Republic of Croatia Office of the National Security
Republic of Croatia Office of the National Security Council Cyber Security, Cyber Defence and Cyber Operations - National Framework and International Cooperation RACVIAC: Building a Cyber Resilient Society in South-Eastern Europe – Advanced Training Course, Supported by The NATO Science for Peace and Security Programme Zagreb, 17 October 2016 Dr. sc. Aleksandar Klaić
Table of Contents: 1. Global trends and developments in Cyberspace - Situational awareness 2. Cyber Terms & Definitions – Taxonomy 3. Information Security Policy vs Cyber Security Policy 4. National Cyber Security Strategy Framework – Croatian Example 5. Conclusion 2
Actual Cyberspace Related Trends in NATO • NATO Warsaw Summit July 2016 - Communique http: //www. nato. int/cps/en/natohq/official_texts_133169. htm • „… recognise cyberspace as a domain of operations in which NATO has to defend itself as effectively as it does in the air, on land, and at the sea …” • Baseline Requirements for National Resilience • Security implications of energy supply and national critical infrastructure • . . . 3

Actual Cyberspace Related Trends in EU • Cybersecurity Strategy of the EU: An Open, Safe and Secure Cyberspace, 7 February 2013 • NIS Directive (EU) 2016/1148, 6 July 2016 • e. IDAS Regulation (EU) No 910/2014 • A Digital Single Market Strategy for Europe, May 2015 • GDPR Regulation (EU) 2016/679, 27 April 2016 • GDPR Directive (EU) 2016/680, 27 April 2016 • Contractual Public Private Partnership on Cybersecurity 4
International Cyberspace Related Trends • Opinion - Council of EU, July 2013, 12109/13 • „. . . international law, including international conventions such as the Council of Europe Convention on Cybercrime (Budapest Convention) and relevant conventions on international humanitarian law and human rights, such as the International Covenant on Civil and Political Rights, the International Covenant on Economic, Social and Cultural Rights provide a legal framework applicable in cyberspace. Efforts should therefore be made to ensure that these instruments are upheld in cyberspace; therefore the EU does not call for the creation of new international legal instruments for cyber issues, . . . ” • UN, OECD, OSCE – Regionally targeted initiatives • Meridian process (CIIP) - https: //www. meridianprocess. org/ • International Chamber of Commerce - http: //www 2. hgk. hr/ • ICC Cyber Security Guide for Business - www. iccwbo. org/cybersecurity 5
Cyberspace • Internet and all connected communication and information systems • Infrastructure and data • People ? Ø Cyberspace = virtual dimension of the society 6
Cyber Security • Capacitation and mutual coordination of all societal sectors • Protection of core values of liberty, fairness, transparency and the efficient rule of law • Primarily organizational issues • Societal sectors (public, academic, economic, citizens) • Sectoral cyber security stakeholders with different understanding of cyber issues, different competences, responsibilities, tasks, needs, expectations, interest, … 7
Cyber Terms & Definitions • NATO CCD COE - https: //ccdcoe. org/cyber-definitions. html#list • NIST - http: //nvlpubs. nist. gov/nistpubs/ir/2013/NIST. IR. 7298 r 2. pdf • Cyber Security: • „Preservation of confidentiality, integrity and availability of information in the Cyberspace. ” ISO/IEC 27032: 2012 Information technology — Security techniques — Guidelines for cybersecurity • „The ability to protect or defend the use of cyberspace from cyber attacks. ” NIST US Department of Commerce: Glossary of Key Information Security Terms • Cyber Operations: • The employment of cyber capabilities with the primary purpose of achieving objectives in or by the use of cyberspace. Tallinn Manual on the International Law Applicable to Cyber Warfare - 2013 8
Cyber Terms & Definitions • Cyber Defence: • Represents the part of the defence strategy falling under the responsibility of the ministry in charge of defence issues: Croatian Cyber Security Strategy (2015) • Refers to all measures to defend cyber space with military and appropriate means for achieving military-strategic goals. Cyber defence is an integrated system, comprising the implementation of all measures relating to ICT and information security, the capabilities of mil. CERT and CNO (Computer Network Operations) as well as the support of the physical capabilities of the army: Austrian Cyber Security Strategy (2013) • The set of all technical and non-technical measures allowing a State to defend in cyberspace information systems that it considers to be critical. Source: Information Systems and Defence – France’s Strategy (2011) 9
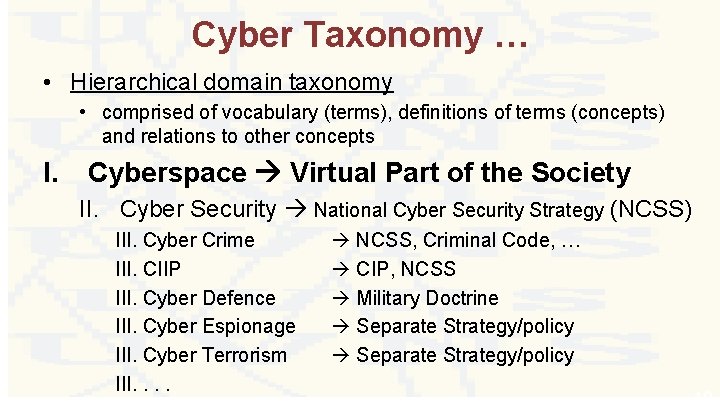
Cyber Taxonomy … • Hierarchical domain taxonomy • comprised of vocabulary (terms), definitions of terms (concepts) and relations to other concepts I. Cyberspace Virtual Part of the Society II. Cyber Security National Cyber Security Strategy (NCSS) III. Cyber Crime III. CIIP III. Cyber Defence III. Cyber Espionage III. Cyber Terrorism III. . NCSS, Criminal Code, … CIP, NCSS Military Doctrine Separate Strategy/policy 10
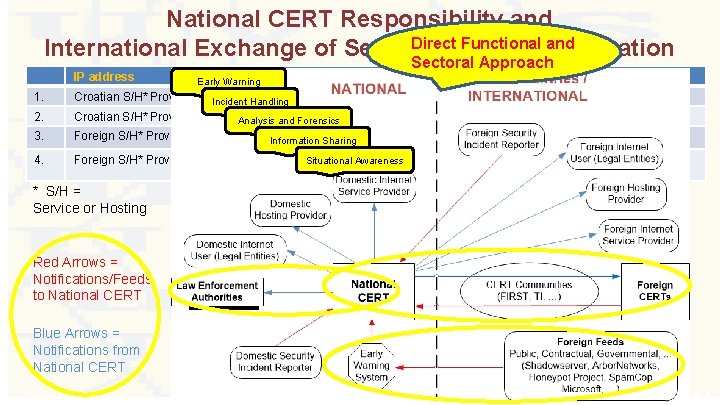
National CERT Responsibility and Direct Functional Information and International Exchange of Security Incident Sectoral Approach IP address Physical Location Domain Owner Croatia (RH) Domestic/Foreign 2. Croatian S/H* Providers Incident Handling. hr Croatian S/H* Providers. com; . net; . org; … Analysis and Forensics Croatia (RH) Domestic/Foreign 3. Foreign S/H* Providers . hr Out of Croatia Domestic/Foreign 4. Foreign S/H* Providers Situational Awareness Out of Croatia. com; . net; . org; … 1. Domain Early Warning Information Sharing Domestic * S/H = Service or Hosting Red Arrows = Notifications/Feeds to National CERT Blue Arrows = Notifications from National CERT 11 11
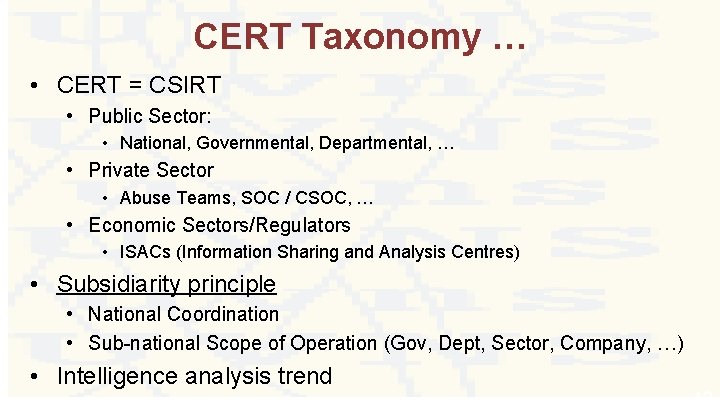
CERT Taxonomy … • CERT = CSIRT • Public Sector: • National, Governmental, Departmental, … • Private Sector • Abuse Teams, SOC / CSOC, … • Economic Sectors/Regulators • ISACs (Information Sharing and Analysis Centres) • Subsidiarity principle • National Coordination • Sub-national Scope of Operation (Gov, Dept, Sector, Company, …) • Intelligence analysis trend 12
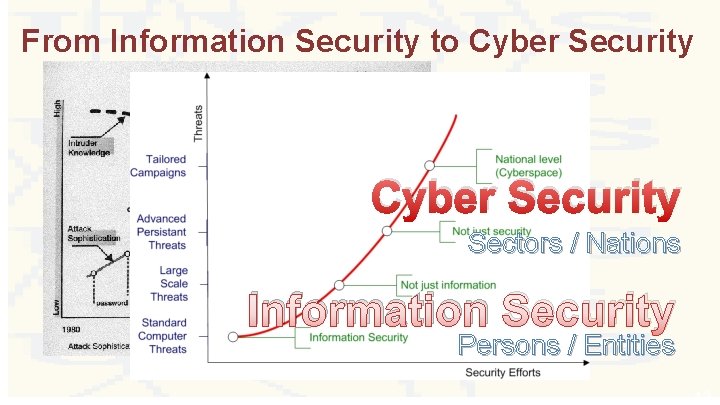
From Information Security to Cyber Security Sectors / Nations Information Security Persons / Entities 13
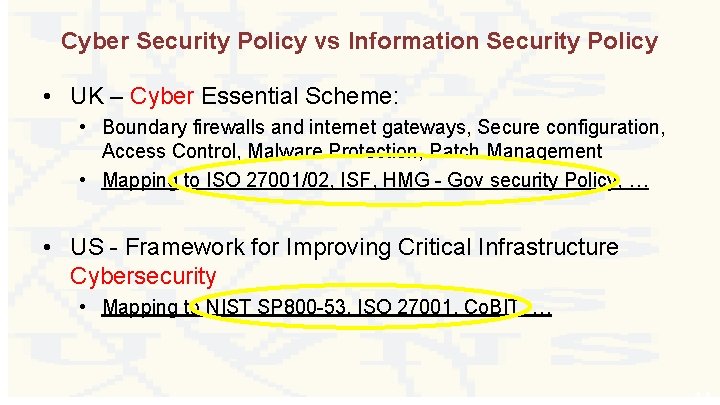
Cyber Security Policy vs Information Security Policy • UK – Cyber Essential Scheme: • Boundary firewalls and internet gateways, Secure configuration, Access Control, Malware Protection, Patch Management • Mapping to ISO 27001/02, ISF, HMG - Gov security Policy, … • US - Framework for Improving Critical Infrastructure Cybersecurity • Mapping to NIST SP 800 -53, ISO 27001, Co. BIT, … 14
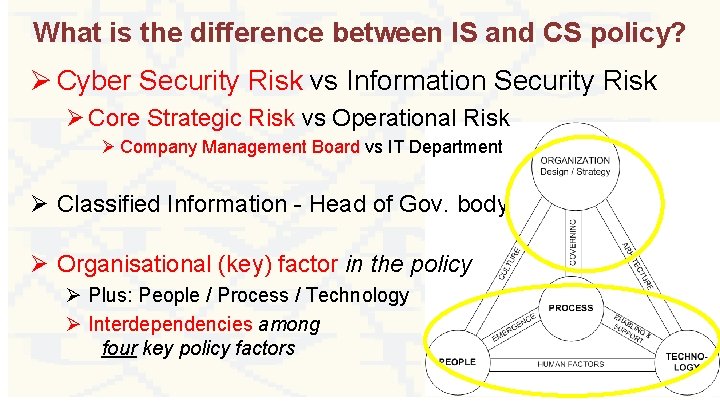
What is the difference between IS and CS policy? Ø Cyber Security Risk vs Information Security Risk Ø Core Strategic Risk vs Operational Risk Ø Company Management Board vs IT Department Ø Classified Information - Head of Gov. body Ø Organisational (key) factor in the policy Ø Plus: People / Process / Technology Ø Interdependencies among four key policy factors 15
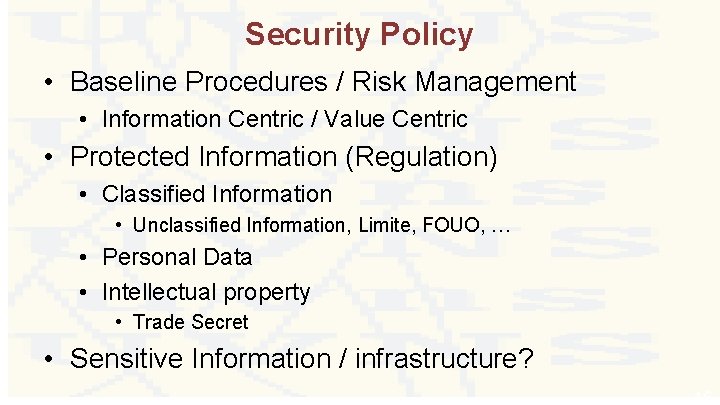
Security Policy • Baseline Procedures / Risk Management • Information Centric / Value Centric • Protected Information (Regulation) • Classified Information • Unclassified Information, Limite, FOUO, … • Personal Data • Intellectual property • Trade Secret • Sensitive Information / infrastructure? 16
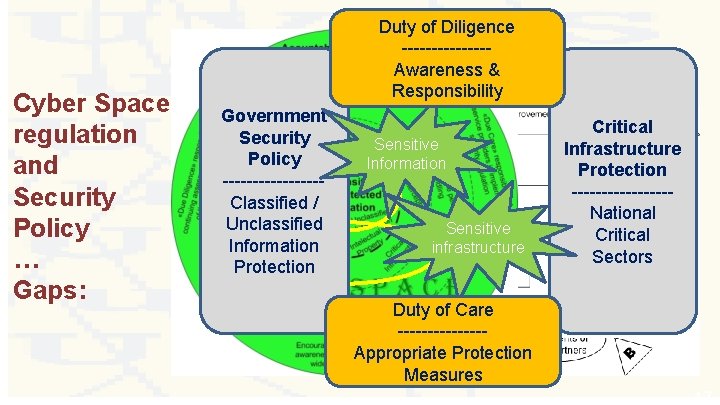
Cyber Space regulation and Security Policy … Gaps: Duty of Diligence -------Awareness & Responsibility Government Security Policy --------Classified / Unclassified Information Protection Sensitive Information Sensitive infrastructure Critical Infrastructure Protection --------National Critical Sectors Duty of Care -------Appropriate Protection Measures 17
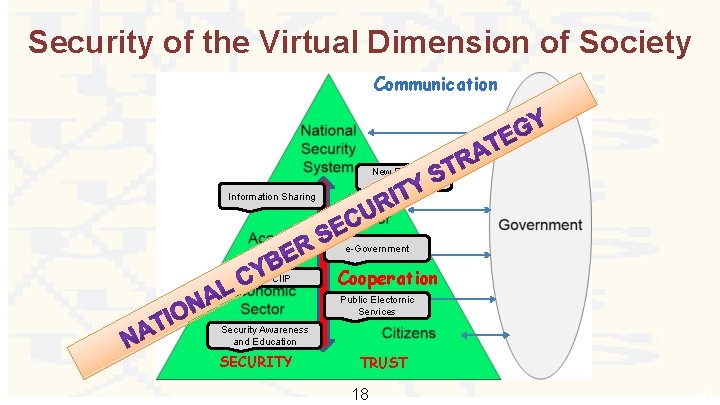
Security of the Virtual Dimension of Society Communication New Emerging Threats Information Sharing e-Government CIP / CIIP Cooperation Public Electornic Services Security Awareness and Education SECURITY TRUST 18 18
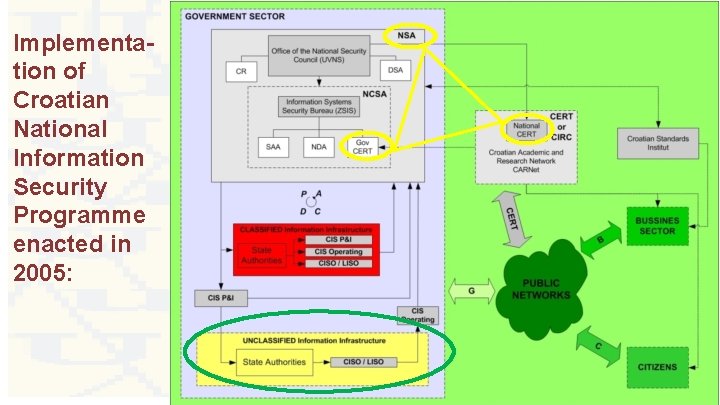
Implementation of Croatian National Information Security Programme enacted in 2005: 19
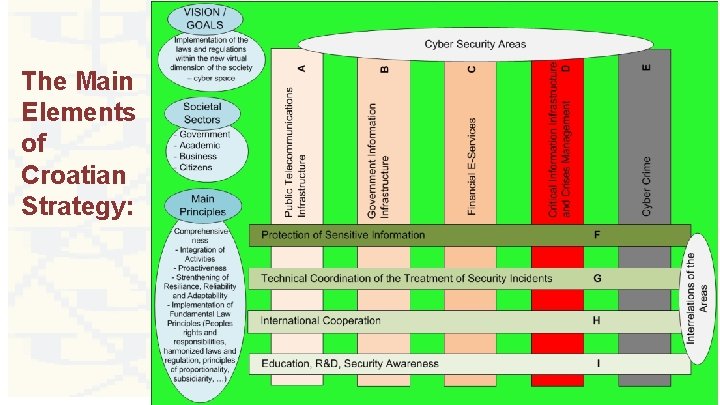
The Main Elements of Croatian Strategy: 20
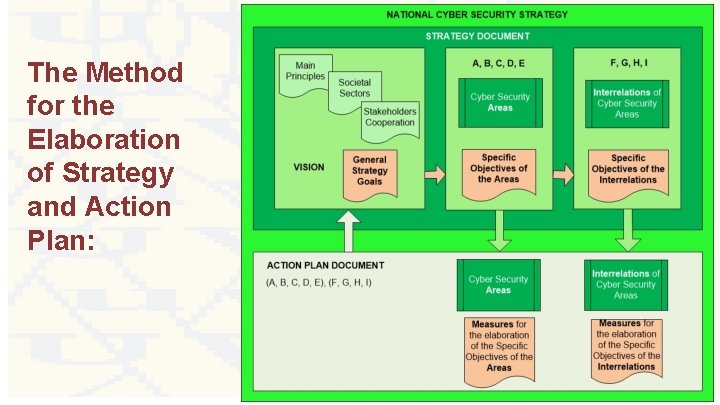
The Method for the Elaboration of Strategy and Action Plan: 21
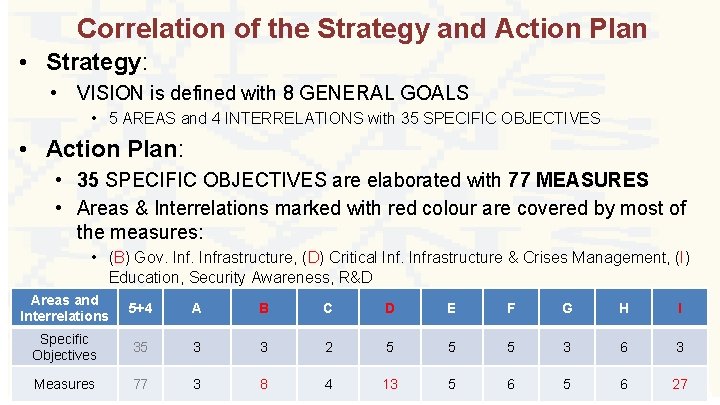
Correlation of the Strategy and Action Plan • Strategy: • VISION is defined with 8 GENERAL GOALS • 5 AREAS and 4 INTERRELATIONS with 35 SPECIFIC OBJECTIVES • Action Plan: • 35 SPECIFIC OBJECTIVES are elaborated with 77 MEASURES • Areas & Interrelations marked with red colour are covered by most of the measures: • (B) Gov. Infrastructure, (D) Critical Infrastructure & Crises Management, (I) Education, Security Awareness, R&D Areas and Interrelations 5+4 A B C D E F G H I Specific Objectives 35 3 3 2 5 5 5 3 6 3 Measures 77 3 8 4 13 5 6 27 22
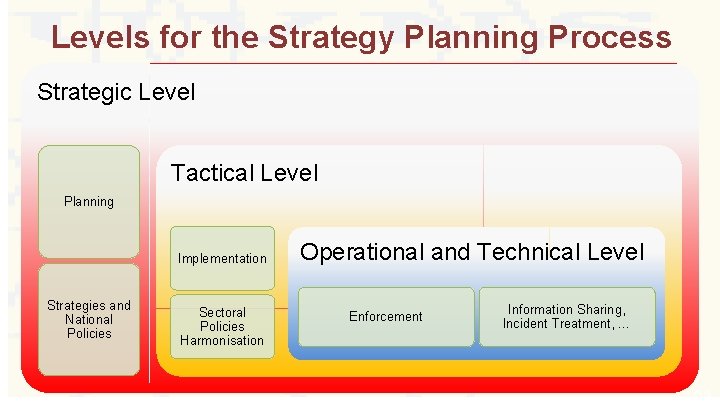
Levels for the Strategy Planning Process Strategic Level Tactical Level Planning Implementation Strategies and National Policies Sectoral Policies Harmonisation Operational and Technical Level Enforcement Information Sharing, Incident Treatment, … 23
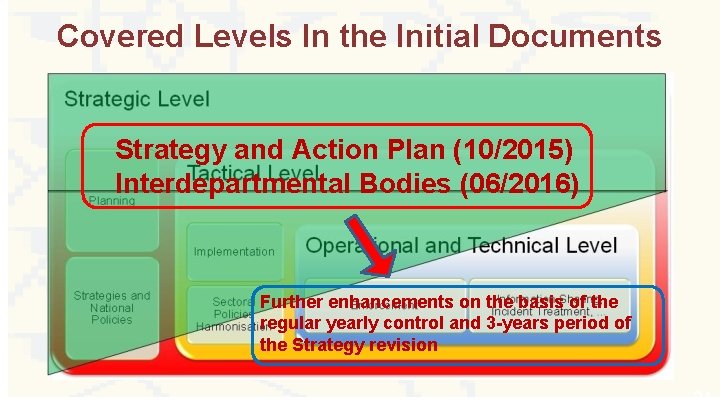
Covered Levels In the Initial Documents Strategy and Action Plan (10/2015) Interdepartmental Bodies (06/2016) Further enhancements on the basis of the regular yearly control and 3 -years period of the Strategy revision 24
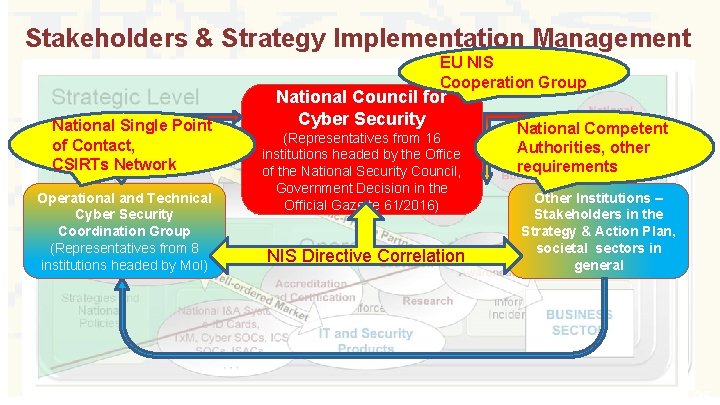
Stakeholders & Strategy Implementation Management EU NIS Cooperation Group National Single Point of Contact, CSIRTs Network Operational and Technical Cyber Security Coordination Group (Representatives from 8 institutions headed by Mo. I) National Council for Cyber Security (Representatives from 16 institutions headed by the Office of the National Security Council, Government Decision in the Official Gazette 61/2016) NIS Directive Correlation National Competent Authorities, other requirements Other Institutions – Stakeholders in the Strategy & Action Plan, societal sectors in general 25
Conclusion • Cyberspace • virtual dimension of the society • Cyber Security • trust for economy development • Cyber Taxonomy • Terms, definitions, relations • Cyber Security Strategy / Policy • National / institutional Frameworks for cooperation in virtual dimension of the society – organisational factor 26
Thank You ! ? Aleksandar Klaić, Ph. D. Assistant Director for Information Security aleksandar. klaic@uvns. hr Office of the National Security Council Croatian NSA/DSA tel. +385. 1. 4681 222; fax. +385. 1. 4686 049 www. uvns. hr 27
- Slides: 27