Requirements for 802 1 AD Provider Bridges June
Requirements for 802. 1 AD Provider Bridges June 2003 Muneyoshi Suzuki NTT
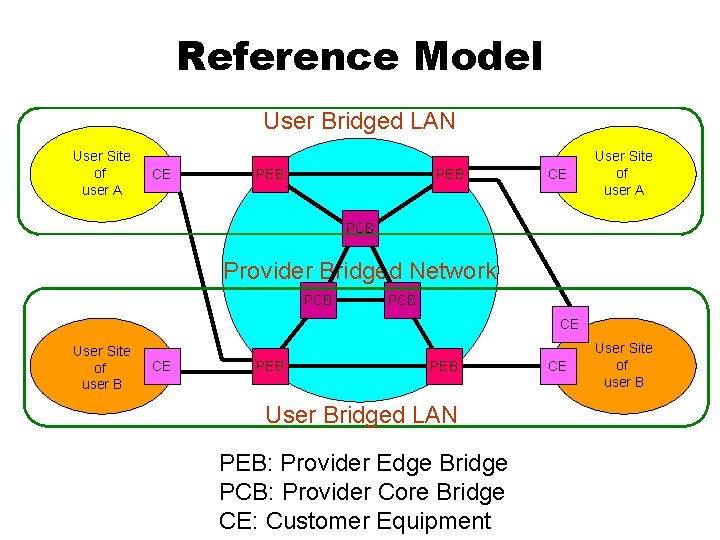
Reference Model User Bridged LAN User Site of user A CE PEB CE User Site of user A PCB Provider Bridged Network PCB CE User Site of user B CE PEB User Bridged LAN PEB: Provider Edge Bridge PCB: Provider Core Bridge CE: Customer Equipment CE User Site of user B
P-VID Space z Problem: 12 bit VID space defined 802. 1 Q-1998 is too small for public service z Requirements: y. If a P-VID identifies an User Bridged LAN, 24 bit (16 M users) ID space is needed y. If a P-VID identifies an user site, 32 bit (4 G sites) ID space is needed
Maximum Bridge Diameter z Problem: Recommended value of the Maximum Bridge Diameter is 7 (802. 1 D-1998, 802. 1 w-2001), but it is too small for public service z The standards don’t address technical background of the value (What happens if it exceeds 7? x. STP does not converge in periodic time? ) z Requirements: y. The value should be extended tens for Provider Bridged Network and 10 for User Bridged LAN y. Diameter of a Provider Bridged Network should not affect diameter of User Bridged LANs
Loop Prevention z Problem: A loop fatally affects a Bridged LAN z Requirements: y. Provider Bridged Network should deploy a mechanism for loop prevention y. User Bridged LAN should deploy a mechanism for loop prevention y. Provider Bridged Network should deploy a mechanism that protects the network from loops caused by users
Loop Prevention in Provider Bridged Network z It is provider’s responsibility to ensure loop-free topology for the Provider Bridged Network z Thus, the topology is decided by the provider’s policy and control z Therefore, it is quite unrealistic scenario to change the topology based on user-x. STP z Requirements: y. Provider Bridged Network should deploy provider-x. STP for loop prevention y. However, it is usually closed to the provider and need not to interwork with user-x. STP
Loop Prevention in User Bridged LAN z It is user’s responsibility to ensure loop-free topology for the User Bridged LAN z This is because, an user can cause a loop whether the provider supports x. STP for the user or not z However, if x. STP is used in an User Bridged LAN and if the provider forwards it transparently, loops can be prevented z This is because, the provider ensures loop-free topology and a single x. STP instance on a loop can detect and cut it z Requirements: y. User Bridged LAN should deploy customer-x. STP for loop prevention y. Provider Bridged Network may support per-user-x. STP, otherwise, it must forward user-x. STP BPDUs transparently
Provider Bridged Network Protection from Loops Caused by Users z If Provider Bridged Network supports per-user-x. STP, it can be protected from loops caused by users z Only Provider Edge Bridges need to support it, because a single x. STP instance on a loop can detect and cut it z However, this is not perfect solution, but it does not mean Providers don’t need protection z Requirements: y. Provider Edge Bridges may support per-user-x. STP to protect the network y. Otherwise, development of an OAM tool that detects loop through User and Provider Bridge Networks is indispensable
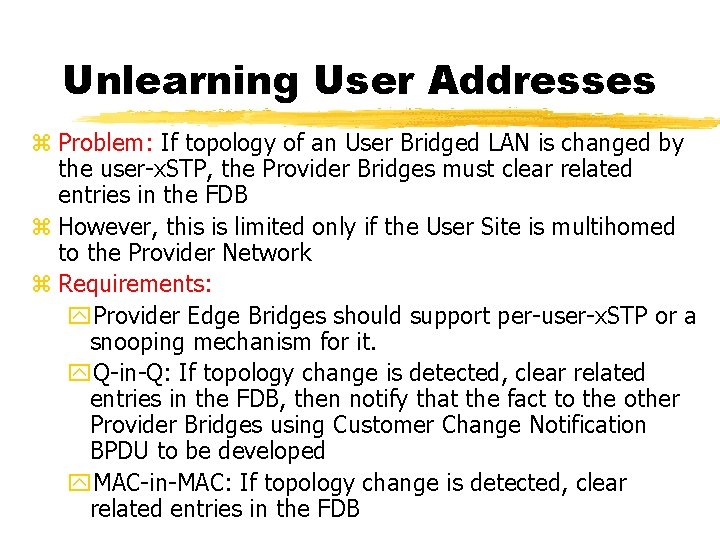
Unlearning User Addresses z Problem: If topology of an User Bridged LAN is changed by the user-x. STP, the Provider Bridges must clear related entries in the FDB z However, this is limited only if the User Site is multihomed to the Provider Network z Requirements: y. Provider Edge Bridges should support per-user-x. STP or a snooping mechanism for it. y. Q-in-Q: If topology change is detected, clear related entries in the FDB, then notify that the fact to the other Provider Bridges using Customer Change Notification BPDU to be developed y. MAC-in-MAC: If topology change is detected, clear related entries in the FDB
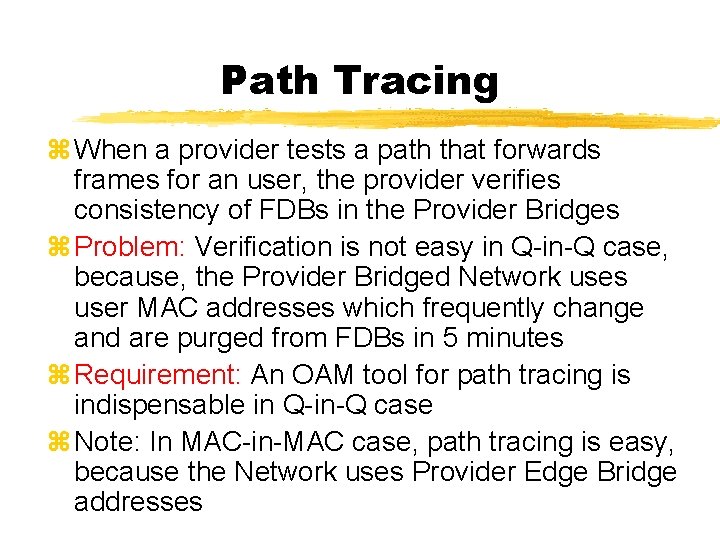
Path Tracing z When a provider tests a path that forwards frames for an user, the provider verifies consistency of FDBs in the Provider Bridges z Problem: Verification is not easy in Q-in-Q case, because, the Provider Bridged Network uses user MAC addresses which frequently change and are purged from FDBs in 5 minutes z Requirement: An OAM tool for path tracing is indispensable in Q-in-Q case z Note: In MAC-in-MAC case, path tracing is easy, because the Network uses Provider Edge Bridge addresses
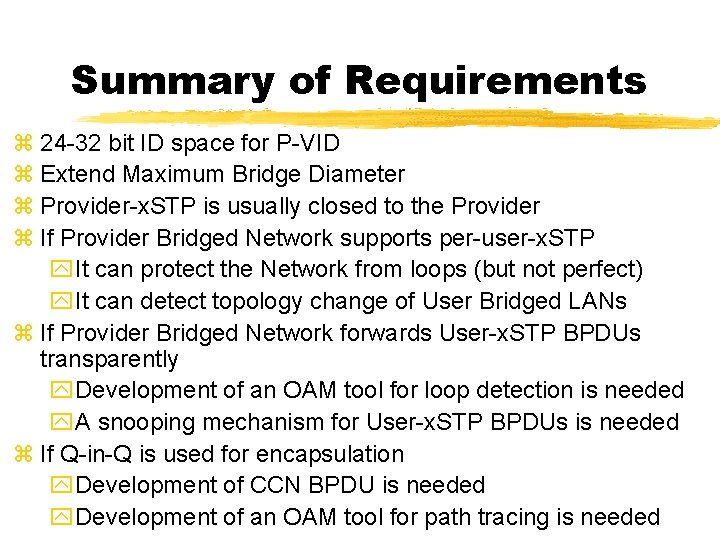
Summary of Requirements z 24 -32 bit ID space for P-VID z Extend Maximum Bridge Diameter z Provider-x. STP is usually closed to the Provider z If Provider Bridged Network supports per-user-x. STP y. It can protect the Network from loops (but not perfect) y. It can detect topology change of User Bridged LANs z If Provider Bridged Network forwards User-x. STP BPDUs transparently y. Development of an OAM tool for loop detection is needed y. A snooping mechanism for User-x. STP BPDUs is needed z If Q-in-Q is used for encapsulation y. Development of CCN BPDU is needed y. Development of an OAM tool for path tracing is needed
- Slides: 11