Registry Analysis Using regedit exe System Information Autostart
- Slides: 37
Registry Analysis • Using regedit. exe – System Information – Autostart locations – USB Removable Storage Devices – Mounted Devices – Finding Users – User Activity – Restore Points
System Information • Located in the Current Control Set • If the systemm is not active must find the Control Set that was current • • Time zone Shares Audit policy Wireless SSIDs
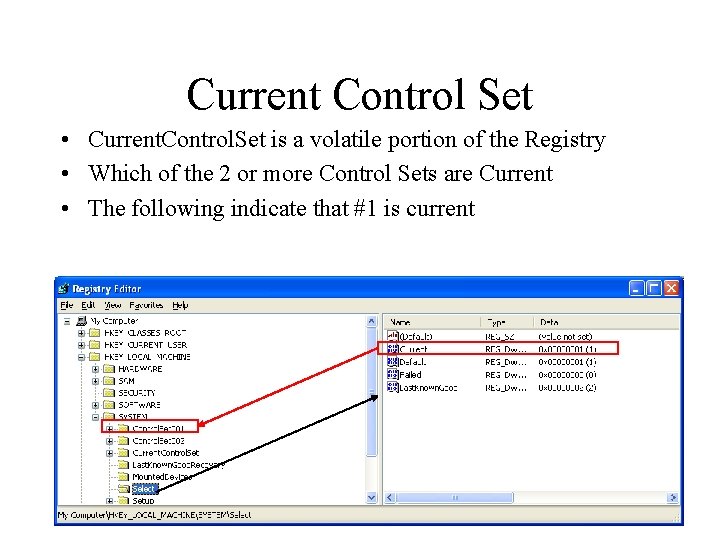
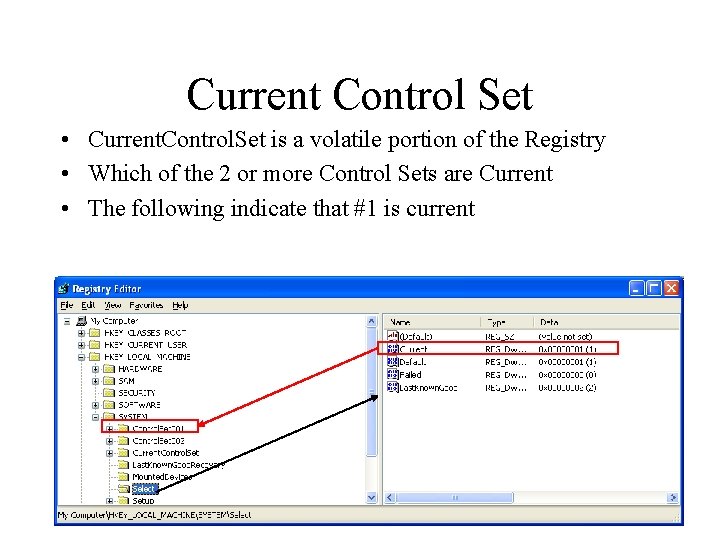
Current Control Set • Current. Control. Set is a volatile portion of the Registry • Which of the 2 or more Control Sets are Current • The following indicate that #1 is current
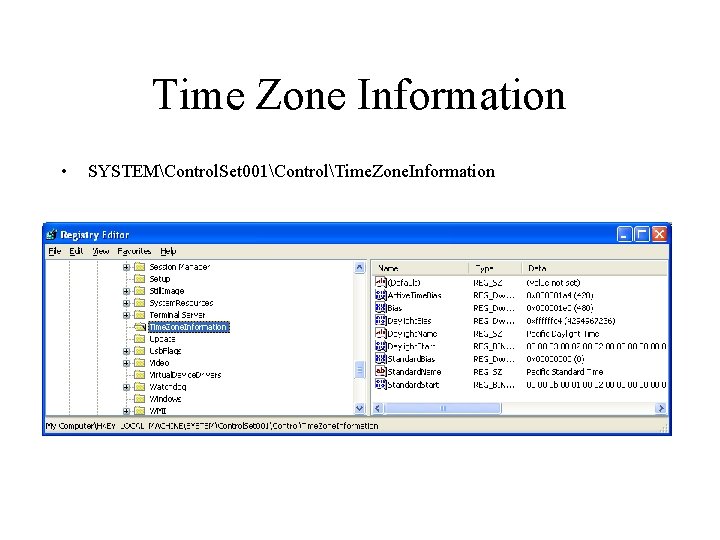
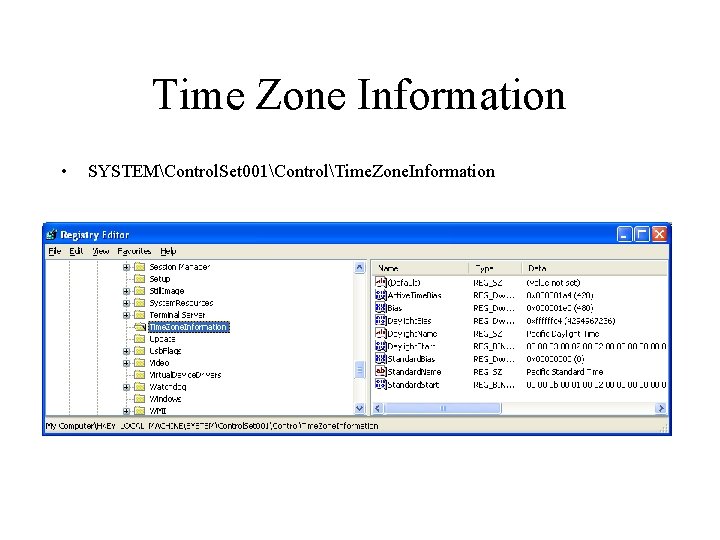
Time Zone Information • SYSTEMControl. Set 001ControlTime. Zone. Information
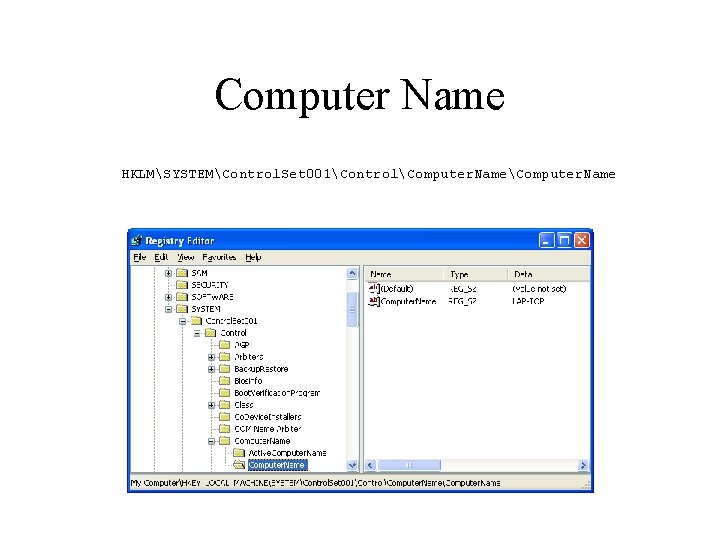
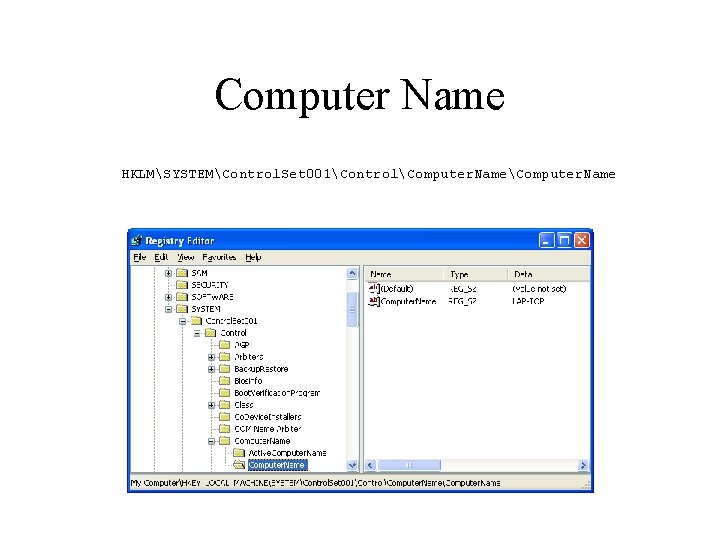
Computer Name HKLMSYSTEMControl. Set 001ControlComputer. Name
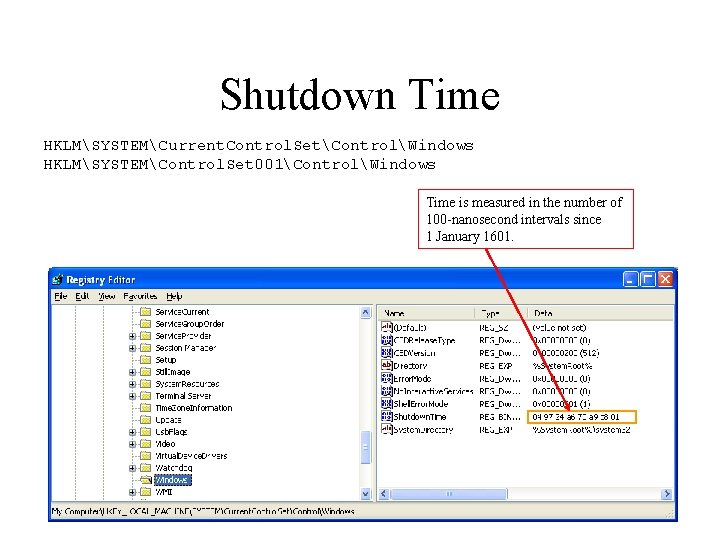
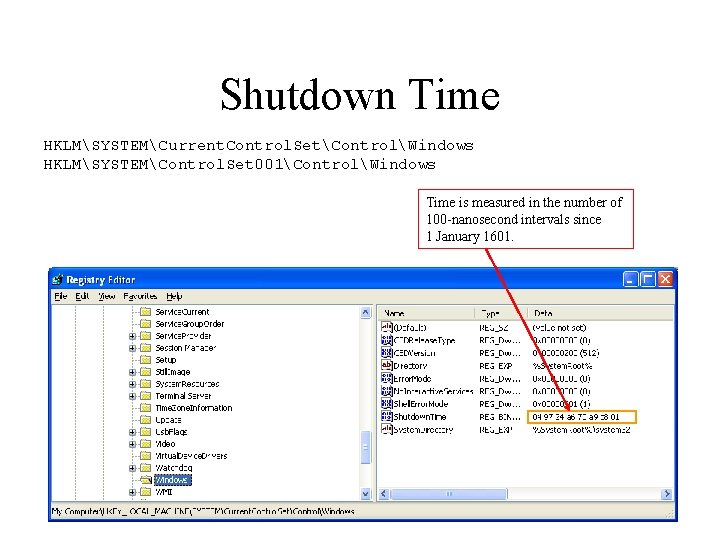
Shutdown Time HKLMSYSTEMCurrent. Control. SetControlWindows HKLMSYSTEMControl. Set 001ControlWindows Time is measured in the number of 100 -nanosecond intervals since 1 January 1601.
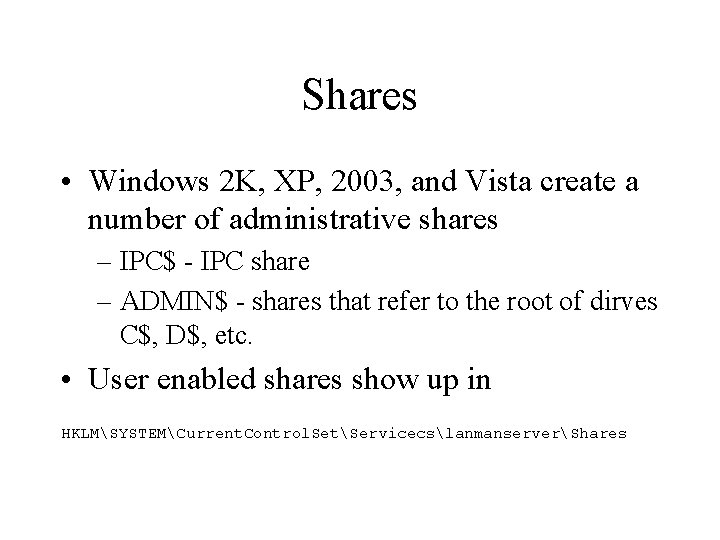
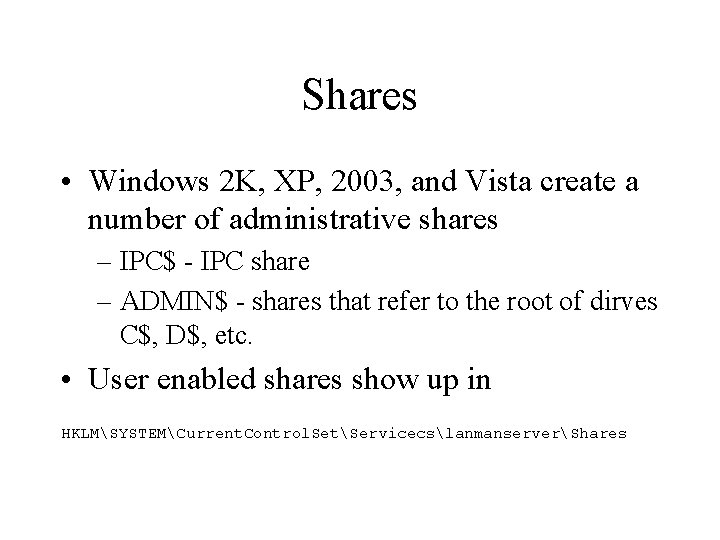
Shares • Windows 2 K, XP, 2003, and Vista create a number of administrative shares – IPC$ - IPC share – ADMIN$ - shares that refer to the root of dirves C$, D$, etc. • User enabled shares show up in HKLMSYSTEMCurrent. Control. SetServicecslanmanserverShares
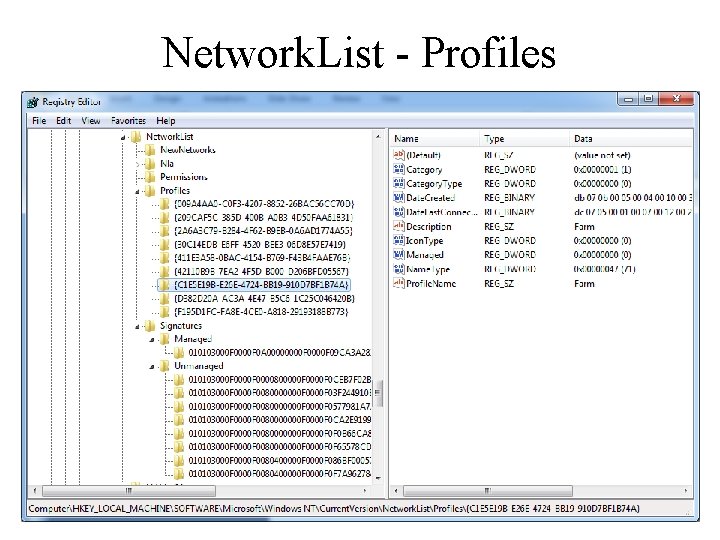
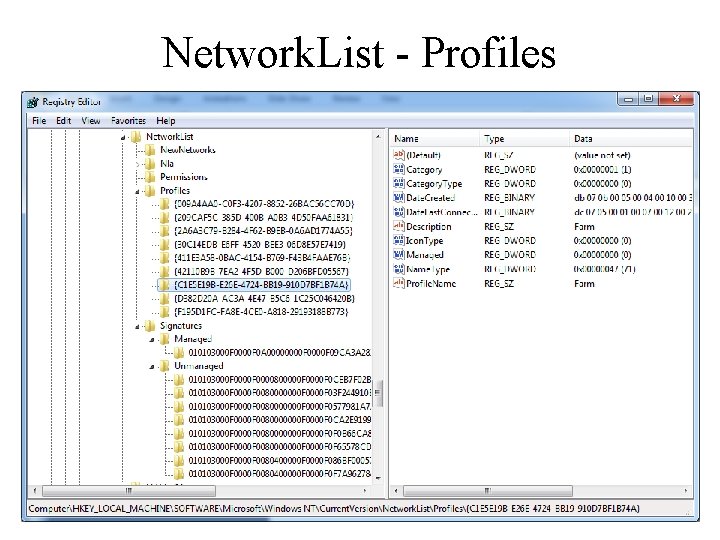
Network. List - Profiles
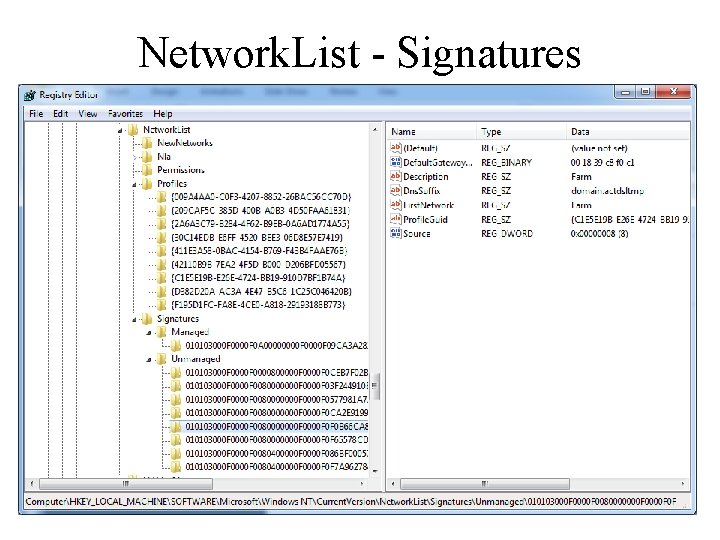
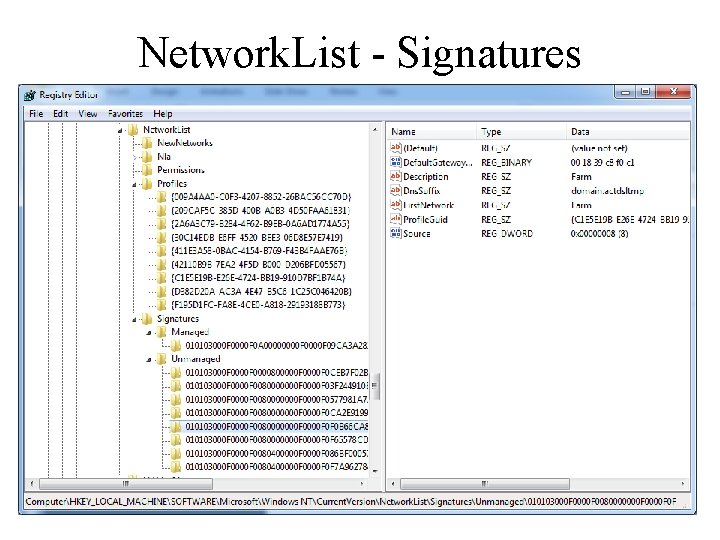
Network. List - Signatures
Wireless SSIDs • XP Laptops maintain a list of service set IDs • The GUID is associated with the wireless interface • Under the Static#000 x lists all of the SSIDs connected
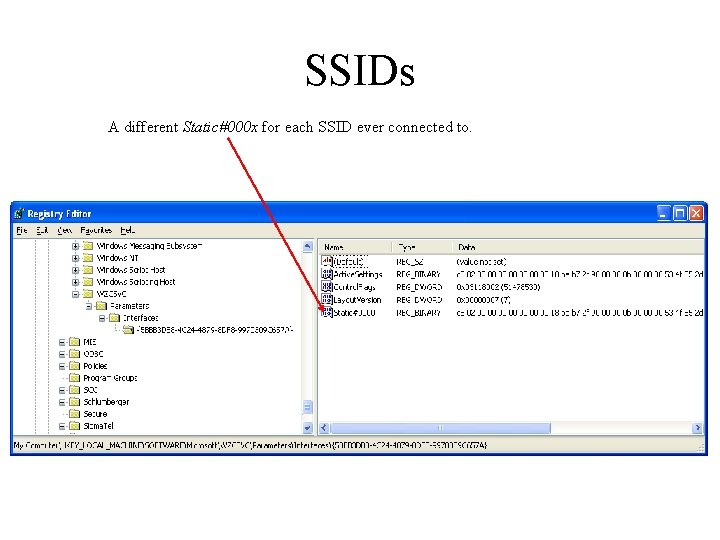
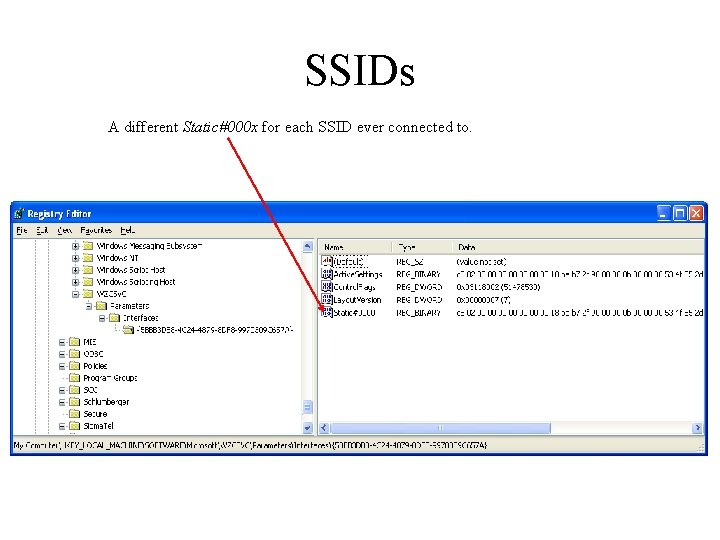
SSIDs A different Static#000 x for each SSID ever connected to.
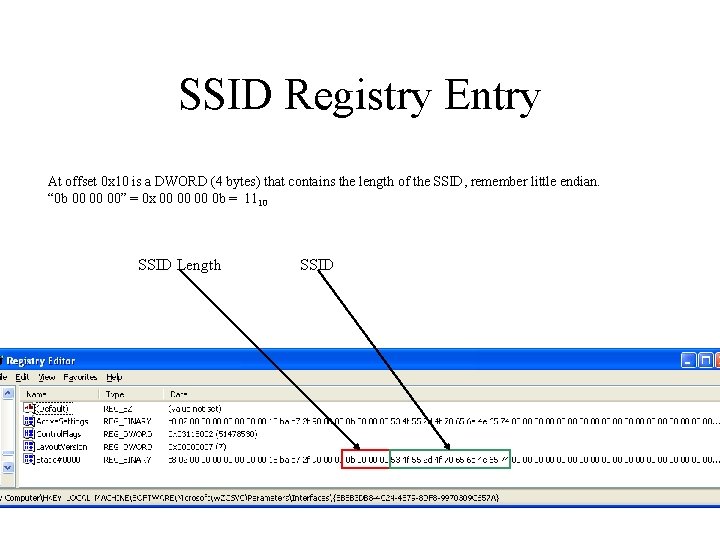
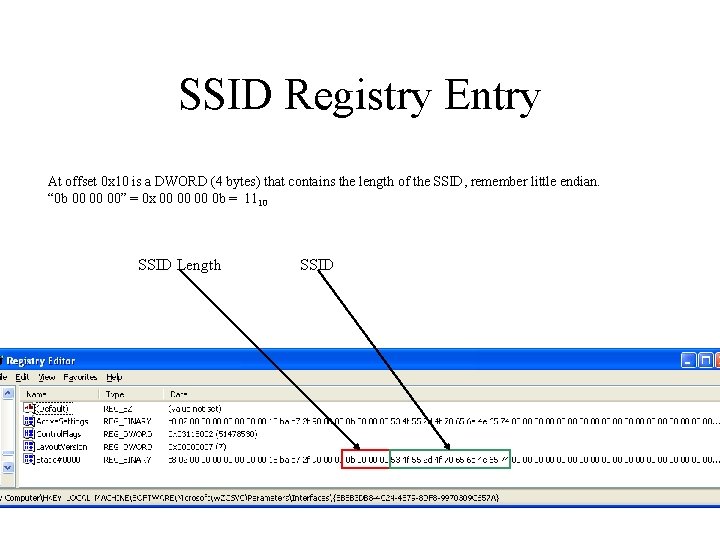
SSID Registry Entry At offset 0 x 10 is a DWORD (4 bytes) that contains the length of the SSID, remember little endian. “ 0 b 00 00 00” = 0 x 00 00 00 0 b = 1110 SSID Length SSID
Autostarts • Applications that are launched without any interaction from the user • Often at boot time • Occasionally upon launch of a app.
Autostart Locations • Auto-start extensibility points (ASEPs) • Registry locations • • HKLMSOFTWAREMicrosoftWindowsCurrent. VersionRun HKCUSOFTWAREMicrosoftWindowsCurrent. VersionRun And elsewhere All over the place
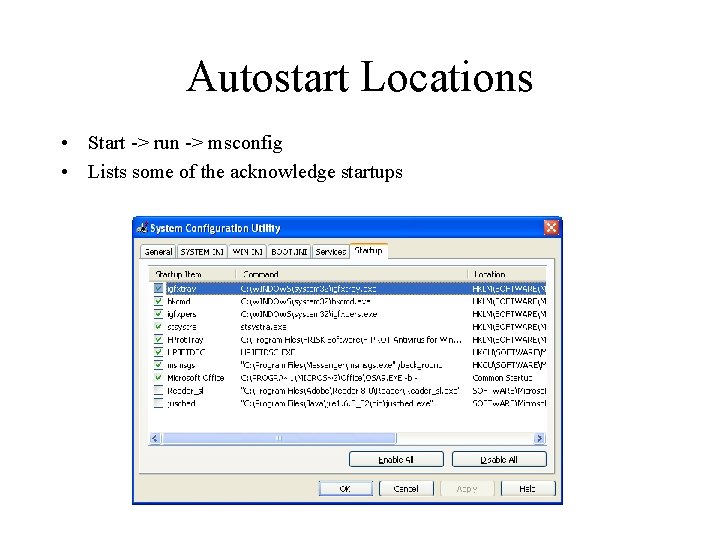
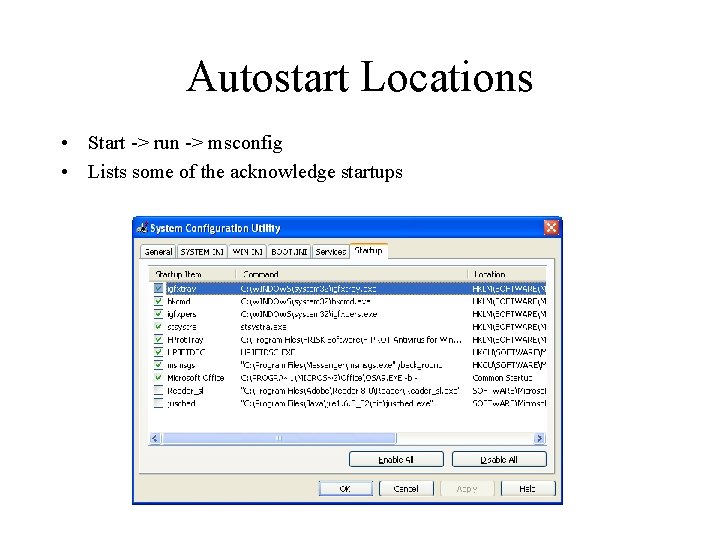
Autostart Locations • Start -> run -> msconfig • Lists some of the acknowledge startups
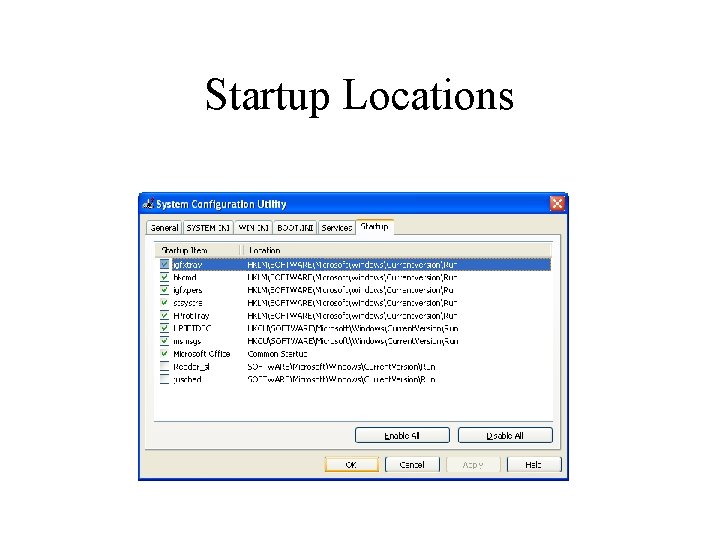
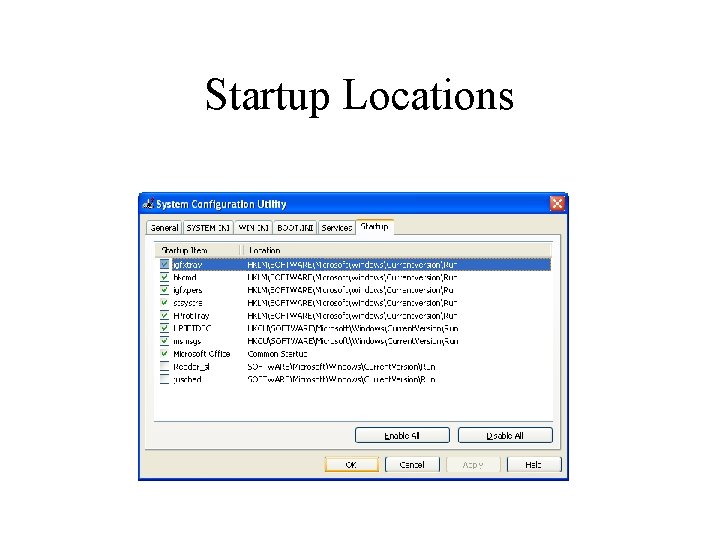
Startup Locations
Other Startup Locations • System boot • User Login • User Activity • See Carvey’s Ch 4 spreadsheet for more locations
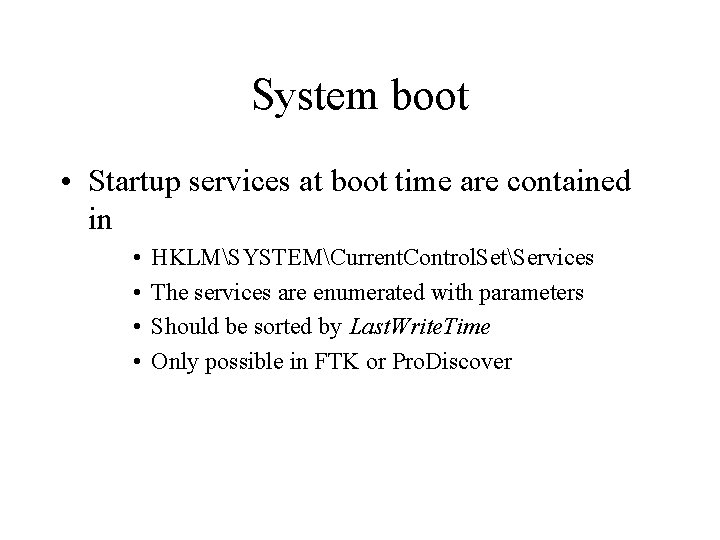
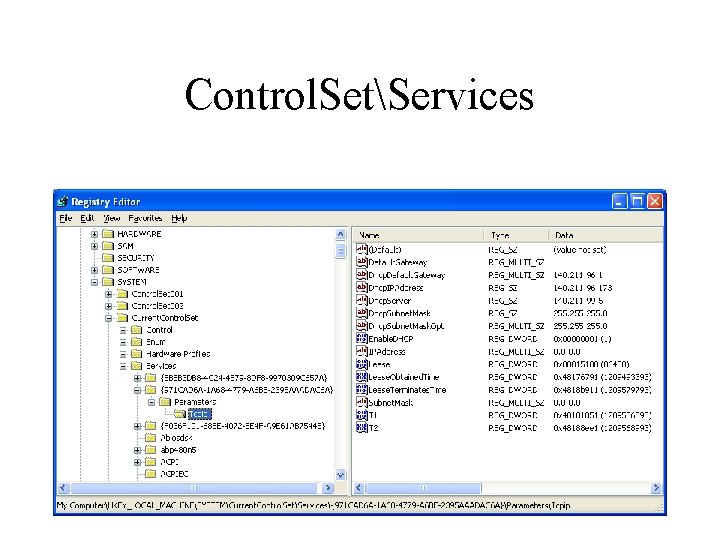
System boot • Startup services at boot time are contained in • • HKLMSYSTEMCurrent. Control. SetServices The services are enumerated with parameters Should be sorted by Last. Write. Time Only possible in FTK or Pro. Discover
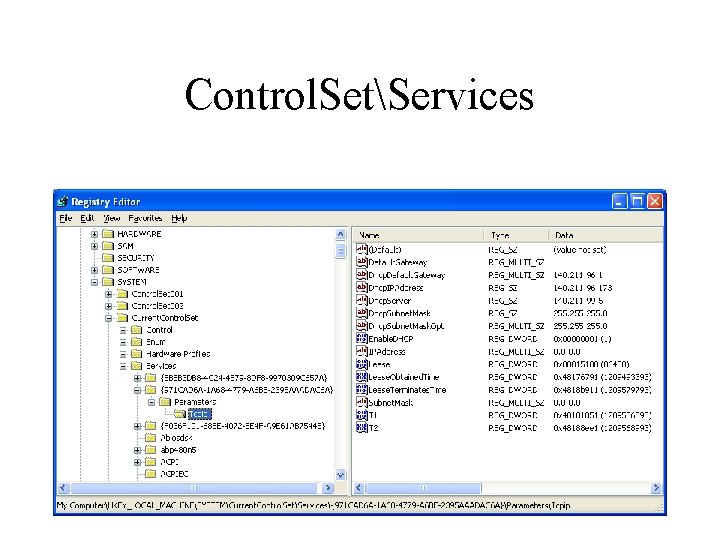
Control. SetServices
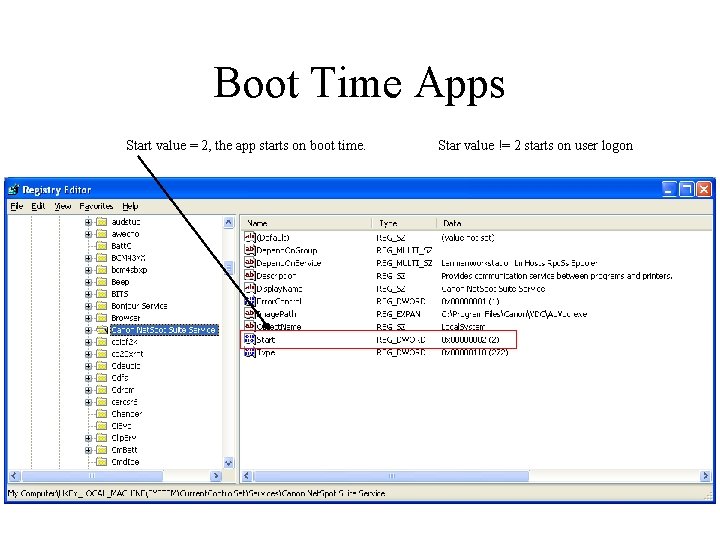
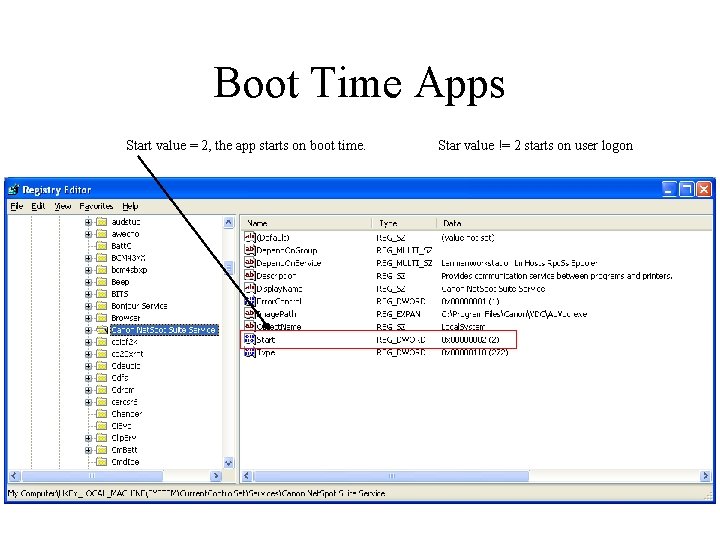
Boot Time Apps Start value = 2, the app starts on boot time. Star value != 2 starts on user logon
Evil Start Time Services • Generally Last. Write times should be about the same time the system was built. • Later dates would suggest that an intruder of sysadmin was altering the boot time sequence
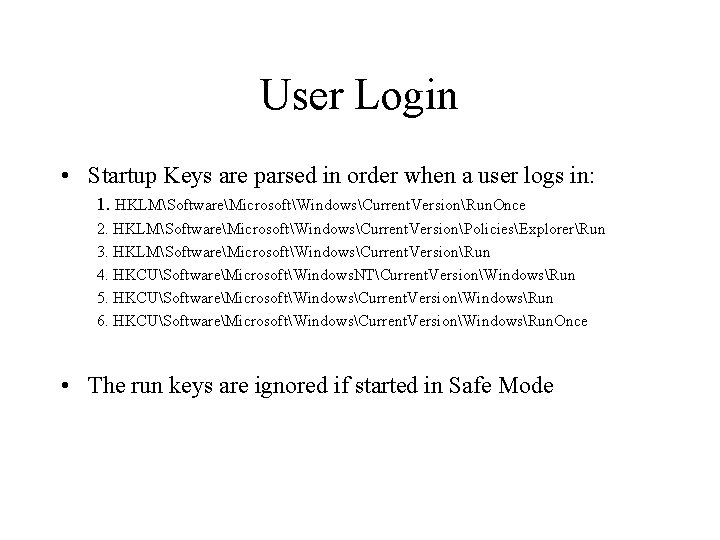
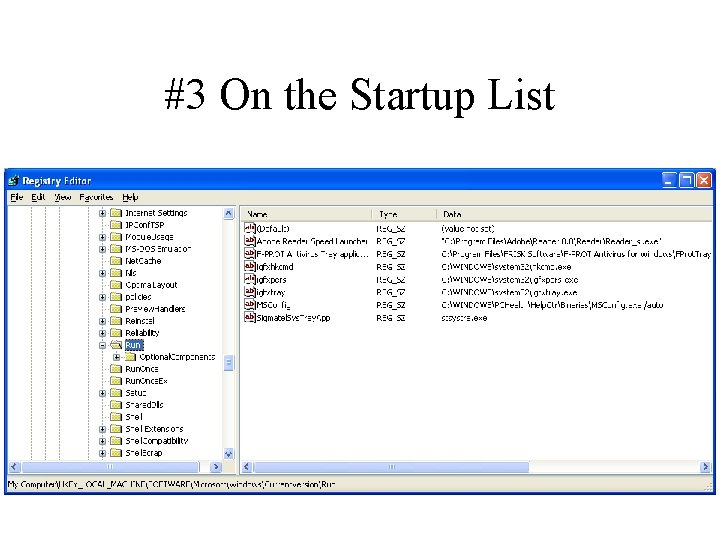
User Login • Startup Keys are parsed in order when a user logs in: 1. HKLMSoftwareMicrosoftWindowsCurrent. VersionRun. Once 2. HKLMSoftwareMicrosoftWindowsCurrent. VersionPoliciesExplorerRun 3. HKLMSoftwareMicrosoftWindowsCurrent. VersionRun 4. HKCUSoftwareMicrosoftWindows. NTCurrent. VersionWindowsRun 5. HKCUSoftwareMicrosoftWindowsCurrent. VersionWindowsRun 6. HKCUSoftwareMicrosoftWindowsCurrent. VersionWindowsRun. Once • The run keys are ignored if started in Safe Mode
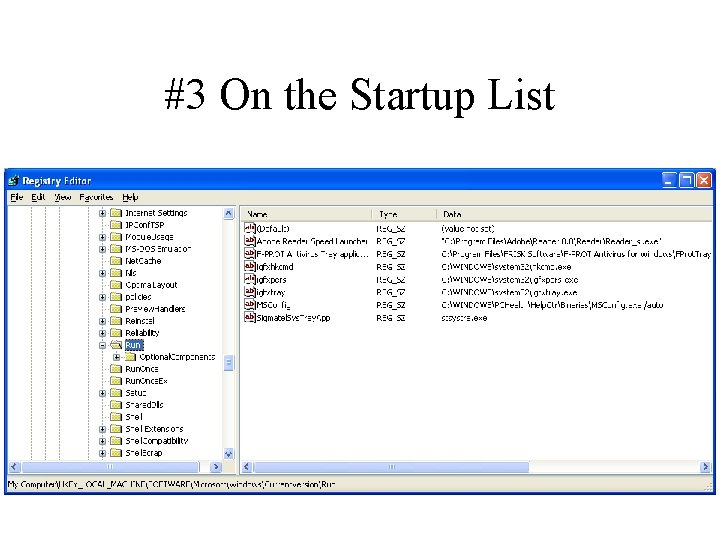
#3 On the Startup List
User Activity • On user action certain registry keys are accessed • Keys for other Classes of files control what happens when that file is opened • Or when the file is double-clicked
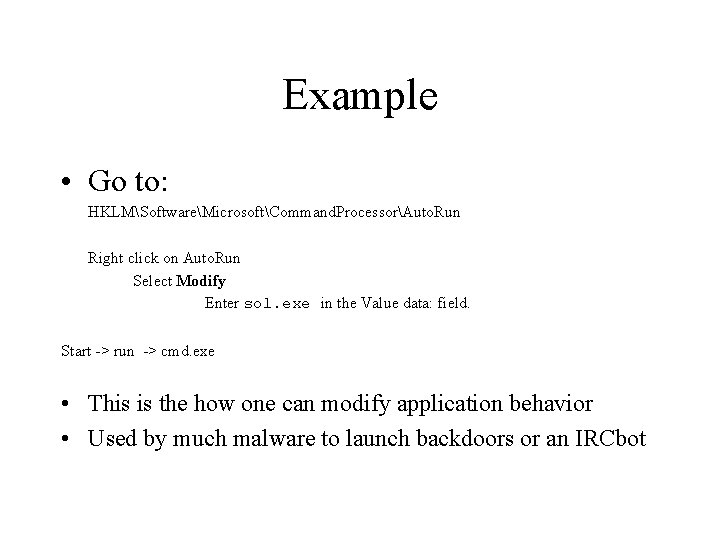
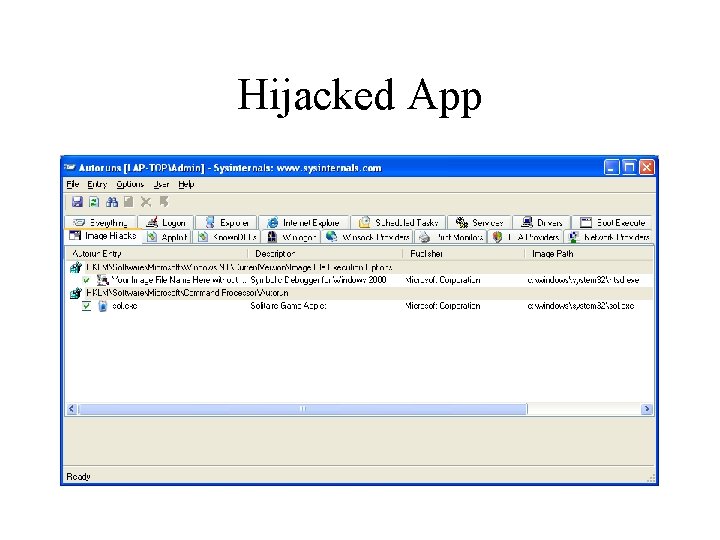
Example • Go to: HKLMSoftwareMicrosoftCommand. ProcessorAuto. Run Right click on Auto. Run Select Modify Enter sol. exe in the Value data: field. Start -> run -> cmd. exe • This is the how one can modify application behavior • Used by much malware to launch backdoors or an IRCbot
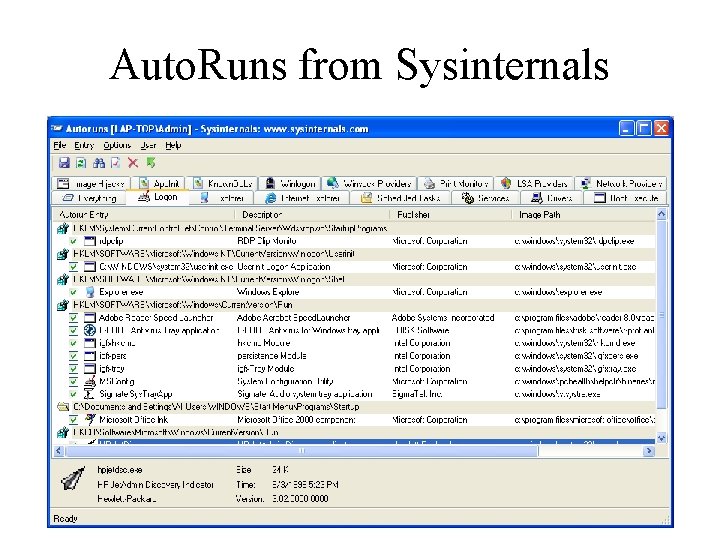
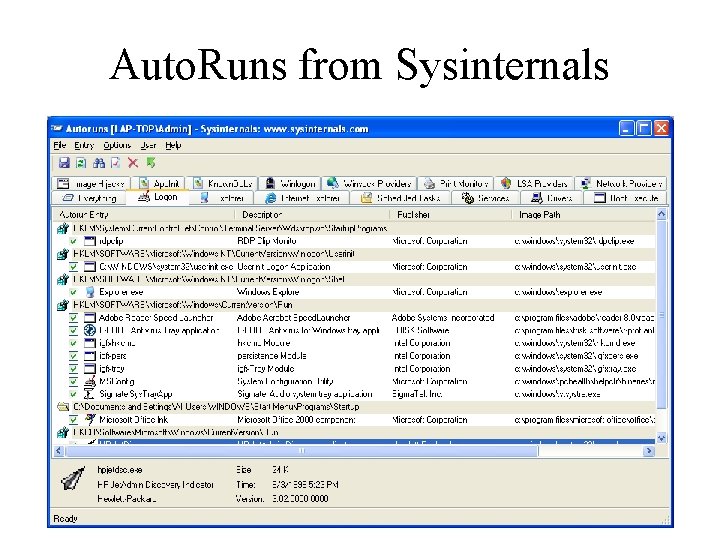
Auto. Runs from Sysinternals
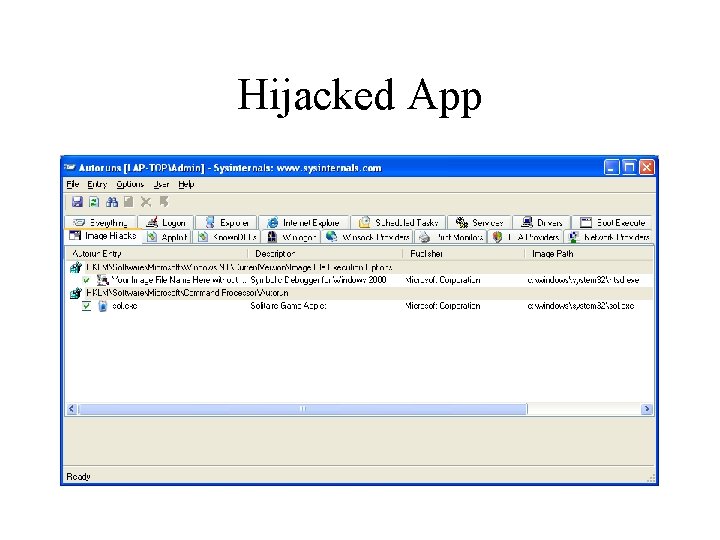
Hijacked App
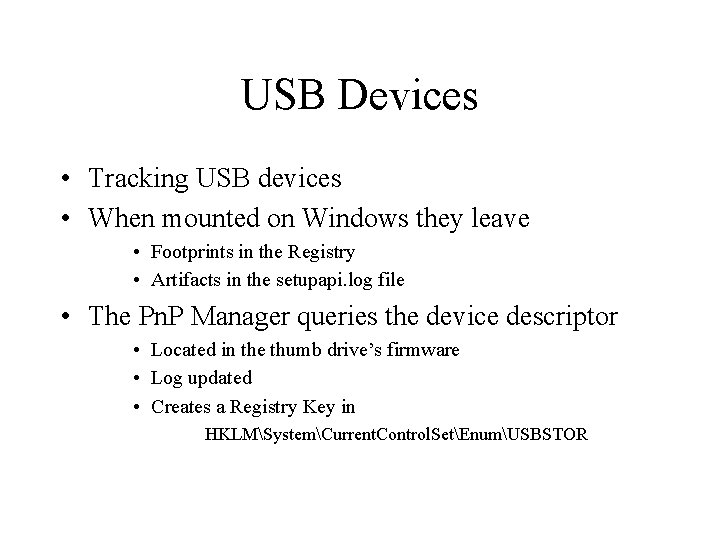
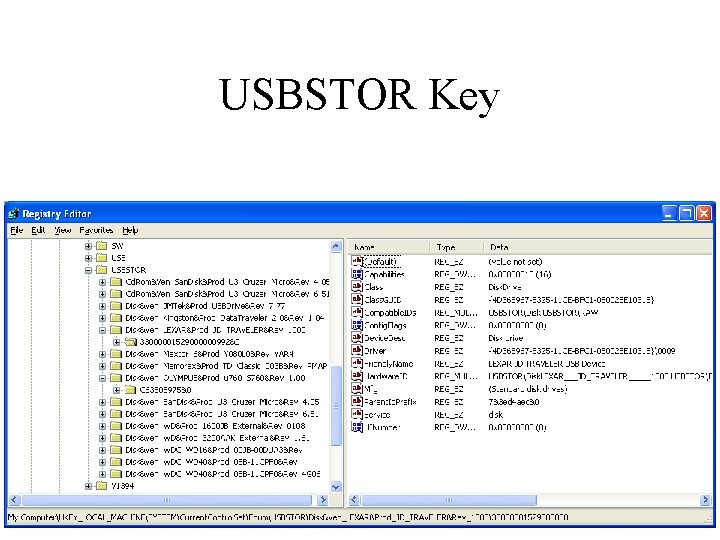
USB Devices • Tracking USB devices • When mounted on Windows they leave • Footprints in the Registry • Artifacts in the setupapi. log file • The Pn. P Manager queries the device descriptor • Located in the thumb drive’s firmware • Log updated • Creates a Registry Key in HKLMSystemCurrent. Control. SetEnumUSBSTOR
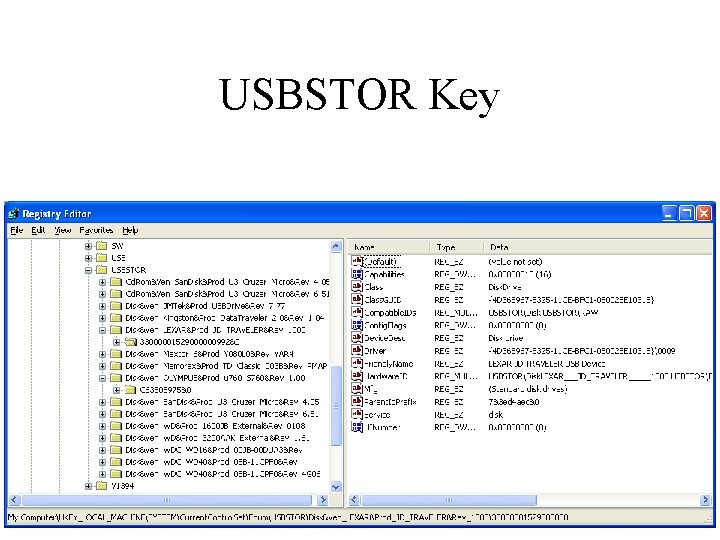
USBSTOR Key
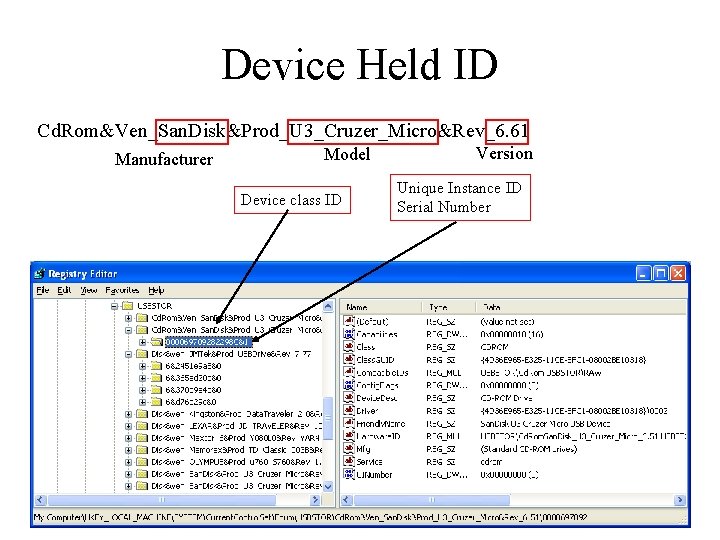
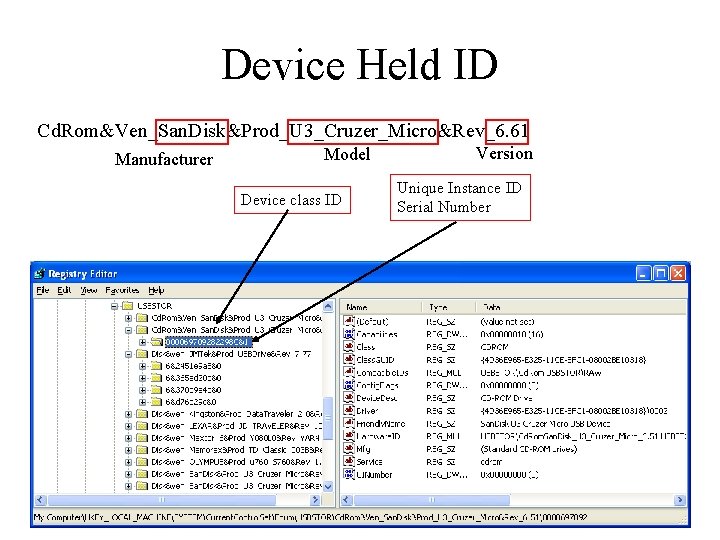
Device Held ID Cd. Rom&Ven_San. Disk&Prod_U 3_Cruzer_Micro&Rev_6. 61 Manufacturer Model Device class ID Version Unique Instance ID Serial Number
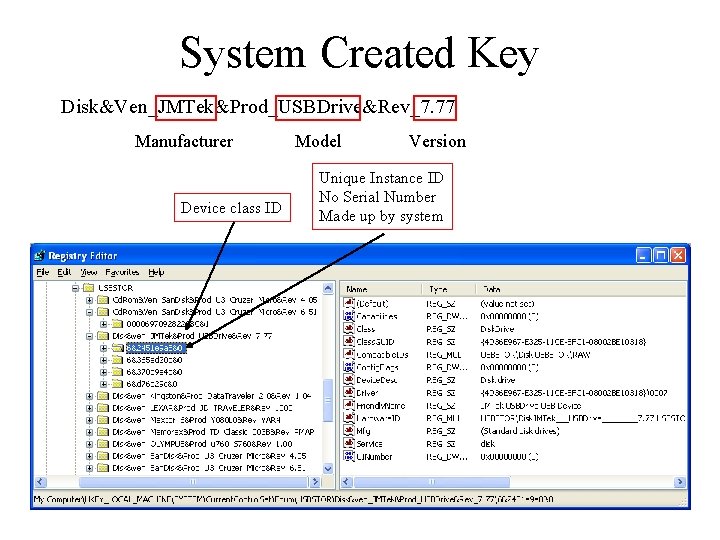
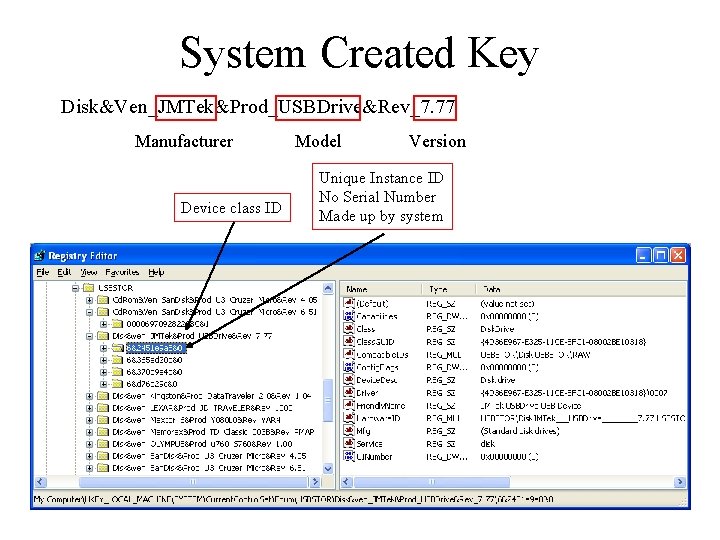
System Created Key Disk&Ven_JMTek&Prod_USBDrive&Rev_7. 77 Manufacturer Device class ID Model Version Unique Instance ID No Serial Number Made up by system
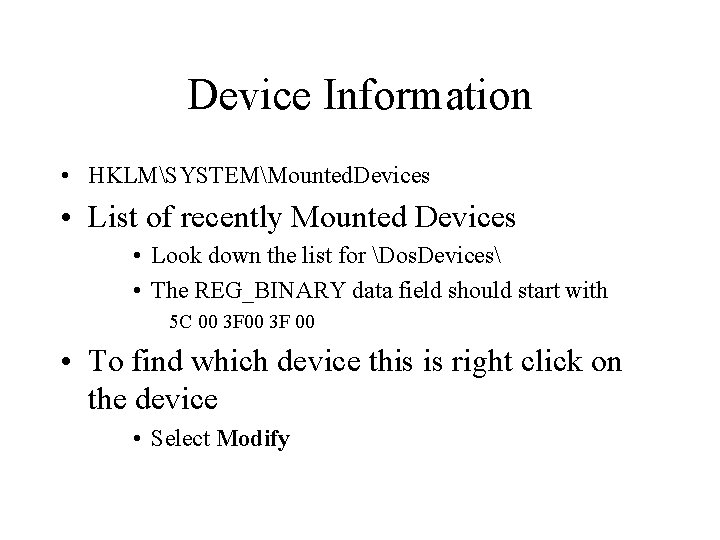
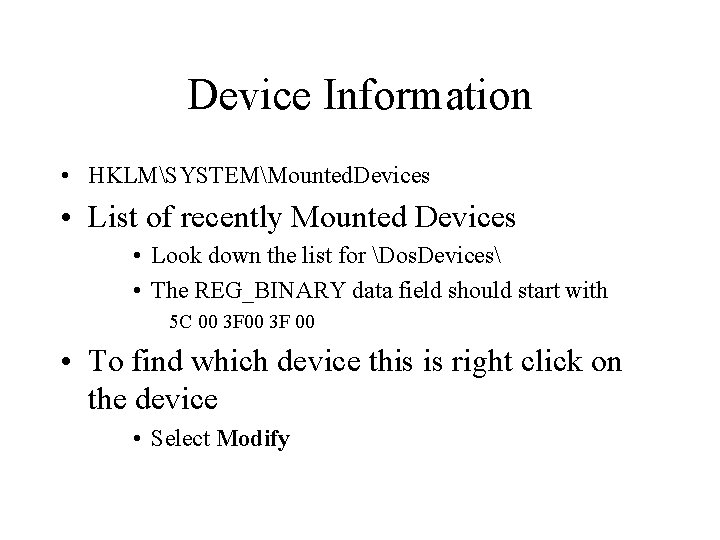
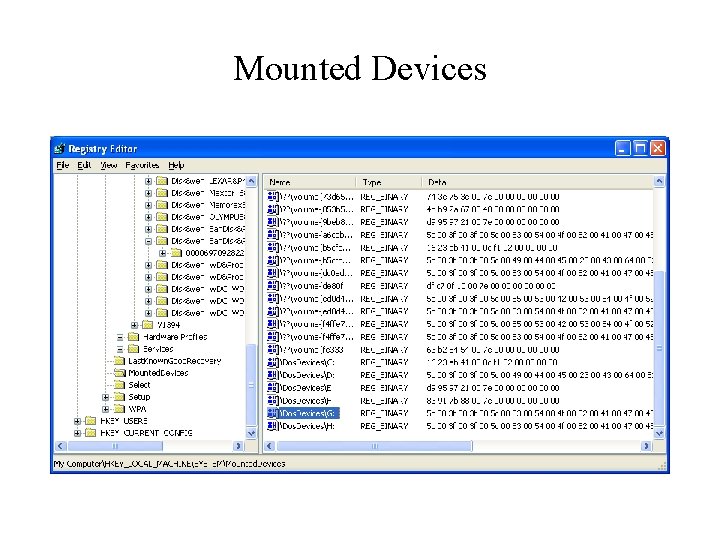
Device Information • HKLMSYSTEMMounted. Devices • List of recently Mounted Devices • Look down the list for Dos. Devices • The REG_BINARY data field should start with 5 C 00 3 F 00 • To find which device this is right click on the device • Select Modify
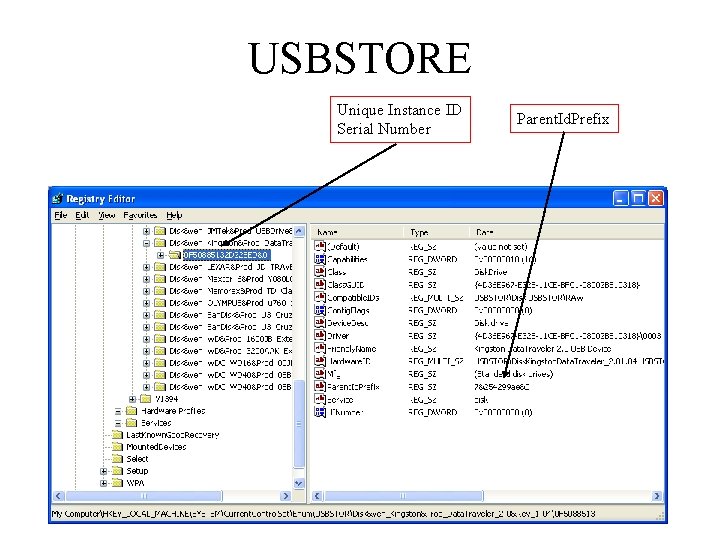
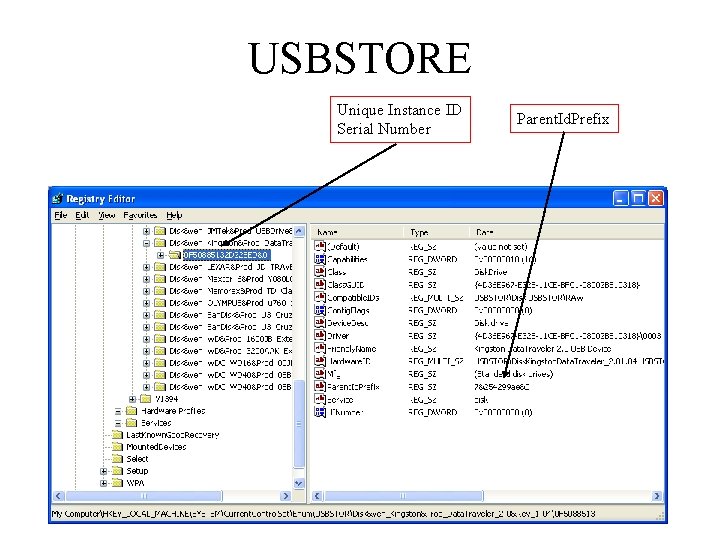
USBSTORE Unique Instance ID Serial Number Parent. Id. Prefix
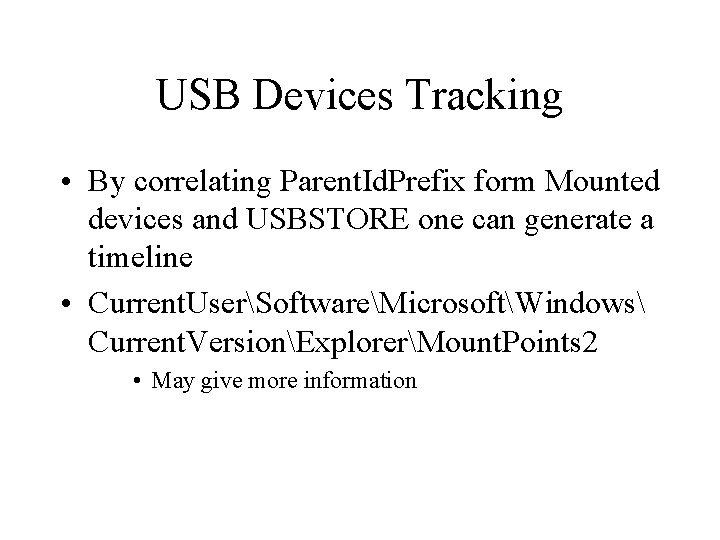
USB Devices Tracking • By correlating Parent. Id. Prefix form Mounted devices and USBSTORE one can generate a timeline • Current. UserSoftwareMicrosoftWindows Current. VersionExplorerMount. Points 2 • May give more information
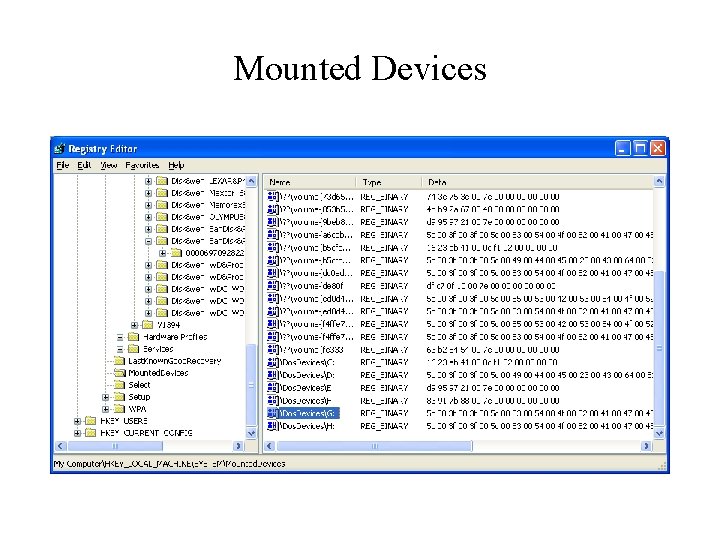
Mounted Devices
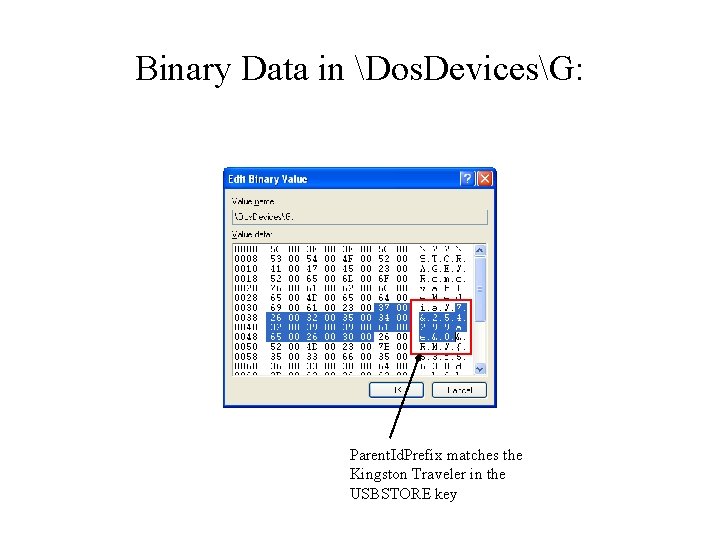
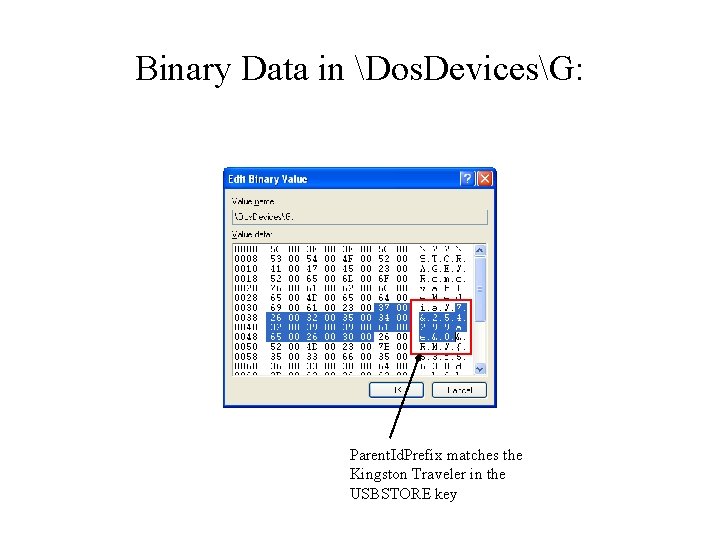
Binary Data in Dos. DevicesG: Parent. Id. Prefix matches the Kingston Traveler in the USBSTORE key
Research Topic • USB devices • Some USB Devices have a Device ID, others do not • Some generate a Parent. Id. Prefix others do not • Some Correlate to the Mounted. Devices ID others do not • Sort it out • Use references to the Microsoft Knowledge Base