RECONFIGURABLE HARDWARE FOR HIGHSECURITYHIGHPERFORMANCE EMBEDDED SYSTEMS THE SAFES
RECONFIGURABLE HARDWARE FOR HIGH-SECURITY/HIGHPERFORMANCE EMBEDDED SYSTEMS: THE SAFES PERSPECTIVE Guy Gogniat, Tilman Wolf, Wayne Burleson, Jean-Philippe Diguet, Lilian Bossuet and Roman Baslin Presented by: Wei Zang Xin Guan Mar. 03, 2010
THE TOPIC(RECONFIGURABLE HARDWARE FOR HIGHSECURITY/HIGH-PERFORMANCE EMBEDDED SYSTEMS: THE SAFES PERSPECTIVE) SAFES? –Security architecture for embedded systems Purpose? Provide high-Security and high-performance for a system Built on reconfigurable hardware - FPGA 2
OUTLINE Attacks and countermeasures on embedded systems SAFES Architecture RC 6 Architecture Monitoring for Performance Policy AES Datapath Implementation Comparison 3

OUTLINE Attacks and countermeasures on embedded systems SAFES Architecture RC 6 Architecture Monitoring for Performance Policy AES Datapath Implementation Comparison 4
SECURITY AND ATTACKS Security objective Protection of private data, design and the system Attacks objectives Break security in order to Access, change or destroy private data Change some module, copy or destroy design Change behavior or destroy the system Challenges ( attack point ) Tamper resistance Facing increasing number of attacks from physical to software Assurance Continue to operate reliably despite attacks 5
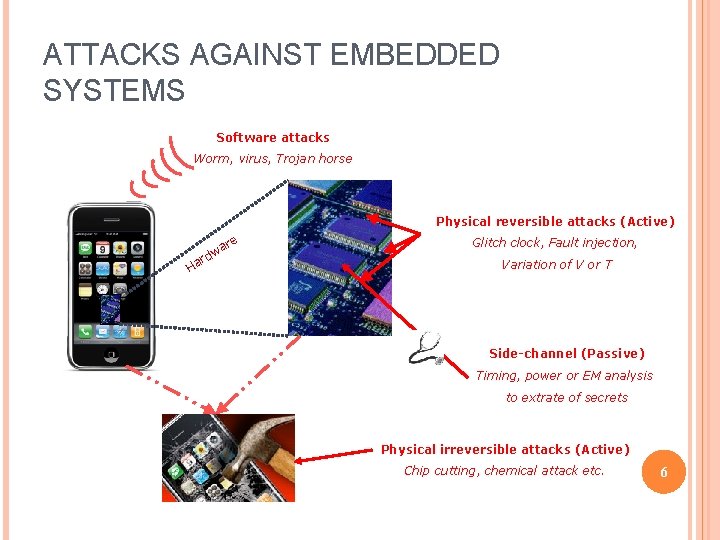
ATTACKS AGAINST EMBEDDED SYSTEMS Software attacks Worm, virus, Trojan horse Physical reversible attacks (Active) re a dw r Ha Glitch clock, Fault injection, Variation of V or T Side-channel (Passive) Timing, power or EM analysis to extrate of secrets Physical irreversible attacks (Active) Chip cutting, chemical attack etc. 6
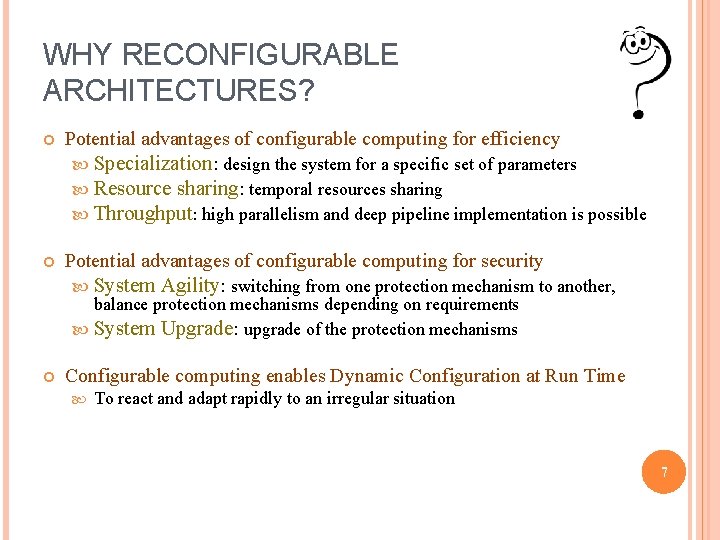
WHY RECONFIGURABLE ARCHITECTURES? Potential advantages of configurable computing for efficiency Specialization: design the system for a specific set of parameters Resource sharing: temporal resources sharing Throughput: high parallelism and deep pipeline implementation is possible Potential advantages of configurable computing for security System Agility: switching from one protection mechanism to another, balance protection mechanisms depending on requirements System Upgrade: upgrade of the protection mechanisms Configurable computing enables Dynamic Configuration at Run Time To react and adapt rapidly to an irregular situation 7

OUTLINE Attacks and countermeasures on embedded systems SAFES Architecture RC 6 Architecture Monitoring for Performance Policy AES Datapath Implementation Comparison 8
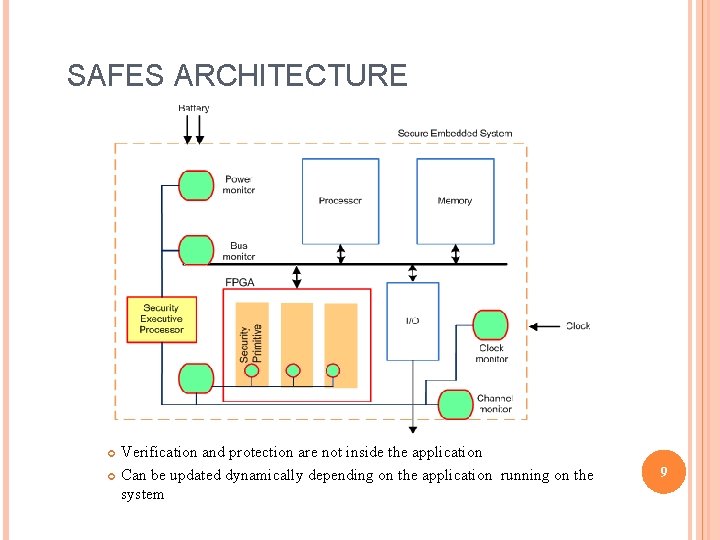
SAFES ARCHITECTURE Verification and protection are not inside the application Can be updated dynamically depending on the application running on the system 9
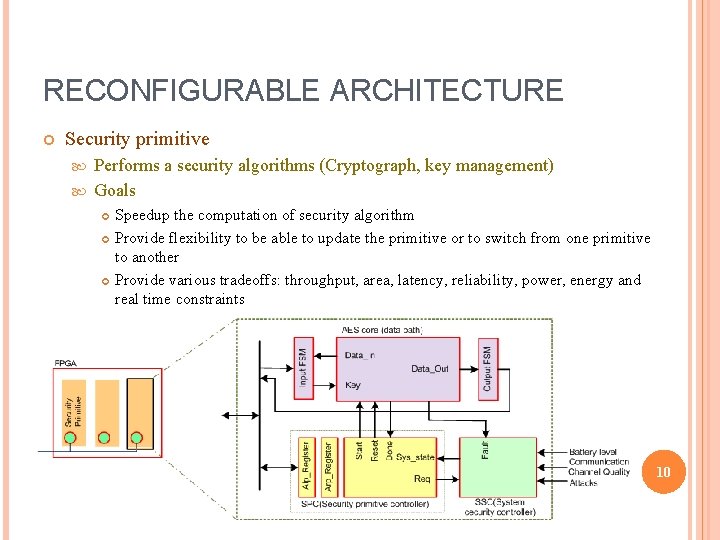
RECONFIGURABLE ARCHITECTURE Security primitive Performs a security algorithms (Cryptograph, key management) Goals Speedup the computation of security algorithm Provide flexibility to be able to update the primitive or to switch from one primitive to another Provide various tradeoffs: throughput, area, latency, reliability, power, energy and real time constraints 10
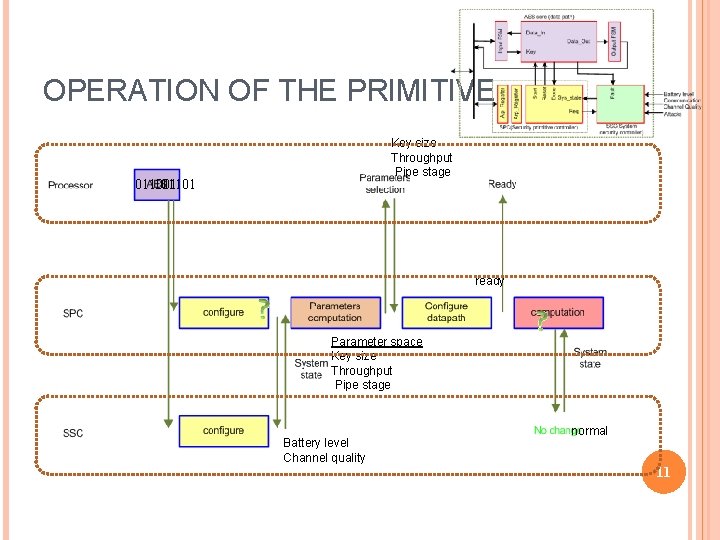
OPERATION OF THE PRIMITIVE Key size Throughput Pipe stage 011001 101101 ready Parameter space Key size Throughput Pipe stage Battery level Channel quality normal 11
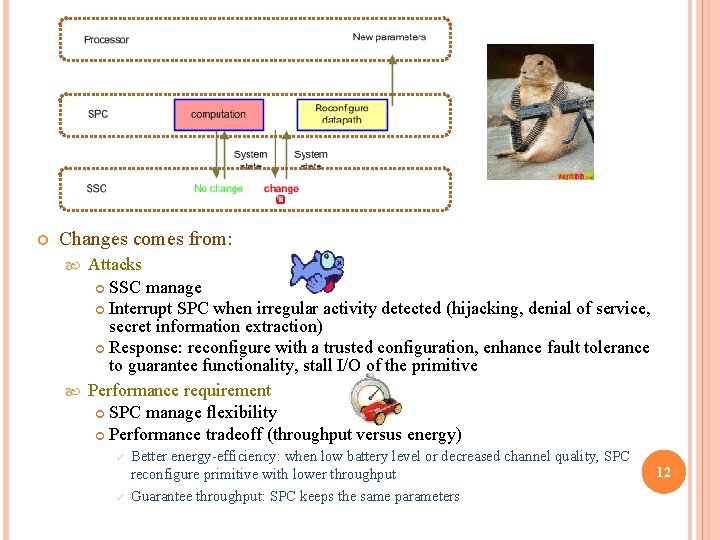
Changes comes from: Attacks SSC manage Interrupt SPC when irregular activity detected (hijacking, denial of service, secret information extraction) Response: reconfigure with a trusted configuration, enhance fault tolerance to guarantee functionality, stall I/O of the primitive Performance requirement SPC manage flexibility Performance tradeoff (throughput versus energy) ü ü Better energy-efficiency: when low battery level or decreased channel quality, SPC reconfigure primitive with lower throughput Guarantee throughput: SPC keeps the same parameters 12
OUTLINE Attacks and countermeasures on embedded systems SAFES Architecture RC 6 Architecture Monitoring for Performance Policy AES Datapath Implementation Comparison 13
RC 6 CASE STUDY RC 6 and AES are two major cryptography algorithms in secure private communication over the Internet. Process a block of data with block size 128 bit. Different Key Sizes, 128 bit, 192 bit, and 256 bit. Primitive operation, includes data-dependent rotations, modular addition and XOR operations, 32 bit multiplication. 14
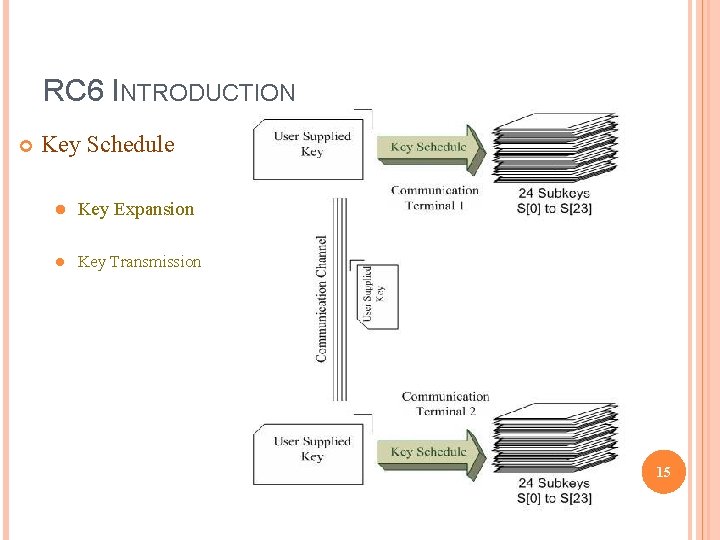
RC 6 INTRODUCTION Key Schedule l Key Expansion l Key Transmission 15
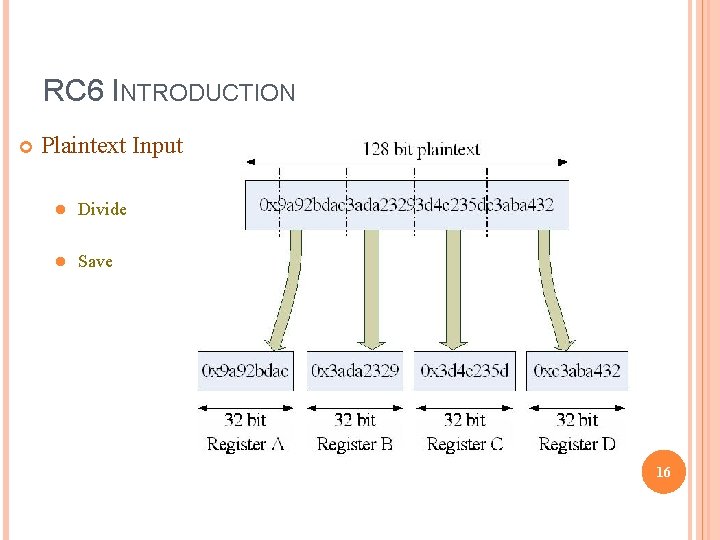
RC 6 INTRODUCTION Plaintext Input l Divide l Save 16

RC 6 INTRODUCTION Encryption 17
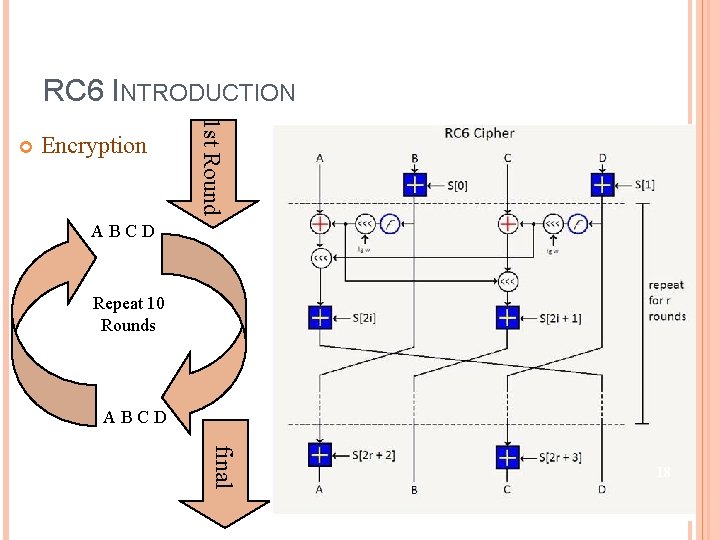
RC 6 INTRODUCTION Encryption 1 st Round ABCD Repeat 10 Rounds ABCD final 18
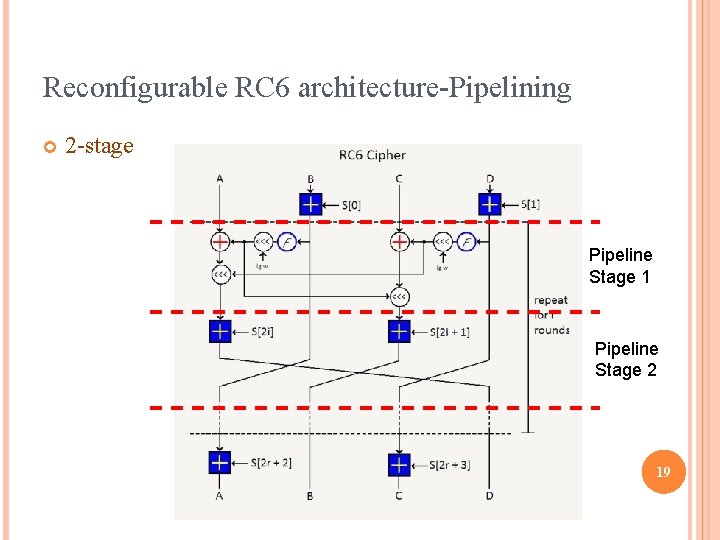
Reconfigurable RC 6 architecture-Pipelining 2 -stage Pipeline Stage 1 Pipeline Stage 2 19
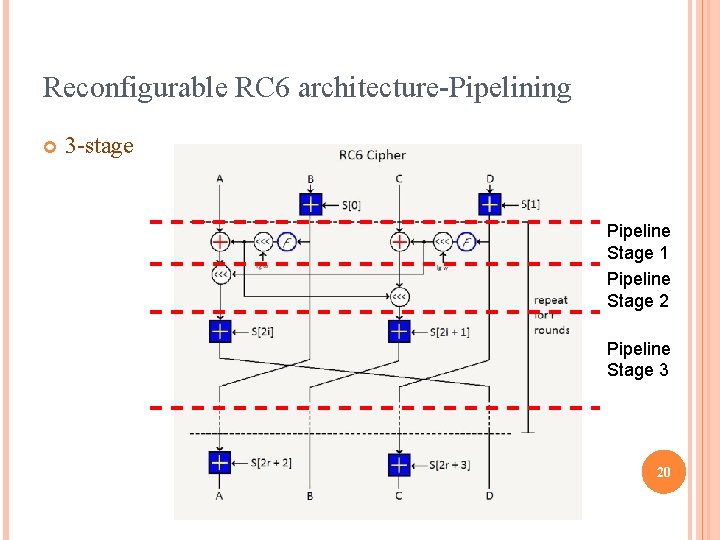
Reconfigurable RC 6 architecture-Pipelining 3 -stage Pipeline Stage 1 Pipeline Stage 2 Pipeline Stage 3 20
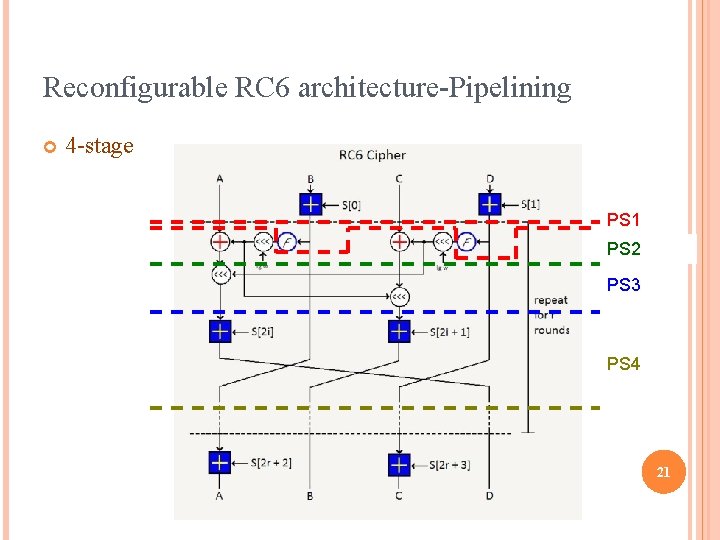
Reconfigurable RC 6 architecture-Pipelining 4 -stage PS 1 PS 2 PS 3 PS 4 21

Architecture Comparison 22
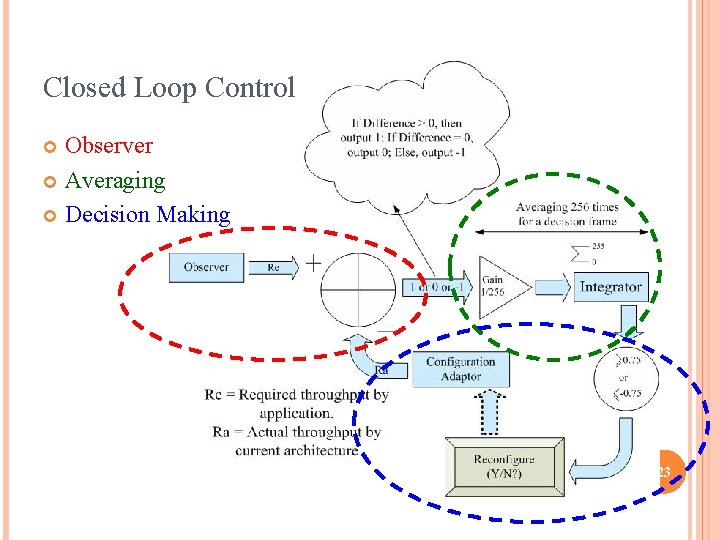
Closed Loop Control Observer Averaging Decision Making 23
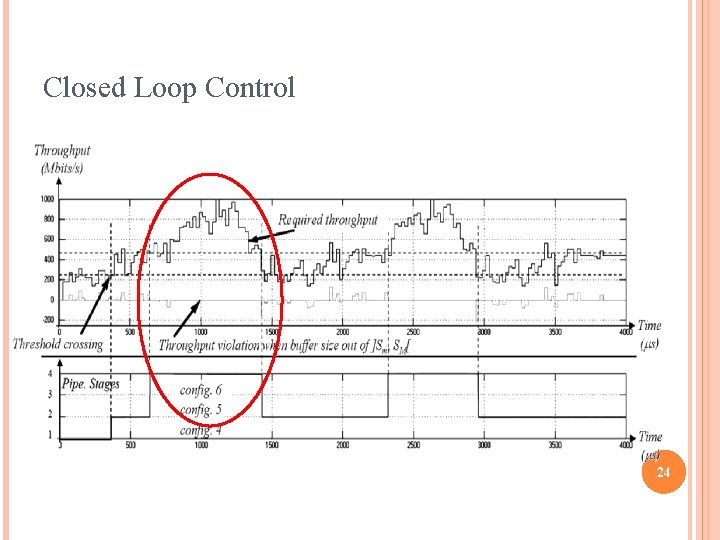
Closed Loop Control 24
OUTLINE Attacks and countermeasures on embedded systems SAFES Architecture RC 6 Architecture Monitoring for Performance Policy AES Datapath Implementation Comparison 25
AES Case Study An encryption standard adopted by the U. S. government. Each AES cipher has a 128 -bit block size, with key sizes of 128, 192 and 256 bits AES operates on a 4× 4 array of bytes, termed the state. AES cipher is specified as a number of repetitions of transformation rounds that convert the input plaintext into the final output of ciphertext. 26
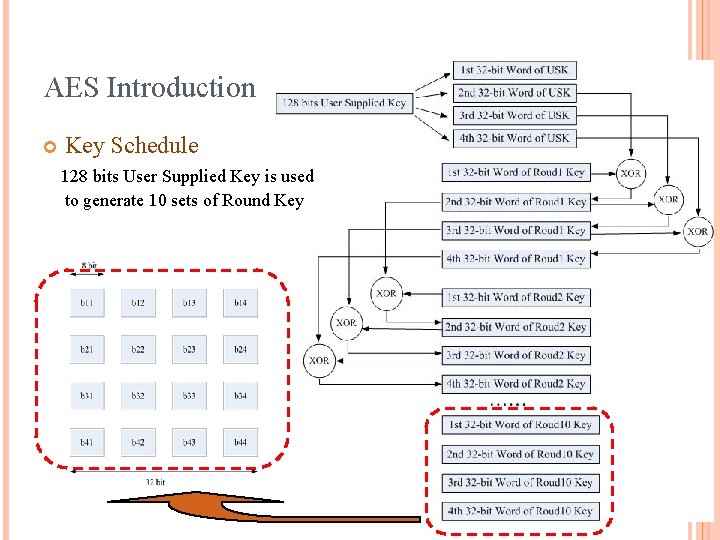
AES Introduction Key Schedule 128 bits User Supplied Key is used to generate 10 sets of Round Key 27
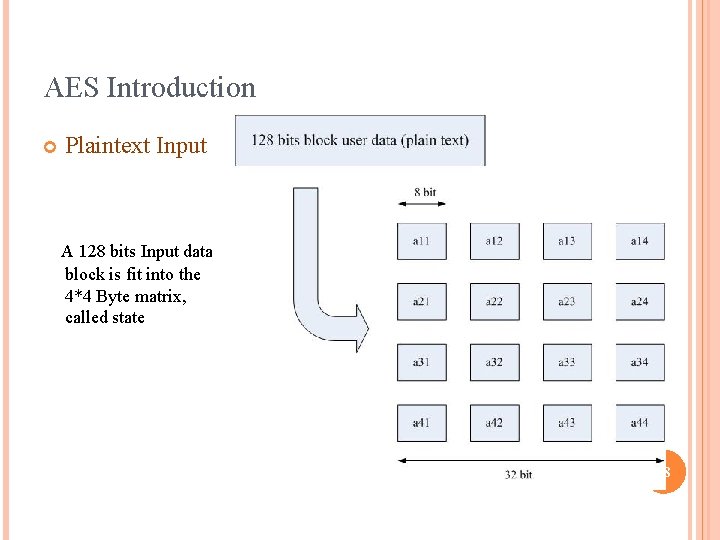
AES Introduction Plaintext Input A 128 bits Input data block is fit into the 4*4 Byte matrix, called state 28

AES Introduction Round Operation Sub. Bytes l Shift. Rows l Mix. Columns l Add. Round. Key l 29
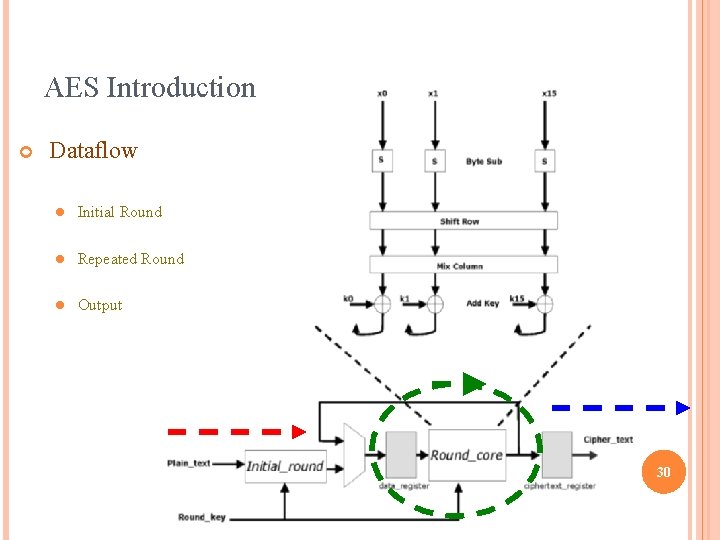
AES Introduction Dataflow l Initial Round l Repeated Round l Output 30
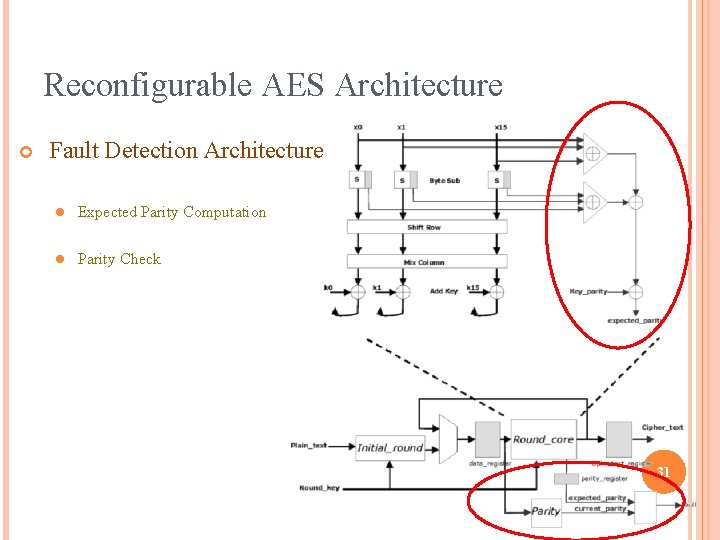
Reconfigurable AES Architecture Fault Detection Architecture l Expected Parity Computation l Parity Check 31

Reconfigurable AES Architecture Fault Tolerant Architecture l TMR (Triple Modular Redundancy) l High overhead 32
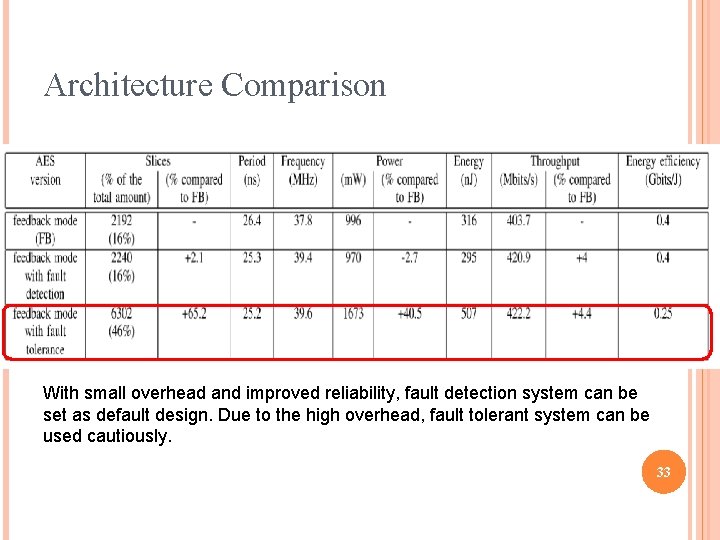
Architecture Comparison With small overhead and improved reliability, fault detection system can be set as default design. Due to the high overhead, fault tolerant system can be used cautiously. 33
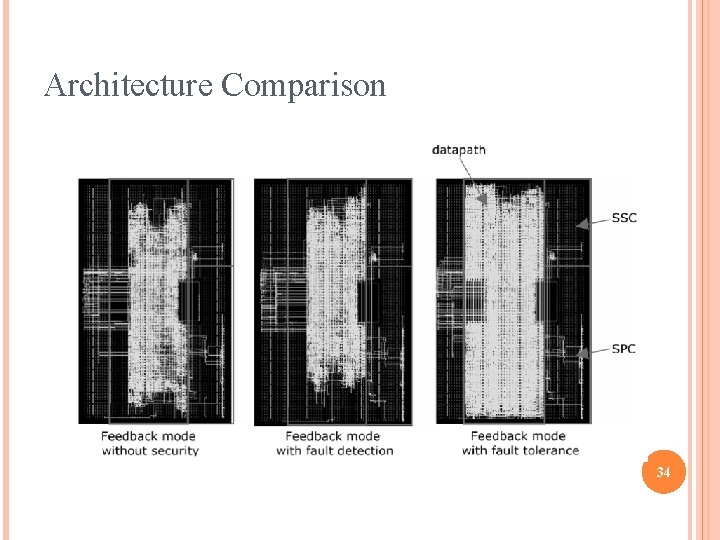
Architecture Comparison 34
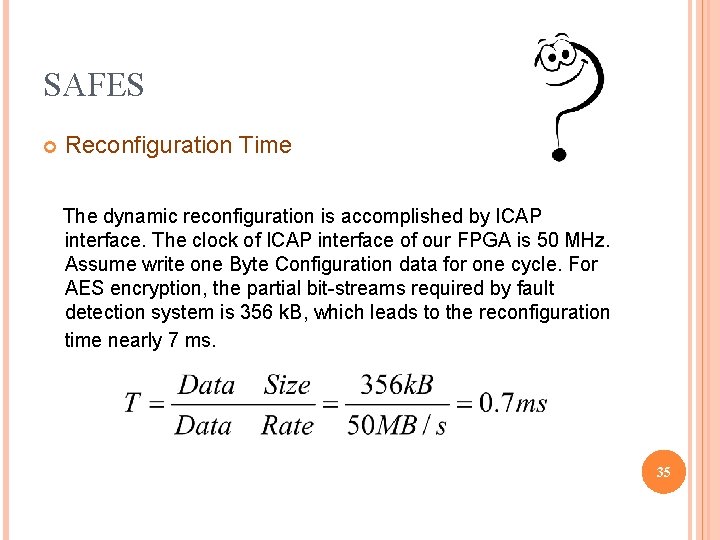
SAFES Reconfiguration Time The dynamic reconfiguration is accomplished by ICAP interface. The clock of ICAP interface of our FPGA is 50 MHz. Assume write one Byte Configuration data for one cycle. For AES encryption, the partial bit-streams required by fault detection system is 356 k. B, which leads to the reconfiguration time nearly 7 ms. 35
CONCLUSIONS SAFES Based on reconfigurable hardware to provide high performance and flexibility and relies on hardware monitors to build instruction detection systems Includes: Reconfigurable security primitives Reconfigurable hardware monitors Hierarchy of secure controllers at the primitive, system and executive level Cases on RC 6 and AES The flexibility of our solution enables the realization of an energyefficient system while addressing the security issue. 36
- Slides: 36