Rerandomizable and Replayable Adaptive Chosen Ciphertext Attack Secure
Rerandomizable and Replayable Adaptive Chosen Ciphertext Attack Secure Cryptosystems Jens Groth BRICS, University of Aarhus Cryptomathic A/S
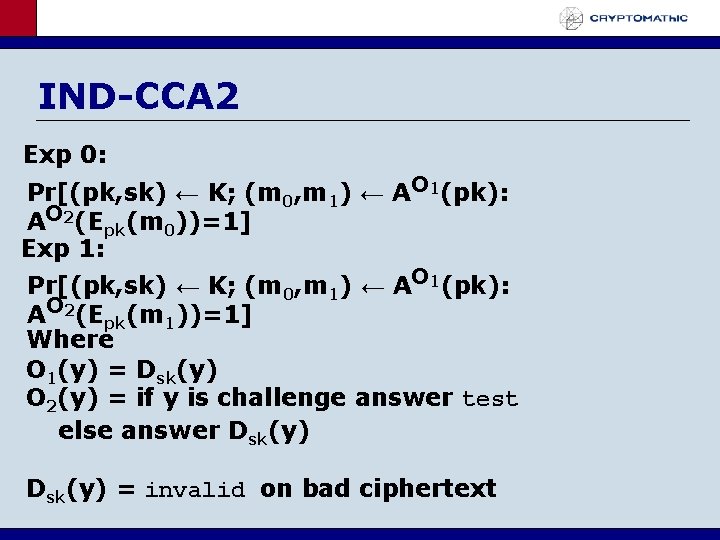
IND-CCA 2 Exp 0: Pr[(pk, sk) ← K; (m 0, m 1) ← AO 1(pk): AO 2(Epk(m 0))=1] Exp 1: Pr[(pk, sk) ← K; (m 0, m 1) ← AO 1(pk): AO 2(Epk(m 1))=1] Where O 1(y) = Dsk(y) O 2(y) = if y is challenge answer test else answer Dsk(y) = invalid on bad ciphertext
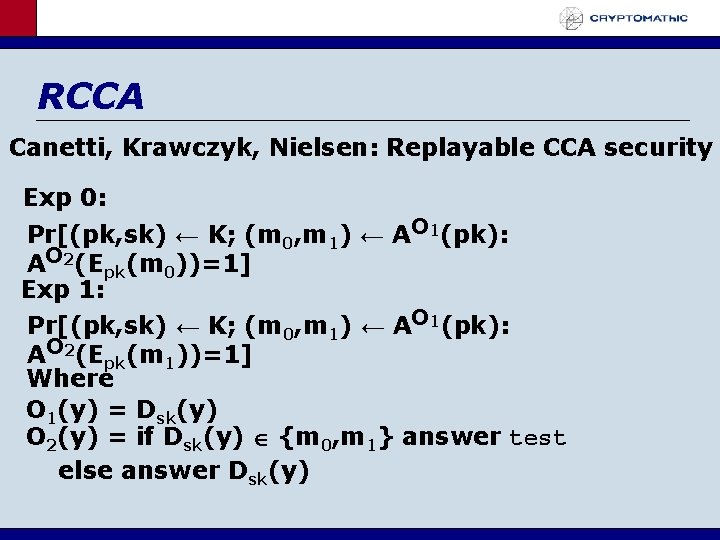
RCCA Canetti, Krawczyk, Nielsen: Replayable CCA security Exp 0: Pr[(pk, sk) ← K; (m 0, m 1) ← AO 1(pk): AO 2(Epk(m 0))=1] Exp 1: Pr[(pk, sk) ← K; (m 0, m 1) ← AO 1(pk): AO 2(Epk(m 1))=1] Where O 1(y) = Dsk(y) O 2(y) = if Dsk(y) {m 0, m 1} answer test else answer Dsk(y)
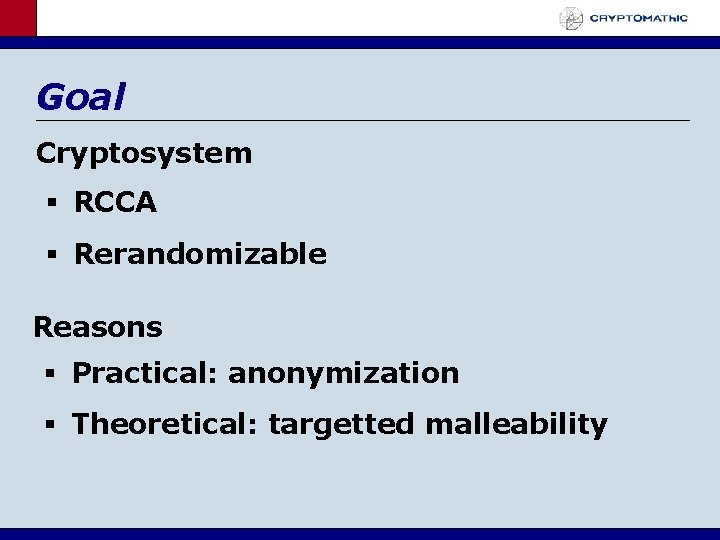
Goal Cryptosystem RCCA Rerandomizable Reasons Practical: anonymization Theoretical: targetted malleability
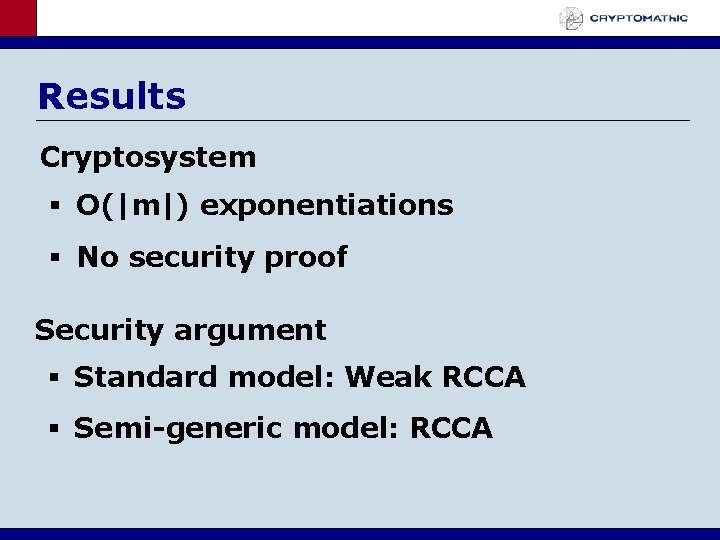
Results Cryptosystem O(|m|) exponentiations No security proof Security argument Standard model: Weak RCCA Semi-generic model: RCCA
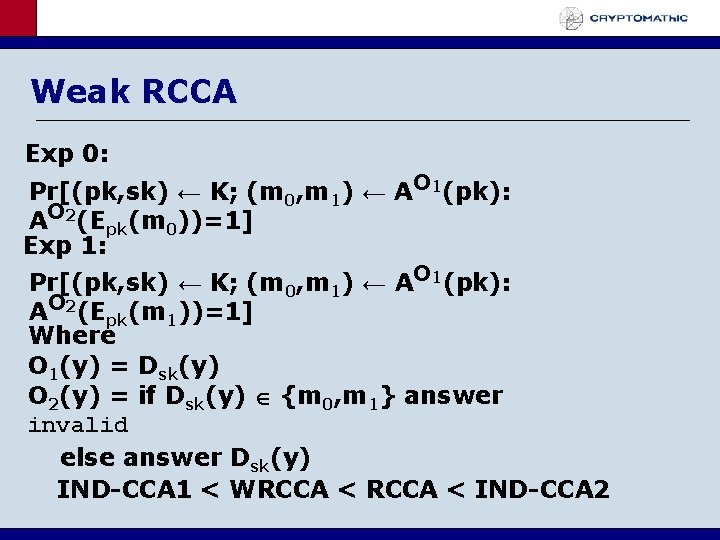
Weak RCCA Exp 0: Pr[(pk, sk) ← K; (m 0, m 1) ← AO 1(pk): AO 2(Epk(m 0))=1] Exp 1: Pr[(pk, sk) ← K; (m 0, m 1) ← AO 1(pk): AO 2(Epk(m 1))=1] Where O 1(y) = Dsk(y) O 2(y) = if Dsk(y) {m 0, m 1} answer invalid else answer Dsk(y) IND-CCA 1 < WRCCA < IND-CCA 2
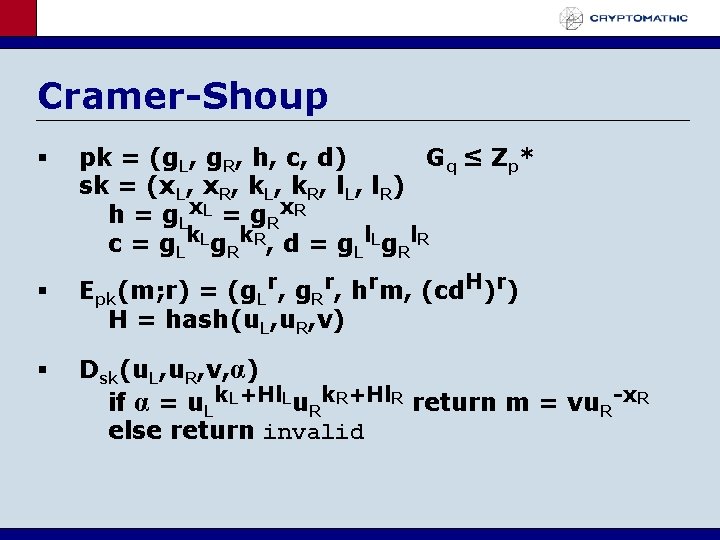
Cramer-Shoup pk = (g. L, g. R, h, c, d) Gq ≤ Z p * sk = (x. L, x. R, k. L, k. R, l. L, l. R) h = g Lx L = g Rx R c = g Lk Lg Rk R, d = g Ll Lg Rl R Epk(m; r) = (g. Lr, g. Rr, hrm, (cd. H)r) H = hash(u. L, u. R, v) Dsk(u. L, u. R, v, α) if α = u. Lk. L+Hl. Lu. Rk. R+Hl. R return m = vu. R-x. R else return invalid
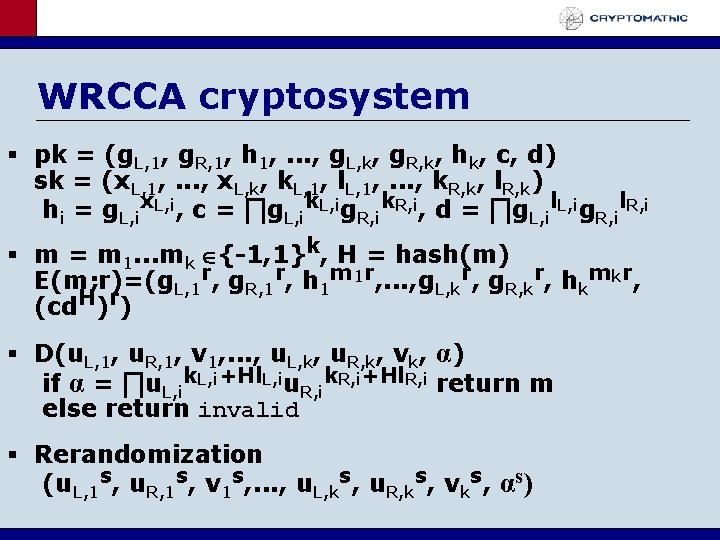
WRCCA cryptosystem pk = (g. L, 1, g. R, 1, h 1, . . . , g. L, k, g. R, k, hk, c, d) sk = (x. L, 1, . . . , x. L, k, k. L, 1, l. L, 1, . . . , k. R, k, l. R, k) hi = g. L, ix. L, i, c = ∏g. L, ik. L, ig. R, ik. R, i, d = ∏g. L, il. L, ig. R, il. R, i m = m 1. . . mk {-1, 1}k, H = hash(m) E(m; r)=(g. L, 1 r, g. R, 1 r, h 1 m 1 r, . . . , g. L, kr, g. R, kr, hkmkr, (cd. H)r) D(u. L, 1, u. R, 1, v 1, . . . , u. L, k, u. R, k, vk, α) if α = ∏u. L, ik. L, i+Hl. L, iu. R, ik. R, i+Hl. R, i return m else return invalid Rerandomization (u. L, 1 s, u. R, 1 s, v 1 s, . . . , u. L, ks, u. R, ks, vks, αs)
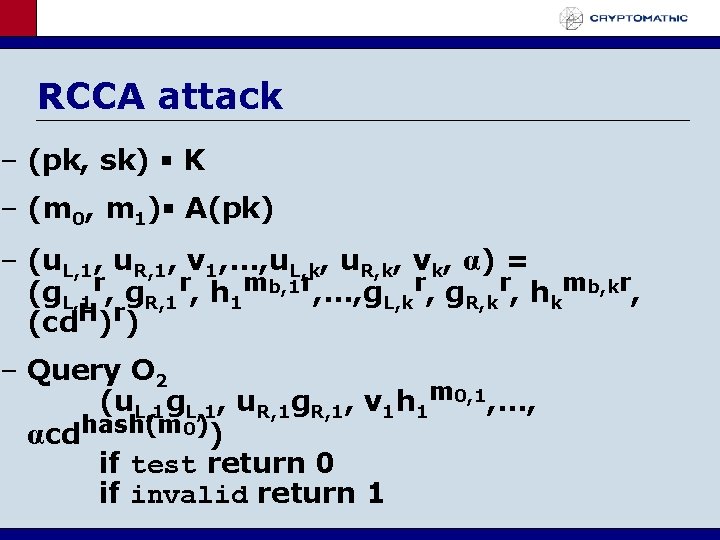
RCCA attack – (pk, sk) K – (m 0, m 1) A(pk) – (u. L, 1, u. R, 1, v 1, . . . , u. L, k, u. R, k, vk, α) = (g. L, 1 r, g. R, 1 r, h 1 mb, 1 r, . . . , g. L, kr, g. R, kr, hkmb, kr, (cd. H)r) – Query O 2 (u. L, 1 g. L, 1, u. R, 1 g. R, 1, v 1 h 1 m 0, 1, . . . , αcdhash(m 0)) if test return 0 if invalid return 1
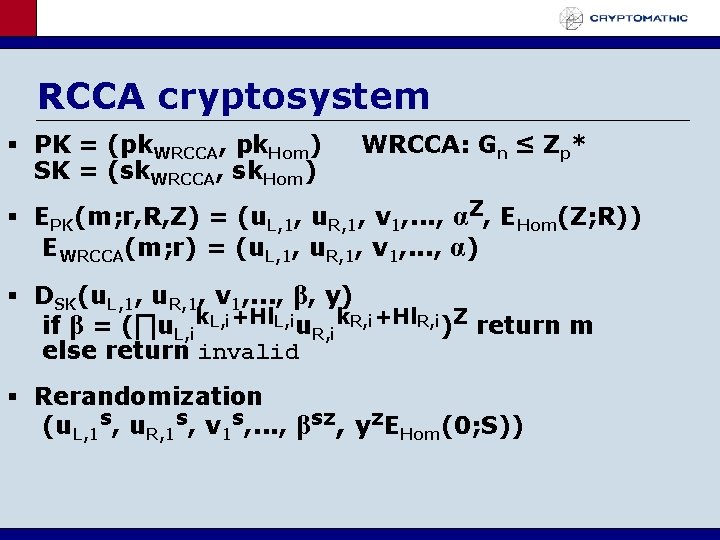
RCCA cryptosystem PK = (pk. WRCCA, pk. Hom) SK = (sk. WRCCA, sk. Hom) WRCCA: Gn ≤ Zp* EPK(m; r, R, Z) = (u. L, 1, u. R, 1, v 1, . . . , αZ, EHom(Z; R)) EWRCCA(m; r) = (u. L, 1, u. R, 1, v 1, . . . , α) DSK(u. L, 1, u. R, 1, v 1, . . . , β, y) if β = (∏u. L, ik. L, i+Hl. L, iu. R, ik. R, i+Hl. R, i)Z return m else return invalid Rerandomization (u. L, 1 s, u. R, 1 s, v 1 s, . . . , βsz, yz. EHom(0; S))
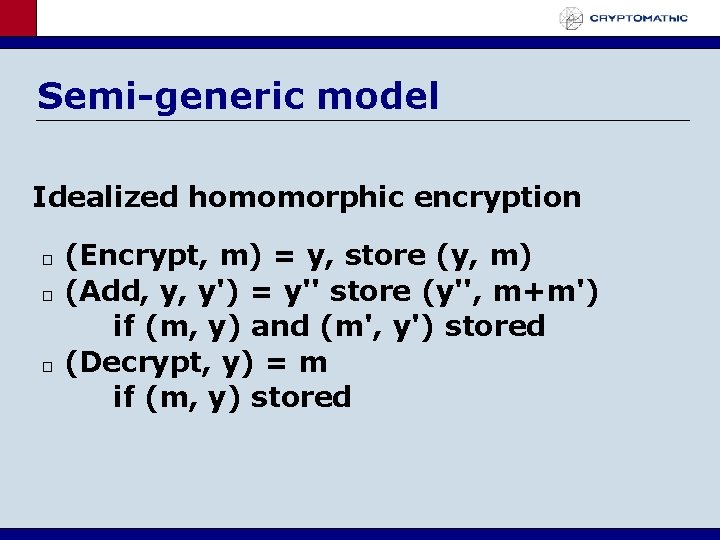
Semi-generic model Idealized homomorphic encryption � � � (Encrypt, m) = y, store (y, m) (Add, y, y') = y'' store (y'', m+m') if (m, y) and (m', y') stored (Decrypt, y) = m if (m, y) stored
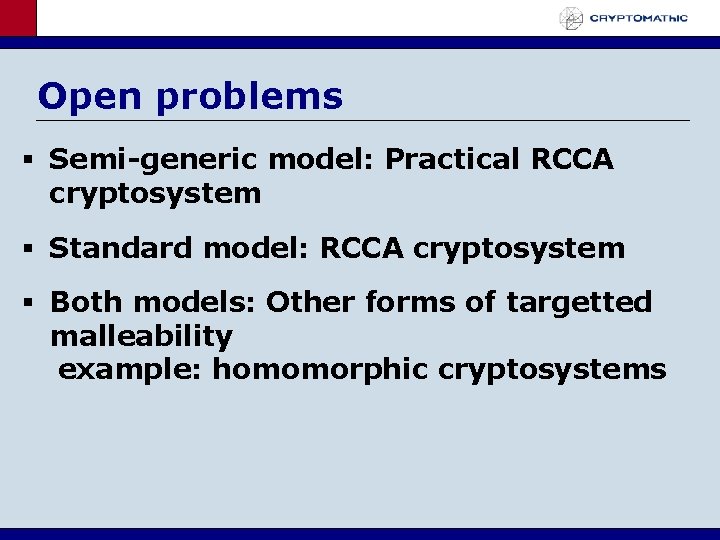
Open problems Semi-generic model: Practical RCCA cryptosystem Standard model: RCCA cryptosystem Both models: Other forms of targetted malleability example: homomorphic cryptosystems
- Slides: 12