Recover the tampered image based on VQ indexing
Recover the tampered image based on VQ indexing Source: Signal Processing, Volume 90, Issue 1, Jan. 2010, pp. 331 -343 Authors: Chun-Wei Yang and Jau-Ji Shen Reporter: Te-Yu Chen(陳德祐)
Outline n Introduction n The Proposed Scheme ¨VQ Index Embedding and Watermark Embedding ¨Wong et al. ’s Watermarking Schemes for Authentication and Ownership Verification ¨Watermark Extraction and Image recovery n Experimental Results n Conclusions & Comments 2
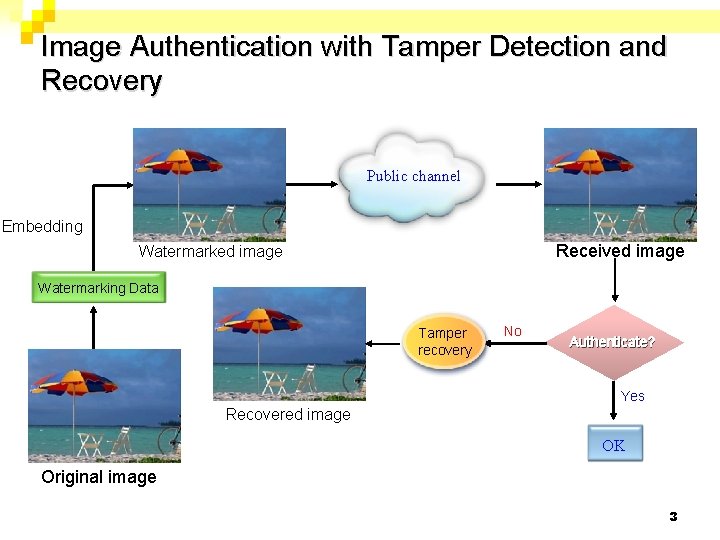
Image Authentication with Tamper Detection and Recovery Public channel Embedding Received image Watermarking Data Tamper recovery No Authenticate? Yes Recovered image OK Original image 3
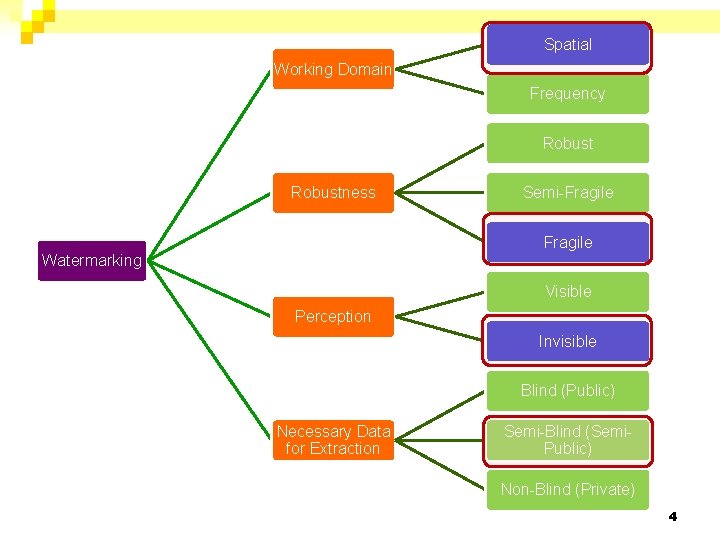
Spatial Working Domain Frequency Robustness Semi-Fragile Watermarking Visible Perception Invisible Blind (Public) Necessary Data for Extraction Semi-Blind (Semi. Public) Non-Blind (Private) 4
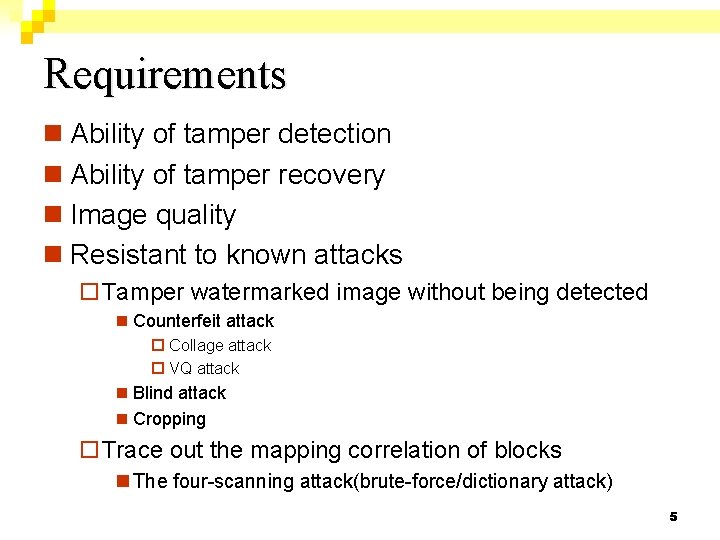
Requirements n Ability of tamper detection n Ability of tamper recovery n Image quality n Resistant to known attacks ¨Tamper watermarked image without being detected n Counterfeit attack ¨ Collage attack ¨ VQ attack n Blind attack n Cropping ¨Trace out the mapping correlation of blocks n The four-scanning attack(brute-force/dictionary attack) 5
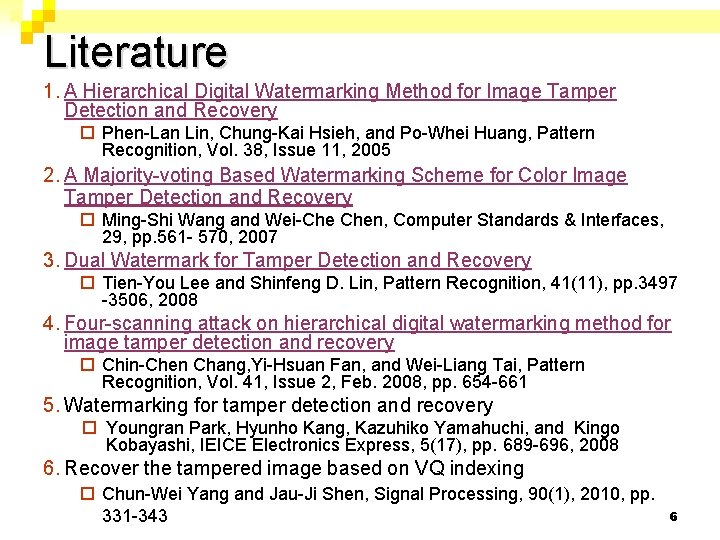
Literature 1. A Hierarchical Digital Watermarking Method for Image Tamper Detection and Recovery ¨ Phen-Lan Lin, Chung-Kai Hsieh, and Po-Whei Huang, Pattern Recognition, Vol. 38, Issue 11, 2005 2. A Majority-voting Based Watermarking Scheme for Color Image Tamper Detection and Recovery ¨ Ming-Shi Wang and Wei-Che Chen, Computer Standards & Interfaces, 29, pp. 561 - 570, 2007 3. Dual Watermark for Tamper Detection and Recovery ¨ Tien-You Lee and Shinfeng D. Lin, Pattern Recognition, 41(11), pp. 3497 -3506, 2008 4. Four-scanning attack on hierarchical digital watermarking method for image tamper detection and recovery ¨ Chin-Chen Chang, Yi-Hsuan Fan, and Wei-Liang Tai, Pattern Recognition, Vol. 41, Issue 2, Feb. 2008, pp. 654 -661 5. Watermarking for tamper detection and recovery ¨ Youngran Park, Hyunho Kang, Kazuhiko Yamahuchi, and Kingo Kobayashi, IEICE Electronics Express, 5(17), pp. 689 -696, 2008 6. Recover the tampered image based on VQ indexing ¨ Chun-Wei Yang and Jau-Ji Shen, Signal Processing, 90(1), 2010, pp. 331 -343 6
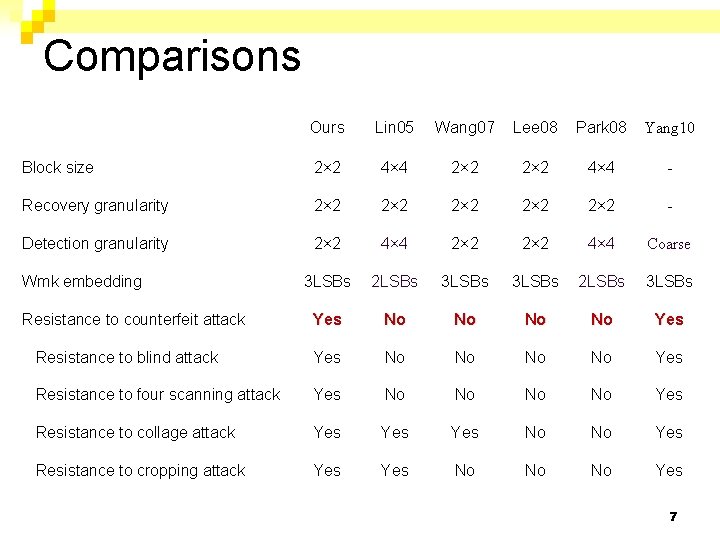
Comparisons Ours Lin 05 Wang 07 Lee 08 Park 08 Yang 10 Block size 2× 2 4× 4 - Recovery granularity 2× 2 2× 2 - Detection granularity 2× 2 4× 4 Coarse 3 LSBs 2 LSBs 3 LSBs Yes No No Yes Resistance to blind attack Yes No No Yes Resistance to four scanning attack Yes No No Yes Resistance to collage attack Yes Yes No No Yes Resistance to cropping attack Yes No No No Yes Wmk embedding Resistance to counterfeit attack 7
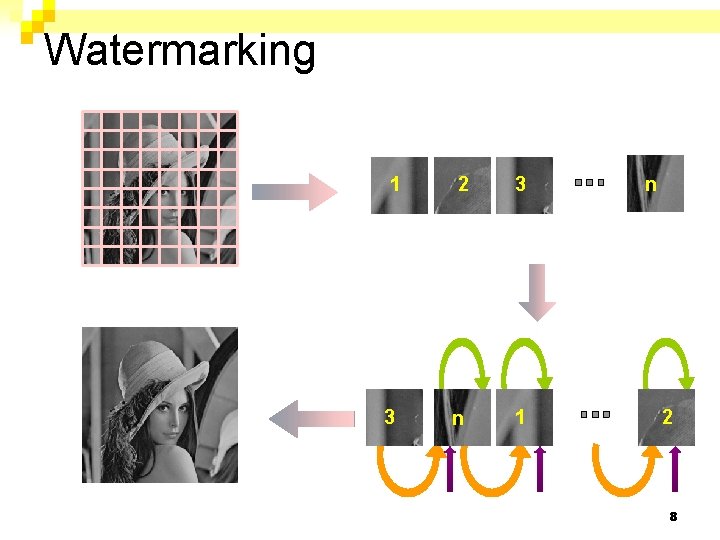
Watermarking 1 2 3 3 n 1 n 2 8
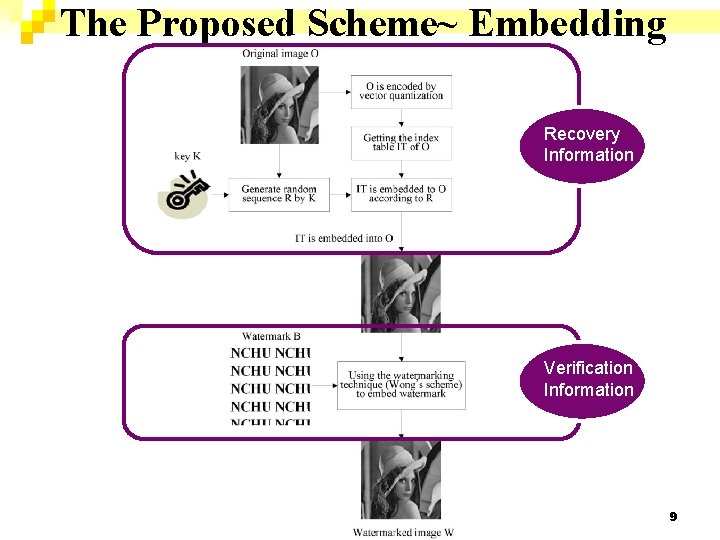
The Proposed Scheme~ Embedding Recovery Information Verification Information 9
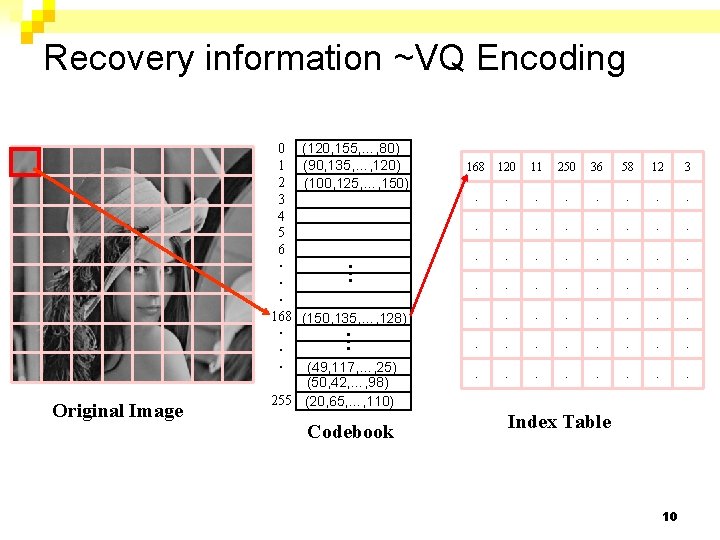
Recovery information ~VQ Encoding 168 120 11 250 36 58 12 3 . . . . (150, 135, …, 128) . . . . … Original Image (120, 155, …, 80) (90, 135, …, 120) (100, 125, …, 150) . . . . … 0 1 2 3 4 5 6 ‧ ‧ ‧ 168 ‧ ‧ ‧ (49, 117, …, 25) (50, 42, …, 98) 255 (20, 65, …, 110) Codebook Index Table 10
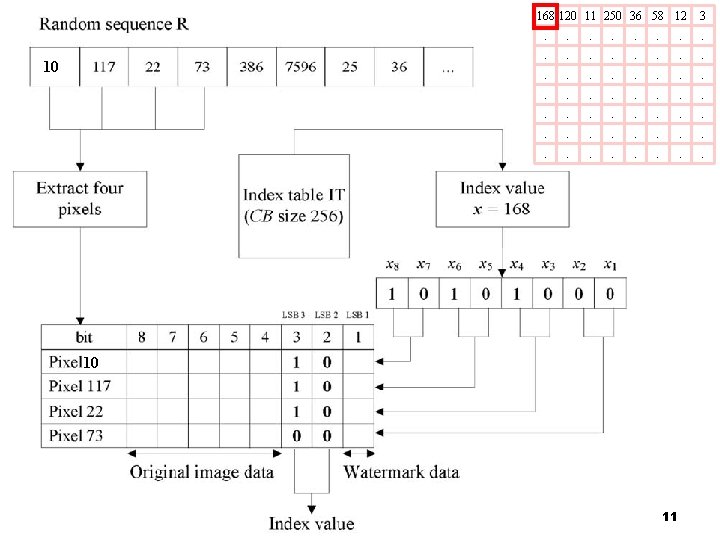
168 120 11 250 36 58 12 10 3 . . . 10 11
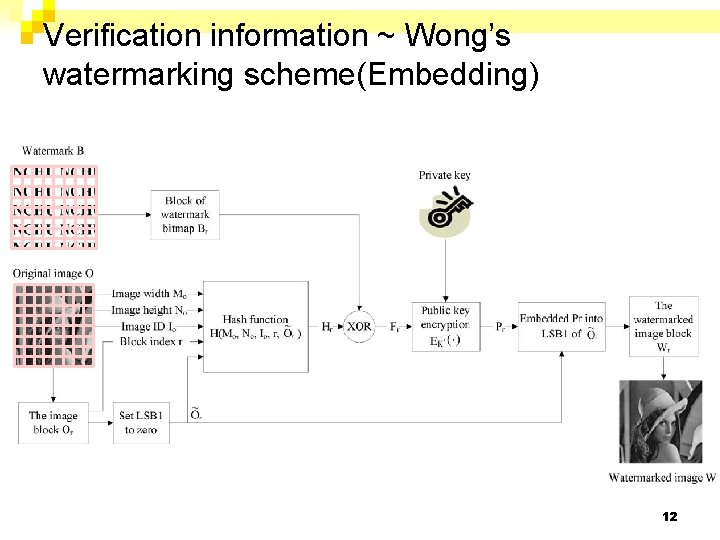
Verification information ~ Wong’s watermarking scheme(Embedding) 12
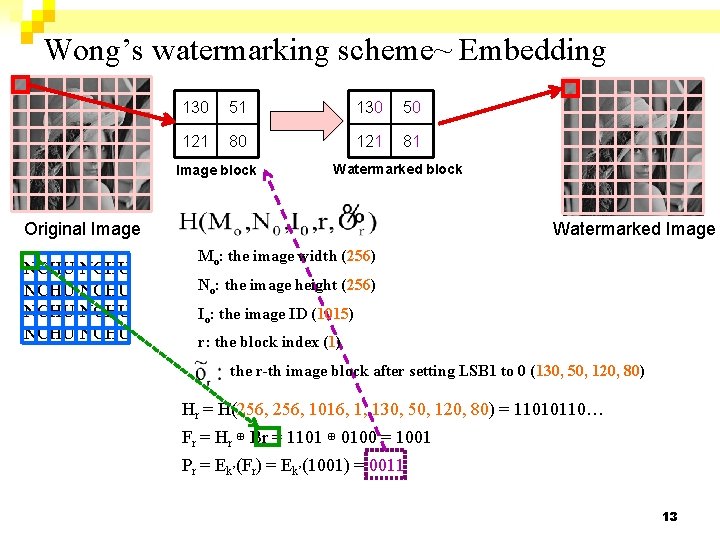
Wong’s watermarking scheme~ Embedding 130 51 130 50 121 81 Image block Watermarked block Original Image NCHU NCHU Watermarked Image Mo: the image width (256) No: the image height (256) Io: the image ID (1015) r: the block index (1) the r-th image block after setting LSB 1 to 0 (130, 50, 120, 80) Hr = H(256, 1016, 1, 130, 50, 120, 80) = 11010110… Fr = Hr ⊕ Br = 1101 ⊕ 0100 = 1001 Pr = Ek’(Fr) = Ek’(1001) = 0011 13
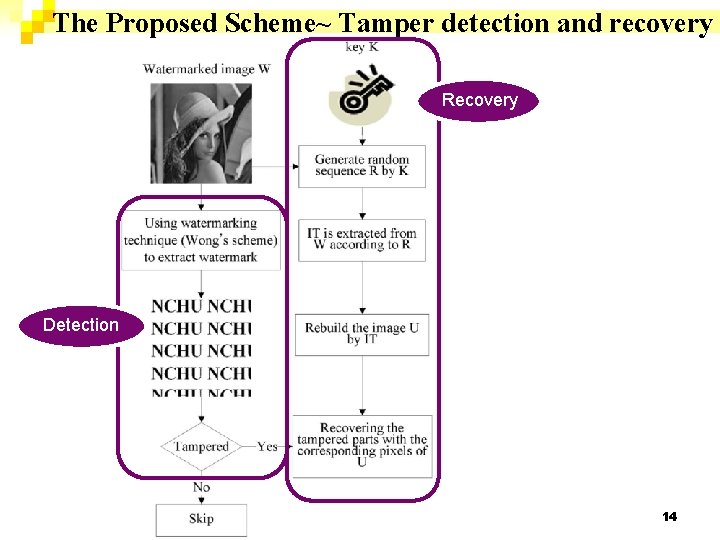
The Proposed Scheme~ Tamper detection and recovery Recovery Detection 14
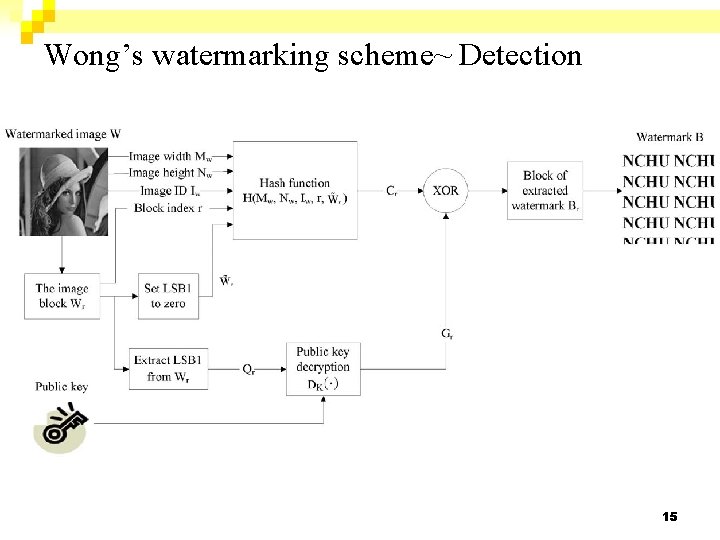
Wong’s watermarking scheme~ Detection 15
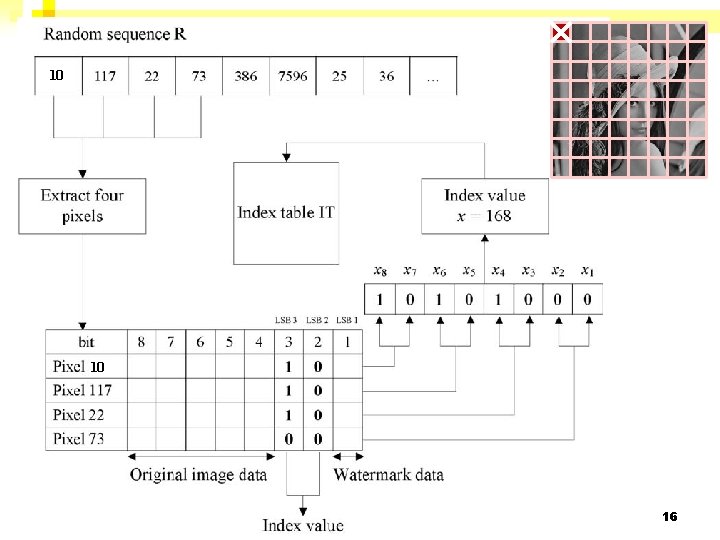
10 10 16
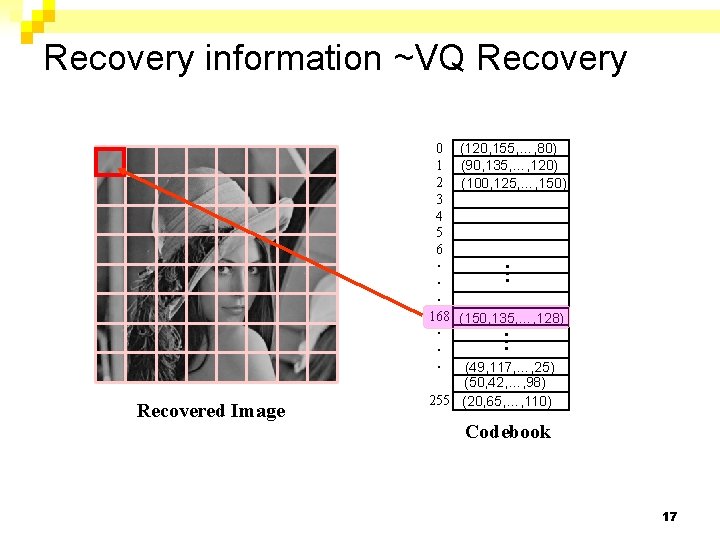
Recovery information ~VQ Recovery (150, 135, …, 128) … Recovered Image (120, 155, …, 80) (90, 135, …, 120) (100, 125, …, 150) … 0 1 2 3 4 5 6 ‧ ‧ ‧ 168 ‧ ‧ ‧ (49, 117, …, 25) (50, 42, …, 98) 255 (20, 65, …, 110) Codebook 17
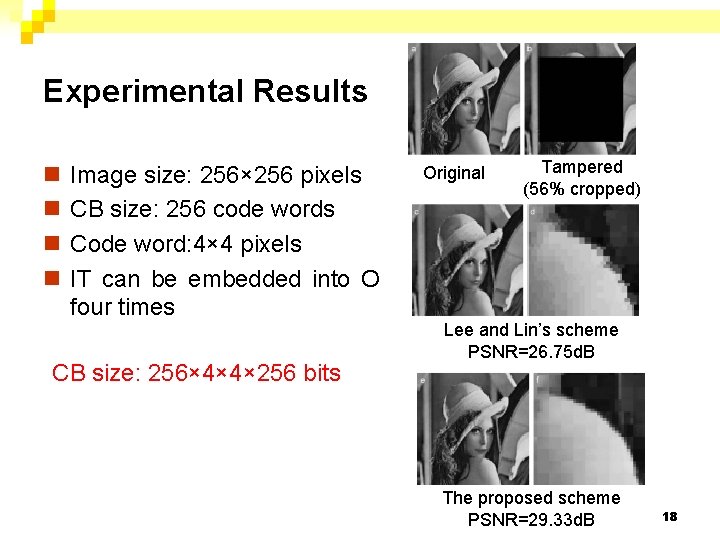
Experimental Results n n Image size: 256× 256 pixels CB size: 256 code words Code word: 4× 4 pixels IT can be embedded into O four times CB size: 256× 4× 4× 256 bits Original Tampered (56% cropped) Lee and Lin’s scheme PSNR=26. 75 d. B The proposed scheme PSNR=29. 33 d. B 18
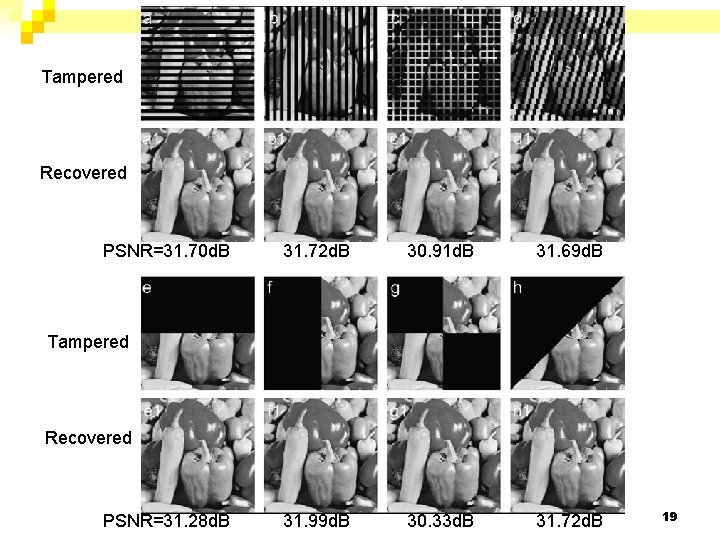
Tampered Recovered PSNR=31. 70 d. B 31. 72 d. B 30. 91 d. B 31. 69 d. B 31. 99 d. B 30. 33 d. B 31. 72 d. B Tampered Recovered PSNR=31. 28 d. B 19
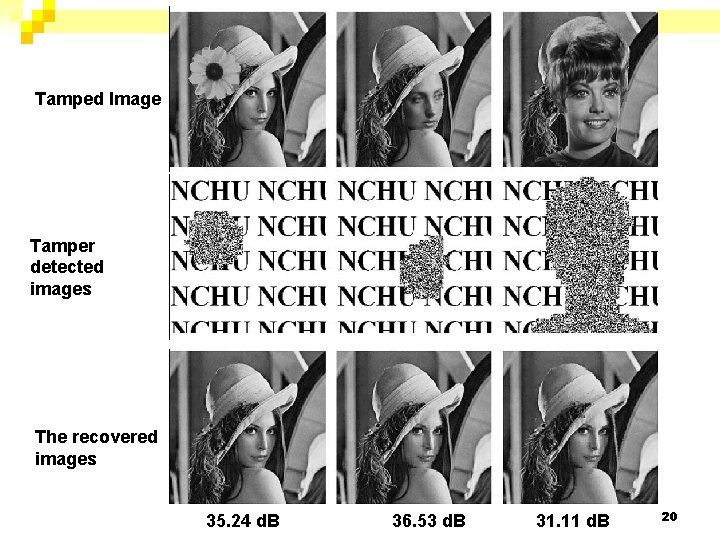
Tamped Image Tamper detected images The recovered images 35. 24 d. B 36. 53 d. B 31. 11 d. B 20
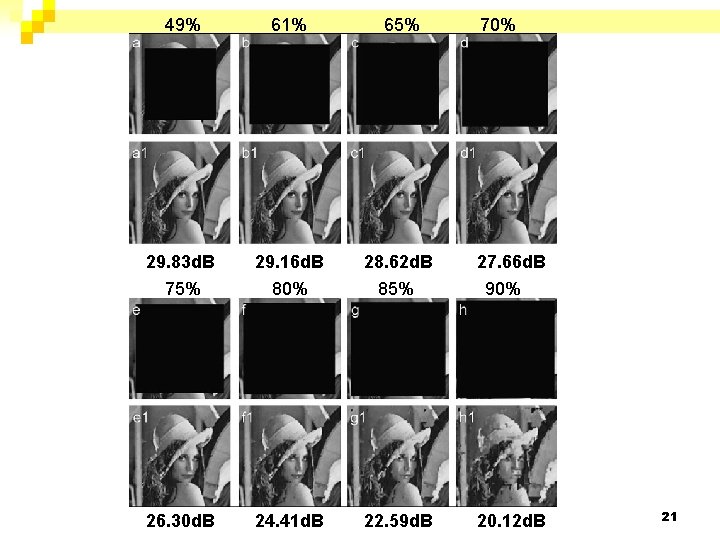
49% 61% 65% 29. 83 d. B 29. 16 d. B 28. 62 d. B 75% 80% 85% 26. 30 d. B 24. 41 d. B 22. 59 d. B 70% 27. 66 d. B 90% 20. 12 d. B 21
Conclusions n An image tamper detection and recovery scheme integrating Wong’s watermarking scheme and VQ is proposed. n The number of times of embedding the recovery info. into the image is adjustable. n The quality of the recovered image is high. n Resistant against the known attacks. (Wong et al. ’s scheme is adopted) 22
Comments n Owing to the use of a public key cryptographic system, the block size should be large enough for the security concern(1024 bits). However, the larger the block size is, the less precision of error detection will be. n Owing to the use of a public key cryptographic system, the computational cost is high. n Additional cost: code book(4× 4 × 256 bits) 23
- Slides: 23