RFID The Problems of Cloning and Counterfeiting Ari
RFID: The Problems of Cloning and Counterfeiting Ari Juels RSA Laboratories 19 October 2005
RFID devices take many forms
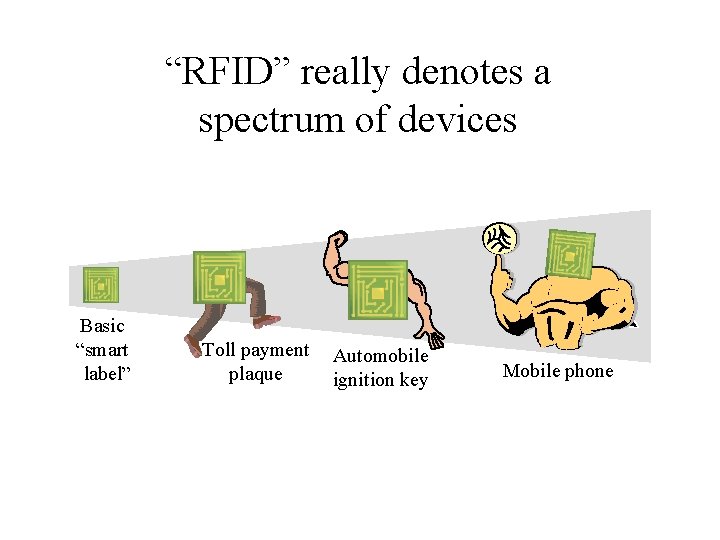
“RFID” really denotes a spectrum of devices Basic “smart label” Toll payment plaque Automobile ignition key Mobile phone
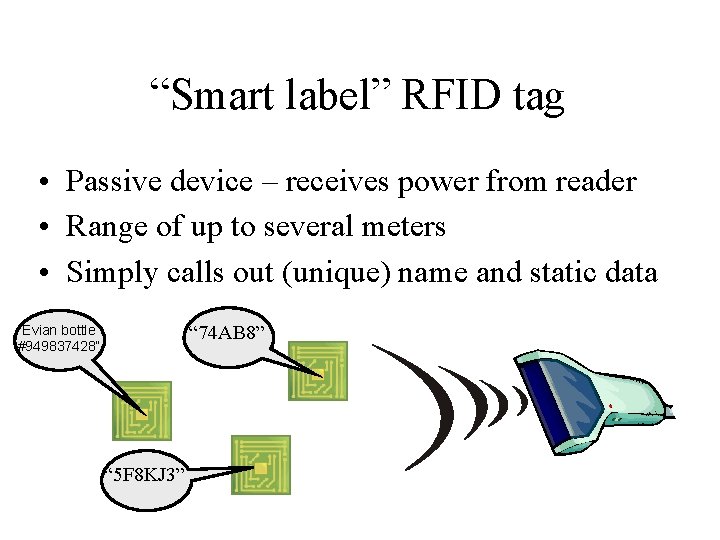
“Smart label” RFID tag • Passive device – receives power from reader • Range of up to several meters • Simply calls out (unique) name and static data “ 74 AB 8” “Evian bottle #949837428” “ 5 F 8 KJ 3”
Capabilities of “smart label” RFID tag • Little memory – Static 96 -bit+ identifier in current ultra-cheap tags – Hundreds of bits soon • Little computational power – Several thousand gates (mostly for basic functionality) – No real cryptographic functions possible – Pricing pressure may keep it this way for a while, i. e. , Moore’s Law will have delayed impact
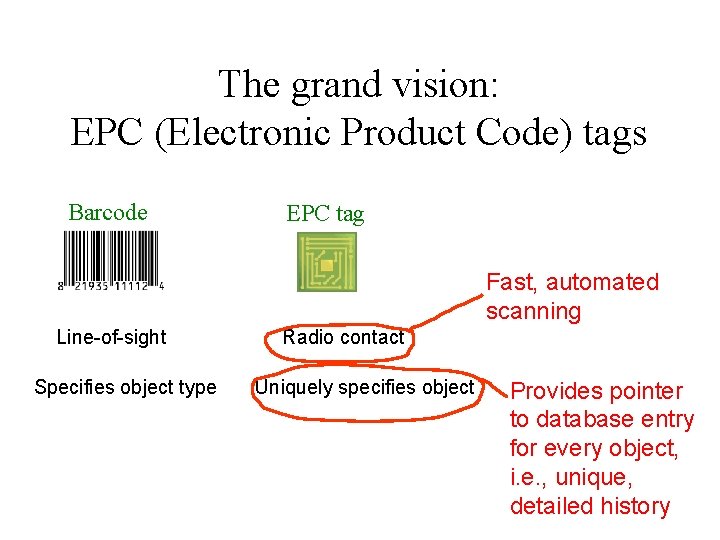
The grand vision: EPC (Electronic Product Code) tags Barcode EPC tag Fast, automated scanning Line-of-sight Specifies object type Radio contact Uniquely specifies object Provides pointer to database entry for every object, i. e. , unique, detailed history
Impending explosion in (EPC) RFID use • EPCglobal – Joint venture of UCC and EAN – Wal-Mart, Procter & Gamble, Do. D, etc. – Recently ratified new EPC-tag standard (Class 1 Gen 2) • Pallet and case tagging first – Item-level retail tagging, automated tills, seem years away • Estimated costs • 2008: $0. 05 per tag; hundreds of dollars per reader (? ) • Beyond: $0. 01 per tag; several dollars per reader (? )
Other forms of RFID • Automobile immobilizers • Payment devices – Currency?
Other forms of RFID “Not Really Mad” • Tracking cattle • Passports

Other forms of RFID • Medical compliance • RFID readers in mobile handsets Showtimes: 16. 00, 19. 00
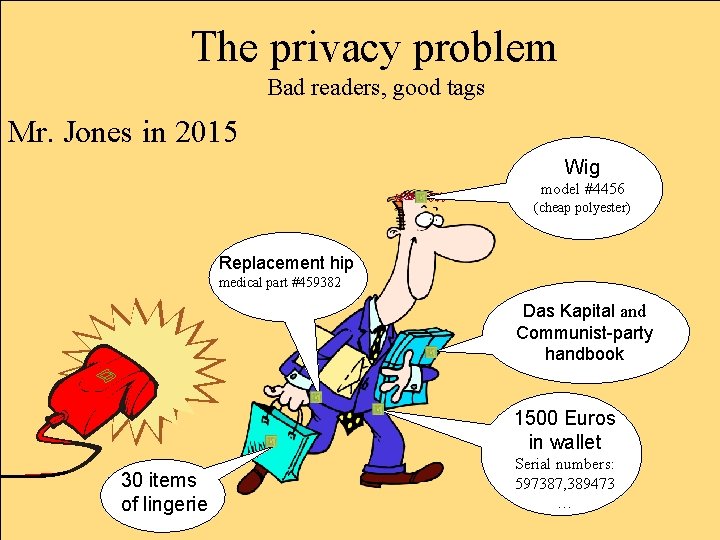
The privacy problem Bad readers, good tags Mr. Jones in 2015 Wig model #4456 (cheap polyester) Replacement hip medical part #459382 Das Kapital and Communist-party handbook 1500 Euros in wallet 30 items of lingerie Serial numbers: 597387, 389473 …
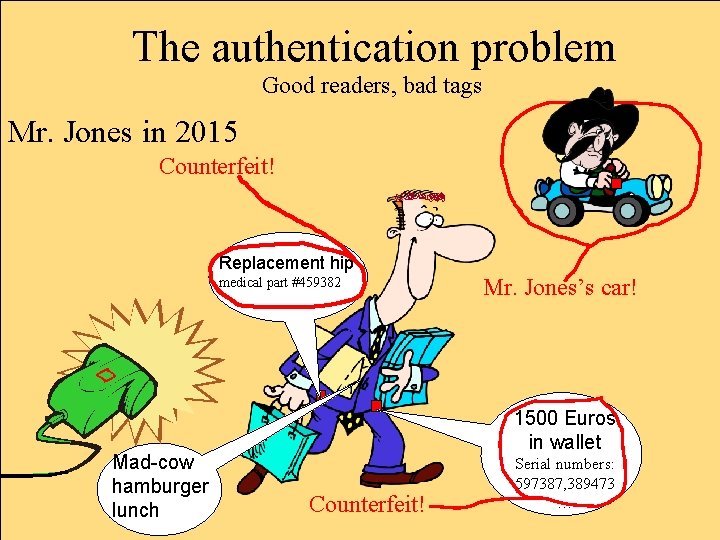
The authentication problem Good readers, bad tags Mr. Jones in 2015 Counterfeit! Replacement hip medical part #459382 Mad-cow hamburger lunch Mr. Jones’s car! 1500 Euros in wallet Counterfeit! Serial numbers: 597387, 389473 …
RFID and sensors will underpin critical infrastructure Authentication therefore has many facets: – Physical security – Consumer goods and pharmaceuticals safety – Transaction security – Brand value …but it’s getting short shrift I’ll talk about three different projects on RFID authentication
The Digital Signature Transponder (DST) Joint work with S. Bono, M. Green, A. Stubblefield, A. Rubin, and M. Szydlo USENIX Security ‘ 05
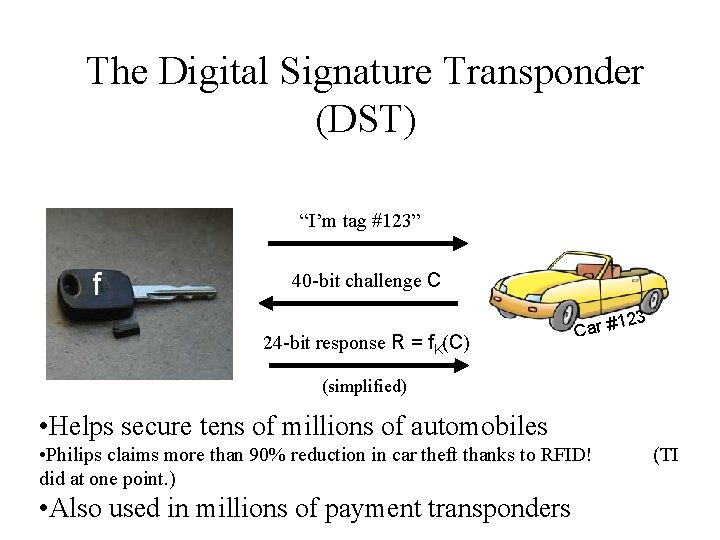
The Digital Signature Transponder (DST) “I’m tag #123” f 40 -bit challenge C 23 24 -bit response R = f. K(C) 1 Car # (simplified) • Helps secure tens of millions of automobiles • Philips claims more than 90% reduction in car theft thanks to RFID! did at one point. ) • Also used in millions of payment transponders (TI
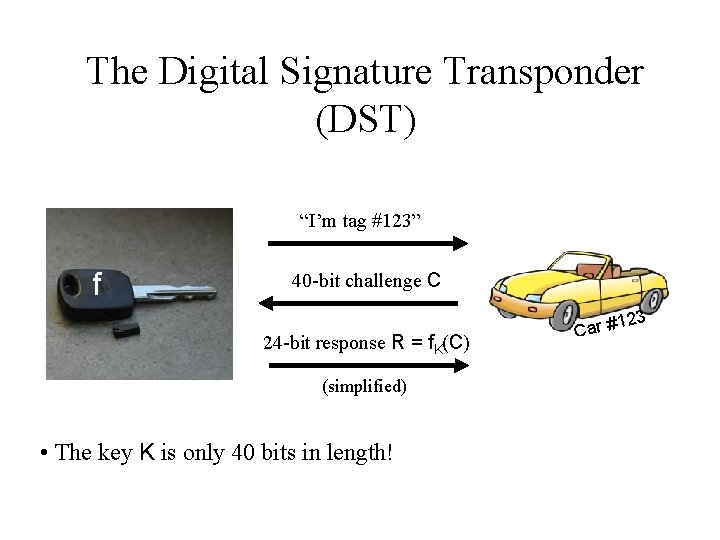
The Digital Signature Transponder (DST) “I’m tag #123” f 40 -bit challenge C 23 24 -bit response R = f. K(C) (simplified) • The key K is only 40 bits in length! 1 Car #
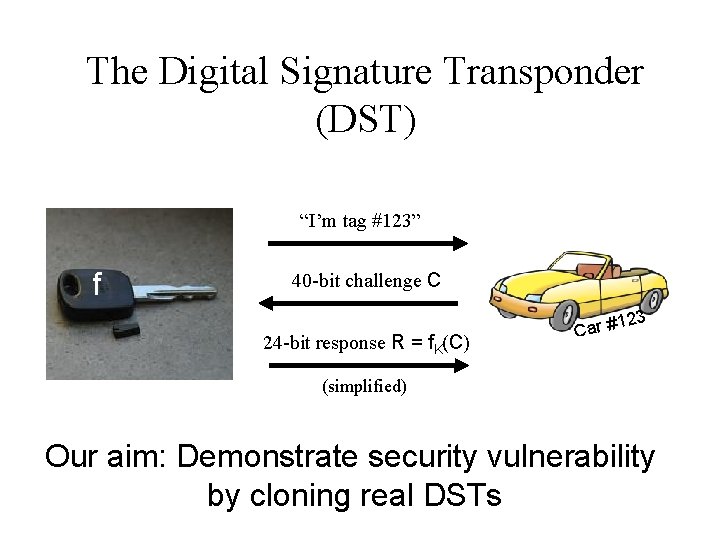
The Digital Signature Transponder (DST) “I’m tag #123” f 40 -bit challenge C 23 24 -bit response R = f. K(C) 1 Car # (simplified) Our aim: Demonstrate security vulnerability by cloning real DSTs
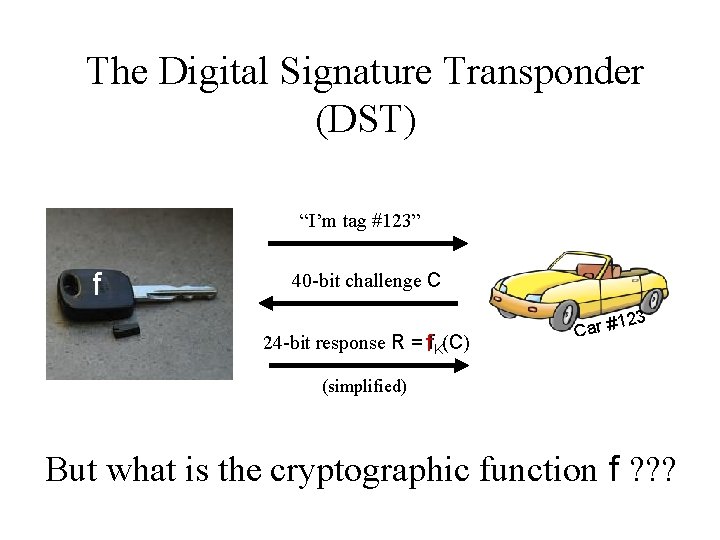
The Digital Signature Transponder (DST) “I’m tag #123” f 40 -bit challenge C 24 -bit response R = f K(C) 23 1 Car # (simplified) But what is the cryptographic function f ? ? ?
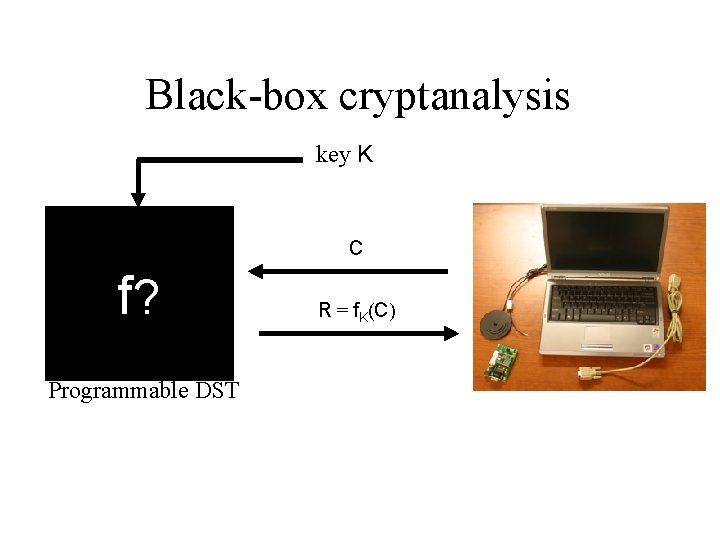
Black-box cryptanalysis key K C f? Programmable DST R = f. K(C)
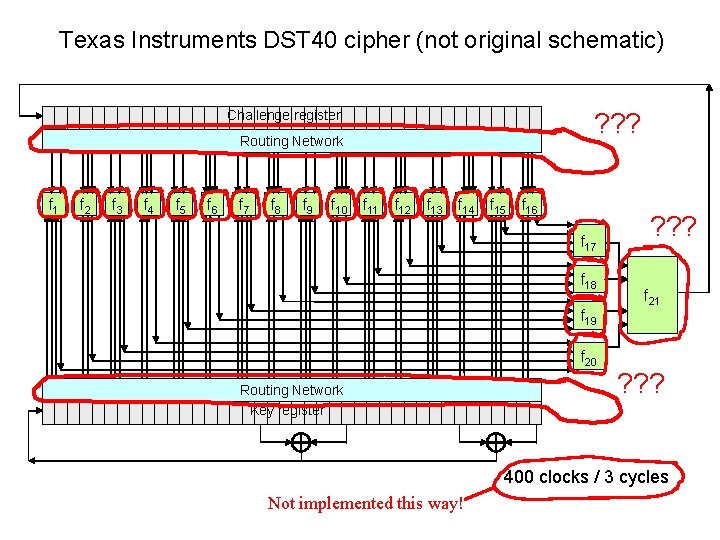
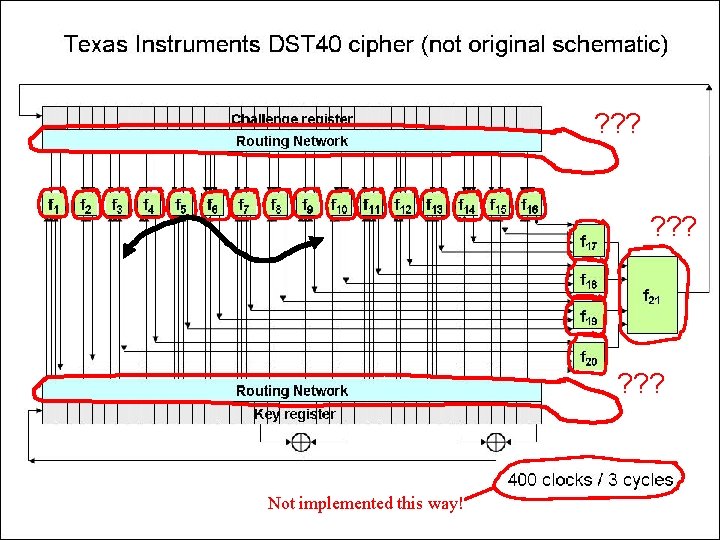
Texas Instruments DST 40 cipher (not original schematic) Challenge register ? ? ? Routing Network f 1 f 2 f 3 f 4 f 5 f 6 f 7 f 8 f 9 f 10 f 11 f 12 f 13 f 14 f 15 f 16 f 17 f 18 f 19 f 20 Routing Network Key register ? ? ? f 21 ? ? ? 400 clocks / 3 cycles Not implemented this way!

Texas Instruments DST 40 cipher (not original schematic) Challenge register ? ? ? Routing Network f 1 f 2 f 3 f 4 f 5 f 6 f 7 f 8 f 9 f 10 f 11 f 12 f 13 f 14 f 15 f 16 f 17 f 18 f 19 f 20 Routing Network Key register ? ? ? f 21 ? ? ? 400 clocks / 3 cycles Not implemented this way!
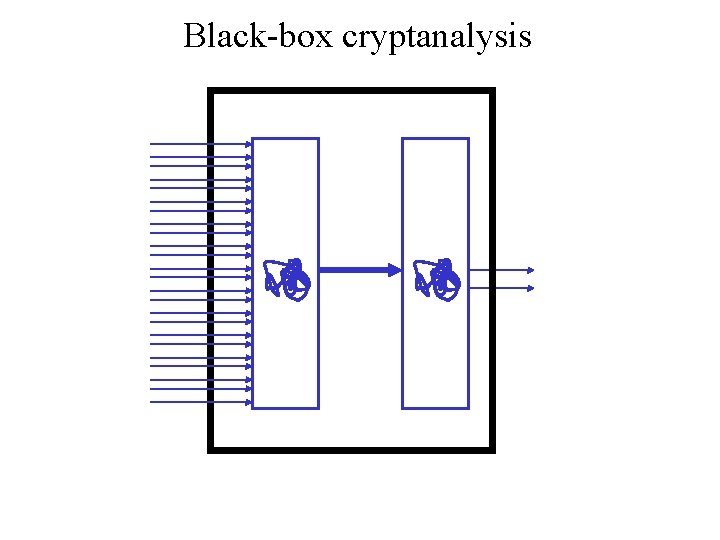
Black-box cryptanalysis
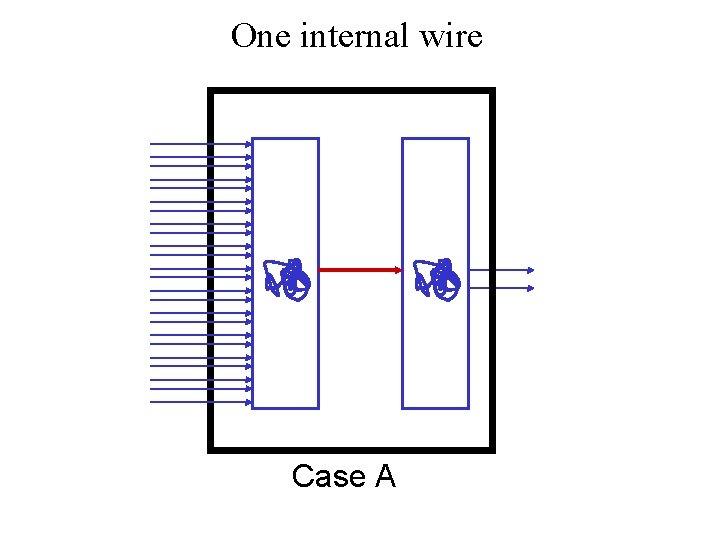
One internal wire Case A
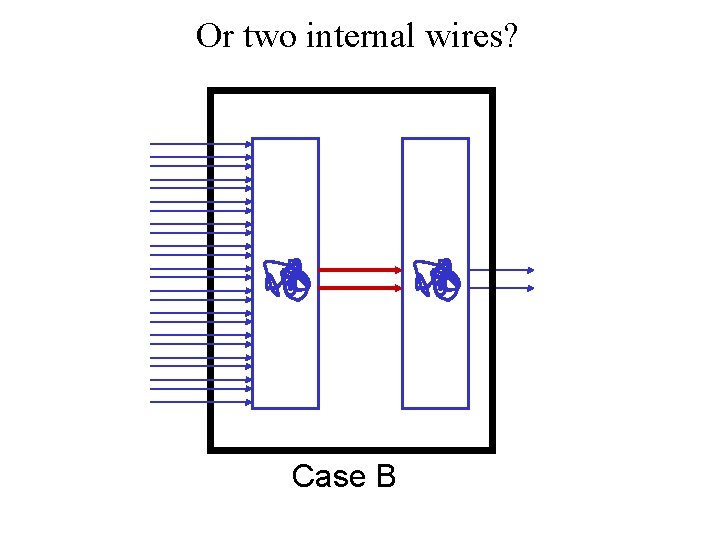
Or two internal wires? Case B
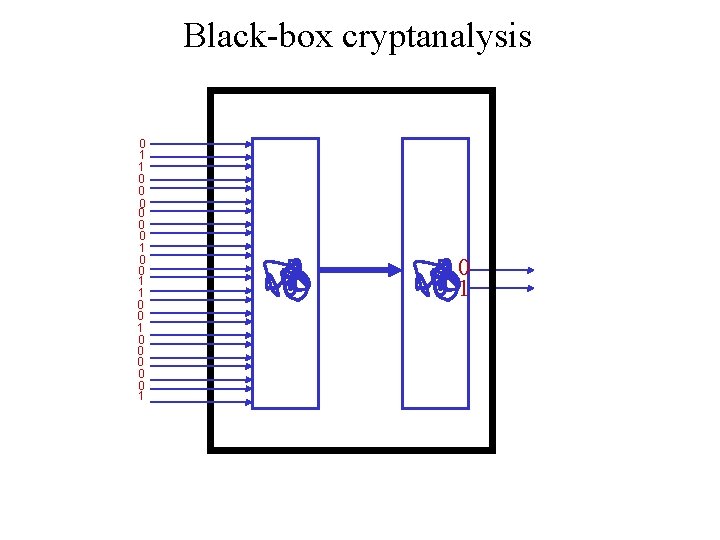
Black-box cryptanalysis 0 1 1 0 0 0 1 0 0 0 1


2 possible values Case A 4 possible values Case B
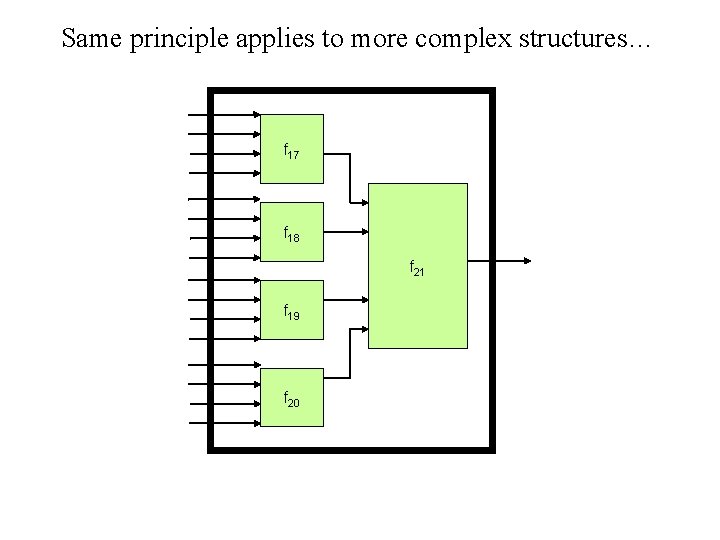
Same principle applies to more complex structures… f 17 f 18 f 21 f 19 f 20
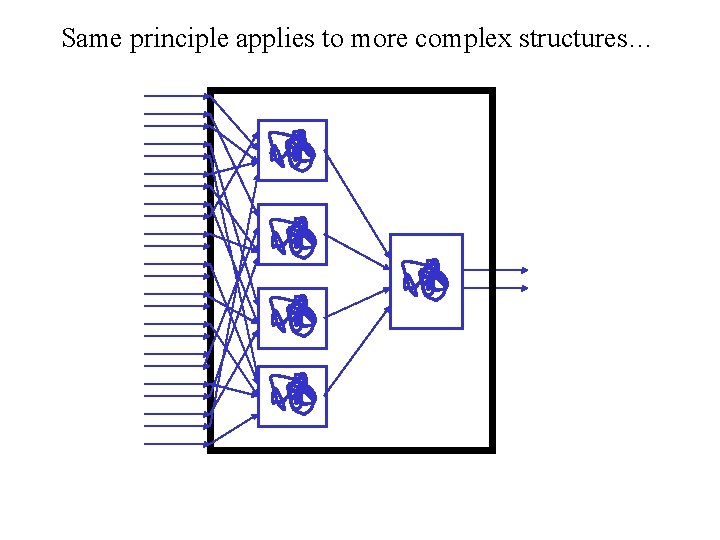
Same principle applies to more complex structures…
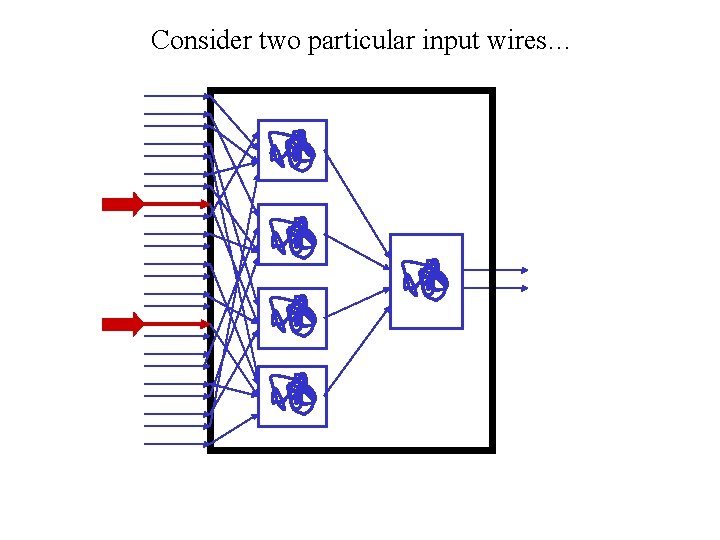
Consider two particular input wires…
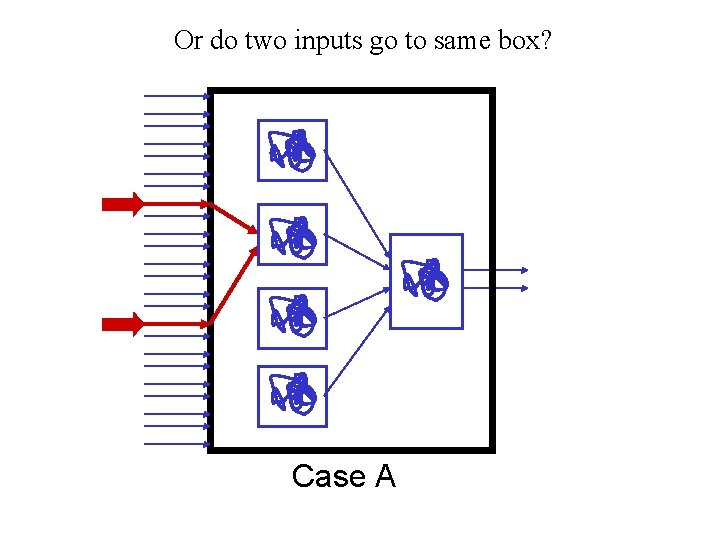
Or do two inputs go to same box? Case A
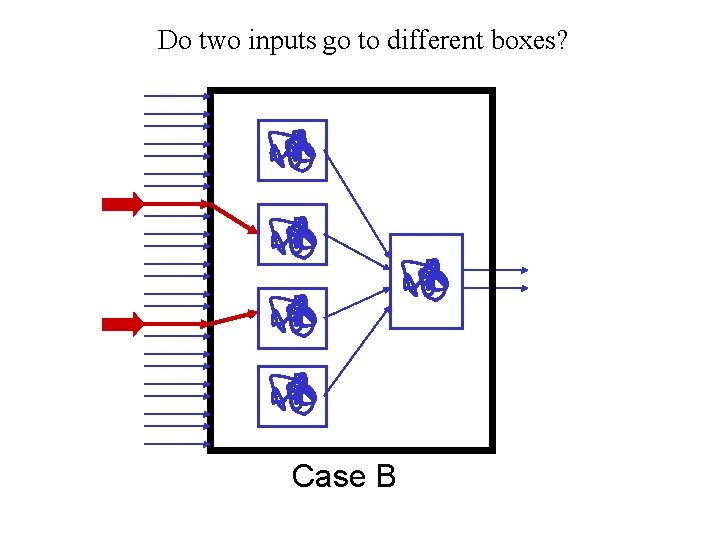
Do two inputs go to different boxes? Case B

One internal wire Case A Two internal wires Case B
? ? ? f ? ? ? Not implemented this way!
The full cloning process 1. Skimming 2. Key cracking 3. Simulation
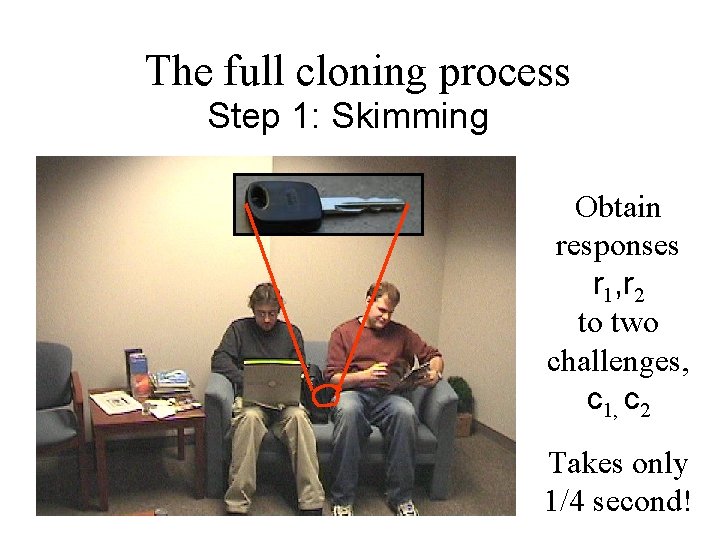
The full cloning process Step 1: Skimming Obtain responses r 1, r 2 to two challenges, c 1, c 2 Takes only 1/4 second!
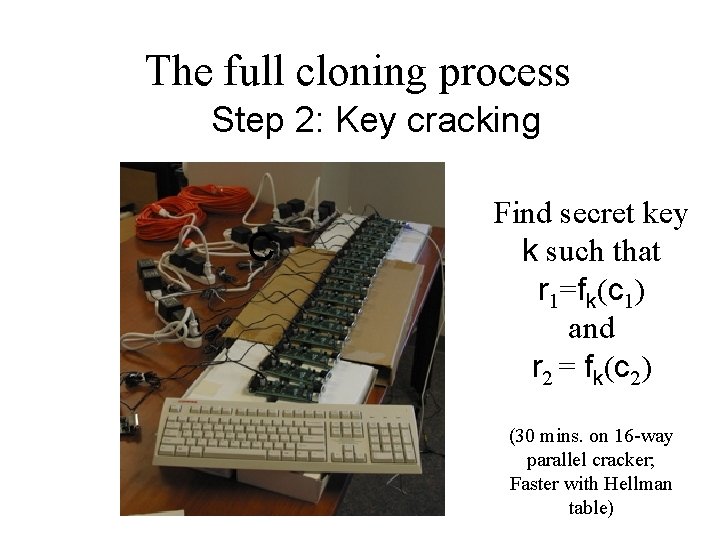
The full cloning process Step 2: Key cracking C Find secret key k such that r 1=fk(c 1) and r 2 = fk(c 2) (30 mins. on 16 -way parallel cracker; Faster with Hellman table)
The full cloning process Step 3: Simulation Simulate radio protocols with computation of fk
“Human” authentication for RFID tags Joint work with Steve Weis Crypto ‘ 05
RFID tags are a little like people ≈ • Very limited memory for numbers • Very limited ability for arithmetic computation

Hopper-Blum (HB) Human Identification Protocol
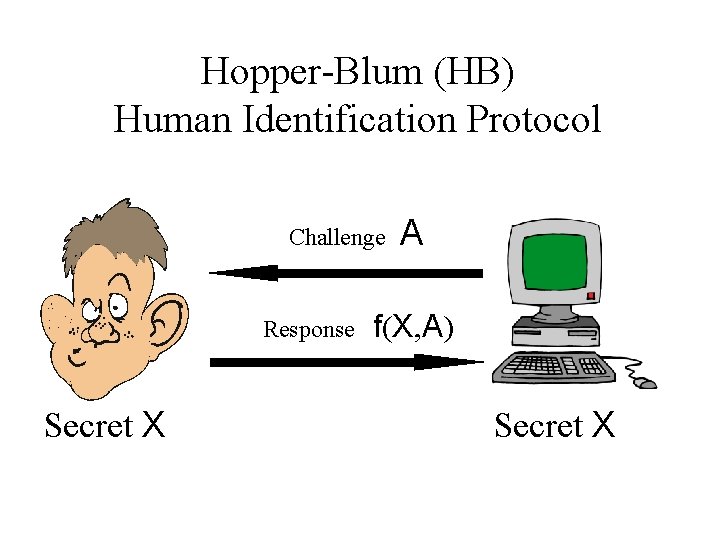
Hopper-Blum (HB) Human Identification Protocol Challenge Response Secret X A f(X, A) Secret X
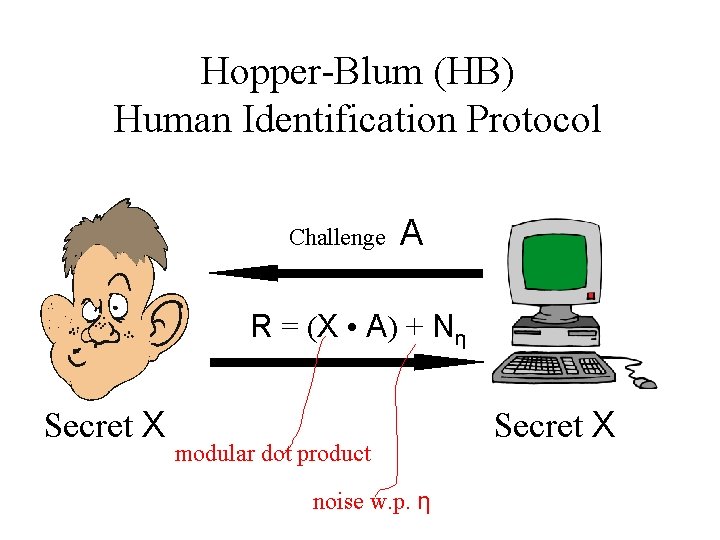
Hopper-Blum (HB) Human Identification Protocol Challenge A R = (X • A) + Nη Secret X modular dot product noise w. p. η Secret X
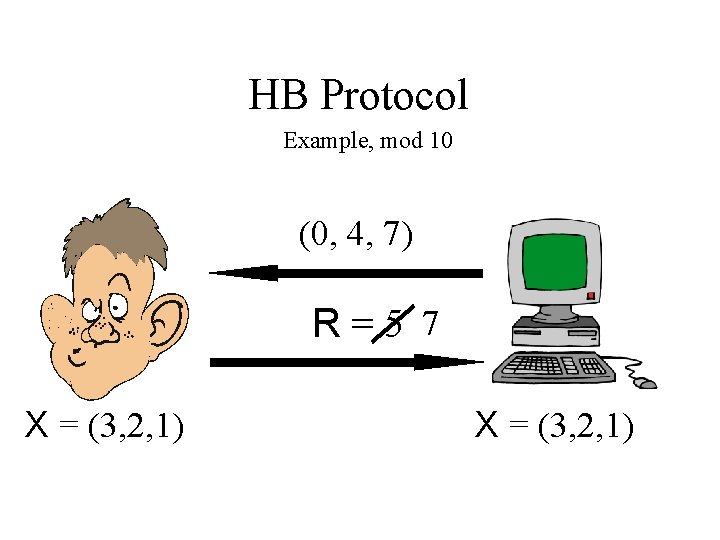
HB Protocol Example, mod 10 (0, 4, 7) R=5 7 X = (3, 2, 1)
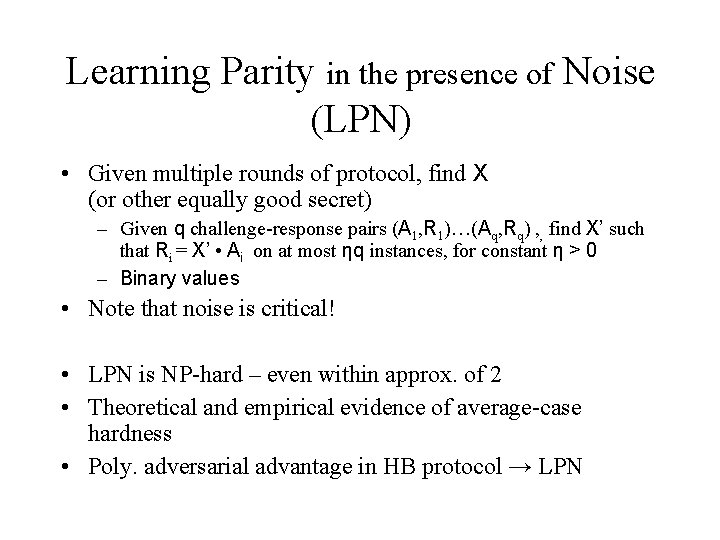
Learning Parity in the presence of Noise (LPN) • Given multiple rounds of protocol, find X (or other equally good secret) – Given q challenge-response pairs (A 1, R 1)…(Aq, Rq) , , find X’ such that Ri = X’ • Ai on at most ηq instances, for constant η > 0 – Binary values • Note that noise is critical! • LPN is NP-hard – even within approx. of 2 • Theoretical and empirical evidence of average-case hardness • Poly. adversarial advantage in HB protocol → LPN
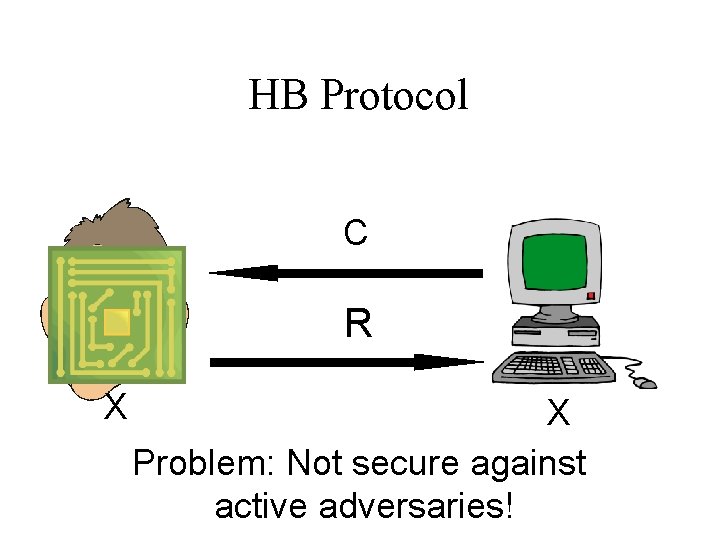
HB Protocol C R X X Problem: Not secure against active adversaries!
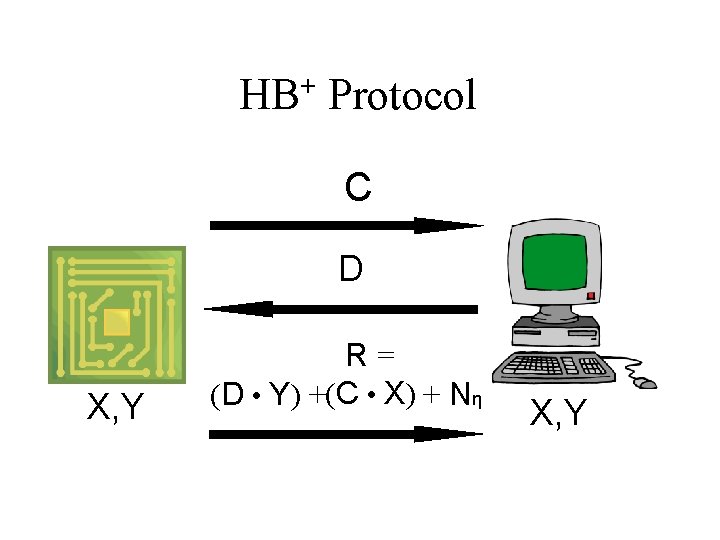
+ HB Protocol C D X, Y R= (D • Y) +(C • X) + Nη X, Y
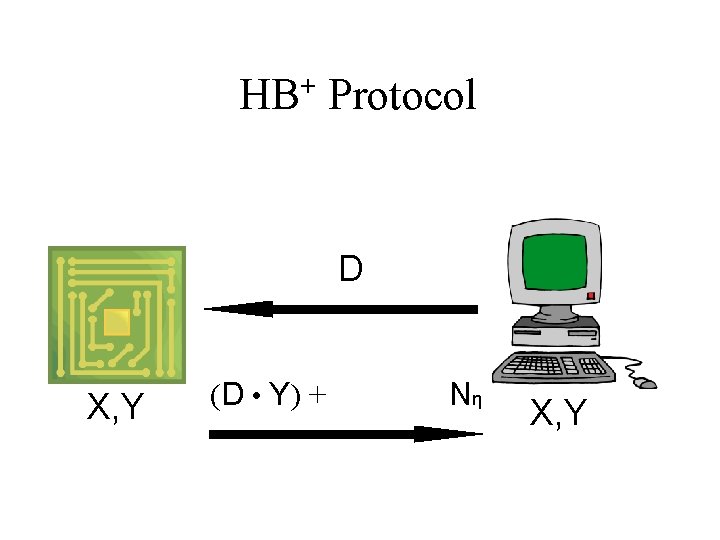
+ HB Protocol D X, Y (D • Y) + + Nη X, Y
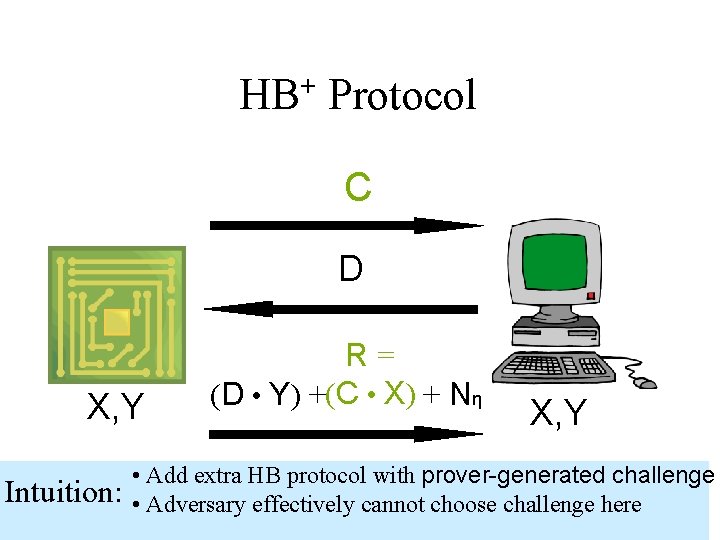
+ HB Protocol C D X, Y Intuition: R= (D • Y) +(C • X) + Nη X, Y • Add extra HB protocol with prover-generated challenge • Adversary effectively cannot choose challenge here
In the paper • Most of paper elaborates security reduction from HB+ to LPN • Implementation of algorithm seems very practical – just linear number of ANDs and XORs and a little noise! – Looks like EPC might be amenable, but…
Further work • Security reduction is concrete, but very loose • What concrete security parameters – key length and communications complexity – yield adequate security? • Limited model: “We win if counterfeiter detected” – Assume counterfeiter aims to duplicate tag without alerting verifier, i. e. , detection model – Appropriate for centralized verifier (with Do. S controls), e. g. , prox cards, casino chips, etc. – Gilbert, Robshaw, and Sibert demonstrate man-in-themiddle attack in stronger prevention model – Can HB techniques be extended to prevention model?
Addressing Cloning of EPC Tags Wi. Se ‘ 05
Inevitable reliance on EPC tags for anti-counterfeiting Drug tracing / anti-counterfeiting n Made i a Canad • EPC (Class-1 Gen-2) is easy to countefeit: It’s basically just a wireless barcode! • Tight tracking is useful per se in combating counterfeiting, e. g. , via duplicate detection • But integrity of tag is needed where data coordination is loose • What can we do today to prevent cloning of EPC tags? • We can use the “kill” feature!
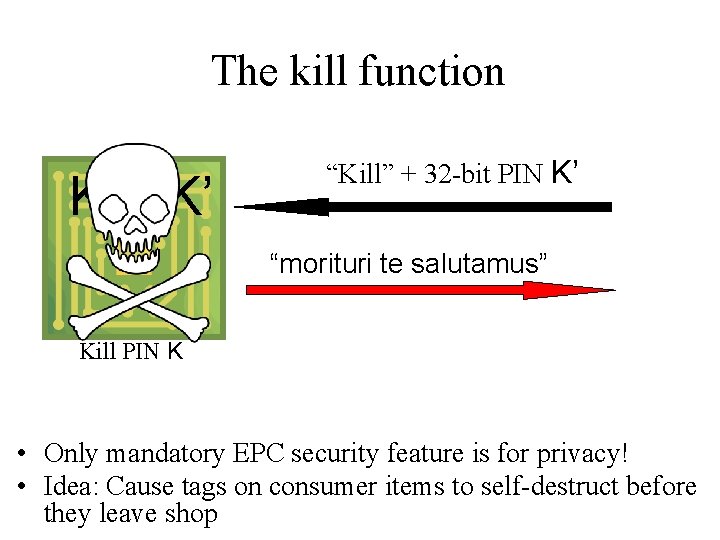
The kill function K = K’ “Kill” + 32 -bit PIN K’ “morituri te salutamus” Kill PIN K • Only mandatory EPC security feature is for privacy! • Idea: Cause tags on consumer items to self-destruct before they leave shop

The kill function K ≠ K’ “Kill” + 32 -bit PIN K’ Bad PIN; [Reset] Kill PIN K • “Kill” authenticates reader, but not very useful for tag authentication since it kills tags!

Low signal strength K ≠ K’ “Kill” + 32 -bit PIN K’ Bad PIN; [Reset] Kill PIN K
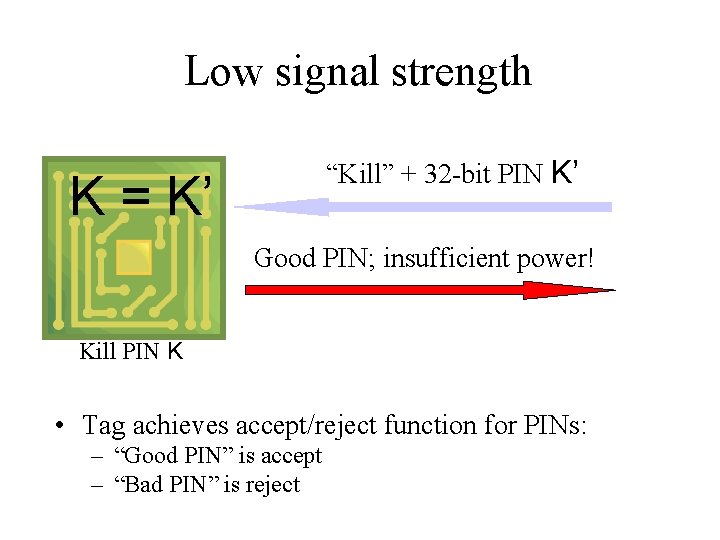
Low signal strength “Kill” + 32 -bit PIN K’ K = K’ Good PIN; insufficient power! Kill PIN K • Tag achieves accept/reject function for PINs: – “Good PIN” is accept – “Bad PIN” is reject
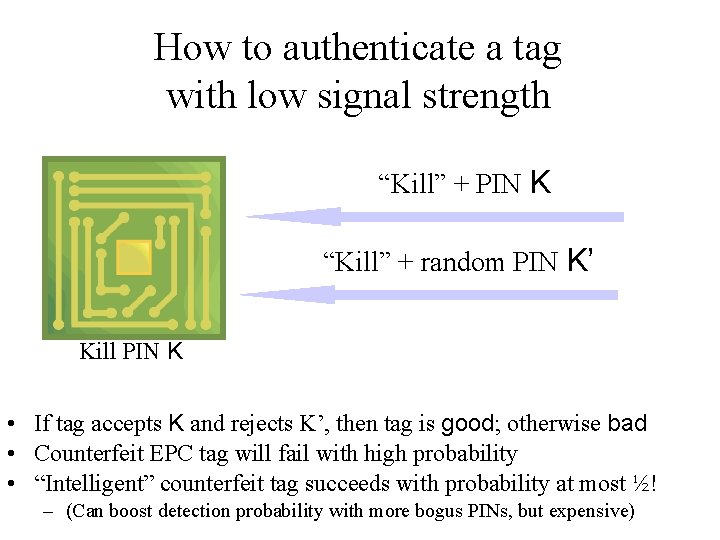
How to authenticate a tag with low signal strength “Kill” + PIN K “Kill” + random PIN K’ Kill PIN K • If tag accepts K and rejects K’, then tag is good; otherwise bad • Counterfeit EPC tag will fail with high probability • “Intelligent” counterfeit tag succeeds with probability at most ½! – (Can boost detection probability with more bogus PINs, but expensive)

Implementing this Scheme • Calibrating signal strength from reader would be hard • Manufacturer can exchange privacy kill feature for authentication kill feature – – Just set tag power threshold required for “kill” very high Tag always thinks signal strength is too low Still complies with EPC standard, which does not specify power threshold Does not comply with conformance specifications • Prob. ½ detection not high for individual clone, but very high for broad supply chain – A little like scheme for detecting fraudulent ballots • Shortcomings: – Vulnerable to short-range eavesdropping – Limited execution on untrusted readers • But much better than no authentication!
Conclusions
Moral 1: Standard crypto modeling fails for cheap RFID Welcome to Hell IT Department 0110010
A cheap RFID tag cannot survive here… but worst case often isn’t reality for RFID Welcome to Hell IT Department 0110010
We need new primitives and flexible modeling • Low-cost tags will probably not be able to do full-blown crypto for some time – Moore’s Law opposed by pricing pressure… • Crypto community should not take black and white view, e. g. , abandon crypto-challenged tags to wolves (EPC Class-1 type) • We need new primitives: – E. g. , can we build good PRFs with really low gate count, e. g. , hundreds of gates? • And new modeling: – What special characteristics do RFID tags present to attackers? • E. g. , physical and radio layers – What security properties can we sacrifice in the real world? • Learning to cut the right corners…
Moral 2 “We have not received one reported incident of fraud in the eight years [the DST] has been used by consumers and we are confident the systems remain secure. ” - Texas Instruments, 10 February 2005 1980: Not one reported incident of a computer virus in the wild 1999: Not one reported incident of a major DDo. S attack on the Internet “This year TI will begin ramping [up] production of its 128 -bit encrypted RFID chips first introduced in early 2003…”
Moral 2 “We have not received one reported incident of fraud in the eight years [the DST] has been used by consumers and we are confident the systems remain secure. ” - Texas Instruments, 10 February 2005 1980: Not one reported incident of a computer virus in the wild 1999: Not one reported incident of a multi-pronged DDo. S attack on the “This Internet year TI will begin ramping [up] production of its 128 -bit encrypted RFID chips first introduced in early 2003…” • RFID is a new critical infrastructure in the making • We should learn from the history of the Internet, where phishing, spam, etc. are crippling e-commerce • Security community must promote and address security in RFID systems before problems become costly and pervasive

To learn more • Primers and current RFID news: – www. rfidjournal. com • RSA Labs RFID Web site: – www. rsasecurity. com/go/rfid – www. rfid-security. com (unofficial) • JHU/RSA RFID Web site: – www. rfidanalysis. org • New survey (and all papers described here) at www. ari-juels. com
- Slides: 66