REQUIREMENTS ENGINEERING PROCESS Prepared by J Stella Janci
REQUIREMENTS ENGINEERING PROCESS Prepared by J. Stella Janci Rani Assistant Professor Department of Computer Science Sarah Tucker College Tirunelveli
REQUIREMENTS ENGINEERING PROCESS Software specification or requirements engineering is the process of understanding and defining what services are required and identifying the constraints on these services. . There are four main activities (or sub-activities) of requirements engineering: The requirements engineering process.
Contents 1. Feasibility Studies 2. Requirements elicitation and analysis. I. Viewpoint-oriented elicitation II. Scenarios III. Ethnography 3. Requirement Validation 4. Requirements management.
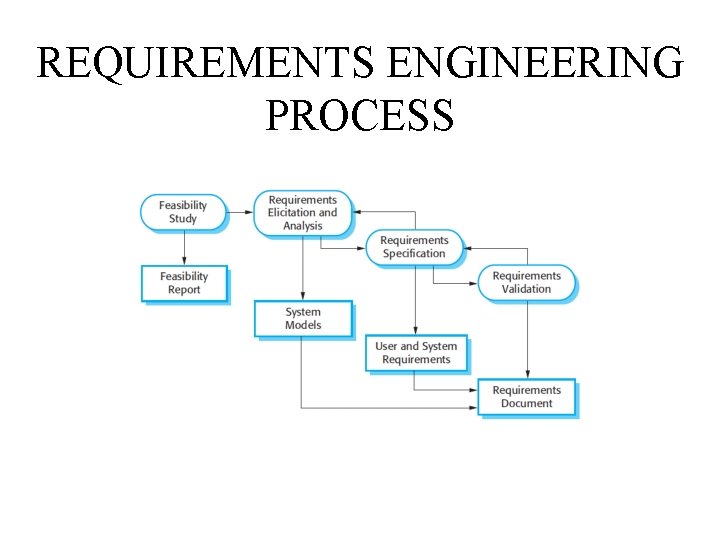
REQUIREMENTS ENGINEERING PROCESS
FOUR MAIN ACTIVITIES • Feasibility study: An estimate is made of whether the identified can be achieved using the current software and hardware technologies, under the current budget, etc. The feasibility study should be cheap and quick; it should inform the decision of whether or not to go ahead with the project. • Requirements elicitation and analysis: This is the process of deriving the system requirements through observation of existing systems, discussions with stakeholders, etc. This may involve the development of one or more system models and prototypes that can help us understanding the system to be specified. • Requirements specification: It’s the activity of writing down the information gathered during the elicitation and analysis activity into a document that defines a set of requirements. Two types of requirements may be included in this document; user and system requirements. • Requirements validation: It’s the process of checking the requirements for realism, consistency and completeness. During this process, our goal is to discover errors in the requirements document. When errors are found, it must be modified to correct these problems.
1. FEASIBILITY STUDIES • A feasibility study decides whether or not the proposed system is worthwhile • A short focused study that checks – If the system contributes to organisational objectives – If the system can be engineered using current technology and within budget – If the system can be integrated with other systems that are used
FEASIBILITY STUDY IMPLEMENTATION • Feasibility study involves information assessment (what is required), information collection and report writing • Questions for people in the organisation – What if the system wasn’t implemented? – What are current process problems? – How will the proposed system help? – What will be the integration problems? – Is new technology needed? What skills? – What facilities must be supported by the proposed system?
2. ELICITATION AND ANALYSIS • Sometimes called requirements elicitation or requirements discovery • Involves technical software development staff working with customers to find out about the application domain, the services that the system should provide and the system’s operational constraints. • Requirement elicitation and analysis may involve a variety of different kinds of people in an organisation. • May involve end-users, managers, engineers involved in maintenance, domain experts, trade unions, etc. These are called stakeholders. • The term stakeholders is used to refer to anyone who should have some direct or indirect influence on the system requirements.
PROBLEMS OF REQUIREMENTS ANALYSIS Elicitation and analysis is a difficult process for a number of reason. . . • Stakeholders don’t know what they really want • Stakeholders express requirements in their own terms • Different stakeholders may have conflicting requirements • Organisational and political factors may influence the system requirements • The economic and business environment in which the analysis takes place is dynamic. The requirements change during the analysis process. New stakeholders may emerge and the business environment change
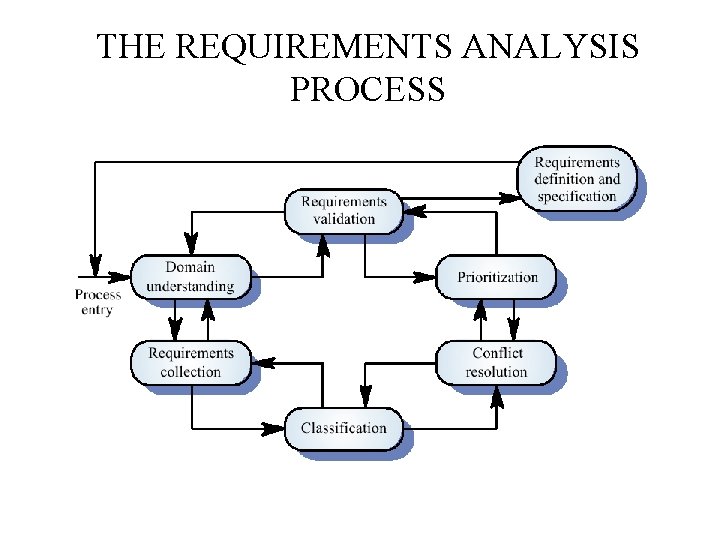
THE REQUIREMENTS ANALYSIS PROCESS
PROCESS ACTIVITIES • • • Domain understanding Requirements collection Classification Conflict resolution Prioritisation Requirements checking
3 Techniques • Three requirements for requirement elicitation and analysis. I. Viewpoint- oriented elicitation II. Scenarios III. ethnography
I. Viewpoint-Oriented Elicitation • For any medium-size or large system, there are usually different types of end-user. • Many stakeholders have some kind of interest in the system requirements. • For example ATM
AUTO-TELLER SYSTEM(ATM) INCLUDE • • Current Bank customers Representatives of other banks Bank’s Marketing department Managers of bank branches Counter staff at bank branches Database administrators Bank security managers Hardware and software maintenance engineers
Types of viewpoint • Data sources or sinks – Viewpoints are responsible for producing or consuming data. Analysis involves checking that data is produced and consumed and that assumptions about the source and sink of data are valid • Representation frameworks – Viewpoints represent particular types of system model. These may be compared to discover requirements that would be missed using a single representation. Particularly suitable for real-time systems • Receivers of services – Viewpoints are external to the system and receive services from it. Most suited to interactive systems
External Viewpoint • The most effective viewpoint-oriented approach for interactive system analysis uses external viewpoints. • These viewpoints interact with the system by receiving services from it and providing data and control signals to the system.
ADVANTAGES • Viewpoints are external to the system so are a natural way to structure the requirements elicitation process. • It is relatively easy to decide if something is a valid viewpoint. Viewpoint must interact with the system in some way. • Viewpoints and services are useful way of structuring non-functional requirements. Each service may have associated non-functional requirements. Multiple viewpoints allow the same service to have different non-functional requirements in different viewpoints.
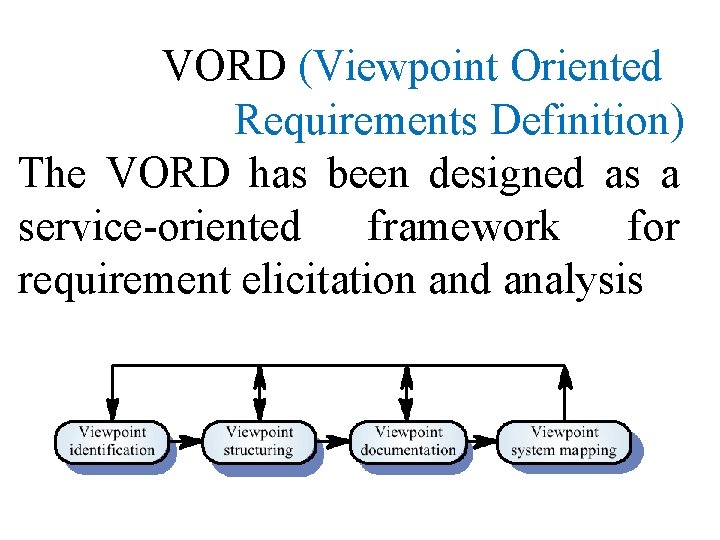
VORD (Viewpoint Oriented Requirements Definition) The VORD has been designed as a service-oriented framework for requirement elicitation and analysis
VORD Process Model • Viewpoint identification – Discover viewpoints which receive system services and identify the services provided to each viewpoint • Viewpoint structuring – Group related viewpoints into a hierarchy. Common services are provided at higher-levels in the hierarchy • Viewpoint documentation – Refine the description of the identified viewpoints and services • Viewpoint-system mapping – Transform the analysis to an object-oriented design
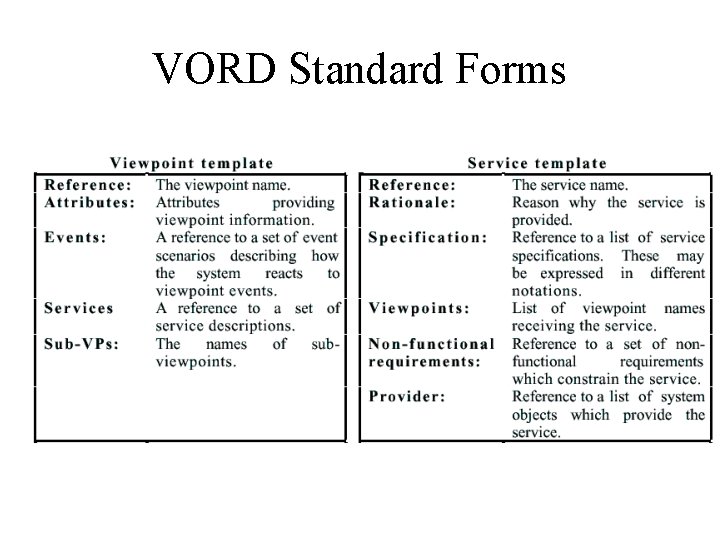
VORD Standard Forms
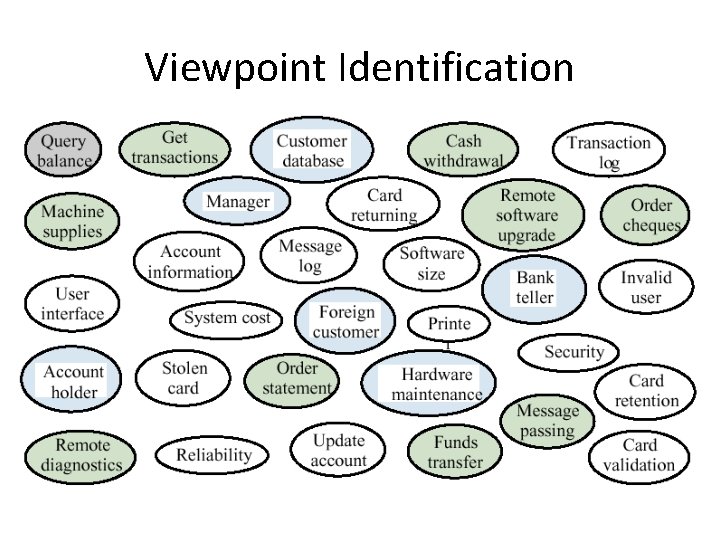
Viewpoint Identification
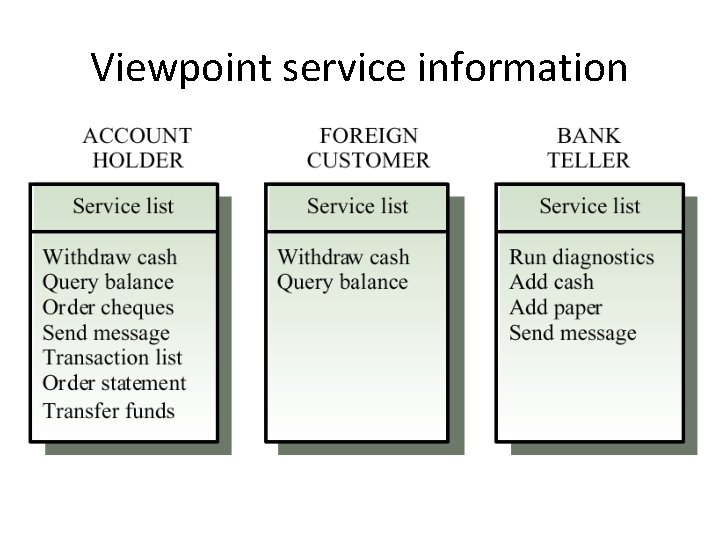
Viewpoint service information
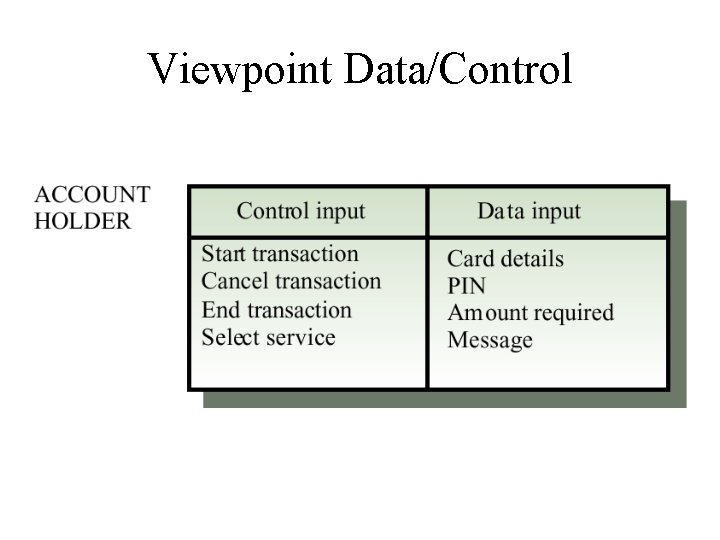
Viewpoint Data/Control
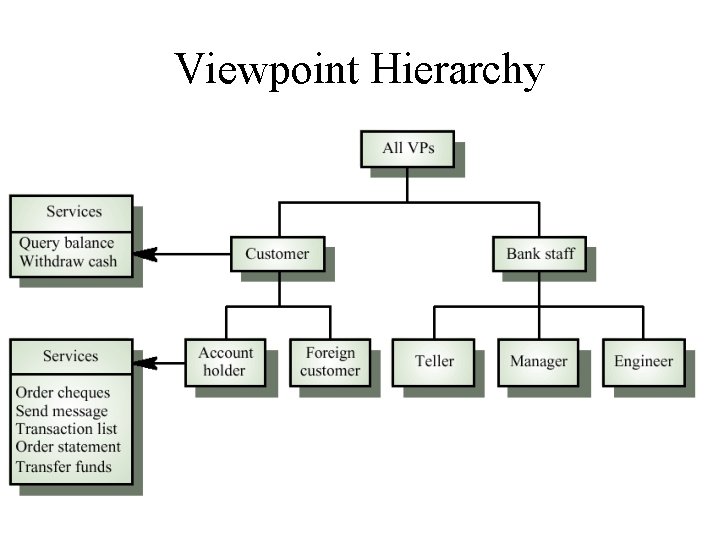
Viewpoint Hierarchy
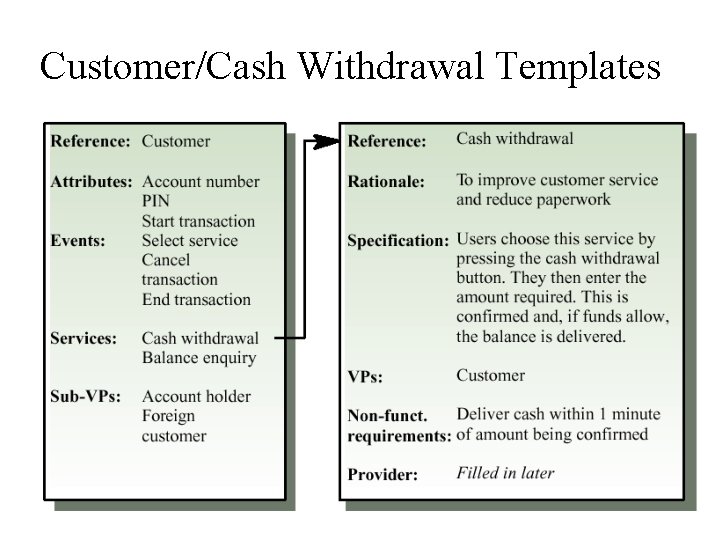
Customer/Cash Withdrawal Templates
II. Scenarios • Scenario of how they might interact with a software system. • Requirements engineers can use the information gained fro this discussion to formulate the actual system requirements. • Scenarios are particularly useful for adding detail to an outline requirements description
Scenario Descriptions • • • System state at the beginning of the scenario Normal flow of events in the scenario What can go wrong and how this is handled Other concurrent activities System state on completion of the scenario
Event Scenarios • Event scenarios may be used to describe how a system responds to the occurrence of some particular event such as ‘start transaction’ • VORD includes a diagrammatic convention for event scenarios. – Data provided and delivered – Control information – Exception processing – The name of the next expected event
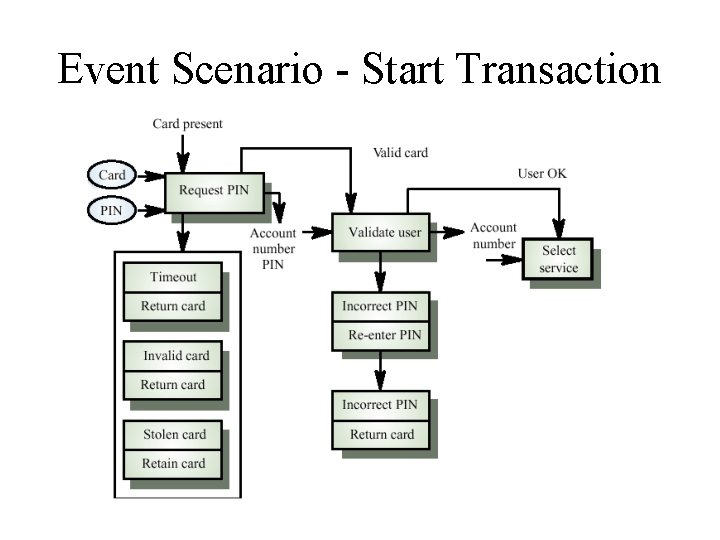
Event Scenario - Start Transaction
Exception Description • In this example, exceptions are – Timeout. Customer fails to enter a PIN within the allowed time limit – Invalid card. The card is not recognised and is returned – Stolen card. The card has been registered as stolen and is retained by the machine
Use Cases • Use-cases are a scenario based technique in the UML which identify the actors in an interaction and which describe the interaction itself • A set of use cases should describe all possible interactions with the system • Sequence diagrams may be used to add detail to use-cases by showing the sequence of event processing in the system
Notation For Data And Control Analysis • Ellipses. data provided from or delivered to a viewpoint • Control information enters and leaves at the top of each box • Data leaves from the right of each box • Exceptions are shown at the bottom of each box • Name of next event is in box with thick edges
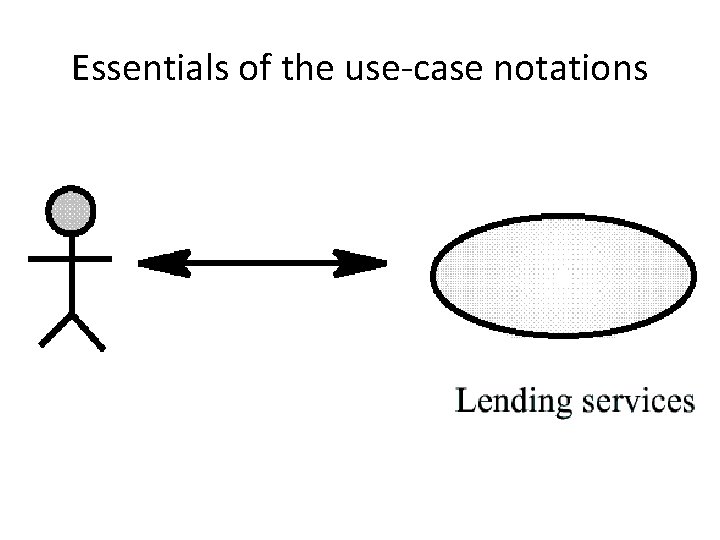
Essentials of the use-case notations
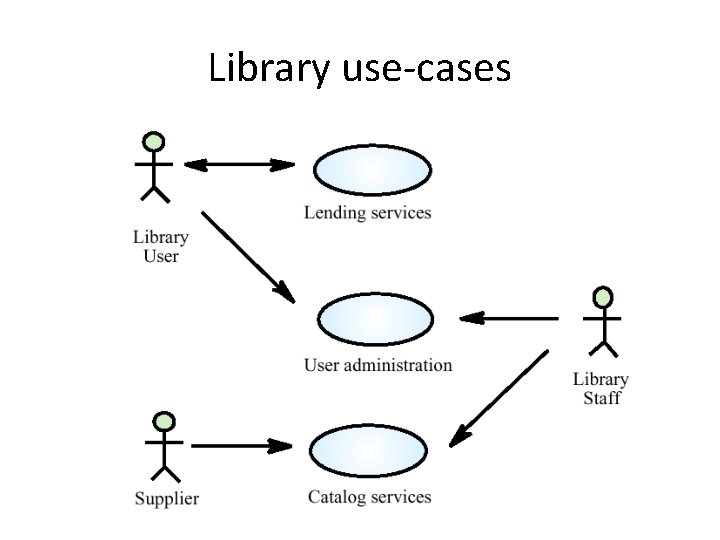
Library use-cases
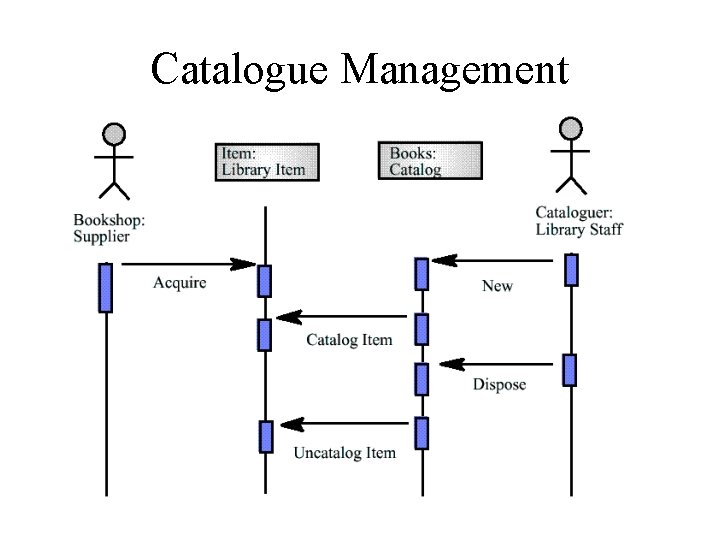
Catalogue Management
Catalogue Management • There are two objects of classes library item and catalog involved in the Catalogue Management use case. • The sequence of actions is from top to bottom and the labels on the arrows between the actors and objects indicate the names of operations. • When a book is bought, the new operation is enacted on Catalog and the Acquire operation on item. Once the book is available the catalog item operation is enacted on item.
III. Ethnography • Ethnography is an observational technique that can be used to understand social and organisational requirements. • The day to day work is observed and notes made of the actual tasks in which participants are involved. • Ethnographic studies have shown that work is usually richer and more complex than suggested by simple system models
Focused Ethnography • Developed in a project studying the air traffic control process • Combines ethnography with prototyping • Prototype development results in unanswered questions which focus the ethnographic analysis • Problem with ethnography is that it studies existing practices which may have some historical basis which is no longer relevant
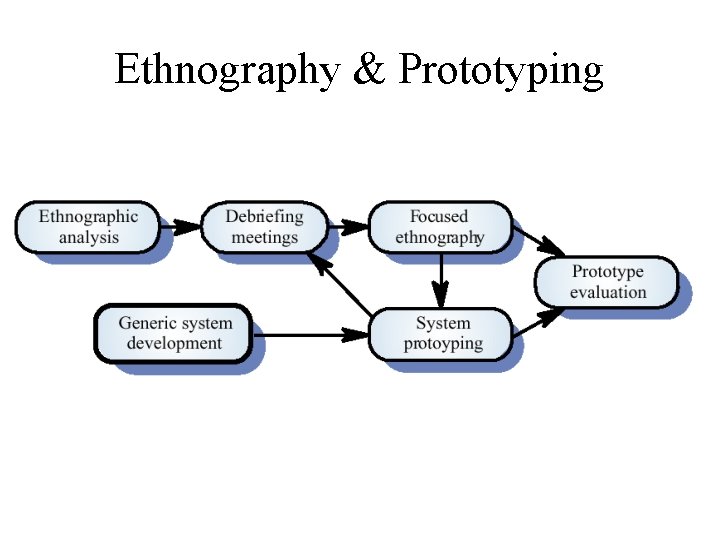
Ethnography & Prototyping
Scope of Ethnography • Requirements that are derived from the way that people actually work rather than the way I which process definitions suggest that they ought to work • Requirements that are derived from cooperation and awareness of other people’s activities
- Slides: 40