Reinventing Remote Access With Direct Access Dawie Human










- Slides: 37


Reinventing Remote Access With Direct. Access Dawie Human Infrastructure Architect Inobits Consulting Session Code: WSV 320
Agenda Secure Access Landscape Demo Direct. Access Solution Benefits Deployment Models & Requirements Name Resolution Supporting Technologies Diagnostics Questions & Answers

Mobile Workforce Increasingly Mobile Data Porous Perimeter Globalization
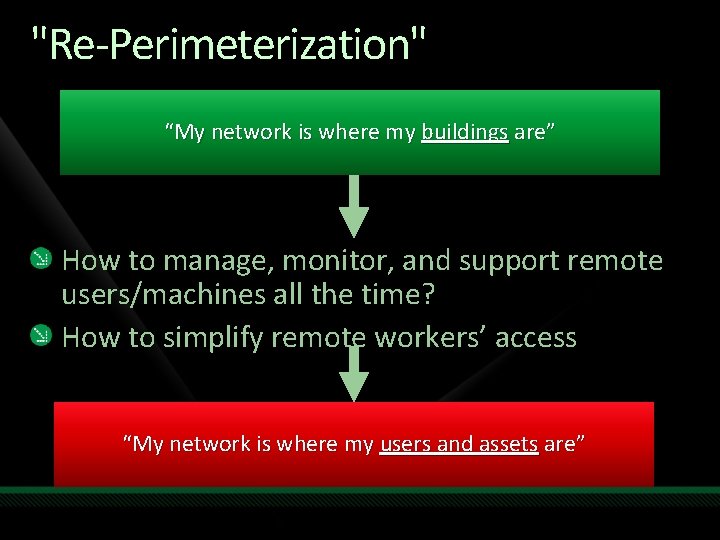
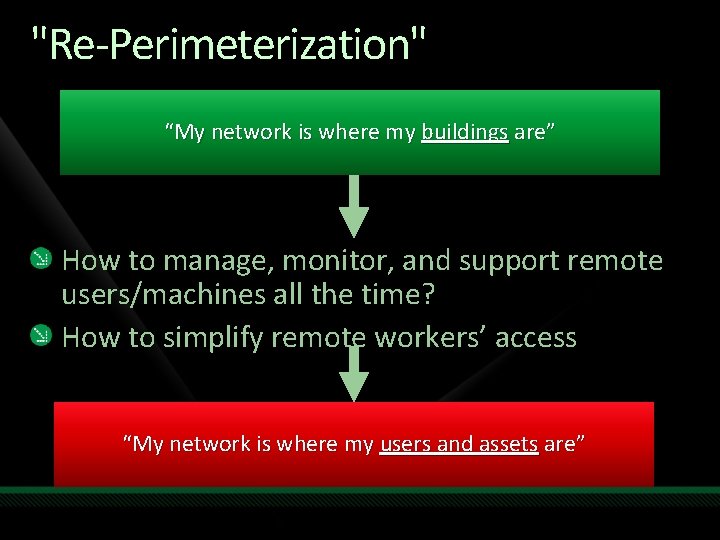
"Re-Perimeterization" “My network is where my buildings are” How to manage, monitor, and support remote users/machines all the time? How to simplify remote workers’ access “My network is where my users and assets are”
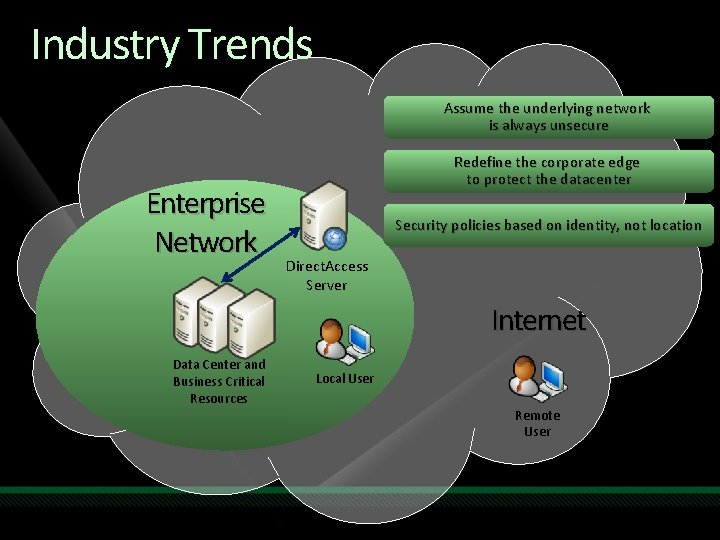
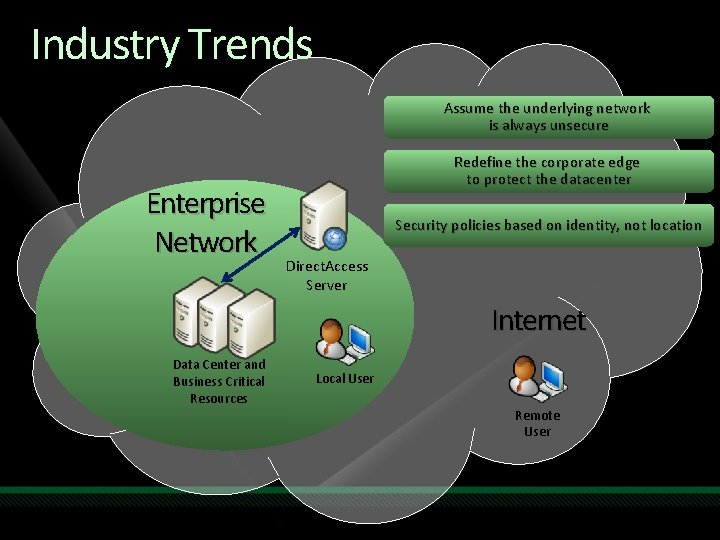
Industry Trends Assume the underlying network is always unsecure Enterprise Network Redefine the corporate edge to protect the datacenter Security policies based on identity, not location Direct. Access Server Internet Data Center and Business Critical Resources Local User Remote User
Windows Server 2008 R 2 Addressing Enterprise Needs Addressing User Needs Supporting IT Professionals Work Anywhere Infrastructure using Direct Access

Direct. Access Providing seamless, secure access to enterprise resources from anywhere

demo Direct. Access in Action
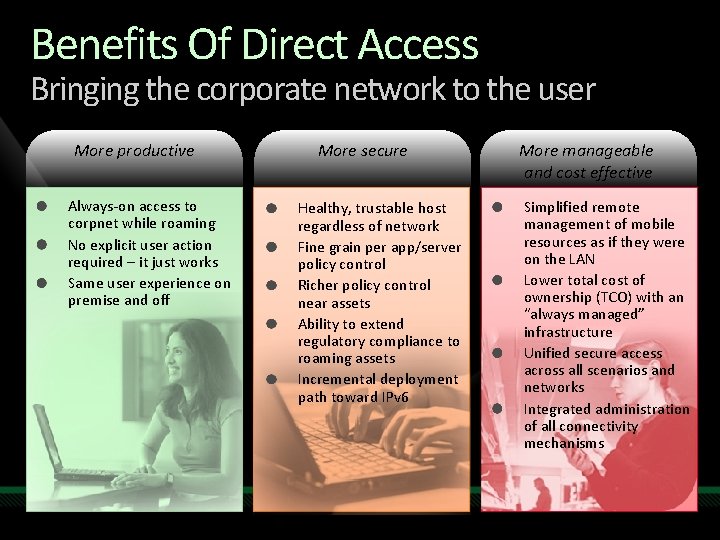
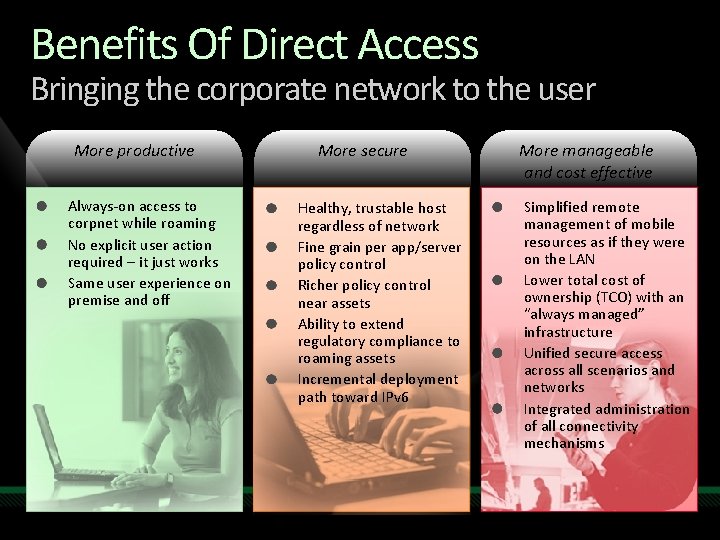
Benefits Of Direct Access Bringing the corporate network to the user More productive Always-on access to corpnet while roaming No explicit user action required – it just works Same user experience on premise and off More secure Healthy, trustable host regardless of network Fine grain per app/server policy control Richer policy control near assets Ability to extend regulatory compliance to roaming assets Incremental deployment path toward IPv 6 More manageable and cost effective Simplified remote management of mobile resources as if they were on the LAN Lower total cost of ownership (TCO) with an “always managed” infrastructure Unified secure access across all scenarios and networks Integrated administration of all connectivity mechanisms
Always On Always connected No user action required Adapts to changing networks
Secure Encrypted by default Works with Smartcards Granular access control Coexists with existing edge, health, and access policies

Manageable Reach out to previously untouchable machines Allows remote clients to process Group Policies NAP integration for health compliance Consolidate Edge Infrastructure
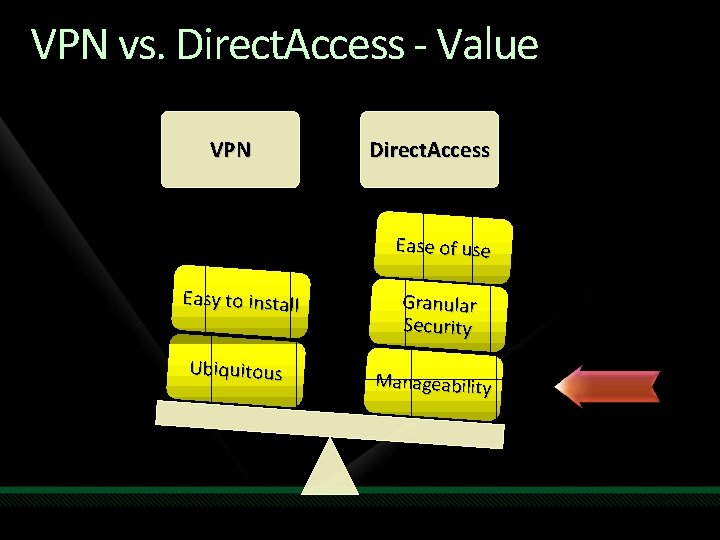
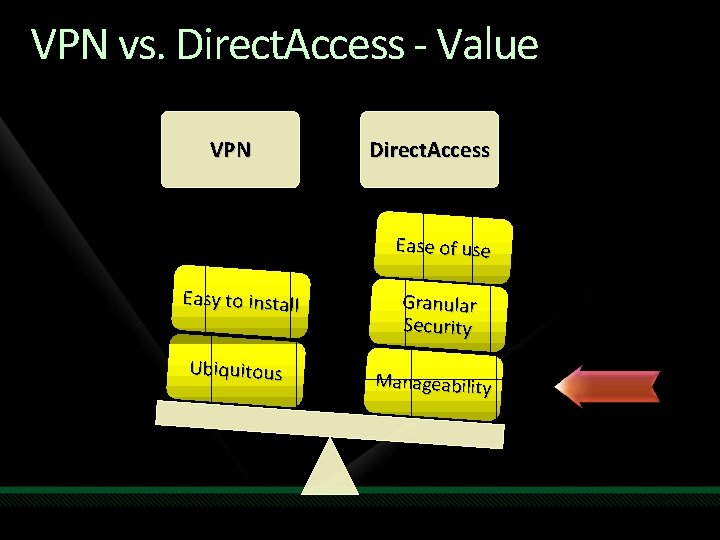
VPN vs. Direct. Access - Value VPN Direct. Access Ease of use Easy to install Ubiquitous Granular Security Manageability
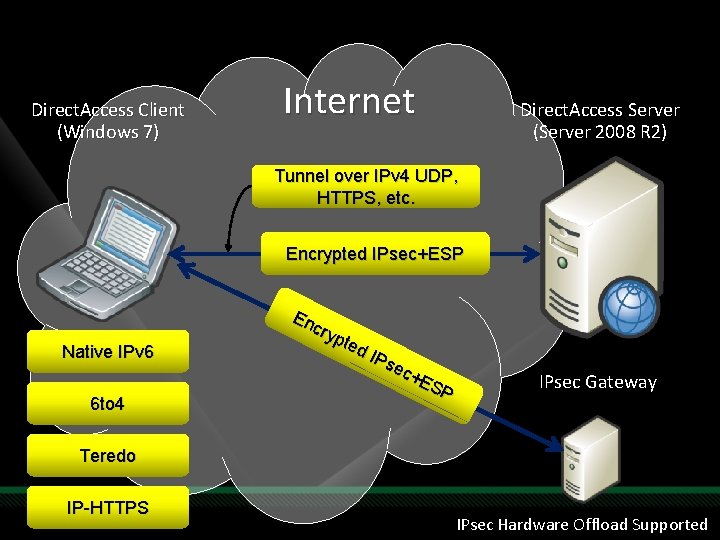
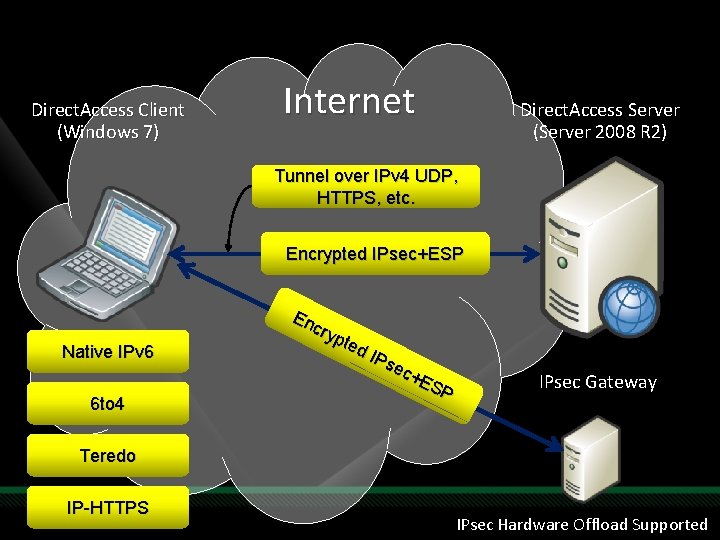
Direct. Access Client (Windows 7) Internet Direct. Access Server (Server 2008 R 2) Tunnel over IPv 4 UDP, HTTPS, etc. Encrypted IPsec+ESP Native IPv 6 6 to 4 En cry pte d IPs ec+ ES P IPsec Gateway Teredo IP-HTTPS IPsec Hardware Offload Supported
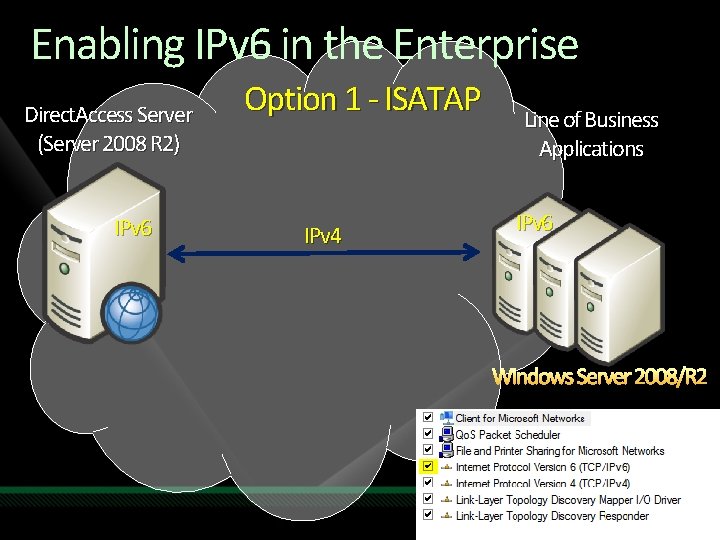
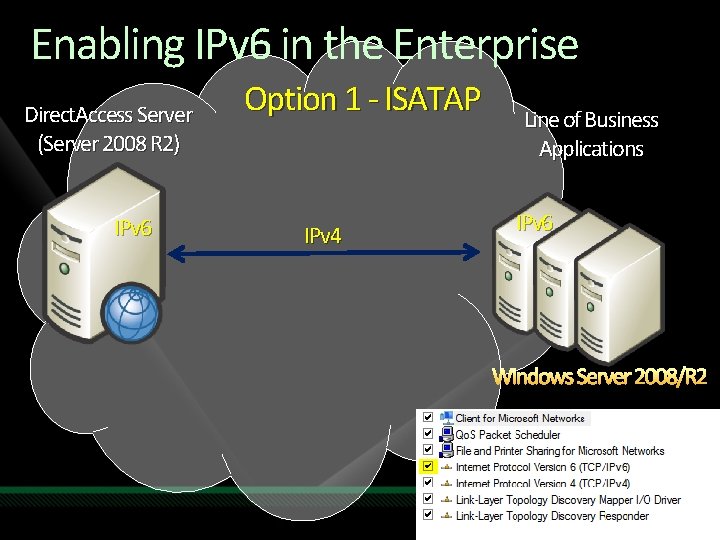
Enabling IPv 6 in the Enterprise Direct. Access Server (Server 2008 R 2) IPv 6 Option 1 - ISATAP IPv 4 Line of Business Applications IPv 6 Windows Server 2008/R 2
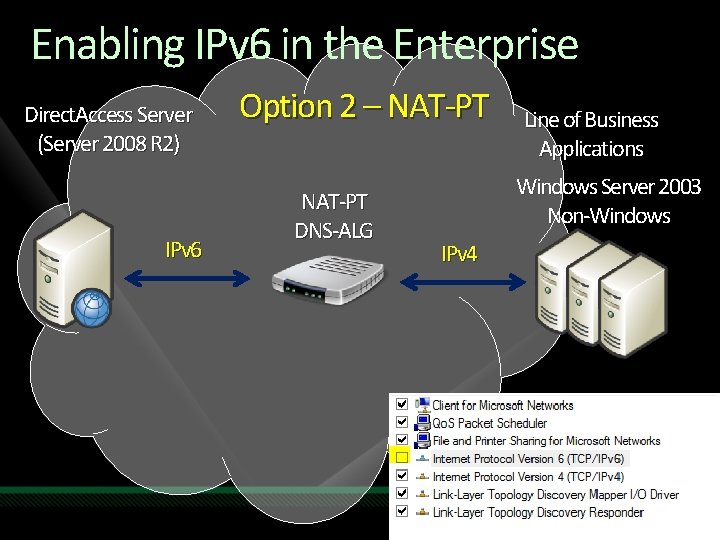
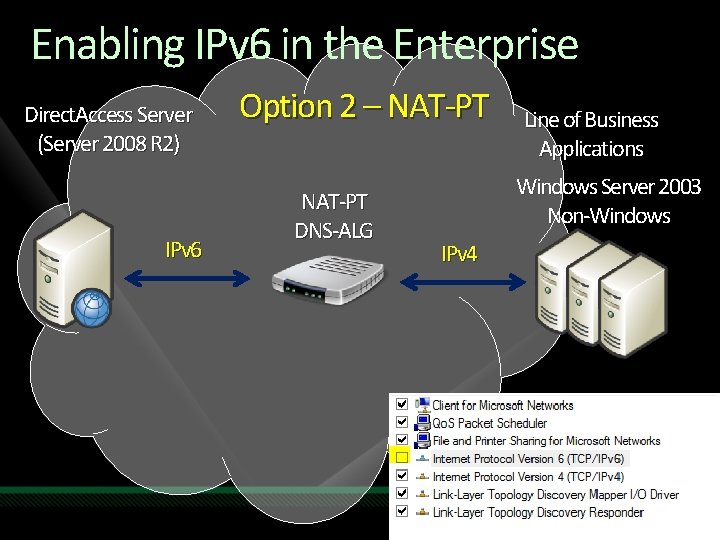
Enabling IPv 6 in the Enterprise Direct. Access Server (Server 2008 R 2) IPv 6 Option 2 – NAT-PT DNS-ALG Line of Business Applications Windows Server 2003 Non-Windows IPv 4
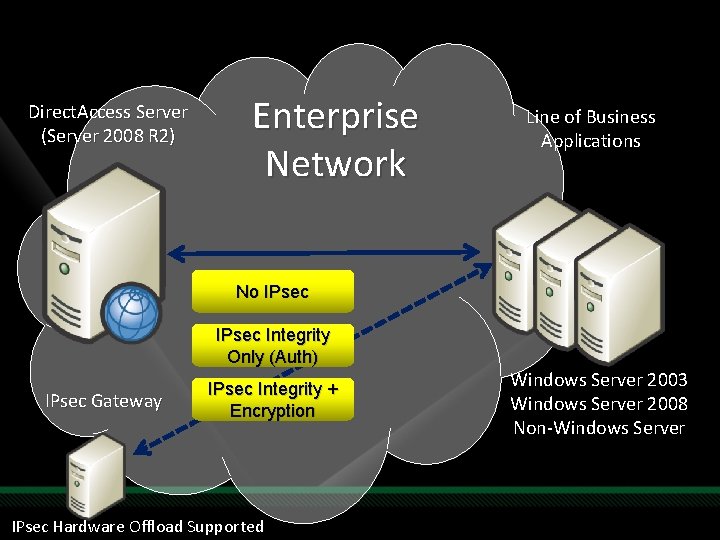
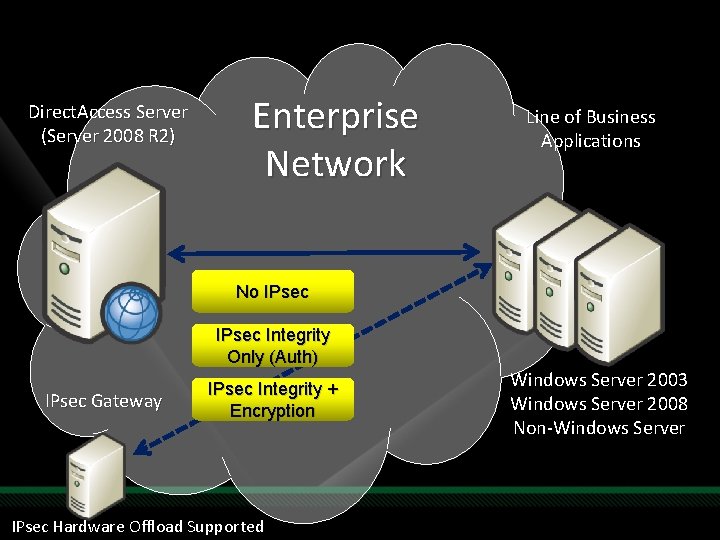
Direct. Access Server (Server 2008 R 2) Enterprise Network Line of Business Applications No IPsec Integrity Only (Auth) IPsec Gateway IPsec Integrity + Encryption IPsec Hardware Offload Supported Windows Server 2003 Windows Server 2008 Non-Windows Server
Deployment Models
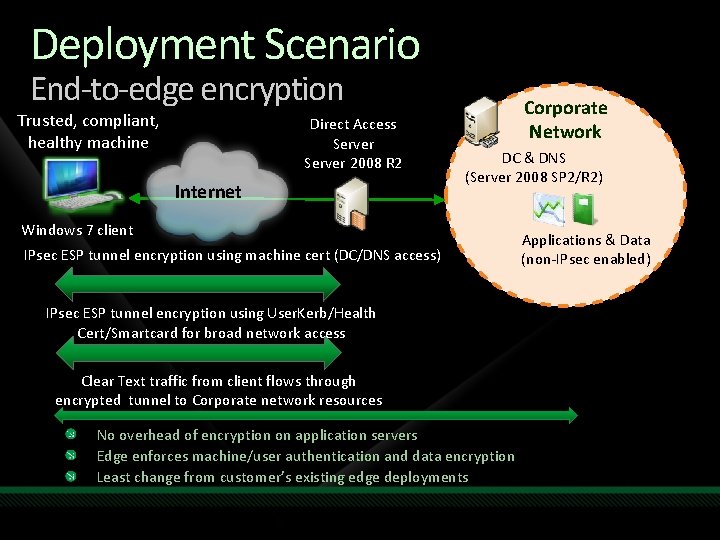
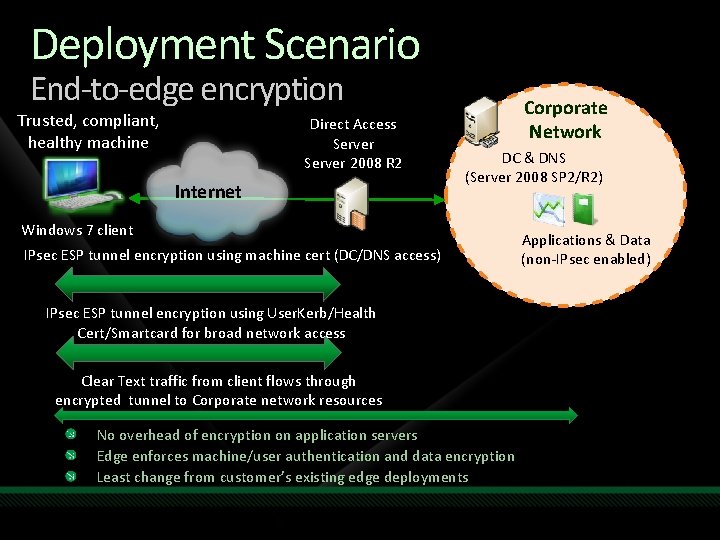
Deployment Scenario End-to-edge encryption Trusted, compliant, healthy machine Direct Access Server 2008 R 2 Internet Corporate Network DC & DNS (Server 2008 SP 2/R 2) Windows 7 client IPsec ESP tunnel encryption using machine cert (DC/DNS access) IPsec ESP tunnel encryption using User. Kerb/Health Cert/Smartcard for broad network access Clear Text traffic from client flows through encrypted tunnel to Corporate network resources No overhead of encryption on application servers Edge enforces machine/user authentication and data encryption Least change from customer’s existing edge deployments Applications & Data (non-IPsec enabled)
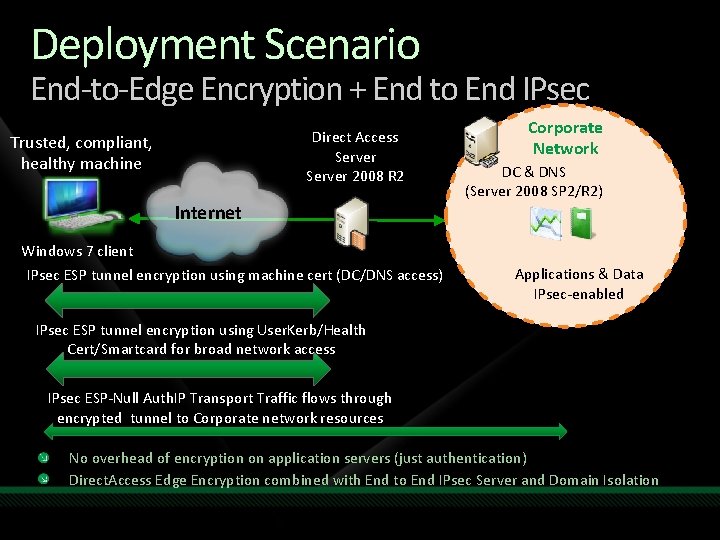
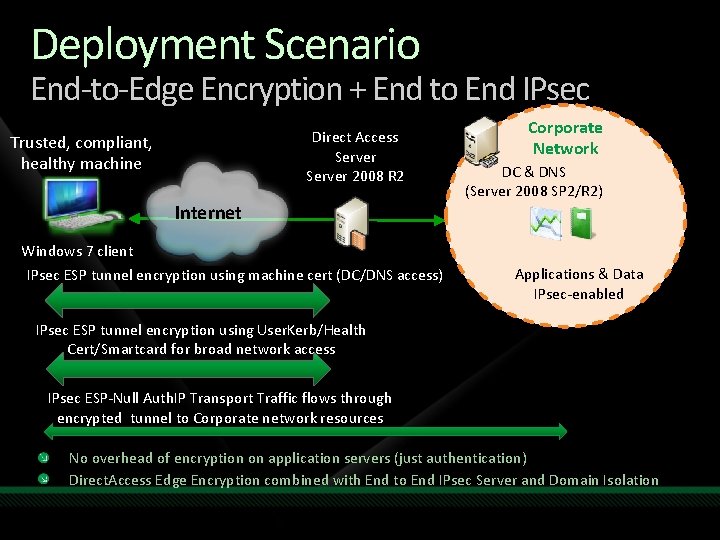
Deployment Scenario End-to-Edge Encryption + End to End IPsec Direct Access Server 2008 R 2 Trusted, compliant, healthy machine Internet Windows 7 client IPsec ESP tunnel encryption using machine cert (DC/DNS access) Corporate Network DC & DNS (Server 2008 SP 2/R 2) Applications & Data IPsec-enabled IPsec ESP tunnel encryption using User. Kerb/Health Cert/Smartcard for broad network access IPsec ESP-Null Auth. IP Transport Traffic flows through encrypted tunnel to Corporate network resources No overhead of encryption on application servers (just authentication) Direct. Access Edge Encryption combined with End to End IPsec Server and Domain Isolation
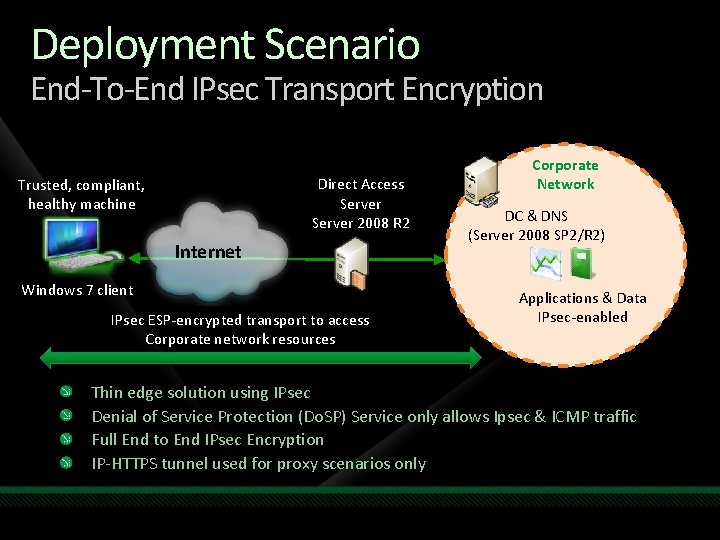
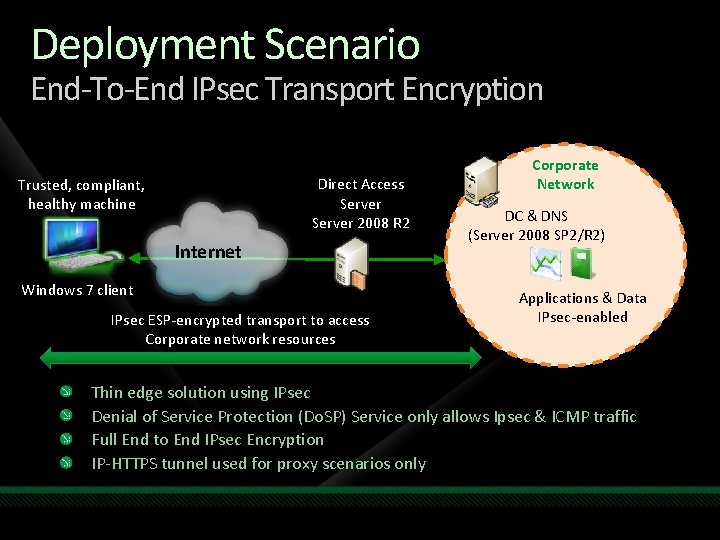
Deployment Scenario End-To-End IPsec Transport Encryption Direct Access Server 2008 R 2 Trusted, compliant, healthy machine Internet Windows 7 client IPsec ESP-encrypted transport to access Corporate network resources Corporate Network DC & DNS (Server 2008 SP 2/R 2) Applications & Data IPsec-enabled Thin edge solution using IPsec Denial of Service Protection (Do. SP) Service only allows Ipsec & ICMP traffic Full End to End IPsec Encryption IP-HTTPS tunnel used for proxy scenarios only
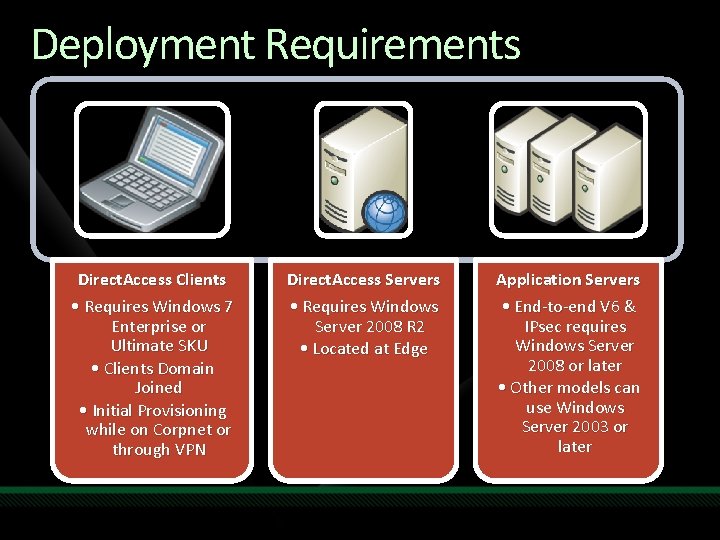
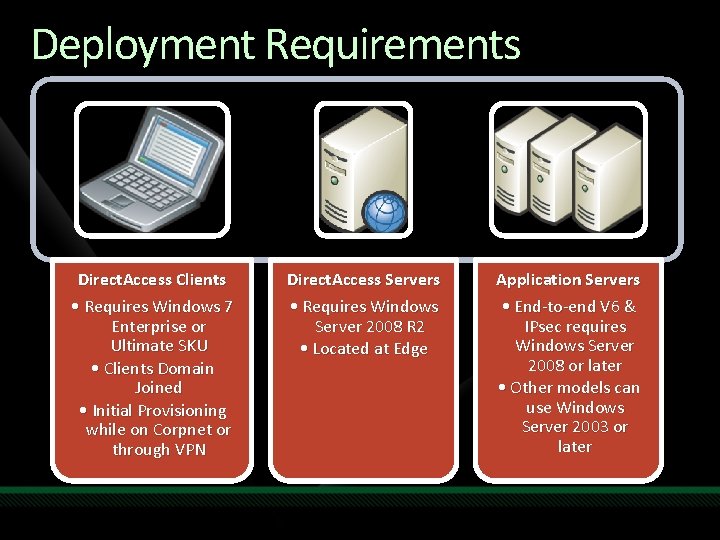
Deployment Requirements Direct. Access Clients • Requires Windows 7 Enterprise or Ultimate SKU • Clients Domain Joined • Initial Provisioning while on Corpnet or through VPN Direct. Access Servers • Requires Windows Server 2008 R 2 • Located at Edge Application Servers • End-to-end V 6 & IPsec requires Windows Server 2008 or later • Other models can use Windows Server 2003 or later
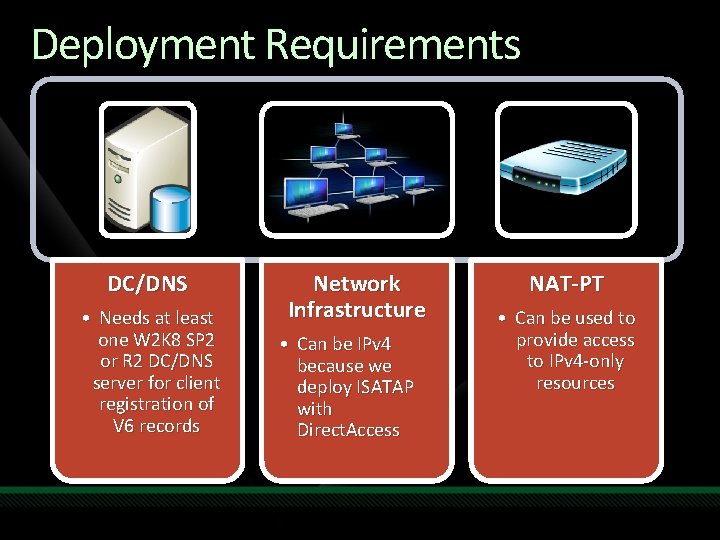
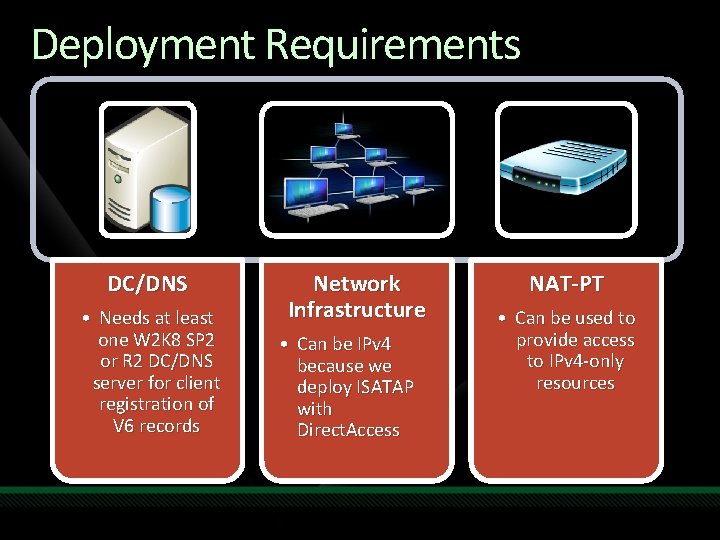
Deployment Requirements DC/DNS • Needs at least one W 2 K 8 SP 2 or R 2 DC/DNS server for client registration of V 6 records Network Infrastructure • Can be IPv 4 because we deploy ISATAP with Direct. Access NAT-PT • Can be used to provide access to IPv 4 -only resources
Name Resolution
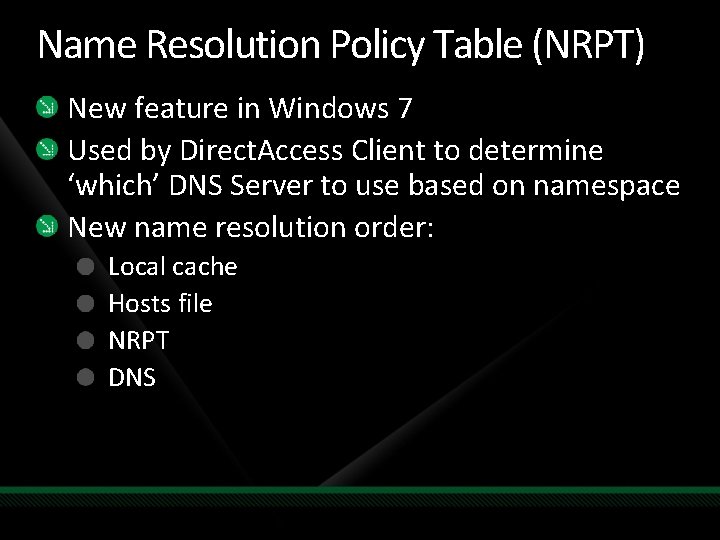
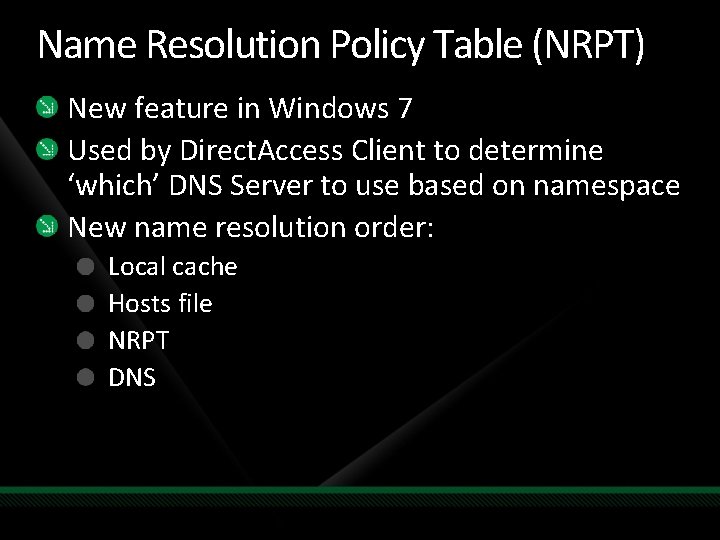
Name Resolution Policy Table (NRPT) New feature in Windows 7 Used by Direct. Access Client to determine ‘which’ DNS Server to use based on namespace New name resolution order: Local cache Hosts file NRPT DNS
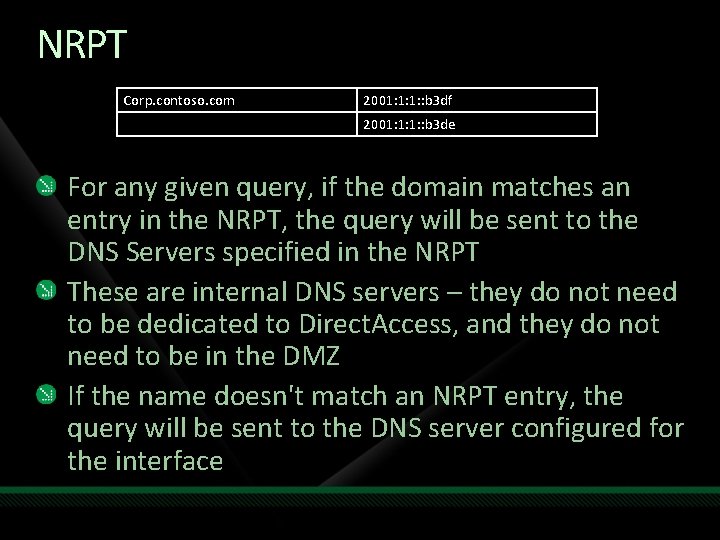
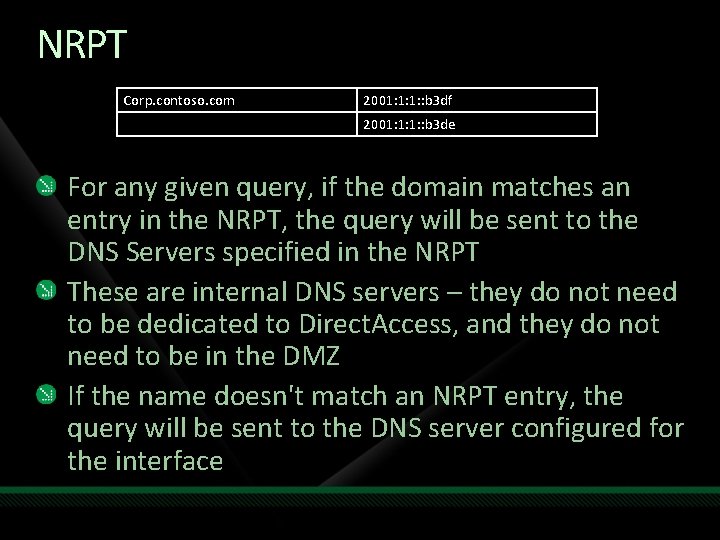
NRPT Corp. contoso. com 2001: 1: 1: : b 3 df 2001: 1: 1: : b 3 de For any given query, if the domain matches an entry in the NRPT, the query will be sent to the DNS Servers specified in the NRPT These are internal DNS servers – they do not need to be dedicated to Direct. Access, and they do not need to be in the DMZ If the name doesn't match an NRPT entry, the query will be sent to the DNS server configured for the interface
Diagnostics
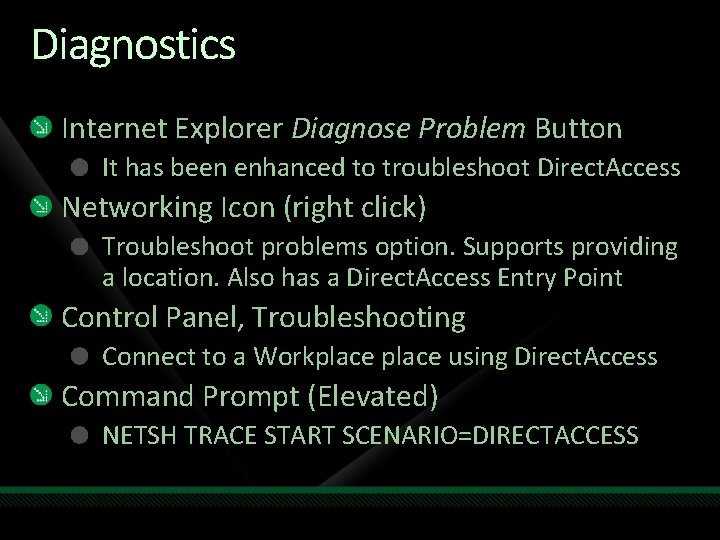
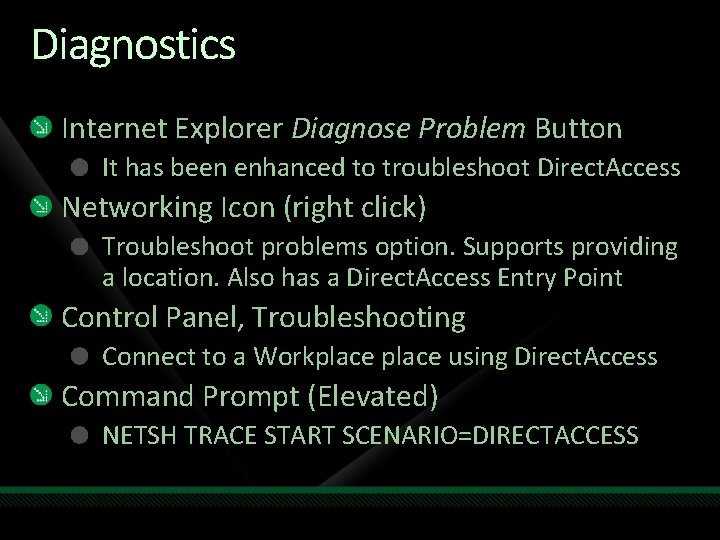
Diagnostics Internet Explorer Diagnose Problem Button It has been enhanced to troubleshoot Direct. Access Networking Icon (right click) Troubleshoot problems option. Supports providing a location. Also has a Direct. Access Entry Point Control Panel, Troubleshooting Connect to a Workplace using Direct. Access Command Prompt (Elevated) NETSH TRACE START SCENARIO=DIRECTACCESS

Supporting Technologies
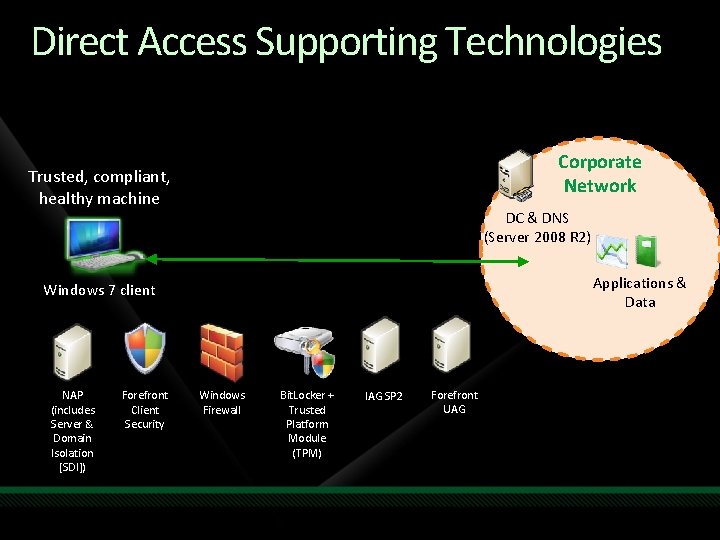
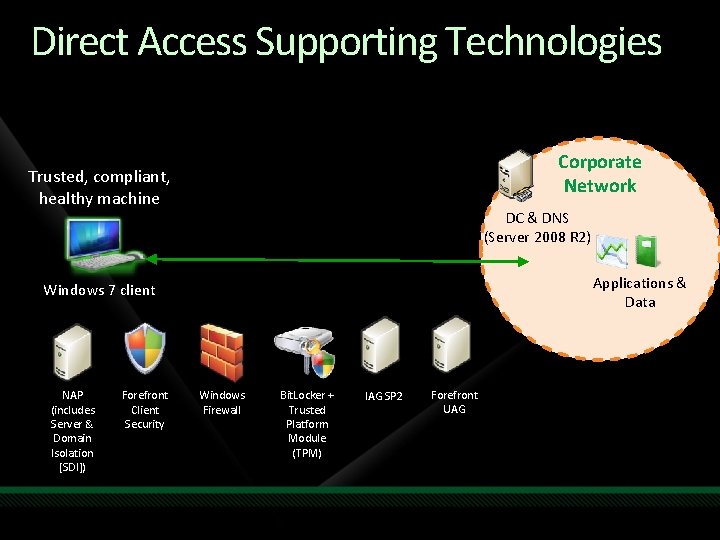
Direct Access Supporting Technologies Corporate Network Trusted, compliant, healthy machine DC & DNS (Server 2008 R 2) Applications & Data Windows 7 client NAP (includes Server & Domain Isolation [SDI]) Forefront Client Security Windows Firewall Bit. Locker + Trusted Platform Module (TPM) IAG SP 2 Forefront UAG
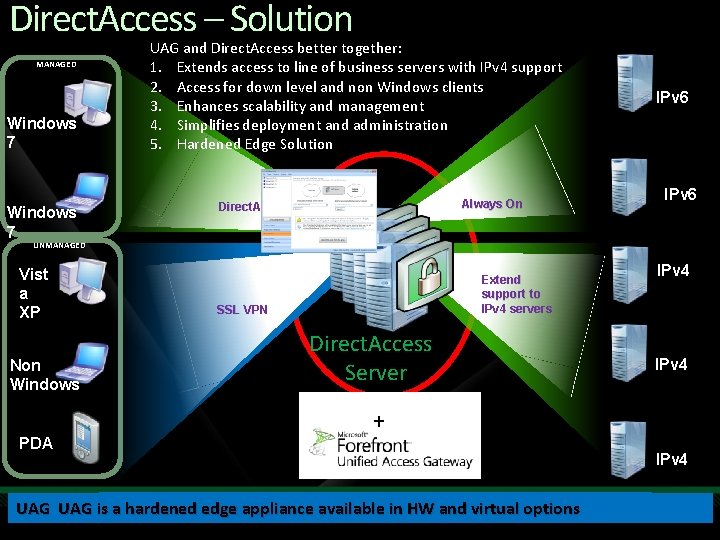
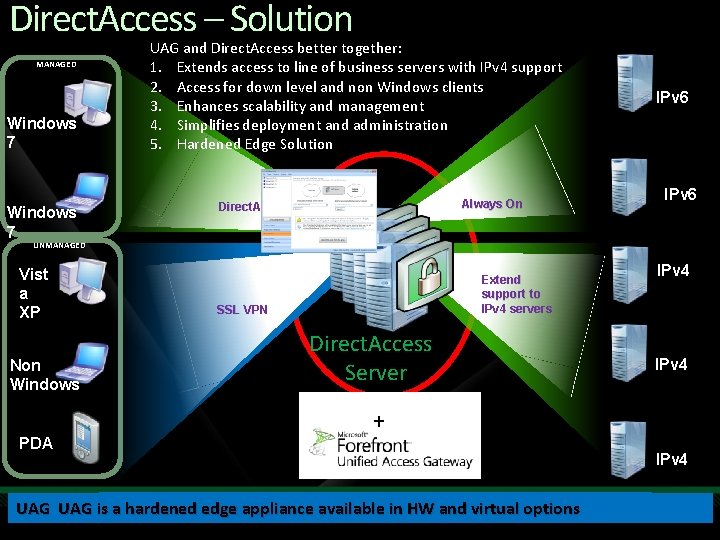
Direct. Access – Solution MANAGED Windows 7 UAG and Direct. Access better together: 1. Extends access to line of business servers with IPv 4 support 2. Access for down level and non Windows clients 3. Enhances scalability and management 4. Simplifies deployment and administration 5. Hardened Edge Solution Always On Direct. Access IPv 6 UNMANAGED Vist a XP Non Windows PDA Extend support to IPv 4 servers SSL VPN Direct. Access Server + + UAG provides access forextends down level and non Windows clients enhances scale and management with integrated LBand andvirtual array capabilities. UAGwizards adoption and access existing infrastructure UAG isimproves a hardened edge available into. HW options UAG uses and tools toappliance simplify deployments and ongoing management. IPv 4
Summary Call-to-action Windows Server 2008 R 2 offers great innovation for your Anywhere Access infrastructure Learn more about Direct Access Start deploying Windows Server 2008 now to get ready http: //www. microsoft. com/directaccess

question & answer

Resources Tech·Ed Africa 2009 sessions will be made available for download the week after the event from: www. tech-ed. co. za www. microsoft. com/teched www. microsoft. com/learning International Content & Community Microsoft Certification & Training Resources http: //microsoft. com/technet http: //microsoft. com/msdn Resources for IT Professionals Resources for Developers

10 pairs of MP 3 sunglasses to be won Complete a session evaluation and enter to win!
© 2009 Microsoft Corporation. All rights reserved. Microsoft, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U. S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION.