Risk assessment BSIT Know your self Know the
Risk assessment BS-IT
• Know your self • Know the enemies “If you know the enemy and know yourself, you need not fear the result of a hundred battles. If you know yourself but not the enemy, for every victory gained you will also suffer a defeat. If you know neither the enemy nor yourself, youwill succumb in every battle. ”
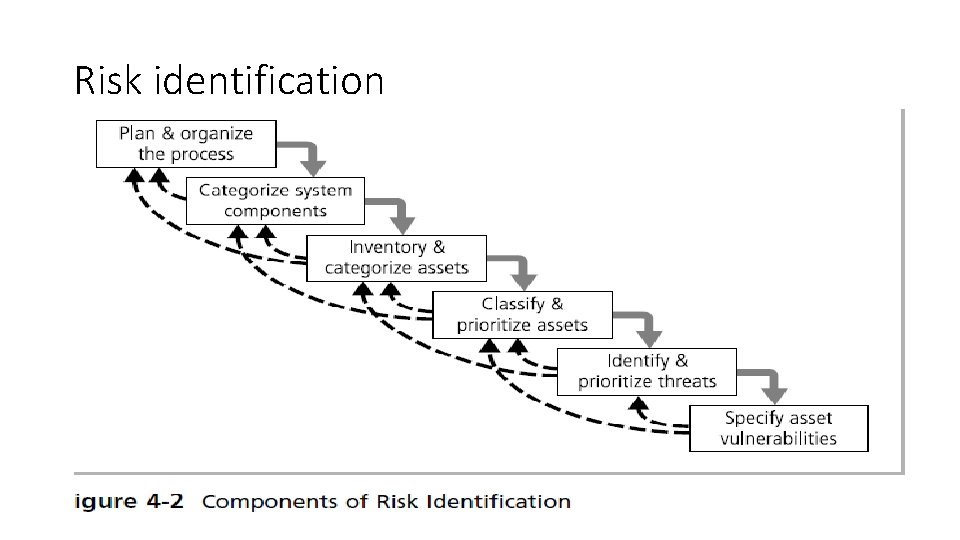
Risk identification
Plan and organize process • You begin by organizing a • team, typically consisting of representatives of all affected groups. With risk identification, • since risk can exist everywhere in the organization, representatives will come from every • department from users, to managers, to IT and Info. Sec groups. The process must then be • planned out, with periodic deliverables, reviews, and presentations to management
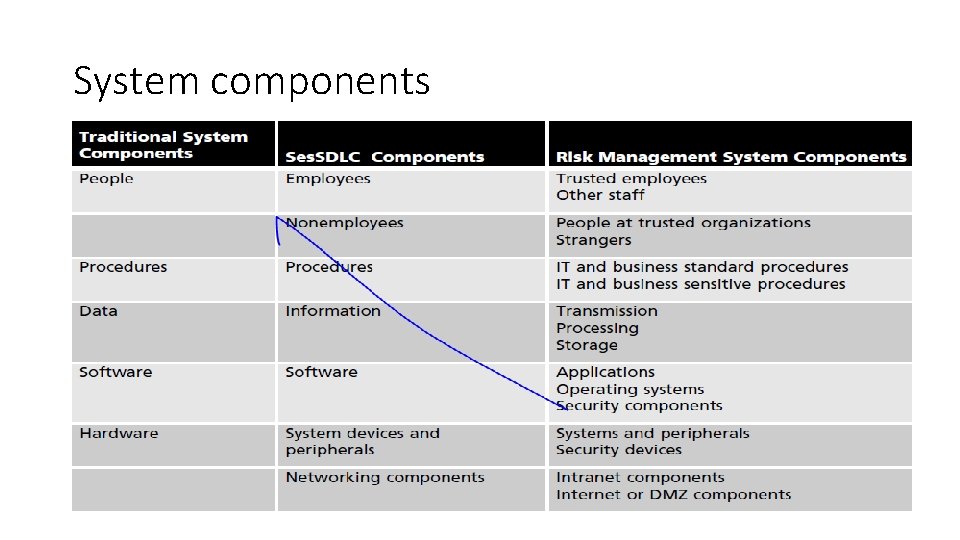
System components
Assesses and inventory • People: Position name/number/ID (avoid names and stick to identifying positions, • roles, or functions); supervisor; security clearance level; special skills • Procedures: Description; intended purpose; relationship to software, hardware, and • networking elements; storage location for reference; storage location for update • Data: Classification; owner, creator, and manager; size of data structure; data structure • used (sequential or relational); online or offline; location; backup procedures employed
Classify and prioritized assests Confidential: Used for the most sensitive corporate information that must be tightly controlled, even within the company. Access to information with this classification is strictly on a need-to-know basis or as required by the terms of a contract. Information with this classification may also be referred to as “sensitive” or “proprietary. ” Internal: Used for all internal information that does not meet the criteria for the confidential • category and is to be viewed only by corporate employees, authorized contractors, • and other third parties. • External: All information that has been approved by management for public release. • • •
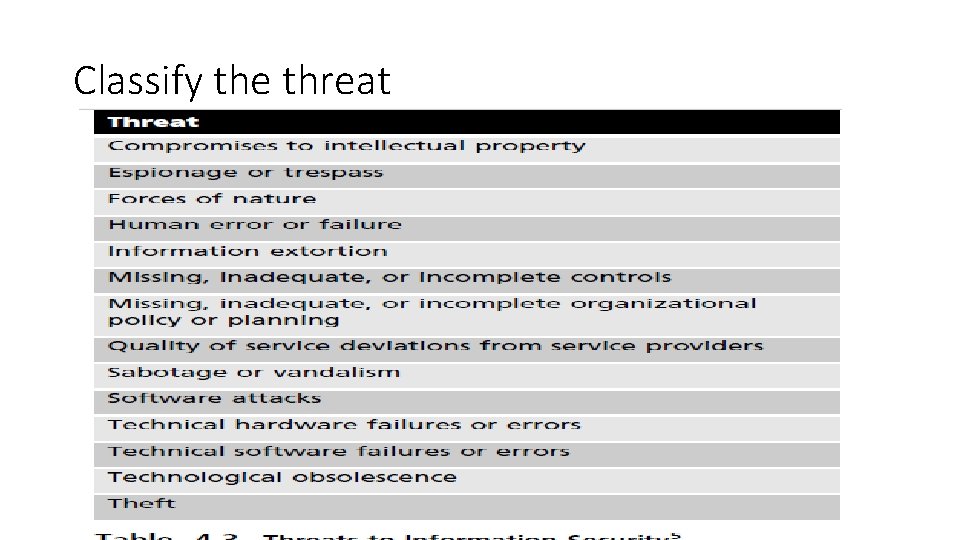
Classify the threat
- Slides: 12