Refactoring Support Based on Code Clone Analysis Yoshiki
コードクローン解析に基づくリファクタリング支援 (Refactoring Support Based on Code Clone Analysis) 肥後 芳樹,神谷 年洋,楠本 真二,井上 克郎 (Yoshiki Higo, Toshihiro Kamiya, Shinji Kusumoto, Katsuro Inoue) 大阪大学 大学院情報科学研究科 (Graduate School of Information Science and Technology, Osaka University) 科学技術振興機構 さきがけ (Presto, Japan Science and Technology Agency) {y-higo, kamiya, kusumoto, inoue}@ist. osaka-u. ac. jp Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 1
Background What is code clone? a code fragment that has identical or similar fragments in the same or different files in a system introduced in the source program because of various reasons such as reusing code by `copy-and-paste’ makes software maintenance more difficult. copy-and-paste copy-andpaste Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 2
Requirements for Code Clone Detection Appropriate code clones should be detected in compliance with demands. To understand the amount and distribution of code clones, it is desirable to detect all code clones To remove code clones (Restructuring or Refactoring), it is useful to detect code clones that can be removed, and also removing them improves software maintainability Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 3
Research Objective and Approach We aim to extract code clones which can be easily refactored Approach To detect code clones efficiently, we use a code clone detection tool, CCFinder. Then, we extract the specific code clones easily refactored and provide applicable refactoring patterns for the code clones. Finally, we develop a refactoring support tool and apply it to an open source program. Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 4
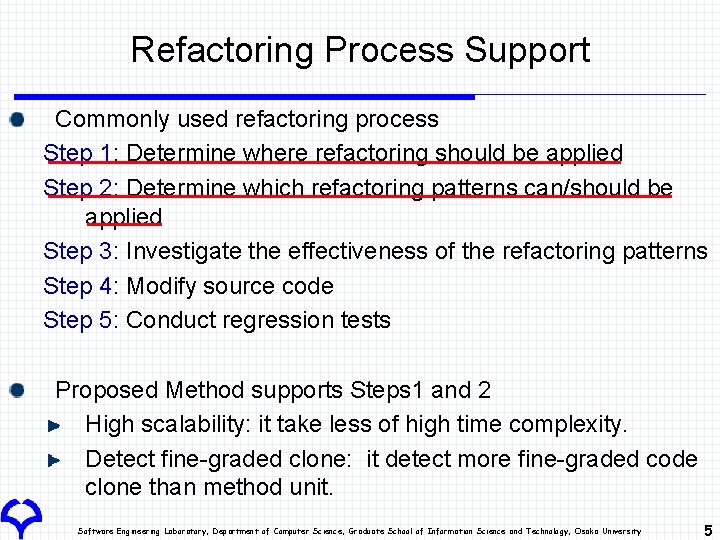
Refactoring Process Support Commonly used refactoring process Step 1: Determine where refactoring should be applied Step 2: Determine which refactoring patterns can/should be applied Step 3: Investigate the effectiveness of the refactoring patterns Step 4: Modify source code Step 5: Conduct regression tests Proposed Method supports Steps 1 and 2 High scalability: it take less of high time complexity. Detect fine-graded clone: it detect more fine-graded code clone than method unit. Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 5
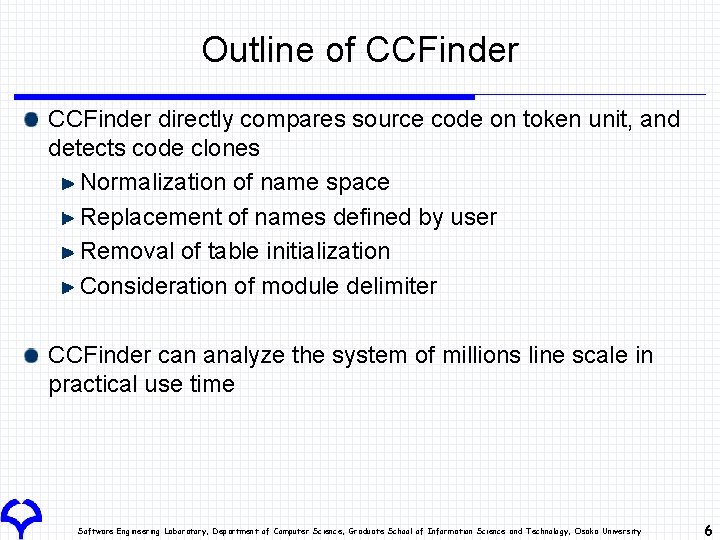
Outline of CCFinder directly compares source code on token unit, and detects code clones Normalization of name space Replacement of names defined by user Removal of table initialization Consideration of module delimiter CCFinder can analyze the system of millions line scale in practical use time Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 6
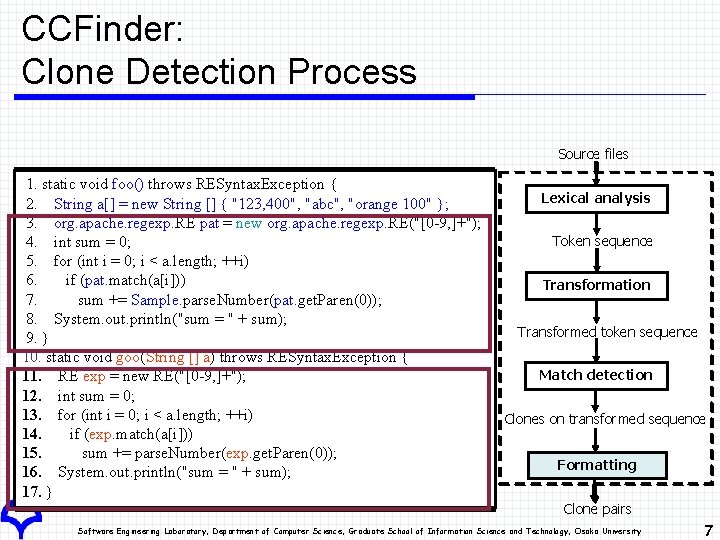
CCFinder: Clone Detection Process Source files 1. static void foo() throws RESyntax. Exception { 2. String a[] = new String [] { "123, 400", "abc", "orange 100" }; 3. org. apache. regexp. RE pat = new org. apache. regexp. RE("[0 -9, ]+"); 4. int sum = 0; 5. for (int i = 0; i < a. length; ++i) 6. if (pat. match(a[i])) 7. sum += Sample. parse. Number(pat. get. Paren(0)); 8. System. out. println("sum = " + sum); 9. } 10. static void goo(String [] a) throws RESyntax. Exception { 11. RE exp = new RE("[0 -9, ]+"); 12. int sum = 0; 13. for (int i = 0; i < a. length; ++i) 14. if (exp. match(a[i])) 15. sum += parse. Number(exp. get. Paren(0)); 16. System. out. println("sum = " + sum); 17. } Lexical analysis Token sequence Transformation Transformed token sequence Match detection Clones on on transformed sequence Formatting Clone pairs Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 7
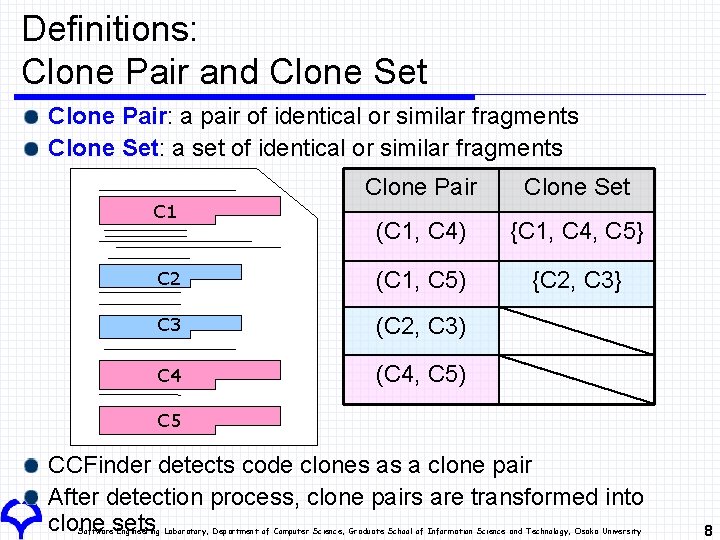
Definitions: Clone Pair and Clone Set Clone Pair: a pair of identical or similar fragments Clone Set: a set of identical or similar fragments Clone Pair Clone Set (C 1, C 4) {C 1, C 4, C 5} C 2 (C 1, C 5) {C 2, C 3} C 3 (C 2, C 3) C 4 (C 4, C 5) C 1 C 5 CCFinder detects code clones as a clone pair After detection process, clone pairs are transformed into clone sets Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 8
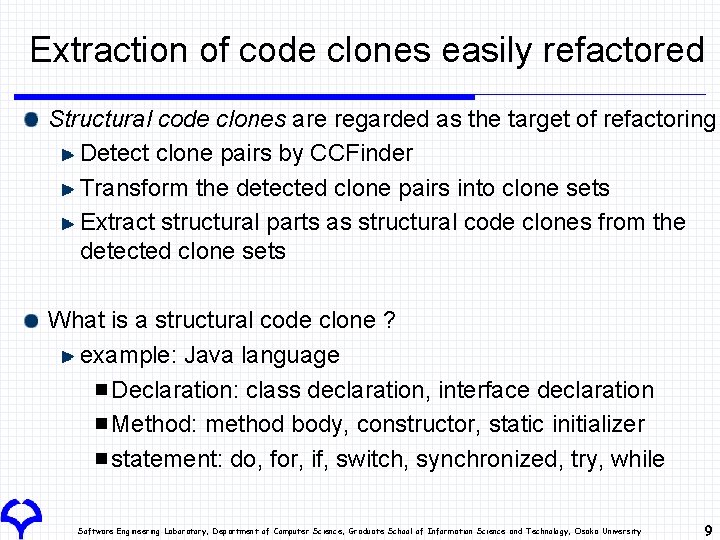
Extraction of code clones easily refactored Structural code clones are regarded as the target of refactoring Detect clone pairs by CCFinder Transform the detected clone pairs into clone sets Extract structural parts as structural code clones from the detected clone sets What is a structural code clone ? example: Java language Declaration: class declaration, interface declaration Method: method body, constructor, static initializer statement: do, for, if, switch, synchronized, try, while Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 9
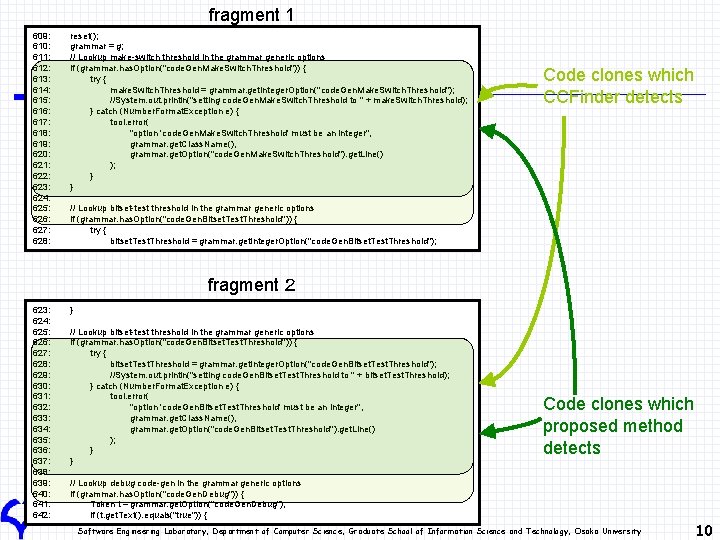
fragment 1 609: 610: 611: 612: 613: 614: 615: 616: 617: 618: 619: 620: 621: 622: 623: 624: 625: 626: 627: 628: reset(); grammar = g; // Lookup make-switch threshold in the grammar generic options if (grammar. has. Option("code. Gen. Make. Switch. Threshold")) { try { make. Switch. Threshold = grammar. get. Integer. Option("code. Gen. Make. Switch. Threshold"); //System. out. println("setting code. Gen. Make. Switch. Threshold to " + make. Switch. Threshold); } catch (Number. Format. Exception e) { tool. error( "option 'code. Gen. Make. Switch. Threshold' must be an integer", grammar. get. Class. Name(), grammar. get. Option("code. Gen. Make. Switch. Threshold"). get. Line() ); } } Code clones which CCFinder detects // Lookup bitset-test threshold in the grammar generic options if (grammar. has. Option("code. Gen. Bitset. Test. Threshold")) { try { bitset. Test. Threshold = grammar. get. Integer. Option("code. Gen. Bitset. Test. Threshold"); fragment 2 623: 624: 625: 626: 627: 628: 629: 630: 631: 632: 633: 634: 635: 636: 637: 638: 639: 640: 641: 642: } // Lookup bitset-test threshold in the grammar generic options if (grammar. has. Option("code. Gen. Bitset. Test. Threshold")) { try { bitset. Test. Threshold = grammar. get. Integer. Option("code. Gen. Bitset. Test. Threshold"); //System. out. println("setting code. Gen. Bitset. Test. Threshold to " + bitset. Test. Threshold); } catch (Number. Format. Exception e) { tool. error( "option 'code. Gen. Bitset. Test. Threshold' must be an integer", grammar. get. Class. Name(), grammar. get. Option("code. Gen. Bitset. Test. Threshold"). get. Line() ); } } Code clones which proposed method detects // Lookup debug code-gen in the grammar generic options if (grammar. has. Option("code. Gen. Debug")) { Token t = grammar. get. Option("code. Gen. Debug"); if (t. get. Text(). equals("true")) { Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 10
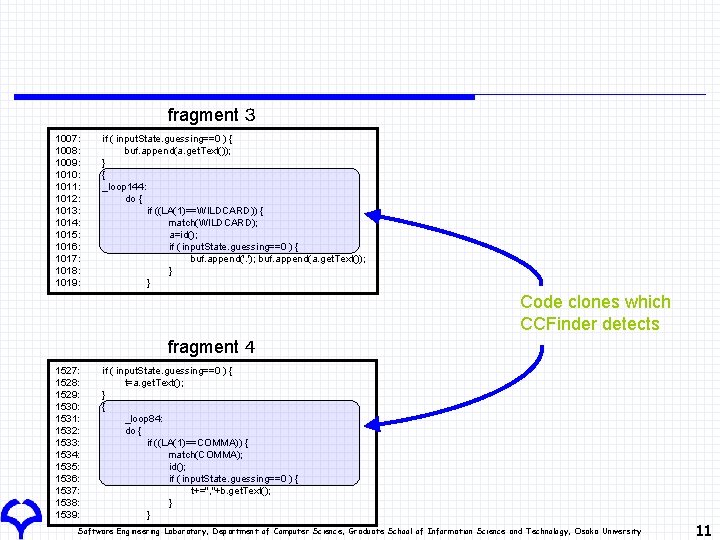
fragment 3 1007: 1008: 1009: 1010: 1011: 1012: 1013: 1014: 1015: 1016: 1017: 1018: 1019: if ( input. State. guessing==0 ) { buf. append(a. get. Text()); } { _loop 144: do { if ((LA(1)==WILDCARD)) { match(WILDCARD); a=id(); if ( input. State. guessing==0 ) { buf. append('. '); buf. append(a. get. Text()); } } Code clones which CCFinder detects fragment 4 1527: 1528: 1529: 1530: 1531: 1532: 1533: 1534: 1535: 1536: 1537: 1538: 1539: if ( input. State. guessing==0 ) { t=a. get. Text(); } { _loop 84: do { if ((LA(1)==COMMA)) { match(COMMA); id(); if ( input. State. guessing==0 ) { t+=", "+b. get. Text(); } } Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 11
![Provision of applicable refactoring patterns Following refactoring patterns[1][2] can be used to remove code Provision of applicable refactoring patterns Following refactoring patterns[1][2] can be used to remove code](http://slidetodoc.com/presentation_image_h/0929acb8ffff83e3381a1c23708e36a5/image-12.jpg)
Provision of applicable refactoring patterns Following refactoring patterns[1][2] can be used to remove code sets including structural code clones Extract Class, Extract Method, Extract Super Class, Form Template Method, Move Method, Parameterize Method, Pull Up Constructor, Pull Up Method, For each clone set, the proposed method determines which refactoring pattern is applicable by using several metrics. [1]: M. Fowler: Refactoring: Improving the Design of Existing Code, Addison-Wesley, 1999. [2]: http: //www. refactoring. com/, 2004. Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 12
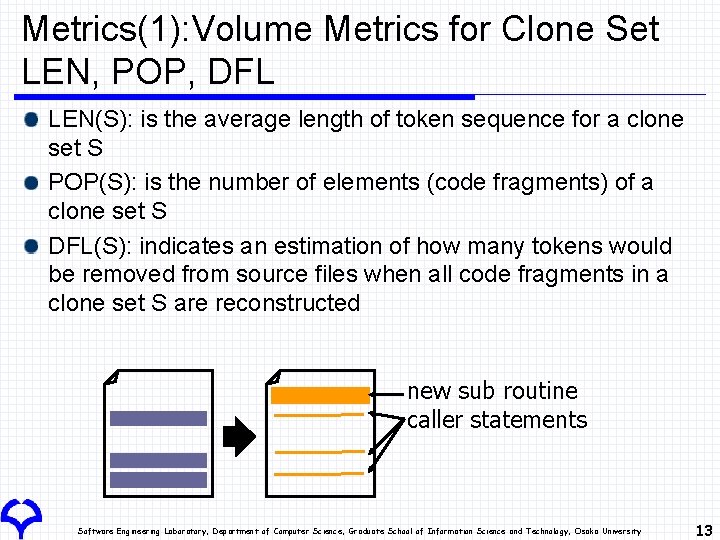
Metrics(1): Volume Metrics for Clone Set LEN, POP, DFL LEN(S): is the average length of token sequence for a clone set S POP(S): is the number of elements (code fragments) of a clone set S DFL(S): indicates an estimation of how many tokens would be removed from source files when all code fragments in a clone set S are reconstructed new sub routine caller statements Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 13
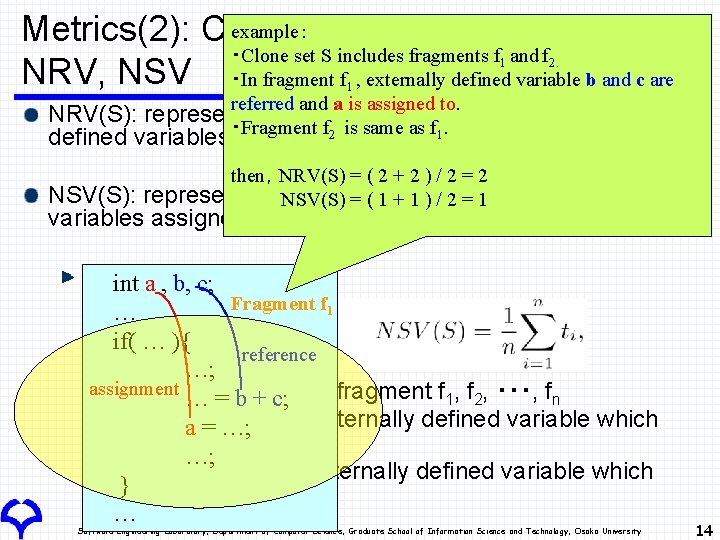
example: Metrics(2): Coupling Metrics for Clone Set ・Clone set S includes fragments f and f NRV, NSV ・In fragment f , externally defined variable b and c are 1 2. 1 referred and a is assigned to. NRV(S): represents the average number of externally ・Fragment f 2 is same as f 1. defined variables referred in the fragment of a clone set S then,NRV(S) = ( 2 + 2 ) / 2 = 2 represents the average number of NSV(S) = ( 1 + 1 ) / 2 = 1 NSV(S): externally defined variables assigned to in the fragment of a clone set S Definition int a , b, c; Fragment f 1 … if( … ){ reference …; assignment Clone set S includes fragment f 1, f 2, ・・・, fn … = b + c; si is the number of externally defined variable which a = …; fragment fi refers …; ti is the number of externally defined variable which } fragment fi assigns … Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 14
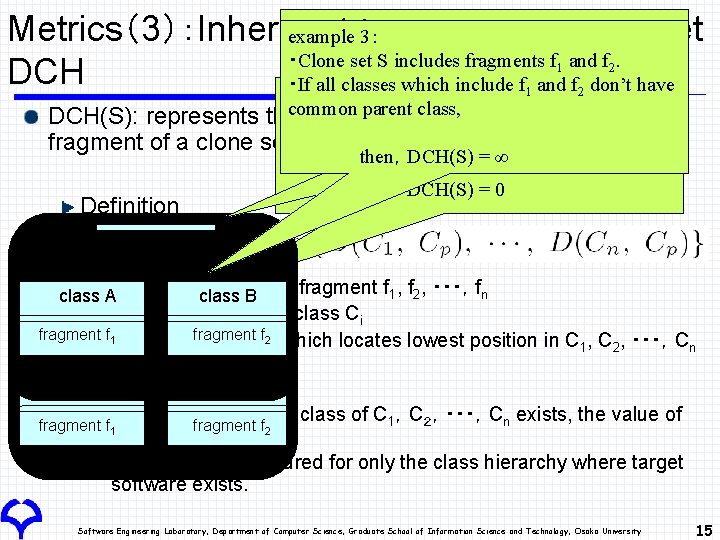
example 2: Metrics(3):Inheritance example 3: Metric for Clone Set ・Clone set S includes fragments f and f. ・If all fragments of clone set S are included in a DCH ・If all classes which include f and f don’t have example 1: 1 1 2 2 1 2 class and its direct child classes, common parent class, ・Clone set S includes fragments f DCH(S): represents the position and distance between 1 and f 2. each fragment of a clone set・If all fragments of clone set S are included in a S then,DCH(S) = 1 then,DCH(S) = ∞ same class, then, DCH(S) = 0 Definition class A S includes fragment f 1, f 2, ・・・,fn B class AClone set class A f exists in class C Fragment i fragment f 1 Class C fragment f 2 fragment fp 1 is a class on classf hierarchy fragment 2 class B i which locates lowest position in C 1, C 2, ・・・,Cn class C If no common parent class of C 1,C2,・・・,Cn exists, the value of fragment f 2 DCH(S) is ∞ This metric is measured for only the class hierarchy where target software exists. fragment f 1 Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 15
Aries: Refactoring Support Tool Overview Target: Java programs Runtime environment: JDK 1. 4 or above Implementation Analysis component: Java 32, 000 Lines CCFinder is used as code clone detection component Java. CC is used to construct syntax and semantic analysis component GUI component: Java 14, 000 Lines User can specify target clone sets through GUI operations. Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 16
Case Study: Ant Overview Ant is one of build tools like ‘make’ Input for Aries Source files of Ant: 627 LOC: about 180, 000 It took 30 seconds to extract structural code clones We got 151 clone sets. Environment OS: Free. BSD 4. 9 CPU: Xeon 2. 8 G x 2 Memory: 4 GB Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 17

Case Study: Ant Extract Method (conditions) To apply ‘Extract Method’ pattern, we filtered clone sets by using following conditions The unit of clone is statement (do, for, if, …) Set the value of DCH(S) = 0 All fragments of a clone set are included in a class Set the value of NSV(S) < 2 Each fragment of a clone set assigns any value to 1 or no externally defined variable. 32 clone sets satisfied these conditions Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 18
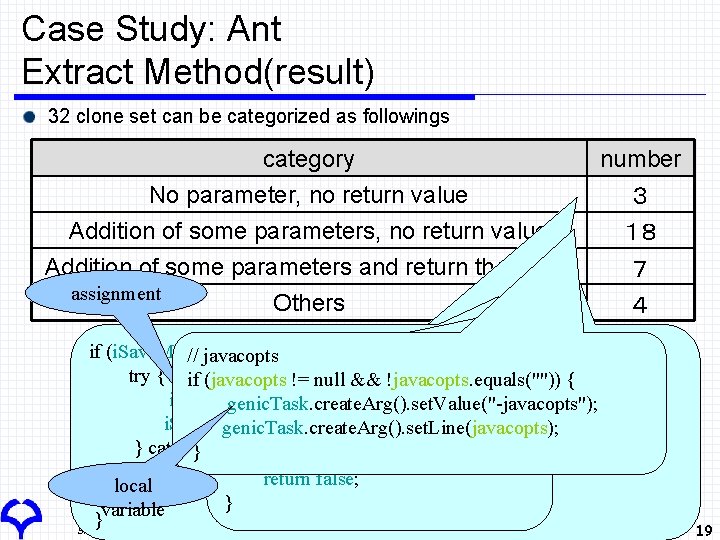
Case Study: Ant Extract Method(result) 32 clone set can be categorized as followings category number No parameter, no return value 3 Addition of some parameters, no return value 18 Addition of some parameters and return the value 7 assignment Others 4 if (!is. Checked()) { if (i. Save. Menu. Item == null) { // javacopts if (name == null) { // make sure we don't have a circular reference here try { if (javacopts != null && !javacopts. equals("")) { if (other. name != null) { Stack stk = new Stack(); i. Save. Menu. Item = new Menu. Item(); genic. Task. create. Arg(). set. Value("-javacopts"); return false; stk. push(this); i. Save. Menu. Item. set. Label("Save Build. Info To Repository"); genic. Task. create. Arg(). set. Line(javacopts); } die. On. Circular. Reference(stk, get. Project()); } catch (Throwable i. Exc) { } } else if (!name. equals(other. name)) { } handle. Exception(i. Exc); return false; local } } variable } Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 19
Conclusion We have proposed refactoring support method implemented a refactoring support tool, Aries conducted a case study to Ant, which is an open source program, and most of filtered clone sets could be removed. Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 20
Future Works As future works, we are going to evaluate whether or not each refactoring should be done as the viewpoint of software quality (support Step 3) find a group of clone sets that can be refactored at once to conduct refactoring more effectively Commonly used refactoring process Step 1: Determine where refactoring should be applied Step 2: Determine which refactoring patterns can/should be applied Step 3: Investigate the effectiveness of the refactoring patterns Step 4: Modify source code Step 5: Conduct regression tests Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 21
Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 22
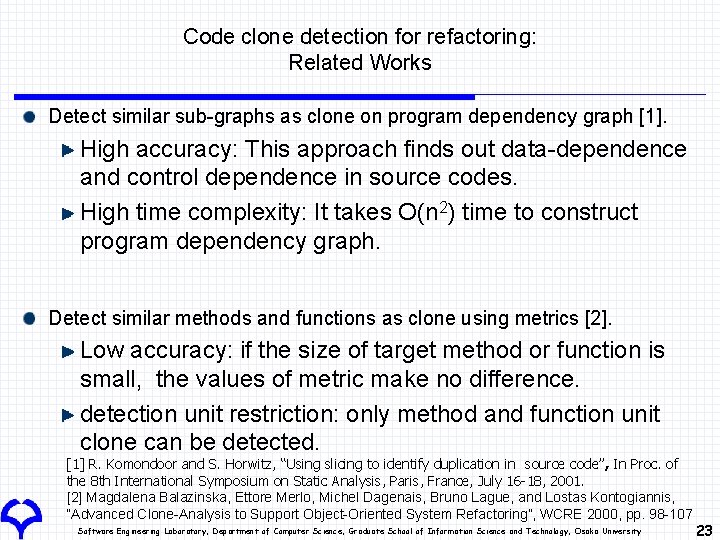
Code clone detection for refactoring: Related Works Detect similar sub-graphs as clone on program dependency graph [1]. High accuracy: This approach finds out data-dependence and control dependence in source codes. High time complexity: It takes O(n 2) time to construct program dependency graph. Detect similar methods and functions as clone using metrics [2]. Low accuracy: if the size of target method or function is small, the values of metric make no difference. detection unit restriction: only method and function unit clone can be detected. [1] R. Komondoor and S. Horwitz, “Using slicing to identify duplication in source code”, In Proc. of the 8 th International Symposium on Static Analysis, Paris, France, July 16 -18, 2001. [2] Magdalena Balazinska, Ettore Merlo, Michel Dagenais, Bruno Lague, and Lostas Kontogiannis, “Advanced Clone-Analysis to Support Object-Oriented System Refactoring”, WCRE 2000, pp. 98 -107 Software Engineering Laboratory, Department of Computer Science, Graduate School of Information Science and Technology, Osaka University 23
- Slides: 23