Research in Security and Dependable Computing Shambhu Upadhyaya
Research in Security and Dependable Computing Shambhu Upadhyaya Computer Science and Engineering University at Buffalo Shambhu@cse. buffalo. edu August 28, 2003
Outline o Background o Students and List of Projects o Brief Description of Projects o Synergistic Activities CEISARE @ 2
Welcome CEISARE @ 3
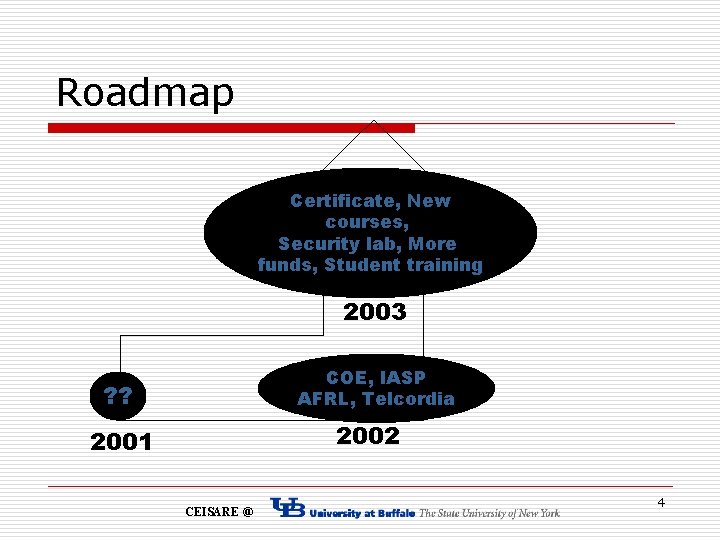
Roadmap Certificate, New courses, Security lab, More funds, Student training 2003 COE, IASP AFRL, Telcordia ? ? 2002 2001 CEISARE @ 4
UB’s Center of Excellence (Unofficial) Logo CEISARE @ 5
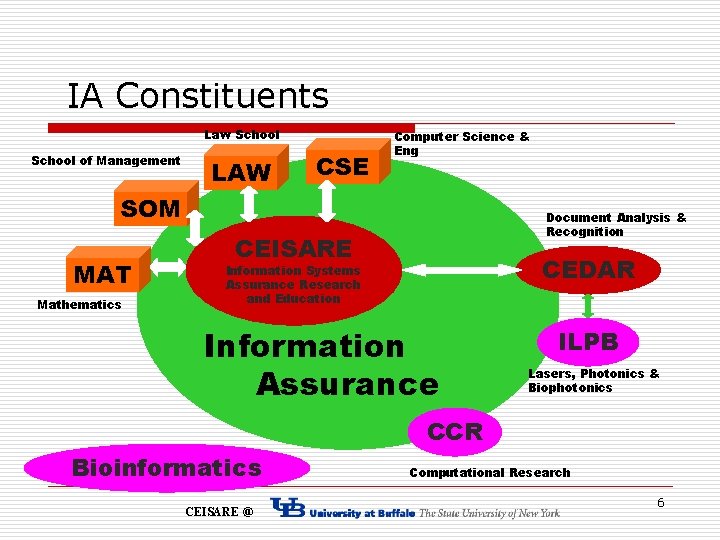
IA Constituents Law School of Management LAW CSE Computer Science & Eng SOM MAT Mathematics Document Analysis & Recognition CEISARE CEDAR Information Systems Assurance Research and Education Information Assurance ILPB Lasers, Photonics & Biophotonics CCR Bioinformatics CEISARE @ Computational Research 6
Students o o Recently graduated students n Kiran Mantha, MS, 2001 (Deloitte & Touche, NY) n Hugh Wu, Ph. D, 2002 (Faculty, Taiwan) n Neelesh Arora, MS, 2003 (Thomson Financial, NY) n Pradeep Nagaraj (2002), Sajit Balraj (2002), Gaurav Bhargava, 2003, MS (Qualcom, CA) Current students n Ramkumar Chinchani, MS, 2002 (Ph. D student) n Suranjan Pramanik (Ph. D student) n Ashish Garg (Ph. D student) n Mohit Virendra (Ph. D student) n Anusha Iyer (Ph. D student) n Dan Zhao (Ph. D student) n M. Nair (Ph. D student) n S. Vidyaraman (Ph. D student) n Aarthie Muthukrishnan (MS student) n Madhu Chandrasekharan (MS student) CEISARE @ 7
Collaborators o o Research n Martin Margala, University of Rochester n P. R. Mukund, RIT n Kevin Kwiat, AFRL n Bharat Jayaraman, CSE, UB n Jim Llinas, IE, UB n H. R. Rao, SOM, UB Education n Jeannette Neal, ECC n Donna Kaputa, ECC n Marina Cappellino, GCC CEISARE @ 8
Research and Educational Grants o o Research Grants n AFRL (2000 – 2004) n NYSTAR (2002 – 2004) n DARPA seedling (2003 – 2004) n NSA/ARDA (2003 – 2005) n AFRL (2003 – 2005), pending final approval n SRC (2003 – 2006) Educational Grants n o Do. D/NSA Students Supported n 7 students as RA and 4 as IA Scholars n 2 -4 new positions available CEISARE @ 9
Research Projects o Computer Security n Intrusion detection by encapsulating user’s intent – Concept development, simulation, investigation of scalability (thrust: anomaly detection) n Reasoning about intrusions (thrust: risk analysis) n Building secure enclaves (thrust: graph theory) n Simulation support for IA experiments (thrust: event-based) n Secure voting protocols (thrust: replication and two-phase commit) n Securing documents from Insider Threat – A multi-phase approach (thrust: attack graph, vulnerability analysis) n Event correlation for cyber attack recognition systems (thrust: data fusion) CEISARE @ 10
Research Projects (Contd. ) o Distributed Systems n Fault tolerance and security in enterprise servers (thrust: checkpointing and recovery) o VLSI Design and Test n Test scheduling in Systems-on-chips (thrust: algorithms) n Adaptive BIST for complex Systems-on-chip (thrust: built-in current sensors) n Test control architecture for future SOCs using on-chip wireless communication (thrust: on-chip RF nodes) CEISARE @ 11
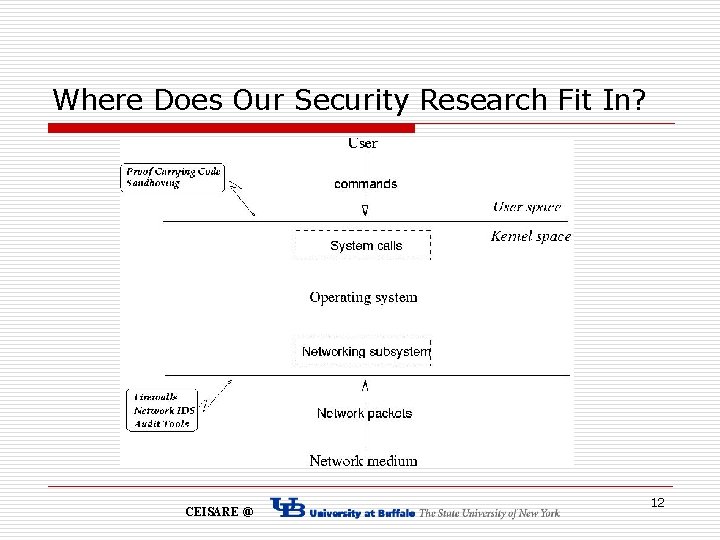
Where Does Our Security Research Fit In? CEISARE @ 12
Underlying Principles n Use the principle of least privilege to achieve better security n Use mandatory access control wherever appropriate n Data used for intrusion detection should be kept simple and small n Intrusion detection capabilities are enhanced if environment specific factors are taken into account CEISARE @ 13
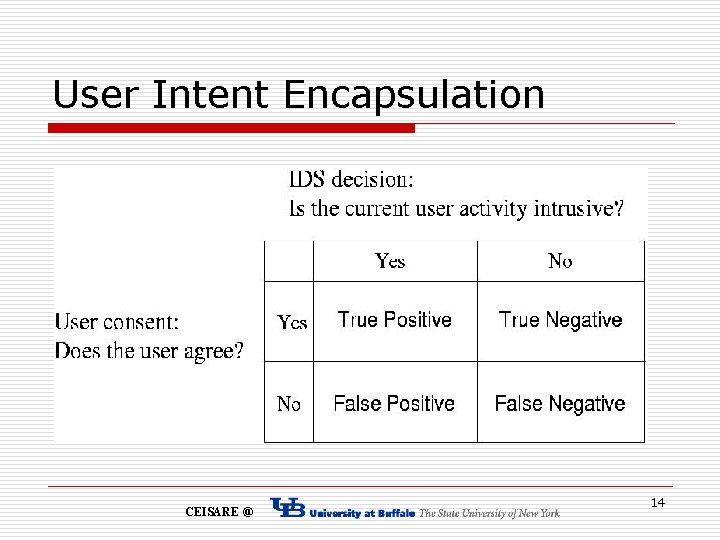
User Intent Encapsulation CEISARE @ 14
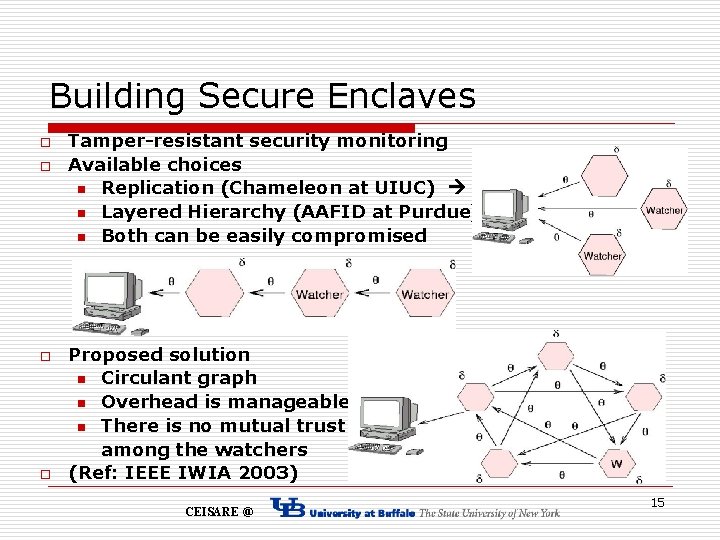
Building Secure Enclaves o o Tamper-resistant security monitoring Available choices n Replication (Chameleon at UIUC) n Layered Hierarchy (AAFID at Purdue) n Both can be easily compromised Proposed solution n Circulant graph n Overhead is manageable n There is no mutual trust among the watchers (Ref: IEEE IWIA 2003) CEISARE @ 15
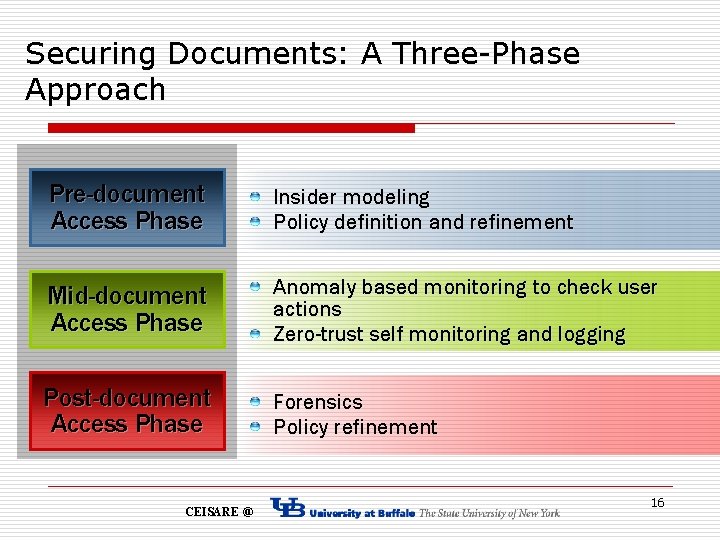
Securing Documents: A Three-Phase Approach Pre-document Access Phase Insider modeling Policy definition and refinement Mid-document Access Phase Anomaly based monitoring to check user actions Zero-trust self monitoring and logging Post-document Access Phase Forensics Policy refinement CEISARE @ 16
Policy Enforcement o o Most systems only log user logins Not easy to determine which user violated normal document policies Violators can act without fear of nonrepudiable trace-back How do you handle the problem? n n Tie each entity with a digital certificate Policy enforcement module Kerberized certificates for authentication and data integrity Scalability? CEISARE @ 17
Synergistic Activities o Information Assurance Scholarship program o Organized 1 st New York State Cyber Security Symposium at Utica, NY, Feb. 2003 jointly with Griffiss Institute, Utica, NY o Planning on a IA Workshop in Buffalo in the area of Secure Knowledge Management CEISARE @ 18
- Slides: 18