Reversible Data Hiding Scheme Using Two Steganographic Images
Reversible Data Hiding Scheme Using Two Steganographic Images Chair Professor Chin-Chen Chang Feng Chia University
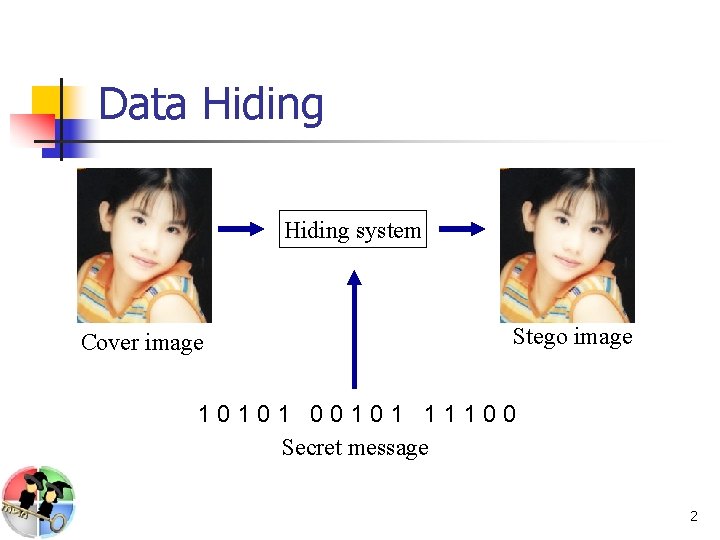
Data Hiding system Cover image Stego image 10101 00101 11100 Secret message 2
Cover Carriers n n Image Video Sound Text 3
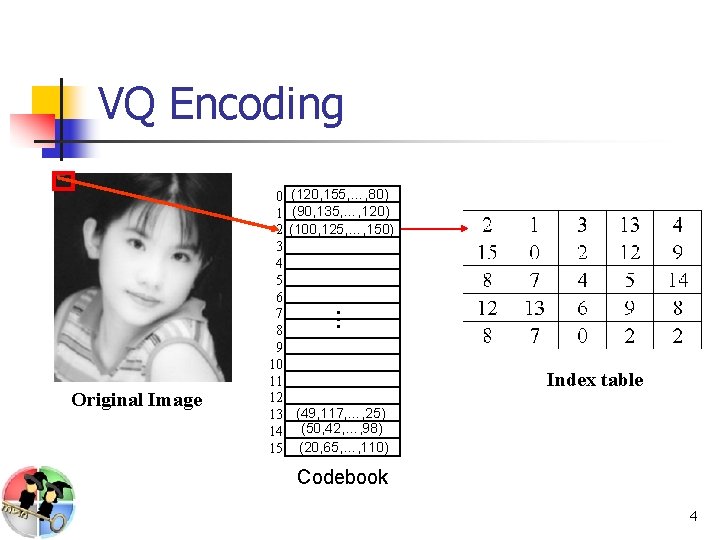
VQ Encoding (120, 155, …, 80) (90, 135, …, 120) (100, 125, …, 150) … Original Image 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 Index table (49, 117, …, 25) (50, 42, …, 98) (20, 65, …, 110) Codebook 4
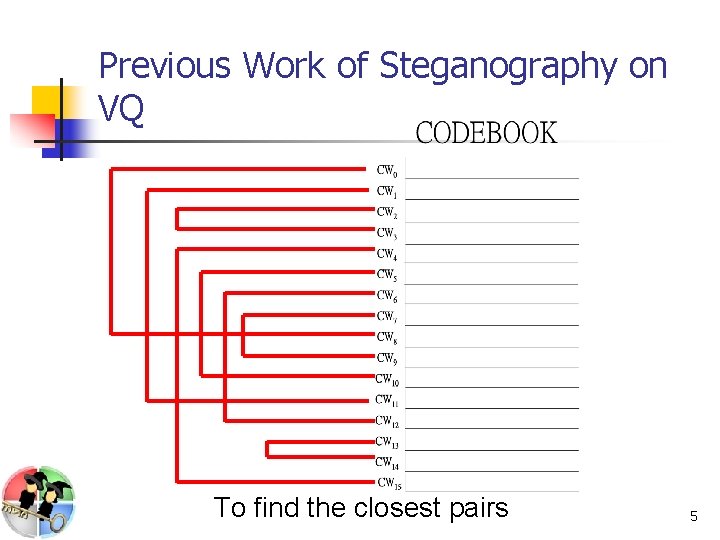
Previous Work of Steganography on VQ To find the closest pairs 5
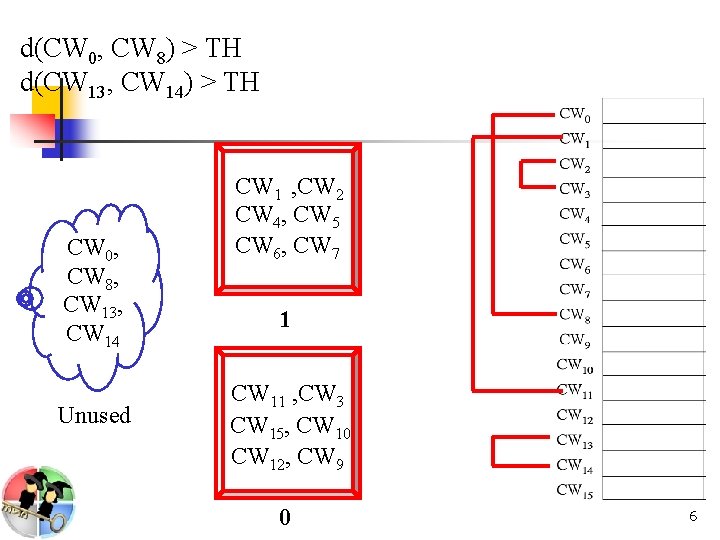
d(CW 0, CW 8) > TH d(CW 13, CW 14) > TH CW 0, CW 8, CW 13, CW 14 Unused CW 1 , CW 2 CW 4, CW 5 CW 6, CW 7 1 CW 11 , CW 3 CW 15, CW 10 CW 12, CW 9 0 6
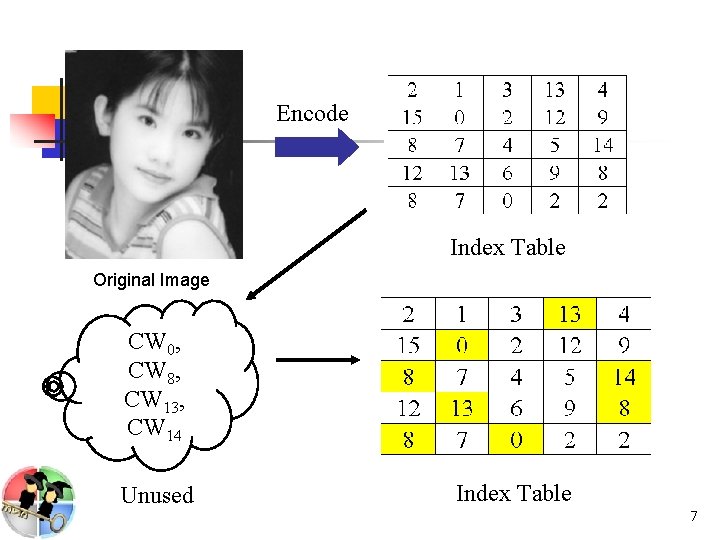
Encode Index Table Original Image CW 0, CW 8, CW 13, CW 14 Unused Index Table 7
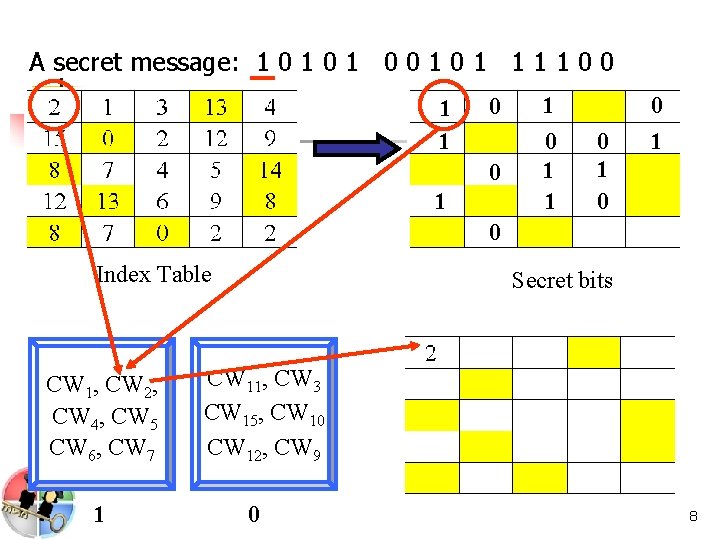
A secret message: 1 0 1 0 0 1 1 1 1 0 0 1 1 0 1 0 Index Table CW 1, CW 2, CW 4, CW 5 CW 6, CW 7 1 Secret bits CW 11, CW 3 CW 15, CW 10 CW 12, CW 9 0 8
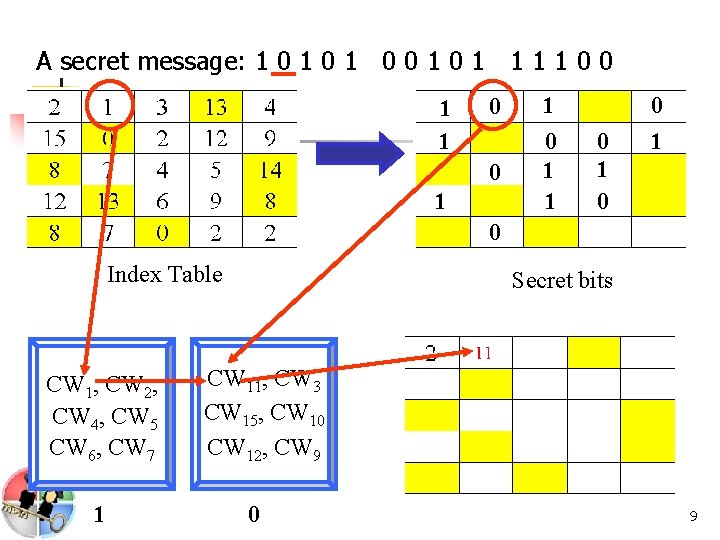
A secret message: 1 0 1 0 0 1 1 1 1 0 0 1 1 0 1 0 Index Table CW 1, CW 2, CW 4, CW 5 CW 6, CW 7 1 Secret bits CW 11, CW 3 CW 15, CW 10 CW 12, CW 9 0 9
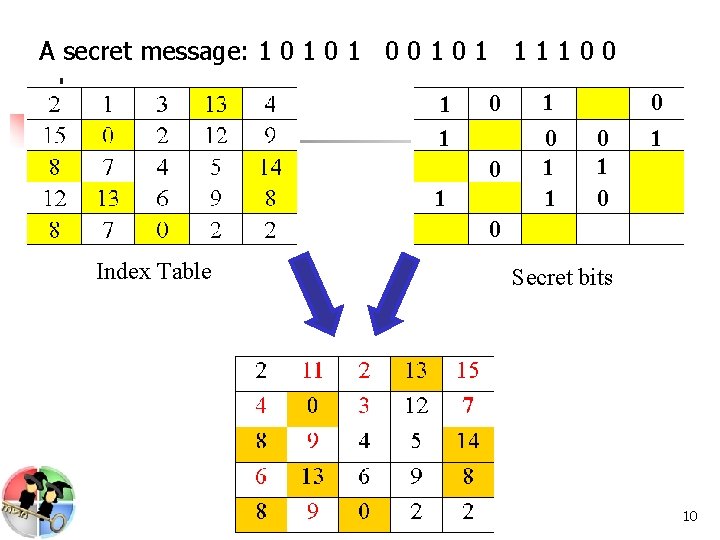
A secret message: 1 0 1 0 0 1 1 1 1 0 0 1 1 0 1 0 Index Table Secret bits 10
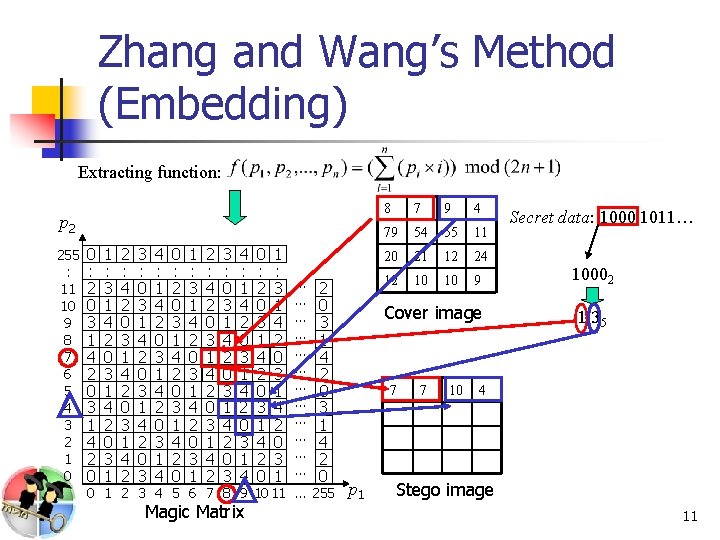
Zhang and Wang’s Method (Embedding) Extracting function: p 2 255 : 11 10 9 8 7 6 5 4 3 2 1 0 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 2 : 4 2 0 3 1 4 2 3 : 0 3 1 4 2 0 3 4 : 1 4 2 0 3 1 4 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 … … … 2 0 3 1 4 2 0 0 1 2 3 4 5 6 7 8 9 10 11 … 255 Magic Matrix 8 7 9 4 79 54 55 11 20 21 12 24 12 10 10 9 Cover image 7 p 1 7 10 Secret data: 1000 1011… 10002 1 35 4 Stego image 11
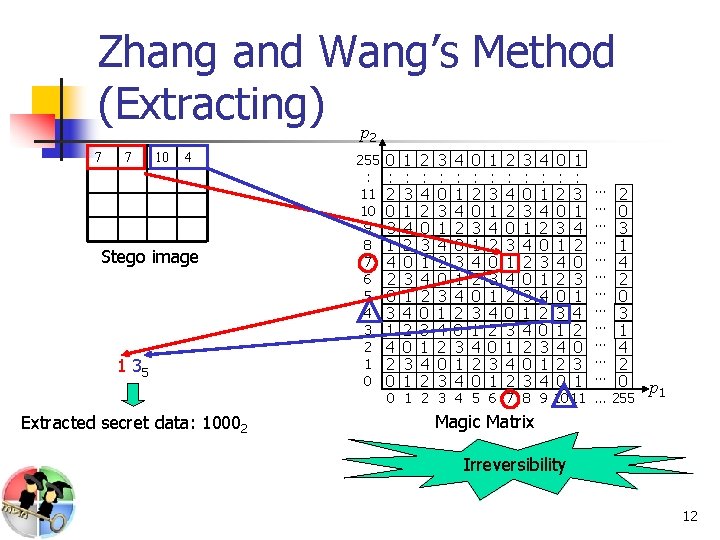
Zhang and Wang’s Method (Extracting) p 2 7 7 10 4 Stego image 1 35 255 : 11 10 9 8 7 6 5 4 3 2 1 0 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 2 : 4 2 0 3 1 4 2 3 : 0 3 1 4 2 0 3 4 : 1 4 2 0 3 1 4 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 … … … 2 0 3 1 4 2 0 0 1 2 3 4 5 6 7 8 9 10 11 … 255 Extracted secret data: 10002 p 1 Magic Matrix Irreversibility 12
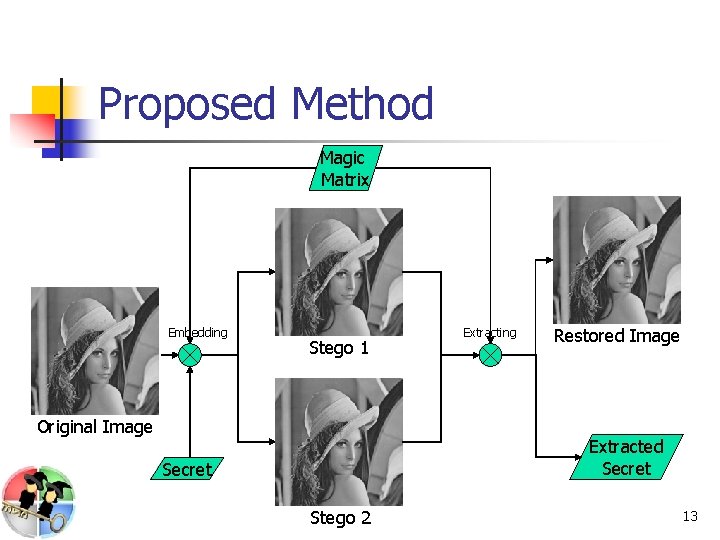
Proposed Method Magic Matrix Embedding Stego 1 Original Image Extracting Restored Image Extracted Secret Stego 2 13
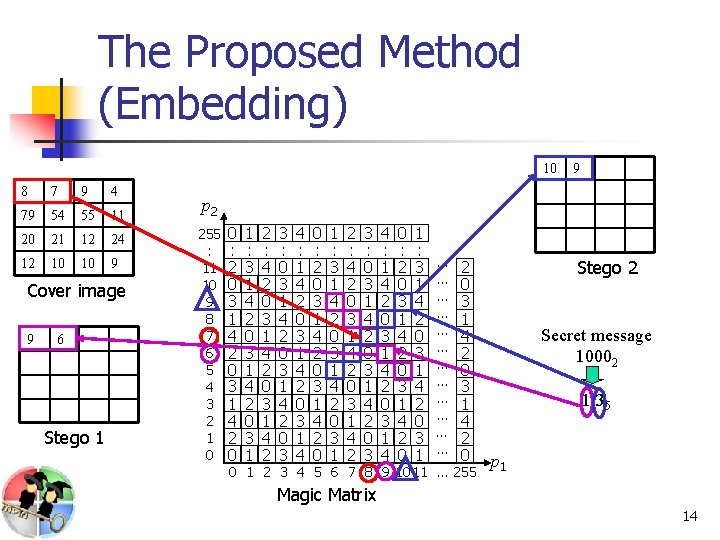
The Proposed Method (Embedding) 10 8 7 9 4 79 54 55 11 20 21 12 24 12 10 10 9 Cover image 9 6 Stego 1 9 p 2 255 : 11 10 9 8 7 6 5 4 3 2 1 0 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 2 : 4 2 0 3 1 4 2 3 : 0 3 1 4 2 0 3 4 : 1 4 2 0 3 1 4 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 … … … 2 0 3 1 4 2 0 0 1 2 3 4 5 6 7 8 9 10 11 … 255 Stego 2 Secret message 10002 1 35 p 1 Magic Matrix 14
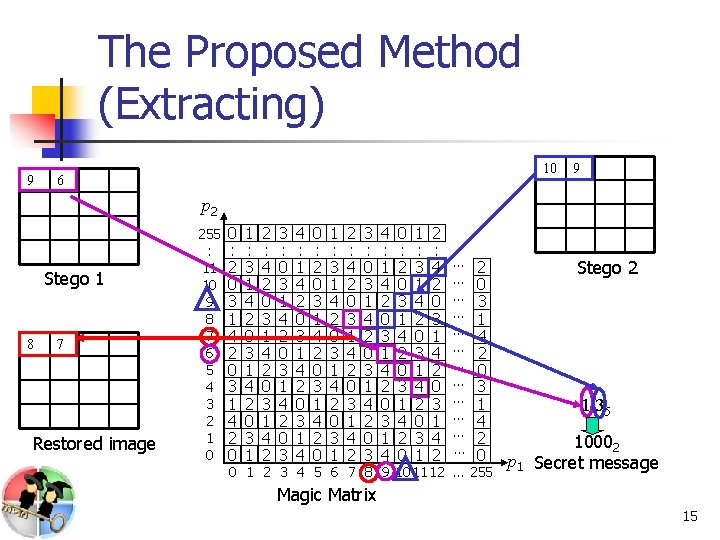
The Proposed Method (Extracting) 9 10 6 9 p 2 Stego 1 8 7 Restored image 255 : 11 10 9 8 7 6 5 4 3 2 1 0 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 2 : 4 2 0 3 1 4 2 3 : 0 3 1 4 2 0 3 4 : 1 4 2 0 3 1 4 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 2 : 4 2 0 3 1 4 2 … … … 2 0 3 1 4 2 0 0 1 2 3 4 5 6 7 8 9 10 11 12 … 255 Stego 2 1 35 10002 p 1 Secret message Magic Matrix 15
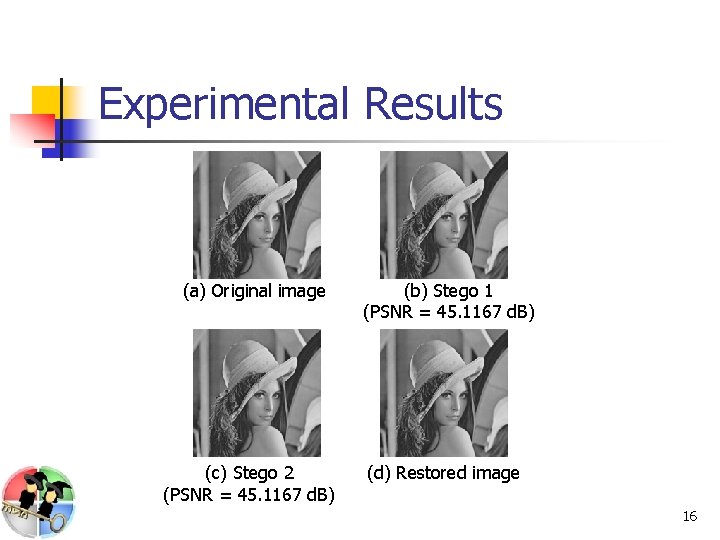
Experimental Results (a) Original image (b) Stego 1 (PSNR = 45. 1167 d. B) (c) Stego 2 (PSNR = 45. 1167 d. B) (d) Restored image 16
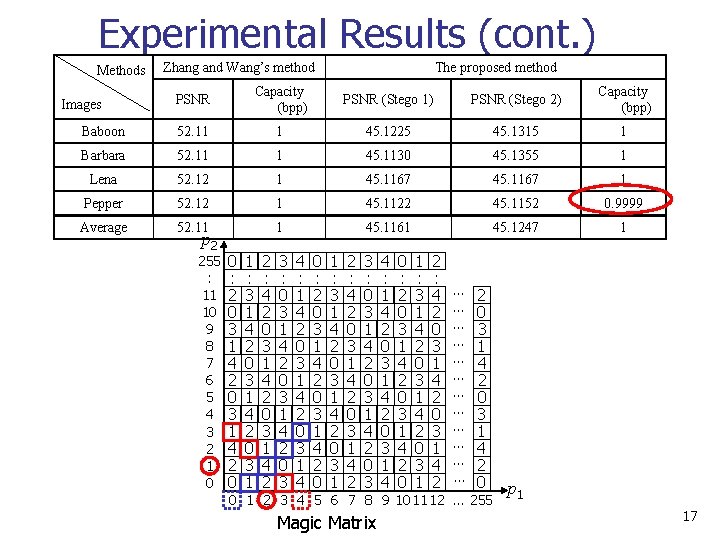
Experimental Results (cont. ) Methods Zhang and Wang’s method The proposed method PSNR Capacity (bpp) PSNR (Stego 1) PSNR (Stego 2) Capacity (bpp) Baboon 52. 11 1 45. 1225 45. 1315 1 Barbara 52. 11 1 45. 1130 45. 1355 1 Lena 52. 12 1 45. 1167 1 Pepper 52. 12 1 45. 1122 45. 1152 0. 9999 Average 52. 11 1 45. 1161 45. 1247 1 Images p 2 255 : 11 10 9 8 7 6 5 4 3 2 1 0 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 2 : 4 2 0 3 1 4 2 3 : 0 3 1 4 2 0 3 4 : 1 4 2 0 3 1 4 0 : 2 0 3 1 4 2 0 1 : 3 1 4 2 0 3 1 2 : 4 2 0 3 1 4 2 … … … 2 0 3 1 4 2 0 0 1 2 3 4 5 6 7 8 9 10 11 12 … 255 Magic Matrix p 1 17
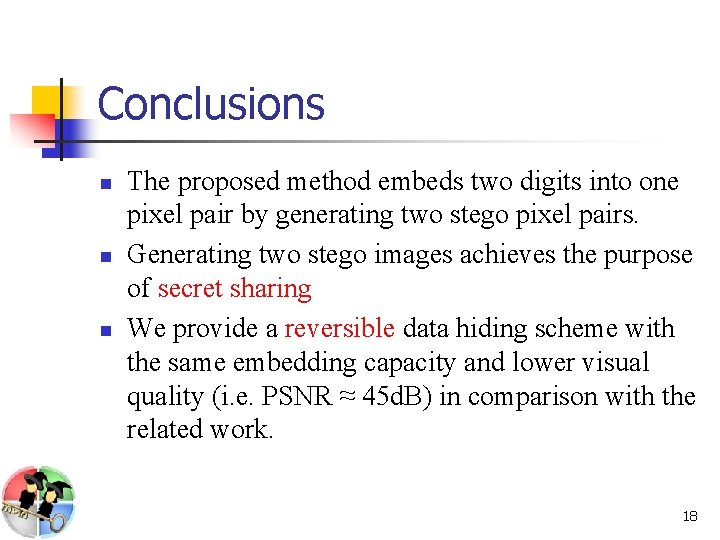
Conclusions n n n The proposed method embeds two digits into one pixel pair by generating two stego pixel pairs. Generating two stego images achieves the purpose of secret sharing We provide a reversible data hiding scheme with the same embedding capacity and lower visual quality (i. e. PSNR ≈ 45 d. B) in comparison with the related work. 18
- Slides: 18