Redesigning the Webs Access Control Systems Wenliang Kevin
Re-designing the Web’s Access Control Systems Wenliang (Kevin) Du Associate Professor Department of Electrical Engineering & Computer Science Syracuse University Joint work with Dr. Karthick Jayaraman, Tongbo Luo, Xi Tan, and Dr. Zutao Zhu Presentation at Microsoft Research, Redmond, 7/28/2011.
Overview �Access control in the Web �Our positions on Web’s access control �Our approaches to improve web security �Escudo: Browser-side access control �Scuta: Server-side access control �Database-side access control
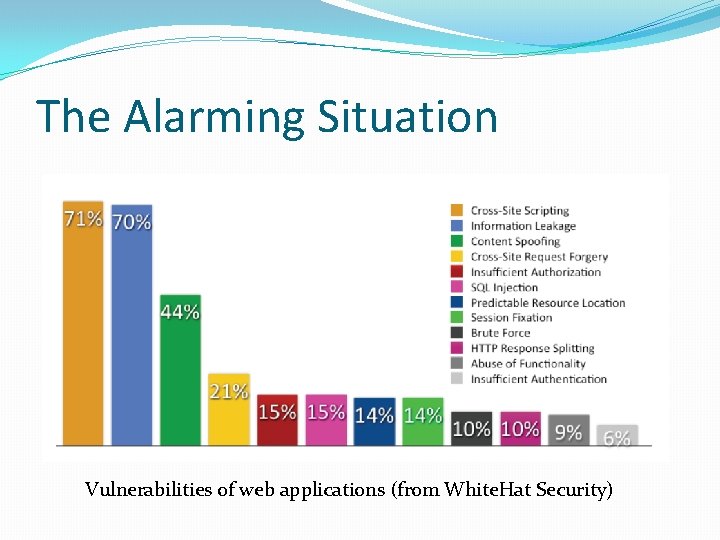
The Alarming Situation Vulnerabilities of web applications (from White. Hat Security)
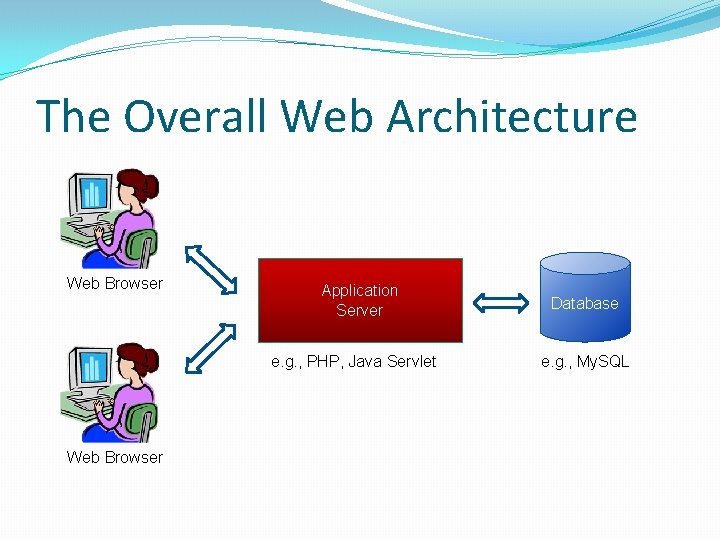
The Overall Web Architecture Web Browser Application Server e. g. , PHP, Java Servlet Web Browser Database e. g. , My. SQL
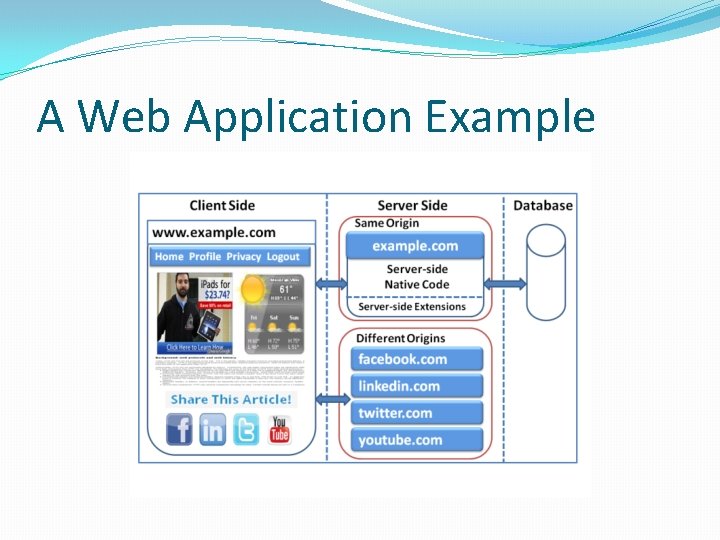
A Web Application Example
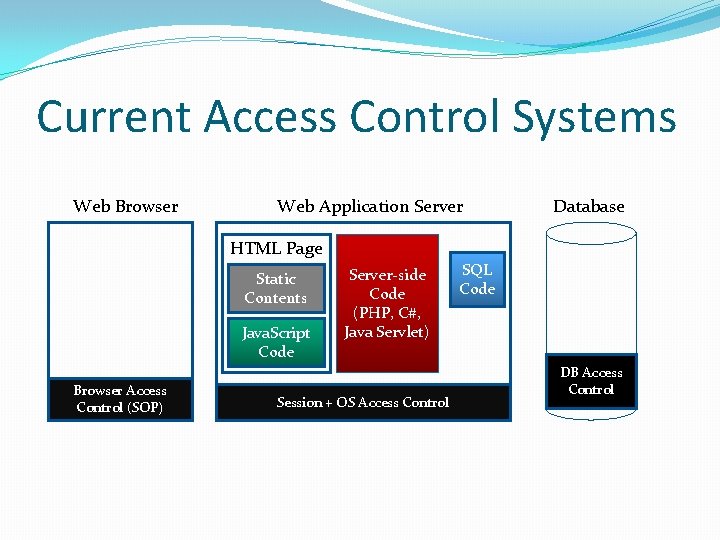
Current Access Control Systems Web Browser Web Application Server Database HTML Page Static Contents Java. Script Code Browser Access Control (SOP) Server-side Code (PHP, C#, Java Servlet) Session + OS Access Control SQL Code DB Access Control
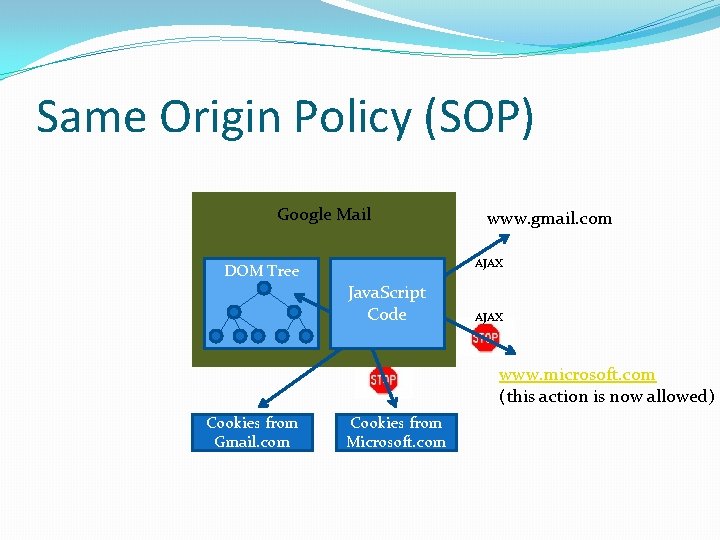
Same Origin Policy (SOP) Google Mail www. gmail. com AJAX DOM Tree Java. Script Code AJAX www. microsoft. com (this action is now allowed) Cookies from Gmail. com Cookies from Microsoft. com
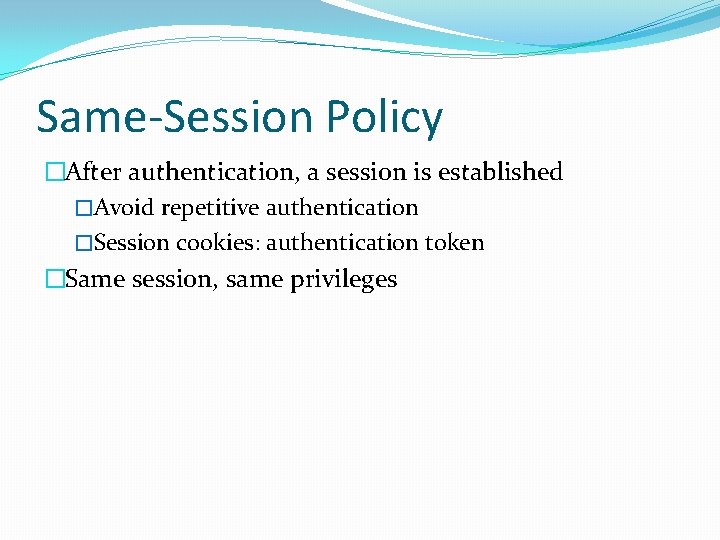
Same-Session Policy �After authentication, a session is established �Avoid repetitive authentication �Session cookies: authentication token �Same session, same privileges
Problems of SOP and SSP �Coarse granularity: one or nothing �No separation of privileges �Do we need to separate privileges?

Diversified Protection Needs Untrusted Region Advertisements Semi-Trusted Region Third-party Content Trusted Region First-party Content Untrusted Region Third-party Content Add. Friends. php Delete. Friends. php View. Friends. php
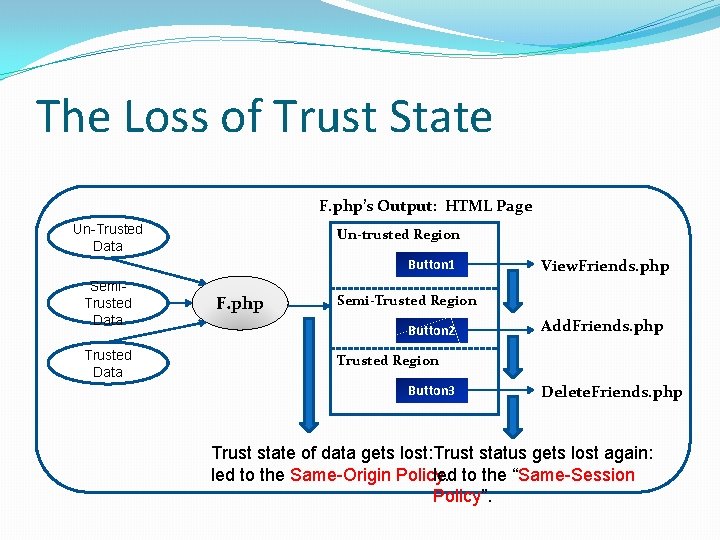
The Loss of Trust State F. php’s Output: HTML Page Un-Trusted Data Un-trusted Region Button 1 Semi. Trusted Data F. php View. Friends. php Semi-Trusted Region Button 2 Add. Friends. php Trusted Region Button 3 Delete. Friends. php Trust state of data gets lost: Trust status gets lost again: led to the Same-Origin Policy. led to the “Same-Session Policy”.
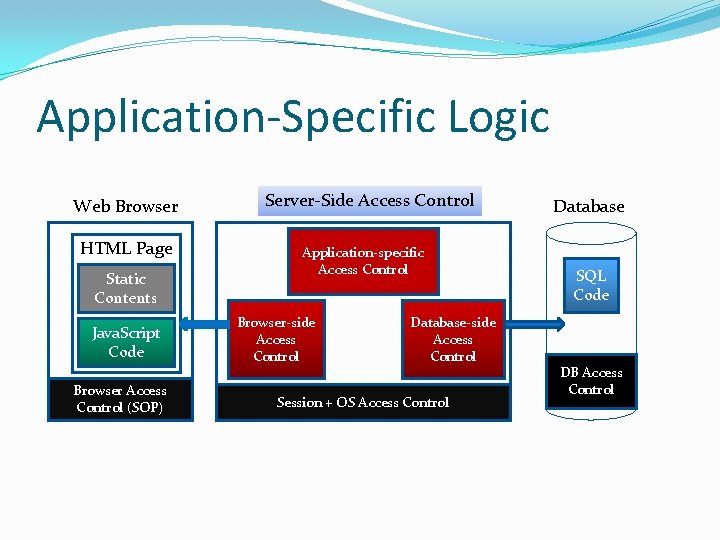
Application-Specific Logic Web Browser HTML Page Static Contents Java. Script Code Browser Access Control (SOP) Server-Side Access Control Application-specific Access Control Browser-side Access Control Database-side Access Control Session + OS Access Control Database SQL Code DB Access Control
Inadequate Access Control �Access control has to be built into program logic �Not easy for programmers � 83% of web sites have at least one serious vulnerability �Deploy countermeasures in programs. �Developers need to be security experts �Do we have enough security experts? �I am a security expert, I am afraid of writing web apps. �Something is fundamentally wrong! �Don’t blame the developers �Blame the Web’s security infrastructure
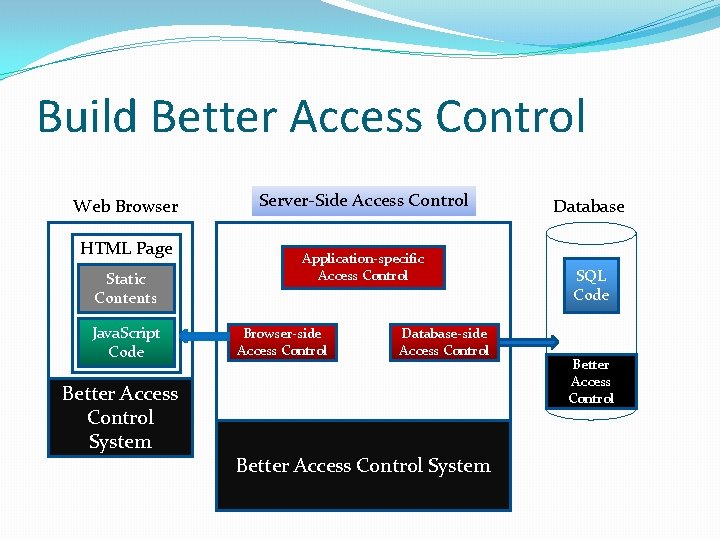
Build Better Access Control Web Browser HTML Page Static Contents Java. Script Code Better Access Control System Server-Side Access Control Application-specific Access Control Browser-side Access Control Database-side Access Control Better Access Control System Database SQL Code Better Access Control
The Benefit �Developers’ security efforts are reduced �They only need to “configure” �Enforcement is done by the system �Configuration: compared to Implementation �Much easier to do �Require less security expertise �Less error prone �Easier to verify
Design Principles Civil Engineering Principles Security Engineering Principles
![Security Engineering Principles �[Saltzer and Schroeder 1975]: 8 design principles for building protection systems: Security Engineering Principles �[Saltzer and Schroeder 1975]: 8 design principles for building protection systems:](http://slidetodoc.com/presentation_image_h/7565abf20f8553df9aff366b8ed65efc/image-17.jpg)
Security Engineering Principles �[Saltzer and Schroeder 1975]: 8 design principles for building protection systems: �Economy of mechanism �Fail-safe defaults �Complete mediation �Open design �Separation of privilege �Least common mechanism �Psychological acceptability
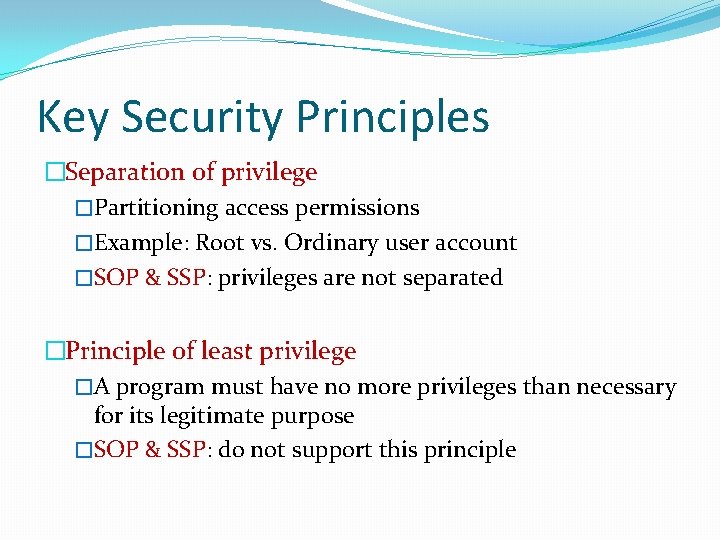
Key Security Principles �Separation of privilege �Partitioning access permissions �Example: Root vs. Ordinary user account �SOP & SSP: privileges are not separated �Principle of least privilege �A program must have no more privileges than necessary for its legitimate purpose �SOP & SSP: do not support this principle
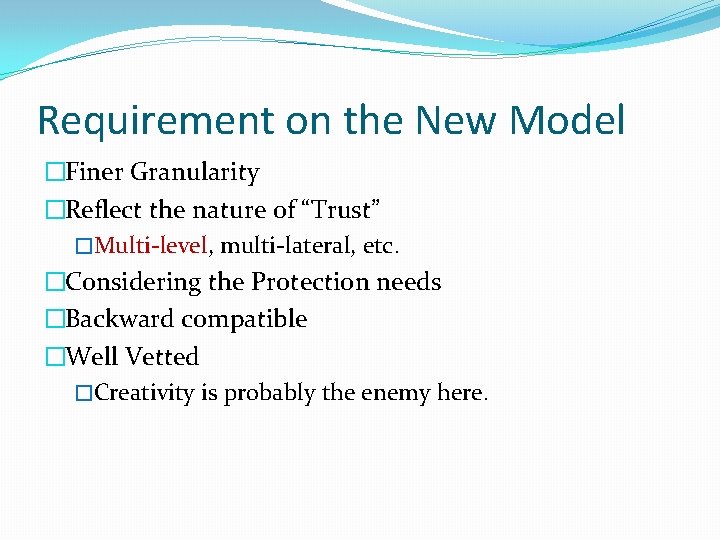
Requirement on the New Model �Finer Granularity �Reflect the nature of “Trust” �Multi-level, multi-lateral, etc. �Considering the Protection needs �Backward compatible �Well Vetted �Creativity is probably the enemy here.
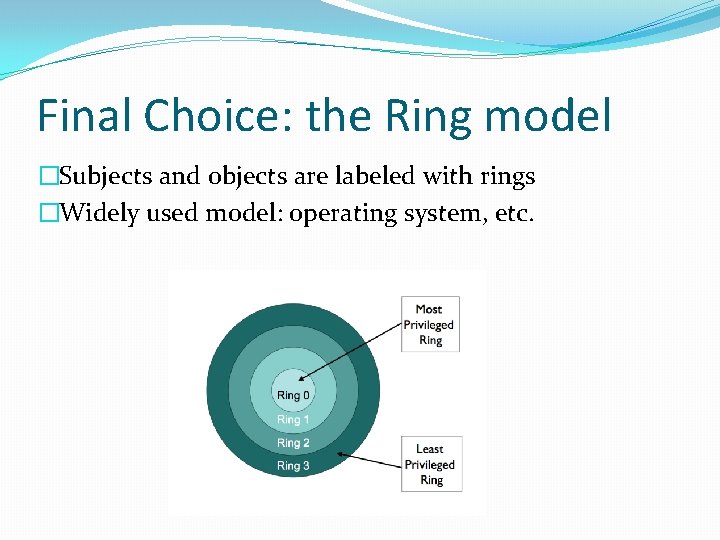
Final Choice: the Ring model �Subjects and objects are labeled with rings �Widely used model: operating system, etc.
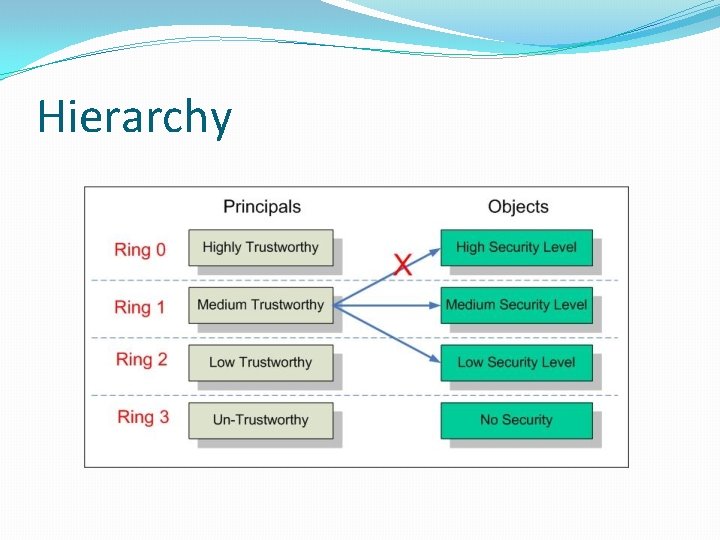
Hierarchy
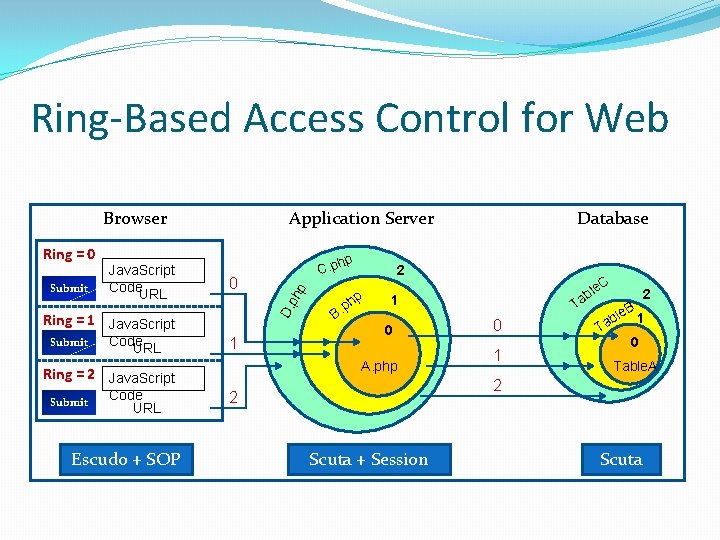
Ring-Based Access Control for Web Browser hp 0 Ring = 1 Java. Script Submit Code URL 1 Submit Escudo + SOP hp. p B Database 2 C ble a T 1 0 A. php Ring = 2 Java. Script Code URL C. p ph p Submit Java. Script Code URL D. Ring = 0 Application Server 0 1 2 le. B 1 b Ta 0 Table. A 2 2 Scuta + Session Scuta
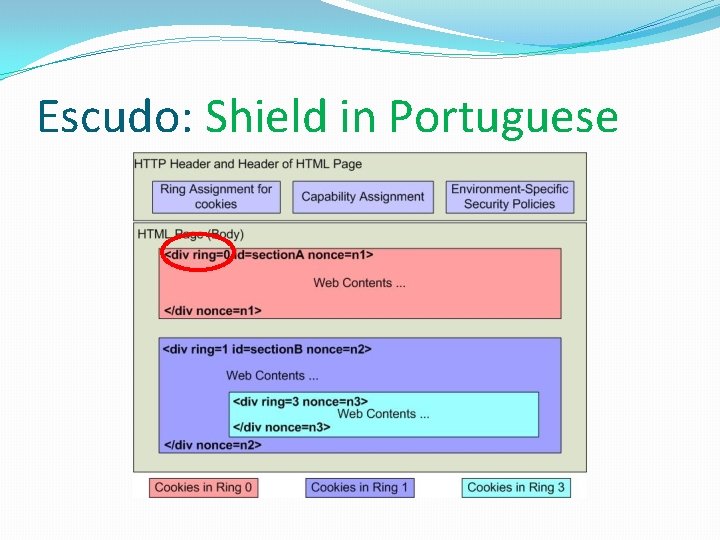
Escudo: Shield in Portuguese
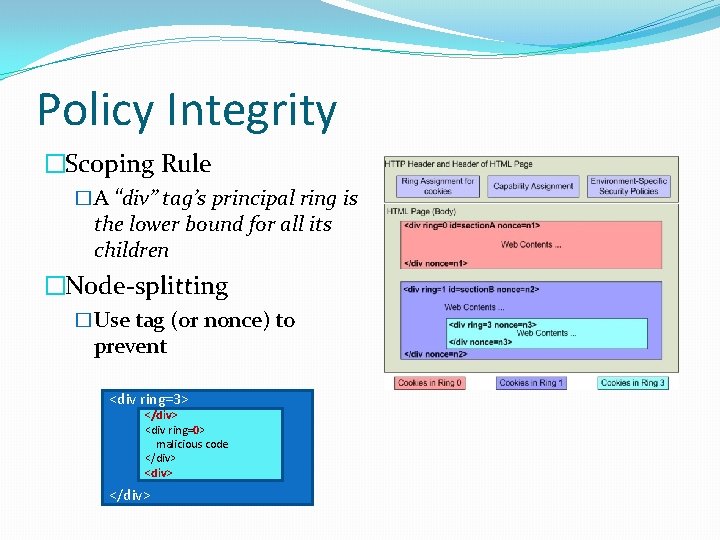
Policy Integrity �Scoping Rule �A “div” tag’s principal ring is the lower bound for all its children �Node-splitting �Use tag (or nonce) to prevent <div ring=3> </div> <div ring=0> malicious code </div>
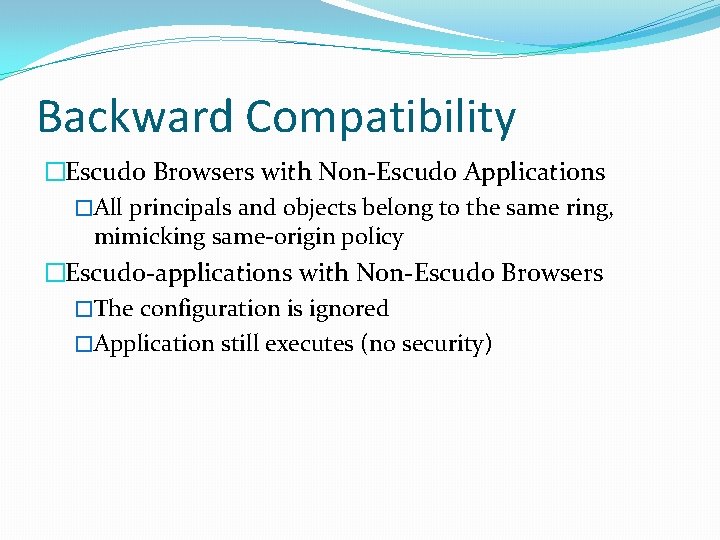
Backward Compatibility �Escudo Browsers with Non-Escudo Applications �All principals and objects belong to the same ring, mimicking same-origin policy �Escudo-applications with Non-Escudo Browsers �The configuration is ignored �Application still executes (no security)
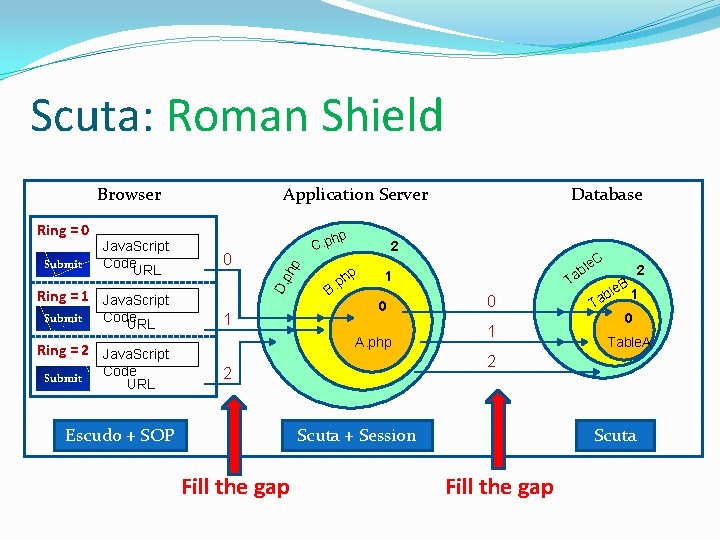
Scuta: Roman Shield Browser hp 0 Ring = 1 Java. Script Submit Code URL C. p ph p Submit Java. Script Code URL D. Ring = 0 Application Server 1 Submit 0 0 1 Scuta + Session Fill the gap 2 le. B 1 b Ta 0 Table. A 2 2 Escudo + SOP C ble a T 1 A. php Ring = 2 Java. Script Code URL 2 hp. p B Database Scuta Fill the gap
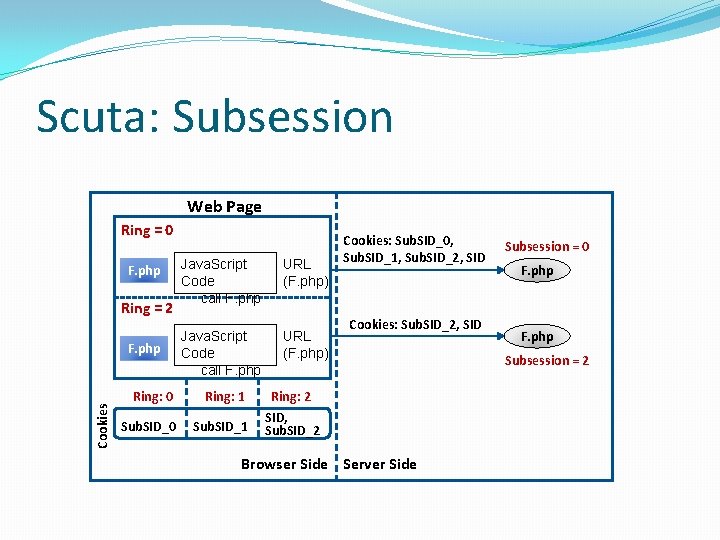
Scuta: Subsession Web Page Ring = 0 F. php Ring = 2 Cookies F. php Java. Script Code call F. php URL (F. php) Ring: 0 Ring: 1 Sub. SID_0 Sub. SID_1 Cookies: Sub. SID_0, Sub. SID_1, Sub. SID_2, SID Cookies: Sub. SID_2, SID Ring: 2 SID, Sub. SID_2 Browser Side Server Side Subsession = 0 F. php Subsession = 2
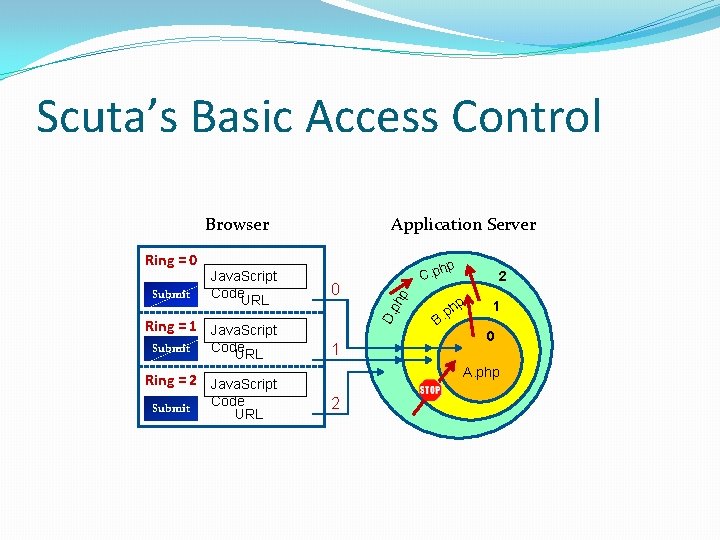
Scuta’s Basic Access Control Browser hp 0 Ring = 1 Java. Script Submit Code URL 1 Code URL 2 p ph. B 1 0 A. php Ring = 2 Java. Script Submit C. p ph p Submit Java. Script Code URL D. Ring = 0 Application Server 2
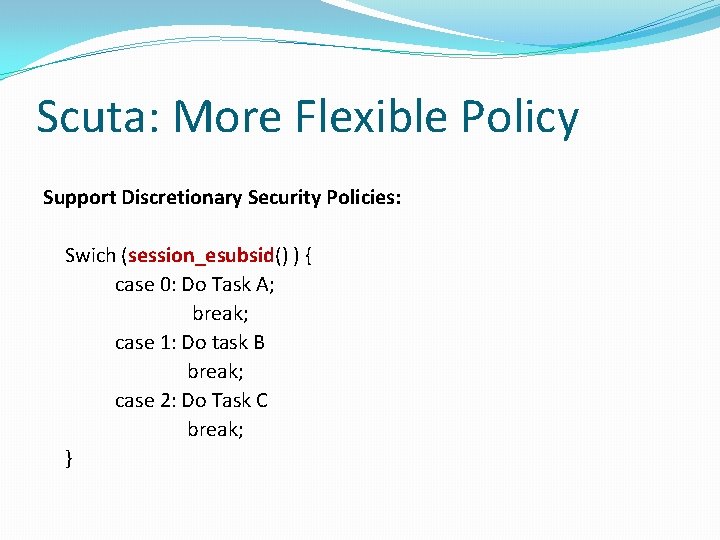
Scuta: More Flexible Policy Support Discretionary Security Policies: Swich (session_esubsid() ) { case 0: Do Task A; break; case 1: Do task B break; case 2: Do Task C break; }
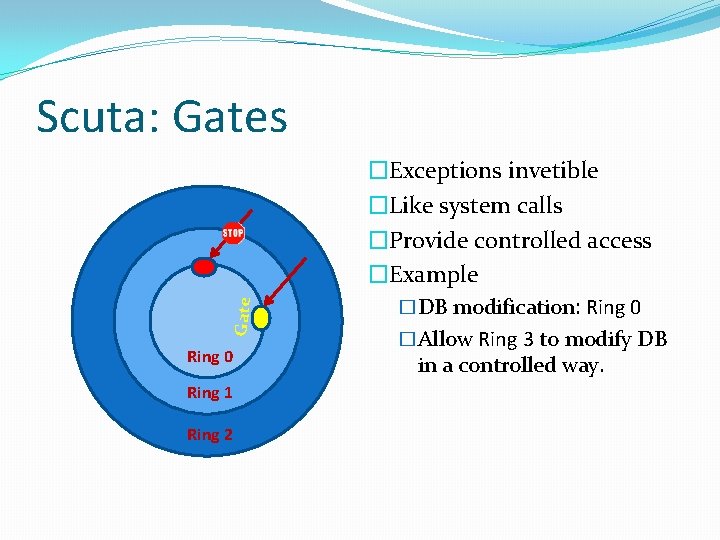
Scuta: Gates Gate �Exceptions invetible �Like system calls �Provide controlled access �Example Ring 0 Ring 1 Ring 2 �DB modification: Ring 0 �Allow Ring 3 to modify DB in a controlled way.
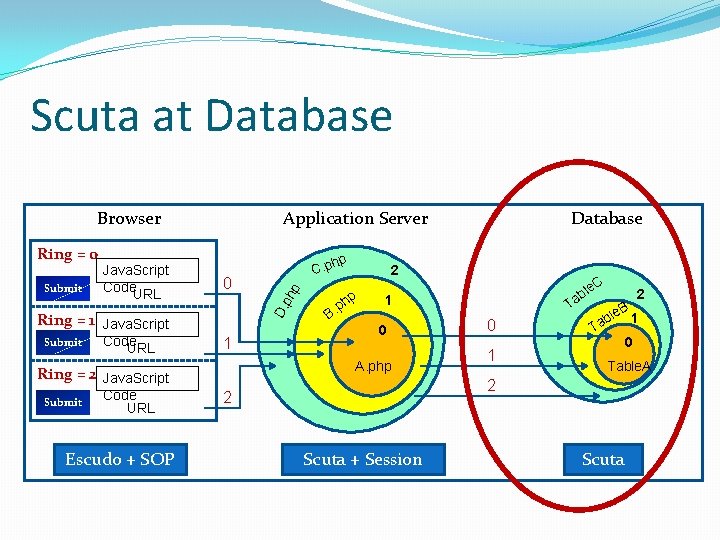
Scuta at Database Browser hp 0 Ring = 1 Java. Script Submit Code URL 1 Submit Escudo + SOP hp. p B Database 2 C ble a T 1 0 A. php Ring = 2 Java. Script Code URL C. p ph p Submit Java. Script Code URL D. Ring = 0 Application Server 0 1 2 le. B 1 b Ta 0 Table. A 2 2 Scuta + Session Scuta
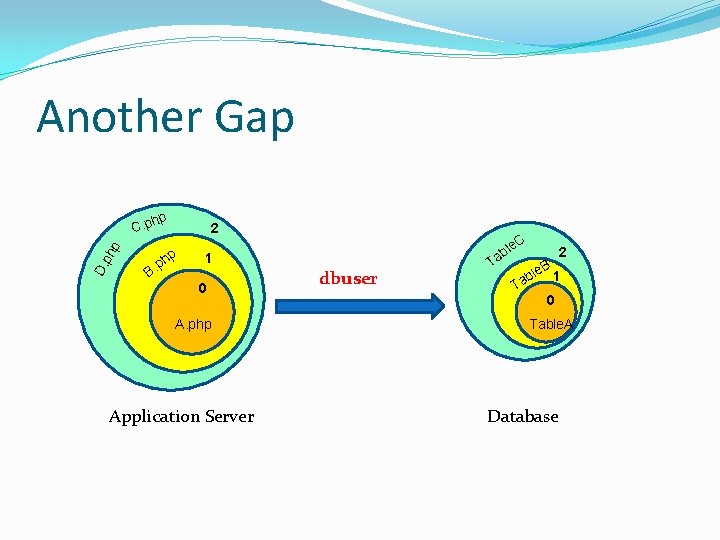
Another Gap D. ph p hp C. p 2 p B. hp C le ab 1 0 A. php Application Server dbuser 2 B ble 1 T Ta 0 Table. A Database
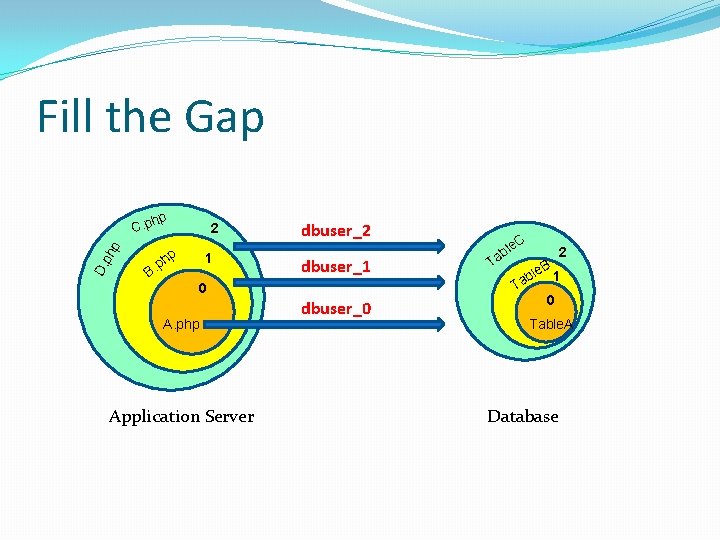
Fill the Gap D. ph p hp C. p 2 hp 1 p B. dbuser_2 dbuser_1 0 A. php Application Server dbuser_0 C le ab 2 B ble 1 T Ta 0 Table. A Database
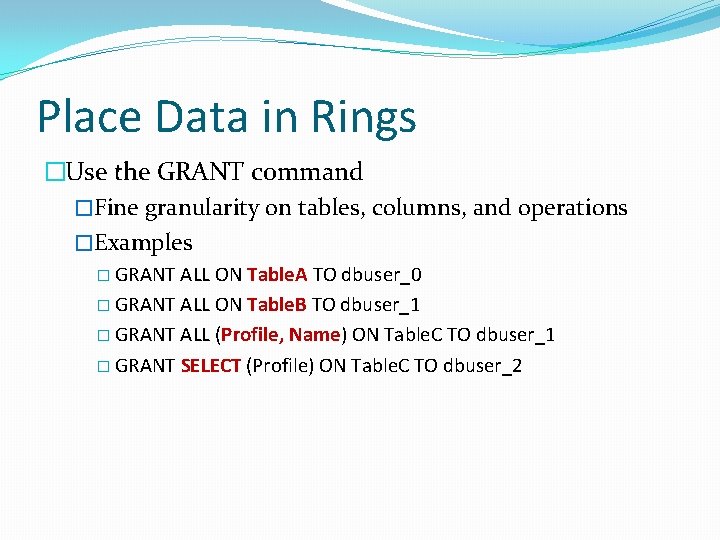
Place Data in Rings �Use the GRANT command �Fine granularity on tables, columns, and operations �Examples � GRANT ALL ON Table. A TO dbuser_0 � GRANT ALL ON Table. B TO dbuser_1 � GRANT ALL (Profile, Name) ON Table. C TO dbuser_1 � GRANT SELECT (Profile) ON Table. C TO dbuser_2
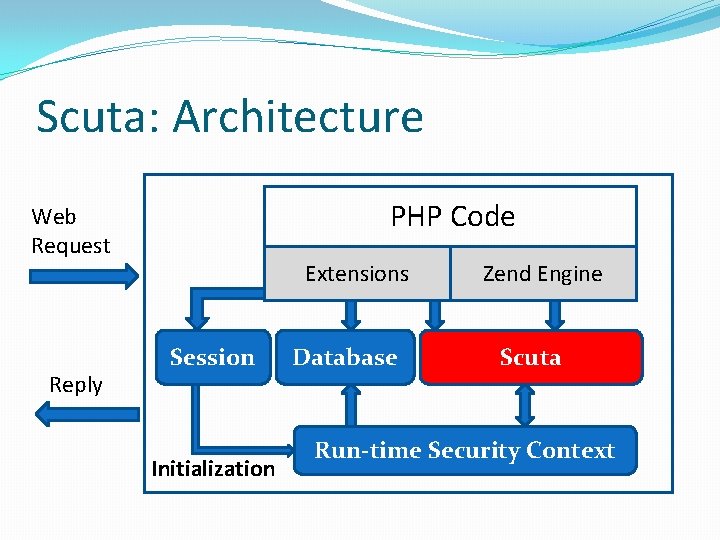
Scuta: Architecture PHP Code Web Request Reply Extensions Session Initialization Database Zend Engine Scuta Run-time Security Context
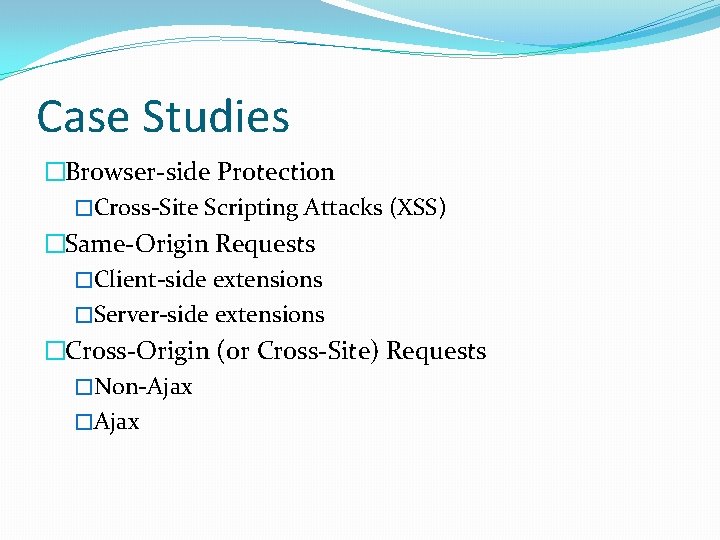
Case Studies �Browser-side Protection �Cross-Site Scripting Attacks (XSS) �Same-Origin Requests �Client-side extensions �Server-side extensions �Cross-Origin (or Cross-Site) Requests �Non-Ajax �Ajax
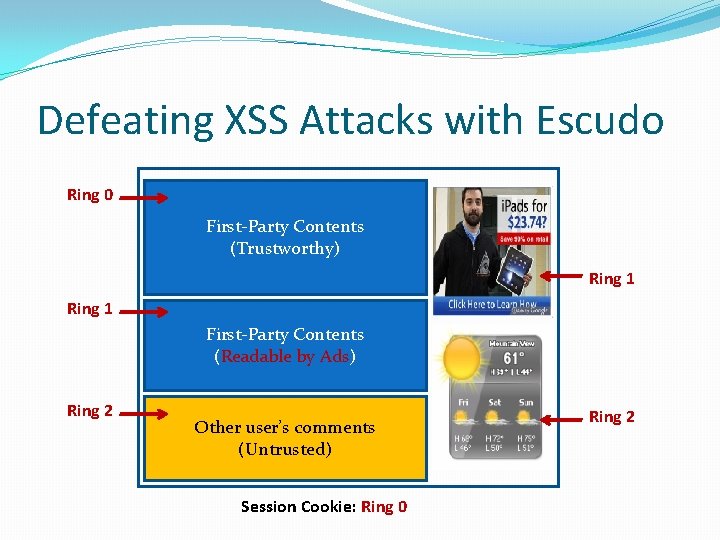
Defeating XSS Attacks with Escudo Ring 0 First-Party Contents (Trustworthy) Ring 1 First-Party Contents (Readable by Ads) Ring 2 Other user’s comments (Untrusted) Session Cookie: Ring 0 Ring 2
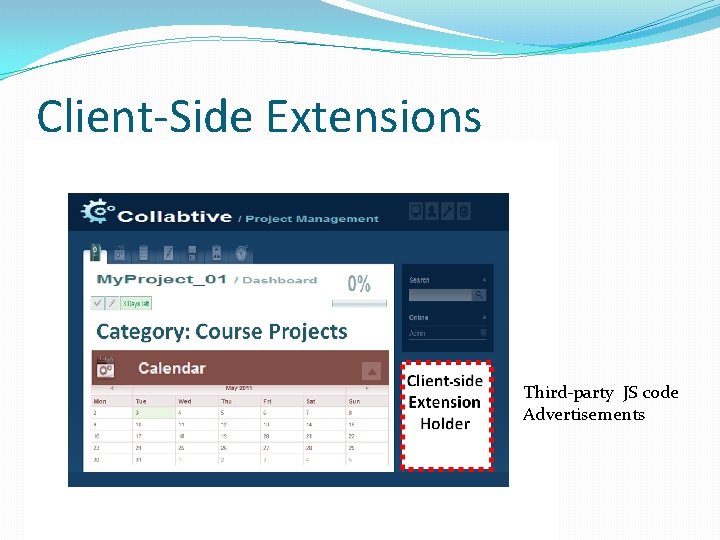
Client-Side Extensions Third-party JS code Advertisements
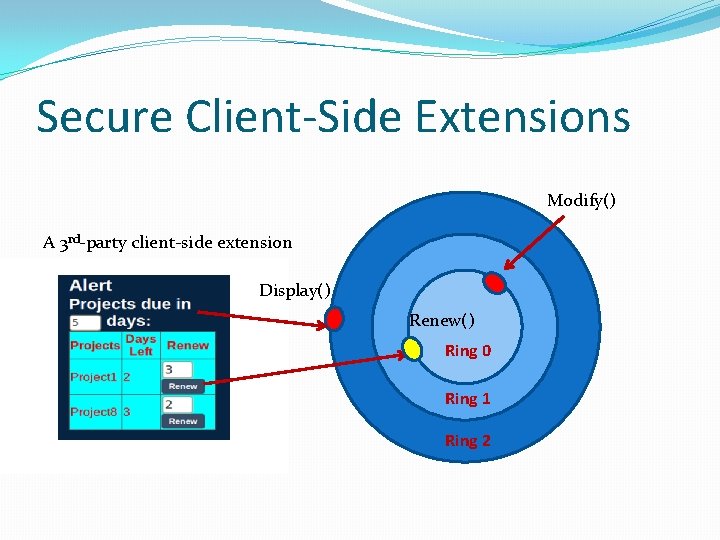
Secure Client-Side Extensions Modify() A 3 rd-party client-side extension Display() Renew() Ring 0 Ring 1 Ring 2
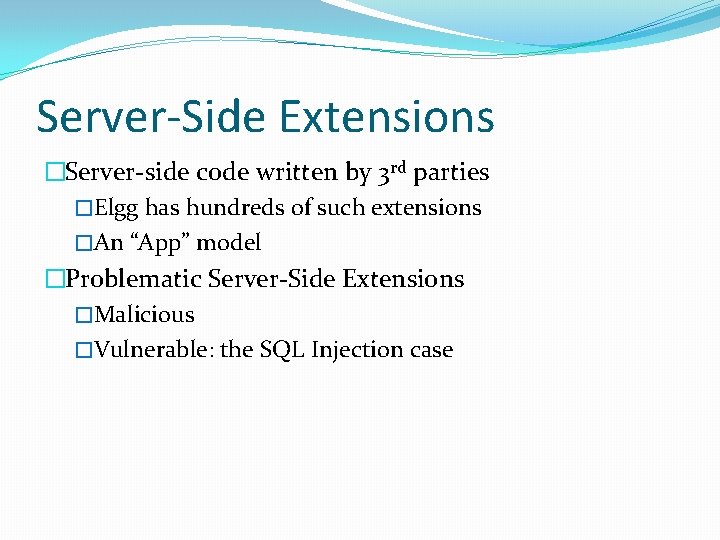
Server-Side Extensions �Server-side code written by 3 rd parties �Elgg has hundreds of such extensions �An “App” model �Problematic Server-Side Extensions �Malicious �Vulnerable: the SQL Injection case
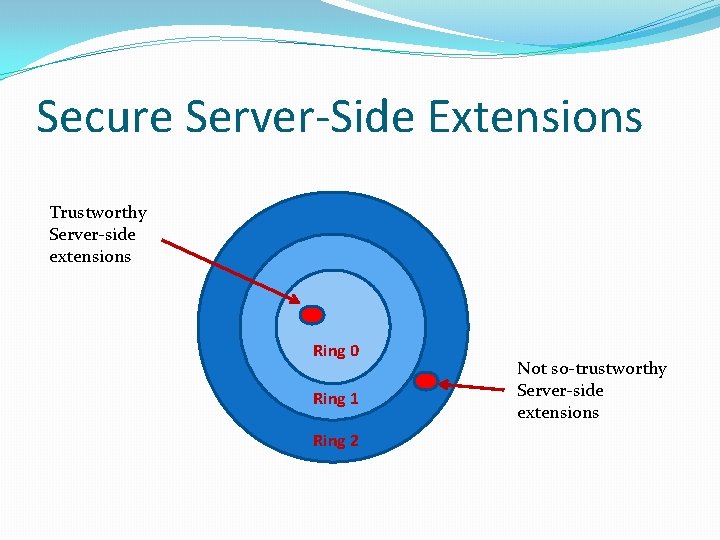
Secure Server-Side Extensions Trustworthy Server-side extensions Ring 0 Ring 1 Ring 2 Not so-trustworthy Server-side extensions
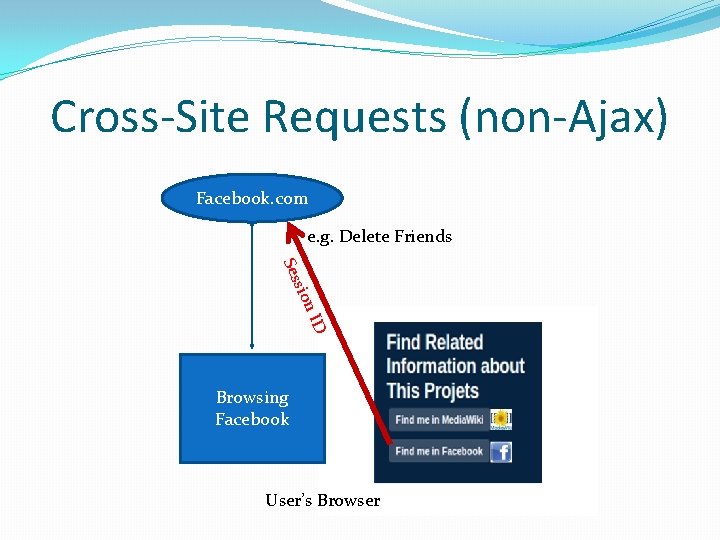
Cross-Site Requests (non-Ajax) Facebook. com e. g. Delete Friends n ID sio Ses Browsing Facebook User’s Browser
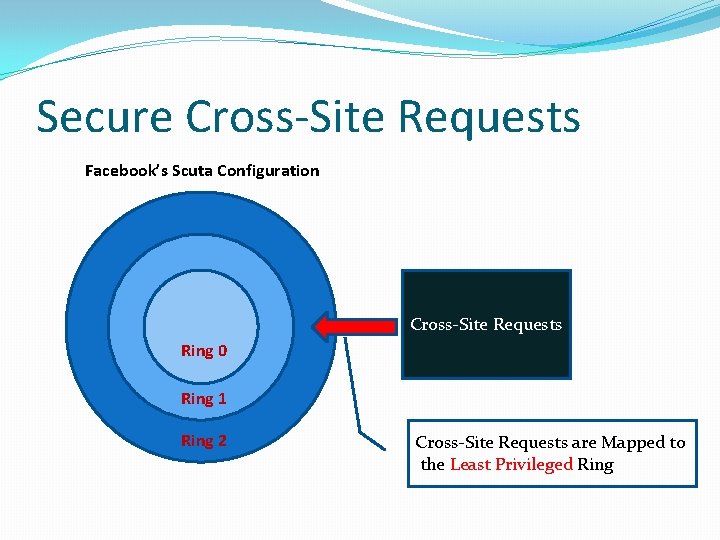
Secure Cross-Site Requests Facebook’s Scuta Configuration Cross-Site Requests Ring 0 Ring 1 Ring 2 Cross-Site Requests are Mapped to the Least Privileged Ring
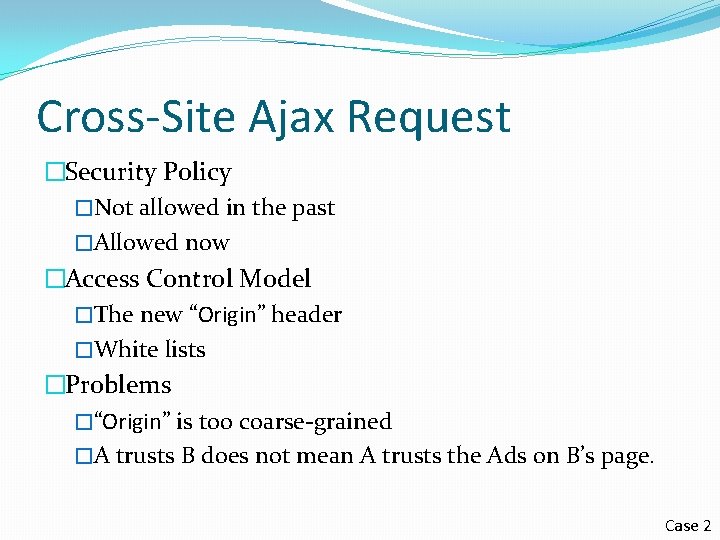
Cross-Site Ajax Request �Security Policy �Not allowed in the past �Allowed now �Access Control Model �The new “Origin” header �White lists �Problems �“Origin” is too coarse-grained �A trusts B does not mean A trusts the Ads on B’s page. Case 2
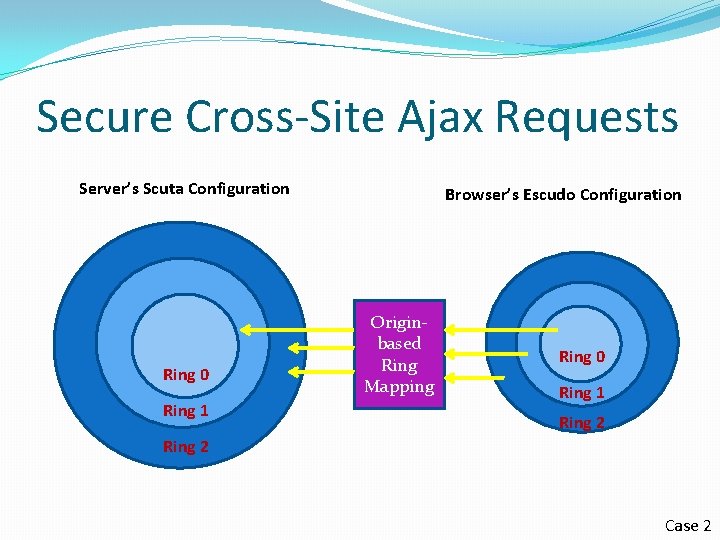
Secure Cross-Site Ajax Requests Server’s Scuta Configuration Ring 0 Ring 1 Browser’s Escudo Configuration Originbased Ring Mapping Ring 0 Ring 1 Ring 2 Case 2
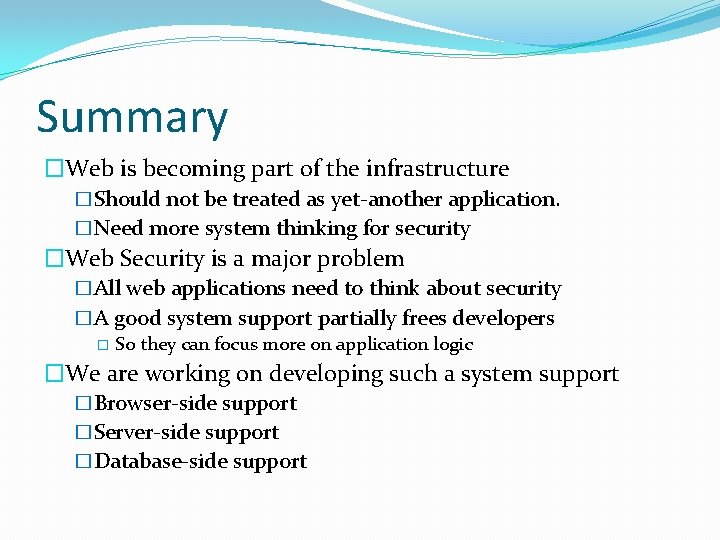
Summary �Web is becoming part of the infrastructure �Should not be treated as yet-another application. �Need more system thinking for security �Web Security is a major problem �All web applications need to think about security �A good system support partially frees developers � So they can focus more on application logic �We are working on developing such a system support �Browser-side support �Server-side support �Database-side support
- Slides: 46