Ransomware Security for Virtualization Zack Ehrhardt Kaspersky Lab

Ransomware & Security for Virtualization Zack Ehrhardt Kaspersky Lab Zachary. Ehrhardt@Kaspersky. com 781 -503 -2680
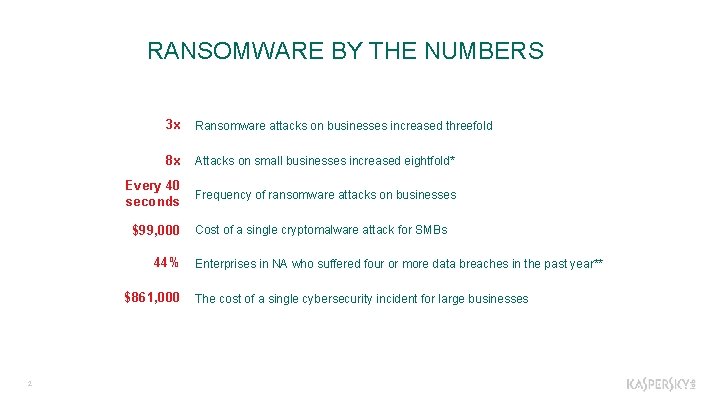
RANSOMWARE BY THE NUMBERS 3 x Ransomware attacks on businesses increased threefold 8 x Attacks on small businesses increased eightfold* Every 40 seconds Frequency of ransomware attacks on businesses $99, 000 44% $861, 000 2 Cost of a single cryptomalware attack for SMBs Enterprises in NA who suffered four or more data breaches in the past year** The cost of a single cybersecurity incident for large businesses
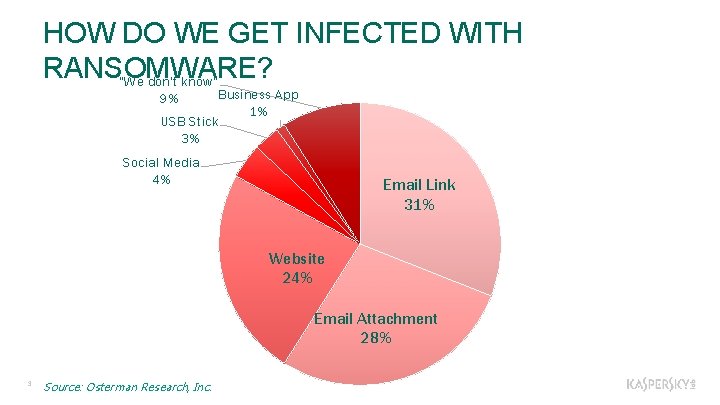
HOW DO WE GET INFECTED WITH RANSOMWARE? "We don't know" Business App 1% USB Stick 3% 9% Social Media 4% Email Link 31% Website 24% Email Attachment 28% 3 Source: Osterman Research, Inc.
NO MORE RANSOM • Founding partners: European Cybercrime Centre, Politie, Intel Security and Kaspersky Lab • Additional partners: Over 30 organizations in security, cloud services and law enforcement • Goal: Help ransomware victims retrieve their encrypted data without paying the criminals • Project aim: Prevent ransomware by educating users about prevention https: //www. nomoreransom. org 4
Kaspersky Security for Virtualization
Dilbert’s Take on Virtualization 6
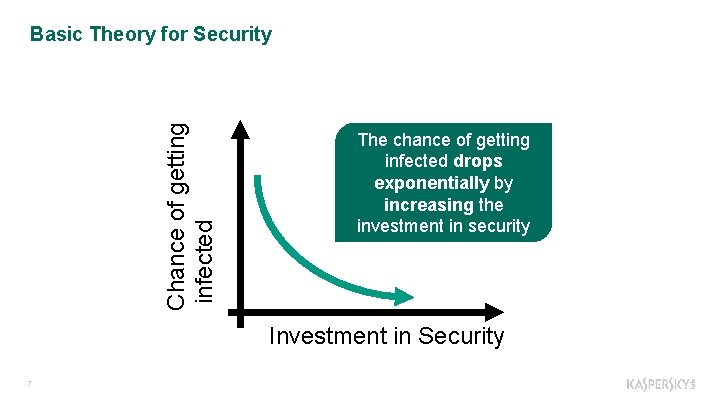
Chance of getting infected Basic Theory for Security The chance of getting infected drops exponentially by increasing the investment in security Investment in Security 7
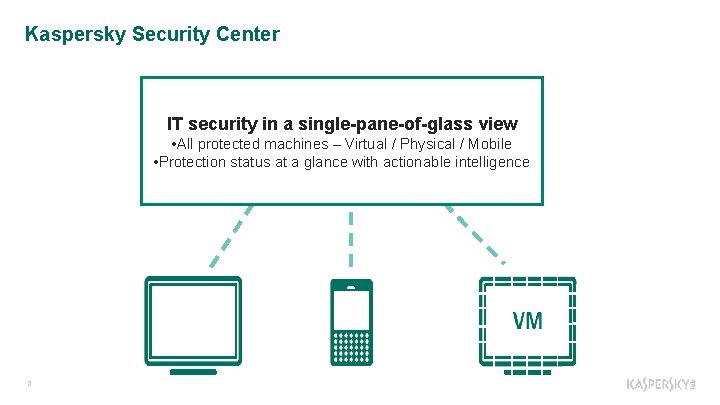
Kaspersky Security Center IT security in a single-pane-of-glass view • All protected machines – Virtual / Physical / Mobile • Protection status at a glance with actionable intelligence 8
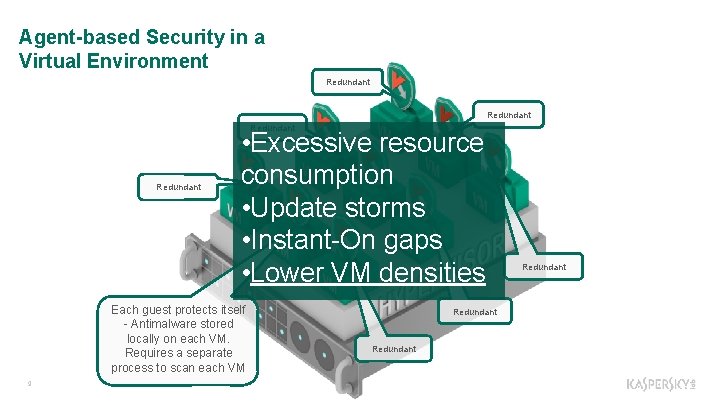
Agent-based Security in a Virtual Environment Redundant • Excessive resource consumption • Update storms • Instant-On gaps • Lower VM densities Each guest protects itself - Antimalware stored locally on each VM. Requires a separate process to scan each VM 9 Redundant

Is there a better way to protect virtualized environments from malware? 10
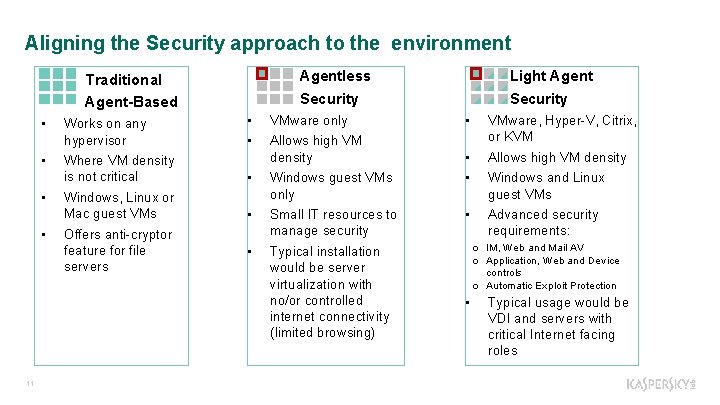
Aligning the Security approach to the environment Agentless Security Traditional Agent-Based • • 11 Works on any hypervisor Light Agent Security • VMware only • • Allows high VM density VMware, Hyper-V, Citrix, or KVM • Allows high VM density Where VM density is not critical • • Windows, Linux or Mac guest VMs Windows guest VMs only Windows and Linux guest VMs • Small IT resources to manage security • Advanced security requirements: • Typical installation would be server virtualization with no/or controlled internet connectivity (limited browsing) Offers anti-cryptor feature for file servers o IM, Web and Mail AV o Application, Web and Device controls o Automatic Exploit Protection • Typical usage would be VDI and servers with critical Internet facing roles
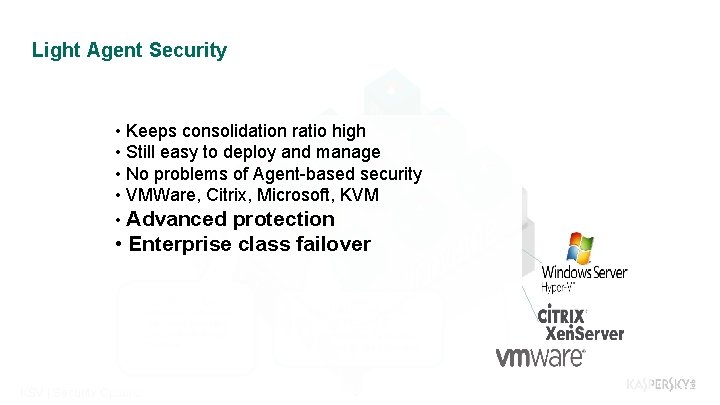
Light Agent Security • Keeps consolidation ratio high • Still easy to deploy and manage • No problems of Agent-based security • VMWare, Citrix, Microsoft, KVM • Advanced protection • Enterprise class failover LIGHT AGENT • • • 12 KSV | Security Options Advanced antimalware Advanced protection from network threats Controls SECURITY VIRTUAL APPLIANCE • Anti-malware databases • Centralized file scanning
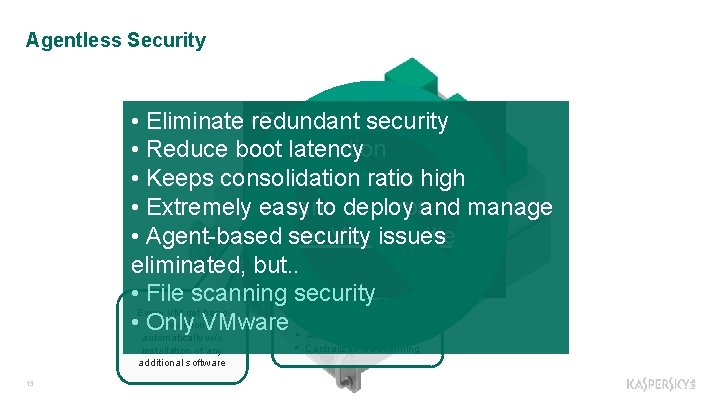
Agentless Security • Eliminate • redundant Excessivesecurity resource • Reduce boot consumption latency • Keeps consolidation • Update storms ratio high • Extremely • Instant-On easy to deploy gapsand manage • Agent-based • Lower security VM densities issues eliminated, but. . • File scanning security SECURITY VIRTUAL Every VM get basic APPLIANCE protection. VMware • automatically Only • Anti-malware databases w/o installation of any additional software 13 • Centralized file scanning
2 Simple Takeaways… • Be proactive when protecting against ransomware • Choose the right security option for your virtual environment 14

Thank you! 15
- Slides: 15