Review For Exam 3 Abdou Illia Spring 2015
Review For Exam 3 © Abdou Illia – Spring 2015
Host Hardening 2
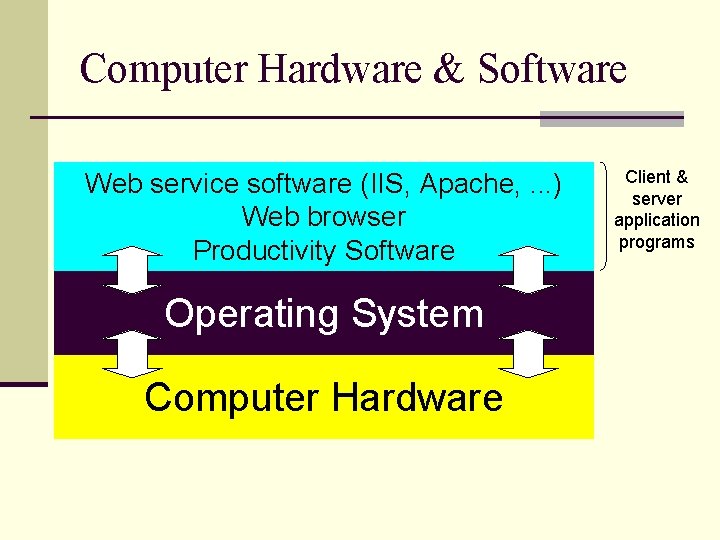
Computer Hardware & Software Web service software (IIS, Apache, . . . ) Web browser Productivity Software Operating System Computer Hardware Client & server application programs
Your knowledge about Host hardening n Which of the following is most likely to make a computer system unable to perform any kind of work or provide any service? a) Client application programs get hacked b) Server application programs (web service software, database service, network service, etc. ) get hacked c) The operating system get hacked d) The connection to the network/Internet get shut down
OS Vulnerability test 2010 by omnired. com n OS tested: n Win XP, Win Server 2003, Win Vista Ultimate, n Mac OS Classic, OS X 10. 4 Server, OS X 10. 4 Tiger OS market share n Free. BSD 6. 2, Solaris 10, Fedora Core 6, Slackware 11. 0, Suse Enterprise 10, Ubuntu 6. 10 n Tools used to test vulnerabilities: n Scanning tools (Track, Nessus) n Network mapping (Nmap command) n All host with OS installation defaults n Results n Microsoft's Windows and Apple's OS X are ripe with remotely accessible vulnerabilities and allow for executing malicious code n The UNIX and Linux variants present a much more robust exterior to the outside n Once patched, however, both Windows and Apple’s OS are secure.
Your knowledge about Host hardening n You performed an Out-of-the-box installation of Windows XP and Linux Free. BSD 6. 2 on two different computers. Which computer is more likely to be secure ? a) b) c) n Windows XP Linux Free. BSD 6. 2 They will have the same level of security What needs to be done, first, in order to prevent a hacker from taking over a server with OS installation defaults that has to be connected to the Internet? a) b) c) Lock the server room Configure the firewall to deny all inbound traffic to the server Download and install patches for known vulnerabilities
Security Baseline n Because it’s easy to overlook something in the hardening process, businesses need to adopt a standard hardening methodology: standard security baseline n Need to have different security baseline for different kind of host; i. e. n n n Different security baselines for different OS and versions Different security baselines for different types of server applications (web service, email service, etc. ) Different security baselines for different types of client applications.
Options for Security Baselines n Organization could use different standards n OS vendors’ baselines and tools n n Standards Agencies baselines n n e. g. Follow MS Installation procedure and use Microsoft Baseline Security Analyzer (MBSA) e. g. Cobi. T* Security Baseline Company’s own security baselines n Security Baseline to be implemented by n Server administrators known as systems admin * Control Objectives for Information and Related Technology
Elements of Hardening n n n n Physical security Secure installation and configuration Fix known vulnerabilities Remove/Turn off unnecessary services (applications) Harden all remaining applications Manage users and groups Manage access permissions n For individual files and directories, assign access permissions to specific users and groups n Back up the server regularly n Advanced protections A c c o r d i n g t o b a s e l i n e
Hardening servers n Choose the OS that provides the following: n n n n Ability to restrict admin access (Administrator vs. Administrators) Granular control of data access Ability to disable services Ability to control executables Ability to log activities Host-based firewall Support for strong authentication and encryption n Disable or remove unnecessary services or applications n n If no longer needed, remove rather than disable to prevent re-enabling Additional services increases the attack vector More services can increase host load and decrease performance Reducing services reduces logs and makes detection of intrusion easier
Hardening servers (cont. ) n Configure user authentication n n n n Remove or disable unnecessary accounts (e. g. Guest account) Change names and passwords for default accounts Disable inactive accounts Assign rights to groups not individual users Don't permit shared accounts if possible Configure time sync Enforce appropriate password policy Use 2 -factor authentication when necessary Always use encrypted authentication
UNIX / Linux Hardening n Many versions of UNIX n No standards guideline for hardening n User can select the user interface n Graphic User Interface (GUI) n Command-Line Interfaces (CLIs) or shells n CLIs are case-sensitive with commands in lowercase except for file names
UNIX / Linux Hardening n Three ways to start services n n n Start a service manually (a) through the GUI, (b) by typing its name in the CLI, or (c) by executing a batch file that does so Using the inetd program to start services when requests come in from users Using the rc scripts to start services automatically at boot up Inetd = Internet daemon; i. e. a computer program that runs in the background
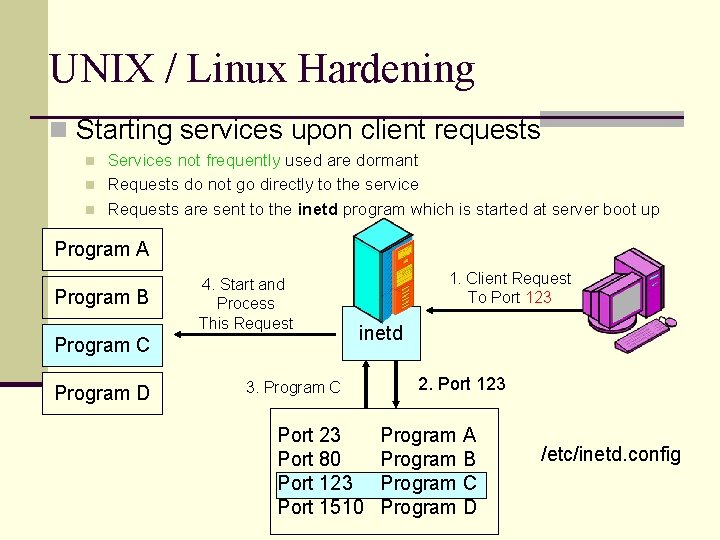
UNIX / Linux Hardening n Starting services upon client requests n n n Services not frequently used are dormant Requests do not go directly to the service Requests are sent to the inetd program which is started at server boot up Program A Program B 4. Start and Process This Request Program C Program D 1. Client Request To Port 123 inetd 3. Program C Port 23 Port 80 Port 123 Port 1510 2. Port 123 Program A Program B Program C Program D /etc/inetd. config
UNIX / Linux Hardening n Turning On/Off unnecessary Services In UNIX n Identifying services running at any moment n ps command (process status), usually with –aux parameters, lists running programs § Shows process name and process ID (PID) n n netstat tells what services are running on what ports Turning Off Services In UNIX n kill PID command is used to kill a particular process § kill 47 (If PID=47)
Advanced Server Hardening Techniques n File Integrity Checker n Creates snapshot of files: a hashed signature (message digest) for each file n After an attack, compares post-hack signature with snapshot n This allows systems administrator to determine which files were changed n Tripwire is a file integrity checker for Linux/UNIX, Windows, etc. : www. tripwire. com (ftp: //coast. cs. purdue. edu/pub/tools/unix)
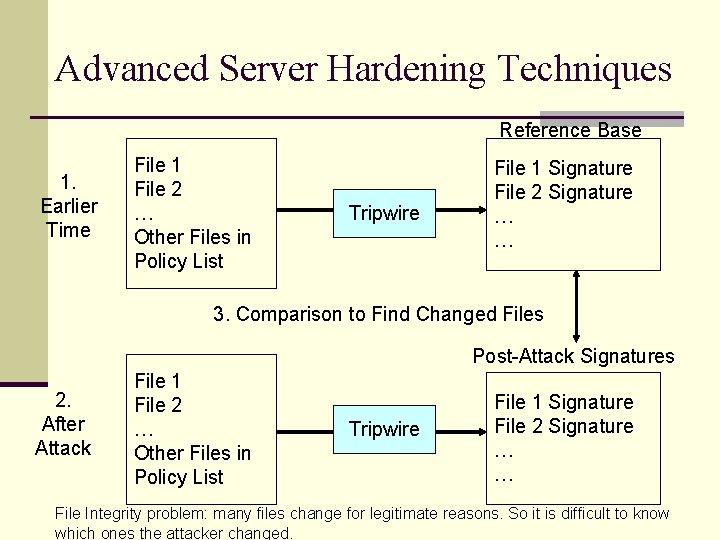
Advanced Server Hardening Techniques Reference Base 1. Earlier Time File 1 File 2 … Other Files in Policy List Tripwire File 1 Signature File 2 Signature … … 3. Comparison to Find Changed Files Post-Attack Signatures 2. After Attack File 1 File 2 … Other Files in Policy List Tripwire File 1 Signature File 2 Signature … … File Integrity problem: many files change for legitimate reasons. So it is difficult to know which ones the attacker changed.
The Elements of Cryptography
Cryptography? n Traditionally, cryptography refers to n The practice and the study of encryption n Transforming information in order to prevent unauthorized people to read it. n Today, cryptography goes beyond encryption/decryption to include n Techniques for making sure that encrypted messages are not modified en route n Techniques for secure identification/authentication of communication partners. 19
Your knowledge about Cryptography 1) Which of the following do cryptographic systems protect? a) Data stored on local storage media (like hard drives) from access by unauthorized users. b) Data being transmitted from point A to point B in a network c) Both a and b #$%^@ #$5 hh&*9(? >/@$#)> 20
Your knowledge about Cryptography 2) Which of the following security issues is addressed by cryptographic systems? a) Confidentiality; i. e. protection against eavesdropping b) Authentication; i. e. assurance parties involved in a communication are who they claim to be c) Message integrity; i. e. assurance that messages are not altered en route d) Availability; i. e. making sure that communication systems are not shut down by intruders. e) All of the above 21
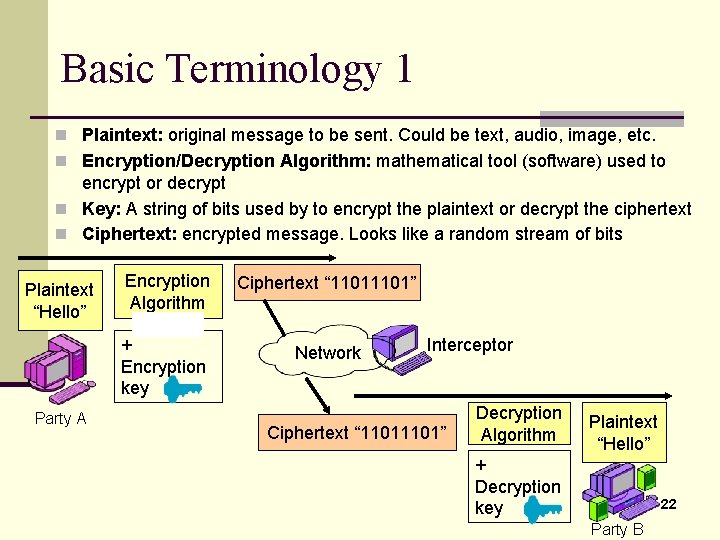
Basic Terminology 1 n Plaintext: original message to be sent. Could be text, audio, image, etc. n Encryption/Decryption Algorithm: mathematical tool (software) used to encrypt or decrypt n Key: A string of bits used by to encrypt the plaintext or decrypt the ciphertext n Ciphertext: encrypted message. Looks like a random stream of bits Plaintext “Hello” Party A Encryption Algorithm Hello + Encryption key Ciphertext “ 1101” Network Interceptor Ciphertext “ 1101” Decryption Algorithm Plaintext “Hello” + Decryption key 22 Party B
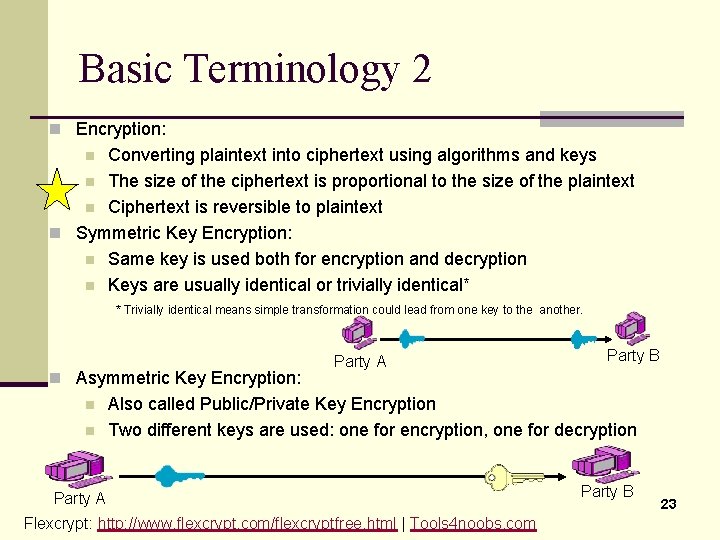
Basic Terminology 2 n Encryption: Converting plaintext into ciphertext using algorithms and keys n The size of the ciphertext is proportional to the size of the plaintext n Ciphertext is reversible to plaintext n Symmetric Key Encryption: n Same key is used both for encryption and decryption n Keys are usually identical or trivially identical* n * Trivially identical means simple transformation could lead from one key to the another. n Asymmetric Key Encryption: n n Party A Party B Also called Public/Private Key Encryption Two different keys are used: one for encryption, one for decryption Party A Flexcrypt: http: //www. flexcrypt. com/flexcryptfree. html | Tools 4 noobs. com Party B 23
Your knowledge about Cryptography 3) Based on how symmetric encryption systems work, which of the following is the worst thing to happen? a) An attacker gets a copy of the encryption and decryption algorithms b) An attacker gets the decryption key c) a and b are equally damaging 4) Which of the following presents more challenge for exchanging keys between partners? a) Asymmetric encryption b) Symmetric encryption c) A and b are equally challenging 24
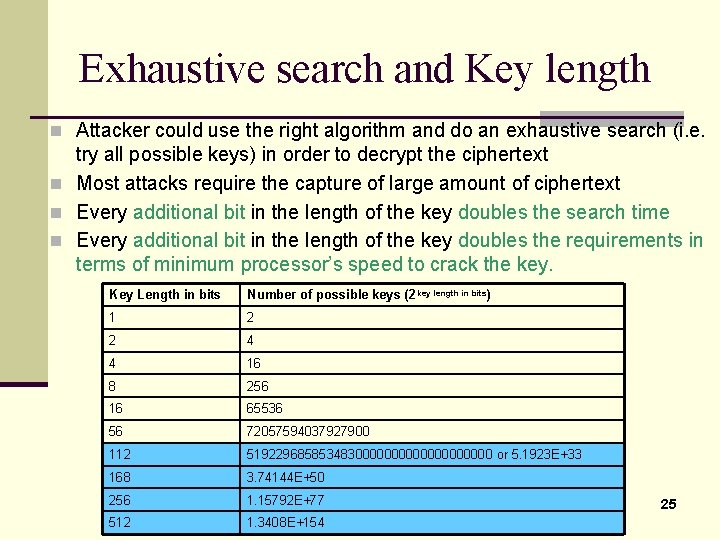
Exhaustive search and Key length n Attacker could use the right algorithm and do an exhaustive search (i. e. try all possible keys) in order to decrypt the ciphertext n Most attacks require the capture of large amount of ciphertext n Every additional bit in the length of the key doubles the search time n Every additional bit in the length of the key doubles the requirements in terms of minimum processor’s speed to crack the key. Key Length in bits Number of possible keys (2 key length in bits) 1 2 2 4 4 16 8 256 16 65536 56 72057594037927900 112 5192296858534830000000000 or 5. 1923 E+33 168 3. 74144 E+50 256 1. 15792 E+77 512 1. 3408 E+154 25
Your knowledge about Cryptography 4) If you increase the key length from 56 bits to 66 bits. How much more key combinations an attacker who captures enough ciphertext will have to try in order to decipher the captured ciphertext using the appropriate algorithm? ____________________ 5) Assuming that it takes 7 days to try all possible combinations of a 56 bit key, how much time it would take to try all possible combinations when the key length is increased to 58 bits? ________ 26
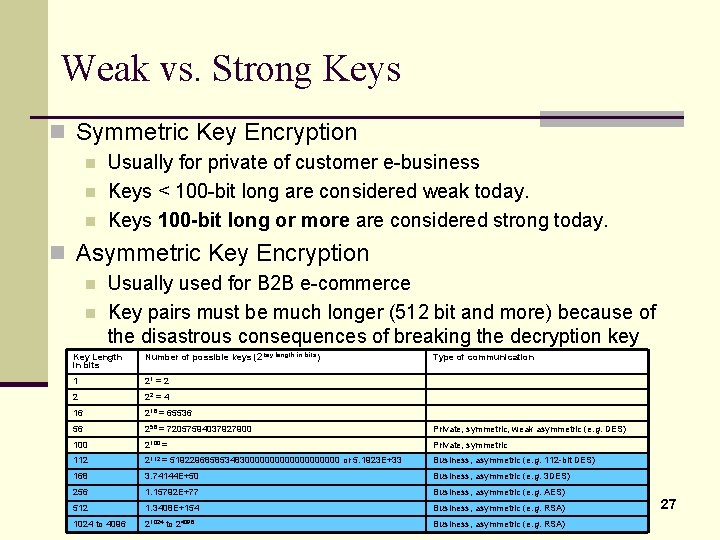
Weak vs. Strong Keys n Symmetric Key Encryption n Usually for private of customer e-business Keys < 100 -bit long are considered weak today. Keys 100 -bit long or more are considered strong today. n Asymmetric Key Encryption n n Usually used for B 2 B e-commerce Key pairs must be much longer (512 bit and more) because of the disastrous consequences of breaking the decryption key Key Length in bits Number of possible keys (2 key length in bits) 1 21 = 2 2 22 = 4 16 216 = 65536 56 256 = 72057594037927900 Private, symmetric, weak asymmetric (e. g. DES) 100 2100 = Private, symmetric 112 2112 = 5192296858534830000000000 or 5. 1923 E+33 Business, asymmetric (e. g. 112 -bit DES) 168 3. 74144 E+50 Business, asymmetric (e. g. 3 DES) 256 1. 15792 E+77 Business, asymmetric (e. g. AES) 512 1. 3408 E+154 Business, asymmetric (e. g. RSA) 1024 to 4096 21024 to 24096 Business, asymmetric (e. g. RSA) Type of communication 27
Your knowledge about Cryptography 6) Most attacks require the capture of large amount of ciphertext, which can take a certain amount of time. Beside using strong keys what else can be done to make it harder to crack the key? Answer: change the key very often 28
Symmetric Key Encryption
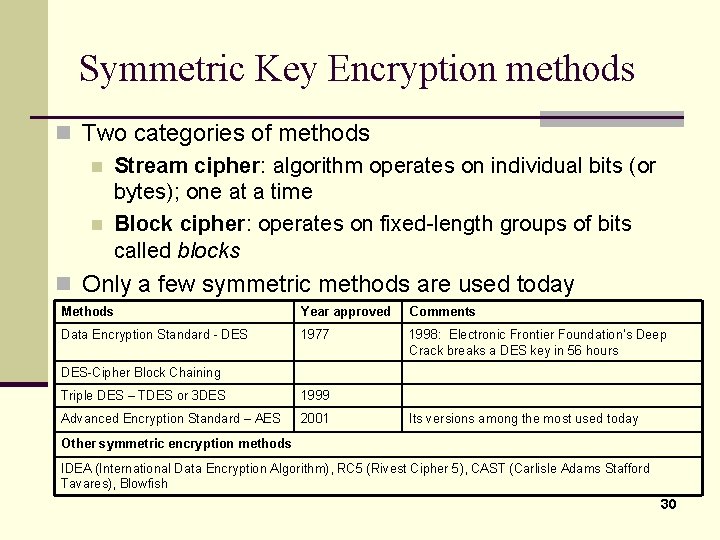
Symmetric Key Encryption methods n Two categories of methods n Stream cipher: algorithm operates on individual bits (or bytes); one at a time n Block cipher: operates on fixed-length groups of bits called blocks n Only a few symmetric methods are used today Methods Year approved Comments Data Encryption Standard - DES 1977 1998: Electronic Frontier Foundation’s Deep Crack breaks a DES key in 56 hours DES-Cipher Block Chaining Triple DES – TDES or 3 DES 1999 Advanced Encryption Standard – AES 2001 Its versions among the most used today Other symmetric encryption methods IDEA (International Data Encryption Algorithm), RC 5 (Rivest Cipher 5), CAST (Carlisle Adams Stafford Tavares), Blowfish 30
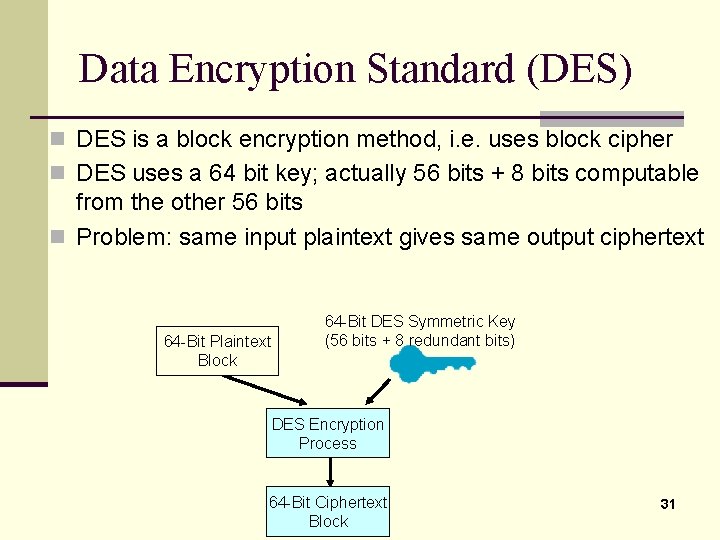
Data Encryption Standard (DES) n DES is a block encryption method, i. e. uses block cipher n DES uses a 64 bit key; actually 56 bits + 8 bits computable from the other 56 bits n Problem: same input plaintext gives same output ciphertext 64 -Bit Plaintext Block 64 -Bit DES Symmetric Key (56 bits + 8 redundant bits) DES Encryption Process 64 -Bit Ciphertext Block 31
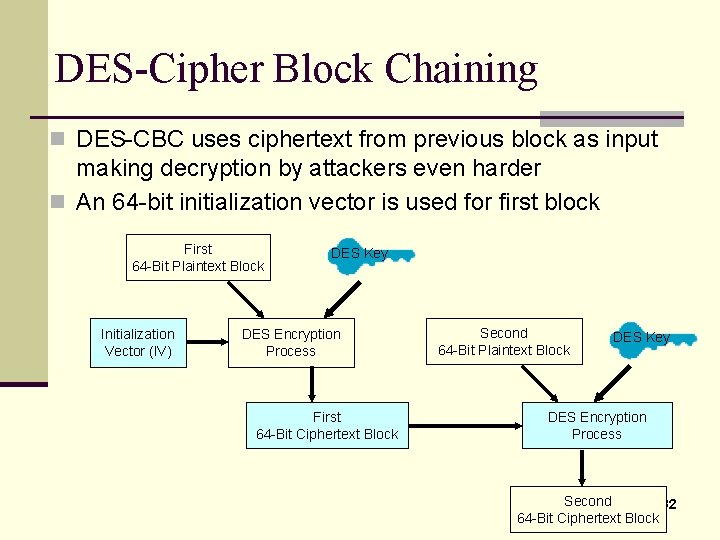
DES-Cipher Block Chaining n DES-CBC uses ciphertext from previous block as input making decryption by attackers even harder n An 64 -bit initialization vector is used for first block First 64 -Bit Plaintext Block Initialization Vector (IV) DES Key DES Encryption Process First 64 -Bit Ciphertext Block Second 64 -Bit Plaintext Block DES Key DES Encryption Process Second 32 64 -Bit Ciphertext Block
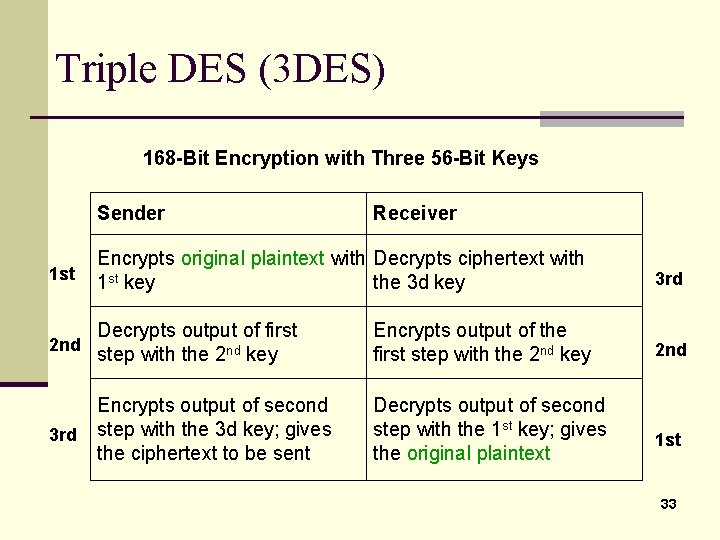
Triple DES (3 DES) 168 -Bit Encryption with Three 56 -Bit Keys Sender Receiver 1 st Encrypts original plaintext with the Decrypts ciphertext with 1 st key the 3 d key 3 rd 2 nd Decrypts output of first step with the 2 nd key Encrypts output of the first step with the 2 nd key 2 nd 3 rd Encrypts output of second step with the 3 d key; gives the ciphertext to be sent Decrypts output of second step with the 1 st key; gives the original plaintext 1 st 33
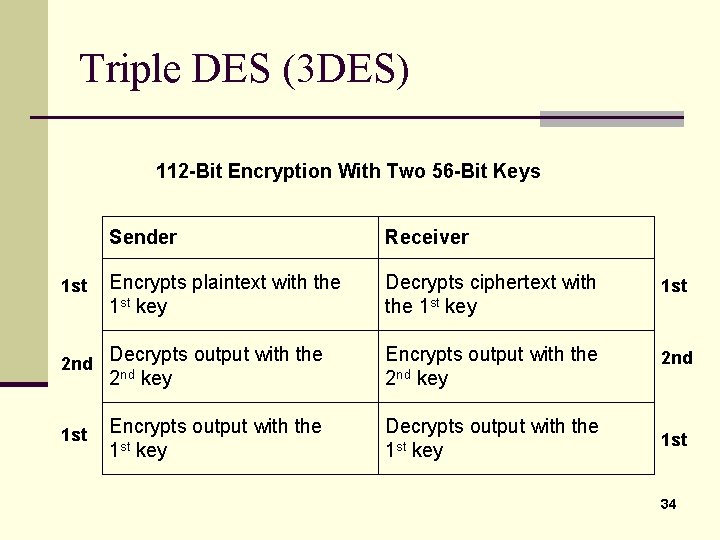
Triple DES (3 DES) 112 -Bit Encryption With Two 56 -Bit Keys Sender Receiver Encrypts plaintext with the 1 st key Decrypts ciphertext with the 1 st key 1 st 2 nd Decrypts output with the Encrypts output with the 2 nd key 2 nd Encrypts output with the 1 st key Decrypts output with the 1 st key 1 st 2 nd 1 st key 34
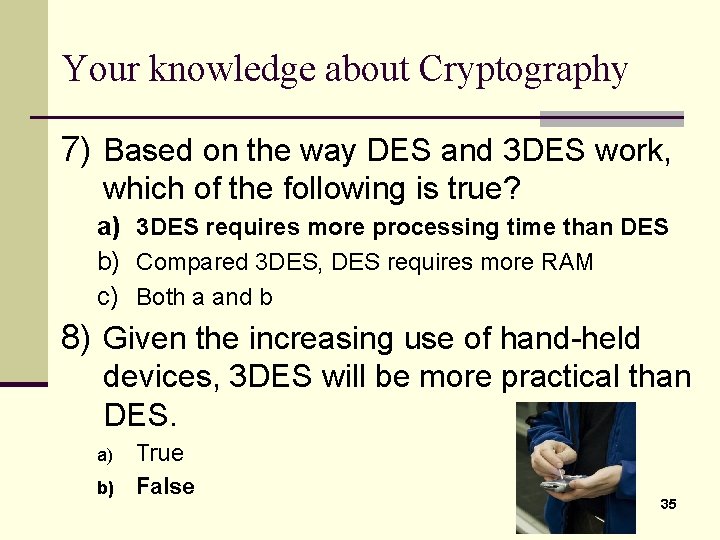
Your knowledge about Cryptography 7) Based on the way DES and 3 DES work, which of the following is true? a) 3 DES requires more processing time than DES b) Compared 3 DES, DES requires more RAM c) Both a and b 8) Given the increasing use of hand-held devices, 3 DES will be more practical than DES. a) b) True False 35
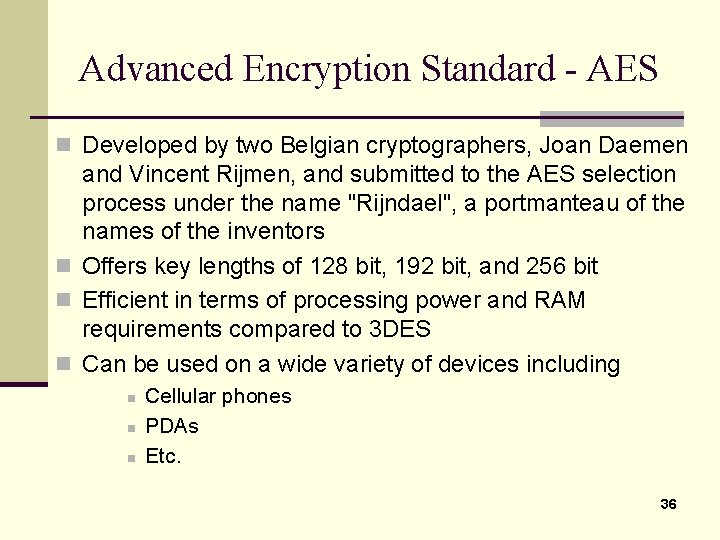
Advanced Encryption Standard - AES n Developed by two Belgian cryptographers, Joan Daemen and Vincent Rijmen, and submitted to the AES selection process under the name "Rijndael", a portmanteau of the names of the inventors n Offers key lengths of 128 bit, 192 bit, and 256 bit n Efficient in terms of processing power and RAM requirements compared to 3 DES n Can be used on a wide variety of devices including n n n Cellular phones PDAs Etc. 36
Asymmetric Key Encryption
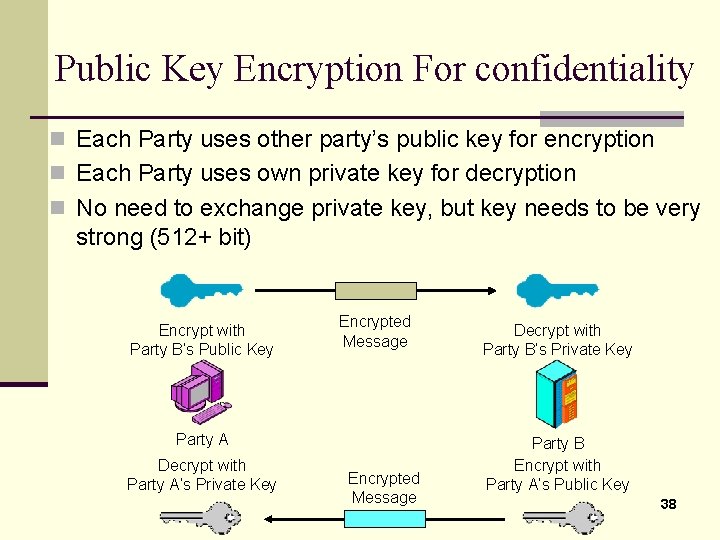
Public Key Encryption For confidentiality n Each Party uses other party’s public key for encryption n Each Party uses own private key for decryption n No need to exchange private key, but key needs to be very strong (512+ bit) Encrypt with Party B’s Public Key Encrypted Message Party A Decrypt with Party A’s Private Key Encrypted Message Decrypt with Party B’s Private Key Party B Encrypt with Party A’s Public Key 38
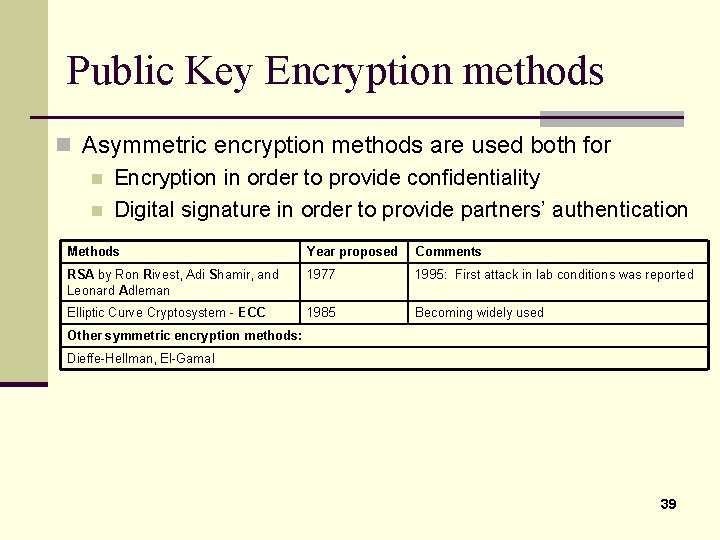
Public Key Encryption methods n Asymmetric encryption methods are used both for n Encryption in order to provide confidentiality n Digital signature in order to provide partners’ authentication Methods Year proposed Comments RSA by Ron Rivest, Adi Shamir, and Leonard Adleman 1977 1995: First attack in lab conditions was reported Elliptic Curve Cryptosystem - ECC 1985 Becoming widely used Other symmetric encryption methods: Dieffe-Hellman, El-Gamal 39
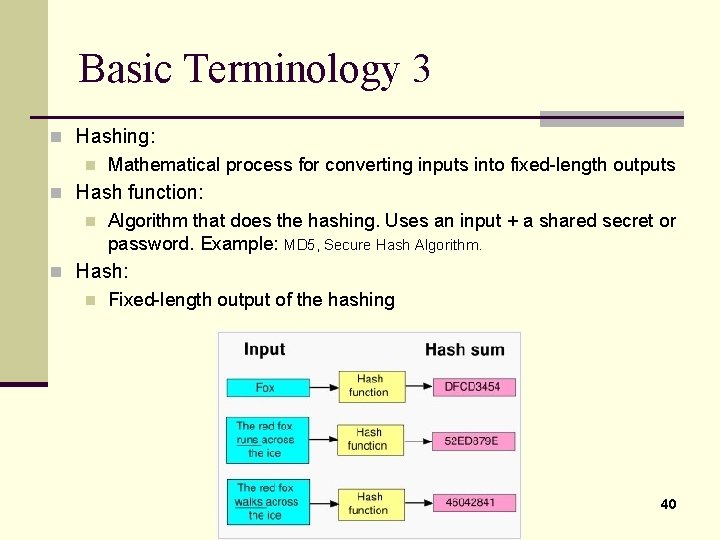
Basic Terminology 3 n Hashing: n Mathematical process for converting inputs into fixed-length outputs n Hash function: n Algorithm that does the hashing. Uses an input + a shared secret or password. Example: MD 5, Secure Hash Algorithm. n Hash: n Fixed-length output of the hashing 40
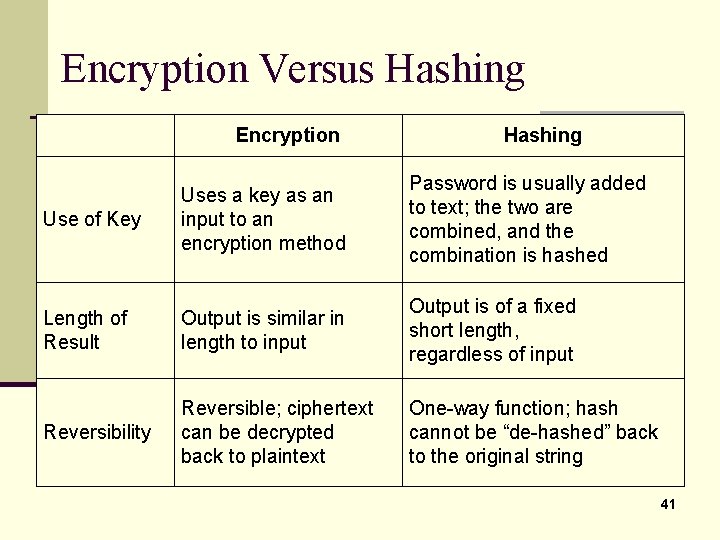
Encryption Versus Hashing Encryption Hashing Use of Key Uses a key as an input to an encryption method Password is usually added to text; the two are combined, and the combination is hashed Length of Result Output is similar in length to input Output is of a fixed short length, regardless of input Reversibility Reversible; ciphertext can be decrypted back to plaintext One-way function; hash cannot be “de-hashed” back to the original string 41
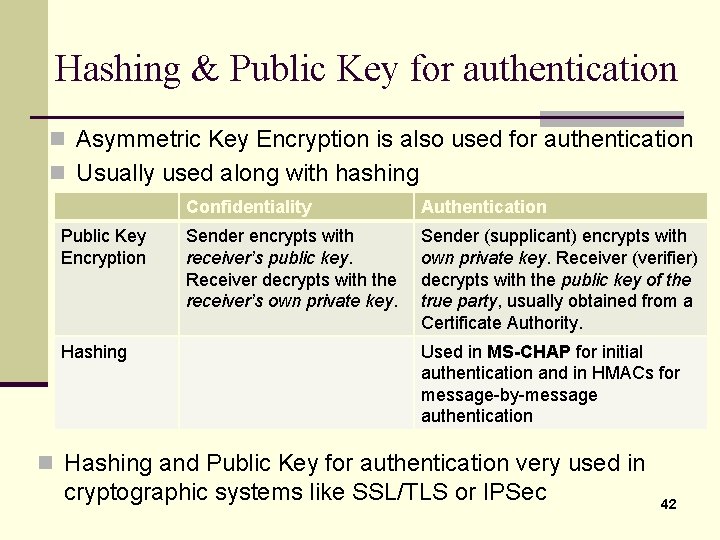
Hashing & Public Key for authentication n Asymmetric Key Encryption is also used for authentication n Usually used along with hashing Public Key Encryption Hashing Confidentiality Authentication Sender encrypts with receiver’s public key. Receiver decrypts with the receiver’s own private key. Sender (supplicant) encrypts with own private key. Receiver (verifier) decrypts with the public key of the true party, usually obtained from a Certificate Authority. Used in MS-CHAP for initial authentication and in HMACs for message-by-message authentication n Hashing and Public Key for authentication very used in cryptographic systems like SSL/TLS or IPSec 42
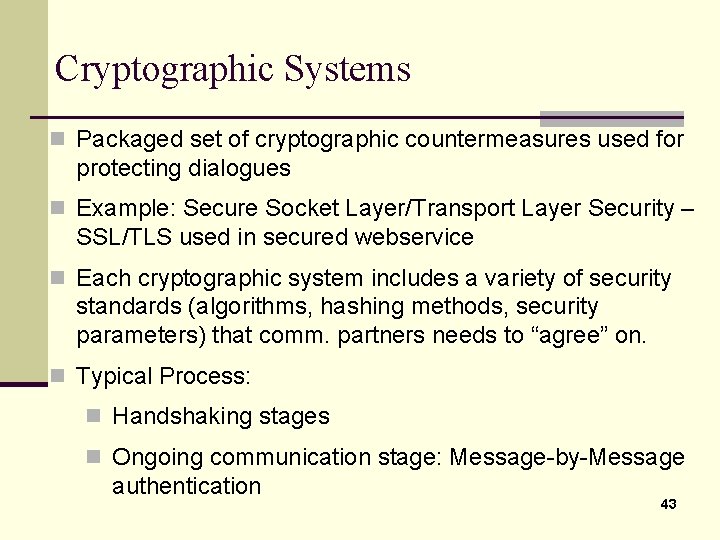
Cryptographic Systems n Packaged set of cryptographic countermeasures used for protecting dialogues n Example: Secure Socket Layer/Transport Layer Security – SSL/TLS used in secured webservice n Each cryptographic system includes a variety of security standards (algorithms, hashing methods, security parameters) that comm. partners needs to “agree” on. n Typical Process: n Handshaking stages n Ongoing communication stage: Message-by-Message authentication 43
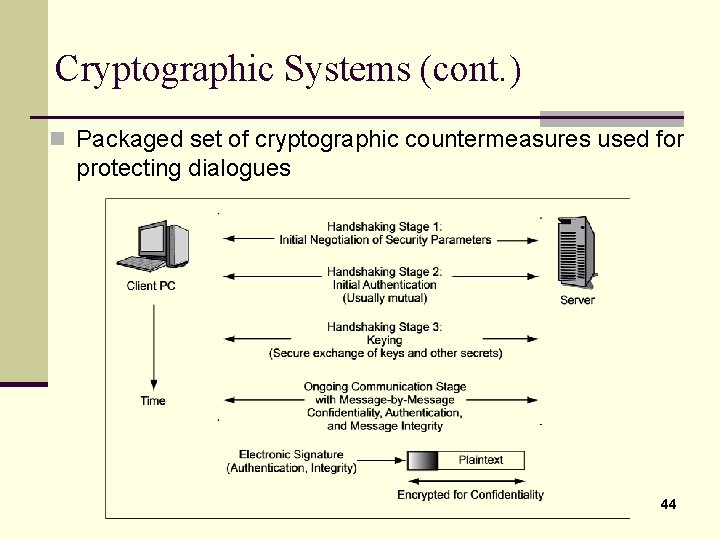
Cryptographic Systems (cont. ) n Packaged set of cryptographic countermeasures used for protecting dialogues 44
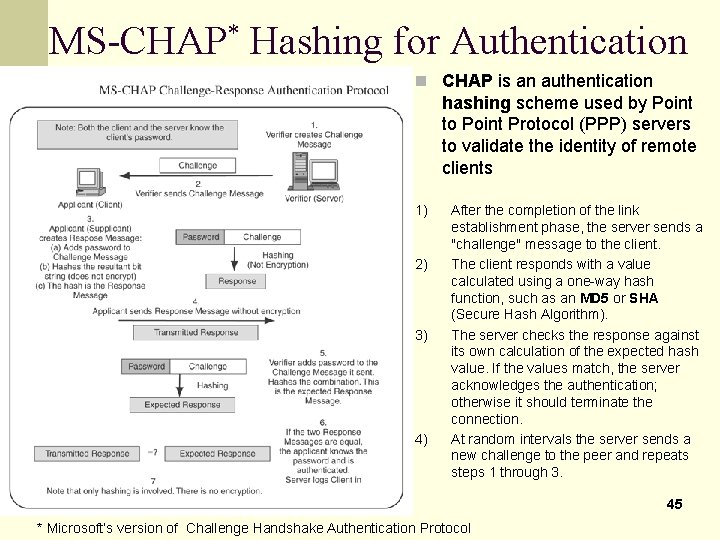
MS-CHAP* Hashing for Authentication n CHAP is an authentication hashing scheme used by Point to Point Protocol (PPP) servers to validate the identity of remote clients Shared secret 1) 2) 3) 4) After the completion of the link establishment phase, the server sends a "challenge" message to the client. The client responds with a value calculated using a one-way hash function, such as an MD 5 or SHA (Secure Hash Algorithm). The server checks the response against its own calculation of the expected hash value. If the values match, the server acknowledges the authentication; otherwise it should terminate the connection. At random intervals the server sends a new challenge to the peer and repeats steps 1 through 3. 45 * Microsoft’s version of Challenge Handshake Authentication Protocol
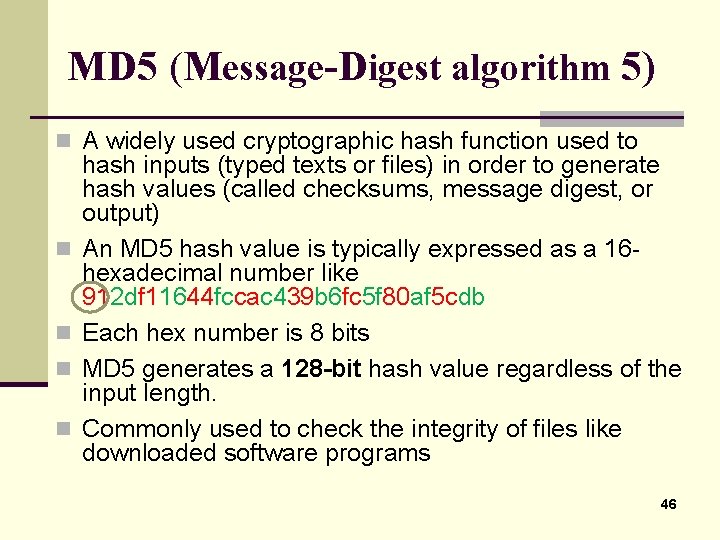
MD 5 (Message-Digest algorithm 5) n A widely used cryptographic hash function used to n n hash inputs (typed texts or files) in order to generate hash values (called checksums, message digest, or output) An MD 5 hash value is typically expressed as a 16 hexadecimal number like 912 df 11644 fccac 439 b 6 fc 5 f 80 af 5 cdb Each hex number is 8 bits MD 5 generates a 128 -bit hash value regardless of the input length. Commonly used to check the integrity of files like downloaded software programs 46
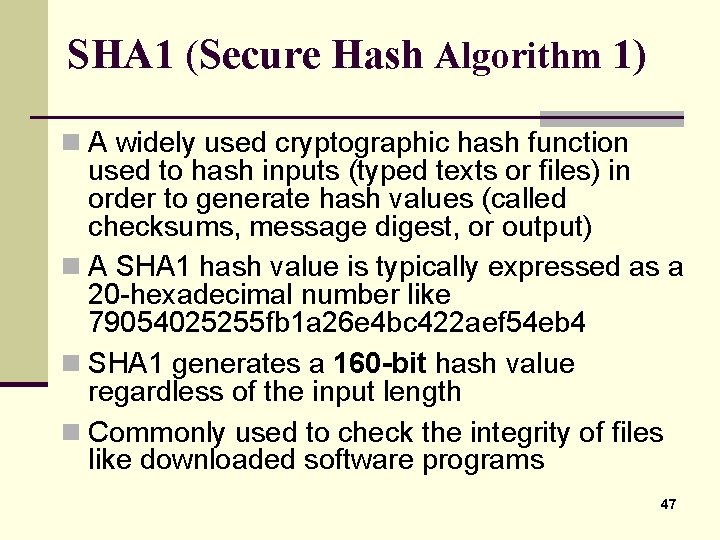
SHA 1 (Secure Hash Algorithm 1) n A widely used cryptographic hash function used to hash inputs (typed texts or files) in order to generate hash values (called checksums, message digest, or output) n A SHA 1 hash value is typically expressed as a 20 -hexadecimal number like 79054025255 fb 1 a 26 e 4 bc 422 aef 54 eb 4 n SHA 1 generates a 160 -bit hash value regardless of the input length n Commonly used to check the integrity of files like downloaded software programs 47
Application Security: General apps &Web service
General Applications Security Issues 49
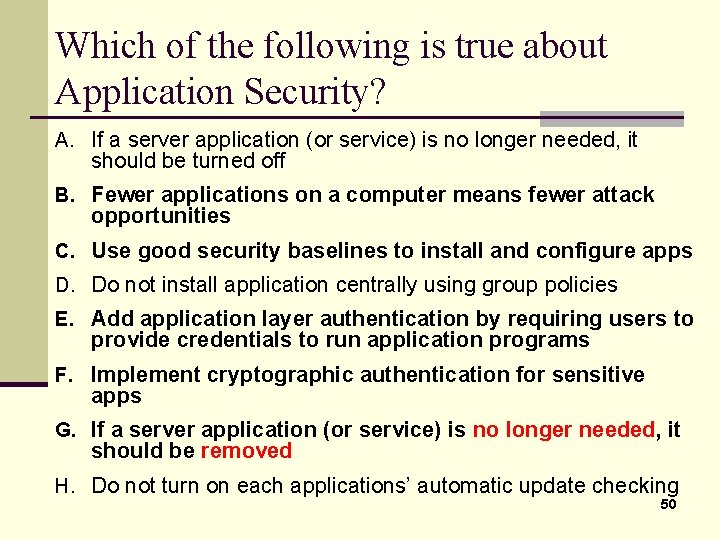
Which of the following is true about Application Security? A. If a server application (or service) is no longer needed, it should be turned off B. Fewer applications on a computer means fewer attack opportunities C. Use good security baselines to install and configure apps D. Do not install application centrally using group policies E. Add application layer authentication by requiring users to provide credentials to run application programs F. Implement cryptographic authentication for sensitive apps G. If a server application (or service) is no longer needed, it should be removed H. Do not turn on each applications’ automatic update checking 50
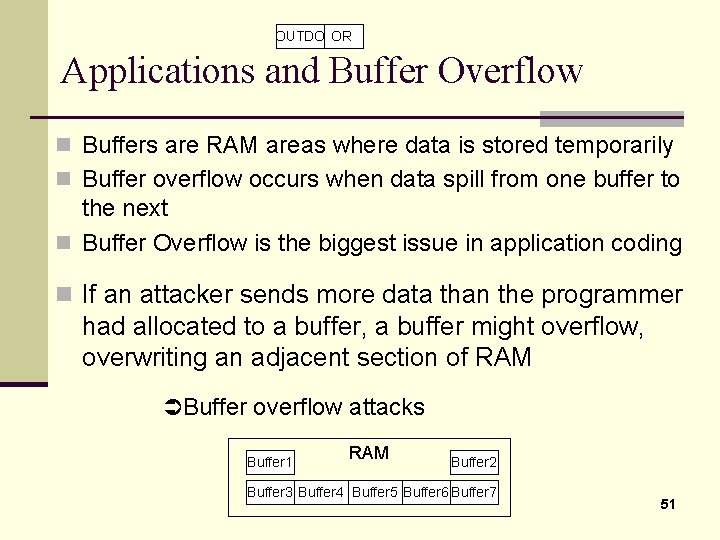
OUTDO OR Applications and Buffer Overflow n Buffers are RAM areas where data is stored temporarily n Buffer overflow occurs when data spill from one buffer to the next n Buffer Overflow is the biggest issue in application coding n If an attacker sends more data than the programmer had allocated to a buffer, a buffer might overflow, overwriting an adjacent section of RAM Buffer overflow attacks Buffer 1 RAM Buffer 2 Buffer 3 Buffer 4 Buffer 5 Buffer 6 Buffer 7 51
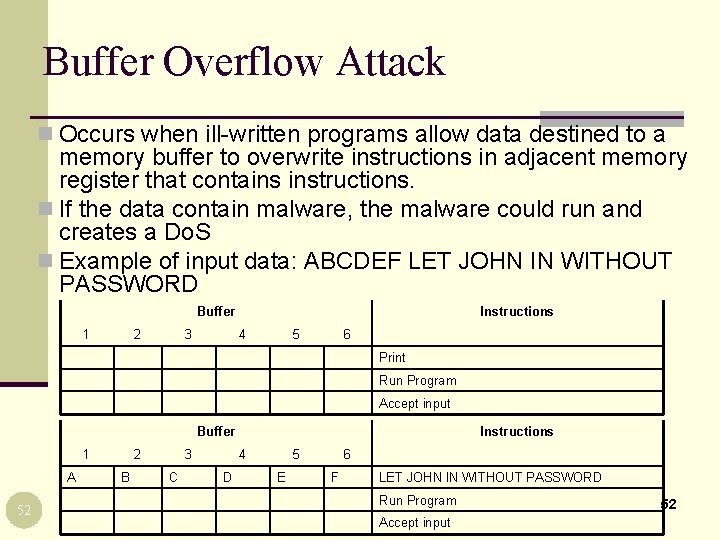
Buffer Overflow Attack n Occurs when ill-written programs allow data destined to a memory buffer to overwrite instructions in adjacent memory register that contains instructions. n If the data contain malware, the malware could run and creates a Do. S n Example of input data: ABCDEF LET JOHN IN WITHOUT PASSWORD Buffer 1 2 3 Instructions 4 5 6 Print Run Program Accept input Buffer 1 A 52 2 B 3 C Instructions 4 D 5 E 6 F LET JOHN IN WITHOUT PASSWORD Run Program Accept input 52
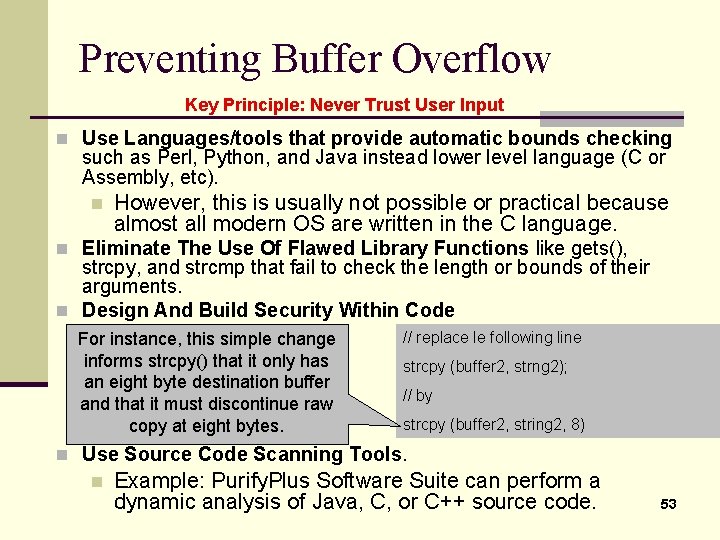
Preventing Buffer Overflow Key Principle: Never Trust User Input n Use Languages/tools that provide automatic bounds checking such as Perl, Python, and Java instead lower level language (C or Assembly, etc). n However, this is usually not possible or practical because almost all modern OS are written in the C language. n Eliminate The Use Of Flawed Library Functions like gets(), strcpy, and strcmp that fail to check the length or bounds of their arguments. n Design And Build Security Within Code For instance, this simple change informs strcpy() that it only has an eight byte destination buffer and that it must discontinue raw copy at eight bytes. // replace le following line strcpy (buffer 2, strng 2); // by strcpy (buffer 2, string 2, 8) n Use Source Code Scanning Tools. n Example: Purify. Plus Software Suite can perform a dynamic analysis of Java, C, or C++ source code. 53
Web service security 54
Webservice & E-Commerce apps n Web applications could be the target of many types of attacks like: n Directory browsing n Traversal attacks n Web defacement n Using HTTP proxy to manipulate interaction between client and server n IIS IPP Buffer Overflow n Browser attacks n Time configuration 55
Web sites’ directory browsing n n Web server with Directory Browsing disabled User cannot get access to list of files in the directory by knowing or guessing directory names 56
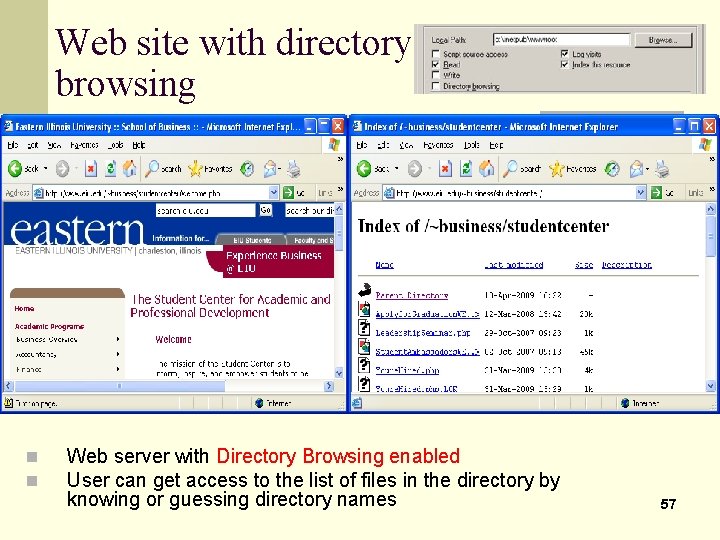
Web site with directory browsing n n Web server with Directory Browsing enabled User can get access to the list of files in the directory by knowing or guessing directory names 57
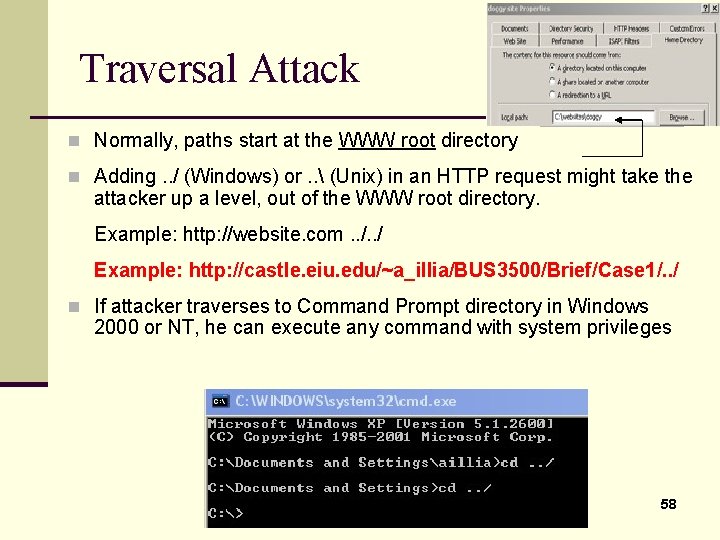
Traversal Attack n Normally, paths start at the WWW root directory n Adding. . / (Windows) or. . (Unix) in an HTTP request might take the attacker up a level, out of the WWW root directory. Example: http: //website. com. . / Example: http: //castle. eiu. edu/~a_illia/BUS 3500/Brief/Case 1/. . / n If attacker traverses to Command Prompt directory in Windows 2000 or NT, he can execute any command with system privileges 58
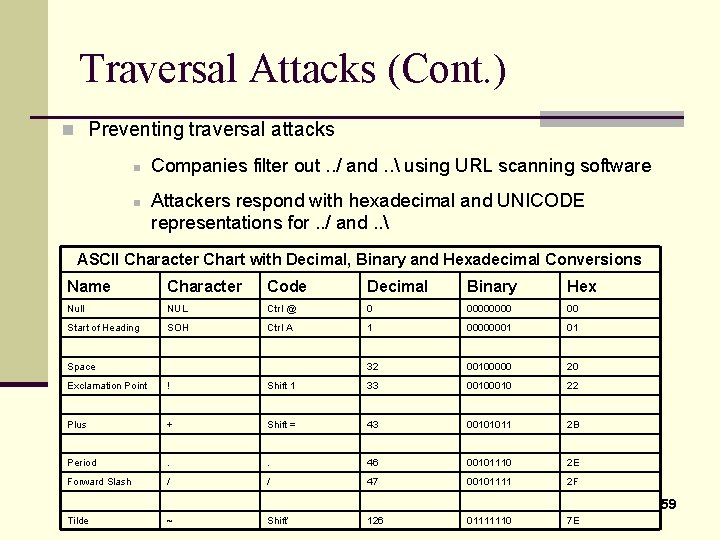
Traversal Attacks (Cont. ) n Preventing traversal attacks n n Companies filter out. . / and. . using URL scanning software Attackers respond with hexadecimal and UNICODE representations for. . / and. . ASCII Character Chart with Decimal, Binary and Hexadecimal Conversions Name Character Code Decimal Binary Hex Null NUL Ctrl @ 0 0000 00 Start of Heading SOH Ctrl A 1 00000001 01 32 00100000 20 Space Exclamation Point ! Shift 1 33 0010 22 Plus + Shift = 43 00101011 2 B Period . . 46 00101110 2 E Forward Slash / / 47 00101111 2 F Tilde ~ Shift’ 126 01111110 7 E 59
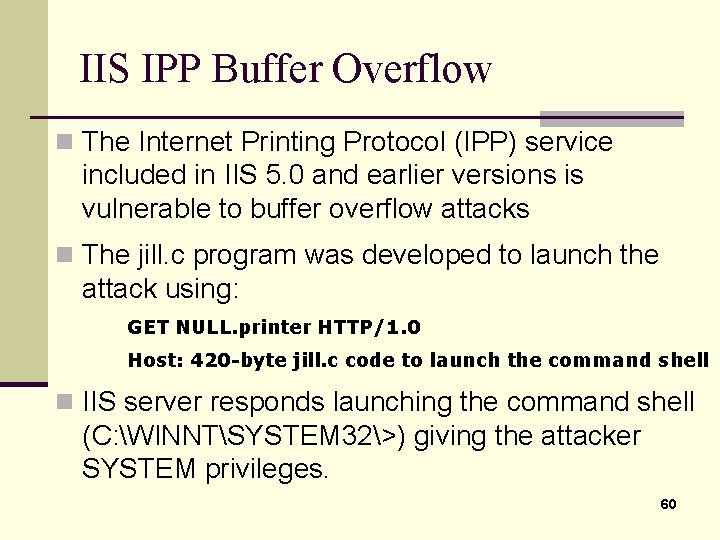
IIS IPP Buffer Overflow n The Internet Printing Protocol (IPP) service included in IIS 5. 0 and earlier versions is vulnerable to buffer overflow attacks n The jill. c program was developed to launch the attack using: GET NULL. printer HTTP/1. 0 Host: 420 -byte jill. c code to launch the command shell n IIS server responds launching the command shell (C: WINNTSYSTEM 32>) giving the attacker SYSTEM privileges. 60
IIS IPP Buffer Overflow (cont. ) n Link to jill. c code n Code compilable using gcc jill. c –o jill on Linux n Precompiled version (jill-win 32. c) and executable (jill-win 32. exe) available at ftp: //ftp. technotronic. com/ n newfiles/jill-win 32. exe. This executable file is ready to run on a Windows machine. 61
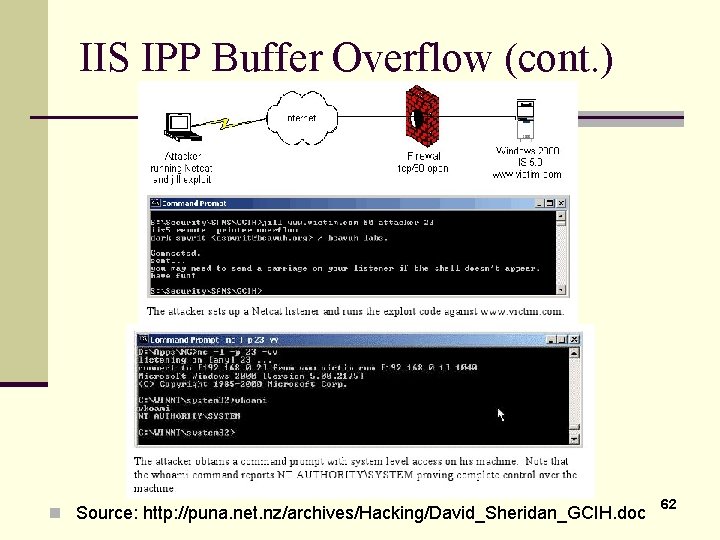
IIS IPP Buffer Overflow (cont. ) n Source: http: //puna. net. nz/archives/Hacking/David_Sheridan_GCIH. doc 62
Login Screen Bypass Attack n Website user gets a login screen n Instead of logging in, user enters a URL to bypass the login screen and gain access without authorization. 63
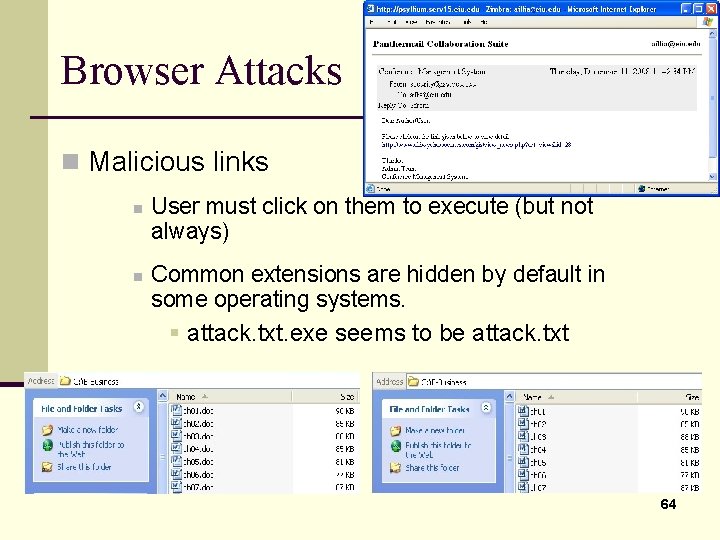
Browser Attacks n Malicious links n n User must click on them to execute (but not always) Common extensions are hidden by default in some operating systems. § attack. txt. exe seems to be attack. txt 64
- Slides: 64