Raytheon Trusted Computer Solutions The Lock Down Dilemma





- Slides: 47

Raytheon Trusted Computer Solutions The Lock Down Dilemma Dirty Little Secrets About Operating System Security Edward Hammersla COO Copyright © 2011 Raytheon Company. All rights reserved. Customer Success Is Our Mission is a registered trademark of Raytheon Company.
Your new Linux OS out of the box: Less Security = Greater Ease of Use “Many of the vulnerabilities we identify are because the operating systems are not securely configured. Usually, vendors set their operating system configurations in the least secure manner in order to facilitate installation and implementation. ” “Q&A: Federal Information Security Isn’t Just About FISMA Compliance, Auditor Says, ” by Jaikumar Vijayan, Computer. World, June 14, 2007. Page 2
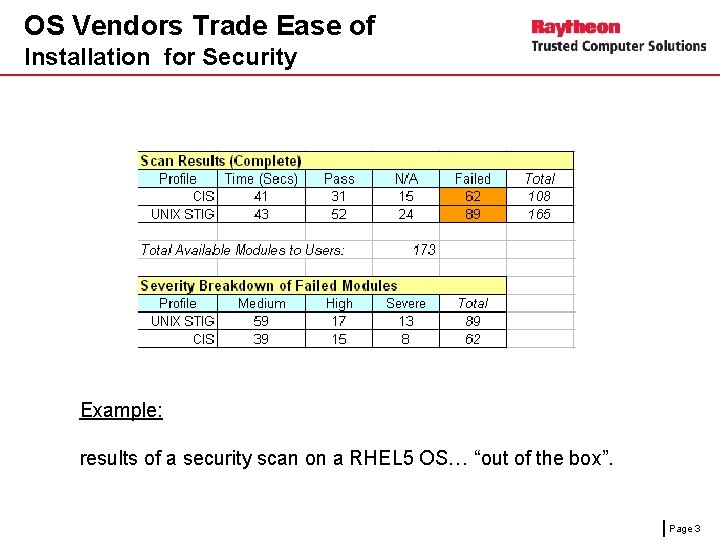
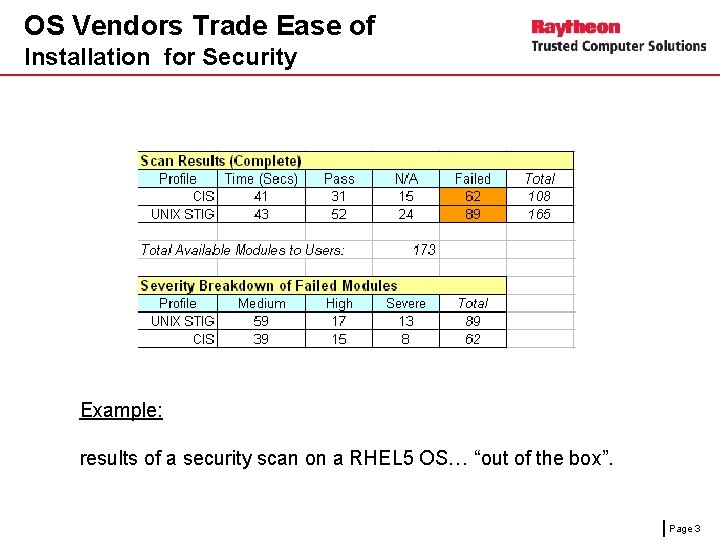
OS Vendors Trade Ease of Installation for Security Example: results of a security scan on a RHEL 5 OS… “out of the box”. Page 3
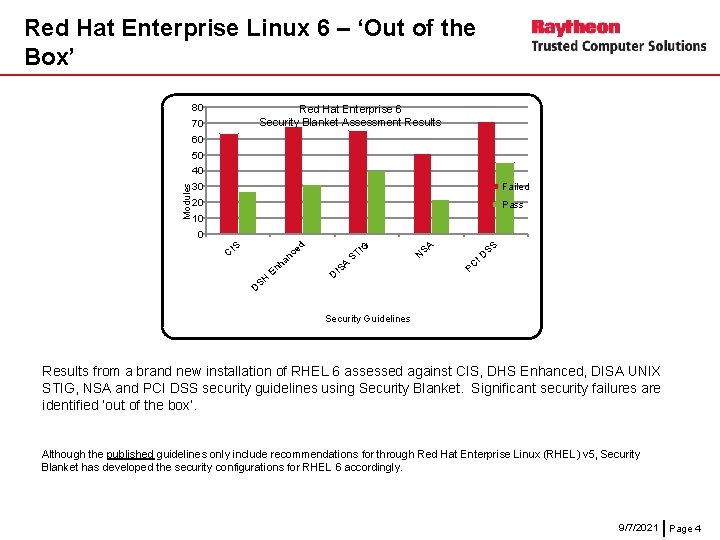
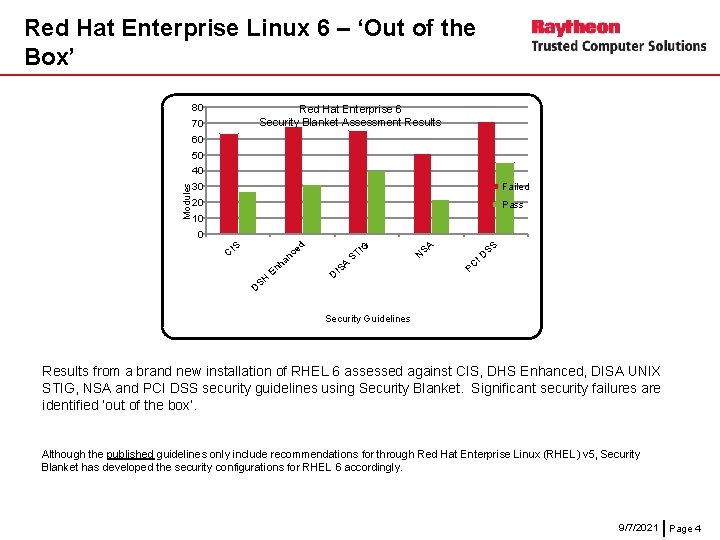
Red Hat Enterprise Linux 6 – ‘Out of the Box’ 80 Red Hat Enterprise 6 Security Blanket Assessment Results 70 60 Modules 50 40 30 Failed 20 Pass 10 0 S CI H DS En n ha d IG ce DI SA ST A SS NS D CI P Security Guidelines Validate Results from a brand new installation of RHEL 6 assessed against CIS, DHS Enhanced, DISA UNIX STIG, NSA and PCI DSS security guidelines using Security Blanket. Significant security failures are identified ‘out of the box’. Although the published guidelines only include recommendations for through Red Hat Enterprise Linux (RHEL) v 5, Security Blanket has developed the security configurations for RHEL 6 accordingly. 9/7/2021 Page 4
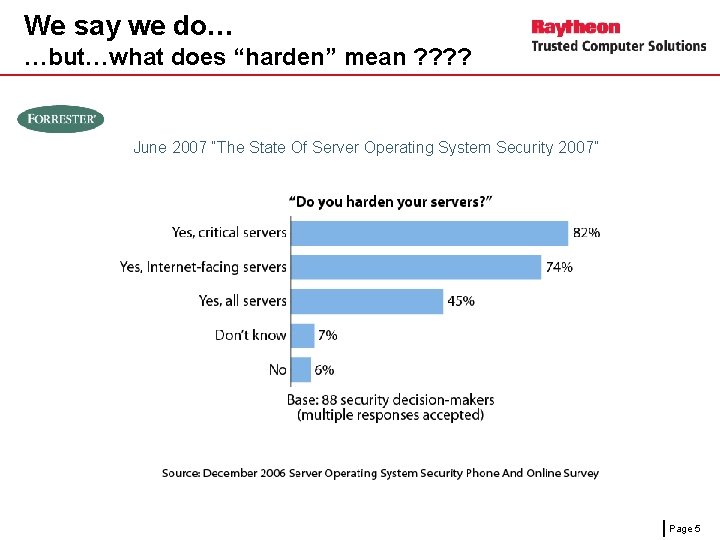
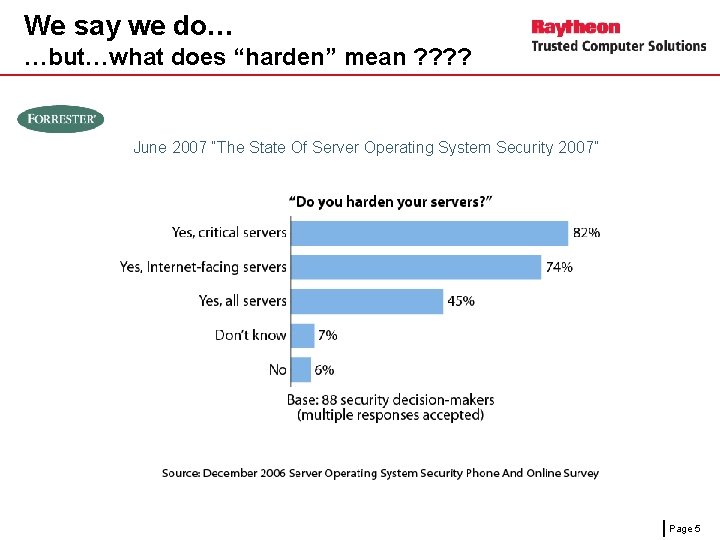
We say we do… …but…what does “harden” mean ? ? June 2007 “The State Of Server Operating System Security 2007” Page 5
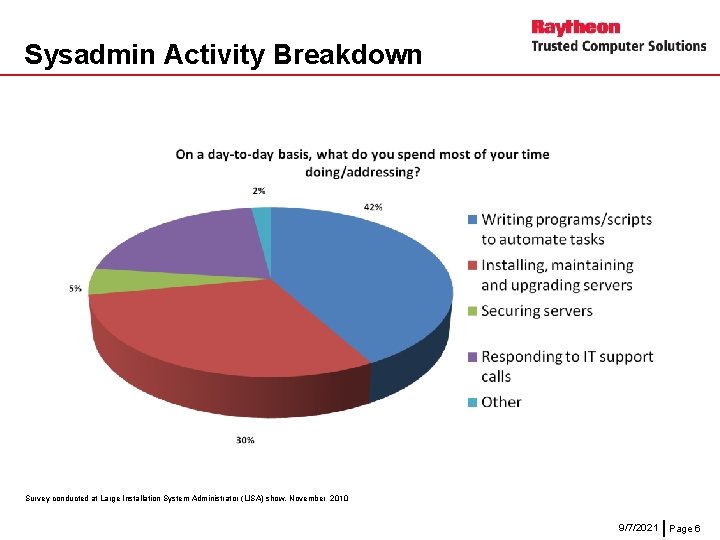
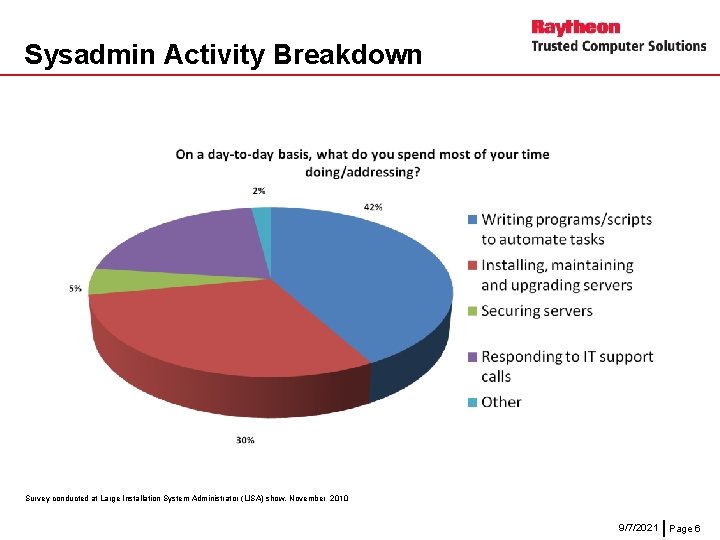
Sysadmin Activity Breakdown Survey conducted at Large Installation System Administrator (LISA) show, November 2010 9/7/2021 Page 6
Some Linux Server Factoids Based on consolidated industry research. . . n n n Approximately ¼ of Linux internet facing servers are not locked down because of the amount of time and expertise it requires. Approximately half of the Linux servers today are manually locked down. Up-time and stability are consistently reported as the top server challenges for System Admins & non-locked down OS configs can lead to down-time and instability. System Administrators widely agree that staying ahead of the OS security game boils down to 3 sets of practices that really work: server hygiene, server patching, and access control. Server hygiene is leagues better when servers are hardened and standardized using NIST or SANS security practices. Page 7
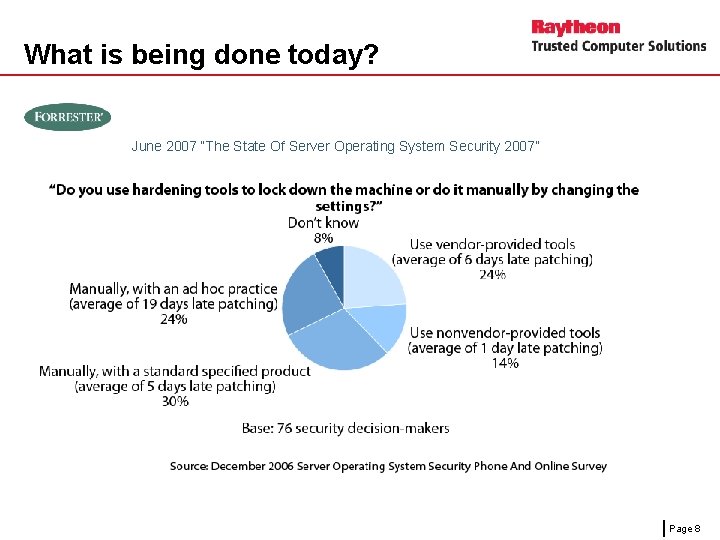
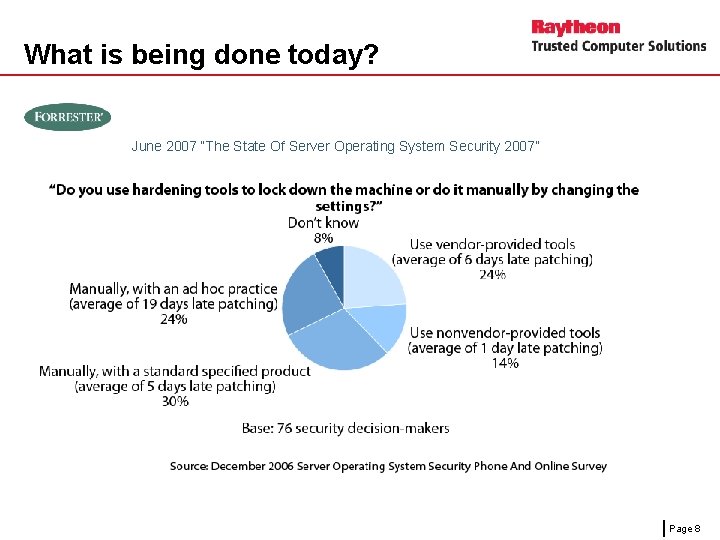
What is being done today? June 2007 “The State Of Server Operating System Security 2007” Page 8
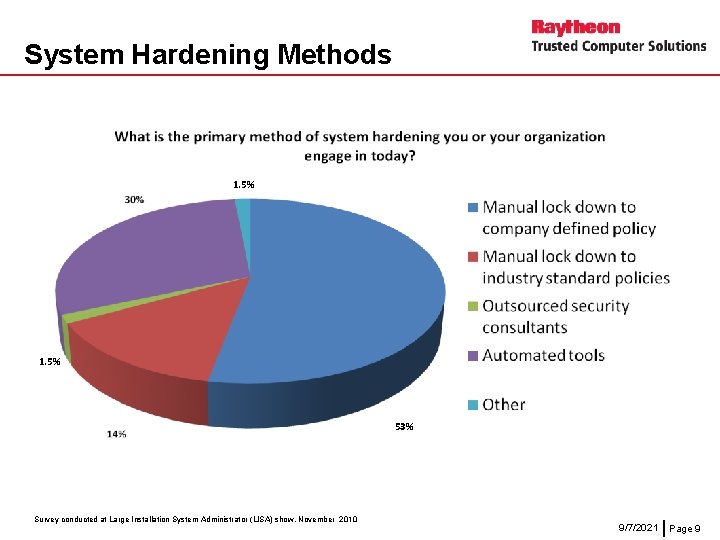
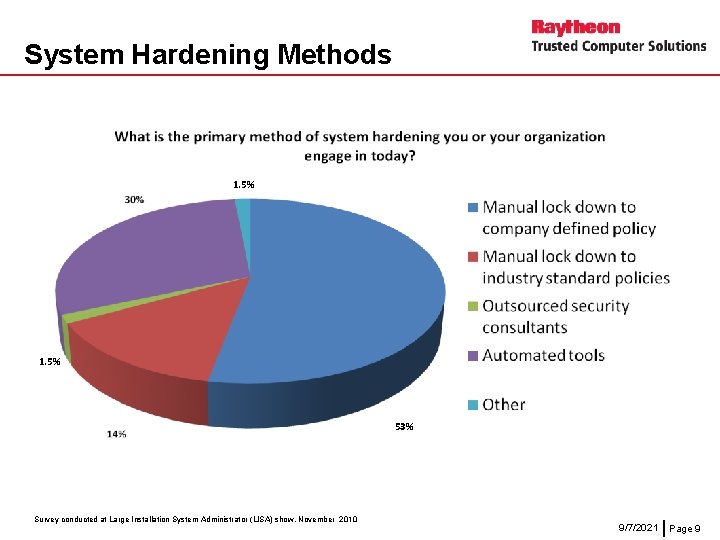
System Hardening Methods 1. 5% Validate • Impact on Operations • Server functionality is uncompromised • Business Impact Analysis Survey conducted at Large Installation System Administrator (LISA) show, November 2010 53% 9/7/2021 Page 9
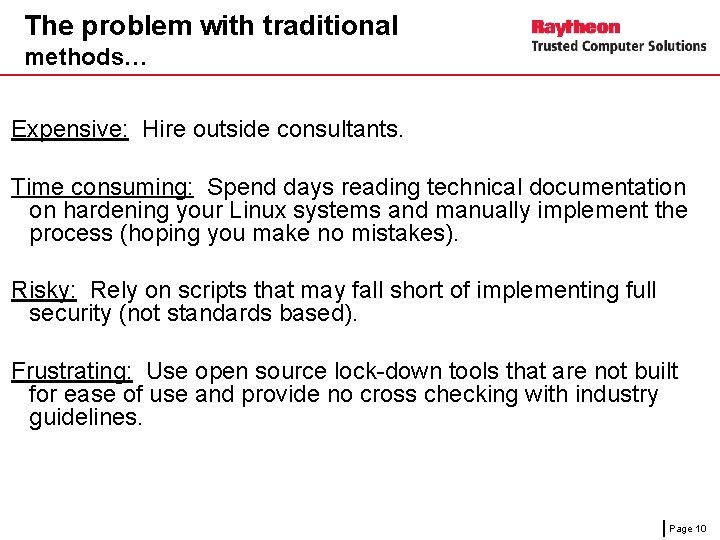
The problem with traditional methods… Expensive: Hire outside consultants. Time consuming: Spend days reading technical documentation on hardening your Linux systems and manually implement the process (hoping you make no mistakes). Risky: Rely on scripts that may fall short of implementing full security (not standards based). Frustrating: Use open source lock-down tools that are not built for ease of use and provide no cross checking with industry guidelines. . Page 10

Industry Standards “Both the US’s National Institute for Standards and Technology (NIST) and SANS Institute provide unbiased lists of steps to disable unnecessary services and optimize security settings. ” “Best Practices: Server Operating System Security” July 12, 2007, Forrester Research Center for Internet Security SANS Institute Unix DISA STIGs Page 11
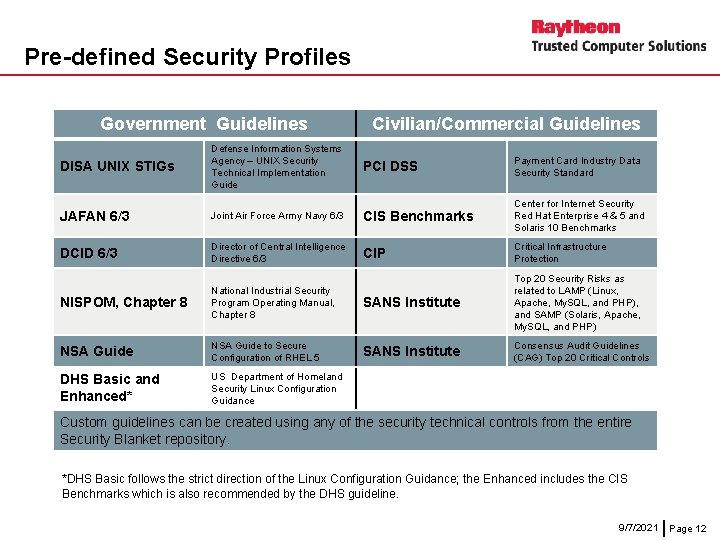
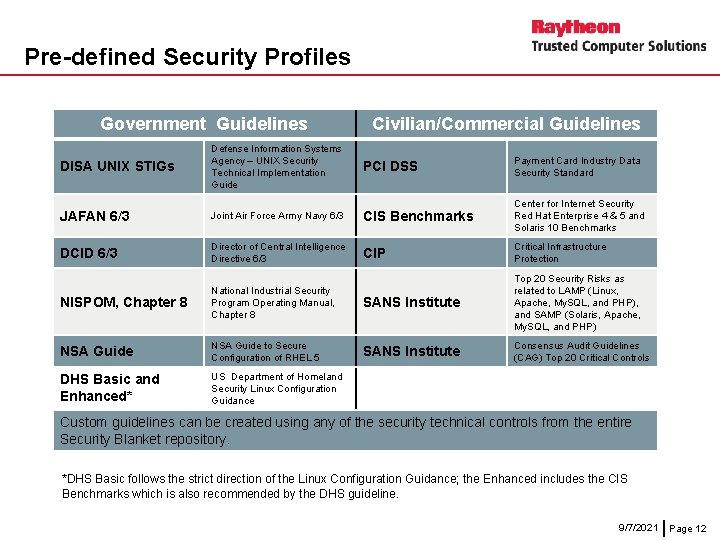
Pre-defined Security Profiles Government Guidelines DISA UNIX STIGs Defense Information Systems Agency – UNIX Security Technical Implementation Guide Civilian/Commercial Guidelines PCI DSS Payment Card Industry Data Security Standard JAFAN 6/3 Joint Air Force Army Navy 6/3 CIS Benchmarks Center for Internet Security Red Hat Enterprise 4 & 5 and Solaris 10 Benchmarks DCID 6/3 Director of Central Intelligence Directive 6/3 CIP Critical Infrastructure Protection NISPOM, Chapter 8 National Industrial Security Program Operating Manual, Chapter 8 SANS Institute Top 20 Security Risks as related to LAMP (Linux, Apache, My. SQL, and PHP), and SAMP (Solaris, Apache, My. SQL, and PHP) SANS Institute Consensus Audit Guidelines (CAG) Top 20 Critical Controls NSA Guide DHS Basic and Enhanced* NSA Guide to Secure Validate Configuration of RHEL 5 US Department of Homeland Security Linux Configuration Guidance Custom guidelines can be created using any of the security technical controls from the entire Security Blanket repository. *DHS Basic follows the strict direction of the Linux Configuration Guidance; the Enhanced includes the CIS Benchmarks which is also recommended by the DHS guideline. 9/7/2021 Page 12
The price of OS security Page 13
Reading a book on lock down… $44. 95 Page 14
Going to a training course on lock down …after you downloaded the free open source tool $2000. 00 Page 15
Hiring security consultants… $100, 000 $1800 per day (at least) Page 16
Writing lock down scripts yourself… “painful” Page 17

Using a fun, industry standard based automated lock down tool… $Priceless (not really… its $298) Page 18
An automated, Stds Based Approach: Security Blanket can automatically assess, configure & measure your Linux operating systems for the level of security you decide it should have. Security Blanket supports CIS, LAMP, and Unix DISA STIGs lock down guidelines. Page 19
Security Blanket Advertising Security Blanket ensures enterprise-wide policy configuration with fully automated OS lock down. Using scripts to lock down your OS can be time consuming and error prone. And, keeping those scripts up-to-date as new guidelines are published requires a continuous cycle of research, interpretation, and script revision. Do you really have the time for this? Security Blanket automatically configures the OS using the most up-to-date industry standard security guidelines. Whether locking down one server or an entire enterprise, Security Blanket performs fast, consisten, and repeatable OS lock down. Copyright © 2010 Trusted Computer Solutions, Inc. | www. Trusted. CS. com | 866. 230. 1307 | page 20 Page 20
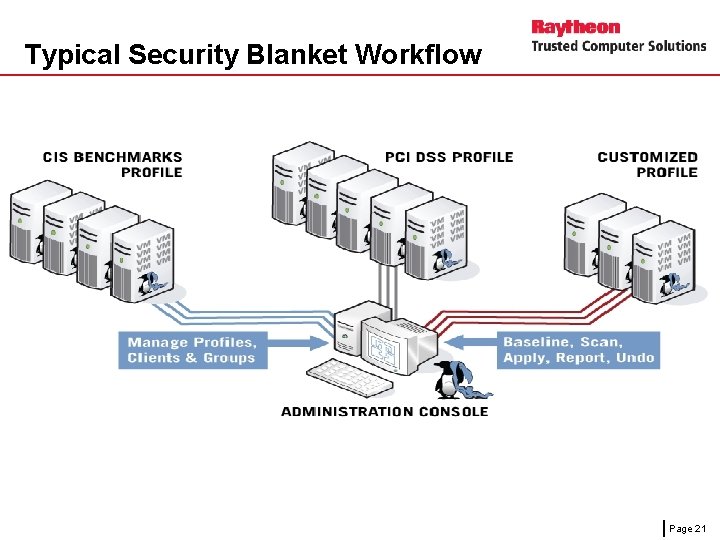
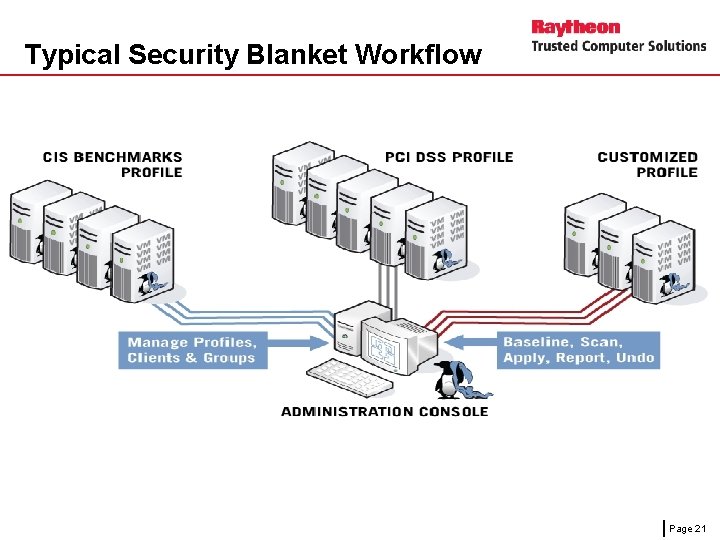
Typical Security Blanket Workflow Page 21
Security Blanket Enterprise Configuration Validate • Impact on Operations • Server functionality is uncompromised • Business Impact Analysis 9/7/2021 Page 22
Some Details… more @ www. Trusted. CS. com System Assessment, Automated lock-down, and Undo n Supported Systems: RHEL 4 and 5, Cent. OS 4 and 5, SUSE, Solaris 10, Oracle Enterprise Linux 4 and 5 n Supported Architectures: 32 -bit and 64 -bit n Will configure both IPv 4 and IPv 6 Kernel settings n Compliancy Model: n • • n Only product (we know) that includes both remediation and assessment Full CIS (and CIS Certified) [Red Hat Benchmark] Full DISA UNIX STIG (v 1. 2 Jan 2008) Address some of the SANS Top 20 Vulnerabilities FISMA Support - aids in providing or directly provides required security controls. Page 23
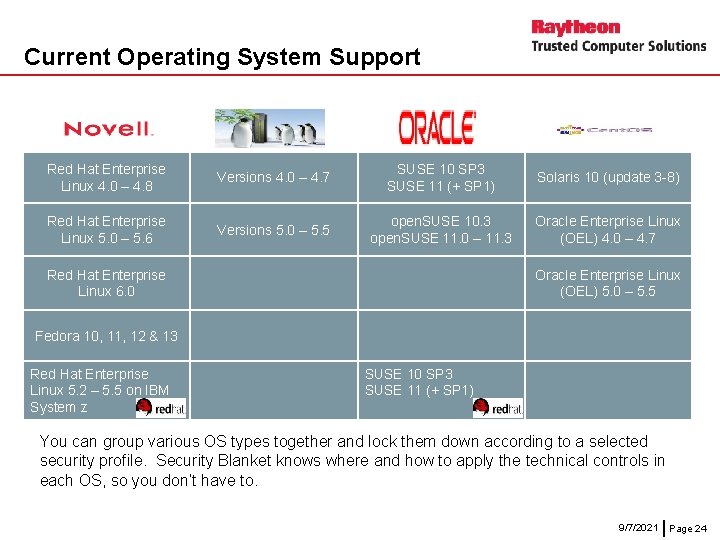
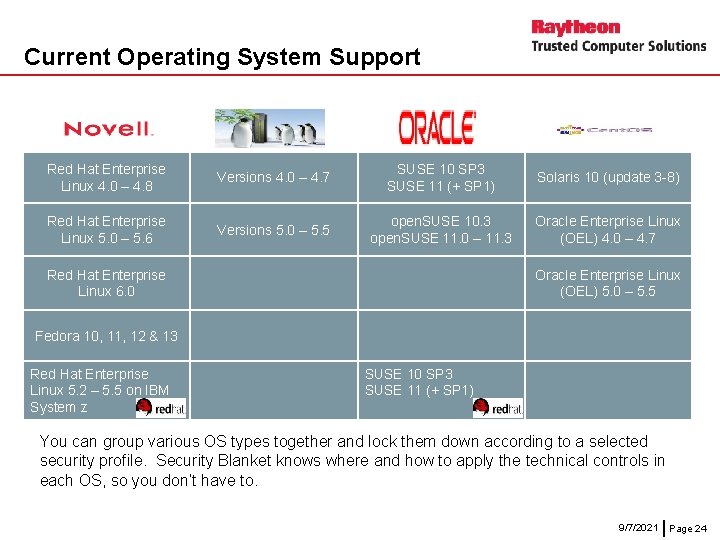
Current Operating System Support Red Hat Enterprise Linux 4. 0 – 4. 8 Versions 4. 0 – 4. 7 SUSE 10 SP 3 SUSE 11 (+ SP 1) Solaris 10 (update 3 -8) Red Hat Enterprise Linux 5. 0 – 5. 6 Versions 5. 0 – 5. 5 open. SUSE 10. 3 open. SUSE 11. 0 – 11. 3 Oracle Enterprise Linux (OEL) 4. 0 – 4. 7 Red Hat Enterprise Linux 6. 0 Oracle Enterprise Linux (OEL) 5. 0 – 5. 5 Fedora 10, 11, 12 & 13 Validate Red Hat Enterprise Linux 5. 2 – 5. 5 on IBM System z SUSE 10 SP 3 SUSE 11 (+ SP 1) You can group various OS types together and lock them down according to a selected security profile. Security Blanket knows where and how to apply the technical controls in each OS, so you don’t have to. 9/7/2021 Page 24
So…midway reveiw… n Your new OS will arrive with the worst possible security settings – This is the dirty little secret, perhaps known but not focused on To fix this you much perform “OS lock down” n You can do this: n – Manually (read about it & write scripts) – Use Open Source tools (free but no reports or compliance info) – Use Industry Std Based tools that keeps baseline and automates process n If done well: – Your Linux Servers will be more stable & go down less often – Your Auditors will see that you are compliant with Industry Standards – Your Management will relax about OS Security – You will win the lottery (ok, not really) Page 25
Linux on the Mainframe Validate Linux runs natively on the IBM System z with the same concerns for OS security. 9/7/2021 Page 26
Securing the Linux VMs Validate Linux virtual servers on System z can help unify your IT infrastructure, leveraging the comprehensive virtualization technology and intelligent workload management. You can grow virtually with IBM z/VM virtualization capabilities, consolidating from tens to hundreds of independent servers onto a single System z platform. How do you manage the security of those hundreds of virtual servers? 9/7/2021 Page 27
IBM Best Practices Practical Migration to Linux on System z October 2009 International Technical Support Organization 11. 1. 3 Hardening the base Linux VM. . . taking a generic purpose operating system and changing it to only provide what is necessary for the production environment. . . if a hardened Linux image does not already exist, then you should create and maintain one. Validate Creating a new hardened Linux VM The basics of hardening a Linux VM consist of removing all unnecessary applications and services, and then securing the applications and services that are left. Explaining this process is beyond the scope of this book Migrating to a hardened Linux VM A hardened Linux VM should have most if not all applications and services removed and or disabled. 9/7/2021 Page 28
IBM Best Practices Practical Migration to Linux on System z October 2009 International Technical Support Organization Maintaining a hardened Linux VM Validate It is necessary to maintain base hardened Linux VMs. Kernels change and security patches are issued, so you need to develop a plan for maintaining the base image and assigning the resources to accomplish it. Thus, successive migrations will benefit from a properly maintained base hardened Linux VM. 9/7/2021 Page 29
66% of Mainframe Users Feel that Security Could be Improved Results are from an opinion poll that was part of the February 2009 issue of IBM Systems Magazine’s Mainframe EXTRA newsletter. Validate 9/7/2021 Page 30
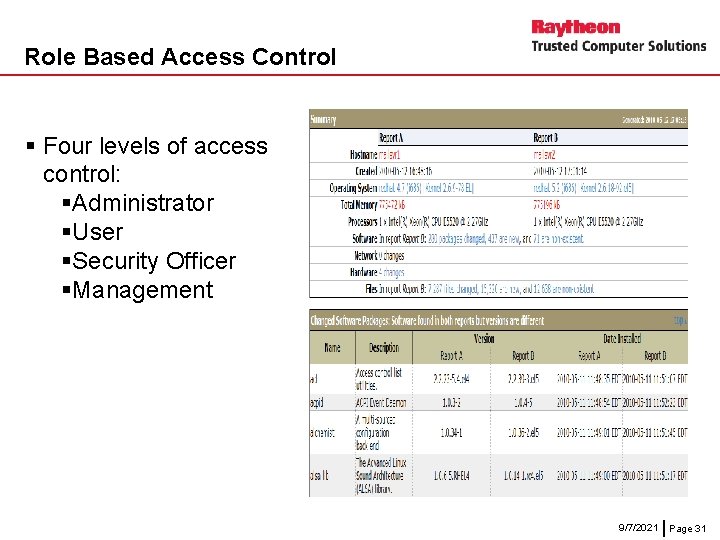
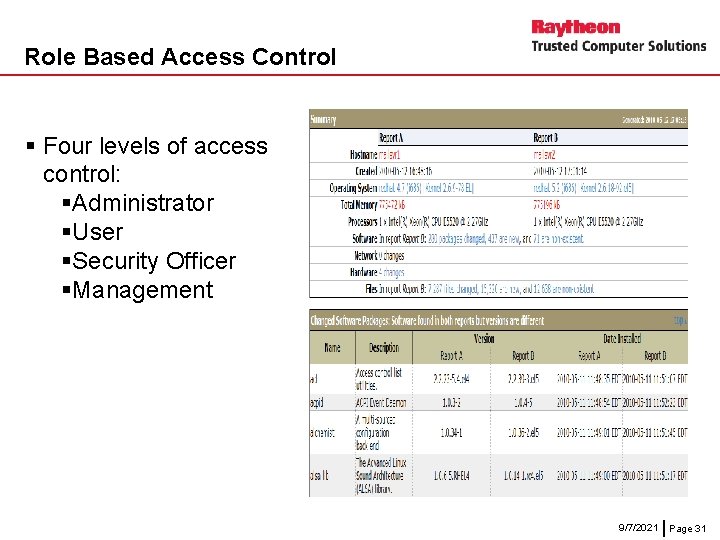
Role Based Access Control § Four levels of access control: §Administrator §User §Security Officer §Management Validate 9/7/2021 Page 31
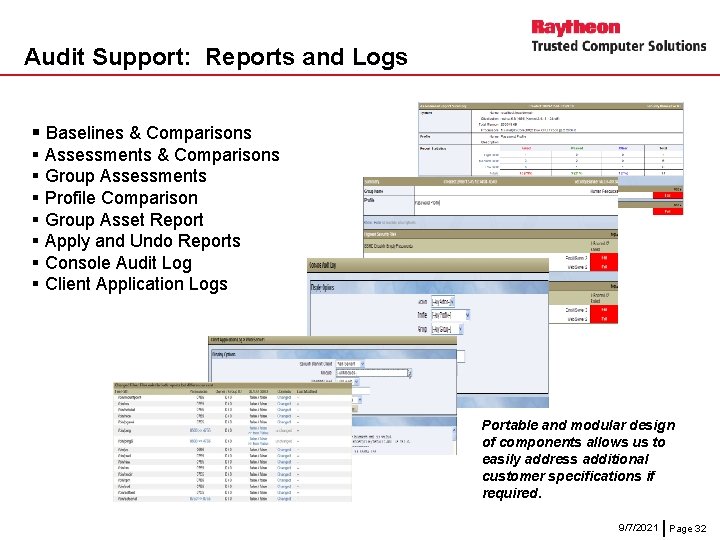
Audit Support: Reports and Logs § Baselines & Comparisons § Assessments & Comparisons § Group Assessments § Profile Comparison § Group Asset Report § Apply and Undo Reports § Console Audit Log § Client Application Logs Validate Portable and modular design of components allows us to easily address additional customer specifications if required. 9/7/2021 Page 32
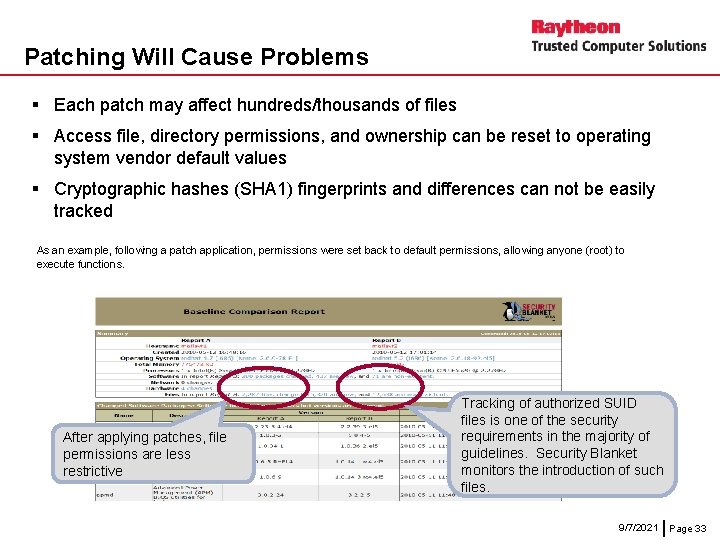
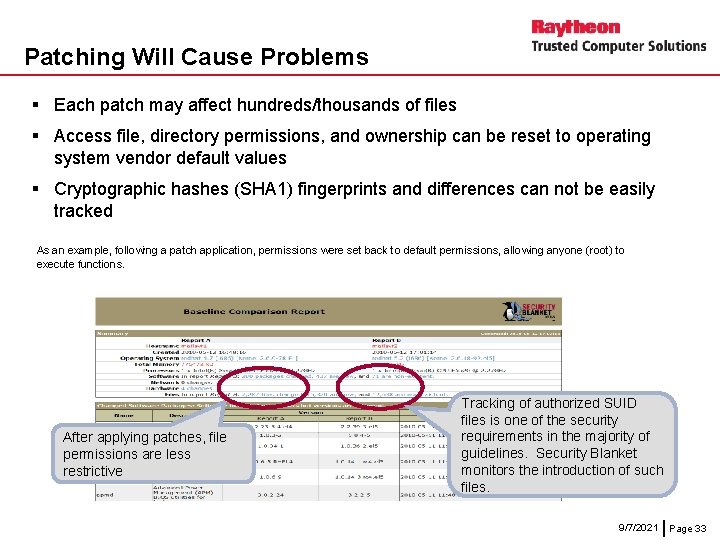
Patching Will Cause Problems § Each patch may affect hundreds/thousands of files § Access file, directory permissions, and ownership can be reset to operating system vendor default values § Cryptographic hashes (SHA 1) fingerprints and differences can not be easily tracked As an example, following a patch application, permissions were set back to default permissions, allowing anyone (root) to execute functions. Validate After applying patches, file permissions are less restrictive Tracking of authorized SUID files is one of the security requirements in the majority of guidelines. Security Blanket monitors the introduction of such files. 9/7/2021 Page 33
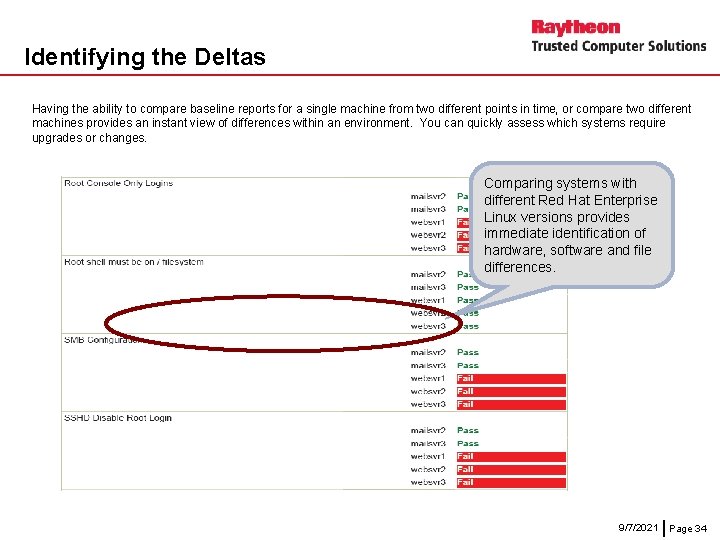
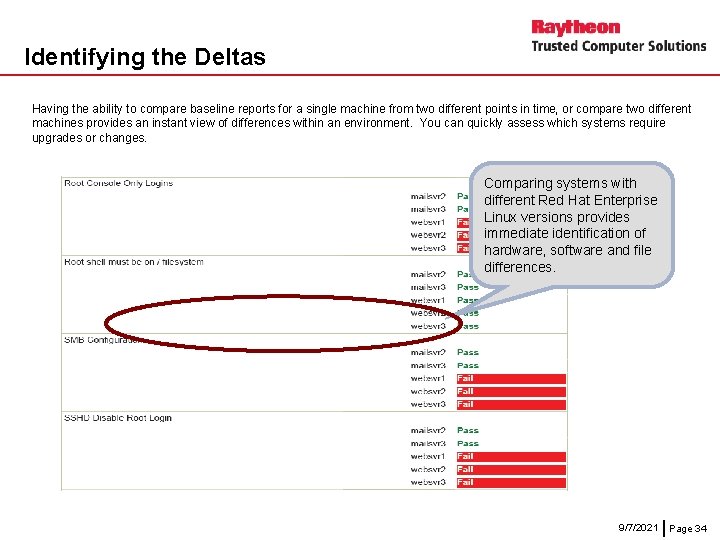
Identifying the Deltas Having the ability to compare baseline reports for a single machine from two different points in time, or compare two different machines provides an instant view of differences within an environment. You can quickly assess which systems require upgrades or changes. Comparing systems with different Red Hat Enterprise Linux versions provides immediate identification of hardware, software and file differences. Validate 9/7/2021 Page 34
Assessment of Compliance – By Group Validate 9/7/2021 Page 35
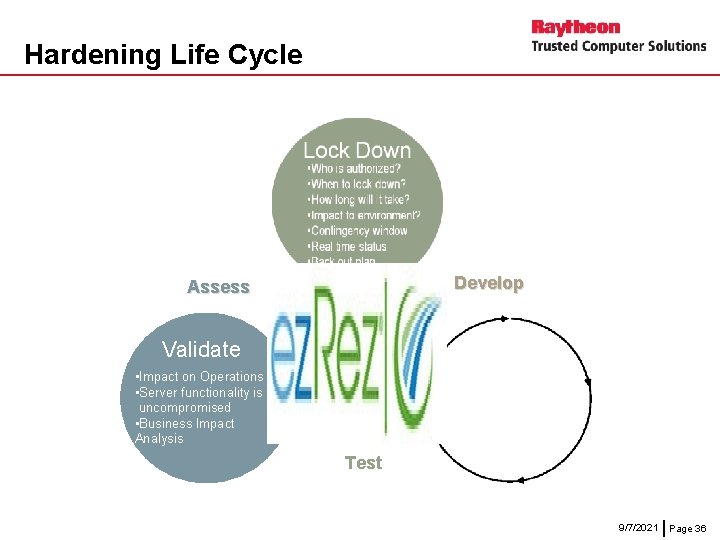
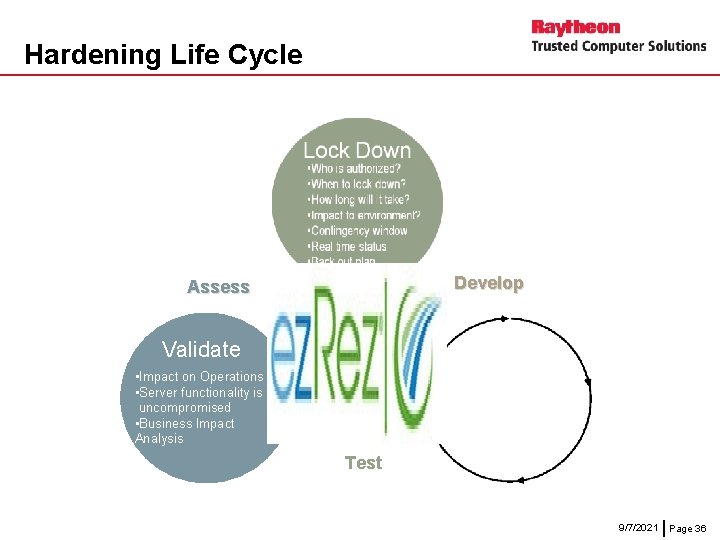
Hardening Life Cycle Develop Assess Validate • Impact on Operations • Server functionality is uncompromised • Business Impact Analysis Maintain Test 9/7/2021 Page 36
Rapid Financial Returns § Leading Software-as-a-Service provider for the online travel industry supporting some the world’s largest airlines, hotels, travel agencies, and banking loyalty programs § Process over 800 K transactions per year and exceed current Service Level Agreements of 99. 95% § Undergo yearly compliancy audits § Implemented a custom hardening profile based on CIS and PCI DSS § Reduces the time to assess and harden systems by 50% Validate § Jared Wright, Data Center Operations Manager, ez. Rez says: “We found that Security Blanket could assess the security posture of our Red Hat and Cent. OS servers, identify non-compliant areas and automatically fix them in half the time versus having to do it manually. Security Blanket is now integrated into our standard server deployment process, and we will use the ‘one click’ automated configuration features to monitor our security posture regularly. ” 9/7/2021 Page 37
Industry Recognition Security Blanket was awarded a Product Excellence Award for “Best Security Product” at Linux. World in 2008 Validated on IBM Systems Application Advantage for Linux Security Blanket supports Linux 5. 2+ on IBM System z **************** Government Specific Lists and Evaluations: Validate Security Blanket has entered Common Criteria Evaluation and Verification Scheme with the National Information Assurance Partnership (NIAP) Security Blanket has been added to the Department of the U. S. Navy’s Application and Database Management (DADMS) List 9/7/2021 Page 38
Independent Product Reviews Linux Pro Magazine says: “A number of features make Security Blanket worth paying for. Overall, I like this product…it actually does what it claims it will do, and it does it pretty painlessly. ” SANS’ Analyst, Dave Shackleford notes: “Security Blanket is a critical layer of defense-in-depth … Security Blanket plays into a larger assessment and configuration management story at the foundational layer while at the same time allowing granular control of configuration policies across all critical and sensitive UNIX and Linux systems. ” SC Magazine says: Validate “Great lock down, reporting, auditing and system roll-back capabilities; provides a very nice set of tools for locking down Linux endpoints. User interface makes it very easy to manage Linux devices, even if operators don’t possess strong Linux skills”. GCN states: “…it might take a week to tweak each of the various functions until it was compliant with DISA UNIX STIG. We were able to (lock down to DISA STIGs) in only a few hours. ” “Security Blanket is… ideal for network administrators who are not experts with all of the operating systems. ” 9/7/2021 Page 39
Customer Feedback “The product efficiently does exactly what it says it does. It provides an assessment to tell you what is noncompliant on a server and then automatically fixes it so that the server is compliant. ” Keith Arthur, Technical Delivery Team Lead Unique Communications Solutions “Security Blanket has the STIGs pre-defined within the product, which results in a STIG lockdown being reduced from 30 days to 2 in a typical deployment. Integrating Security Blanket will increase our productivity and ensure the highest level of system security for our clients. ” Gary Royal, Founder and Chief Operating Officer Cistera Networks Validate “We estimate that we have been able to save 40 -60 hours in the development of the initial security configuration that we use for all of our Linux systems. With each new system deployment, we are saving between 4 -6 hours per system. The time savings alone is a huge benefit, but knowing that our systems are DISA STIG compliant is especially beneficial for our clients. ” Larry Pakieser, Chief Operating Officer GBProtect 9/7/2021 Page 40
Customer Feedback (continued) “…. Security Blanket demystified the whole (lock down)process. It is easy to use, extremely flexible and should be used by anyone who really is interested in securing their machine and keeping it that way. I am amazed it could be this simple. Thank you”. Daniel Halstead, Engineer Department of Defense “…I was able to lock down all 18 of my classified servers in one day. Prior to using Security Blanket, locking down one server would have take an entire week. Now…I have more time to focus on mission-critical tasks and projects”. Principal Field Engineer National Test Range Validate “This software has done in 8 minutes what I have been working on for 3 weeks. Amazing!” Systems Administrator Do. D Contractor “With Security Blanket I can lock down a Linux or Solaris system to DISA STIG compliance in under a minute”. Security Blanket can turn the most novice Linux/Solaris administrators into system security professionals”. Senior Engineer Intelligence Community 9/7/2021 Page 41

Recognized Security Experts Validate 9/7/2021 Page 42

Background and Experience § Trusted Computer Solutions was recently acquired by Raytheon § Over 16 years of experience building security products that meet the most stringent security requirements mandated by the Intelligence Community & Federal government § Products Accredited and in Operational use today protecting our nation’s most valuable digital assets § Solutions include: § Cross Domain Solutions for Do. D, Intelligence Community, and Civilian Validate Government § Automated Operating System Lock Down solution § Network security solutions (For information on all of our products go to www. Trusted. CS. com) 9/7/2021 Page 43
In Summary § Automatically harden systems to industry standards in minutes, rather than days § Hardening systems is not a one time activity § System Administrators can become proficient in hardening unfamiliar/new operating systems quickly and easily § Easily manage security for multiple servers with varying operating systems § Significant savings Validate = 9/7/2021 Page 44
Security Blanket Technical Characteristics § Operating Systems: § Red Hat Enterprise Linux (RHEL) 4 & 5 § Cent. OS 4 & 5 § Oracle Enterprise Linux (OEL) 4 & 5 § Solaris 10 § Fedora 10, 11, 12 &13 § Novell SUSE 10 and 11 and open. SUSE 10 and 11 § Architectures: 32 -bit and 64 -bit § Platforms: § IBM System z (RHEL 5. 2+ and SUSE 10 and 11) § Solaris x 86 and SPARC § ESX guests (on supported operating systems) § Console-to-client communications use Simple Object Access Protocol (SOAP) messages using HTTP over Transport Layer Security (TLS) so that the communication is both secure and encrypted. § Reports are generated in XML format and can be printed in. HTML, . PDF, . TXT, and. CSV formats § Client functions can also be performed via command line § Utilizes plug-in architecture for addition of new protocols and interfaces to 3 rd party applications § Easy client-to-console configuration enables organizations to aggressively repurpose systems while maintaining security posture § Role Based Access Control Validate 9/7/2021 Page 45
Security Blanket Resources Len Santalucia, CTO & Business Development Manager One Penn Plaza – Suite 2010 New York, NY 10119 212 -799 -9375 lsantalucia@vicominfinity. com Security Blanket Technical Blog http: //tcs-security-blanket_blogspot. com/ Validate Security Blanket web page: www. trustedcs. com/Security. Blanket 9/7/2021 Page 46
Security Blanket Inquiries For More Information Or To Buy Security Blanket Please Contact… Len Santalucia, CTO & Business Development Manager One Penn Plaza – Suite 2010 New York, NY 10119 212 -799 -9375 lsantalucia@vicominfinity. com About Vicom Infinity n n n Account Presence Since Late 1990’s IBM Premier Business Partner Reseller of IBM Hardware, Software, and Maintenance Vendor Source for the Last 3 Generations of Mainframes/IBM Storage Professional and IT Architectural Services Copyrightand © 2010 Vicom Family of Companies Also Offer Leasing & Financing, Computer Services, IT Raytheon Trusted Staffing & IT Project Management Computer Solutions, Inc. | www. Trusted. CS. co m | 866. 230. 1307 | page 47 Page 47