communications can be waived if disclosed to employees who did not need to access the communications for purposes of legal advice. • Waiver of A/C privilege may extend to related communications (communications on the same subject matter). • Waiver of work product protection is document-specific. • General waiver principles under attorney-client privilege apply to work product, but result may differ based on different policies underlying each. • An inadvertent disclosure may constitute a “breach” of protected information under statutory law or contract. www. dlapiper. com 32
Common interest doctrine – key points • Confidential communications between multiple parties to advance a common claim or defense in actual or potential litigation remain privileged. • The communication must be: 1. for the purpose of assisting the attorney in rendering legal advice and 2. Made to a third party which shares a common legal interest with the disclosing party. • This is an exception to the general rule of waiver of a privilege. • Some courts have limited the doctrine to situations in which the legal interest of the multiple parties is identical, not merely similar. • This can be complicated where cross-claims or third-party claims between the parties sharing the communications potentially exist. • This may apply to communications with: • Insurance carriers or brokers • Third-party service providers involved in the incident response and investigation www. dlapiper. com 33
Key causes of action in data breach class actions • Negligence per se • Breach of contract/implied contract • Violation of federal/state privacy and information security statutes • Violation of breach notification statutes • Unfair trade practices/consumer fraud • Fraudulent misrepresentation www. dlapiper. com 34
A tort duty to safeguard personal data Dittman v. UPMC (Pa. S. Ct. Nov. 21, 2018) • Arose out of data breach impacting personal information of all employees. • Reversed dismissal of data breach class action. • An employer that collects personal information from employees has a common law duty to exercise reasonable care in securing that information against foreseeable cybersecurity risks. • The economic loss doctrine does not prevent the recovery of purely economic damages for a data breach under a negligence theory. • Broad rationale easily expandable to all data collectors. www. dlapiper. com 35
Cyber-incident litigation defense strategy • No qualifying data • Non-retention of qualifying personal information • Encryption/redaction • Procedural defenses • 30 -day right to cure – get your data back!? • Use of arbitration clauses and class action waivers – CCPA purports to prevent these, but federal FAA law preempts • Removal and motion to dismiss issues (jurisdiction, standing, failure to state a claim, pleading deficiencies) • Certification issues (commonality, predominance) • Substantive defenses • Early injury-focused discovery and settlement with motion to dismiss pending • No qualifying breach • Reasonableness of cybersecurity program and incident response = cure • No causal connection between data breach and breach of standard of care • Mitigation of damages by plaintiff and under statutory damages factors www. dlapiper. com 36
Key takeaways www. dlapiper. com 37
Steps to consider • Balance risk versus reward • Make informed investments in technology, talent, and time • Keep the “big picture” fundamentals in mind • Implement cyber-hygiene basics • Follow the data • Pay attention to partners, business associates and supply chain • Utilize external experts and consultants where needed www. dlapiper. com 38
Questions Angeline G. Chen Jim Halpert Dawn Stern angeline. chen@us. dlapiper. com jim. halpert@us. dlapiper. com dawn. stern@us. dlapiper. com www. dlapiper. com 39
This publication is intended as a general overview and discussion of the subjects dealt with, and does not create a lawyer-client relationship. It is not intended to be, and should not be used as, a substitute for securing legal advice in any specific situation. DLA Piper will accept no responsibility for any actions taken or not taken on the basis of this publication. This may qualify as "Lawyer Advertising” requiring notice in some jurisdictions. Prior results do not guarantee a similar outcome. www. dlapiper. com 40
Thank you www. dlapiper. com 41
- Slides: 41