Ransomware Darkweb and Organized Crime BUZZ HILLESTAD SR
Ransomware, Darkweb, and Organized Crime BUZZ HILLESTAD – SR SECURITY CONSULTANT © 2017 SBS Cyber. Security, LLC www. sbscyber. com 1 1
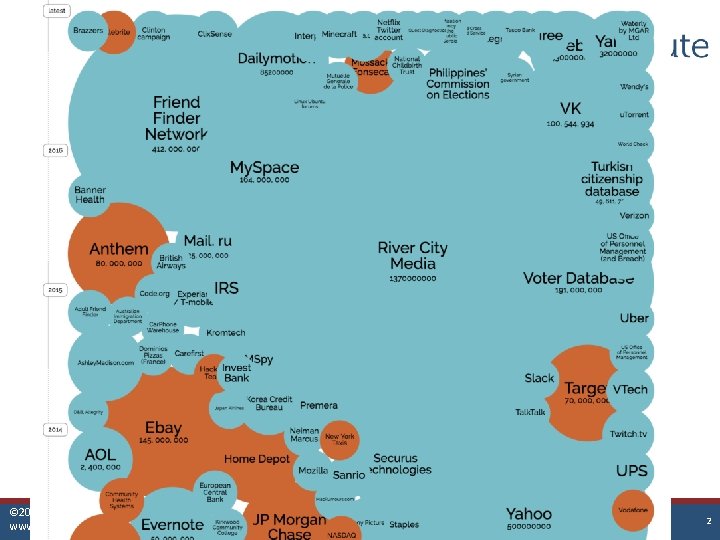
© 2017 SBS Cyber. Security, LLC www. sbscyber. com 2
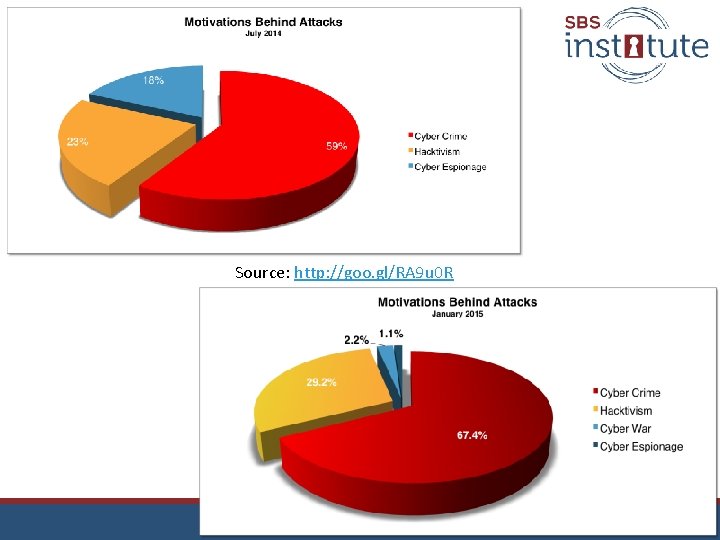
Source: http: //goo. gl/RA 9 u 0 R
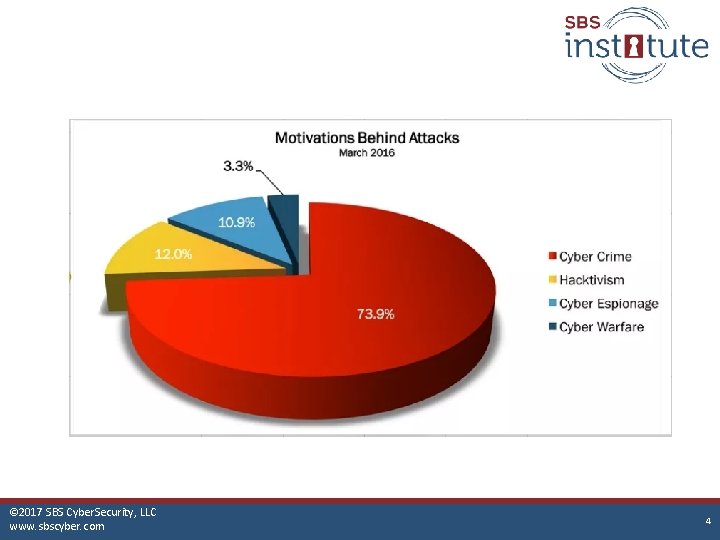
© 2017 SBS Cyber. Security, LLC www. sbscyber. com 4 4
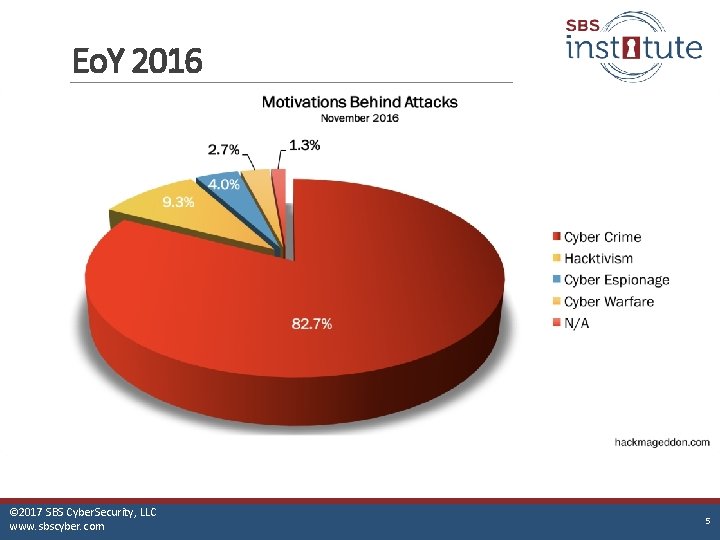
Eo. Y 2016 © 2017 SBS Cyber. Security, LLC www. sbscyber. com 5
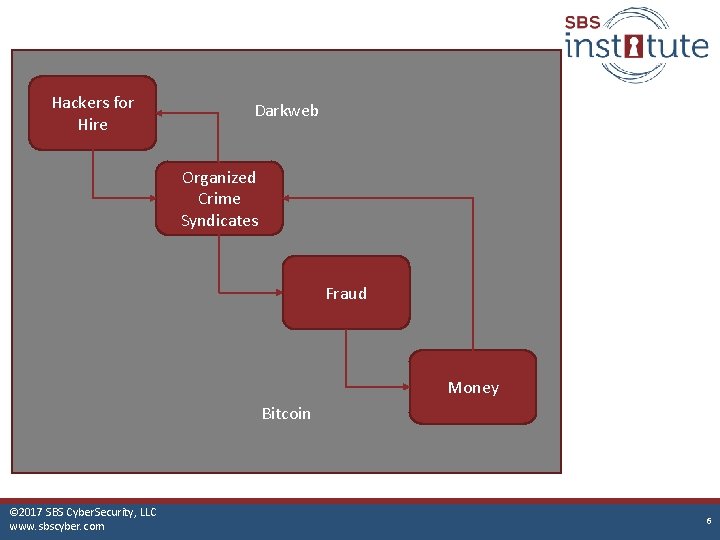
Hackers for Hire Darkweb Organized Crime Syndicates Fraud Money Bitcoin © 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 6 6
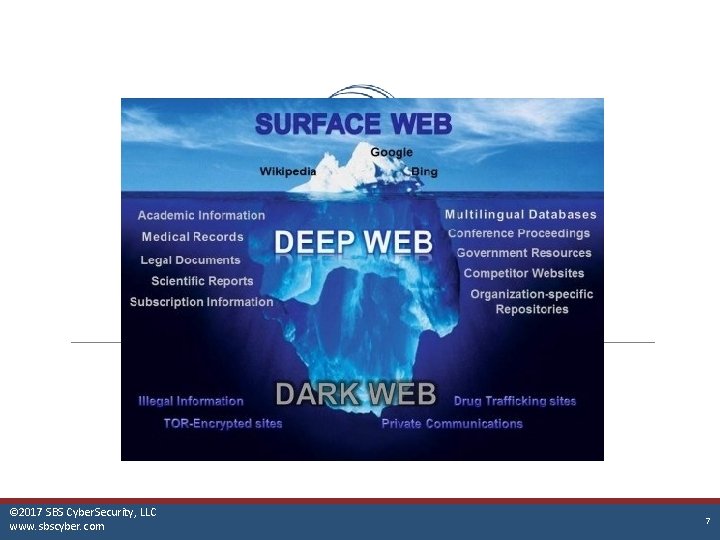
© 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 7 7
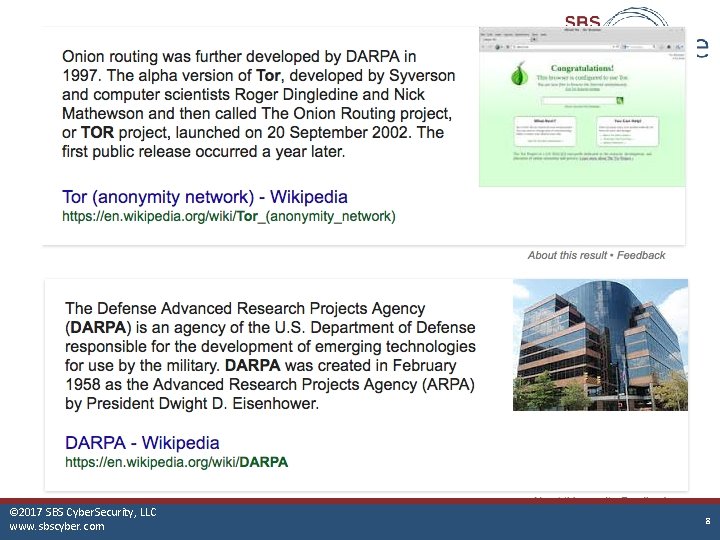
© 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 8 8
Usage • Originally intended for military use to disguise the geographic location of communications • Adapted for freedom of speech and noncensorship • Currently, vastly used for nefarious activities – but still for those other things to a lesser extent © 2017 SBS Cyber. Security, LLC www. sbscyber. com 9
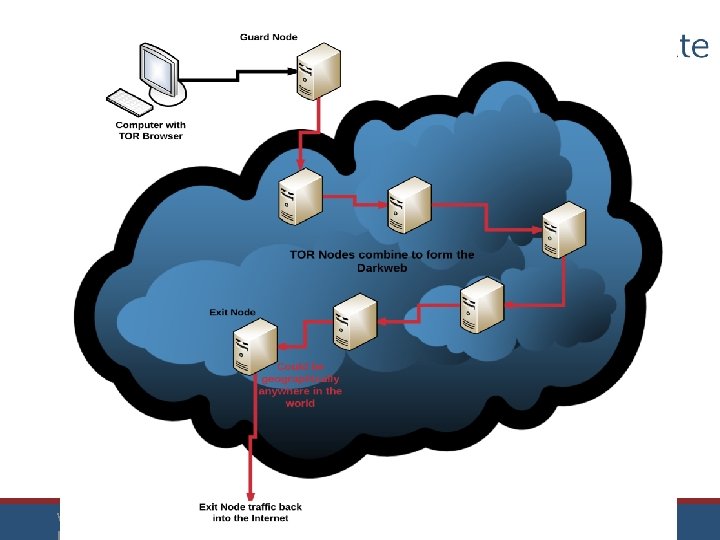
www. protectmyban © 2015 Secure Banking Solutions, LLC 10

Common Fraud Markets • Medical Insurance Claim Fraud • Carding – Stolen Credit Card Fraud • Commercial Account Takeover • Cyber Extortion © 2017 SBS Cyber. Security, LLC www. sbscyber. com 11

Medicare Medicaid Fraud Healthcare or Insurance Company Attacker Hacker © 2017 SBS Cyber. Security, LLC www. sbscyber. com Medicare/Medicaid/ Insurance Org Fraud Operations Shell Company 12
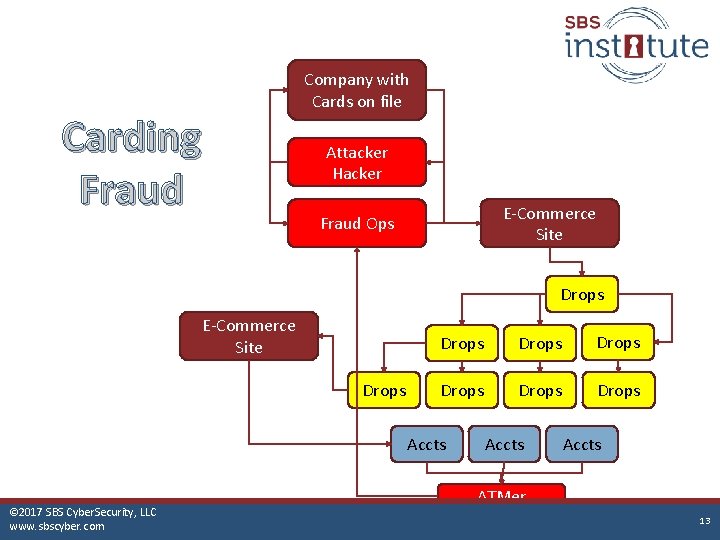
Carding Fraud Company with Cards on file Attacker Hacker E-Commerce Site Fraud Ops Drops E-Commerce Site Drops Drops Accts © 2017 SBS Cyber. Security, LLC www. sbscyber. com Accts ATMer 13
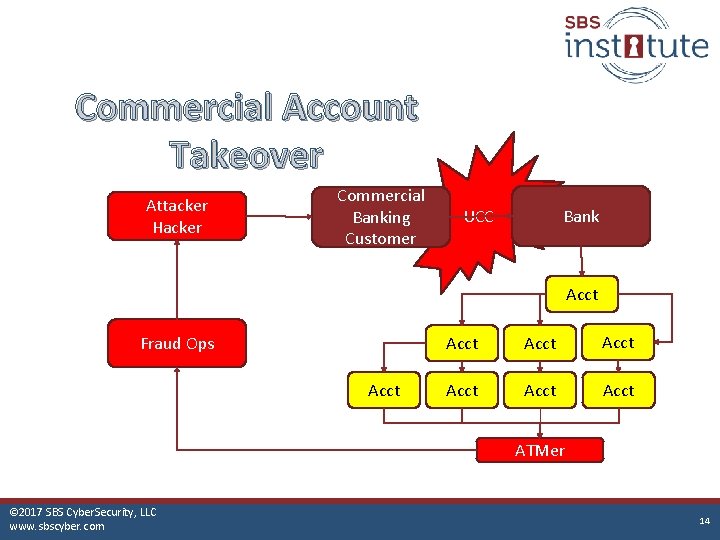
Commercial Account Takeover Attacker Hacker Commercial Banking Customer UCC Bank Acct Fraud Ops Acct Acct ATMer © 2017 SBS Cyber. Security, LLC www. sbscyber. com 14

Cyber Extortion Infiltrate Launch droppers Ransom Data © 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com Money Cashed Darkweb used to Hide Origin Encryption © 2015 Secure Banking Solutions, LLC Money Paid in Bit. Coin 15 15
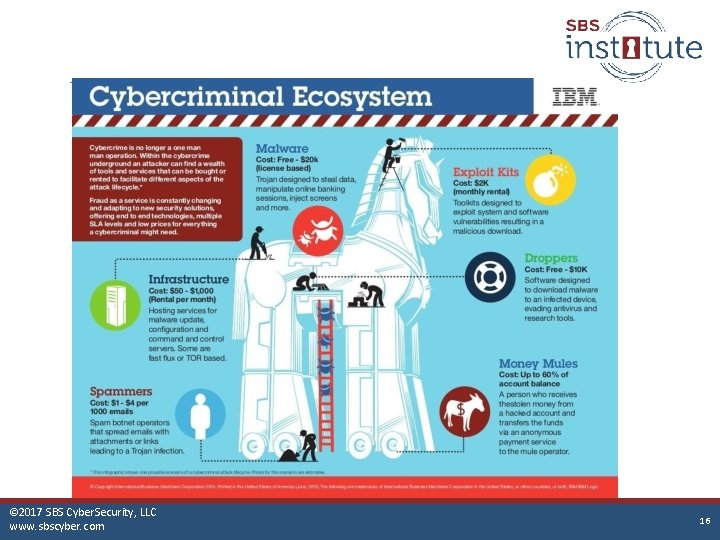
© 2017 SBS Cyber. Security, LLC www. sbscyber. com © Secure Banking Solutions, LLC 16
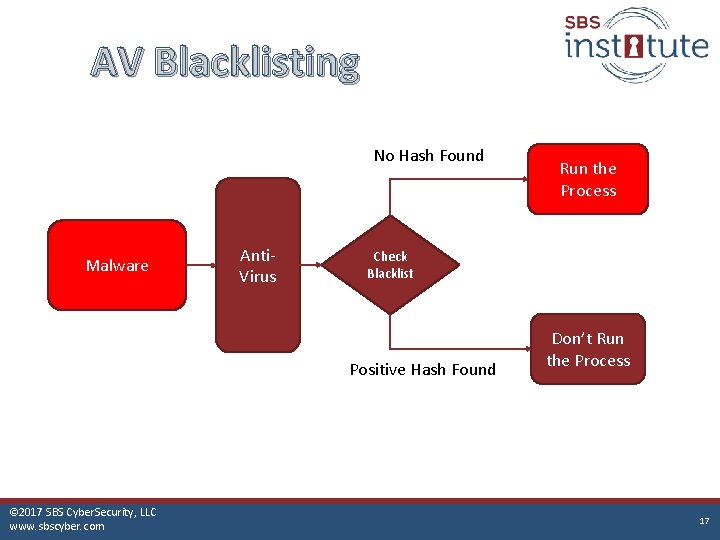
AV Blacklisting No Hash Found Malware Anti. Virus Check Blacklist Positive Hash Found © 2017 SBS Cyber. Security, LLC www. sbscyber. com Run the Process Don’t Run the Process 17
Saa. S and Iaa. S in the Underground • • • Phising as a service DDOS as a service Hacking as a service Social Engineering as a service Malware as a service Ransomware as a service © 2017 SBS Cyber. Security, LLC www. sbscyber. com 18
Phishing MATHEW 4: 10 -20 NLT JESUS C A LLE D OUT TO THEM, “C OME, F OLLO W ME, AND I WI LL S HOW YOU HOW TO F ISH F OR PEO PLE!” © 2017 SBS Cyber. Security, LLC www. sbscyber. com 19
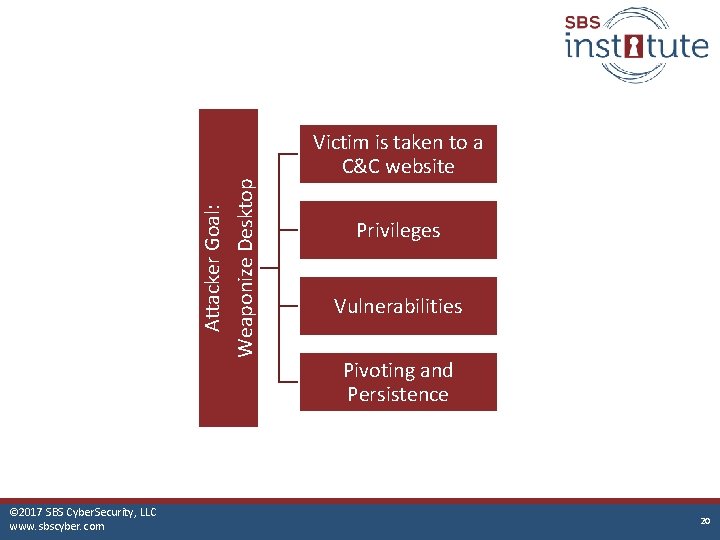
Attacker Goal: Weaponize Desktop Victim is taken to a C&C website © 2017 SBS Cyber. Security, LLC www. sbscyber. com Privileges Vulnerabilities Pivoting and Persistence 20
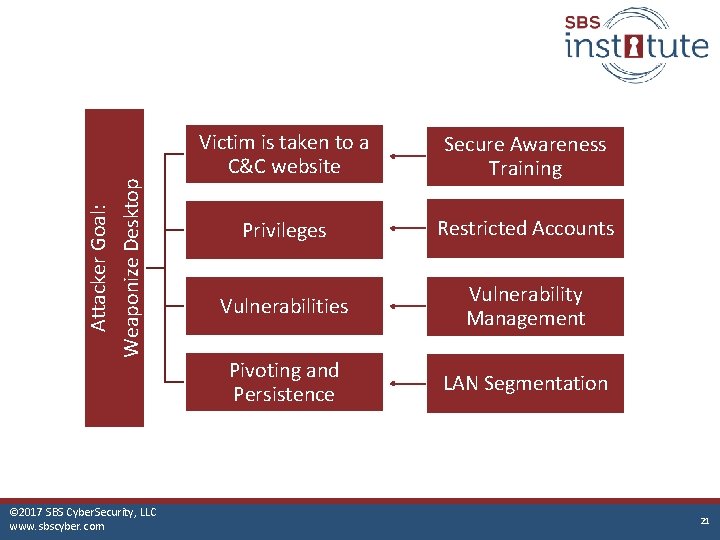
Attacker Goal: Weaponize Desktop © 2017 SBS Cyber. Security, LLC www. sbscyber. com Victim is taken to a C&C website Secure Awareness Training Privileges Restricted Accounts Vulnerabilities Vulnerability Management Pivoting and Persistence LAN Segmentation 21
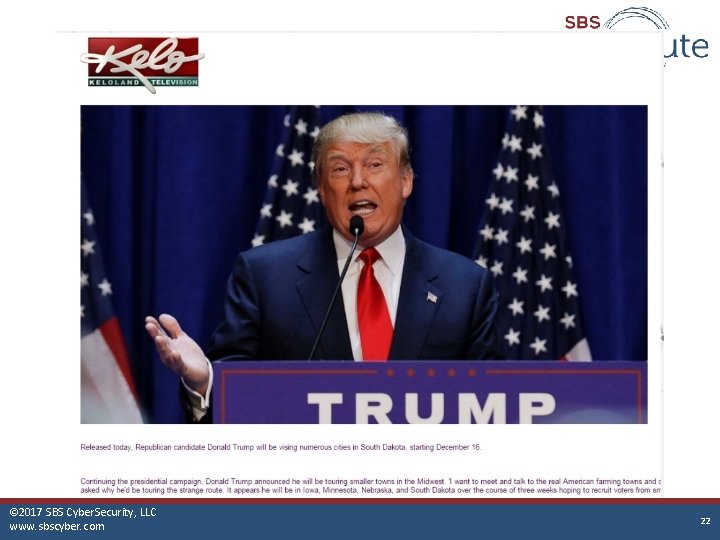
© 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 22 22
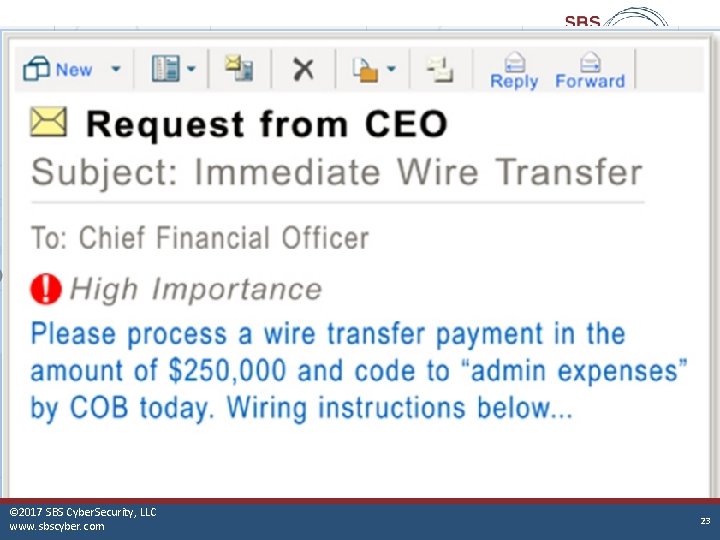
© 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 23 23

© 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 24 24
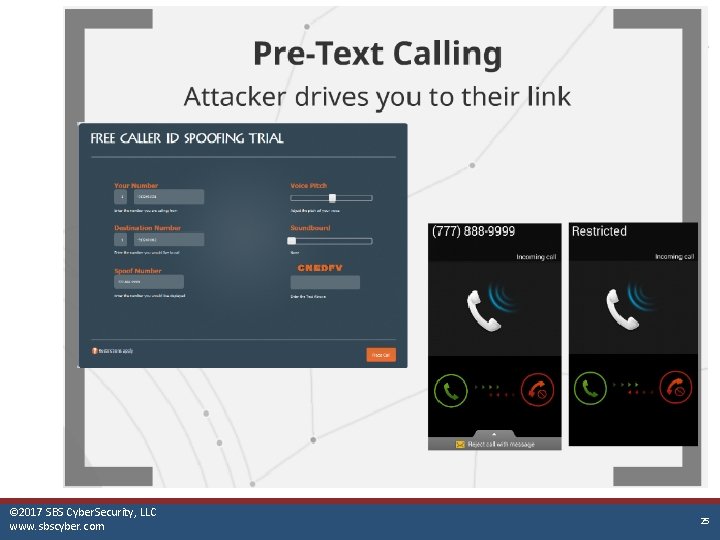
© 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 25 25
Ransomware ONE OF THE MOST DISRUPTIVE ATTACKS AN ORGANIZATION CAN SUFFER… © 2017 SBS Cyber. Security, LLC www. sbscyber. com 26
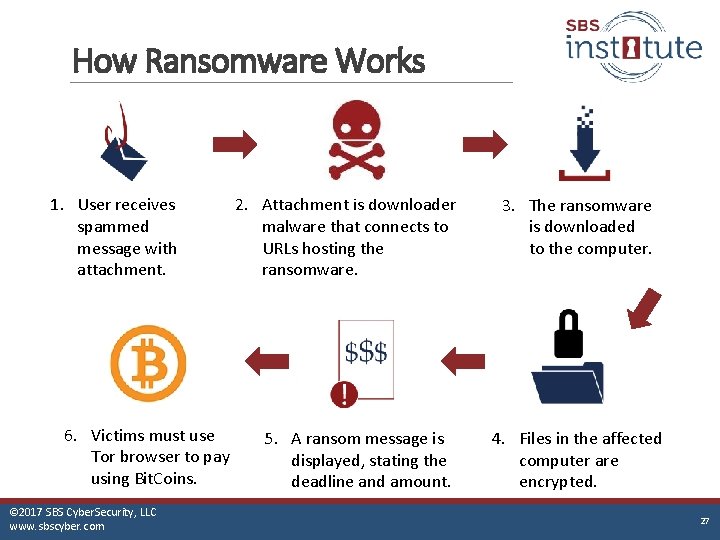
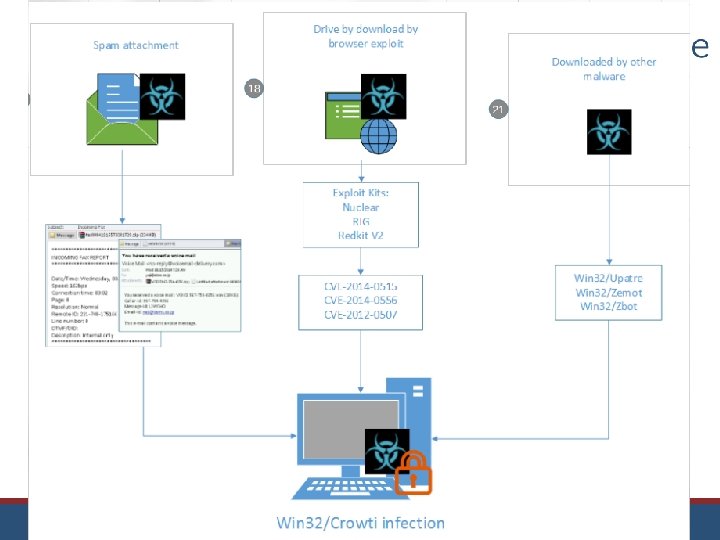
How Ransomware Works 1. User receives spammed message with attachment. 6. Victims must use Tor browser to pay using Bit. Coins. © 2017 SBS Cyber. Security, LLC www. sbscyber. com 2. Attachment is downloader malware that connects to URLs hosting the ransomware. 5. A ransom message is displayed, stating the deadline and amount. 3. The ransomware is downloaded to the computer. 4. Files in the affected computer are encrypted. 27
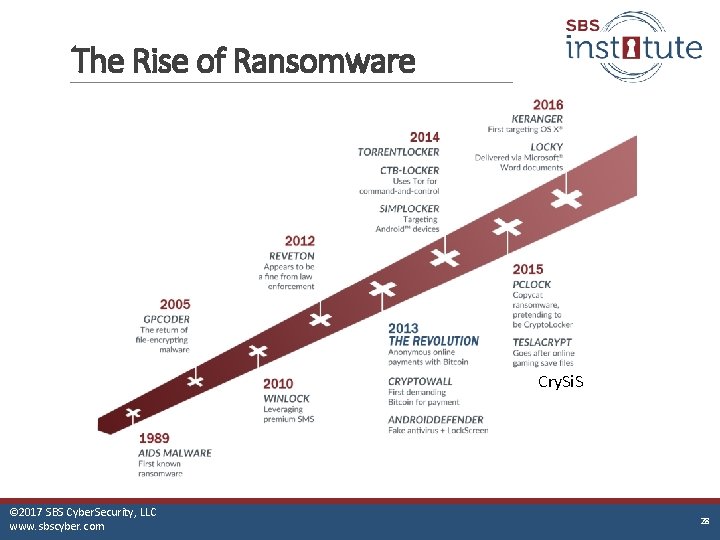
The Rise of Ransomware Cry. Si. S © 2017 SBS Cyber. Security, LLC www. sbscyber. com www. protectmybank. com © Secure Banking Solutions, LLC 28 28
www. protectmyban © 2015 Secure Banking Solutions, LLC 29
www. protectmyban © 2015 Secure Banking Solutions, LLC 30
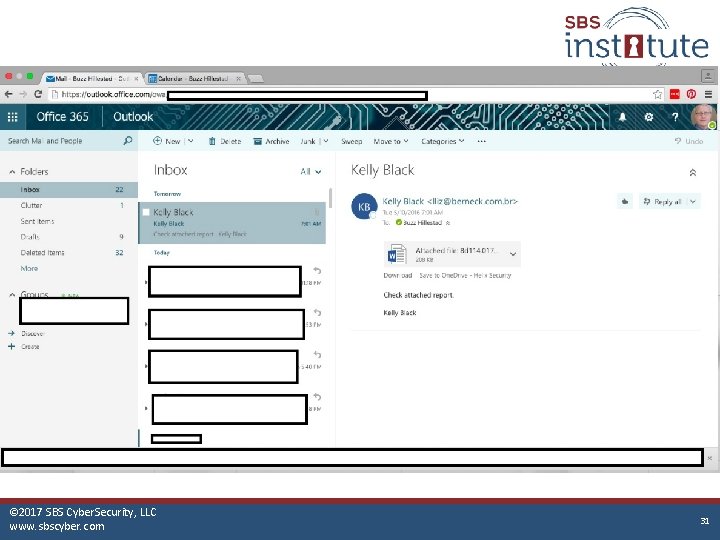
© 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 31 31
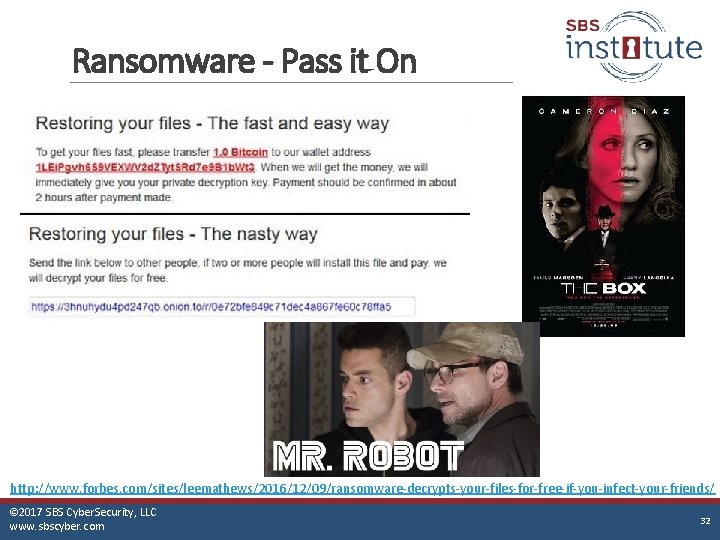
Ransomware - Pass it On http: //www. forbes. com/sites/leemathews/2016/12/09/ransomware-decrypts-your-files-for-free-if-you-infect-your-friends/ © 2017 SBS Cyber. Security, LLC www. sbscyber. com 32 32

Ransomware - HR Applicant http: //www. securityweek. com/ransomwarecampaign-targets-hr-departments © 2017 SBS Cyber. Security, LLC www. sbscyber. com 33 33
www. protectmyban © 2015 Secure Banking Solutions, LLC 34
© 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 35 35
www. protectmyban © 2015 Secure Banking Solutions, LLC 36
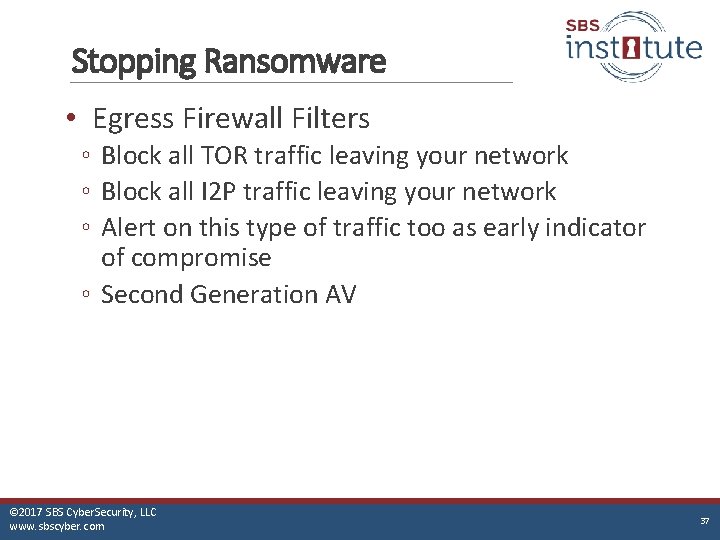
Stopping Ransomware • Egress Firewall Filters ◦ Block all TOR traffic leaving your network ◦ Block all I 2 P traffic leaving your network ◦ Alert on this type of traffic too as early indicator of compromise ◦ Second Generation AV © 2017 SBS Cyber. Security, LLC www. sbscyber. com 37 37

Creating a Better Password THE ONLY THING PROTECTING YOUR ORGANIZATION FROM A HACKER PRETENDING TO BE YOU… © 2017 SBS Cyber. Security, LLC www. sbscyber. com 38
Password Demonstration Let’s talk about passwords • • Length Complexity Cypher Entropy • We’ll use a few tools to demonstrate these items ◦ https: //howsecureismypassword. net/ ◦ Based on the actual password you type in, calculates how long it would take to crack it © 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 39 39
Password Research • Another tool: http: //calc. opensecurityresearch. com/ • Calculates password cracking times based on a single modern computer • Keep in mind that attackers can use distributed data processing to crack passwords – essentially a group of many computers © 2017 SBS Cyber. Security, LLC www. sbscyber. com 40
Entropy • The practice of making something so random, that it is un-guessable and very hard to crack • Issue with entropy – humans cannot remember the password © 2017 SBS Cyber. Security, LLC www. sbscyber. com 41
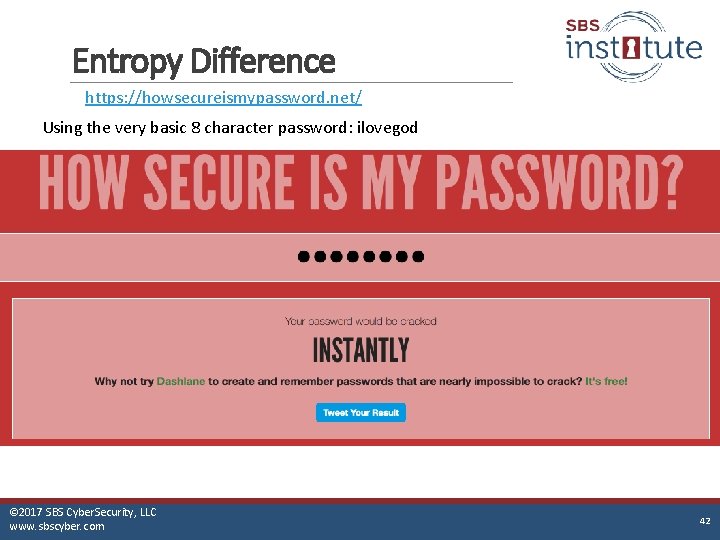
Entropy Difference https: //howsecureismypassword. net/ Using the very basic 8 character password: ilovegod © 2017 SBS Cyber. Security, LLC www. sbscyber. com 42

Entropy Difference https: //howsecureismypassword. net/ Using a highly entropic 8 character password: 8&uj%RVp © 2017 SBS Cyber. Security, LLC www. sbscyber. com 43
Entropy • Entropy can make a big difference – but not a big enough difference • Also, humans have a hard time memorizing highly entropic passwords ◦ If you can memorize a long and entropic password, great, but most cannot © 2017 SBS Cyber. Security, LLC www. sbscyber. com 44
Cypher • The algorythm that mixes up the password and substitutes letters, numbers, and symbols for other characters to create a password hash that is machine readable • Issue with cypher – early cyphers were easy to reverse engineer • Modern cyphers are a lot better – need to use modern cyphers © 2017 SBS Cyber. Security, LLC www. sbscyber. com 45
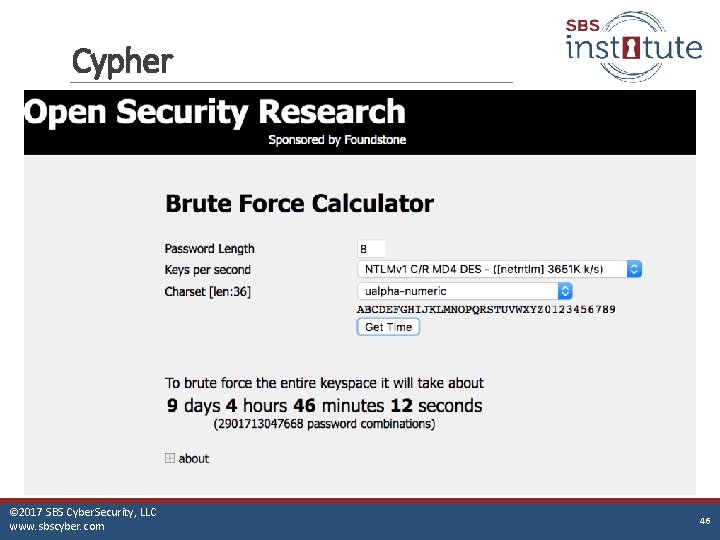
Cypher © 2017 SBS Cyber. Security, LLC www. sbscyber. com 46
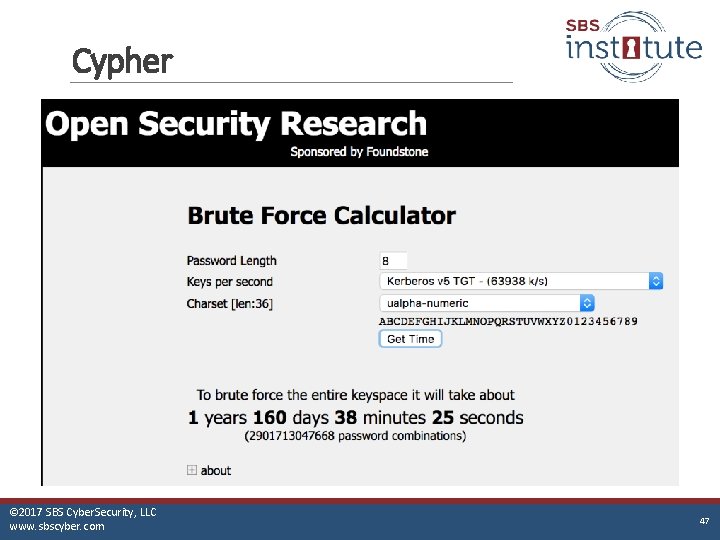
Cypher © 2017 SBS Cyber. Security, LLC www. sbscyber. com 47
Cypher • Makes a pretty big difference • Issue - Highly dependent on technology used © 2017 SBS Cyber. Security, LLC www. sbscyber. com 48
Complexity • This is the amount of different types of characters in a password ◦ ◦ ◦ Upper case letters Lower case letters Numbers Special characters - !@#$%^&*() etc… Spaces © 2017 SBS Cyber. Security, LLC www. sbscyber. com 49
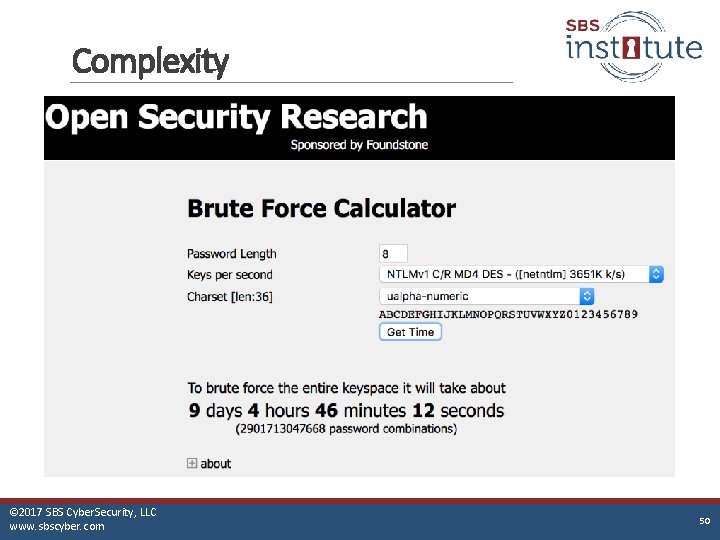
Complexity © 2017 SBS Cyber. Security, LLC www. sbscyber. com 50
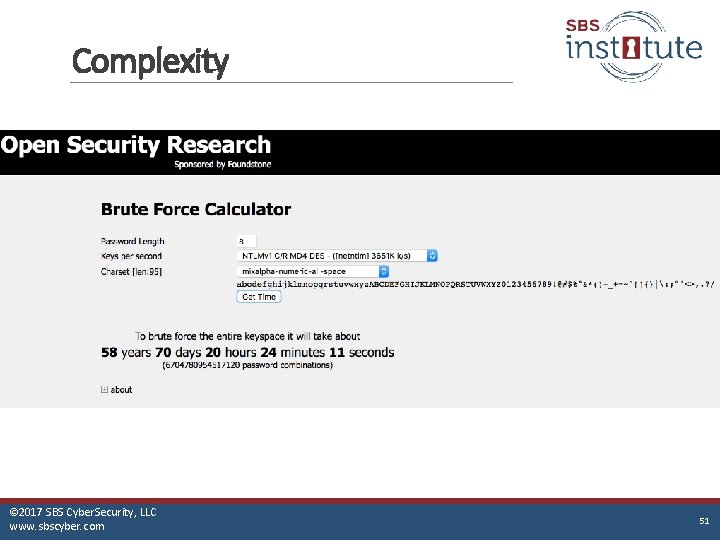
Complexity © 2017 SBS Cyber. Security, LLC www. sbscyber. com 51
Complexity • Makes a very big difference • Issue – humans have a hard time with complex passwords both typing them and remembering them © 2017 SBS Cyber. Security, LLC www. sbscyber. com 52
Length • Simply – the number of characters in a password © 2017 SBS Cyber. Security, LLC www. sbscyber. com 53
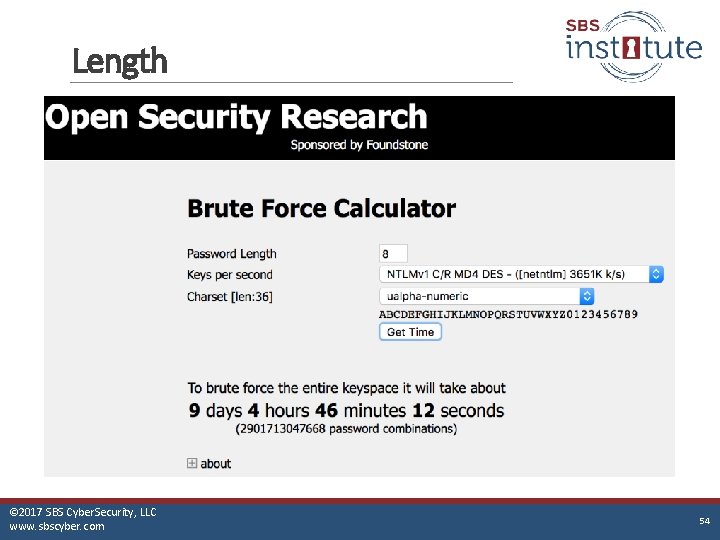
Length © 2017 SBS Cyber. Security, LLC www. sbscyber. com 54
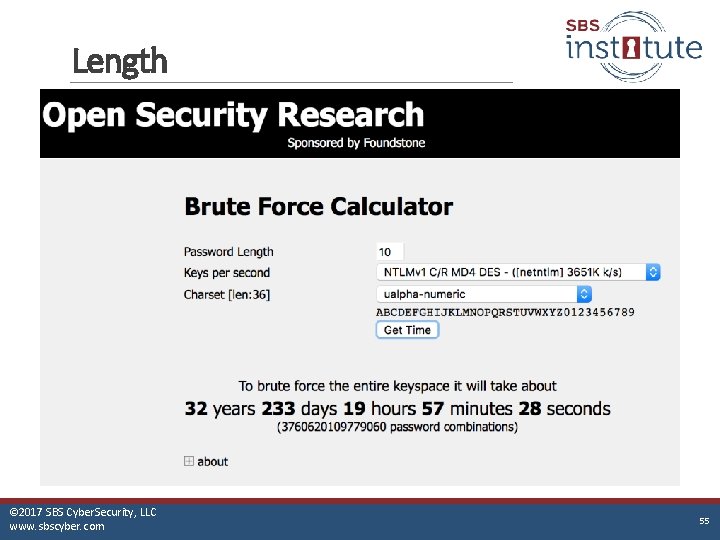
Length © 2017 SBS Cyber. Security, LLC www. sbscyber. com 55
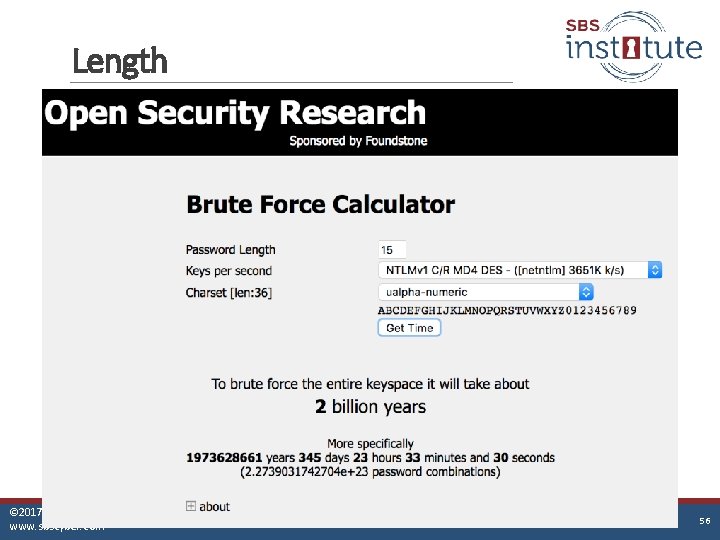
Length © 2017 SBS Cyber. Security, LLC www. sbscyber. com 56
Length • Length is the single biggest difference in password strength • It’s the only password factor that follows and exponential curve of growth rather than a linear progression • It is also very easy for humans to control © 2017 SBS Cyber. Security, LLC www. sbscyber. com 57
Creating a Better Password • So what if we combine all the tricks we’ve learned AND also make it easy to remember? • I l 0 ve the Yank 33 s! ◦ ◦ ◦ Easy to remember! Not guessable because I hate baseball Decent complexity Almost no entropy Using a modern cypher MS Windows 2012 R 2 or better © 2017 SBS Cyber. Security, LLC www. sbscyber. com 58
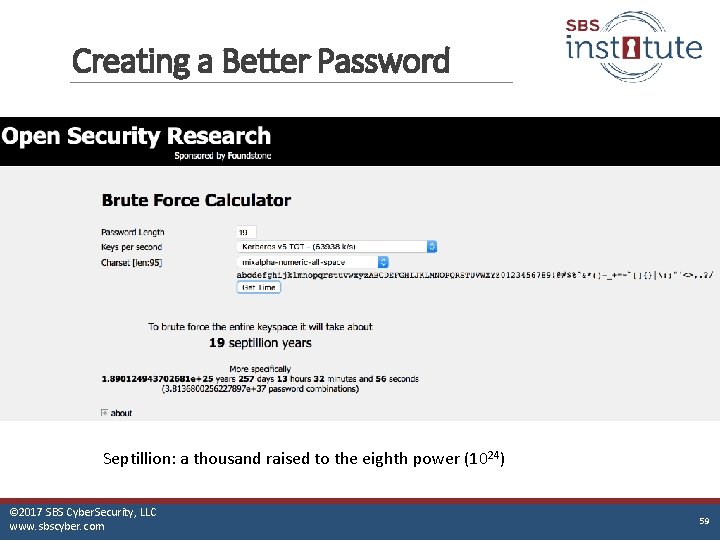
Creating a Better Password Septillion: a thousand raised to the eighth power (1024) © 2017 SBS Cyber. Security, LLC www. sbscyber. com 59
Additional Controls • Other attacks that good passwords won’t help ◦ ◦ Credential stealing Pass the hash Phishing for passwords Keylogging • Fix ◦ Multi-factor authentication § 2 factors – something you know § 1 factor – something you have (physical key gen) or are (biometrics) © 2017 SBS Cyber. Security, LLC www. sbscyber. com 60
Security is Everyone’s Responsibility. © 2017 SBS Cyber. Security, LLC www. protectmyban www. sbscyber. com © 2015 Secure Banking Solutions, LLC 61 61
- Slides: 61