RFID IN LIBRARY By Bhojdutt Saraswat Librarian K
RFID IN LIBRARY By Bhojdutt Saraswat Librarian K V Ponda
Presentation Highlights • Overview of Current Library Management Systems • Introduction of RFID and Objective, Components • RFID Components for Library • Selection of RFID Components • Application of RFID in Library • Advantages / Dis Advantages • Standards • Vendor Selection • NISO Recommendation • Conclusions
Current Library Management System • Operated Manually or with Barcode • Most Libraries are Staff intensive • Large amount of Routine Procedures • Difficult for Searching a specific book • Card based Issue of Books • Technology Used • Barcode Technology for identification – Very cost effective
Current Library Management System, cont’d • Drawbacks of Barcode Technology: • Barcode readers require a direct line of sight, using laser technology • Scan and read one tag at a time and also time consuming • Human intervention is required to scan a barcode • It should be visible on the product for scanning • Does not have read/write memory • The readability of the barcode can be impaired by dirt, moisture, abrasion and packaging etc. . • Less read range & Holds fixed and Limited data. • Technology is old and outdated • Cannot read a bar code if there is any obstacle between the reader and the bar code
Introduction Radio-frequency identification (RFID) is the wireless non-contact use of radiofrequency electromagnetic fields to transfer data, for the purposes of automatically identifying and tracking tags attached to objects.
Objective of RFID System • The objective of any RFID system is to carry data in suitable transponders, generally known as tags and to retrieve data, by machine readable means, at a suitable time and place and to satisfy particular application needs
Components of RFID System • AN ANTENNA / READER • R F TAGS • CONTROLLERS
Components of RFID System • An antenna / reader • Antennae are the conduits between the tag and the transceiver, which controls the system’s data acquisition and communication. • The antenna emits radio signals to activate the tag and read and write data to it
Components of RFID System • R F TAGS • Passive tags : These tags do not carry on-board power and derive it from the reader to enable reading and writing to the tag. • Active tags : have a built in power cell.
Components of RFID System • Controllers • The controller is the interface between one or more antenna and the device requesting information from or writing information to the RF tags. There are controllers for interfacing antenna to PCs servers and networks. The selection of controller and interface device will affect the antenna’s transmission speed. Some controllers can be programmed to perform data translation and interrogation. This transfers some of data processing load from the devices to the controllers.
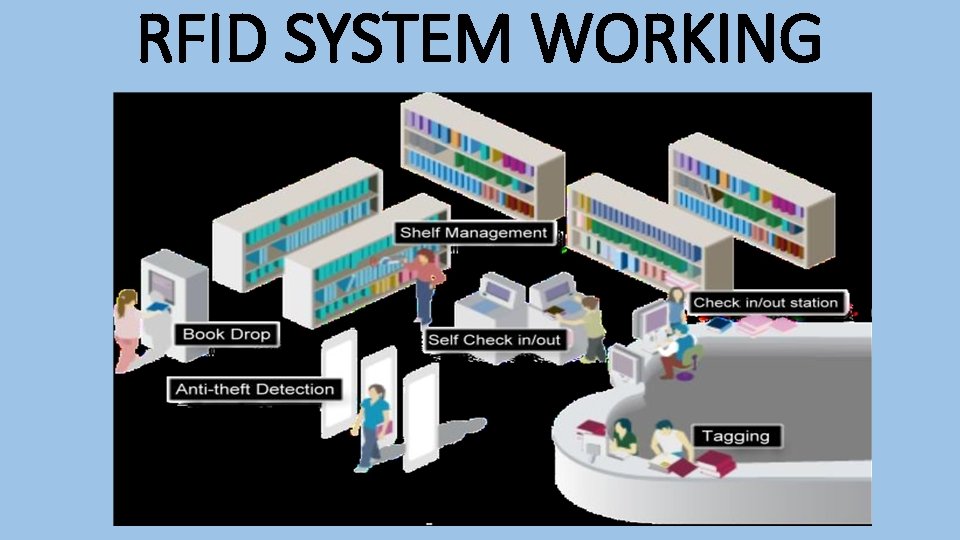
RFID SYSTEM WORKING
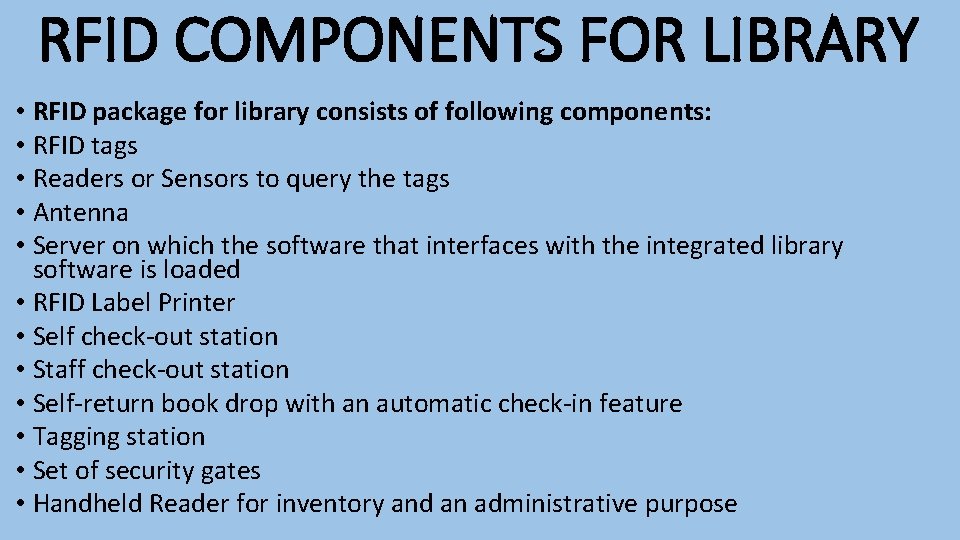
RFID COMPONENTS FOR LIBRARY • RFID package for library consists of following components: • RFID tags • Readers or Sensors to query the tags • Antenna • Server on which the software that interfaces with the integrated library software is loaded • RFID Label Printer • Self check-out station • Staff check-out station • Self-return book drop with an automatic check-in feature • Tagging station • Set of security gates • Handheld Reader for inventory and an administrative purpose
SELECTION OF RFID COMPONENTS • Selecting tags: • Size and form factor – where does the tag have to fit? • How close the tags be to each other • Durability – will the tag need to have a strong outer protection against regular wear and tear • Is the tag re-usable • Resistance to harsh environment(corrosive, steam…) • Polarization – what will be tag orientation with the respect to the reader field • Exposure to different temperature ranges • Communication distance
• Influence of the materials such as metals and liquids • Environment (electrical noise other radio device and equipments) • Operating frequencies(LF, HF, UHF, MW) • Supported communication standards and protocols • Regional regulations(Europe, Asia, USA. . ) • Anti-collision how many tags in the field at the same time how quickly must they be detected • How fast will tags move through the reader field • Does the tag need to have security data protection by encryption
Application of RFID in Library • Self-Issue : Self-issue stations come in a wide variety of shapes and sizes. • • Operation is straightforward, typically: Borrowers present their identification to the unit. (This might be another RFID enabled card, a barcode or some other technology) Depending on library policy they may be required to enter a PIN code or password. Items are placed on the reading table Items are read and passed for checking to the LMS using SIP (Standard Interchange Protocol) The LMS returns its decision to the Self Service Unit (or SSU) (again via SIP) Any items that may not be loaned will be advised on screen Security data is written to the tags to allow or deny them to pass the security gates. A receipt may optionally be printed
• Self-Return : Items may be returned in a similar way to self- issue but in most cases a borrower card is not required for a return. The operation is even simpler than issue: • Borrowers place items on the reading table • Items are checked by the exchange of SIP messages with the LMS • Borrowers place returned items in bins or on shelves as instructed by the unit • A receipt may optionally be printed • The system indicates that the item's tag has been read and recognised. This can be done by using a beep, a light or a message on the display. When the system is first deployed there is a learning curve for both staff and customers. When there is a problem for example a book's tag doesn't read correctly, customers must be able to call on staff to sort out the problem.
• Fine/Charge Payment • Another function that SIP and self-service may be required to provide is fine and charge payment. • Fines will be generated and managed by the LMS, either at the point of issue or on return. • Clients may be prevented from borrowing items because they have exceeded maximum charge limits. • RFID suppliers have a number of solutions available to facilitate financial operations ranging from separate payment stations to integrated units supporting payment technologies as varied as smart card and mobile phones through chip and pin to cash machines – with and without change facilities. • Self-service issue and return are the most common reasons for deploying RFID in the library. Many libraries however have found that the next application delivers even more significant economic returns
• Automatic Sorting • The borrower activates the return function via a touch screen • Items are passed through a slot (resembling a letter box) • RFID tags are read and checked to ensure: • it is an item belonging to the library • if it is a set, that it is complete • SIP messages are exchanged with the LMS to determine the delivery location. • Optionally a receipt is printed.
• Security : • There are two ways in which it does this – using either EAS (Electronic Article Surveillance) or AFI (Application Family Identifier). • Electronic Article Surveillance (EAS): EAS encodes the status of an item on the tag in a similar way to AFI. EAS-based security is, however, entirely proprietary in its nature – each supplier implements EAS security in its own way. EAS is also unable to determine whether an item is a library item or not. In other words the alarm may be set off by an item which is not from the library, e. g. a customer's shopping which has not had its tag de-sensitised. • Application Family Identifier (AFI): The ISO (International Standards body) issues AFI codes for RFID tags to be used in a specific application (such as pharmaceutical brand protection or libraries). This is what stops a library book from setting off the security alarm in a supermarket.
• RFID security requires designated exit routes which are monitored by suitably equipped antenna panels (in a variety of designs). These panels detect the security data encoded in each tag and trigger an alarm whenever an illegal operation is detected. Antennae may also be concealed in existing furniture. • Gates may be installed either to detect that an un-issued item is passing the gates and so sound the alarm or additionally to report the item directly to the LMS. This enables some systems to report which item is in the process of leaving the library and this can be useful when a customer or student is taking out a number of items. • The range at which gates detect items is determined by a number of factors. The size of the aerial, local environmental conditions (such as the presence of large amounts of metal) and the quality of tags and readers will all have an impact on performance. Typically gates will generate a signal all around the gate up to 0. 6 metres giving a central aisle of 1. 2 metres. This is obviously an important consideration when positioning the gates in the library. It is important to discuss gate positioning and tag detection rates with suppliers to ensure that the security element of the solution functions to an acceptable level.
• Stock management • This solution makes locating and identifying items on the shelves an easy task for librarians. It comprises basically of a portable scanner and a base station. • The solution is designed to cover three main requirements: • Search for individual books requested • Inventory check of the whole library stock • Search for books which are miss-shelved
Advantages of RFID in Libraries • To Libraries • Searching & Stock management: Operations such as managing material on the shelves, identifying missing & mis-helved items and taking stocks regularly will be feasible • Improved Patron Services • Spending minimal time on circulation operations allows library staff to assist patrons. • Routine patron services are not disturbed even when libraries are facing staff shortages & budget cuts • Flexibility And Modularity • Ability to add newer products and features as finances and customer needs dictate • Security • Library item identification & security is combined into a single tag, there by eliminating the need to attach an additional security strip
To Library Staff. . • Less time needed for circulation operations • Implementing RFID will considerably reduce the amount of time required to issue, receive, transport, sort & shelve library materials • Efficient Inventory management • Inventory management can be done using a handheld reader without closing the library and is at least 20 times faster compared to existing barcode based system • Reducing Repetitive Stress Injuries (RSI) • RFID based system reduces repetitive scanning of individual items at the circulation desk during check in, check out and hence avoids RSI such as carpal tunnel syndrome • Taking inventory in a rfid based system doesn’t require physical deshelving & shelving of library materials
To Patrons… • • • Patrons will spend less time waiting in check-out lines by using Self Check in - Check out systems Patrons find what they are looking for quickly & easily Reminders for due dates allows patrons to submit borrowed materials in time Use of book drops & return for returning library material, allows for flexible timings RFID enabled patron cards allows for easy patron identification
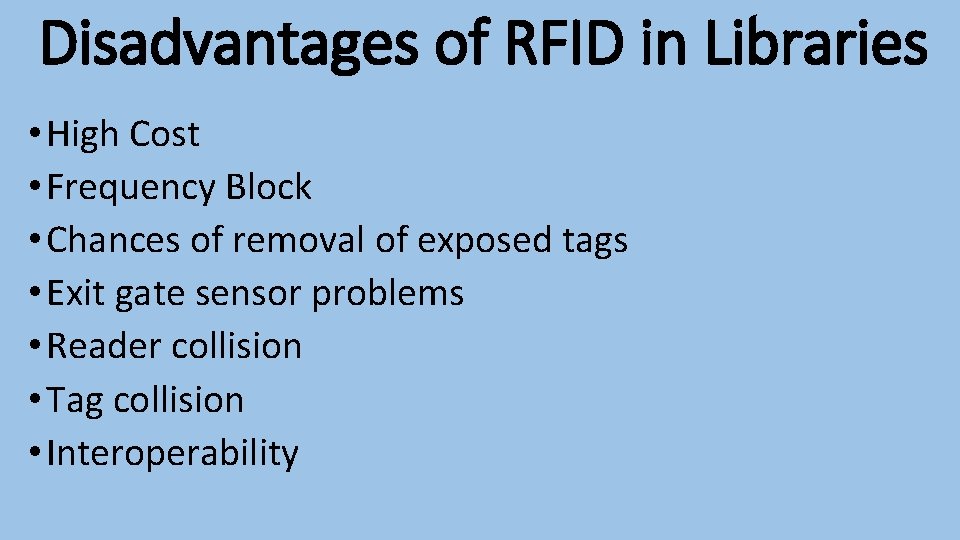
Disadvantages of RFID in Libraries • High Cost • Frequency Block • Chances of removal of exposed tags • Exit gate sensor problems • Reader collision • Tag collision • Interoperability
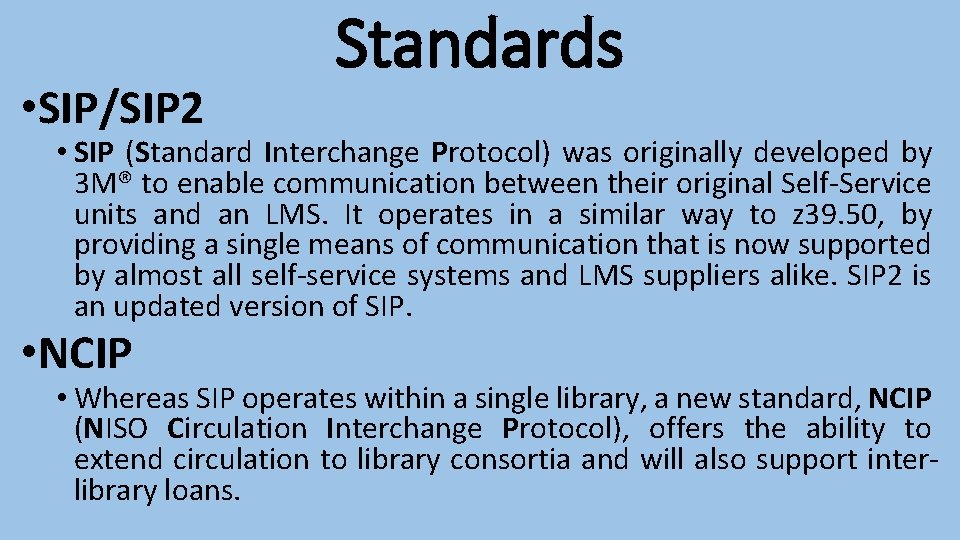
• SIP/SIP 2 Standards • SIP (Standard Interchange Protocol) was originally developed by 3 M® to enable communication between their original Self-Service units and an LMS. It operates in a similar way to z 39. 50, by providing a single means of communication that is now supported by almost all self-service systems and LMS suppliers alike. SIP 2 is an updated version of SIP. • NCIP • Whereas SIP operates within a single library, a new standard, NCIP (NISO Circulation Interchange Protocol), offers the ability to extend circulation to library consortia and will also support interlibrary loans.
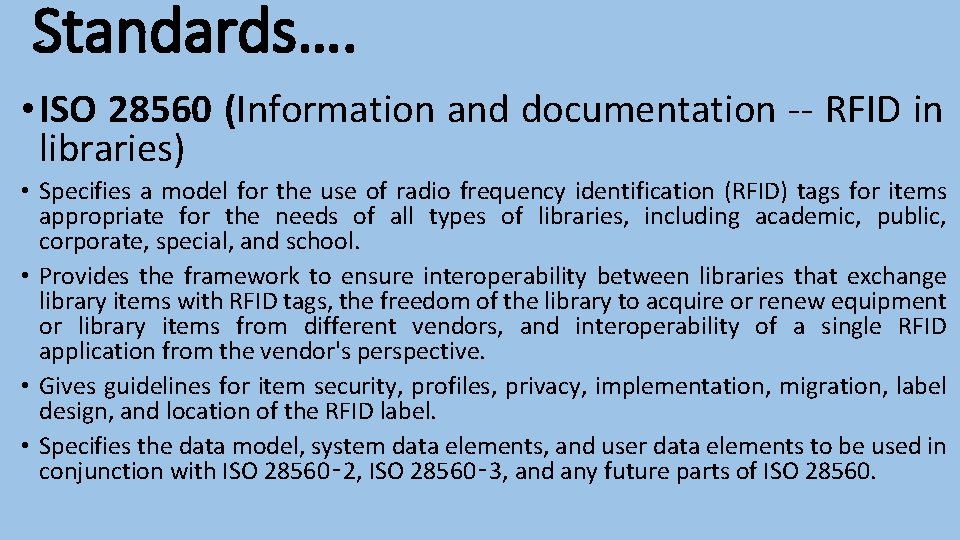
Standards…. • ISO 28560 (Information and documentation -- RFID in libraries) • Specifies a model for the use of radio frequency identification (RFID) tags for items appropriate for the needs of all types of libraries, including academic, public, corporate, special, and school. • Provides the framework to ensure interoperability between libraries that exchange library items with RFID tags, the freedom of the library to acquire or renew equipment or library items from different vendors, and interoperability of a single RFID application from the vendor's perspective. • Gives guidelines for item security, profiles, privacy, implementation, migration, label design, and location of the RFID label. • Specifies the data model, system data elements, and user data elements to be used in conjunction with ISO 28560‑ 2, ISO 28560‑ 3, and any future parts of ISO 28560.

Vendor Selection • Hardware & Software should meet global recommended standards for use of RFID in Libraries • RFID hardware products for library should be compatible with global protocols such as SIP 2 , NCIP, ISO 18000 -3, ISO 15693, ISO 14443 A & ISO 28560 (Part 1, 2 & 3) • Supplied equipment should allow forward compatibility with anticipated new standards • Can we purchase tags from other manufacturers & still be sure of interoperability with existing hardware in future • Will the existing protocols & software work with the new hardware & tags? If not, what is required to make them compatible? • Vendors should make hardware & software upgrades in future to conform to standards • Judge Vendors Technology know how for products to be supplied • Ask for Customer reference & discuss your concerns with them • Special emphasis on Staff training & Local Support
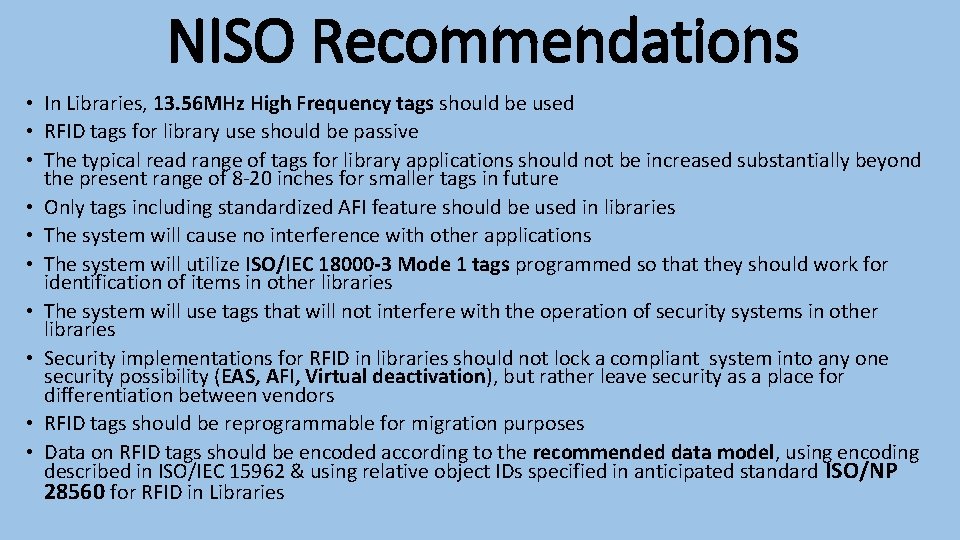
NISO Recommendations • In Libraries, 13. 56 MHz High Frequency tags should be used • RFID tags for library use should be passive • The typical read range of tags for library applications should not be increased substantially beyond the present range of 8 -20 inches for smaller tags in future • Only tags including standardized AFI feature should be used in libraries • The system will cause no interference with other applications • The system will utilize ISO/IEC 18000 -3 Mode 1 tags programmed so that they should work for identification of items in other libraries • The system will use tags that will not interfere with the operation of security systems in other libraries • Security implementations for RFID in libraries should not lock a compliant system into any one security possibility (EAS, AFI, Virtual deactivation), but rather leave security as a place for differentiation between vendors • RFID tags should be reprogrammable for migration purposes • Data on RFID tags should be encoded according to the recommended data model, using encoding described in ISO/IEC 15962 & using relative object IDs specified in anticipated standard ISO/NP 28560 for RFID in Libraries
Conclusion • RFID technology is not only emerging but also more effective, convenient and cost efficient technology in library security. This technology has slowly begun to replace the traditional bar-code on library items • The cost of the technology is main constraint. • RFID in the library speeds up book borrowing, monitoring, books searching processes and thus frees staff to do more user-service tasks. • But the performance varies with respect to RFID readers and tags.
References • http: //ifla. queenslibrary. org/IV/ifla 69/papers • https: //www. iso. org/standard/75672. html • http: //www. ala. org/ala/plapubs/technotes/rfidtechnology • Lib. Best: Library Management System: http: //www. rfid. library. com • eprints. rclis. org/15253/3/RFID. pdf

Thanks
- Slides: 32