Rich QR Codes With ThreeLayer Information Using Hamming

![Proposed scheme (3/3) Suppose p=3 Example: [7, 4] Hamming code, the parity check matrix Proposed scheme (3/3) Suppose p=3 Example: [7, 4] Hamming code, the parity check matrix](https://slidetodoc.com/presentation_image_h2/78d82cd514afbc2222c804a83716f567/image-8.jpg)
![Experimental results (4/6) --Comparison(1/3) [9] P. -Y. Lin, ‘‘Distributed secret sharing approach with cheater Experimental results (4/6) --Comparison(1/3) [9] P. -Y. Lin, ‘‘Distributed secret sharing approach with cheater](https://slidetodoc.com/presentation_image_h2/78d82cd514afbc2222c804a83716f567/image-12.jpg)
- Slides: 16

Rich QR Codes With Three-Layer Information Using Hamming Code Source: IEEE Access (2019): 78640 -78651 Authors: Liu, Sijia, Zhengxin Fu, and Bin Yu Speaker: Huang Peng-Cheng Date: 6/16/2021 1
Outline • Introduction • Related Works • Proposed scheme • Experimental results • Conclusions • Comments 2
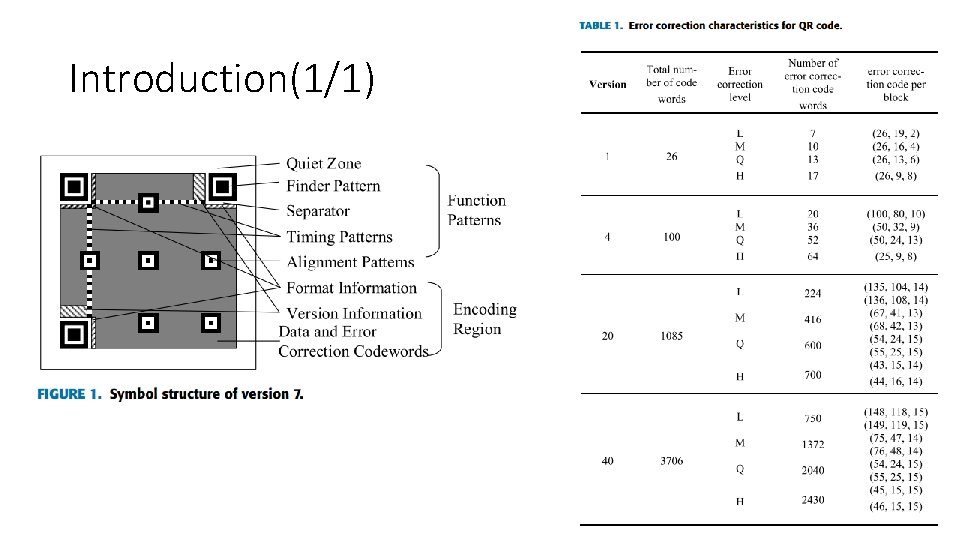
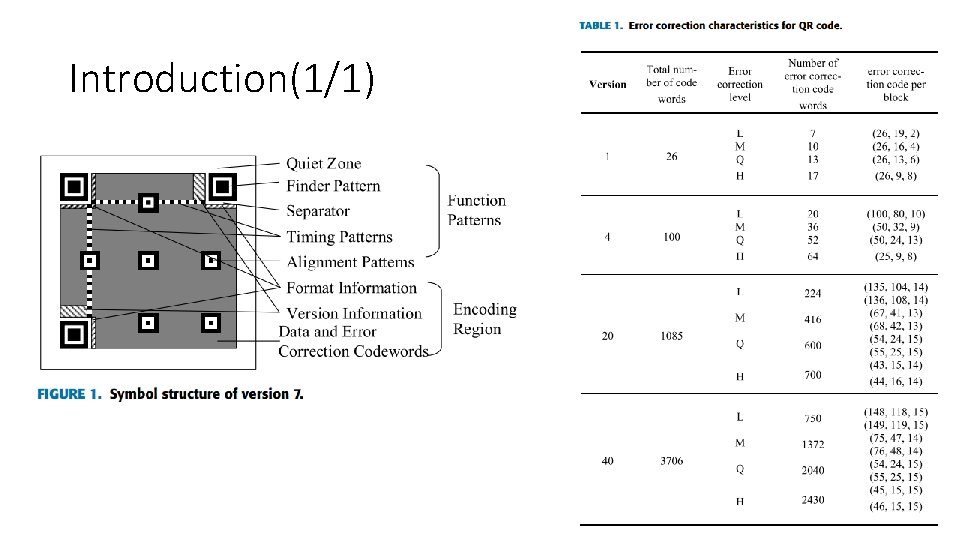
Introduction(1/1)
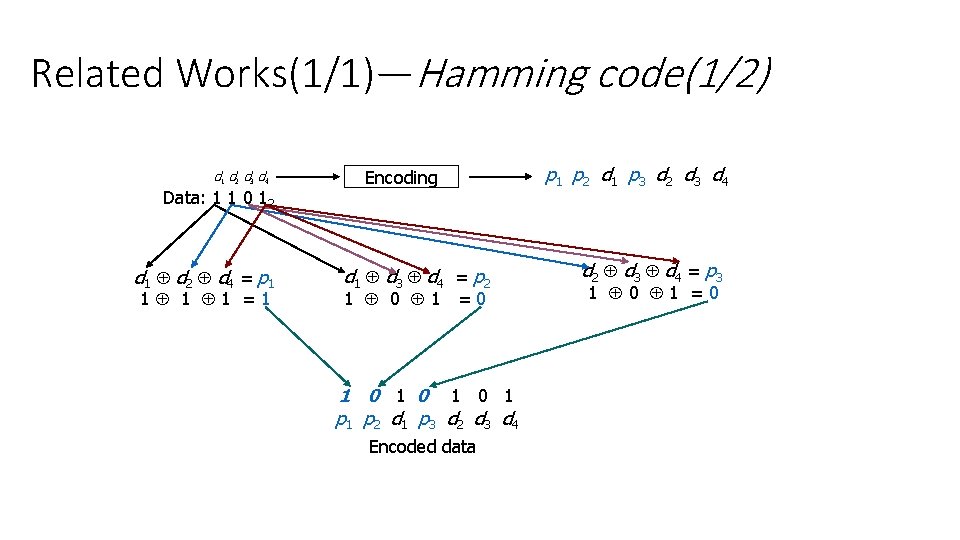
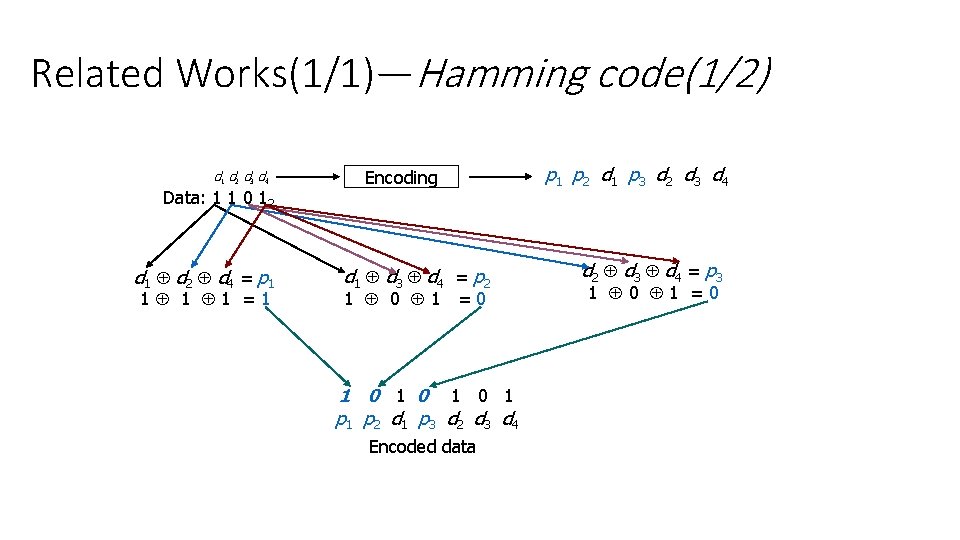
Related Works(1/1)—Hamming code(1/2) d 1 d 2 d 3 d 4 Data: 1 1 0 12 d 1 d 2 d 4 = p 1 1 =1 Encoding d 1 d 3 d 4 = p 2 1 0 1 =0 1 0 1 p 1 p 2 d 1 p 3 d 2 d 3 d 4 Encoded data p 1 p 2 d 1 p 3 d 2 d 3 d 4 d 2 d 3 d 4 = p 3 1 0 1 =0
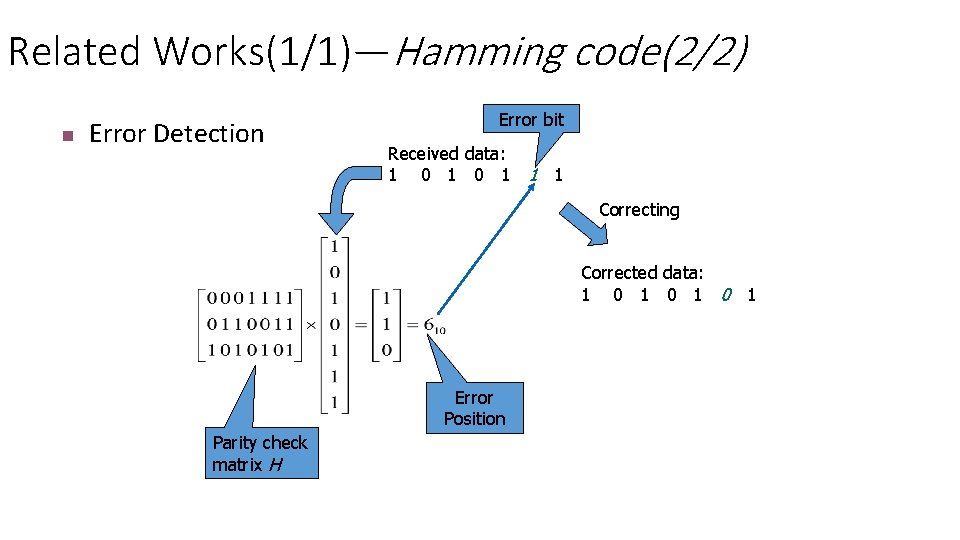
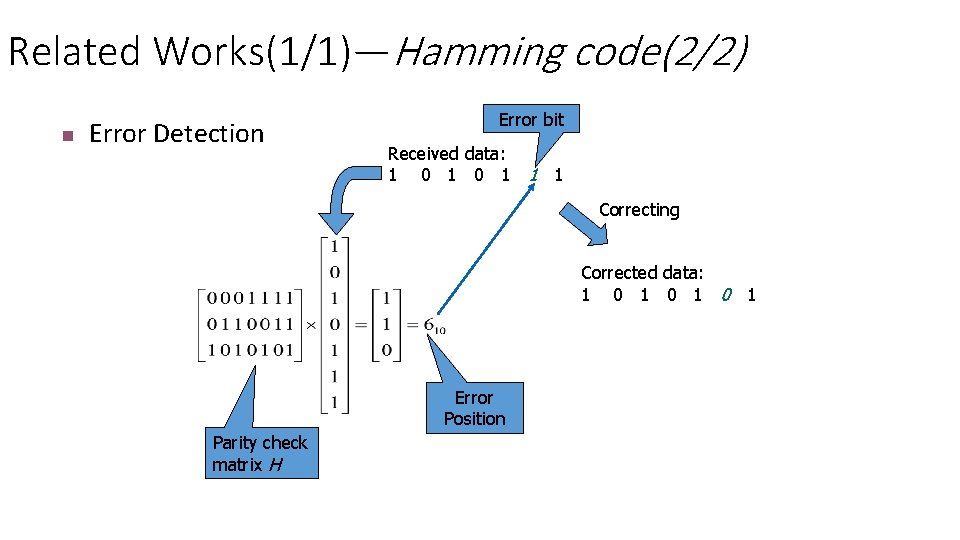
Related Works(1/1)—Hamming code(2/2) n Error Detection Error bit Received data: 1 0 1 1 1 Correcting Corrected data: 1 0 1 0 1 Error Position Parity check matrix H
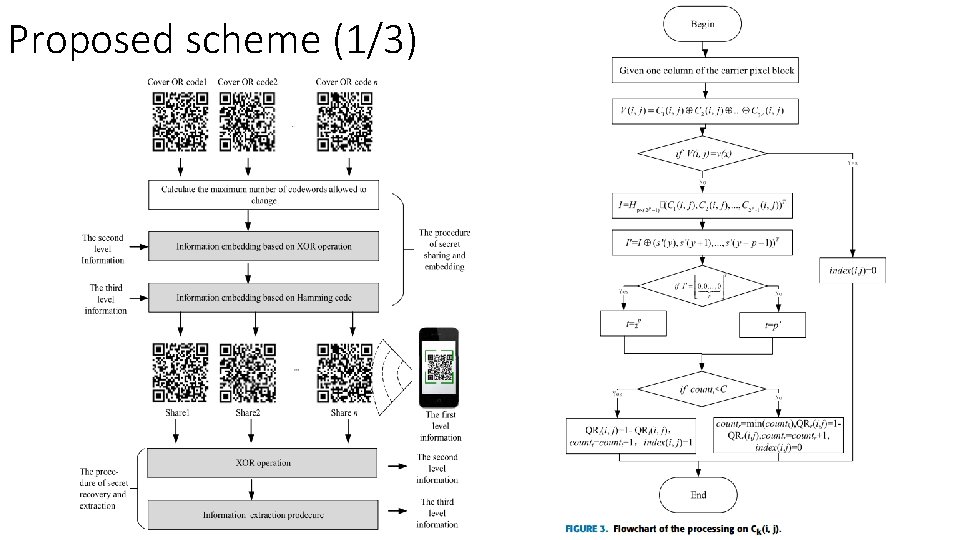
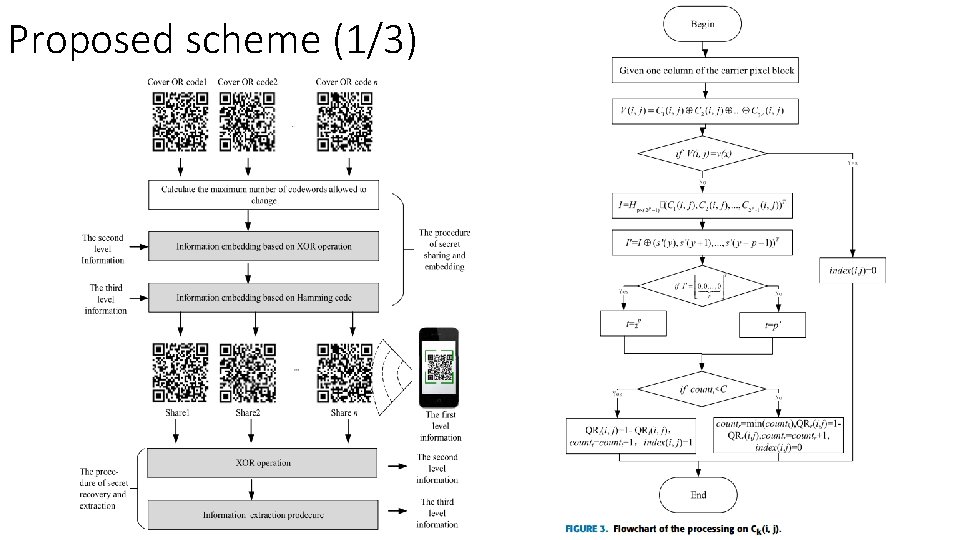
Proposed scheme (1/3)
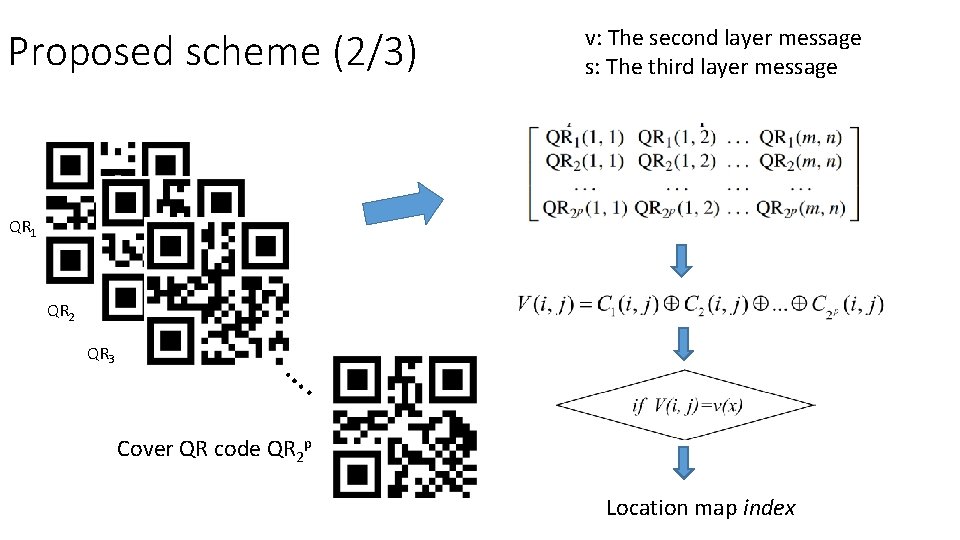
Proposed scheme (2/3) v: The second layer message s: The third layer message QR 1 QR 2 QR 3 …. Cover QR code QR 2 p Location map index
![Proposed scheme 33 Suppose p3 Example 7 4 Hamming code the parity check matrix Proposed scheme (3/3) Suppose p=3 Example: [7, 4] Hamming code, the parity check matrix](https://slidetodoc.com/presentation_image_h2/78d82cd514afbc2222c804a83716f567/image-8.jpg)
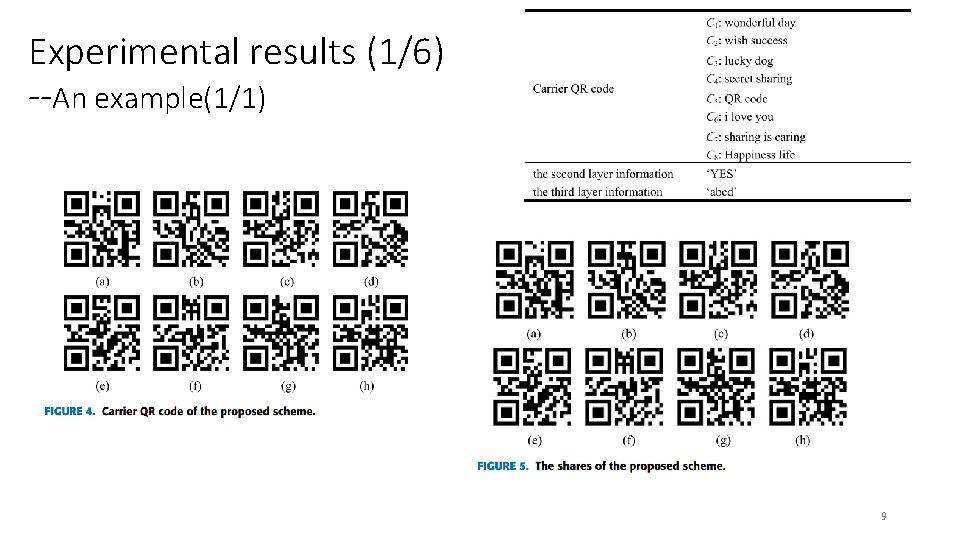
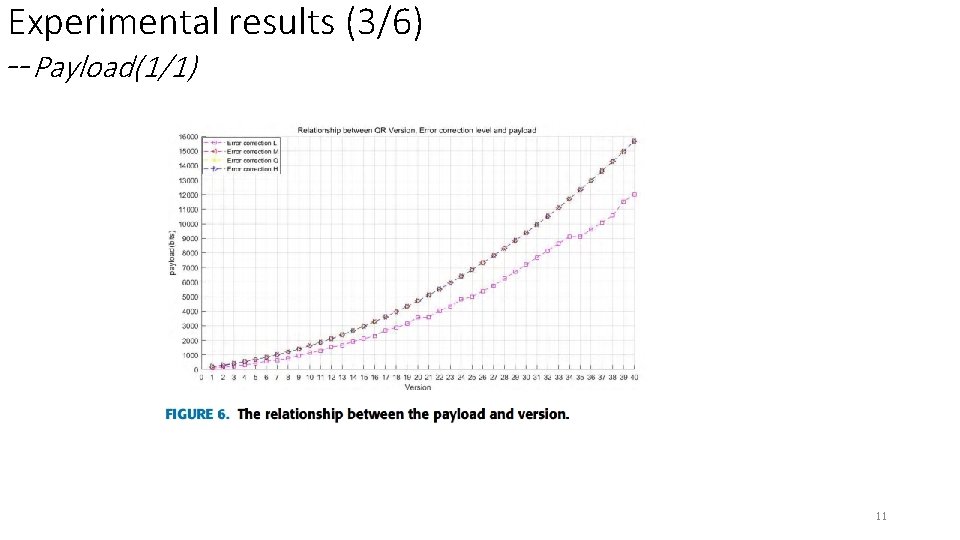
Proposed scheme (3/3) Suppose p=3 Example: [7, 4] Hamming code, the parity check matrix H is : Embedding process: Cover vector Stego vector x’ = Change one bit in x according to coset leader associated to syndrome = Change one bit in x according to coset leader associated to = Change one bit in according to coset leader associated to = [0010100] Extraction process:
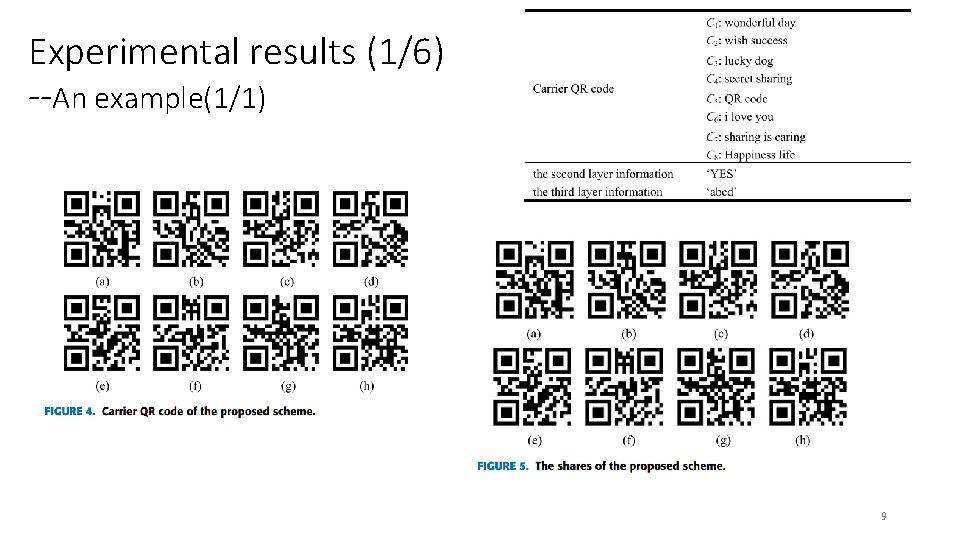
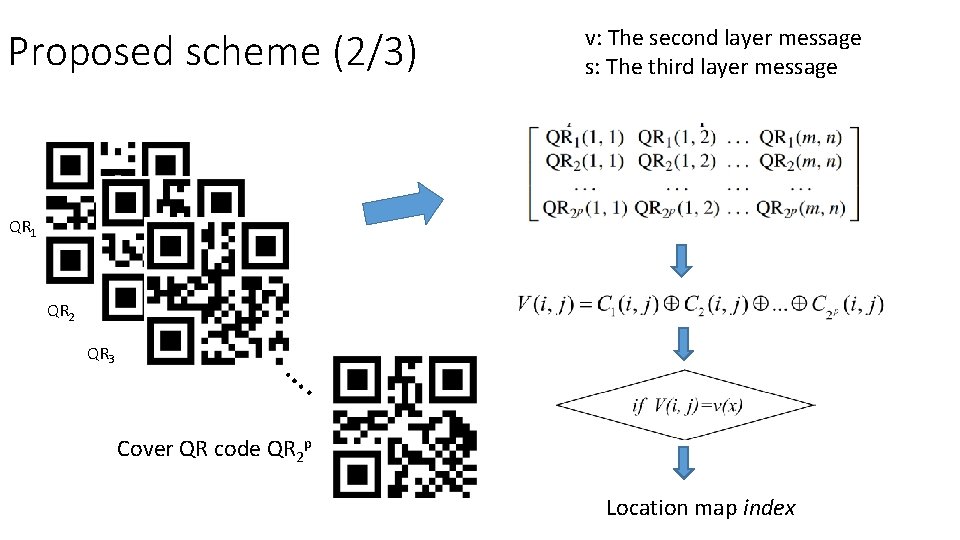
Experimental results (1/6) --An example(1/1) 9
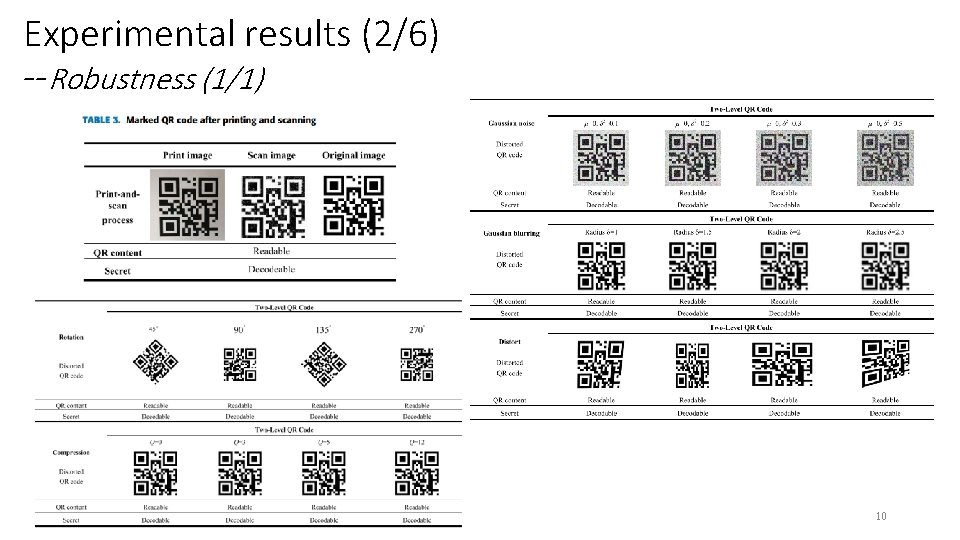
Experimental results (2/6) --Robustness (1/1) 10
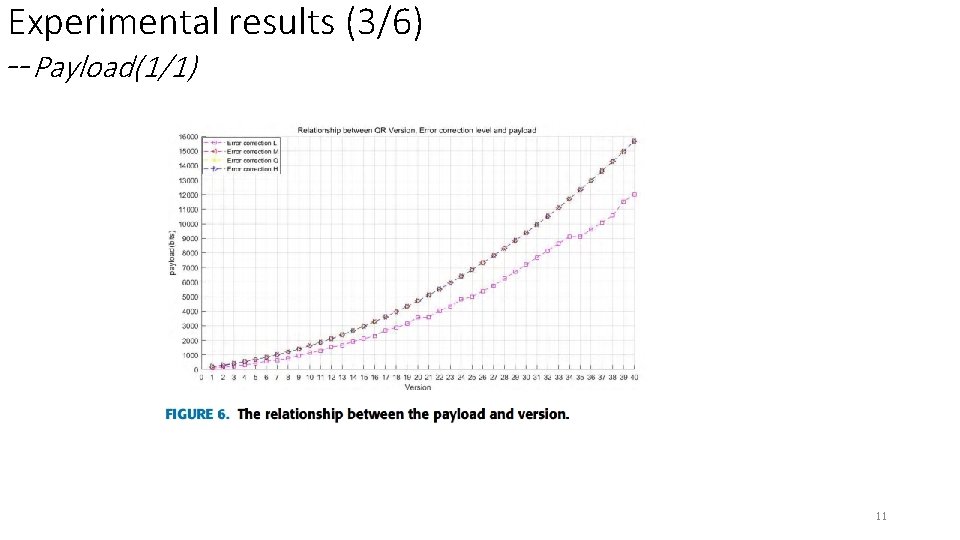
Experimental results (3/6) --Payload(1/1) 11
![Experimental results 46 Comparison13 9 P Y Lin Distributed secret sharing approach with cheater Experimental results (4/6) --Comparison(1/3) [9] P. -Y. Lin, ‘‘Distributed secret sharing approach with cheater](https://slidetodoc.com/presentation_image_h2/78d82cd514afbc2222c804a83716f567/image-12.jpg)
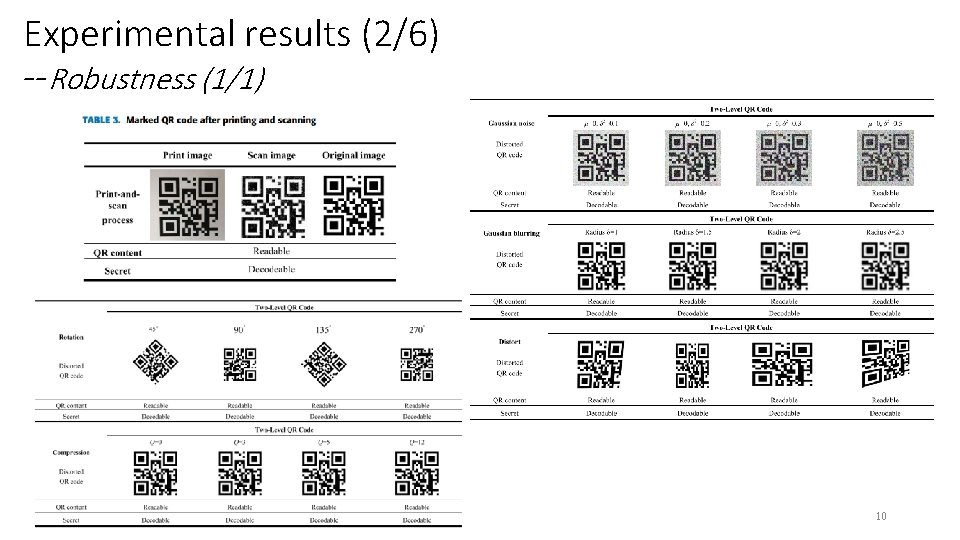
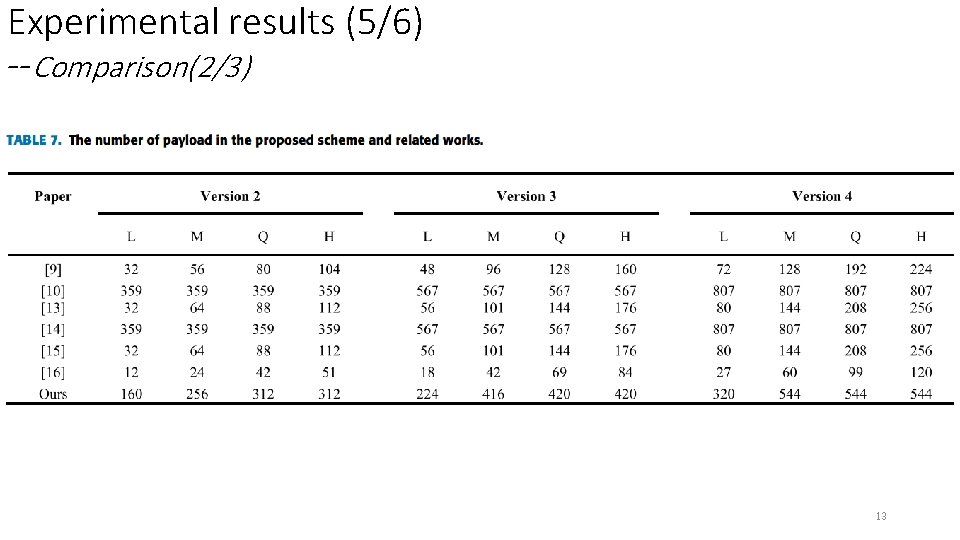
Experimental results (4/6) --Comparison(1/3) [9] P. -Y. Lin, ‘‘Distributed secret sharing approach with cheater prevention based on QR code, ’’ IEEE Trans. Ind. Informat. , vol. 12, no. 1, pp. 384– 392, Feb. 2016. [13] Y. W. Chow, W. Susilo, G. Yang, J. G. Phillips, and I. A. M. P. Barmawi, ‘‘Exploiting the error correction mechanism in QR codes for secret sharing, ’’ in Proc. ACISP, 2016, pp. 409– 425 [14] Y. Liu, Z. Fu, and Y. Wang, ‘‘Two-level information management scheme based on visual cryptography and qr code, ’’ Appl. Res. Comput. , vol. 33, pp. 3460– 3463, Nov. 2016. [15] S. Wan, Y. Lu, X. Yan, Y. Wang, and C. Chang, ‘‘Visual secret sharing scheme for (k, n) threshold based on QR code with multiple decryptions, ’’ J. Real-Time Image Process. , vol. 14, no. 1, pp. 25– 40, Jan. 2018 [16] P. -C. Huang, Y. -H. Li, C. -C. Chang, and Y. Liu, ‘‘Efficient scheme for secret hiding in QR code by improving exploiting modification direction, ’’ KSII Trans. Internet Inf. Syst. , vol. 12, no. 5, pp. 2348– 2365, 2018. 12
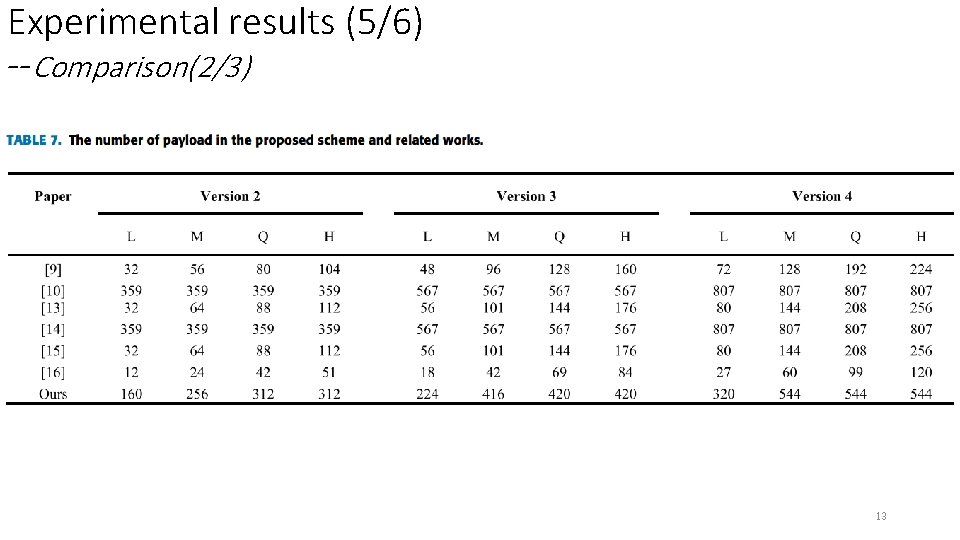
Experimental results (5/6) --Comparison(2/3) 13
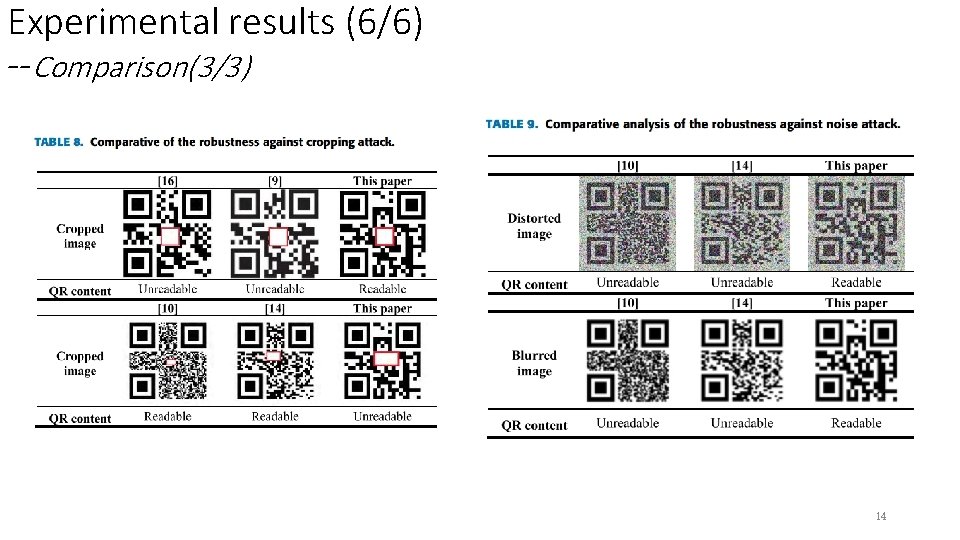
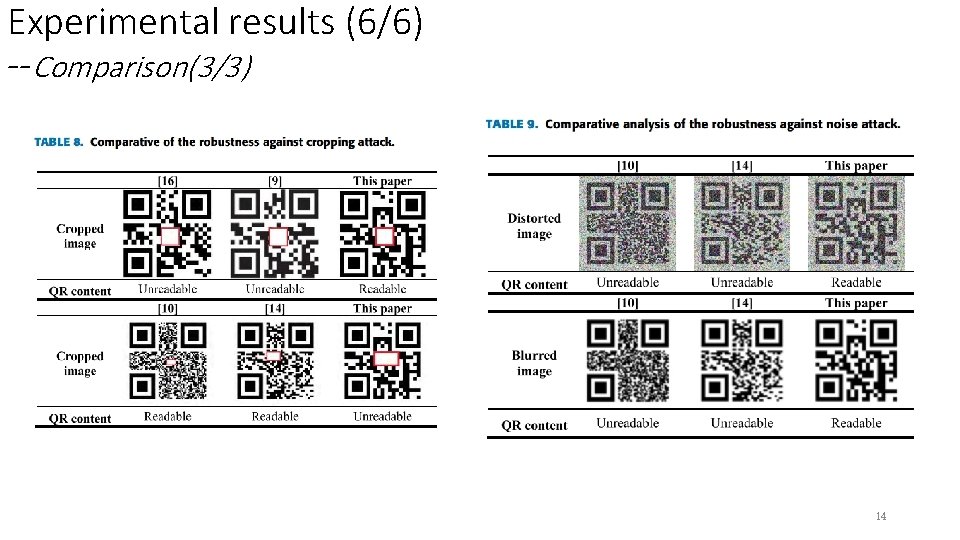
Experimental results (6/6) --Comparison(3/3) 14
Conclusions • Three-layer information storage • Large secret payload • Low computational complexity • Robust against common image post-processing attacks 15
Comments • (n, n)-threshold SS => (2 p, 2 p)-threshold SS • Requires side information to extract secret message, such as the length of secret message, location map, parity check matrix H. • Poor Robustness. 16