RC 4 Stream Ciphers Blowfish RC 5 Block
RC 4 -Stream Ciphers Blowfish, RC 5 Block Ciphers M. Sakalli, Marmara Univ. Chapter 6 of Cryptography and Network Security by William Stallings Modified from the original slides of Lawrie Brown
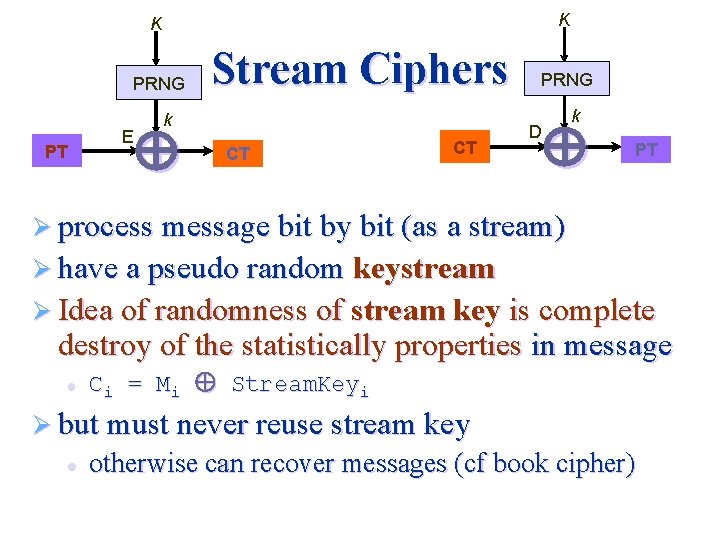
K K PRNG PT E Stream Ciphers k CT CT PRNG D k PT Ø process message bit by bit (as a stream) Ø have a pseudo random keystream Ø Idea of randomness of stream key is complete destroy of the statistically properties in message l Ci = Mi Stream. Keyi Ø but must never reuse stream key l otherwise can recover messages (cf book cipher)

Stream Cipher Properties Ø some design considerations are: l l l long sequence with no periodicities statistically random depends on large enough key large linear complexity correlation immunity confusion, diffusion (cryptographically) Ø can be as secure as a block cipher with same size key Ø but simpler & faster
(Ron Rivest!!! Cipher) RC 4 the period of the cipher is overwhelmingly likely to be greater than 10100 Ø Runs faster - five/fifteen times than DES/3 DES Ø Used in Ø l l SSL/TLS (Secure socket, transport layer security) between web browsers and servers, IEEE 802. 11 wirelss LAN std: WEP (Wired Equivalent Privacy), WPA (Wi. Fi Protocol Access) protocol a proprietary cipher owned by RSA, kept secret, released at the sites of Cyberpunk remailers. Ø simple but effective, variable key length from 1 to 256 bytes; starts with an array S of numbers: 0. . 255 and after initialization 0 S[. ] 255. . Ø
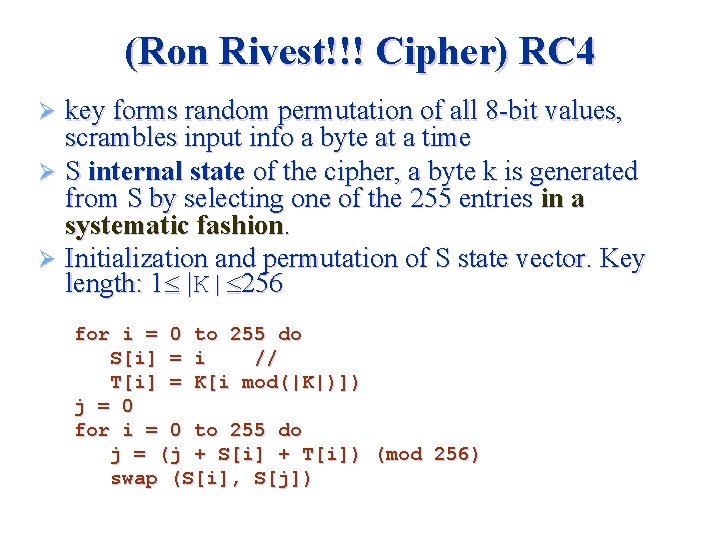
(Ron Rivest!!! Cipher) RC 4 key forms random permutation of all 8 -bit values, scrambles input info a byte at a time Ø S internal state of the cipher, a byte k is generated from S by selecting one of the 255 entries in a systematic fashion. Ø Initialization and permutation of S state vector. Key length: 1 |K| 256 Ø for i = 0 to 255 do S[i] = i // T[i] = K[i mod(|K|)]) j = 0 for i = 0 to 255 do j = (j + S[i] + T[i]) (mod 256) swap (S[i], S[j])

KSA Key scheduling Ø encryption continues shuffling array values Ø sum of shuffled pair selects "stream key" value from permutation Ø XOR S[t] with next byte of message to en/decrypt i = j = 0 for each message byte Mi i = (i + 1) (mod 256) j = (j + S[i]) (mod 256) swap(S[i], S[j]) t = (S[i] + S[j]) (mod 256) Ci = Mi XOR S[t]
RC 4 Encryption Ø claimed secure against known attacks l l l have some analyses in a number of papers, but none to be practical with a reasonable key length, such as 128 bits. In one authors demonstrate that in the case of WEP, it is vulnerable to a particular attack approach due to the initialization of the keys but not the RC 4 itself but the way in which keys are generated. Remedied by changing the way in which keys are generated. Ø since RC 4 is a stream cipher, must never reuse a key
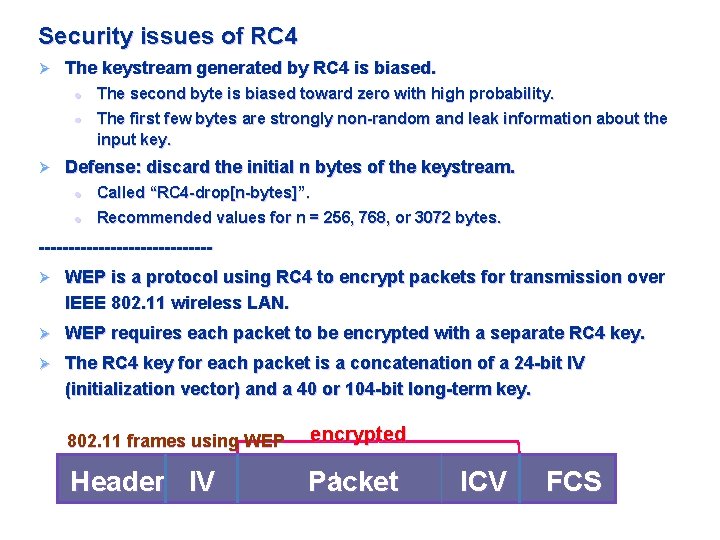
Security issues of RC 4 Ø The keystream generated by RC 4 is biased. l l Ø The second byte is biased toward zero with high probability. The first few bytes are strongly non-random and leak information about the input key. Defense: discard the initial n bytes of the keystream. l Called “RC 4 -drop[n-bytes]”. l Recommended values for n = 256, 768, or 3072 bytes. --------------Ø WEP is a protocol using RC 4 to encrypt packets for transmission over IEEE 802. 11 wireless LAN. Ø WEP requires each packet to be encrypted with a separate RC 4 key. Ø The RC 4 key for each packet is a concatenation of a 24 -bit IV (initialization vector) and a 40 or 104 -bit long-term key. 802. 11 frames using WEP encrypted Header IV l Packet ICV FCS
Ø Fluhrer, Mantin, and Shamir showed that: Ø If the same secret key is used with numerous IVs, and the attacker can obtain the first word of RC 4 output (keystream) corresponding to each IV, then he can construct the secret key with little effort. Ø The first word is known for many plaintext packets. Ø Recall: Ciphertext = plaintext keystream Ø So, the first word of RC output (keystream) can be obtained. Ø Tews, Weinmann, and Pyshkin wrote an article, “Breaking 104 bit WEP in less than 60 seconds, ” discussing how to discover the RC 4 key by analyzing the easily identified ARP packets. 9

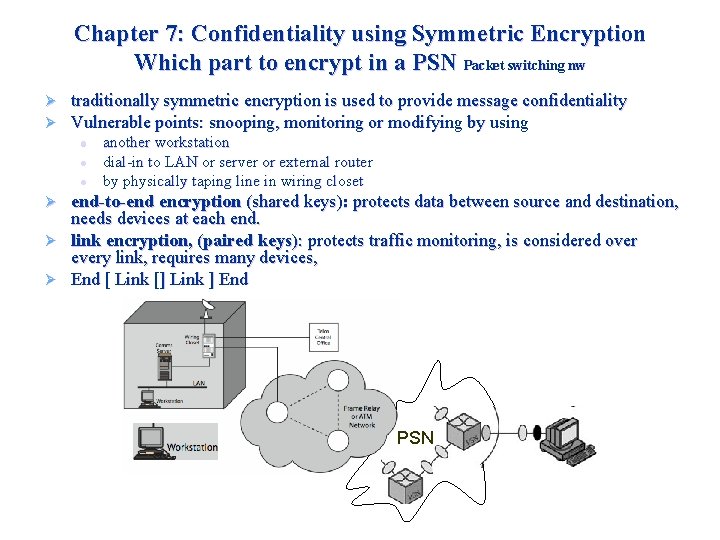
Chapter 7: Confidentiality using Symmetric Encryption Which part to encrypt in a PSN Packet switching nw Ø Ø traditionally symmetric encryption is used to provide message confidentiality Vulnerable points: snooping, monitoring or modifying by using l l l another workstation dial-in to LAN or server or external router by physically taping line in wiring closet end-to-end encryption (shared keys): protects data between source and destination, needs devices at each end. Ø link encryption, (paired keys): protects traffic monitoring, is considered over every link, requires many devices, Ø End [ Link [] Link ] End Ø PSN
Placement of Encryption in the various levels of OSI Encapsulation Model (b) TCP Layer level (c) Link Layer Level
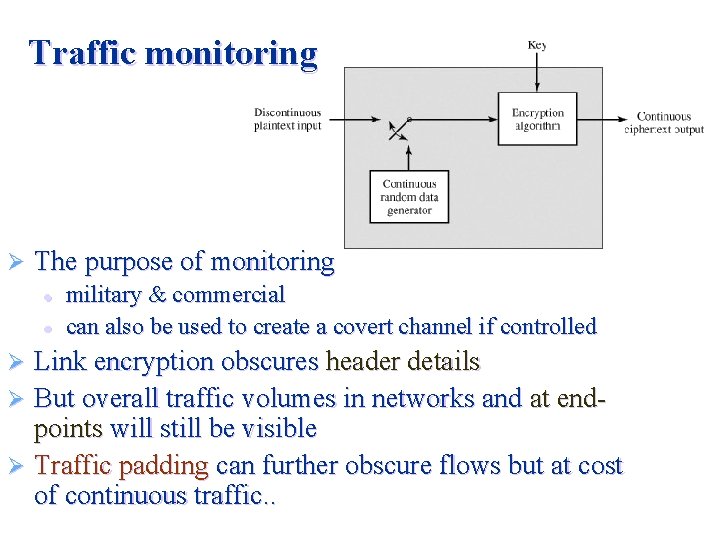
Traffic monitoring Ø The purpose of monitoring l l military & commercial can also be used to create a covert channel if controlled Link encryption obscures header details Ø But overall traffic volumes in networks and at endpoints will still be visible Ø Traffic padding can further obscure flows but at cost of continuous traffic. . Ø

How to distribute key symmetric schemes require to share a common secret key Ø often secure system failure due to a break in the key distribution scheme Ø given parties A and B have various key distribution alternatives: Ø 1. 2. Ø Physically delivery from A to B Third party can issue & deliver key to A & B, if A & B have secure communications with a third party C, C can relay key between A & B Distribution of Key is based on a Hierarchy, at least two levels of keys are used l temporary key referred as session key • used for the duration of a logical connection between users • for one logical session then discarded l master key • used to encrypt session keys • shared by user & key distribution center
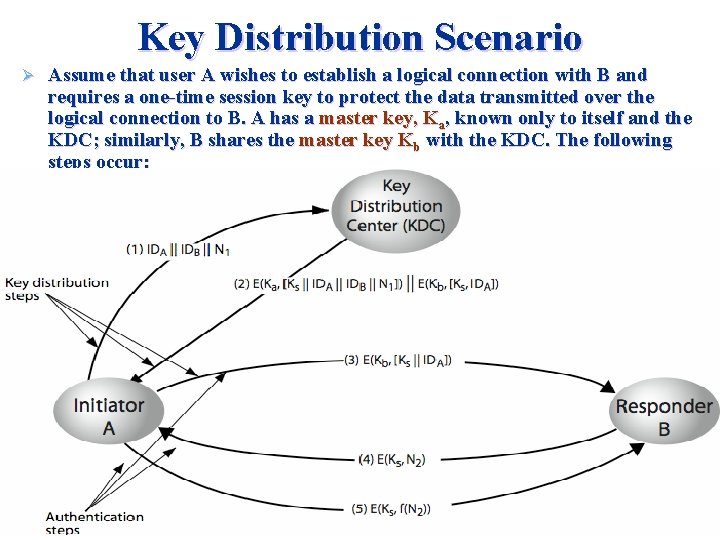
Key Distribution Scenario Ø Assume that user A wishes to establish a logical connection with B and requires a one-time session key to protect the data transmitted over the logical connection to B. A has a master key, Ka, known only to itself and the KDC; similarly, B shares the master key Kb with the KDC. The following steps occur:
A issues a request to the KDC for a session key to B including the identity of A and B and a unique session identifier, N 1, valid for this transaction, nonce: a timestamp, a counter, or a random number; differs with each request. I. e. to prevent masquerading, suppose something like, a random number. b. The KDC’s response to A: KA Thus, only A can decrypt the message. One-time session key, KS, to be used for the session. Items for A: The original message so that, A can verify the original request not altered before reception by the KDC. The nonce, so that this is not a replay of some previous request Items for B: The one time session key KS and IDSA (e. g. , its network address), both encrypted with KB (the master key that the KDC shares with B). a.

c. A stores KS for use in the upcoming session and forwards to B the information originated from the KDC for B, namely, E(KB, [KS || IDA]). Because this information is encrypted with KB, it is protected from eavesdropping. B knows the session key (KS), and A, and the information that must have originated at the KDC Kb. --A secure KS delivered to A and B, to proceed with protected exchange---. 1. Protected exchange with sym key KS used by A and B for encryption. d. B sends a nonce, N 2, E(KS N 2). A responds with E(KS f(N 2)). (e. g. , adding one). . Last steps involve authentication. 2.

Random Numbers uses of random numbers: nonces in authentication protocols to prevent replay, session keys, public key generation Ø statistically random, uniform distribution, Ø l Ø independent so that unpredictable l l Ø If a problem is to hard, time-consuming, then use randomization, i. e. RSA public key exchange, large prime number N, sqrt(10150) (ie reciprocal authentication and session key generation), where the requirement is not so much that the numbers be statistically random but be unpredictable. With "true" random sequences, each number is statistically independent, therefore unpredictable. However used seldom. Often deterministic algorithmic techniques used to create “random numbers”. “Pseudorandom Number Generators (PRNGs)”. Care to be taken that an opponent not be able to predict future elements.
Linear Congruential Generator Ø The most common to produce random sequences and an iterative technique: Xn+1 = (a. Xn + c) mod m Ø Only a small number of suitable values available: Consider the values a = 7, c = 0, m = 32, and X 0 = 1. This generates the sequence {7, 17, 23, 1, 7, etc. }, which is also clearly unsatisfactory. Of the 32 possible values, only 4 are used; thus, the sequence is said to have a period of 4. If, instead, we change the value of a to 5, then the sequence is {5, 29, 17, 21, 9, 13, 1, 5, etc. }, which increases the period to 8.

Linear Congruential Generator Ø m to be very large, for producing a long series of distinct random numbers, nearly equal to the maximum representable nonnegative integer for a given computer, equal to m=231 -1. l l l Function should generate a long full-period sequence between 0 and m, Generated deterministically, should appear random. Efficient implementation with 32 -bit. an attacker can reconstruct sequence given a small number of values. 3 unknowns, a, c, m, 3 equations. Ø One solution is using internal system clock to modify the random number stream. Ø l l Restart the sequence after every N numbers with the current clock value (mod m) as the new seed Add the current clock value to each random number (mod m).
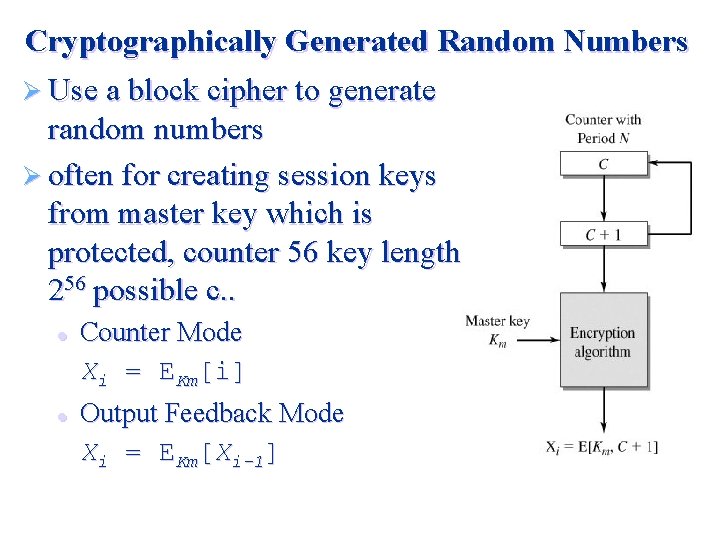
Cryptographically Generated Random Numbers Ø Use a block cipher to generate random numbers Ø often for creating session keys from master key which is protected, counter 56 key length, 256 possible c. . l l Counter Mode Xi = EKm[i] Output Feedback Mode Xi = EKm[Xi-1]
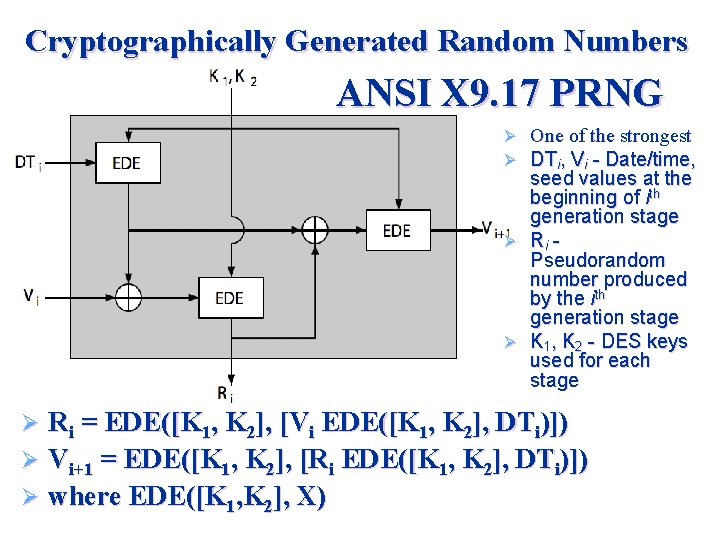
Cryptographically Generated Random Numbers ANSI X 9. 17 PRNG One of the strongest DTi, Vi - Date/time, seed values at the beginning of ith generation stage Ø Ri Pseudorandom number produced by the ith generation stage Ø K 1, K 2 - DES keys used for each stage Ø Ø Ri = EDE([K 1, K 2], [Vi EDE([K 1, K 2], DTi)]) Ø Vi+1 = EDE([K 1, K 2], [Ri EDE([K 1, K 2], DTi)]) Ø where EDE([K 1, K 2], X) Ø
Blum Shub Generator Ø Ø based on public key algorithms use least significant bit from iterative equation: l l l Ø Ø Ø xi = xi-12 mod n where n=p. q, and primes p, q should be congruent to = 3 mod 4 = p, q and gcd(φ(p-1), φ(q-1)) should be small unpredictable, passes next-bit test security rests on difficulty of factoring N is unpredictable given any run of bits slow, since very large numbers must be used too slow for cipher use, good for key generation
Natural Random Noise Ø best source is natural randomness in real world Ø find a regular but random event and monitor Ø do generally need special h/w to do this l eg. radiation counters, radio noise, audio noise, thermal noise in diodes, leaky capacitors, mercury discharge tubes etc Ø starting to see such h/w in new CPU's Ø problems of bias or uneven distribution in signal l l have to compensate for this when sample and use best to only use a few noisiest bits from each sample
Published Sources Ø a few published collections of random numbers Ø Rand Co, in 1955, published 1 million numbers l l generated using an electronic roulette wheel has been used in some cipher designs cf Khafre Ø earlier Tippett in 1927 published a collection Ø issues are that: l l these are limited too well-known for most uses
A symmetric block cipher Blowfish Ø Ø Designed by Bruce Schneier in 1993/94 characteristics l l Ø Ø Ø has been implemented in various products uses a 32 to 448 bit key used to generate l l Ø fast implementation on 32 -bit CPUs compact in use of memory simple structure for analysis/implementation variable security by varying key size 18 32 -bit subkeys stored in K-array Kj four 8 x 32 S-boxes stored in Si, j key schedule consists of: l l initialize P-array and then 4 S-boxes using pi XOR P-array with key bits (reuse as needed) loop repeatedly encrypting data using current P & S and replace successive pairs of P then S values requires 521 encryptions, hence slow in re-keying
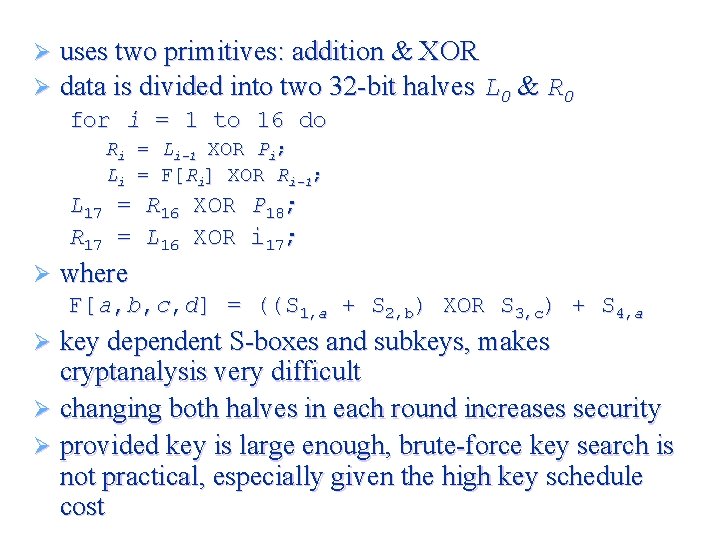
Ø Ø uses two primitives: addition & XOR data is divided into two 32 -bit halves L 0 & R 0 for i = 1 to 16 do Ri = Li-1 XOR Pi; Li = F[Ri] XOR Ri-1; L 17 R 17 Ø = = R 16 L 16 XOR P 18; i 17; where F[a, b, c, d] = ((S 1, a + S 2, b) XOR S 3, c) + S 4, a key dependent S-boxes and subkeys, makes cryptanalysis very difficult Ø changing both halves in each round increases security Ø provided key is large enough, brute-force key search is not practical, especially given the high key schedule cost Ø
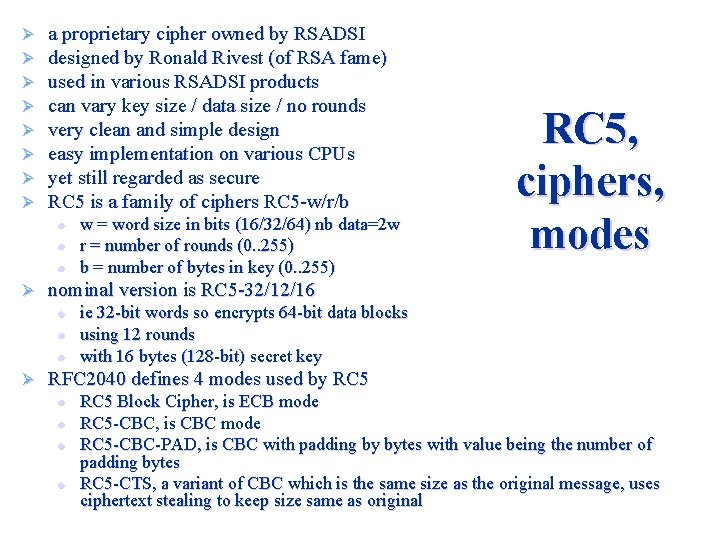
Ø Ø Ø Ø a proprietary cipher owned by RSADSI designed by Ronald Rivest (of RSA fame) used in various RSADSI products can vary key size / data size / no rounds very clean and simple design easy implementation on various CPUs yet still regarded as secure RC 5 is a family of ciphers RC 5 -w/r/b l l l Ø nominal version is RC 5 -32/12/16 l l l Ø w = word size in bits (16/32/64) nb data=2 w r = number of rounds (0. . 255) b = number of bytes in key (0. . 255) RC 5, ciphers, modes ie 32 -bit words so encrypts 64 -bit data blocks using 12 rounds with 16 bytes (128 -bit) secret key RFC 2040 defines 4 modes used by RC 5 l l RC 5 Block Cipher, is ECB mode RC 5 -CBC, is CBC mode RC 5 -CBC-PAD, is CBC with padding by bytes with value being the number of padding bytes RC 5 -CTS, a variant of CBC which is the same size as the original message, uses ciphertext stealing to keep size same as original
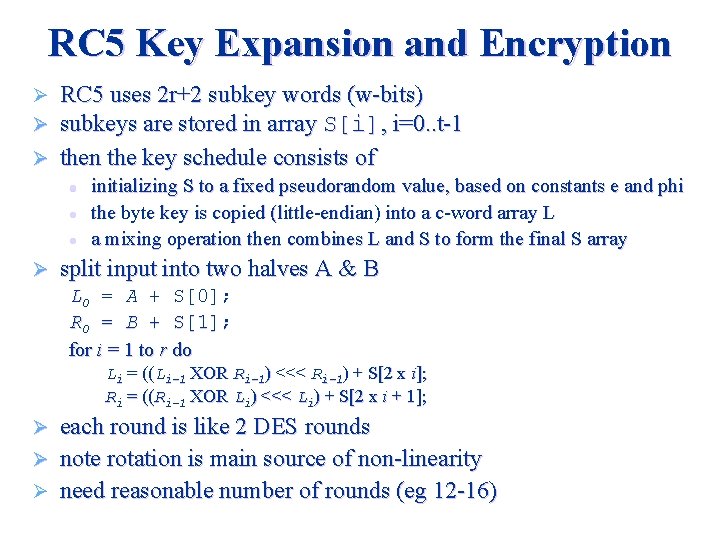
RC 5 Key Expansion and Encryption RC 5 uses 2 r+2 subkey words (w-bits) subkeys are stored in array S[i], i=0. . t-1 Ø then the key schedule consists of Ø Ø l l l Ø initializing S to a fixed pseudorandom value, based on constants e and phi the byte key is copied (little-endian) into a c-word array L a mixing operation then combines L and S to form the final S array split input into two halves A & B L 0 = A + S[0]; R 0 = B + S[1]; for i = 1 to r do Li = ((Li-1 XOR Ri-1) <<< Ri-1) + S[2 x i]; Ri = ((Ri-1 XOR Li) <<< Li) + S[2 x i + 1]; each round is like 2 DES rounds Ø note rotation is main source of non-linearity Ø need reasonable number of rounds (eg 12 -16) Ø
In summary Ø have considered: l l use and placement of symmetric encryption to protect confidentiality need for good key distribution use of trusted third party KDC’s random number generation issues
- Slides: 30