Reversible visible watermarking and lossless recovery of original
Reversible visible watermarking and lossless recovery of original images Source: IEEE transactions on circuits and systems for video technology, vol. 16, no. 11, November 2006 Authors: Yongjian Hu and Byeungwoo Jeon Speaker: Chia-Chun Wu (吳佳駿) Date: 2007/05/02 1
Outline n n n Introduction Reversible visible watermarking Proposed method n n n Embedding Lossless Recovery Experimental results Conclusions Our proposed method 2

Introduction n (1/2) Generally, a visible watermark is translucently laid on the host image and designed to be irreversible so as to resist unintentional modifications or malicious attacks. 3

Introduction n n (2/2) However, in some potential applications, a visible watermark is first used as a tag or ownership identifier and then needs to be removable. Example: n 1. patient’s images n 2. remote sensing n 3. military imagery 4
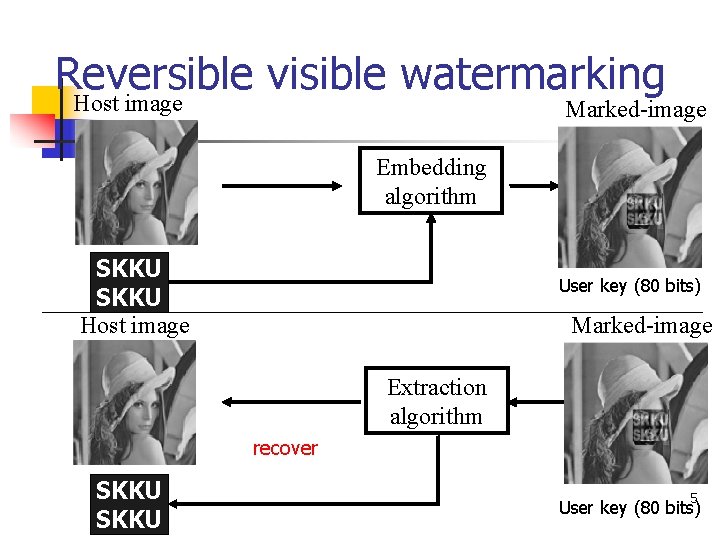
Reversible visible watermarking Host image Marked-image Embedding algorithm SKKU Host image User key (80 bits) Marked-image Extraction algorithm recover SKKU 5 User key (80 bits)

The Proposed method − Embedding (1/5) H=Sc ∪ Dc W =Binary watermark S =Pixel sequence composed of one-bit pixels on Ik Fig. 1. Framework of visible watermark embedding and data hiding. User key (80 bits) = Watermark size (8 bits+8 bits) + Origin position of R (16 bits+16 bits) + Dc size (16 bits) + key bit plane level (3 bits) … 6
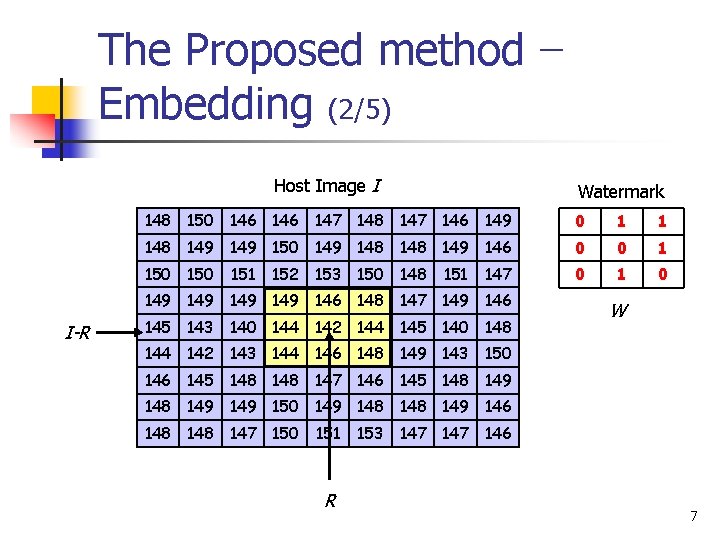
The Proposed method − Embedding (2/5) Host Image I Watermark 148 150 146 147 148 147 146 149 0 1 1 148 149 150 149 148 149 146 0 0 1 150 0 151 152 153 150 148 151 147 149 149 146 148 147 149 146 I-R 145 143 140 144 142 144 145 140 148 W 144 142 143 144 146 148 149 143 150 146 145 148 147 146 145 148 149 149 150 149 148 149 146 148 147 150 151 R 153 147 146 7
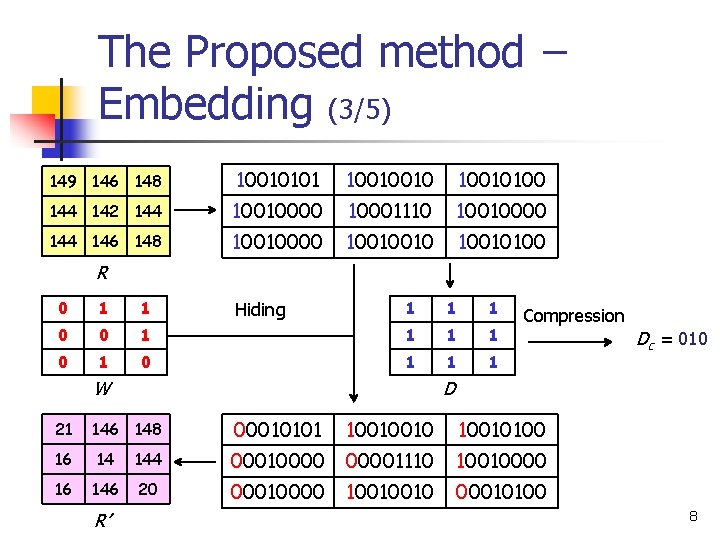
The Proposed method − Embedding (3/5) 149 146 148 10010101 10010010100 144 142 144 10010000 10001110 10010000 144 146 148 10010000 10010010100 R 0 1 1 1 0 0 1 1 1 Hiding W 21 Compression D 146 148 00010101 10010010100 16 14 144 000100001110 10010000 16 146 20 00010000 10010010 00010100 R’ Dc = 010 8
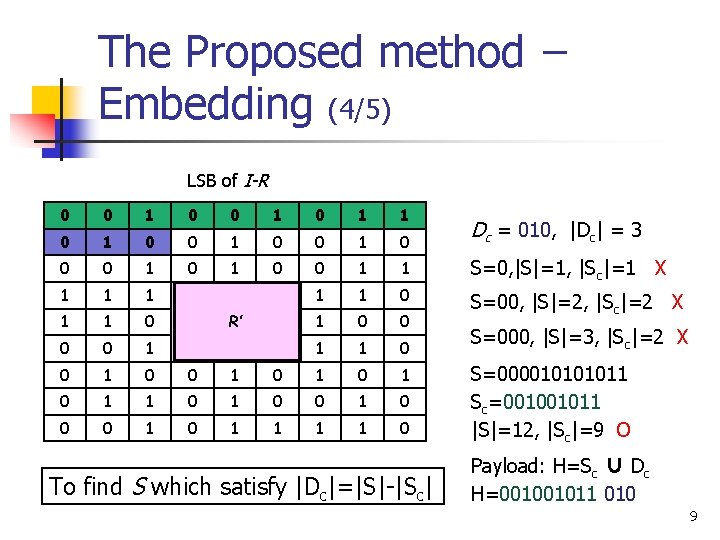
The Proposed method − Embedding (4/5) LSB of I-R 0 0 1 1 0 1 1 0 0 1 0 Dc = 010, |Dc| = 3 0 0 1 1 1 1 0 S=0, |S|=1, |Sc|=1 X 1 1 0 0 0 0 1 1 1 0 0 1 0 1 0 1 0 1 1 0 R’ To find S which satisfy |Dc|=|S|-|Sc| S=00, |S|=2, |Sc|=2 X S=000, |S|=3, |Sc|=2 X S=00001011 Sc=001001011 |S|=12, |Sc|=9 O Payload: H=Sc ∪ Dc H=001001011 010 9
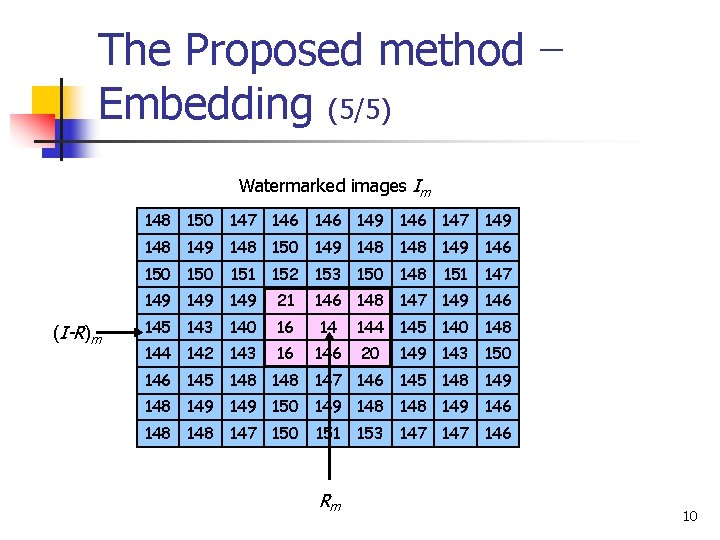
The Proposed method − Embedding (5/5) Watermarked images Im 148 150 147 146 149 146 147 149 148 150 149 148 149 146 150 (I-R)m 151 152 153 150 148 149 149 21 145 143 140 16 14 142 143 16 146 151 147 146 148 147 149 146 144 145 140 148 20 149 143 150 146 145 148 147 146 145 148 149 149 150 149 148 149 146 148 147 150 151 Rm 153 147 146 10
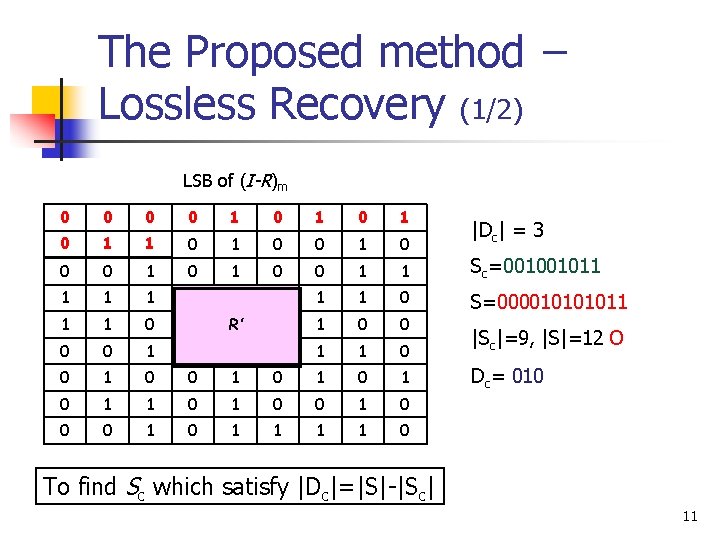
The Proposed method − Lossless Recovery (1/2) LSB of (I-R)m 0 0 0 1 1 0 1 1 0 0 0 1 0 0 1 1 Sc=001001011 1 1 0 0 S=00001011 0 0 1 1 1 0 0 1 0 1 0 1 0 1 1 0 R’ |Dc| = 3 |Sc|=9, |S|=12 O Dc= 010 To find Sc which satisfy |Dc|=|S|-|Sc| 11
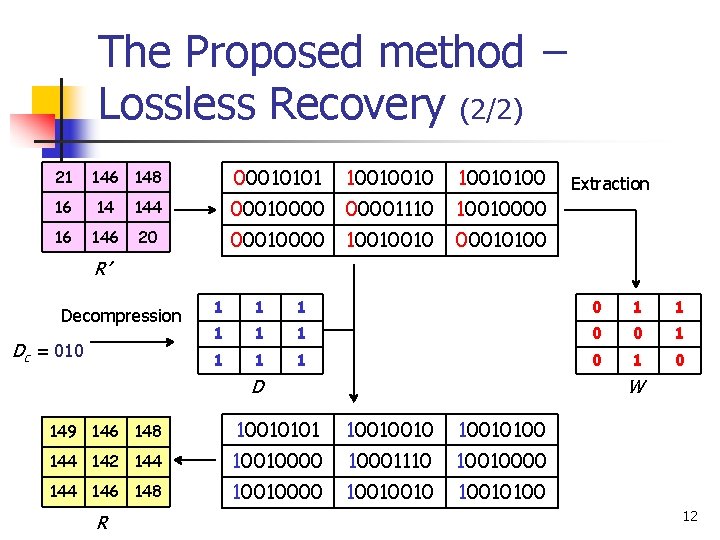
The Proposed method − Lossless Recovery (2/2) 21 146 148 00010101 10010010100 16 14 144 000100001110 10010000 16 146 20 00010000 10010010 00010100 Extraction R’ Decompression Dc = 010 1 1 1 1 1 0 0 1 1 0 1 0 D W 149 146 148 10010101 10010010100 144 142 144 10010000 10001110 10010000 144 146 148 10010000 10010010100 R 12
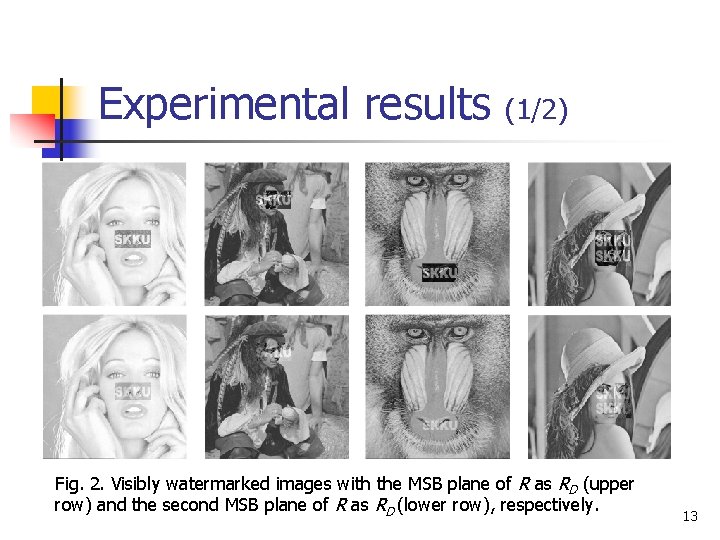
Experimental results (1/2) Fig. 2. Visibly watermarked images with the MSB plane of R as RD (upper row) and the second MSB plane of R as RD (lower row), respectively. 13
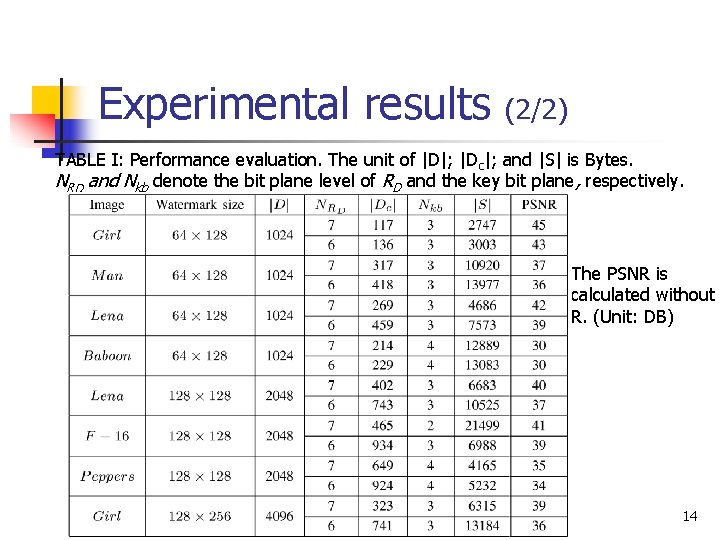
Experimental results (2/2) TABLE I: Performance evaluation. The unit of |D|; |Dc|; and |S| is Bytes. NRD and Nkb denote the bit plane level of RD and the key bit plane, respectively. The PSNR is calculated without R. (Unit: DB) 14
Conclusions n n Design for binary watermarks The first work that implements a reversible visible watermarking system. 15
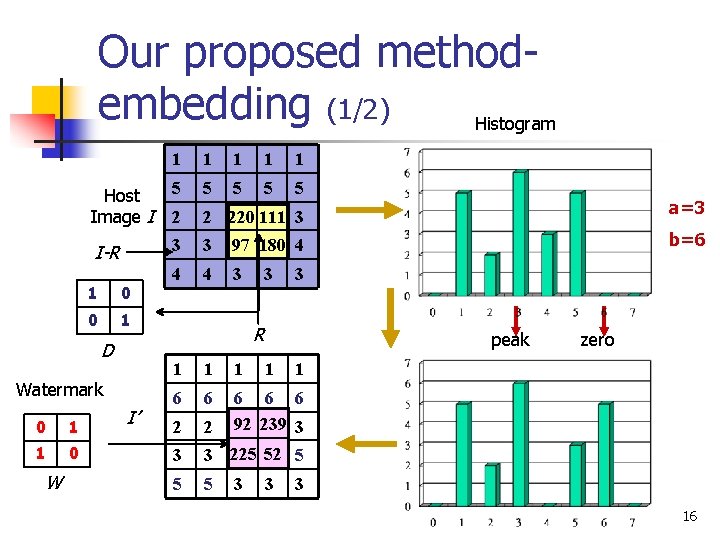
Our proposed methodembedding (1/2) Histogram 1 1 1 Host Image I 5 5 5 2 2 220 111 3 I-R 3 3 97 180 4 4 4 3 1 0 0 1 D Watermark 0 1 1 0 W I’ 3 1 6 6 1 peak 1 3 5 5 3 3 zero 1 6 6 6 92 111 239 3 2 220 52 5 97 180 3 225 2 b=6 3 R 1 a=3 3 16
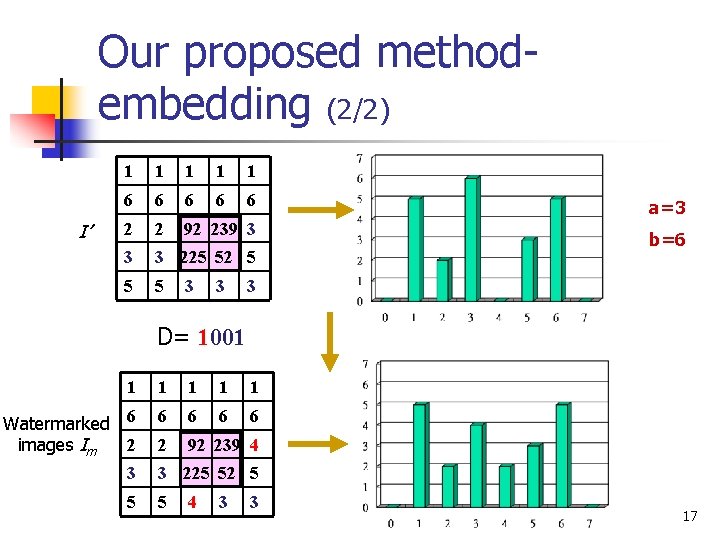
Our proposed methodembedding (2/2) I’ 1 1 1 6 6 6 2 2 92 239 3 3 3 225 52 5 5 5 3 3 a=3 b=6 3 D= 1001 1 1 Watermarked 6 2 images Im 6 6 2 92 239 4 3 3 225 52 5 5 5 4 3 3 17
- Slides: 17