Random Number Generators for Cryptographic Applications Part 2
Random Number Generators for Cryptographic Applications (Part 2) r Werner Schindler Federal Office for Information Security (BSI), Bonn, January 24, 2008
Outline (Part 2) r Repetition r Design of crucial facts and evaluation criteria for physical RNGs r general advice r stochastic model r entropy r online r AIS tests, tot test, self test 31 and ISO 18031 r Conclusion Schindler 24. 01. 2008 Slide 2
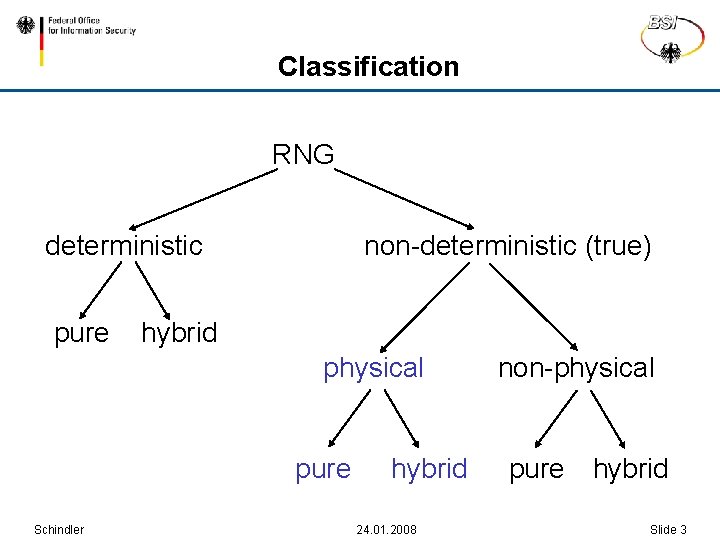
Classification RNG deterministic pure non-deterministic (true) hybrid physical pure Schindler hybrid 24. 01. 2008 non-physical pure hybrid Slide 3
General Requirements (I) R 1: Random numbers should not show statistical weaknesses (i, e. , they should pass statistical “standard tests”). R 2: The knowledge of subsequences of random numbers shall not allow to practically compute predecessors or successors or to guess them with non-negligibly larger probability than without knowledge of these subsequences. Schindler 24. 01. 2008 Slide 4

General Requirements (II) R 3: It shall not be practically feasible to compute preceding random numbers from the internal state or to guess them with non-negligibly larger probability than without knowledge of the internal state. R 4: It shall not be practically feasible to compute future random numbers from the internal state or to guess them with non-negligible larger probability than without knowledge of the internal state. Schindler 24. 01. 2008 Slide 5
Ideal RNGs r Even with maximum knowhow, most powerful technical equipment and unlimited computational power an attacker has no better strategy than “blind guessing” (brute force attack). r Guessing n random bits costs 2 n-1 trials in average. r The guess work remains invariant in the course of the time. r An ideal RNG clearly meets Requirements R 1 - R 4 r An ideal RNG is a mathematical construct. Schindler 24. 01. 2008 Slide 6
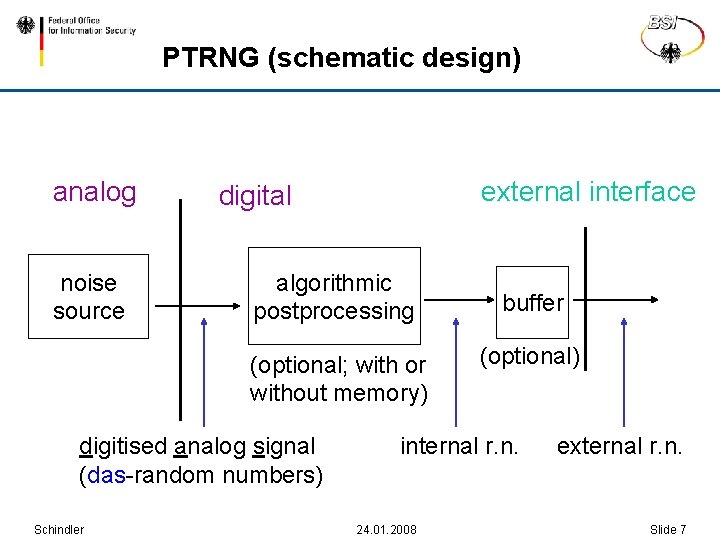
PTRNG (schematic design) analog noise source external interface digital algorithmic postprocessing (optional; with or without memory) digitised analog signal (das-random numbers) Schindler buffer (optional) internal r. n. 24. 01. 2008 external r. n. Slide 7
Noise source r The noise source is given by dedicated hardware. r The noise source exploits, for example, r noisy diodes r free-running r radioactive r quantum oscillators decay photon effects r. . . Physical RNGs (should) aim at information theoretical security. Schindler 24. 01. 2008 Slide 8
Development and Security Evaluation of PTRNGs The challenge is threefold: r Development and implementation of a strong RNG design r Verification that design and implementation are indeed strong r effective detection mechanisms for possible nontolerable weaknesses of random numbers while the PTRNG is in operation Schindler 24. 01. 2008 Slide 9
r The central part of a PTRNG security evaluation is to verify Requirement R 2. r R 1 is easy to fulfil and to check. Apart from very unusual designs R 3 and R 4 are “automatically” fulfilled. Schindler 24. 01. 2008 Slide 10
Optimal guessing strategy r Let X denote a random variable that assumes values in a finite set S = {s 1, . . . , st}. r The optimal guessing strategy begin with those values that are assumed with the largest probability. Schindler 24. 01. 2008 Slide 11
Guess work and entropy (I) r Goal of a PTRNG security evaluation: Try to estimate the expected number of guesses that is necessary to find a random number with a certain (reasonable) probability. r For real-world PTRNGs it is usually yet not feasible to determine this value directly. r Instead, entropy shall provide a reliable estimator. r Goal: Determine (at least) a lower bound for the entropy per bit (general purpose RNG). Schindler 24. 01. 2008 Slide 12
Evaluation Note: Entropy is a property of random variables and not of values that are assumed by these random variables (here: random numbers). r In particular, entropy cannot be measured as temperature, voltage etc. r General entropy estimators for random numbers do not exist. Schindler 24. 01. 2008 Slide 13
Warning r The test values of Maurer‘s „universal entropy test“ and of Coron‘s refinement are closely related to the entropy per random bit if the respective random variables fulfil several conditions. r If these conditions are not fulfilled (e. g. for pure DRNGs!) the test value need not be related to the entropy. r The adjective “universal” has caused a lot of confusion in the past. Schindler 24. 01. 2008 Slide 14
Fundamental model assumptions r We interpret random numbers as realizations of random variables. r Although entropy is a property of random variables in the following we loosely speak of the “(average) entropy per random number” instead of “(average) gain of entropy per corresponding random variable”. r. A reliable security evaluation of a PTRNG should be based on a stochastic model. Schindler 24. 01. 2008 Slide 15
Guess work and entropy (II) r The min entropy is the most conservative entropy measure. For arbitrary distribution of X a lower bound for the guesswork can be expressed in terms of the min entropy while the Shannon entropy may pretend larger guess work. Schindler 24. 01. 2008 Slide 16
Conditional entropy (I) Let X 1, X 2, . . . denote random variables that assume values in a finite set S = {s 1, . . . , st}. The conditional entropy H(Xn+1 | X 1, . . . , Xn) = H(Xn+1 | X 1=x 1, . . . , Xn=xn) * Prob(X 1 = x 1, …, Xn = xn) x 1, . . . , xn S quantifies the increase of the overall entropy when augmenting Xn+1 to the sequence X 1, . . . , Xn. Schindler 24. 01. 2008 Slide 17
Conditional entropy (II) H(X 1, . . . , Xn+1) = H(X 1, . . . , Xn) H(Xn+1 | X 1, . . . , Xn) =. . . = H(X 1) H(X 2 | X 1). . . H(Xn+1 | X 1, . . . , Xn) This formula is very useful to determine the entropy of dependent sequences. There is no pendant for the min entropy. Schindler 24. 01. 2008 Slide 18
Guess work and entropy (III) r Assume that X 1, X 2, . . . denotes a sequence of binaryvalued iid (identically and identically distributed) random variables. Unless n is too small H(X 1, X 2, . . . , Xn)/n log 2(E(number of guesses per bit)) r The assumption “iid” may be relaxed, e. g. to “stationary with finite memory”. r If the random variables X 1, X 2, . . . , Xn are ‘close’ to the uniform distribution all parameters give similar Renyi entropy values. Schindler 24. 01. 2008 Slide 19
Guess work and entropy (IV) r (At least) the internal random numbers usually fulfil both the second and the third condition. r Hence we use the Shannon entropy in the following since it is easier to handle than the min entropy ( conditional entropy). Schindler 24. 01. 2008 Slide 20
The stochastic model (I) r Goal: Estimate the increase of entropy per internal random number r Ideally, a stochastic model should specify a family of probability distributions that contains the true distribution of the internal random numbers. r It should at least specify a family of distributions that contain the distribution of the r das random numbers or r of ‚auxiliary‘ random variables that allow to estimate the increase of entropy per internal random number. Schindler 24. 01. 2008 Slide 21
Example 5: Coin Tossing r PTRNG: A single coin is tossed repeatedly. "Head" (H) is interpreted as 1, "tail" (T) as 0. r Stochastic model: r The observed sequence of random numbers (here: heads and tails) are interpreted as values that are assumed by random variables X 1, X 2, …. r The random variables X 1, X 2, … are assumed to be independent and identically distributed. (Justification: Coins have no memory. ) rp Schindler : = Prob(Xj = H) [0, 1] with unknown parameter p 24. 01. 2008 Slide 22
Example 5: Coin Tossing (II) r Note: A physical model of this experiment considered the impact of the mass distribution of the coin on the trajectories. The formulation and verification of the physical model is much more complicated than for the stochastic model. Schindler 24. 01. 2008 Slide 23
The stochastic model (II) r. A stochastic model is not equivalent to a physical model. In particular, it does not provide the exact distribution of the das random numbers or the internal numbers in dependency of the characteristics of the components of the analog part. r Instead, the stochastic model only specifies a class of probability distributions which shall contain the true distribution (see also Example 5). r The class of probability distributions usually depends on one or several parameters. Schindler 24. 01. 2008 Slide 24
The stochastic model (III) r The stochastic model shall be verified by measurements / experiments. r The parameter(s) of the true distribution are guessed on basis of measurements. r The stochastic model allows the design of effective online tests that are tailored to the specific RNG design. Schindler 24. 01. 2008 Slide 25
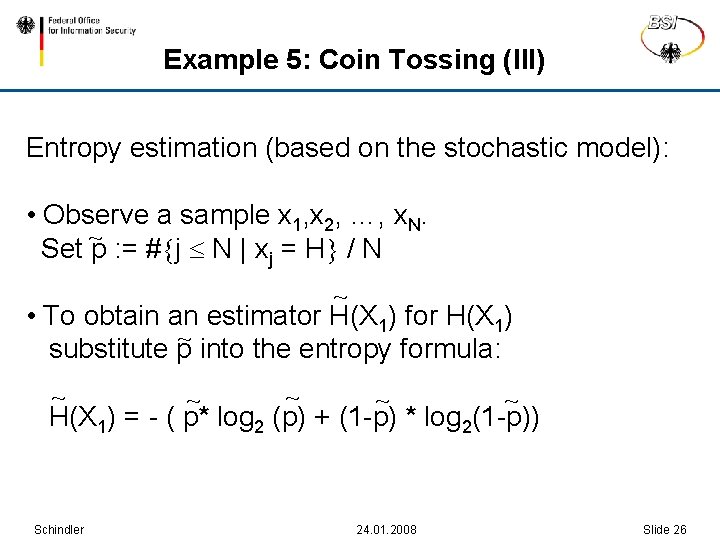
Example 5: Coin Tossing (III) Entropy estimation (based on the stochastic model): • Observe a sample x 1, x 2, …, x. N. Set ~p : = # j N | xj = H / N ~ • To obtain an estimator H(X 1) for H(X 1) ~ substitute p into the entropy formula: ~ ~ ~ H(X 1) = - ( p* log 2 (p) + (1 -p) * log 2(1 -p)) Schindler 24. 01. 2008 Slide 26
The stochastic model (IV) r For PTRNGs the justification of the stochastic model is usually more complicated and requires more sophisticated arguments. r To estimate entropy the parameter(s) are estimated first, and therefrom an entropy estimate is computed (cf. Example 5). r If the random numbers are not independent the conditional entropy per random bit has to be considered. Schindler 24. 01. 2008 Slide 27
![Example 6 (I) PTRNG design proposed in [Tk] ring oscillator 1 43 bit LFSR Example 6 (I) PTRNG design proposed in [Tk] ring oscillator 1 43 bit LFSR](http://slidetodoc.com/presentation_image/1c460ac971c428ea2ad228c2f07fe445/image-28.jpg)
Example 6 (I) PTRNG design proposed in [Tk] ring oscillator 1 43 bit LFSR k bit permutation k bit ring oscillator 2 permutation output (internal random number) 37 bit CASR = Cellular Automaton Shift Register (GF(2)-linear) Schindler 24. 01. 2008 Slide 28
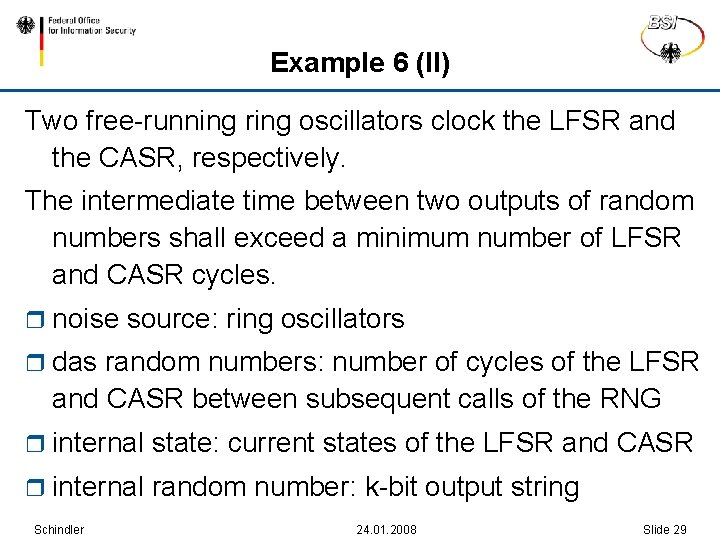
Example 6 (II) Two free-running ring oscillators clock the LFSR and the CASR, respectively. The intermediate time between two outputs of random numbers shall exceed a minimum number of LFSR and CASR cycles. r noise source: ring oscillators r das random numbers: number of cycles of the LFSR and CASR between subsequent calls of the RNG r internal state: current states of the LFSR and CASR r internal random number: k-bit output string Schindler 24. 01. 2008 Slide 29
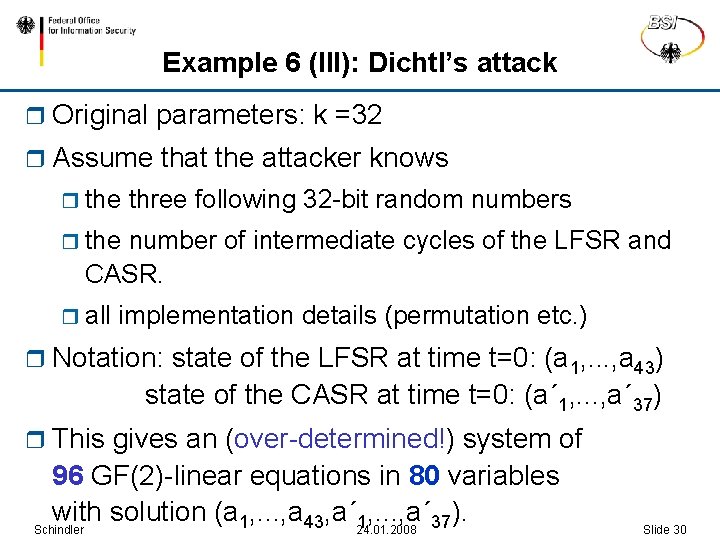
Example 6 (III): Dichtl’s attack r Original parameters: k =32 r Assume that the attacker knows r the three following 32 -bit random numbers r the number of intermediate cycles of the LFSR and CASR. r all implementation details (permutation etc. ) r Notation: state of the LFSR at time t=0: (a 1, . . . , a 43) state of the CASR at time t=0: (a´ 1, . . . , a´ 37) r This gives an (over-determined!) system of 96 GF(2)-linear equations in 80 variables with solution (a 1, . . . , a 43, a´ 24. 01. 2008 1, . . . , a´ 37). Schindler Slide 30
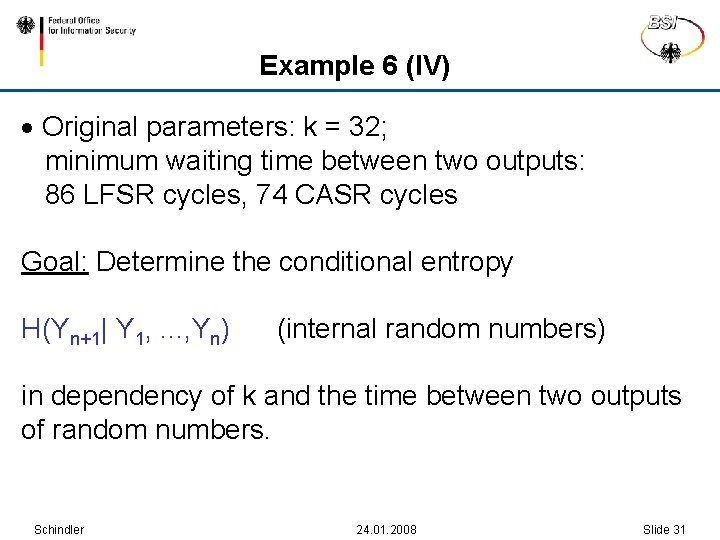
Example 6 (IV) · Original parameters: k = 32; minimum waiting time between two outputs: 86 LFSR cycles, 74 CASR cycles Goal: Determine the conditional entropy H(Yn+1| Y 1, . . . , Yn) (internal random numbers) in dependency of k and the time between two outputs of random numbers. Schindler 24. 01. 2008 Slide 31
Example 6 (V) Upper entropy bound: At least in average, H(Yn+1| Y 1, . . . , Yn) H(V 1, n+1) + H(V 2, n+1) where the random variables V 1, n+1 and V 2, n+1 describe the number of cycles of the two ring oscillators between two calls of the RNG Lower entropy bound: Estimate the entropy from below that the output function extracts from the internal state. Schindler 24. 01. 2008 Slide 32
![Example 6 (VI) r In [Sch 3] a thorough analysis of the PTRNG design Example 6 (VI) r In [Sch 3] a thorough analysis of the PTRNG design](http://slidetodoc.com/presentation_image/1c460ac971c428ea2ad228c2f07fe445/image-33.jpg)
Example 6 (VI) r In [Sch 3] a thorough analysis of the PTRNG design is given. Both a lower and an upper entropy bound per internal random bit are given that depend on r the intermediate time between subsequent outputs in multiples of the average cycle time r the jitter of the ring oscillators r the bit length k of the internal random numbers. Schindler 24. 01. 2008 Slide 33
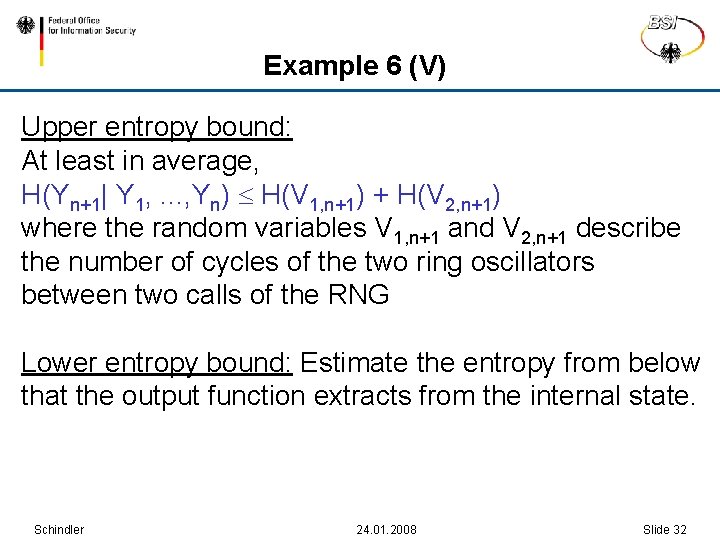
Example 6 (VII): Numerical values r r = average cycle length = 0. 01 (optimistic assumption) Time k internal state entropy per random number (increase of entropy) 10000 1 10000 60000 Schindler 4, 209 0. 943 4. 209 0. 914 3 4. 209 0. 866 1 6. 698 0. 991 2 24. 01. 2008 Slide 34
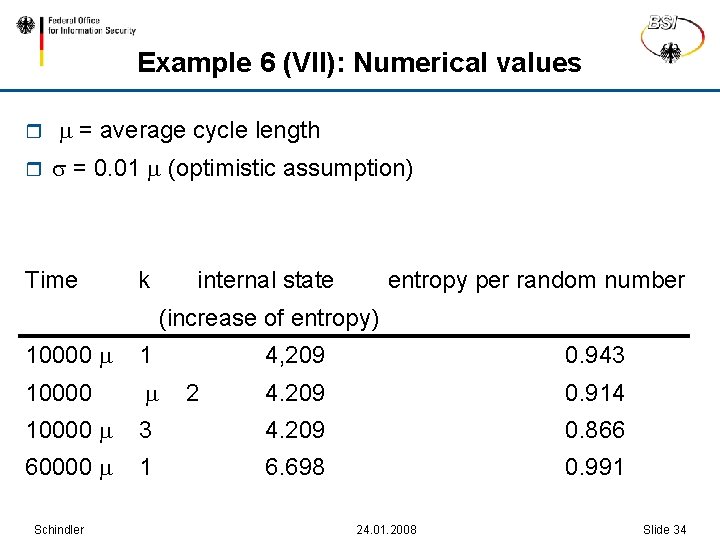
Example 7 internal random numbers Schindler 24. 01. 2008 Slide 35
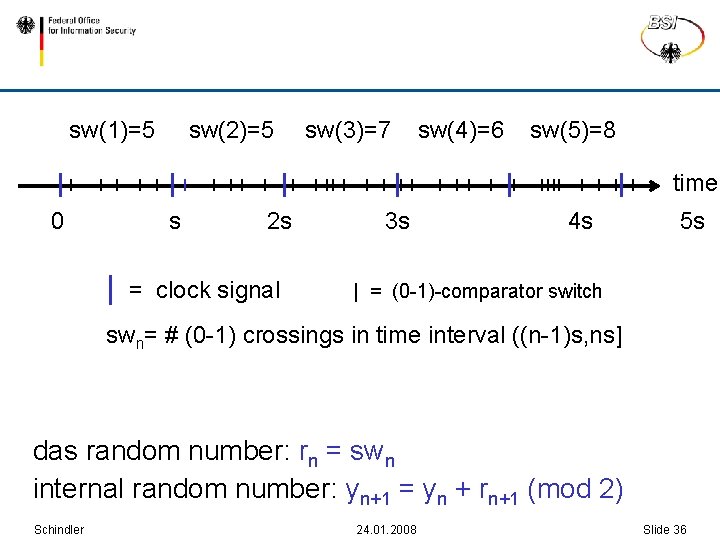
sw(1)=5 sw(2)=5 sw(3)=7 sw(4)=6 sw(5)=8 time 0 s | 2 s = clock signal 3 s 4 s 5 s | = (0 -1)-comparator switch swn= # (0 -1) crossings in time interval ((n-1)s, ns] das random number: rn = swn internal random number: yn+1 = yn + rn+1 (mod 2) Schindler 24. 01. 2008 Slide 36
Strategy r Goal: Determine (at least a lower bound for) H(Yn+1 | Y 0, . . . , Yn) r. Remark: Example 7 contains joint research work with Wolfgang Killmann. Schindler 24. 01. 2008 Slide 37
Notation r t 1, t 2, . . : time periods between subsequent switches of the comparator r zn: smallest index m for which t 0+t 1+t 2+. . . +tm>sn r wn = t 0+t 1+t 2+. . . +tm -sn (or, equivalently, wn t 0+t 1+t 2+. . . +tm (mod s) ) wn denotes the time between sn and the next comparator switch Schindler 24. 01. 2008 Slide 38
Stochastic model (II) r It is reasonable to assume that the noise source is in equilibrium state shortly after start-up. r The stochastic process T 1, T 2, . . . is assumed to be stationary (not necessarily independent !). Schindler 24. 01. 2008 Slide 39
Stochastic Model (III) The das random numbers in Example 6 and Example 7 (and the das random numbers of other RNGs designs) can be modelled as follows: T 1, T 2, … are stationary Rn : = Zn-1 with Zn : = min {m N | T 0 + … + Tm >sn} Schindler 24. 01. 2008 Slide 40
General remark r Even if two different RNG designs fit to this model the distribution of the random variables T 1, T 2, … and thus of R 1, R 2, . . . may be very different. Schindler 24. 01. 2008 Slide 41
Stationarity r The stochastic process T 1, T 2, . . . is assumed to be stationary r. Under weak assumptions (essentially, the partial sums T 1+T 2 +. . . + Tm (mod s) should tend to the uniform distribution on [0, s)) it can be shown that the sequences W 1, W 2, . . . and R 1, R 2, . . . are stationary, too. r. Strategy: Study the stochastic process R 1, R 2, . . . first. Schindler 24. 01. 2008 Slide 42
Stochastic model (IV) Definition r V(u) : = # 0 -1 switchings in [0, u] r μ = E(Tj) r σ² : = generalized variance of T 1, T 2, . . . r (. ): = cumulative distribution function of the standard normal distribution Schindler 24. 01. 2008 Slide 43
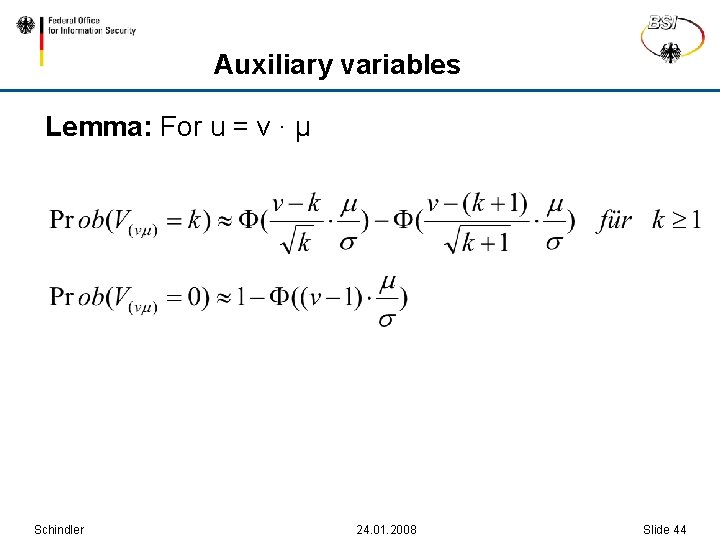
Auxiliary variables Lemma: For u = v ∙ μ Schindler 24. 01. 2008 Slide 44
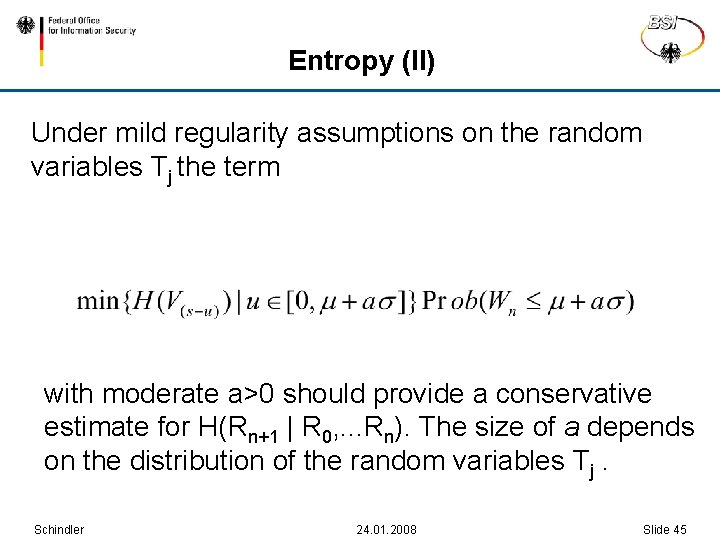
Entropy (II) Under mild regularity assumptions on the random variables Tj the term with moderate a>0 should provide a conservative estimate for H(Rn+1 | R 0, . . . Rn). The size of a depends on the distribution of the random variables Tj. Schindler 24. 01. 2008 Slide 45
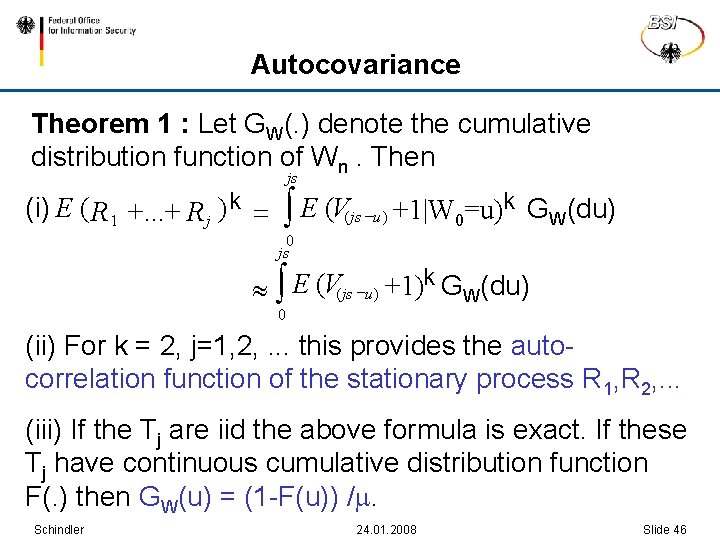
Autocovariance Theorem 1 : Let GW(. ) denote the cumulative distribution function of Wn. Then (i) E ( R 1 +. . . + R j ) k = js ò E (V ( js -u ) +1|W 0=u)k GW(du) 0 js ò E (V(js -u ) +1)k GW(du) 0 (ii) For k = 2, j=1, 2, . . . this provides the autocorrelation function of the stationary process R 1, R 2, . . . (iii) If the Tj are iid the above formula is exact. If these Tj have continuous cumulative distribution function F(. ) then GW(u) = (1 -F(u)) /. Schindler 24. 01. 2008 Slide 46
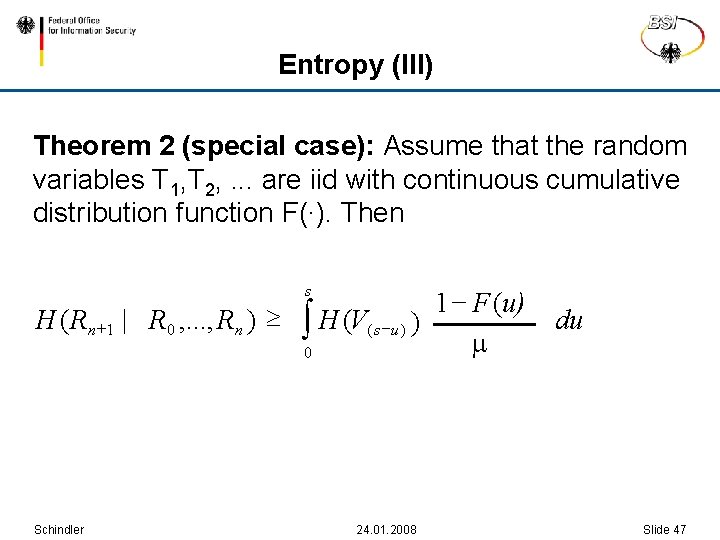
Entropy (III) Theorem 2 (special case): Assume that the random variables T 1, T 2, . . . are iid with continuous cumulative distribution function F(∙). Then 1 - F (u) H ( Rn +1 | R 0 , . . . , Rn ) ò H (V( s -u ) ) 0 s Schindler 24. 01. 2008 du Slide 47
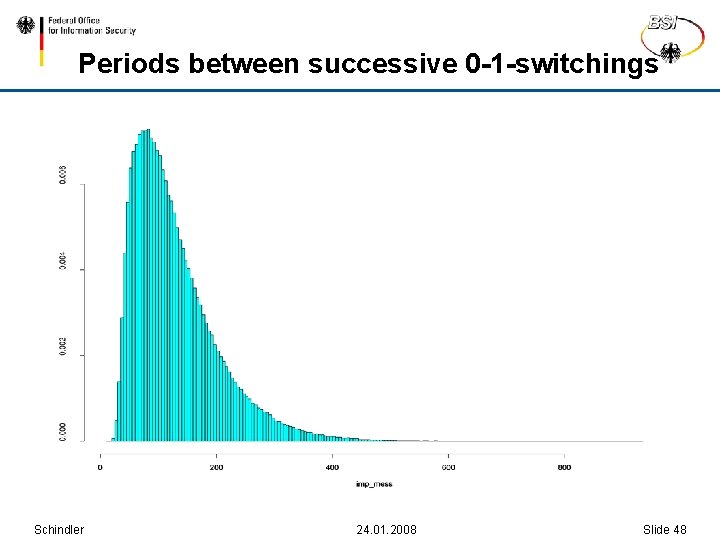
Periods between successive 0 -1 -switchings Schindler 24. 01. 2008 Slide 48
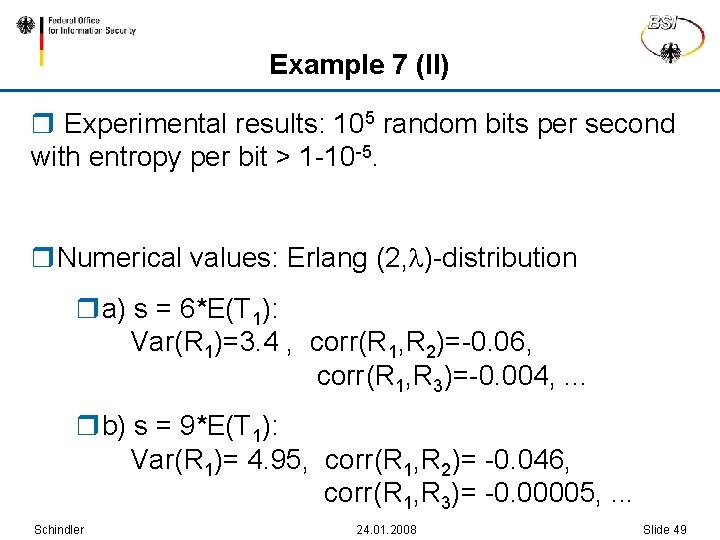
Example 7 (II) r Experimental results: 105 random bits per second with entropy per bit > 1 -10 -5. r. Numerical values: Erlang (2, )-distribution ra) s = 6*E(T 1): Var(R 1)=3. 4 , corr(R 1, R 2)=-0. 06, corr(R 1, R 3)=-0. 004, . . . rb) s = 9*E(T 1): Var(R 1)= 4. 95, corr(R 1, R 2)= -0. 046, corr(R 1, R 3)= -0. 00005, . . . Schindler 24. 01. 2008 Slide 49
PTRNGs in operation: Potential risks r Worst case: total breakdown of the noise source r. Ageing effects, tolerances of components of the noise source and external influences might cause the generation of random numbers with unacceptably low quality. Such events must be detected certainly so that appropriate responses can be initiated. Schindler 24. 01. 2008 Slide 50
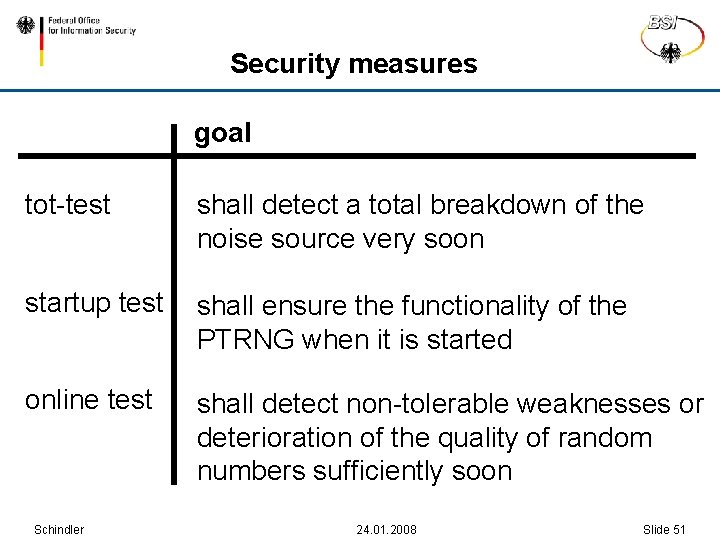
Security measures goal tot-test shall detect a total breakdown of the noise source very soon startup test shall ensure the functionality of the PTRNG when it is started online test shall detect non-tolerable weaknesses or deterioration of the quality of random numbers sufficiently soon Schindler 24. 01. 2008 Slide 51
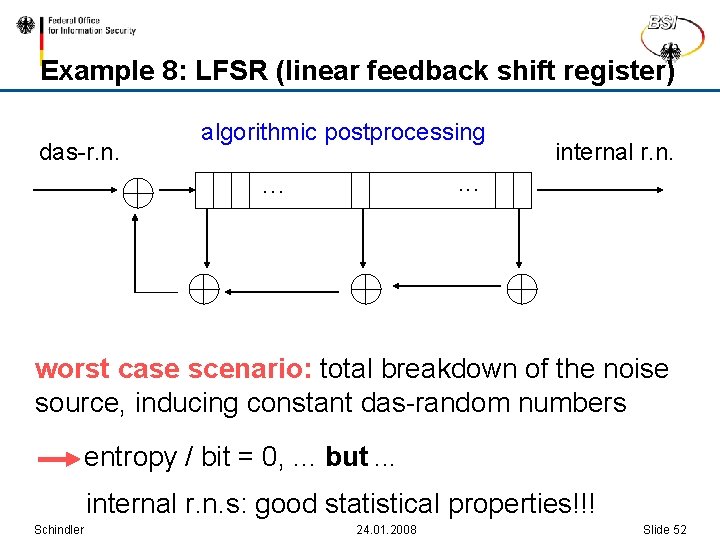
Example 8: LFSR (linear feedback shift register) das-r. n. algorithmic postprocessing internal r. n. . . . worst case scenario: total breakdown of the noise source, inducing constant das-random numbers entropy / bit = 0, . . . but. . . internal r. n. s: good statistical properties!!! Schindler 24. 01. 2008 Slide 52
Example 8 (II) r Statistical blackbox tests that are applied to the internal random numbers will not even detect a total breakdown of the noise source (unless the linear complexity profile is tested). r Instead, the online test should be applied to the das random numbers (typical situation). Schindler 24. 01. 2008 Slide 53
General Remark r The online test should be tailored to the particular RNG ( stochastic model). r In Example 5 (coin tossing) a monobit test would be appropriate. r In [Sch 1] a generic two-step procedure for the tot test, the startup test and the online test is introduced. Schindler 24. 01. 2008 Slide 54
Noise alarms r A failure of the online test, the tot test or the startup test causes a noise alarm. r (At least) the online test is usually realized by statistical tests. Consequently, „false noise alarms“ may occur. r The probability for a false noise alarm depends on the significance level of the statistical tests and the evaluation rules. Schindler 24. 01. 2008 Slide 55
Consequences of a noise alarm The consequences of a noise alarm may depend on the conditions of use. Possible reactions: r The PTRNG is shut down. r A human operator or the PTRNG software initiates an „emergency test“. Depending on the outcome of this emergency test the PTRNG is either shut down or put into operation again. r audit of noise alarms r… Schindler 24. 01. 2008 Slide 56
ITSEC and CC ITSEC (Information Technology Security Evaluation Criteria) and CC (Common Criteria) r provide evaluation criteria for IT products which shall permit the comparability between independent security evaluations. r A product or system that has successfully been evaluated is awarded with an internationally recognized IT security certificate. Schindler 24. 01. 2008 Slide 57
CC: Evaluation of Random Number Generators ITSEC, CC and the corresponding evaluation manuals do not specify evaluation criteria for random number generators. In the German evaluation and certification scheme the evaluation guidance document AIS 31: Functionality Classes and Evaluation Methodology for Physical Random Number Generators has been effective since September 2001 Schindler 24. 01. 2008 Slide 58
AIS 31 distinguishes between two functionality classes with increasing requirements P 1 (for less sensitive applications as, for instance, IVs that are transmitted in clear) P 2 (for sensitive applications as, for instance, the generation of session keys, signature parameters, ephemeral keys) Schindler 24. 01. 2008 Slide 59
AIS 31: Reference Implementation r The AIS 31 is technically neutral. The applicant for a certificate has to give evidence that the PTRNG meets all requirements. r The AIS 31 has been well-tried in a number of product evaluations. r A reference implementation of the applied statistical tests can be found www. bsi. bund. de/zertifiz/zert/interpr/ais_cc. htm Schindler 24. 01. 2008 Slide 60
Alternative security paradigm r The crucial points of an AIS 31 evaluation are the understanding of the design and the effectiveness of the online test. Alternative approach (e. g. , ANSI X 9. 82, Part 2 (draft)): r complex algorithmic postprocessing algorithm with memory that meets requirements R 1 -R 3. Schindler 24. 01. 2008 Slide 61
Alternative security paradigm: Advantages and disadvantages r (+) minor requirements on the understanding of the RNG design r (+) minor requirements on the effectiveness of the online tests r (-) requires a time-consuming postprocessing algorithm r (-) possibly (without being noticed!) only practical security r (-) requires the protection of the internal state Schindler 24. 01. 2008 Slide 62
ISO / IEC 18031 „Random Bit Generation“ r covers all classes of RNGs r PTRNGs: Allows design principles that either follow the AIS 31 or the ANSI X 9. 82 (draft) approach r considers also the correctness of the implementation Schindler 24. 01. 2008 Slide 63
Final remark Combining ra strong noise source r with effective online tests r and a strong algorithmic postprocessing algorithm provides two security anchors which ensure theoretical security and computational security, respectively. Schindler 24. 01. 2008 Slide 64
Contact Federal Office for Information Security (BSI) Prof. Dr. Werner Schindler Godesberger Allee 185 -189 53175 Bonn Tel: +49 (0)3018 -9582 -5652 Fax: +49 (0)3018 -10 -9582 -5652 Werner. Schindler@bsi. bund. de www. bsi-fuer-buerger. de Schindler 24. 01. 2008 Slide 65
Ersatzfolien r ERSATZFOLIEN Schindler 24. 01. 2008 Slide 66
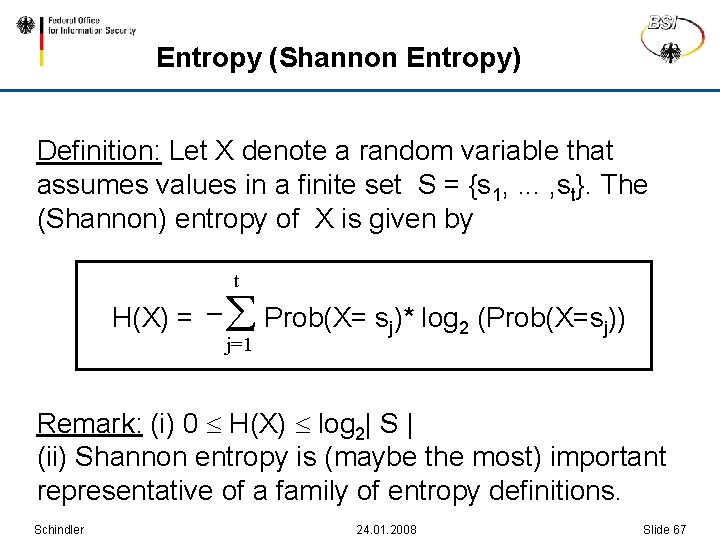
Entropy (Shannon Entropy) Definition: Let X denote a random variable that assumes values in a finite set S = {s 1, . . . , st}. The (Shannon) entropy of X is given by H(X) = _ t Prob(X= sj)* log 2 (Prob(X=sj)) j=1 Remark: (i) 0 H(X) log 2| S | (ii) Shannon entropy is (maybe the most) important representative of a family of entropy definitions. Schindler 24. 01. 2008 Slide 67
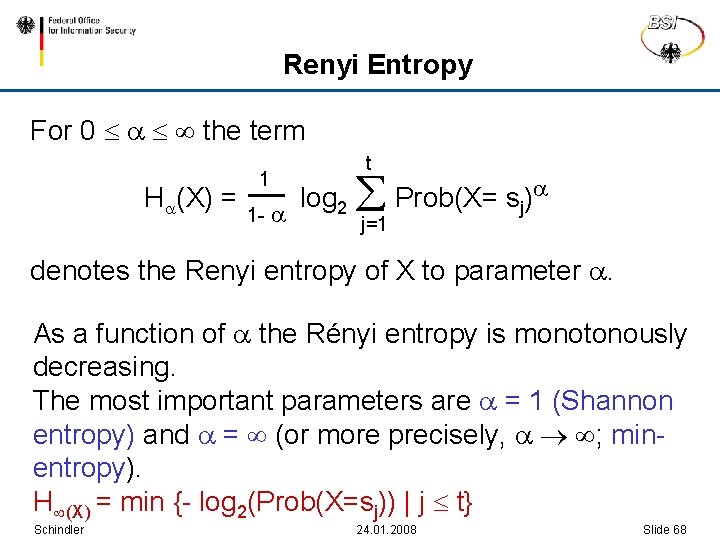
Renyi Entropy For 0 the term t 1 __ H (X) = log 2 Prob(X= sj) 1 - j=1 denotes the Renyi entropy of X to parameter . As a function of the Rényi entropy is monotonously decreasing. The most important parameters are = 1 (Shannon entropy) and = (or more precisely, ; minentropy). H (X) = min {- log 2(Prob(X=sj)) | j t} Schindler 24. 01. 2008 Slide 68
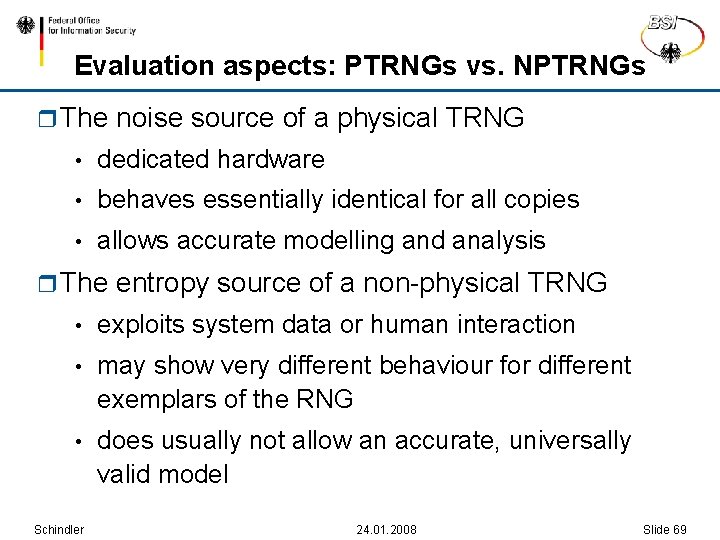
Evaluation aspects: PTRNGs vs. NPTRNGs r The noise source of a physical TRNG • dedicated hardware • behaves essentially identical for all copies • allows accurate modelling and analysis r The entropy source of a non-physical TRNG • exploits system data or human interaction • may show very different behaviour for different exemplars of the RNG • does usually not allow an accurate, universally valid model Schindler 24. 01. 2008 Slide 69
- Slides: 69