Random Subdomain DDo S Attack Mitigation Using Efficient
Random Subdomain DDo. S Attack Mitigation Using Efficient Distinct Heavy Hitters Shir Landau Feibish, Yehuda Afek, Anat Bremler-Barr, Edith Cohen, Michal Shagam 1
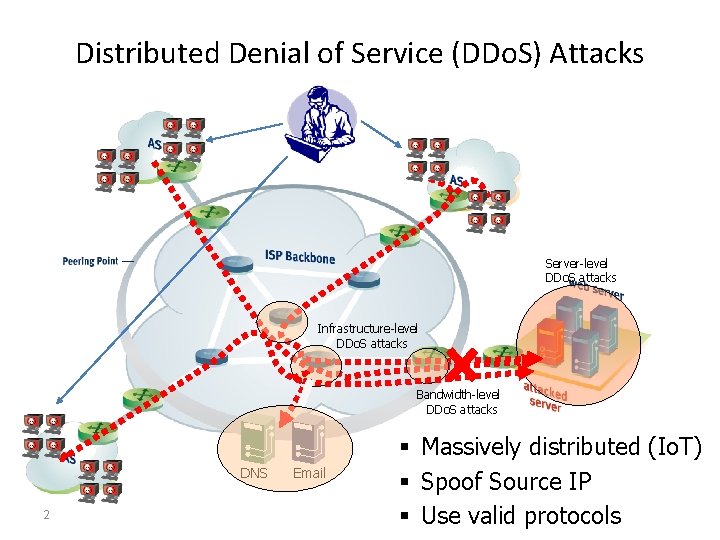
Distributed Denial of Service (DDo. S) Attacks Server-level DDo. S attacks Infrastructure-level DDo. S attacks Bandwidth-level DDo. S attacks DNS 2 Email § Massively distributed (Io. T) § Spoof Source IP § Use valid protocols
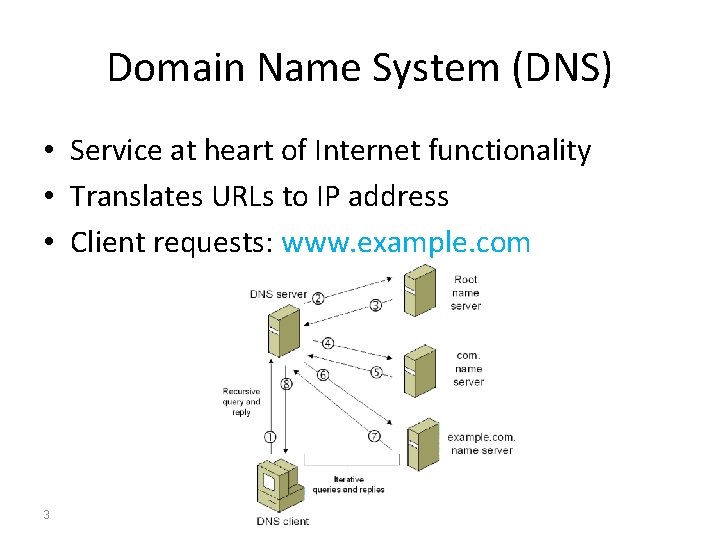
Domain Name System (DNS) • Service at heart of Internet functionality • Translates URLs to IP address • Client requests: www. example. com 3
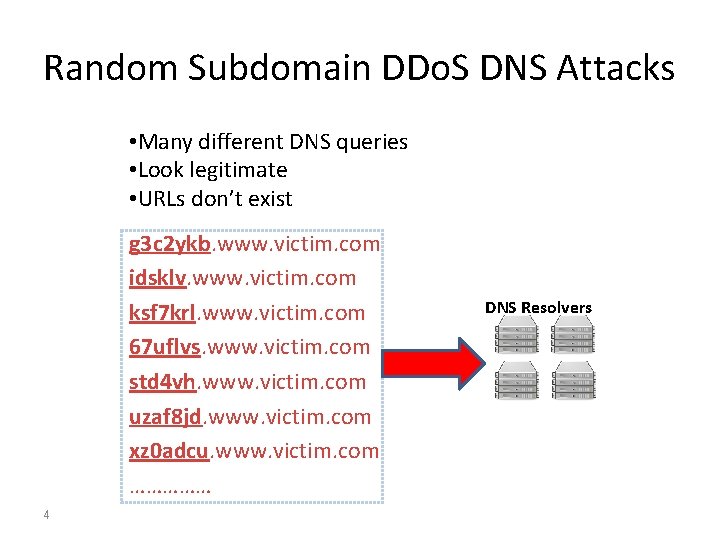
Random Subdomain DDo. S DNS Attacks • Many different DNS queries • Look legitimate • URLs don’t exist g 3 c 2 ykb. www. victim. com idsklv. www. victim. com ksf 7 krl. www. victim. com 67 uflvs. www. victim. com std 4 vh. www. victim. com uzaf 8 jd. www. victim. com xz 0 adcu. www. victim. com …………… 4 DNS Resolvers
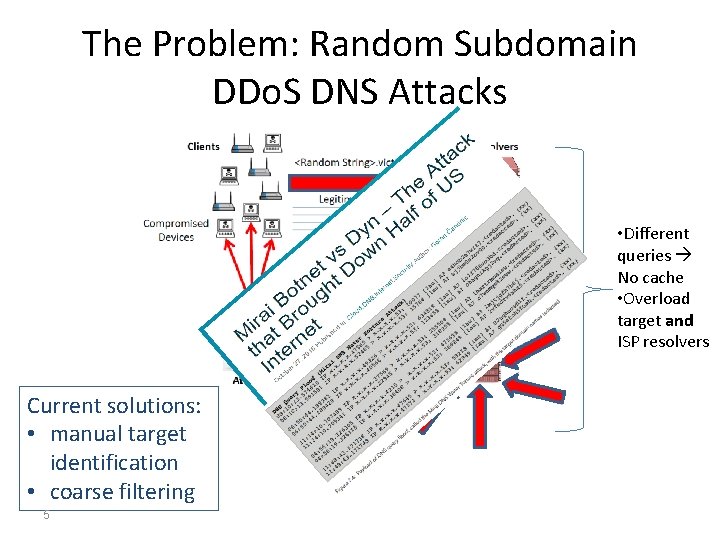
The Problem: Random Subdomain DDo. S DNS Attacks • Different queries No cache • Overload target and ISP resolvers Current solutions: • manual target identification • coarse filtering 5
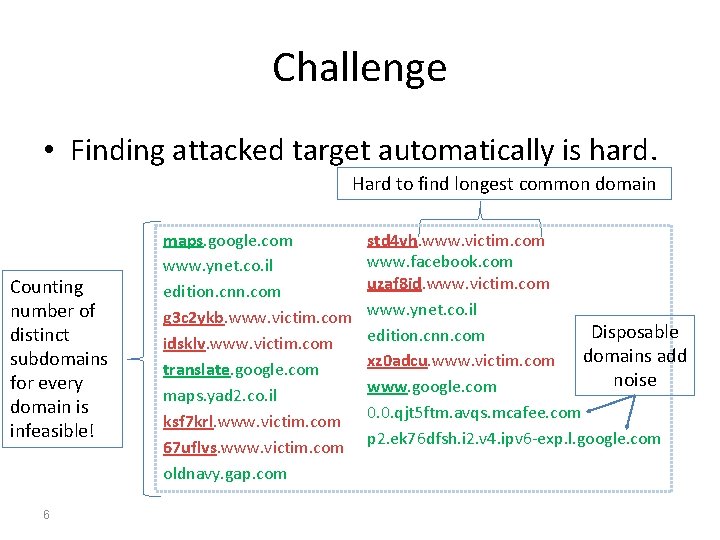
Challenge • Finding attacked target automatically is hard. Hard to find longest common domain Counting number of distinct subdomains for every domain is infeasible! 6 maps. google. com www. ynet. co. il edition. cnn. com g 3 c 2 ykb. www. victim. com idsklv. www. victim. com translate. google. com maps. yad 2. co. il ksf 7 krl. www. victim. com 67 uflvs. www. victim. com oldnavy. gap. com std 4 vh. www. victim. com www. facebook. com uzaf 8 jd. www. victim. com www. ynet. co. il Disposable edition. cnn. com domains add xz 0 adcu. www. victim. com noise www. google. com 0. 0. qjt 5 ftm. avqs. mcafee. com p 2. ek 76 dfsh. i 2. v 4. ipv 6 -exp. l. google. com
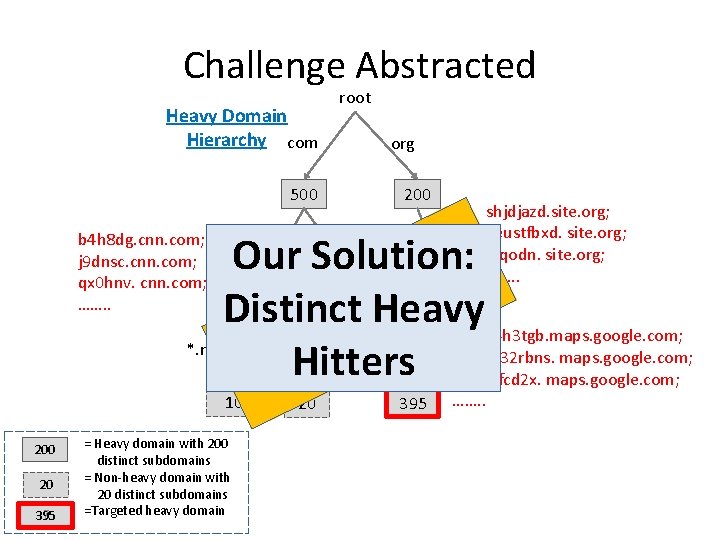
Challenge Abstracted Heavy Domain Hierarchy com root org 500 200 shjdjazd. site. org; keustfbxd. site. org; *. site alqodn. site. org; ……. . 155 : n Our Solution: o i t u l o 60 420 s e Distinct Heavy t l c b i Jch 894 h 3 tgb. maps. google. com; a s *. maps *. news. Ex *. mail a bfkas 332 rbns. maps. google. com; e f Hitters n 32562 fcd 2 x. maps. google. com; I 10 20 395 ……. . b 4 h 8 dg. cnn. com; j 9 dnsc. cnn. com; qx 0 hnv. cnn. com; ……. . 200 20 7 395 = Heavy domain with 200 distinct subdomains = Non-heavy domain with 20 distinct subdomains =Targeted heavy domain cnn google
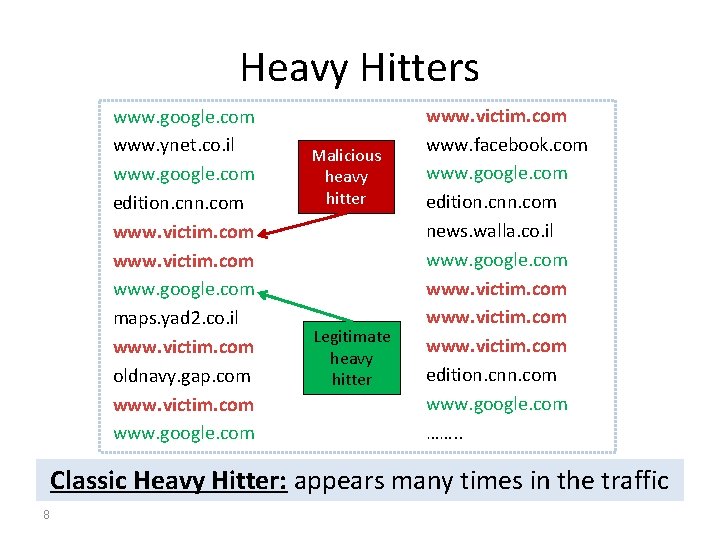
Heavy Hitters www. google. com www. ynet. co. il www. google. com edition. cnn. com www. victim. com www. google. com maps. yad 2. co. il www. victim. com oldnavy. gap. com www. victim. com www. google. com Malicious heavy hitter Legitimate heavy hitter www. victim. com www. facebook. com www. google. com edition. cnn. com news. walla. co. il www. google. com www. victim. com edition. cnn. com www. google. com ……. . Classic Heavy Hitter: appears many times in the traffic 8
![Distinct Heavy Hitters aka Superspreaders [Venkataraman et al. NDSS ‘ 05 ] 9 Distinct Distinct Heavy Hitters aka Superspreaders [Venkataraman et al. NDSS ‘ 05 ] 9 Distinct](http://slidetodoc.com/presentation_image_h/1b01cb22669a0791f93865a7d84bd4e8/image-9.jpg)
Distinct Heavy Hitters aka Superspreaders [Venkataraman et al. NDSS ‘ 05 ] 9 Distinct Heavy Hitter: has many different subdomains
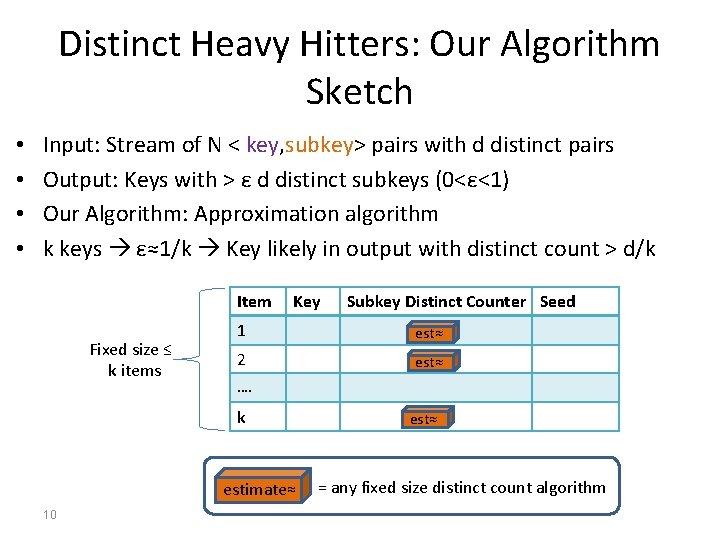
Distinct Heavy Hitters: Our Algorithm Sketch • • Input: Stream of N < key, subkey> pairs with d distinct pairs Output: Keys with > ε d distinct subkeys (0<ε<1) Our Algorithm: Approximation algorithm k keys ε≈1/k Key likely in output with distinct count > d/k Item Fixed size ≤ k items Key 1 est≈ 2 est≈ …. k estimate≈ 10 Subkey Distinct Counter Seed est≈ = any fixed size distinct count algorithm
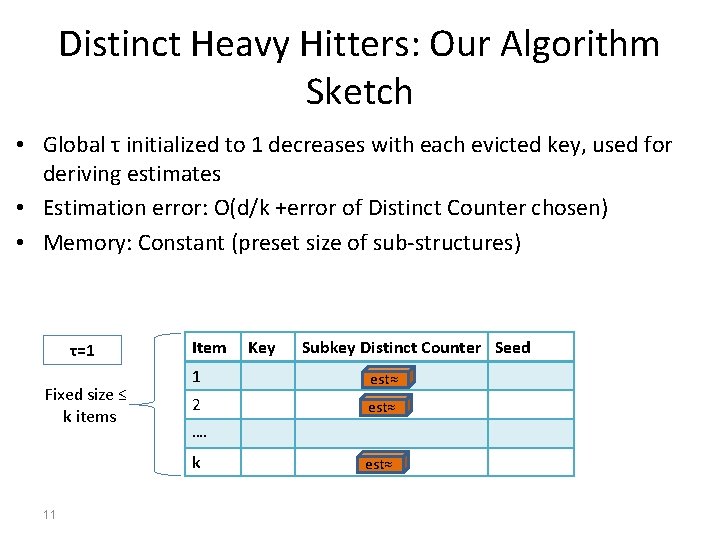
Distinct Heavy Hitters: Our Algorithm Sketch • Global τ initialized to 1 decreases with each evicted key, used for deriving estimates • Estimation error: O(d/k +error of Distinct Counter chosen) • Memory: Constant (preset size of sub-structures) τ=1 Fixed size ≤ k items Item Subkey Distinct Counter Seed 1 est≈ 2 est≈ …. k 11 Key est≈
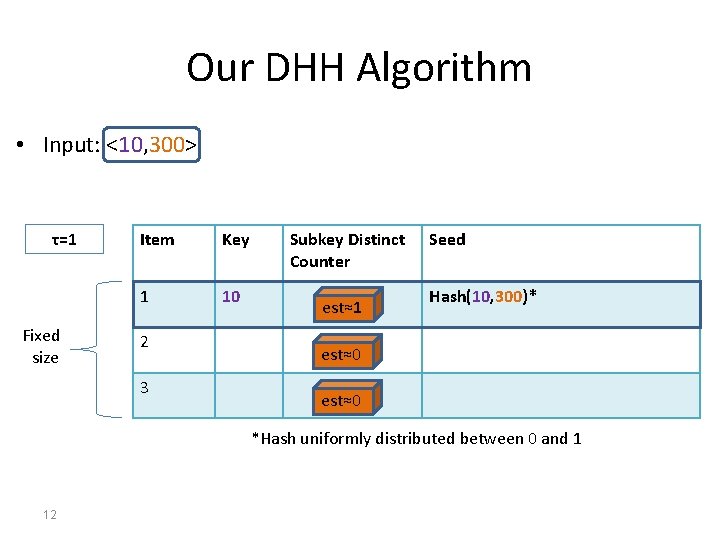
Our DHH Algorithm • Input: <10, 300> τ=1 Fixed size Item Key 1 10 2 3 Subkey Distinct Counter est≈1 Seed Hash(10, 300)* est≈0 *Hash uniformly distributed between 0 and 1 12
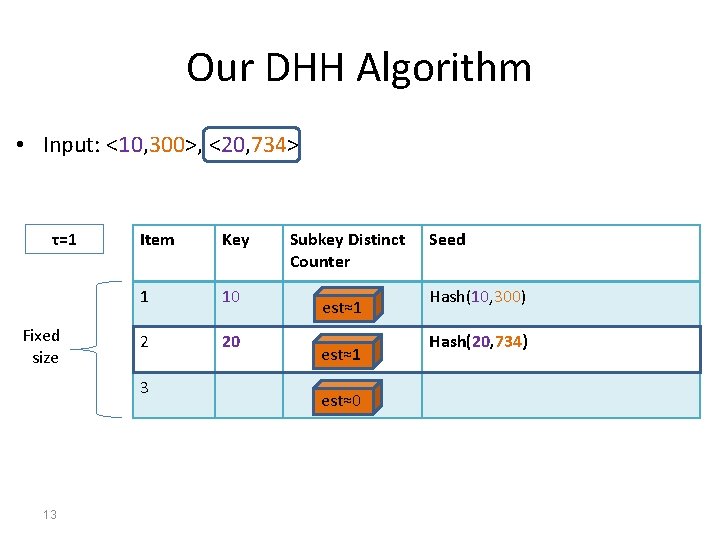
Our DHH Algorithm • Input: <10, 300>, <20, 734> τ=1 Fixed size Item Key 1 10 2 20 3 13 Subkey Distinct Counter est≈1 est≈0 Seed Hash(10, 300) Hash(20, 734)
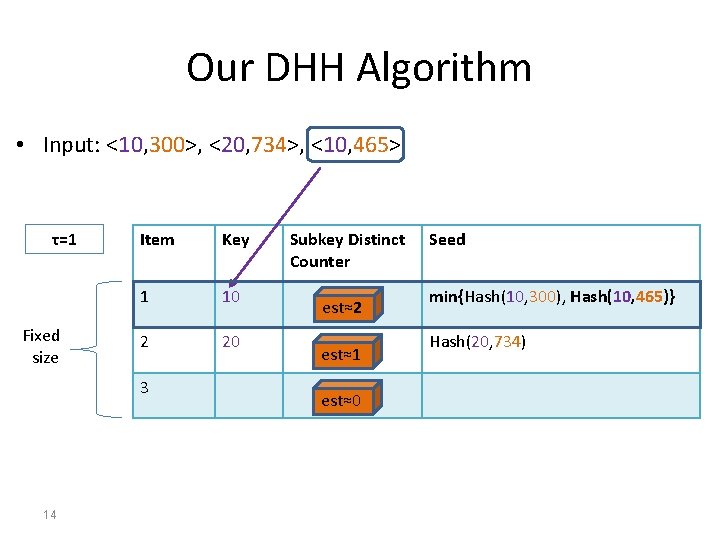
Our DHH Algorithm • Input: <10, 300>, <20, 734>, <10, 465> τ=1 Fixed size Item Key 1 10 2 20 3 14 Subkey Distinct Counter est≈2 est≈1 est≈0 Seed min{Hash(10, 300), Hash(10, 465)} Hash(20, 734)
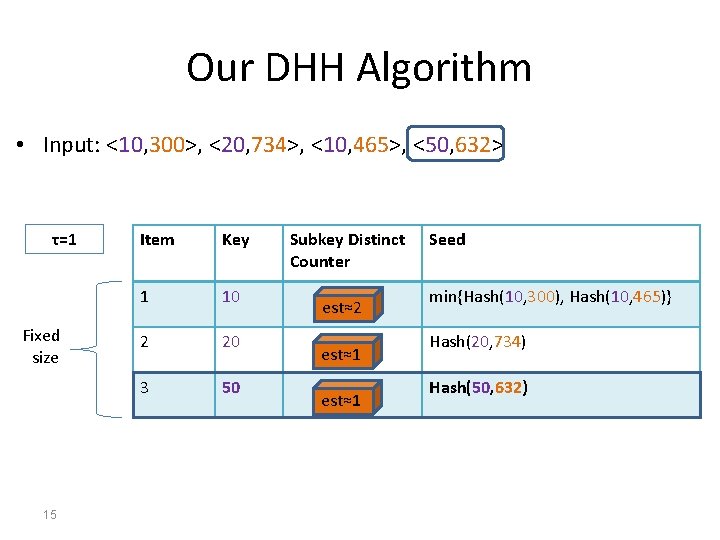
Our DHH Algorithm • Input: <10, 300>, <20, 734>, <10, 465>, <50, 632> τ=1 Fixed size 15 Item Key 1 10 2 20 3 50 Subkey Distinct Counter est≈2 est≈1 Seed min{Hash(10, 300), Hash(10, 465)} Hash(20, 734) Hash(50, 632)
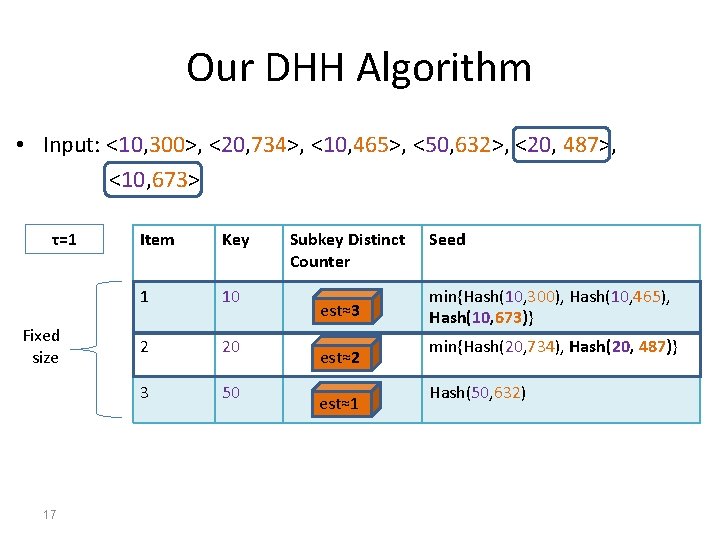
Our DHH Algorithm • Input: <10, 300>, <20, 734>, <10, 465>, <50, 632>, <20, 487>, <10, 673> τ=1 Fixed size 17 Item Key 1 10 2 20 3 50 Subkey Distinct Counter est≈3 est≈2 est≈1 Seed min{Hash(10, 300), Hash(10, 465), Hash(10, 673)} min{Hash(20, 734), Hash(20, 487)} Hash(50, 632)
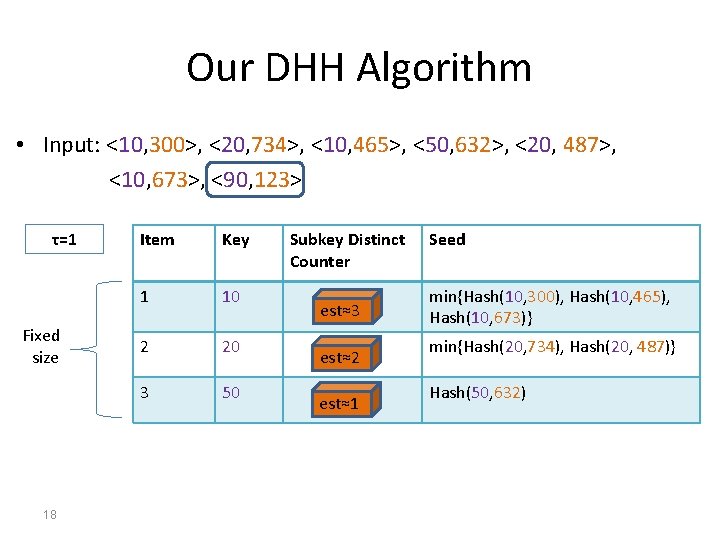
Our DHH Algorithm • Input: <10, 300>, <20, 734>, <10, 465>, <50, 632>, <20, 487>, <10, 673>, <90, 123> τ=1 Fixed size 18 Item Key 1 10 2 20 3 50 Subkey Distinct Counter est≈3 est≈2 est≈1 Seed min{Hash(10, 300), Hash(10, 465), Hash(10, 673)} min{Hash(20, 734), Hash(20, 487)} Hash(50, 632)
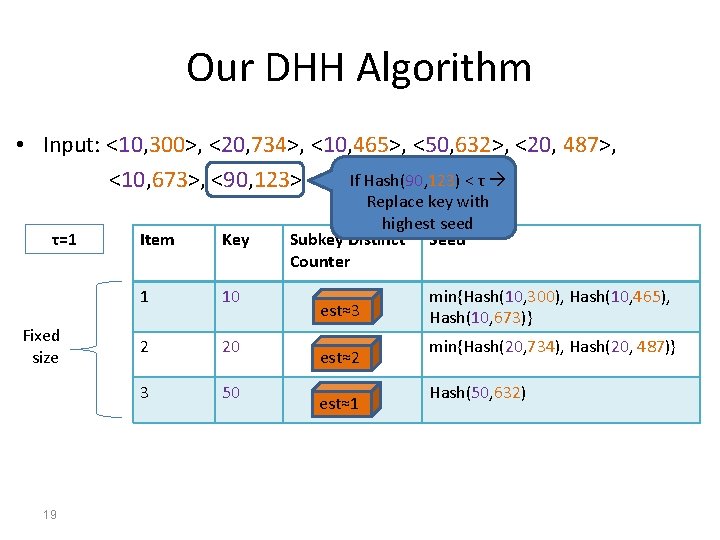
Our DHH Algorithm • Input: <10, 300>, <20, 734>, <10, 465>, <50, 632>, <20, 487>, If Hash(90, 123) < τ <10, 673>, <90, 123> τ=1 Fixed size 19 Item Key 1 10 2 20 3 50 Replace key with highest seed Subkey Distinct Seed Counter est≈3 est≈2 est≈1 min{Hash(10, 300), Hash(10, 465), Hash(10, 673)} min{Hash(20, 734), Hash(20, 487)} Hash(50, 632)
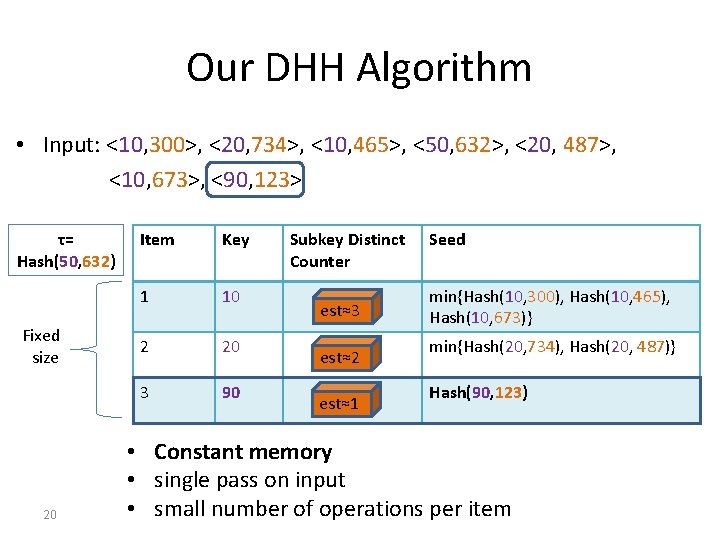
Our DHH Algorithm • Input: <10, 300>, <20, 734>, <10, 465>, <50, 632>, <20, 487>, <10, 673>, <90, 123> τ= Hash(50, 632) Fixed size 20 Item Key 1 10 2 20 3 90 Subkey Distinct Counter est≈3 est≈2 est≈1 Seed min{Hash(10, 300), Hash(10, 465), Hash(10, 673)} min{Hash(20, 734), Hash(20, 487)} Hash(90, 123) • Constant memory • single pass on input • small number of operations per item
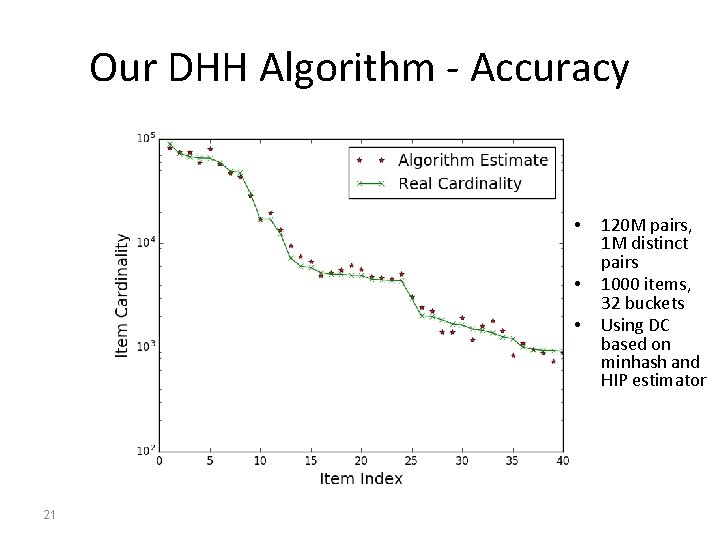
Our DHH Algorithm - Accuracy • • • 21 120 M pairs, 1 M distinct pairs 1000 items, 32 buckets Using DC based on minhash and HIP estimator
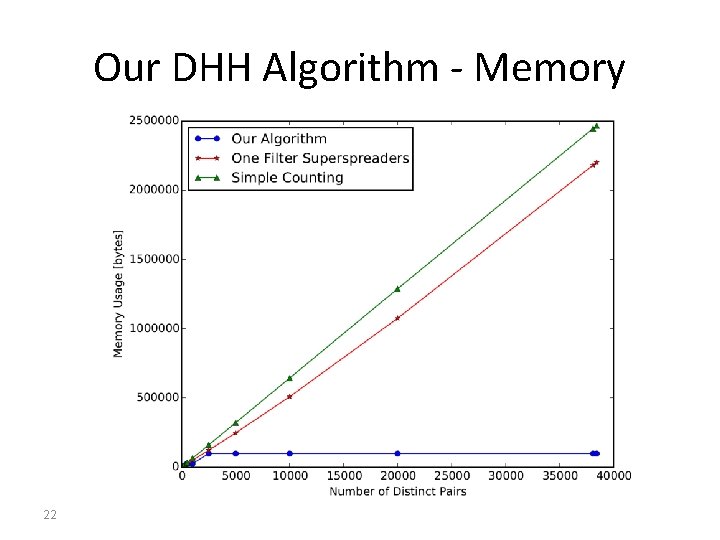
Our DHH Algorithm - Memory 22
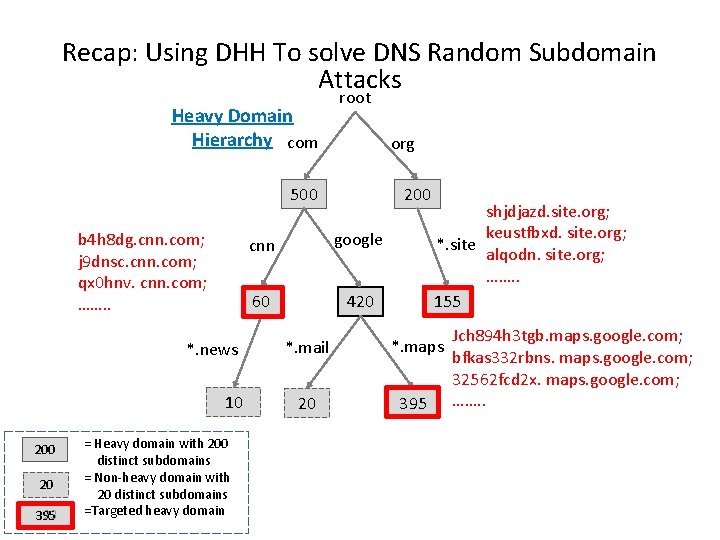
Recap: Using DHH To solve DNS Random Subdomain Attacks Heavy Domain Hierarchy com root org 500 b 4 h 8 dg. cnn. com; j 9 dnsc. cnn. com; qx 0 hnv. cnn. com; ……. . *. news 10 20 23 395 = Heavy domain with 200 distinct subdomains = Non-heavy domain with 20 distinct subdomains =Targeted heavy domain 200 cnn google 60 420 shjdjazd. site. org; keustfbxd. site. org; *. site alqodn. site. org; ……. . 155 *. mail *. maps 20 395 Jch 894 h 3 tgb. maps. google. com; bfkas 332 rbns. maps. google. com; 32562 fcd 2 x. maps. google. com; ……. .
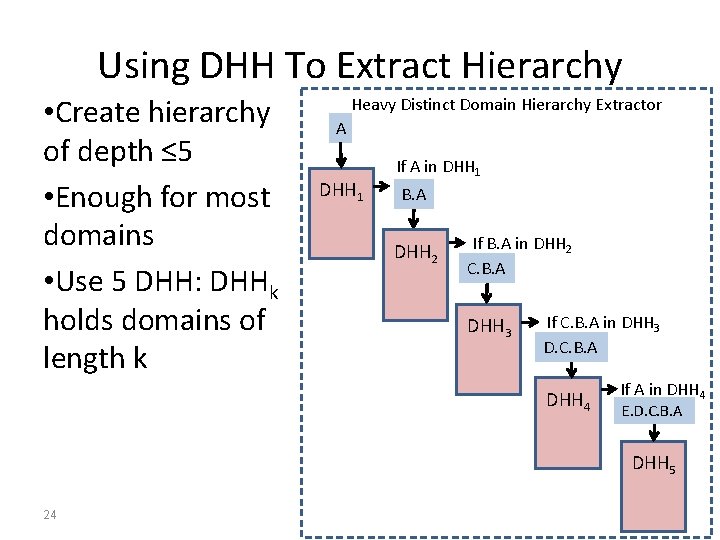
Using DHH To Extract Hierarchy • Create hierarchy of depth ≤ 5 • Enough for most domains • Use 5 DHH: DHHk holds domains of length k Heavy Distinct Domain Hierarchy Extractor A DHH 1 If A in DHH 1 B. A DHH 2 If B. A in DHH 2 C. B. A DHH 3 If C. B. A in DHH 3 D. C. B. A DHH 4 If A in DHH 4 E. D. C. B. A DHH 5 24
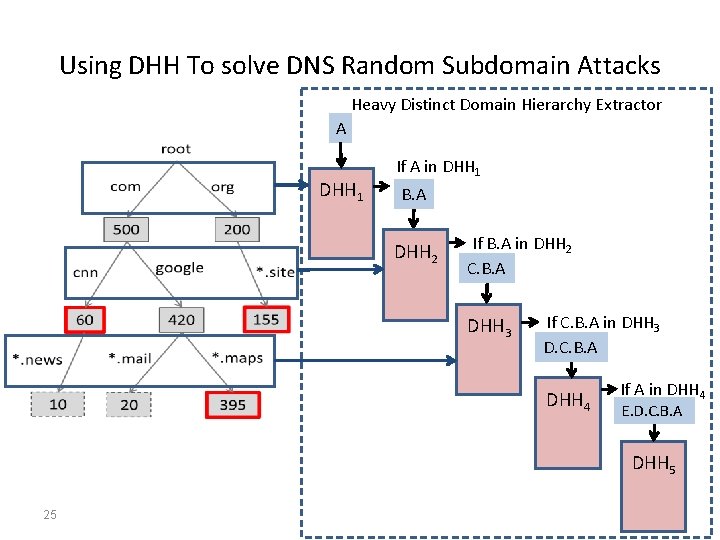
Using DHH To solve DNS Random Subdomain Attacks Heavy Distinct Domain Hierarchy Extractor A DHH 1 If A in DHH 1 B. A DHH 2 If B. A in DHH 2 C. B. A DHH 3 If C. B. A in DHH 3 D. C. B. A DHH 4 If A in DHH 4 E. D. C. B. A DHH 5 25
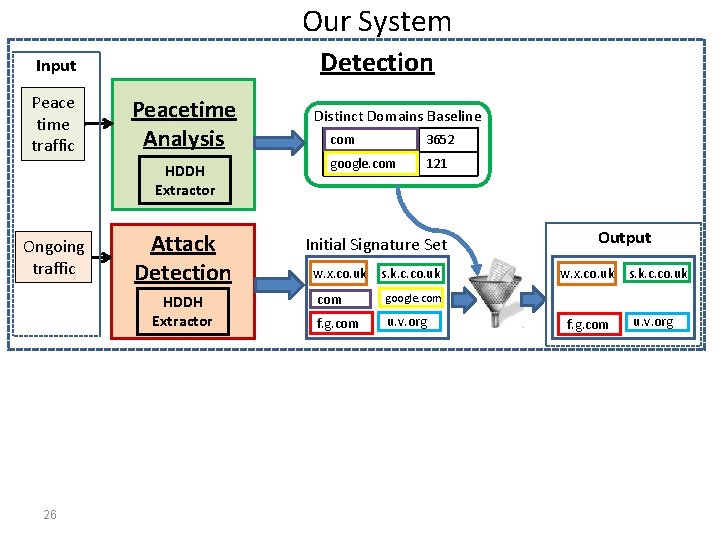
Our System Detection Input Peace time traffic Peacetime Analysis HDDH Extractor Ongoing traffic Attack Detection HDDH Extractor 26 Distinct Domains Baseline com 3652 google. com 121 Initial Signature Set w. x. co. uk s. k. c. co. uk com google. com f. g. com u. v. org Output w. x. co. uk f. g. com s. k. c. co. uk u. v. org
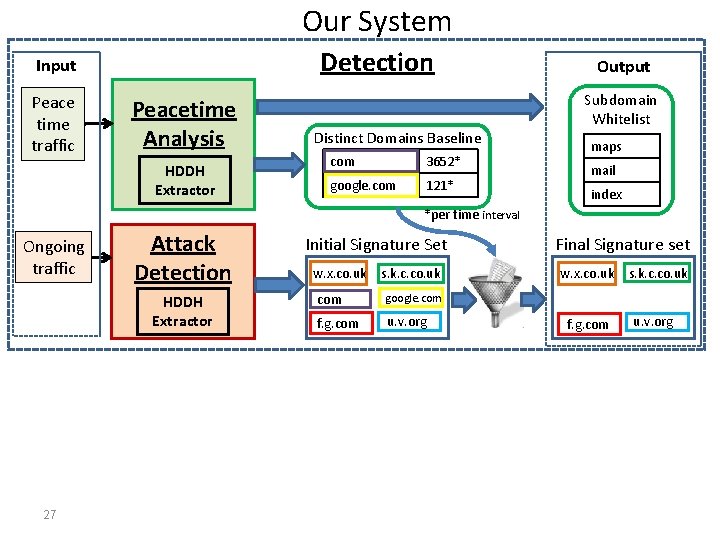
Our System Detection Input Peace time traffic Peacetime Analysis HDDH Extractor Distinct Domains Baseline com 3652* google. com 121* Output Subdomain Whitelist maps mail index *per time interval Ongoing traffic Attack Detection HDDH Extractor 27 Initial Signature Set w. x. co. uk s. k. c. co. uk com google. com f. g. com u. v. org Final Signature set w. x. co. uk f. g. com s. k. c. co. uk u. v. org
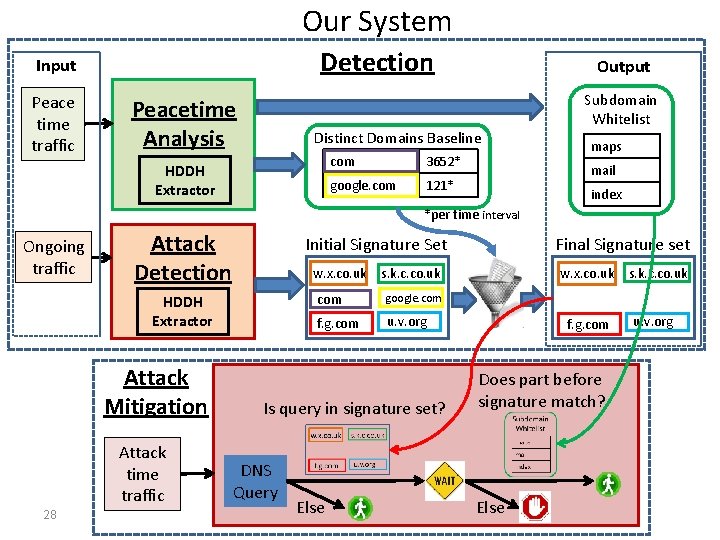
Our System Detection Input Peace time traffic Peacetime Analysis Output Distinct Domains Baseline HDDH Extractor com 3652* google. com 121* Subdomain Whitelist maps mail index *per time interval Ongoing traffic Attack Detection Initial Signature Set w. x. co. uk HDDH Extractor Attack Mitigation Attack time traffic 28 s. k. c. co. uk com google. com f. g. com u. v. org Is query in signature set? DNS Query Else Final Signature set w. x. co. uk f. g. com Does part before signature match? Else s. k. c. co. uk u. v. org
Conclusion • We present the first known system for Random Subdomain attack mitigation. • We present an algorithm for finding distinct heavy hitters with improved space-accuracy tradeoffs 29

30
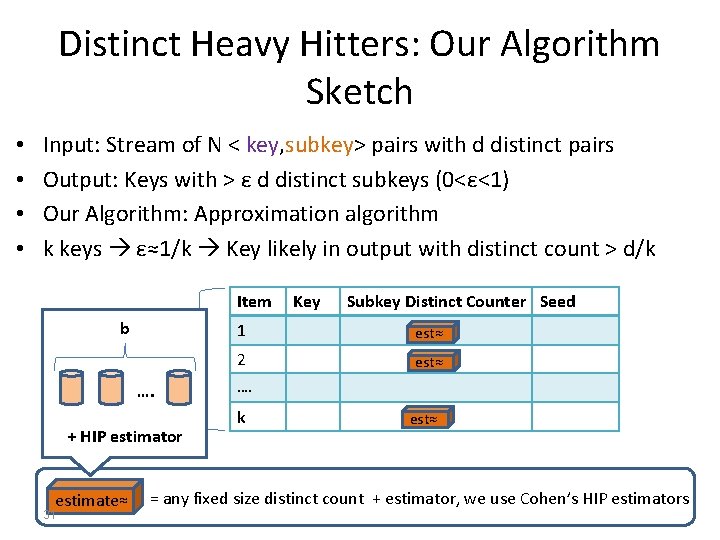
Distinct Heavy Hitters: Our Algorithm Sketch • • Input: Stream of N < key, subkey> pairs with d distinct pairs Output: Keys with > ε d distinct subkeys (0<ε<1) Our Algorithm: Approximation algorithm k keys ε≈1/k Key likely in output with distinct count > d/k Item b Fixed size ≤ k items …. + HIP estimator estimate≈ 31 Key Subkey Distinct Counter Seed 1 est≈ 2 est≈ …. k est≈ = any fixed size distinct count + estimator, we use Cohen’s HIP estimators
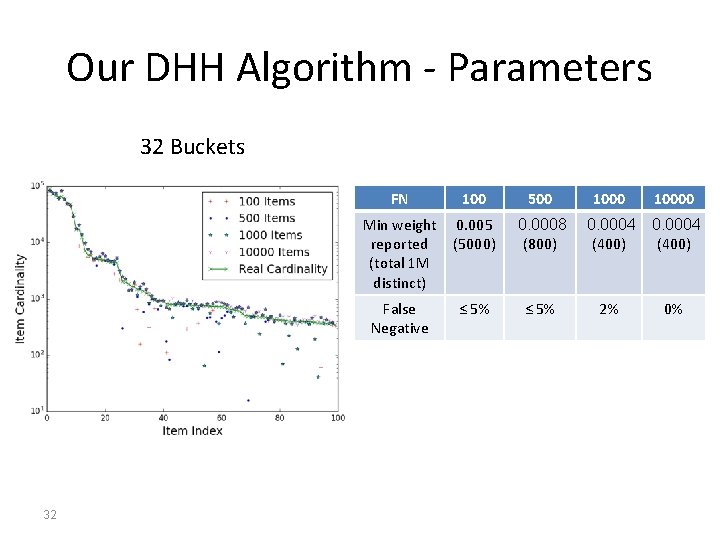
Our DHH Algorithm - Parameters 32 Buckets 32 FN 100 500 Min weight reported (total 1 M distinct) 0. 005 (5000) 0. 0008 (800) False Negative ≤ 5% 10000 0. 0004 (400) 2% 0%
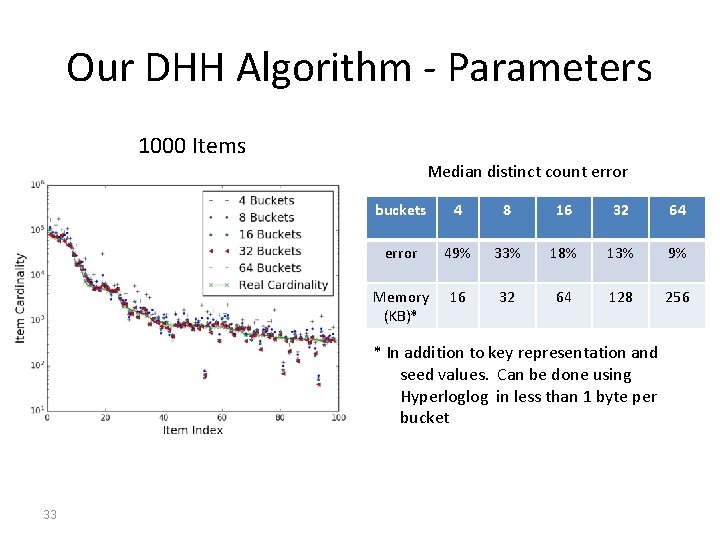
Our DHH Algorithm - Parameters 1000 Items Median distinct count error buckets 4 8 16 32 64 error 49% 33% 18% 13% 9% Memory (KB)* 16 32 64 128 256 * In addition to key representation and seed values. Can be done using Hyperloglog in less than 1 byte per bucket 33
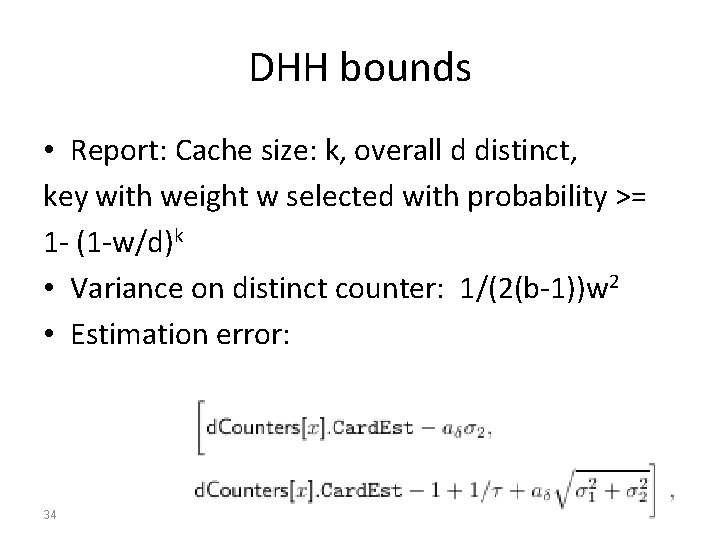
DHH bounds • Report: Cache size: k, overall d distinct, key with weight w selected with probability >= 1 - (1 -w/d)k • Variance on distinct counter: 1/(2(b-1))w 2 • Estimation error: 34
- Slides: 33